Multilayer Approach to Defend Phishing Attacks
Spam messes up users inbox, consumes resources and spread attacks like DDoS, MiM, phishing etc. Phishing is a byproduct of email and causes financial loss to users and loss of reputation to financial institutions. In this paper we examine the charact…
Authors: Cynthia Dhinakaran, Dhinaharan Nagamalai, Jae Kwang Lee
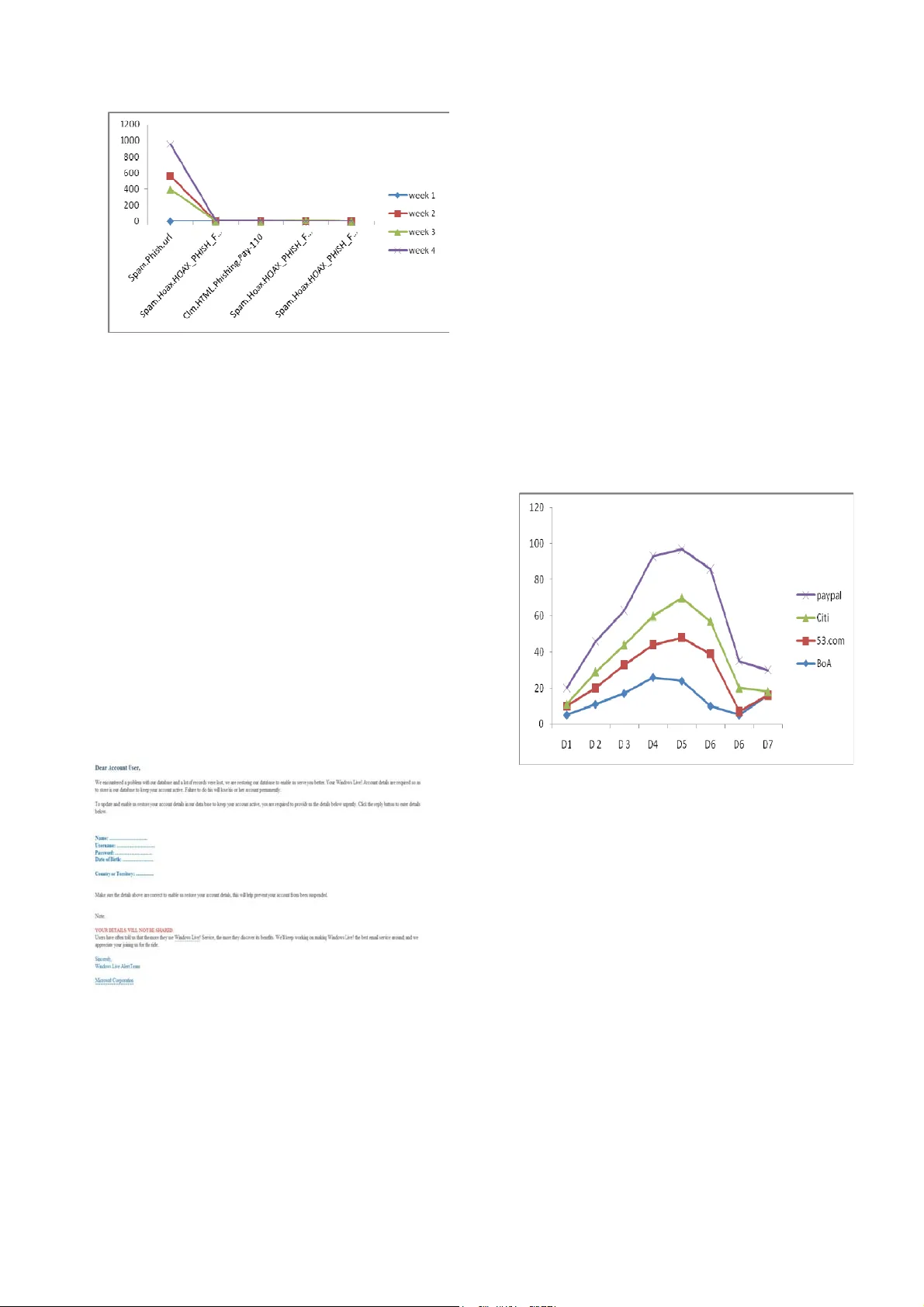
Multilayer Approach to Defend Phishing Attacks CYNTHIA DHINAKARAN 1 , DHINAHARAN NAGAMALAI 2 , JAE KWANG LEE 1 1 Department of Computer E ngineerin g 1 Hannam University, 2 Wireilla Net Solutions 1 SOUTH KOREA Abstract Spam messes up users inbox, c onsum es resources and spread attacks like DDoS, MiM, phishing etc. Phishing is a byproduct of email and causes fi nancial loss to users a nd loss of reputa tion to financial institutions. In this paper we examine the characteristics of phishing and techno logy used by Phishers. In order to co unter anti- phishing technology, phishers cha nge thei r mode of ope ration; t herefore a co ntinuous e valuation o f phishing only help s us combat phisher effectiveness. In our study, we col lected seven hundre d thous and spam fro m a corporate server for a period of 13 months from February 2008 to February 2009. From the collected data, we identified different kinds of phishing sc ams and m ode of operat ion. Our observation s hows that phishers a re dynam ic and de pend m ore on social e ngineerin g technique s rather t han soft ware vulnerabilities. We believe that this stud y will develop more efficient anti -phishi ng methodol ogies. Ba sed on o ur analys is, we develope d an anti- phishing m ethodol ogy and im plem ented in our networ k. The results show that this approach is highly effective to prevent phishing a ttacks. The proposed approach reduced more than 80% of the false ne gatives and more tha n 95% of phishing attacks in our network. Keywords : Phishing, vir us, worms and t rojon, s ocial engineering , spam . 1 Introduction Our modern world belie ves that em ail is great tool for the manageme nt and dissemi nation of info rmation. Em ail provides an e asy path fo r data fl ow in and out of a controlled local network. At the same time, the market of illegal business through In ternet is growing. Phishing is one kind of illegal business that ch allenges online transaction systems. Phishing m ail reaches millions of end users by s pam[5] and spammers are using well designed software tools as well as social engineeri ng methodolo gies to reach thes e end users. Phis hing tools are highly sophisticated such that phishers can fix the duration of the attack, frequency of att ack to the particular target, subject of t he phishing mail, co ntents of t he message, hiding the sour ce of the mail etc., Some of the sample automated tools are Email Spoofer, Bulk Mailer, Aneim a 2.0, Avalanche 3.5, Eut hanasia etc[4]. P hishing is a kind o f spam causing reputation, economic and man power loss. Phishers heavily utilize social en gineering techniques to lure email users and divulge their valuable data. The data includes name , pass phrase, social secu rity numbers, telephone numbers, address , and email accounts etc. Many types of phishi ng have been re ported in rece nt years, including: a ) the m ost common way of diverting t he end-user to f raudulent we bsite cont rolled by a phisher by clicking a hyperlink av ailable in an email; the fraudulent website then asks the user to divulge the sensitive information and this lead s to loss. b) asking the us er to contact a phis hers telepho ne num ber or fax num ber. c) through instant messagi ng from unknown cont acts leading to password and identity th eft. Most phishing activities are associated with fin ancial institutions, eco mmerce websites, and online greeting card services. Phishing is closely related to spamming . We identify that some spammers are do ing spamming as well as phishing simultaneously. Anti-spam techno logy ranges from simple content filters to sophisticated software based on various algorithm s such as Bayesian and are widely used to stop s pam. But spammers always find new ways to reach users inbox. The ar ms race between anti-spam software devel opers and s pamm ers causes huge co ncern to the Internet commun ity. Anti-spam filters are highly useful to defend the p hishing scam s an d, apart from this, there are plenty of tools that are av ailable to fight against phish ing scams. For exam ple CallingI d, Cloudm ark, Earthl ink, eBay, Netcraft, Tr ustwatch, Sp oofguard, Si te Advisor [3] are some of th e anti-phishi ng tools wo rth mentioni ng here. But unfort unately m ost of these to ols do not p rovide adequate prot ection to the e nd users. Acco rding to the [3] research, the best anti-ph ishi ng software too l identifies 50% of false positives. There are more than 2 do zen free anti-phishing too ls available to en d users but because phishers change t heir tacti cs regularly based on anti-phishe rs take do wn appro ach as well as anti-phishing software, the anti-phishing tools are not ab le to cope with the technology of phishers. Phish ing is an attack exploitin g human vulnerabilities rath er than technical vulnerabilities. According to the Gardener [16] survey, phish ing will grow in near future since it is a profitable busin ess. In this paper we will discuss how the phis hers operate a successful businesses and th e kind of technology they u se and how they make use of s ocial engineering m ethods. Final ly we conclude with effective countermeasures to this problem. We believe that this study will develop more efficient anti-phishi ng met hodologies. In our study, we collected seven hundred thou sand spam from a corp orate server f or a perio d of 13 m onths from February 2008 to Februar y 2009. From the collected data, we identified d ifferent ki nds of phishi ng scam s and mode of operation. Our observ ation shows that ph ishers are dynamic and depend m ore on social en gineering techniques rather than softwa re vulnerab ilities. We believe that this study will develop more efficient anti-phish ing methodologies. Based on our an alysis, we developed an anti-phishing methodolog y and implemented in our network fr om Februa ry 2009 to February 2010. T he results show that this approach is highly effecti ve to prevent phishing attack s. The proposed appro ach reduced more than 80% of the false negatives and m ore than 95% of phishing at tacks in o ur networ k.In this paper we propose a multi layer approach to defend phishing attacks. This approach is a combinatio n fine tuning of spamming techniques, periodically classify ing false negative to spam, block the attackers IP addres ses, using source and content filters to mark phishing attemp t, educate and train users, report to service providers and targ et Institution. Th e results show that this approach is highly effective to prevent phis hing attacks. The proposed a pproach re duced more than 80% of the false negatives and more than 95% of phishing att acks in our network. The remaining sections are or ganized as follows. Section 2 provides bac kground on phishin g and spa m and the e ffects. Section 3 pr ovides data c ollection a nd experi mental resul ts. In section 4 and 5 we describe t he methodol ogies used by phishers. Sect ion 6 pr ovides the c ountermeasure propose d by us to the p hishing scam . We concl ude in secti on 7. 2 Related Work [1] Authors analyze the human factors involved in phishing attacks and suggest few techni ques as remedy. According to their study, m ost phishing em ails are not si gned by a person but by position or org anization like Account Manager, PayPal etc. Phishers are least bothered about the design, spelling errors and copyright information in their web site. Even legitimate web pages emphasize more on security issues, creates panic among the user c ommunity. Their study reveals that some of the th ird party security endorsements are not well re ceived by the users. Also the email stimuli is more phishy than web stimuli and the phishers use automated phone m essages to increase the vulnerability of th e users. [2]The authors examine the characteristics of phishing URLs, domain and machines used to host phish ing domains and determined phish ers are more active than ordinary user s and they activate their sites immediately after reg istering their domain and bring it down whene ver desired. Phis hing URLs nor mally contain the target’s name but the l ength of t he target name is different f rom the original, for phishi ng doma in names are significantl y diffe rent from regular En glish c haracter frequency. T heir study also reveals that m ost phishing hosted servers are not available in standard ports. Phishers usually do this to avo id the identificatio n of life span of the web site. [3] Present a multi-layer approach to defend DDoS attacks caused by spam . Their study reveals the effectiveness of SURBL, DN SBLs, content filters and present chara cterist ics of vir us, worms and T rojans accompanied by spam as an attachment. The multi-layer approach defends agai nst DDoS attacks effectively. [4] The authors o bserve that s pammers use aut omated t ools to send spam with attachment. The m ain features of this software are hiding sender’s identity, randomly selecting text messages, identifying open relay machines, mass mailing capab ility and defining spamming duration . They table that heavy users email a ccounts are m ore vulnerable than relatively new email acco unts[5][20][21]. The authors test ten well- known anti-p hishing software tools to evaluate the perf ormance of anti -phishing s oftware tools . Their study reveals that none of t he tools are 100% accurate and only one tool works better than rest with more than 42% of false positive. The authors also id entify many of the phishing sites taken down within hours. Some of these tools didn’t detect phishing. In our study , we identify phishers sen ding ma il from different so urces or dif ferent IP addresses . The take down approach works good to chase phisher s temporaril y but not to eliminate them total ly. The authors iden tify that the perform ance of anti -phishing tools va ry dependi ng on t he source of phis hing URLs. These to ols are base d on black lists, white lists, heuristics and community rating s. Most of these technologies a re simi lar to anti-spa m technolo gies with little modification s for phishing. 3 Data Collection In our study we character ized phishing mail fr om a collection of ov er 700 000 spam over a per iod of 13 month s from Feb 2008 to Feb 2009 f rom a corporat e mail server. The mail server provides se rvices to 280 users with 30 group emai l accounts and 290 indi vidual mail accounts. The speed of Internet conn ection is 100 Mpbs with 40 Mbps upload and download s peed; due to security and privacy conce rns, we are unable to disclose the real domain name. In order to segregate spam from legitimate mails, we conducted standard spam detection tests on our server. The spam mails detected by thes e techniques were directed to the spam trap that is set up on mail server. The spam mails were usually related to f inance, phar macy, busine ss promoti on, adultery services and viruses. C onsidera ble portion of these spam mai ls were used for phi shing, DDoS attacks, MiM attacks etc. From this collection, we separated phishing mails by a small progra m written in Python. In this pape r we study the characteristics of phishing a nd the technol ogy use d by phishe rs. In or der to counter anti -phishi ng techno logy, phis hers change t heir mode of ope ration frequentl y; this required us to pe rform a continual eval uation of the c h aracteristics of phishing and their technology. Th e results of these evalu ations help us to enhance exist ing anti-phis hing tech nology an d combat phishers effectively. 0 20000 40000 60000 80000 100000 120000 140000 160000 180000 Feb Mar Apr May Jun Jul Aug Sep Oct Nov Dec Jan F eb email sp a m vi ru s phis hing Figure 1. Mail traffic Figure 1 shows the incoming mail traffic of our mail server for 13 months from Feb 2008 to Feb 2009. X ax is identifies the month and Y axis identifies the number of mail, spam, virus, and phishing mail received by en d use rs. As seen from the graph, the spam traffic is not related to virus and phishing quantitatively. But o ur analysis shows common factors in spa m and phishi ng like se nders, and t he technol ogy used. R oughly the number of phis hing ma ils ranges f rom 369 to 3459 with an average rate of 1516 per month. Th is statistic does not include false negatives. We believe that this analysis could be useful to develop m ore efficient ant i-phishing t echniques 4 Phishing Methodologies Since phishers use c ombination o f spam and othe r techniqu es to reach end users, we have genera ted a table of our fi ndings in this section. Our spam collection contains ma jor phi shing scam s as shown in Table 1. It is evident th at other virus, worm, and Trojan entities are used to phish end users. There are two types of phishing methodolo gies detected t hrough our data coll ection: one method is a simple link in the spam mail where phishers lure end users to divulge their sensitive information and the other is approaching end users with Tr ojan, malware & viruses. The following are the malware, Troj an and virus entities u sed for phishin g. Name of vir us, worm , Trojan Spam.Phish.url Spam.Hoax.HOAX_PH ISH_FORGED_PAYPAL Clm.HTML.Phishing.Pay-110 Spam.Hoax.HOAX_PH ISH_FORGED_EBA Y Spam.Hoax.HOAX_PH ISH_FORGED_CITIBNK Trojan.spy.h tml.bankfraud.od Table 1:List of Virus,worm ,Trojon 4.1 Spam.Phis h.url This is a common phish ing scam used to target all the types of users with al l brands. The m ajor brand sp oofed by spam.Phish.url are Citi, Paypal, 53, fifth third bank and some other s mall brands. The num ber of spam mail received by these scam are far more than others. As shown in Table 1, the num ber of such m ails is 100 t imes m ore than any other part icular phishing scam. We identified two types of phi shing m ethods for spam.Phish. url. The fi rst method in volves phi shers direct ing spam to end-users through their own machines with well designed software. By targeting users in this manner, ph ishers target big brands. The s econd method spammers target unpopular brands and their users through Botn et. Mostly the target contains a logi n and password page w here users are asked to enter the log in and password which, ulti mately, are controlled by phishers. T heir subject li ne is not pr operly designed like the previous o ne. 4.2SPAM.H OAX_PHISH _FORGED_ CI TIBNK This phishing spam target s Citibank account holders to divulge their Citibank ATM/Debit card and PIN numbers. The link given in the mail takes the user to a non -secure site controlled by the phishers. Mostly these sites are owned by frau dsters using fake names. Wh en we checked their websites, they seemed to have disappear ed by the take down approa ch. The phishing related to Citiban k was mostly sh ort lived a nd the number of sca m our domain received in this category is less as s hown in the Figure 2. 4.3 Spam.hoax.Hoax_ Phish_forged_ paypall This is another ki nd of phis hing scam t hat targets Paypal users. Spam using this method ask users to divulge their Paypal identity b y using social engineering techn iques that tell users to update their iden tity as earlier as possible before doing an y financial online activity such as onlin e purchases, m oney transfers through em ail, and paym ent to the commercial websites. The phishi ng mail asks use rs to update their details before using the Paypal account. The user will be taken to a non-secure website controlled by fraudsters. 4.4 Clm.HTM L.Phishing.P ay-110 This type of phishing scam doesn’t target any part icular type of institution or br and; instead it targets naive users to disclose credit card nu mbers, bank account information and various ot her personal details. Aut hors of this t ype of mail pret end to be from a l egitim ate authority and dem and the confirma tion of personal da ta. The working principle is similar to other phishing scams. Some of this mail m ight contain attachm ents but openin g the attachme nts is not harmful. The m ail contents are modified base d on the target and users. Clm.HTML.Ph ishing.Pay-110 is a Troj an horse that does not sp read automatically lik e other DDoS attack causing spam or instal l any soft ware or modify the destination systems registry. 4.5 Spam.Hoax.HOAX_PHISH_FORGED_EBAY This kind of phi shing scam ta rgets eBay users . The number of scams received by users are m ore than other scams as shown in figure 2. T he take do wn approac h of this brand does not completely eliminat e th e scam but, as seen in the table, there are fluctuations in the number of mail received by the users. T his follows t he same m e thodology use d by other brand spoofers like Paypal, Citibank etc. 4.6 Troj an.spy.h tml.bankfr aud.od This spam is a kind of Trojan vir us used for phishi ng. This Tro jan targets al l kinds of users an d brands sim ilar to spam.Phish.url where all information such as passwords, credit card details, and account details can be st olen. Various versi ons of this scam is also received by end users as shown in the figure 2. The fo llowing figure shows the traffic of all viruses, worm s and Trojans . Figure 2. Virus , worm, Trojan traf fic 4.7 Password Phishing Apart from directly targeting financial institutions and its customers, p hishers are ta rgeting ordinary e mail users f or possible fin ancial gain by st ealing em ail account.Fraudsters send emails to recipient to supply account details, if not within a week users email account will be closed. Fraudsters send this mail as its coming from the email service provi der. If the user supp lies their password and other details, ph ishers will change the password and lock the user out of their online account . They can read users email and access other personal information through the em ail account. If th ey find the right personal information, they can commit identity theft which includes u sing user’s credit card details or steal money from user’s bank accounts. I f they don ’t get any useful information, the ph ishers will send email to other email account s in the address boo k to trick them . The fraudulent email contains in form ation that the user is in trouble or si ck and needs financial assistance. The fraudsters will ask the end users con tacts to send money in order to help the en d user fr om sufferi ng as s hown in the figure.3 below. Figure 3. Sample Password phishing mail If the above method doesn’t work, phishers will u se the users email account for spamming and phishing attacks Newly created email accounts have restrictions to send emails in a day, but t his is not applicable f or age ol d email accounts. So spammers t arget third pa rty email account s to spam end users and phishing. 5 Phishing Technology and Social Engineering Phishers target end users w ith extraordinary precautions based on so cial engineering t echnique s. Instead of targeting the entire domain by using the br ute force method, phi shers send m ail to a small group of em ail accounts (end users). On the first day, our domain received only 2 u nique phi shing m ail for a partic ular brand. After that the number of em ail that target a particular brand and end users steadily increased as sh own in Figure 4. After 4 to 5 days, once again, users got a rem inder mail regarding their first phishing mail. Phishers alway s send reminder m ail to make the end users believe their contact is legitimate. If th e phishers use brute force attack on the domain, the scam will reach the entire organizatio n and the end users will be aware of the attack . To avoid this, phishers t arget sm all number o f users fi rst and increase the number of targ ets on the same domain day by day. Figure 4.Phi shing m ails for pa rticular target. Phishers follow t he end users re gularly. After the first mail, they change their subject lines and contact the end user again. The sender’s em ail account is used only once because a different email account is used to send rem inder or confirmation mail. Usually the confirmation mail address contains the word refi d (refe rence id) just to m ake the users believe it is a legitimate re minder. 5.1 Methodol ogy behind the attac k: Characterizing the sender (“fr om”) address Phisher pays a lot of attention to social eng ineering techniques to lure end users. The design of the m ail such as sender id, subject line, and contexts are carefully designed to lure victims. T hese scam messages a r e sent by spam software whi ch have t he tools nee ded to generate email accounts as instructed. It can generate fake email accounts, subjects, durat ion of the spammi ng, domai n name creation and modify t he body of the m essage sent to the users [7][19]. This spam softwa re can also generate the se nder email accounts with a specif ic form at. The sender’s account plays an important role to lure the victims to divulge the sensitiv e information. The sen der’s id designed such as real em ail accounts from the spoofed brands. T he senders email account is des i gned exactly sim ilar to the format of the l egitimate us er accounts. The length of the sender account is always more th an 21 characters and up to 28 characters. It has three parts before the “at” symbol. The format of the se nder’s mail account is as follows. (word1) ( numeric value) (wor d2)@ for ged domain.com Word1 contains sensitive words su ch as customerservice, support, op erator, service-n umber, operato r_id, Clientservice,ref, referencenum ber, customers, accsupport. Phishers are usi ng people who hold responsibl e jobs and have access to custom er’s info rmation. The length of the second num eric part, num ericvalue, ranges from 5 to 12 digits. In some cases word 1 and num ericword are connected by a “–“ or “_” sym bol as shown in the Figure 5. The length of word2, the third portion, is typically on ly 2 characters; mostly they are ch aracters such as “ib”, ”ver”, “ct” etc. as shown in the Figure. customerservice-num90359 5453175ib@53.com accsupport8013401 973226ib@53.com refnumber_id11 9700216971ver @security.53.com reference_25 676ver@securi ty.53.com referencenumber-75544317194 94ct@citi.com Referencenumber-843319866ib @citi.com service_72673ib@citi.com customers-20113070889ct@citi.co m Figure 5. Se nder email account syntax 5.2 An alyzing the “subject” of the phi shing mai l Another im portant way to m ake user open s pam is by issuing an attractive subject line, where th e subject is carefully designed to lure vi ctims. Examples of attractive subject lines include “to account confirmation”, “m essage from the bank”, “security warning” , “update details”, etc. By looking at the subject line, e nd users think incom ing mail is legitimate and requires reading. Some of the subject lines also cont ain the date an d time stam ping to make end users believe the messages are legitim ate. The format can include time of day, date month year, time (hour:m inute:seconds-t ime zone ). Often, the s ubject line contains only t hree time zones –“08 00”, “-0600”, “ -0500”, all time zones from the US or Canada. Since all brands are North American users tend to believe the North Am erican time zones. T here is no ot her time zone stampi ng in phishi ng ma ils. Fifth Thir d Bank - confirm your information! Fifth Thir d Bank - secu re confi rmation Bank of America - official inform ation! Citibank - Please Confirm Your Information e-banking acc ount confirmation attention fr om fifth bank security maintenance. reminder: plea se update your det ails Figure 6. Exa mple subjects The phishing mail subj ect line can also confirm a bank name and phrases like “custom er service” etc., with date and time to make the end-users believ e that the message is legitimate. The end users get phishin g mail every day of the week. Mostly phis hing ma il sent duri ng weekends has t he date an d time in the subject area. notification from Citibank . -Tue, 13 Jan 2009 08:15:07 -0800 Fifth Thir d Bank rem inder: confirm y our account details -Tue, 13 Jan 2009 16:24:33 -0000 Fifth Third Bank - urge nt security notification for client. -Tue, 13 Jan 2009 08:31:15 -0800 customer service: your account in Fifth Thi rd Bank. –Tue, 1 3 Jan 2009 18:13: 37 -0600 Alert! [Tue, 13 Jan 2009 11:49 :19 -0500] Figure 7. Exa mple subjects with tim e stampings 5.3 Difference between Phishing an d DDoS attacks Phishing scams are mass-mailed by a gr oup of crim inals. Although received by e-mail, they do not spread themselves like DDoS attacks. DDoS attacks also spread through emails via ph ishing but DDoS targets the entire domain and causes a service interruption. Typically, phishing targ ets only financial institutions for financial gain. Phis hing mai l does not s pread from users addres s book of the infected m achin es as DDoS attacks, which messes up registry settings and results in a system becoming inopera ble. Where an infected user machines will download malicious code from the attacker’s machine and dama ge the networ k of the vi ctim, t he phishing scam doesn’t ha rm the vict im’s networ k. 6 Countermeasures: Multi Layer approach to defend Phishing attack There a re more th an 100 anti-phish ing tools freely available to co mbat phishi ng threats but none of these t ools stop phishing effectively. Phis hers always come up with new methodl ogy to bypass anti-p hishing c ounterm easuers. Like spammi ng, phishing is heavil y dependent on social engineering techniques rather than technologica l innovations. Fro m our study, we understand that most spammers involved in phish ing activities follow the same methodlogie s of Spammers. Effective ant i-spam method s should be implem eted to counte rmeasures spam threats [4]. Since there is no bullet proof mechanism to combat spam , the combination of m ethods such as SURBL, DNSBL, rDNS etc and content filter techniqu es can help stop spam reach the end user’s inbox. Defe nding against spam will help to reduce the risk of phishing attacks. User awareness also plays an im portant role to avoid bei ng tricked by phishers. Som etimes, however, bo stering m ore about the security will cause a negative impact on the us er communit y [8]. Finall y we conclude by recom mending multi-l ayer spam . Phishing defending approach a nd user awareness are the best way to deal with Phishers so Phishers do n’t bring down user net works or ca use any interruption; it just steals users information for finanacial gain. Based on our analysis, we developed a n anti-phishing methodol ogy and im plemented in our network. We monitored t h e phishin g victim s in our network for t he last 24 months from February 20 08 to Feb ruary 201 0 i.e. before implementing and after implementing the multi layer scheme. The results show that this approach is highly effective to preve nt phishing at tacks. The propose d approach reduced more than 80% of the false negatives and more than 95% of phishing attack s in our network. 6.1 Multilayer approach to defen d Phishing attacks In this paper we propose a multi layer approach to d efend phishing attack s. This approach is a combination fine tuning of s pamming technique s, periodic ally classi fying false negative to spam , block the attackers IP addresses , using source and co ntent filters to mark phishing attempt, educate and train users, re po rt to service providers and target Institution. Th e results show that this approach is highly effective to preven t phishing attacks. The multi layer approach is shown as figure 8. We implemented this approach in our mail syste m and monitored the r esults for a year from Feb 2009 to Feb 2010. We sa w a significant improvem ent to avert phishi ng attacks in our community . Figure.8 Proposed Multi layer approach to defend phishi ng attacks The result shows that our appro ach is very effective. The approach has si x layers as shown in fi gure 8. This approach i s a combination of implem enting anti spamming techni ques, periodically classifying false negative to spam, after initial phishing att empt block IP addresses of source, ena ble source and content filters to mark phish ing attempt, educate and train users a nd report to service pr ovider and tar get Institution. In the first ste p, we have to t ighten anti spam technique s to counter all incoming p hishing attempts thro ugh spamming. Even with strict anti spam techniques, some of spam will infiltrate user inbox. To avoid this, the network administrator should classify false negative to spam regularly. This will reduce the risk of phishing attacks. After initial ph ishing attacks in the dom ain, the email accounts, dom ains, IP address range of the sender sho uld be bl ocked. In the ne xt step, this attack method and pa ttern should be added to the database through learning. The content filters ex amine the contents of the m ails and blocks the incoming unwa nted mails. Netwo rk monit oring appr oach provi des general solution to identify attacks prior an d also during the attack. Institutions shou ld educate user about possible phishin g attack scenarios and how to act after being targeted . Sample phishing m ails should be circulated to use rs to educate them. Institutions should advise users to report any po ssible phishing mails to network the ad ministrator. If phishing attacks are identified, it shou ld be reported to th e service provider and targ et institutions. We implemented this approach for the last thirteen m onths from February 20 09 to February 201 0. The number of phishing victims, false negatives has gone down drastically as shown figure 9 . . Figure 9.False negati ves We monitored the phishing attacks in our network for the last 24 months f rom February 2008 t o February 2010 i.e befo re implem enting and after impl ementing t he propose d schem e. The above graph sh ows the num ber of false negative s before and after implementing the propo sed mechanism. Before implementing this m echanism, the network received false negatives rangin g from 35 to 167, at the averag e of 111 per month. B u t after i mplem enting the propose d mechanism , the network users received false negativ es ranging from 8 to 26 at the average of 18 pe r month. Our result s show that the mechanism reduced more tha n 80% of false negative received by phishin g attacks. Figure 8. Phish ing victim s We monitore d the phis hing victim s in our network for the l ast 24 m onths from Feb ruary 200 8 to Fe bruary 2010 i.e before implem enting and a fter implem enting the sche me. Th e above grap h shows th e numbe r of vict ims before and after im plementing the propos ed mechanism . Before im plementing t his mechanism, the num ber of victims am ong the network us ers ranged fr om 0 t o 4, at the average of 1.1 5 per month. B ut after im plementi ng the proposed m echanism, the number of vi ctims had go ne down drastical ly as shown i n figure 8. It shows that t he mechanism reduced more tha n 99% of victims or incid ents in the user comm unity. The vict im doesn’t mean that he or she faced financial loss. Here the word “victim” for users that lost email accounts to th e phishers and user that saved in lost m oment of t he financi al loss. We have t o mention that the users faced financial l o ss is less than .001% in our network or org anization. But vi ctims ment ioned over here lost their personal email accoun t due to the phishing attacks. 7 Conclusion Phishing is a byproduct of s pam and ou r data show s that a large number of victims of phis hing are end users, bra nds and financial institutions. We analyzed millions of spam mail received in our server spam trap and our analysis shows two types of phishin g attack. The first m ethod used by phishers is to target end us er email requesting they divulge sens itive informtion to the ph ishers controlled machines by clicking a link. The second method is through virus, malware and Trojan entities which infect and take users to fra dulent we bsites hoping they di vulge their idendity. Us ually spam ming techniques are u sed to reach a n end user’s i nbox. Of f late spam mers are in volved in phishing att acks. Phishers use social enginee ring techniques rather than software vulnerabilites and usually target users by sending mails to small group in the particular domain and then slowly increase their rea ch. After a few days, phishers start sending “reminder” mails to their initial mail targets to make them believ e the original mail is legitimate. If they use the brute force method, phisher s believe the user will think it’s a hoax mail and pre vent the user from accepting the mail. Spamm ers usually use a brute forec m ethod only to spam end users and mimic DD oS attacks. Past studies show the number of spam m a il goes down during the weekend, but our recent study [6] reve als that this is not true. Since spammers change their t actics and bypass spam countermeasuers, they don’t minimize their activity du ring weekends. Si nce there are several specia lly designed software tools available to automatically generate spam, phishing ca n be perf ormed o n a contin ual basis. Ba sed on our analysis, we design ed an anti-ph ishing methodo logy and implemented in our network . The results show that the multi layer approach is highly effective to preven t phishing attacks. The proposed approa ch reduced more than 80% of the false negatives and more than 95% of phishing attack s in our network. References [1] Markus Jaconson, “T he human fact ors in Phishing”, Privacy & Security of Consumer Info rmation '07, 2007. [2] D.Ke vin Mc Grath, Mi naxi Gupt a, “Behin d Phishin g, An examination o f phisher M odi operandi “Proc of the 1st Usenix Workshop on Large-Scale Exploits and Em ergent Threats , Article No. 4 ,pp. 1-8 [3] yue Zhang, Serge Egelman, Lorrie Cra nor and Jason Hong,”Phindi ng phish: Eval uating Anti Phishing T ools”, CyLab Technical Report,2006. [4] Dhinaharan Nagamalai, Beatrice Cynthia Dhinakaran, Jae-Kwang Lee: Multi layer Approach to defend DDoS attacks caused by Spam ,IEEE MUE 07, pp 97-102, April 2007. [5] Dhinaharan Nagamalai, Beatrice Cynthia Dhinakaran, Jae-Kwang Lee:”An in depth a nalysis of spam and spammers” IJSA Vol 2.No 2, 2008, pp 9- 22 [6] Cynthia Dhinakaran B, Ja e-Kwang Lee an d Dhinahar an Nagamalai ,“An Empirical St udy of S pam and Spam Vulnerable email Accounts”,FGC N-2007, IEEE CS Publications, Vo lume 1, 2007. pp 408 – 413 [7] Cynthia Dhinakaran B, Ja e-Kwang Lee an d Dhinahar an Nagamalai:Characterizing Spam Traffic and Spamm ers ” ICCIT 2007, IEEE CS Publica tions, 2008, pp 831 – 836 [8] Tom Jagat ic, Nathani el Johnson, M arkus Jakobs son, and Filippo Menczer, “Social Ph ishing” Communications of the ACM,2007, pp: 94 – 100. [9] Zulfika r Ramzan, Candid Wue st, “Phishi ng attacks:Analysing trends in 2006”, CEAS 2007,2007 [10] The Spamhaus Proj ect. www.spamhaus.org [11] SpamAssassin http://spamassassin.apach e.org [12] SpamCop http://spamcop.n et [13] Cloudmark, http://www.cloudmark.com [14] Counter spy research center, http://research.sunb elt-software.com/ [15] Internet User Forecas ts by Country http:// www. etforecasts.Com [16] Nige rian fraud m ail Gallery http://www.potifos.com/fraud/ [17] Fairfax Digital http://www.smh.com.au/ [18] The Ra dicati Group Inc , www.ra dicati.com [19]Steve Sheng,Brad War dman, gary warner,Lo rrie faith Cranor,Jason Hong,Chens han Zhang, An empirical analysys of Phishing blacklist,CEA S 2009,2009,74-83. [20] Cyn thia Dhin akar an and Jae K wang lee , Dhinaha ran Nagamalai “Reminder: please update your details”: Phishing Trends, Netcom 2009,p p.295-300 [21] Cynthia Dh inakar an and Jae Kw ang lee , Dhinahar an Nagamalai, Bayesian Appr oach Based Comment Spam Defending To ol, ISA 2009, pp 578-587 ,
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment