A New Secret key Agreement Scheme in a Four-Terminal Network
A new scenario for generating a secret key and two private keys among three Terminals in the presence of an external eavesdropper is considered. Terminals 1, 2 and 3 intend to share a common secret key concealed from the external eavesdropper (Termin…
Authors: Parisa Babaheidarian, Somayeh Salimi, Mohammad Reza Aref
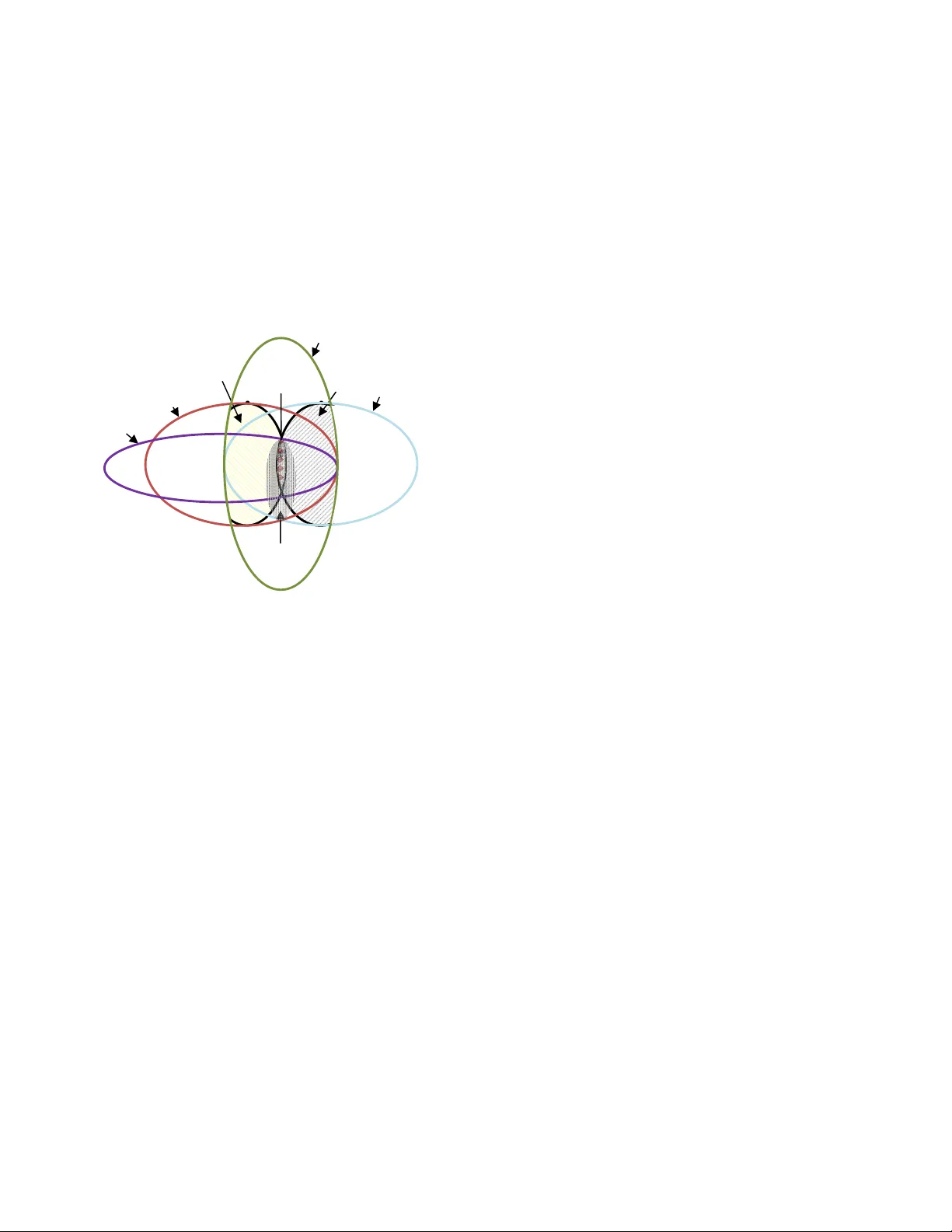
A New Secret Key Agreement Scheme in a Four- Terminal Network Parisa Babahei darian ISSL Lab., Dept. of Elec trical Engineering Sharif University of Tec hnology Tehran, Iran babaheidar ian@ee.sharif.edu Somayeh Salimi ISSL Lab., Dept. of Elec trical Engineering Sharif University of Technol ogy Tehran, Iran salimi@ee.sharif.edu Mohammad R eza Aref ISSL Lab., Dept. of Electrical Engineeri ng Sharif University of Technol ogy Tehran, Iran aref@sharif.edu Abstract: A new scenario for generatin g a secret key and two private keys a mong three Termi nals in the pres ence of an external eavesdrop per is considered. Terminals 1, 2 and 3 intend to share a commo n secret key concealed from the external eavesdropper (Termi nal 4) and simultaneously, each of Terminals 1 and 2 intends to share a private key with Term inal 3 while keepin g it concealed from each other and from Terminal 4. All four Terminal s observe i.i.d. outputs of correlated sources and there is a public channel from Terminal 3 to Terminals 1 and 2. An inner bou nd of the "secret k ey-private keys capac ity region" is derived an d the single letter capa city regions are obtained for som e special cases. Keywords-informat ion-theoretic security, source model secret key sharing , secret key-private keys capacity region. I. I NTRODUCTION 1 The broadcasting nature of wireless com munication networks leads to easy eavesdropping. Due to this fact, secret key sharing between Terminals is of great importance to provide secure communicatio n. An approach to achieve this goal is based on exploiting correlated source s as common randomness between Term inals and communicating over a public channel. Communication of confide ntial message was characterize d by Wyner [1], in which the model of wiretap channel was introduced. Subsequent ly, Csiszar and Korner in [2] conside red the problem of transmitting a confidential message with a common message in a non-degraded discrete memoryless broadcast channel. S haring a secret key between tw o Terminals in the presence of an eavesdropper was first investiga ted by Maurer in [3] and Ahlswede and Csiszar in [4] where the source and the channel common randomness were used to share a secret key between th e two Terminals. Csiszar and Narayan in [5] considered the mentioned problem in the presence of a forth node as a helper. Sharing a sec ret key between more than two Ter minals has been explored by several 1 . This work was partially supporte d by Iranian NFS under Contract No.88.114/46 and a lso by Iran telecommunica tion research center (IT RC). authors such as [6-14]. In some ot her scenarios, it is intended to share multiple se cret keys among different groups of Terminals simultaneously. In [11] Ye and Narayan examined the problem of sharing a secret-key and a private-ke y for three Terminals. They investigated the problem for generating a secret key among three Terminals and simultaneously a designated pair of Terminals generates a private key . They explored the problem at the presence of an eavesdropper who can just wiretap the communications over the public channel an d has not any other resources to eavesdr op. In [13] Salimi et.al investigated generating two private-ke ys in a source model consist ing of three users. Each of users 1 and 2 intends to share a private key with user 3 where user 1 acts as a wire tapper for user 2 and vice versa. In their scenar io, two situations wer e investigated based on directio n of public channel. In this paper, a new scenario is consider ed for sharing one secret key and two private keys, simultaneous ly. In our scheme, there are four Terminals that observe i.i.d. outputs of distinct correlated sources. Ter minals 1, 2 and 3 wish to share a secret key among them which should be effectively conce aled from the forth Terminal which acts as an external eavesdropper. Simultaneously, eac h of Terminals 1 and 2 intends to share a private key with Terminal 3 while keeping it concealed from each other and from the external eavesdropper. There is a noiseless public channel of unlimited capac ity from Terminal 3 to the other Terminals. Compared to [11], our work requires different security requirements due to the fact that the external wire tapper is equipped with source observations rather than the public channel observa tions. Also, sharing two private keys are intended in our work. Beside, compared to [12,13], our work necessitates another requirement as sharing a common secret key betwee n the three Terminals and considering an external eavesdropper. We have derived an inner bound of the secret key-private keys capacity region in the described scenario. It is not known if this bound is the capacity region in general, however, we have shown that the inner bound is the capacity region in som e special cases which means that our bound is tight. The organization of this pape r is as follows. In Section II, the model and the problem preliminaries are illustrated. In Section III, our main results and the intuition behind them are given. In Section IV, the proofs are provided. Finally, in Section V, the concluding remarks are given. Throughout the paper, the upper case letters indicate r andom variables and the lower case letters indicate their realizations. II. P ROBLEM SE TUP Consider a discrete memoryless multiple sources (DMMS) consisting of four componen ts with alphabets 123 4 (, , , ) χ χχ χ and corresponding generic random variables (r.v.s) 123 4 ,, , XX X X . Terminals 1, 2, 3 and 4, respecti vely, observe n i.i.d. repetitions of the r.v.s 1234 ,, , XX X X . Furthermore, a noiseless public channe l of unlimited capacity is available such that Terminal 3 can broadcast its required i nformation over it. The information sent over the public channel is de picted by 3 F which is a stochastic function of Terminal 3’s observation or in other words 33 () N Ff X = . The r.v.s 012 ,, KK K are all functions of 3 N X taking values from the finite sets 012 ,, ΚΚ Κ , respe cti vel y. 0 K represe nts t he common secret key among Terminals 1 and 2 and 3 and 12 , K K represent private keys for Terminals 1, 2 respectively. Terminal 3 generates a secret key and two private keys 12 (, , ) S K PK PK as a function of 3 N X or in other words * 12 3 (, , ) ( ) N S K PK PK f X = and then, Terminal 3 sends 3 F over the public channel. After rece iving 3 F , Terminals 1 and 2 compute the estimation of key pairs 01 0 2 (,) , (, ) KK KK , respectively, as deterministic functio ns of the information availa ble at each Terminal, such that: 0, 1 1 1 1 3 0,2 2 2 2 3 ˆˆ ˆ ˆ (, ) ( , ) , ( , ) ( , ) NN K Kg X F K K g X F == Here 0, 1 0, 2 ˆˆ (, ) KK take value from the finite set 0 Κ , and 12 ˆˆ (, ) K K take value from the finite sets 12 , ΚΚ , respecti vely . Now we define conditions which should be addressed in our key sharing scheme. Definition 1 : The secret key-private keys rate tripl e 012 (,, ) RR R is an achie vable rate triple , if for every 0 ε > and N sufficiently large, we have: 2 0, 0 1 11 2 2 21 3 12 3 012 4 3 0 ˆ Pr{ { } } ( 1 ) ˆˆ Pr{ } , Pr{ } (2) 11 ( ; , ) , ( ; , ) (3 ) 1 ( , , ; , ) (4) 11 log | | i i NN N kk kk k k I K XF I K XF NN IK K K X F N KH NN ε εε εε ε = ≠< ≠< ≠ < << < < ∪ 0 22 1 1 00 1 1 22 ( ) (5) 11 1 1 log | | ( ) , log | | ( ) , ( 6) 11 1 () , ( ) , () ( 7 ) K KH K K H K NN N N HK R HK R HK R NN N ε εε εε ε + <+ < + >− > − >− Equations (1) and (2 ) are the reliability conditions of the keys at Terminals 2 and 3. Equation (3) means that the private keys of Terminals 2 and 3 are effec tively hidden from each other. Equation (4) means that all the keys should be kept secret from Terminal 4. Finally the set of equations in (5-6) indicate the uniformity condi tions. Definition 2 : The reg ion co ntaini ng all the ac hieva ble secret key-private keys rate triple 012 (,, ) RR R is the secret key- private keys capacity region. III. S TATE MENT OF RESU LTS In this section we state our main results. Theorem 1: ( inner bound ) The following region of non- negative rate triples is achievable for the described sourc e model: 0 1 21 234 ( , , , ,, ,, ) I P uu u xx x x q RC o n v = ∪ 012 012 00 1 0 2 0 4 11 1 0 12 2 0 14 2 0 22 2 0 21 1 0 2 4 1 0 (,, ) : 0, 0, 0 [min{ ( ; | ), ( ; | )} ( ; | )] [( ; | , ) max { ( ; , | , ), ( ; , | , )}] [( ; | , ) max { ( ; , | , ) , ( ; , | , ) } ] RR R RR R R I UX Q I UX Q I UX Q RI U X U Q IU X U U Q IU X U U Q RI U X U Q IU X U U Q IU X U U Q + + + ⎧⎫ ⎪⎪ ≥≥ ≥ ⎪ ⎪ ≤− ⎪ ⎪ ≤− ⎨⎬ ⎪ ⎪ ⎪ ≤− ⎪ ⎪ ⎩ (8) ⎪ ⎪ ⎪ ⎪ ⎪ ⎪ ⎪ ⎪ ⎪ ⎭ where 012 ,, , QU U U are random variables taking values in sufficiently large finite sets and accor ding to the distribution: 012 1 2 3 4 01 2 0 3 1 0 3 2 0 3 1234 ( , , , , , , , ) ( | , , )( | )( | , )( | , ) (, , , ) p uu u x x x x q p q uu u p u x p u u x p u u x px x x x = The function [] x + equal s x if 0 x ≥ and 0 if 0 x < , and Conv operator is a convex closure of the set. The sketch of the proof is given in Section IV.A. However, in continue, we briefly explain our coding scena rio. Remark 1 : The above region can be achieved via separate decoding. For achievabil ity, we use a scheme which utilizes Fig1. Key agreement between Term inals 012 4 3 (, , | , ) N HK K K X F 1 N X ← 2 N X ← 02 1 2 3 ˆˆ ,, ( | , ) N KKH K X F 012 ,, K KK 3 N X → 01 2 1 3 ˆˆ ,, ( | , ) N KK H K X F 4 N X → Terminal3 Terminal4 Terminal2 Terminal1 superposition coding as well as double layer binning. A similar method, called the secret supe rposition scheme , was used in [16] to send a confidential message in the channel model. Here, we use superposition c oding to handle the secret key. In addition, double layer Binni g is used to meet the secrecy constrains in all layers which means that all the keys should be kept secret from the forth node. Our coding scheme is illustrated in Fig. 2. Remark 2 : The dual problem of the described model in channel model is a broadcast channel with three receivers, in which different levels of secrecy must be satisfied and this problem is an open problem in general. We could not prove that the rate region in (8) is the capacity region in gener al; however, we have investiga ted some special cases where the rate region in (8) is the secret key-private keys capac ity region. First, we derive an explicit outer bound for the secret key-private keys capacity region, and then we provide some special cases where the region in (8) coincides with the explici t outer bound. Proposition 1 : In the key agreement scenario of the described model, if the rate triple 012 (,, ) RR R is achievable, then it satisfy: 03 1 4 3 2 4 13 1 4 3 1 2 23 2 4 3 2 1 min{ ( ; | ), ( ; | )} min{ ( ; | ), ( ; | ) } (9) min { ( ; | ) , ( ; | ) } R I XX X I XX X R I XX X I XX X R I XX X I XX X ≤ ⎧⎫ ⎪⎪ ≤ ⎨⎬ ⎪⎪ ≤ ⎩⎭ for any joint distribution 123 4 (, , , ) PX X X X . This bound can be automatically deduc ed from Theorem 1 of [4]. Corollary 1 : When the sour ce observations form a Markov chai n as 31 4 2 XX X X −− − , the secret key-private keys capacity region reduces to: 02 1 3 1 4 0, 0, 0 ( ; | ) RR R I X X X == ≤ ≤ . Achievability follow s from Theorem 1 by setting 13 0 2 , UX U UQ == = = ∅ and not ing t hat 13 1 3 4 3 1 4 (; ) (; ) (; | ) RI X X I X X I X X X =− = . The converse can be deduced from Proposition 1. It should be noted that when the source observations form a Markov chain as 324 1 X XXX − −− , the Secret key-private keys capacity region can be derived by sym metry from Corollary 1. Corollary 2 : When the source observations form a Markov chain as 13 4 2 XX X X − −− , the secret key-private keys capacity region reduces to: 02 1 3 1 4 0, 0, 0 ( ; | ) RR R I X X X == ≤ ≤ . Achievability proof is the same as Corollary 1. The converse proof directly follows from the explicit up per bound of Proposition 1. When the source observation s form a Markov chain as 234 1 XX XX − −− , the secret key-private keys capacity region can be der ived by symmetry from Corollary 2. Corollary 3 : When the source observations form a Markov chain as 31 2 4 XX X X − −− , the secret key-private keys capacity region reduces to: 00 2 0 4 11 1 0 1 2 0 2 0 ( ;| ) ( ;| ) , 0( ; | , ) ( ; | , ) , 0 R I UX Q I UX Q RI U X U Q I U X U Q R ≤ ≤− ≤ ≤− = where Q U U , , 0 1 are auxiliary random va riables taking values in sufficiently large finite sets and according to the distribution 1 0 1 234 1 0 1 0 3 1 234 (, , , , , , ) ( | , ) (, | ) ( , , , ) p uu q x x x x p q uu p uu x p x x x x = that form Markov chains as 03 1 3 , QU XQU X −− − − . Achievability fol lows from Theorem 1 and the Markov chain 31 2 4 XX X X −− − . The converse is proved in section IV.B. When the source observations form a Markov chain as 32 1 4 XX X X − −− , the Secret key-private keys capacity region can be derived by symm etry from Corollary 3. Corollary 4 : When the source observations form a Markov chain as 213 4 XX X X − −− , the secret key-private keys capacity region reduces to: 00 2 0 4 11 1 0 1 4 02 0( ; | ) ( ; | ) , 0( ; | , ) ( ; | , ) , 0 R I UX Q I UX Q RI U X U Q I U X U Q R ≤≤ − ≤ ≤− = where 10 ,, UU Q are auxiliary random variables taking values in sufficiently large finite sets and according to the distribution 1 0 1 234 1 0 1 0 3 1 234 (, , , , , , ) ( | , ) (, | ) ( , , , ) p uu q x x x x p q uu p uu x p x x x x = that form Markov chains as 03 1 3 , QU XQU X −− − − and 14 0 0 2 (, ,) ( , , ) U X QU QU X − − . Existence of such variables can be deduced from the Markov chain 213 4 XX X X −− − . Achievabilit y directly follows from Theorem 1 by settin g 2 U = ∅ . The converse can be proved the same as Corollary 3. When the source observations form a Markov chain as 1234 XX X X −− − , the s ecret key -priv ate keys capa city region can be derived by symm etry from Corollary 4. Corollary 5 : When the source observations form a Markov chain as 23 14 XX X X −− − , the secret key-private keys capacity region is achievable if : Fig. 2. Coding scheme 0 0 0 0 (1) () (2 ) n n nR n u um u ) 2 , ( 2 ) 2 , ( 2 ) 1 , ( 2 2 nR m n u l m n u m n u ) 2 , ( 1 ) 1 , ( 1 ) 1 , ( 1 1 nR m n u l m n u m n u 00 2 0 4 11 1 0 1 2 0 22 2 0 2 1 0 0 ( ;| ) ( ;| ) , 0( ; | , ) ( ; | , ) , 0( ; | , ) ( ; | , ) R I UX Q I UX Q R IU X U Q IU X U Q R IU X U Q IU X U Q ≤≤ − ≤≤ − ≤≤ − where 210 ,, , UU UQ are auxiliary random variables taki ng values in sufficiently large finite sets and according to the distribution 210 1 2 3 4 210 210 3 1 2 3 4 ( , ,, ,, , , ) ( | , ,) ( , , | ) ( , , , ) p uu u q x x x x p q uu u p uu u x p x x x x = that form Markov chains as 03 1 3 23 2 0 3 1 ,, , ( , ) QU X QU X QU X U UX U −− − − −− − − . The proof is similar to the converse proof of corollary 3. This bound coincides w ith the inner bound if we have : 0 1 2 1 0 1 02 2 2 1 021 04 (, ) ( , ) (, , ) (, , ) ( , , , ) ( , , , ) U X Q X Q U U Q X U Q X U U UU Q X UU Q X −− − − − − − This situation is illustrated in Fig.3. When the source observations form a Markov chain as 13 2 4 XX X X −− − , the secret key-private keys capacity region can be derived by symm etry from Corollary 5. For two remaining Mark ov chains 34 1 2 XX X X −− − and 342 1 XX X X −−− all the rates will be e qual to zero. It can be shown by the e xplicit upper bound in (9). IV. P ROO FS A. proof of Theorem 1(achieavblity) Due to space limitation, w e avoid the details of the proof and the proof scheme is given in this section. For more details, it can be referred to the extended version of this paper in [17]. In order to construct the codebook, Term inal 3 generates its random codebook as follow. For an arbitrary distribution 0 () p u generates collection of codew ords each uniformly drawn from the set 03 1 () | () N UX Tp ε . Terminal 3 partitions these codewords into 000 () 2 NR R R ′′ ′ ++ bins with the same size in a uni formly manner , wher e 00 0 4 1 (| , ) 2 RR H U X Q ε ′ += + and 00 4 1 (; | ) RI U X Q ε ′′ =− . The bin index of each bin is denoted by the triple 000 (, , ) kkk ′ ′′ and the corresponding random variables are 000 ,, KKK ′ ′′ , respectively. Next, for every codeword 000 0, { , , } N kkk u ′′ ′ , Terminal 3 generates 111 () 2 N RRR ′′ ′ ++ codewords 1 111 (, , ) N u kkk ′ ′′ 111 111 { 1 , ..., 2 }, { 1 ,..., 2 }, { 1 , ..., 2 } NR NR NR kkk ′ ′′ ′′ ′ ∈∈∈ , where 1 1 12 2 0 14 2 0 1 min{ ( | , , , ), ( | , , , )} 2 R R H U X UUQH U X UUQ ε ′ + =+ and 1 1 22 0 1 42 0 1 max{ ( ; , | , ), ( ; , | , )} R I UX U UQ I UX U UQ ε ′ ′ = − , according to 10 3 |, 1 , 0 , 0 0 0 3 , 1 (| ( , , ) , ) N UU X i i i i p u u kkk x = ′′ ′ ∏ and the corresponding random varia bles of bin indices are 111 ,, KKK ′ ′′ . Similarly Terminal 3 generates 222 () 2 NR R R ′′ ′ ++ codewords 2 222 (, , ) N u kkk ′ ′′ , 222 222 { 1 , ..., 2 }, { 1 , ..., 2 }, { 1 , . .., 2 }, NR NR NR kkk ′′ ′ ′′ ′ ∈∈∈ where 2 2 2 1 10 2 410 1 min{ ( | , , , ), ( | , , , )} 2 R R HU X U U Q HU X U U Q ε ′ + =+ and 22 1 1 0 2 4 1 0 1 max{ ( ; , | , ) , ( ; , | , )} , R I U X UU Q I U X UU Q ε ′ ′ = − according to 20 3 | , 2, 0, 0 0 0 3, 1 (|( , , ) , ) N UU X i i i i p u u kkk x = ′′ ′ ∏ and the corresponding random variables of bin indices are 222 ,, KK K ′ ′′ . Now, for a fixed distribution 012 (| , , ) Pq u u u Terminal 3 generates 012 (( ; ) ) 2 NI U U U Q i.i.d. code words of length N with the distribution () pq . All Terminals are info rmed of binning scheme and distributions. For every ε -ty pical sequence 33 NN X x = , the set of codewords 0 N u which are jointly typical with 3 N x is denoted by 3 0 () N N x U and for a fixed jointly typical sequences 03 (, ) NN ux , the set of codewords 1 N u which are jointly typical with 03 (, ) NN ux is denoted by 03 1 , () N N N ux U . Similarly we can establish the set of codew ords 03 2 , () N N N ux U . For encoding, Terminal 3 observes the i.i.d. sequence of 33 NN X x = from its memoryless source and selects the corresponding sub-codebo ok. If the observed sequence was not ε -typical, it wou ld declare an error and tries for the next observation. Afterward, Terminal 3 randomly selects the sequence 0 N u from the set 3 0 () N N x U and then randomly selects sequences 12 (, ) NN uu from the set 03 03 12 ,, () , () N NN N NN ux ux UU , respectively. Then H e chooses respe ctive row indices, 012 ,, kk k of the selected codewords 01 2 (, , ) NNN uuu as a secret key, private key 1 and private key 2 respectively, and he sends the column indices 012 ,, kk k ′ ′′ of the codewords over the public channel. In addition Terminal 3 sends index i of () N Qi which is jointly typical with the selected sequenc es 01 2 (, , ) NNN uuu . For decoding, Term inals 1 and 2 should be abl e to reconstruct random variables pairs 01 (,) UU and 02 (, ) UU respectively. For the purpose of reliable decoding of sequenc e 0 n u by Terminals 1 and 2, Terminal 3 should at least send information with the rate 00 1 0 2 max { ( | , ) , ( | , ) } , R H UX Q H UX Q ′ = therefore the maxim um achievable secret ke y rate is obtained as: 0 04 0 0 1 02 04 () (; , ) m i n { (; | ) , (; | ) } (; | ) , H U I UXQ R I UX Q I UX Q I UX Q ′ − −= − Fig.3. An exa mple for case 23 14 XX X X −− − 3 () H X 2 () H U 1 () H U 1 () H X 4 () H X 2 () H X 0 () H U () H Q where the term 04 0 (; , ) I UXQ R ′ + is the lea kage infor mat ion rate . With a ccess to 0 U , our equivocation from 1 U reduces to 10 (| ) HU U . From slepian-wolf coding [15], we deduce that Terminal 3 should send information at least with the rate 11 1 0 (| ,, ) R HU X U Q ′ = , so that Terminal 1 can cor rectly reconstruct 1 U . Hence: 1 1 0 1 0 1 22 0 1 42 0 1 ( | ) [ (;| ) m a x { (; , | , ) , (; , | , ) } ] . R H U U I U Q U I UXU UQ I UXU UQ R ′ =− + + The same approach can be followed for 2 R . In continue, we will prove security conditions (3). Security condit ion (4) can be deduced using the same approaches. We have: 12 3 12 0 12 12 0 2 1 11 1 2 0 2 1 1 2 0 2 1 1 () 11 2 0 2 11 2 0 2 1 1 11 (; , ) (; , , , , ) ( ; ,,, , ) ( ) ( , | ,,,, ) ( | ,,, , , ) ( ) ( | ,,,, ) ( | ,,,, , ) () ( NN NNN N N NNNN N NNNN a N NNNN N NNNN IK X F IK X K K K I IK X U U Q K HK H U K X U U Q K H U X U U Q K K HK H U X U U Q K H U X U U Q K K HK H U ′′ ′ = ′ ≤ ′′ =− + ′′ =− + =− 202 1 202 12 0 2 1 1 1 1 1 202 1 202 1 1 12 0 2 1 1 2 0 2 12 0 2 | ,,,) ( | ,,,) (| ,, , , , ) ( ) ( ) ( | ,,,) ( | ,,, , , ) ( | , , , ) 2 ( | ,,,) (| ,, , , N NNNN NNN N NN N N N N NNNN N NNNN NN N N N NN N N N XU UQ H K XU UQ HU X U U Q K K HK HK H U X U U Q H U X U U Q K K NH U X U U Q N H U X U U Q HU X U U Q ε ′ + ′ + ′′ ≤+− + =+ − ′ + 11 () 12 0 2 1 12 0 2 2 12 0 2 1 1 12 1 2 0 2 1 1 () 12 3 ,) (| , , , ) 2 (| , , , ) (| ,, , , , ) 2( | , , , , , ) 2. b NN N N N N NNNN c KK N H UX U U Q N N H UX U U Q N HU X U U Q K K NN H U X U U Q K K NN N εε εε εε ε ≤+ − + ′ + ′ =+ + ≤+ + Inequality (a) follows from the fact that 11 2 0 2 1 ( | , ,,,, ) 0 NN N N N HK U X U U Q K ′ = because 1 K is one of the indices of 1 N U , (b) from the same approach as lemma 1 in [14] to show 12 0 2 1 2 0 2 2 (| , , , ) ( | , , , ) NN N N N NH U X U U Q H U X U U Q N ε ≤+ and (c) from the same approach as lemma 2 in [14] to show 12 0 2 1 1 3 (| , , , , , ) NN N N N HU X U U Q K K N ε ′ ≤ . By choosing 12 3 ,, ε εε such that 12 3 ε εεε ++≤ , the security condition (3) is proved. Using the same approaches, we can deduce 21 0 1 2 (; , ,, , ) N IK X K K K I ε ′′ ′ ≤ and hence, the security condition ( 3) is satisfied. Analysis of security condition in (4) is given in [17]. B. Converse proof In this subsection, the converse par t of corollary 3 is proved in which the source observations form the Markov chain 31 2 4 XX X X −− − . First, we bound the secret key rate 0 R . Fano’s inequality at Terminal 2 results in: () 02 3 0 (| , ) 1 nn en HK X F n R P n ε ≤+ = Also the security condition at the forth Term inal should be satisfied as 012 4 3 (,, ; , ) n I KK KX F n ε ≤ . We have: () 00 4 3 () 04 3 02 3 (| , ) ( | ,) ( | ,) a n b nn n nR H K X F n H KX F n H KX F n ε ε ε ≤+ ≤+ − + 02 3 04 3 () 11 11 0 2 ,3 2 4 0 4 ,3 2 4 1 111 11 02 , 32 4 4 04 , 32 4 4 1 ( ; | ) ( ; | ) ( ) ( ; | , , ) ( ; | , , ) ( ) = ( ; | , , , ) ( ; | , , , nn n n c ii ii ii n i n iii iii ii i IK X F IK X F n I K XF XX I K XF XX n IK X F X X X IK X F X X X εε ε ε +− +− = +−+ +− = =− + + =− + + − ∑ ∑ 1 11 1 11 1 04 32 4 4 , 04 32 4 2 , 1 () 111 111 02 , 32 4 4 04 , 32 4 4 1 02 , 4 , ) ( ; | , , , ) ( ; | , , , ) () (; | , , , )(; | , , , ) () ( ; | , n ii i ii i ii i n n d iii iii ii i n ii IK X F X X X IK X FX X X n IK X F X X X IK X F X X X n IK X X F εε εε + ++ − ++ − = +−+ +−+ = +− ++ ≤− ++ ≤ ∑ ∑ 111 32 4 4 1 11 1 1 0 1 2, 4, 3 2 4 4 1 () 0, 2, 4, 1 () 0, 2, 0, 4, 1 ,,,) ( ) ( , ; | , , , , ) ( ) ( ; | , ) ( ) ( ; | ) ( ; | ) ( n iii n i n ii i i ii n i n e ii ii n i n f ii i ii i n i XXX n IK X X X F X X X n IU X Q X n IU X Q IU X Q n εε εε εε εε +−+ = −+ − + = = = ++ ≤+ + =+ + =− + + ∑ ∑ ∑ ∑ () 0, 2, 0, 4, ) ( ( ; | ) ( ; | ) ), g VV V VV V n I UX Q I UX Q ε ′ =− + where in the above equations, (a) results from the security condition, (b) from Fano’s inequality, (c) from Lem ma 1 of [2], (d) from the fact that 11 1 04 1 3 4 4 , (; | , , , ) 0 ii i i IK X FX X X ++ − = which can be deduced from the Markov chain 31 2 4 XX X X −− − , and memoryless property, it is shown in lemma 1 in [17], (e) from the defin ition of the random variables 0, , ii QU as: 111 1 32 4 4 0 , 0 1 ( , , , ), ( , , ) iii i ii i QF X X X U K X Q ++− − == (f) from the fact that 0, 4, 2, (; | , ) 0 ii ii IU X Q X = which can be deduced fr om the Markov chain 31 2 4 XX X X −− − and (g ) from considering V as a time sharing random variable independent of all the other random variables which uniformly takes value from the set {1 , 2 , . . . , } n and by setting n ε εε ′ + . Now, we will b ound 1 R . According to F ano’s inequality for Terminal 1’s private key, we have: 11 3 (| , ) n n HK X F n ε ≤ Also, the security condition for the mentioned private key establishes as: 12 3 (; , ) n I KX F n ε ≤ and consequently: 12 3 0 1 2 3 1 0 2 3 02 3 (; , , ) (; , ) (; | , ) (| , ) ( ) nn n n n I K X F K IK X F IK K X F nH K X F n εε ε =+ ≤+ ≤ + By setting n ε εε ′ + we can conclude 12 30 (; , , ) n I KX F K n ε ′ ≤ . We have: () 11 2 3 0 () 12 30 1 13 12 30 1 13 0 11 30 1 2 30 () 11 11 , 3 01 2 1 1 (, , ) ( , , ) ( , ) ( , ,) ( , ,) = ( ; | , ) ( ; | , ) (2 ) (; | , , , ) (; a n b nn nn nn n n c ii i i nR H K X F K n HK X F K HK X F n n HK X F K HK X F K n n IK X F K IK X F K n IK X FK X X IK ε εε εε εε −+ = ′ ≤+ ′ ≤− + + ′ ≤−+ + −+ + =− ∑ 11 2, 3 0 1 2 1111 1111 11 , 3 0 1 2 4 4 1 2 , 3 0 1 2 4 4 1 11 11 11 14 4 30 1 2 2 , 14 4 3 01 1 |, , , ) ( 2 ) ( ; | , ,, ,,) ( ;| , ,, ,,) (; , | , , , , ) (; , | , , ii in n iiii iiii ii i n ii ii ii i i i XF K XX n I K X F K XXXX I K XF K XXXX IK X X FK X X X IK X X F K X εε −+ −+−+ −+−+ = −+ −+ −+ = ++ =− +− ∑ ∑ 11 21 , () 1111 1111 11 , 3 0 1 2 4 4 1 2 , 3 0 1 2 4 4 1 () 1, 1, 0 , 1, 2 , 0 , 1 () 1, ,, ) (2 ) ( ; | , ,, ,,) ( ; | , ,,,, ) (2 ) (; | , ) (; | , )( 2 ) (( ; i i n n d iiii iiii ii i n n e i i ii i i ii n i f V XX n I K X F K XXXX I K XF K XXXX n IU X U Q IU X U Q n nIU X εε εε εε −+ −+−+ −+ −+ = = ++ ≤− ++ =− + + ≤ ∑ ∑ 1, 0 , 1, 2 , 0 , |, ) ( ; |, ) ) VV V V VV V UQ I UX UQ ε ′′ −+ where in the above e quations, (a) results from the security condition, (b) from Fano's inequality, (c) from lemma 1 in [2], (d) from the fact that 11 11 14 4 3 0 1 2 2 , (; , |, , , , ) 0 ii ii i I K XX F K XX X −+ −+ = which can be deduced from the Markov chain 31 2 4 XX X X −− − , and memoryless property, it is shown in [17], (e) from the definition of the random var iables 1 1, 1 1 (, , ) i ii UK X Q − = and 0, , ii QU as before, and (f) from considering V as a time sharing random variable independen t of all the other random variables which uniformly takes value from the set {1 , 2 , . . . , } n and by setting 2 n ε εε ′′ + . For rate 2 R , it is clear from the Markov chain that every message Terminal 2 deco des can also be decode by Ter minal 1. Therefore in this case the private key 2 rate is e qual to zero. But still we can prove this claim by noting that in the explicit outer bound we have 32 1 (; | ) 0 IX X X = due to the Markov chain 31 2 4 XX X X −− − . V. C ONCLUSI ON In this paper, we have studie d the problem of simultaneou s sharing a secret key and two private ke ys among three Terminals with an additional wire tapper. We have obtained an inner bound to the secret key-private keys capacity region. Also for some special cases, w e have shown that the inner bound is the secret key-private keys c apacity region demonstrating that the inner bound is tight. The investigated special cases include all the different Markov chains that the sources from. As a generalization of this work, for the case in which Terminal 3 is not a trusted party, one can study the case of having three private keys in this m odel. For now, we are working on a case in which the direction of the public chan nel is reversed; meaning the case in which only Terminals 1 and 2 are allowed to talk over the public channel. R EFERENCES [1] A. D. Wyner , “The w ire-t ap cha nnel,” Bell Sys. Tec h. J. , vol. 54, 1975, pp.1355-1387. [2] I. Csi szar an d J. Ko rner, “Broadcast channels with c onfidential messages ,” Information Theory , IEEE Transac tions on, vol. 24, 1978, pp. 339-348. [3] U. M. Maurer, “Secret key agreement by public discussi on from common informa tion,” IEEE Trans. Inform. Theory , vol. 39, 1993, pp. 733-742. [4] R. Ahlswede and I. Csiszár, “Comm on randomness in information theory and crypto graph y. i. secr et shar ing,” Information Theory, IEEE Transactions on , vol. 39, 2002, pp. 1121–1132. [5] I. Csiszár and P. Narayan, “Comm on randomness and sec ret key generation wit h a helper,” Information Theory , IEEE Transactions on , vol. 46, 2002, pp. 344–366. [6] C. Ye and A. Reznik, “Group secret key genera tion algorithms,” Information Theory, 2007. ISIT 2007. IEEE International Symposium on , 2008, pp. 2596–2600. [7] A.A. Gohari and V. Anantharam, “Informa tion-Theoretic Key Agreement of Multi ple Terminals—Part I,” Information Theory , IEEE Transactions on , vol. 56, 2010, pp. 3973–3996. [8] A.A. Gohari and V. Anantharam, “Information-the oretic key agreem ent of multiple Termina ls—Part II: Channel model,” Information Theory, IEEE Transactions on , vol. 56, 2010, pp. 3997–4010. [9] A.A. Gohari and V. Anantharam , “New bounds on the information- theoretic key agreement of m ultiple Terminals,” Information Theory, 2008. ISIT 2008. IE EE International Symposium on , 2008, pp. 742–746. [10] I. Csiszár and P. Narayan, “Sec recy capacities for multiple Terminals,” Information Theory, IEEE Transactions on , vol. 50, 2004, p p. 3047– 3061. [11] C. Ye and P. Narayan, “The secret key~priva te key capacity region for three Ter minals ,” Information Theory, 2005. ISIT 200 5. Proceedings. International Symposium on , 2005, pp. 2142–2146. [12] S. Salimi , M. Sal masizadeh , and M.R . Aref, “ Secret ke y sharin g in a new source m odel: Rate regions,” Communications T heory Workshop (AusCTW), 2010 Australi an , 2010, pp. 117–122. [13] S. S alim i, M. S alma si zad eh, M. R. Ar ef, “Rat e R egio ns of Secr et K ey Sharing in a New Source Model,” ac cepted for publicati on at IET Communication J ournal [14] I. Csis zár and P. N arayan, “ Secrecy capaciti es for multiTer minal cha nnel m odel s,” Information Theory , IEEE Transactions on , vol. 54, 2008, pp. 2437–2452. [15] D. Slepian and J. Wolf, “Noise less coding of correlated informa tion sources,” IEEE Transactions on Info rmation Theory , vol. 19, 1973, pp. 471–480. [16] G. Bagheri karam and A. S. Motah ari and A. K. Khan dani, “ The secrecy rate region of the broa dcast channel,” in Proceedings of the Alle rton Conference on C ommunications, Control and Computing , , July 2008. [17] Extended version of this pape r. Preprint available at ee.sharif .edu\~bab aheidari an.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment