The Danger Theory and Its Application to Artificial Immune Systems
Over the last decade, a new idea challenging the classical self-non-self viewpoint has become popular amongst immunologists. It is called the Danger Theory. In this conceptual paper, we look at this theory from the perspective of Artificial Immune Sy…
Authors: Uwe Aickelin, Steve Cayzer
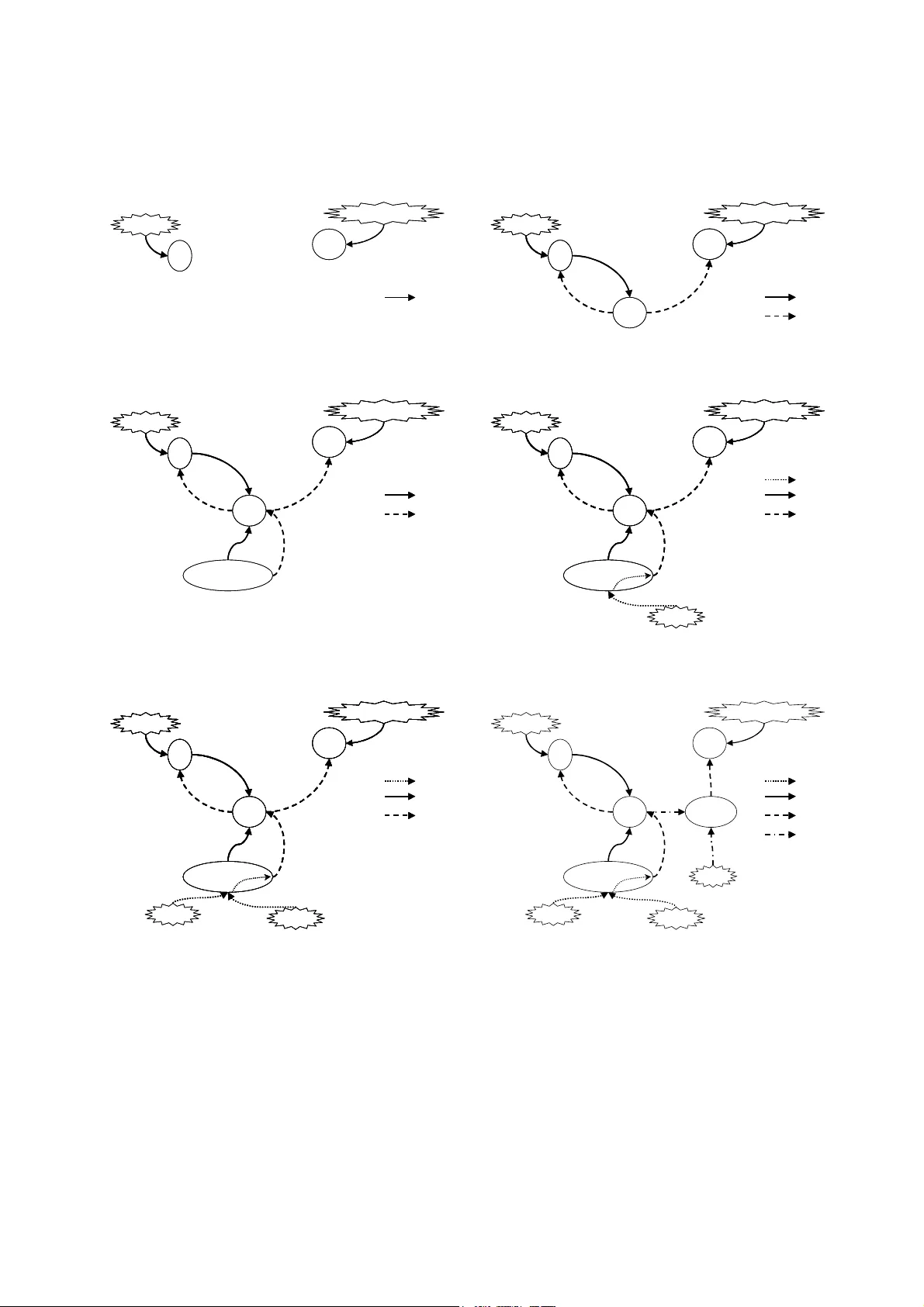
The Danger Theory and It s Applic ation to Artificia l Immune Systems Proceedings of the 1st Internat Conference o n ARtificial I mm une Syst ems (ICARIS -2002), pp 141-148, Canterbury, UK , 2002. Uwe Aickeli n School o f Computer Science University of Notti ngham NG8 1BB UK uxa@cs.nott.ac.u k Steve Ca yzer Hewlett-Packard Laborato ries Filton Road Bristol BS12 6QZ Steve_Cayzer @hp.com Abstract Over the last decade, a ne w i dea challengin g the classical self-non-self viewp oint h as become popular amongst immunologists. It is called the Danger Theo ry. In this conceptual paper, we look at this theory from the perspective of Artificial Immune Sys tem practitio ners. An overview of the D anger T heory is p resented with particular emphasis on a nalogies in the Artificial Immune Syste ms world. A n umber of po tential application areas are then used to pro vide a framing for a critical a ssessment of the concept, and its relevance for Artificial Immune Systems. 1 INTRODUCTION Over the last decad e, a new theor y has become popular amongst immunol ogists. It is called the D anger T heory, and its chie f advocate is Matzinger [1 8], [19] and [2 0]. A number of advantage s are claimed for this theor y; not least t hat i t provides a m ethod o f ‘gro unding’ the immune response. T he theory is n ot complete, and there are some doubts about how much it act ually c hanges behaviour and / or structure. Nevertheless, t he theory contains enough potentiall y i nteresting ideas to make it worth assessi ng its relevance to Artificial Immun e Systems. It should be noted that we d o not intend to defend t his theory, which is still controversial [21]. Rather we are interested i n its merits for A rtificial Immune Syste m applications and hence its act ual existe nce in the hu moral immune syste m is o f little importance to us. Our question is: Can it help us build better Artificial Immune Systems? Few other Artificial Immune S ystem practitioners are aware of the Danger Theor y, notable exceptions being Burgess [5] and Willa ms on [2 2]. Hence, thi s is the first paper t hat d eals directly with the Danger Theory, and it is the authors’ intentio n t hat t his p aper stimulates disc ussion in our research co mmunity. In the next section, we pro vide an o verview o f the Danger Theor y, po inting out, where ap propriate, so me analogies in curre nt Artificial Immune S yst em models. We then assess the rel evance of the t heory for Art ificial Immune System security app lications, which is probabl y the m ost obvious application area for the danger model. Other Artificial I mmune S ystem appli cation areas are also considered. Finally, we draw some p reliminary conclusions ab out the potential o f the Danger concept. 2 THE DANGER THEORY The immune system is co mmonly thought to work at three levels: External barr iers (skin, mucus) , innate immunity and the acq uired or adaptive im mune syste m. As part of the third a nd most co m ple x level, B- Lymphocytes secrete specific antibodies that recognise and react to stimuli. It is this p attern matching bet ween antibodies a nd antigens that lies at the heart of most Artificial Immune System im plementations. Another type of cell, t he T (killer) lym ph ocyte, is a lso important in different types of immune reactio ns. Although not usually present in Artificial Immune System models, the behaviour of this cell is i mplicated in the Danger model and so it is i ncluded here. Fro m the Artificial I mm une System practitioner’s point of view, the T killer cel ls match stimuli i n much the same way as antibod ies do. However, it i s not simply a question o f matc hing i n the humoral imm une system. It is funda mental that onl y the ‘corr ect’ cells are m atched as otherwise t his could lead to a s elf-destructive autoi mmune r eaction. Classical immunology [12] stipulates that a n immune response is triggered whe n the bod y encounters something no n-self or foreign. It i s not yet fully un derstood how this self-no n- self discri mination is a chieved, but many i mmunologists believe that the difference betwee n them i s learnt early in life. In particular it is thou ght that t he maturation pro cess plays an i mportant role to achieve self -tolerance b y eliminating those T and B cells that react to self. In addition, a ‘ confirmation’ si gnal is required; that is, for either B cell or T (killer) cell activa tion, a T (helper) lymphocyte must also be activ ated. This dual activation is further pr otection a gainst t he c hance of accidentally reacting to sel f. Matzinger’s Da ng er Theory debates this po int o f view (for a good introductio n, see Matzinger [18 ]). Technical overviews can be f ound in Mat zinger [ 19] and Matzinger [20]. Sh e points out that there must be discrimination happening that goes b eyond t he self-non-self di stinction described above. For instance: • There i s no immune reactio n to foreign bacteri a in the gut or to the fo od we eat alt hough b oth are fo reign entities. • Conversely, some au to- reactive processes are useful, for example against s elf molecules expressed b y stressed cells. • The definition of self is proble matic – real istically, self is co nfined to the subset actually seen by th e lymphocytes duri ng maturation. • The human body changes o ver its lifetime and thus self changes as well. T herefore, the question ari ses whether d efences again st non-sel f learned ear ly in life might be auto reactive later . • Other aspects that see m t o be at odds with the traditional viewpoint are autoimmune d iseases and certain types of tumours t hat are fou ght by the immune system (both attacks against self) a nd successful transpla nts (no attack agains t non-self). Matzinger concludes t hat the immune s ystem actually discriminates “some se lf from some no n-self”. S he asserts that the Danger T heory intr oduces not j ust new labels, but a way of escapi ng the semantic diffic ulties with sel f and non-self, and thus pro vides groundin g for the i mmune response. If w e ac cept the Danger T heory as valid we can take care of ‘no n-s el f b ut harmless’ and of ‘self but harmful’ invaders into our system. To see how th is is possible, w e will ha ve to examine the t heory in m ore detail. The central idea in the Danger Theory is that the i mm une system do es not re spond to no n-self but to danger. T hus, just like the self-non-self theori es, it fundamentally supports t he need for discrimination. However, it differs in t he answer to what s hould be respo nded to. Instead of responding t o foreignness, t he i mmune syst em react s to danger. This theory i s borne out o f t he ob servation t hat there is no need to attac k ever ything tha t is foreign, something that seems to be suppor ted by t he counter example s abo ve. I n this t heory, d anger is measured b y da mage to cells indicated b y distres s signals that ar e sent out when cells die an unnatural death ( cell stress or lytic cell de ath, a s oppo sed to programmed cell d eath, or ap optosis ). Figure 1 depicts how we might picture an i mmune response accord ing to the Dan ger T heory. A cel l that is in distress sends out an alarm si gn al, whe reupon antigens in the neighbourhoo d are captured by antig en-presenting cells such as macrop hages, which the n travel to the l ocal lymph nod e and present the a ntigens to ly mphocytes. Essentially, the dan ger si gnal establishes a dan ger zo ne around it self. Thus B cells pro ducing antibod ies t hat match an tigens within the dan ger zone get st imulated a nd undergo the clo nal expan sion proce ss. T hose that d o not match or are too f ar away do not ge t sti mulated. Antigens Antibodies Match, but too far awa y Stim ulation Danger Zone Danger Signal Damaged Cell Cells No match Figure 1: Danger Theory Model. Matzinger admits t hat the exact nature o f t he dan ger signal is unclear . It may be a ‘positive’ signal ( for example hea t shock protein release) or a ‘negative’ s ignal (for example lac k of synap tic contact w ith a dendritic antigen-prese nting cell). This is where the Danger T heory shares some of the p roble ms associa ted with traditional self-non-self discrimination (i.e. how t o d iscriminate danger from non -danger). However, in this case, the signal is grou nded rather than being some a bstract representation o f danger. Another way of lo oking at the d anger model is to see it as an exten sion of the T wo-Signal model b y Bretsc her and Cohn [4 ]. In this model, the two signals are a ntigen recognition (signal one) a nd co-stimulation (signal two). Co-stimulation is a signal tha t means “this anti gen real ly is foreign” o r, i n t he D anger T heory, “t his a ntigen reall y is dangerous”. How t he signa l ar ises will b e explained later. The Danger T heory t hen op erates b y app lying three laws to lymphocyte beha viour ( the laws of lymphoti cs [20]) : • Law 1 . Beco me activat ed if you rece ive signals one and two together. Die if you receive signal o ne i n t he absence of signal t wo. Igno re signal t wo without signal one. • Law 2. Accept signal t wo from antigen-presenting cells o nly (or, for B cells, f rom T helper cells). B cells can act as anti gen-presenting cells only for experienced ( memory) T cells. Not e t hat s ignal one can come fro m a ny cel ls, no t just antigen -presenting cells. • Law 3. After activation (activated cells d o not need signal two) revert to resting stat e after a short time. For the m ature lymp hocyte, (whether virgin or experienced) these rule s are adhered to. However, there are t w o e xceptions i n the lymp hocyte lifec ycle. Firstly, immature cells are unable to accep t signal two fro m a ny source. This enables an initial negative selection screening to oc cur. Secondly, ac tivated (effector) cells respond only to signal one (ignoring signal two), but revert to the rest ing state shortly after wards. An i mplication of this theory is that autoreacti ve effects are not neces sarily harmful, a nd are in fact expected during an infecti on. T his is bec ause an y l ymphocyte reacting to an antigen in t he ‘danger zo ne’ will be activated. These anti gens are not necessaril y the culprits for the danger signal. If they are, then the reacting lymphocytes will continue to be restimu la ted until the antigens (and therefor e the danger signal) are re moved. After this, they will re st, receivi ng neither signal one nor signal two. On the other ha nd, lymphocytes r eacting to innocuou s (self) antigens will continue to recei ve signal one from these antigens, e ven after the d anger (and ther efore signal two) has vanis hed. Ther efore these lymphocytes will be deleted, and to lerance will b e achie ved. H owever, further autoreactive effects ca n be exp ected, partly becau se ‘self’ changes o ver time, and partl y beca use of new lymphoc yte generation (p articularly B cells, which produce hypermutated clones during activatio n). A p roblem is p osed b y the a ntigen-presenti ng cell it self, whose (innocuous ) antigens ar e by definition alwa ys i n the danger zone. L ymphocytes r eacting to these antigens might destro y the a ntigen-presenting cell and t hus interfere with the i mmune response. The negative selection of i mm at ure lymphocytes pro tects against this possibility. Figure 2 shows a more detailed picture of how the Dan ger Theor y can be viewed as an extension of i mmune signals. These diagra m s are adapted fro m tho se presented in Matzinger [19] excep t for the sixth, which incorpo rates suggestions made in Matzinger [20]. In the original vie w of the world by Bur net [6], o nly signal one is considered . This is shown in the first diagram, where the onl y signal shown is that between infectious agents and lymp hocytes (B cells, marked B, and T ki ller, marked Tk). Signal t wo (second diagram) was introduced by Bretscher and Cohn [4]. This helper signal c omes from a T helper cell ( marked T h), o n recei pt of signal one fro m t he B cell. That is, the B cell pres ents antigens to t he T helper cell and a waits the T cell’s confirmation signal. If t he T cell r ecognises t he antigen (which, if negative selection has worked, should mean the antigen is no n-self) t hen the im mune response can commence. I t was Laffe rty and C uningha m [17] w ho proposed that the T helper c ells themsel ves al so need to be ‘sw i tched o n’ by signals one and two, both from antigen-prese nting c ells. This process is depicted i n t he third diagra m. Note that the T hel per cell gets signal one from t w o sources – the B ce ll and the antigen-prese nting cell. In the former case the antige ns ar e not chosen rando mly – the very oppo site, since B cells are hig hly selective f or a range o f ( hopefully non-self) antigens. I n the latter case, the a ntigens ar e chose n rando mly (the a ntigen-presentin g cell simply presents an y anti gen it picks up) but signal two s hould o nly be provided to the T help er c ell for non- self anti gens. I t is not necessar ily clear ho w the ant igen- presenting ce ll ‘k nows’ the a ntigen is non-sel f. J aneway [14] introduced the idea of infectious non-self (for example bacteria), which ‘ primes’ antigen present ing cells, i.e. ca using signal two to be prod uced ( fourth diagram). This pri ming signal is labelled as signal 0 in the figures. Matzinger pro poses to allow priming of ant igen- presenting cells b y a danger signal (fifth diagram). She also proposes to ext end the efficac y of T helper cells b y routing si gnal two t hrough antigen presenting cells [ 20]. We have marked this as ‘signal 3’ in t he sixth di agram (although M atzinger doe s not use that term, the intention is clear) . In Matzinger’ s w or ds “the antige n seen by t he killer need not be th e same as the h elper ; the only require m ent i s that they must bo th be presented b y t he same antigen -presenting cell”. T his arrangeme nt allows T helper cells to p rime many more T killer cells than the y would otherwise have been abl e to. Tk B Bacterium Virus Infected Cell Tk B Bacterium Virus Infected Cell 1. Antigen in Control (Burnet) Signal 1 Signal 1 2. Helper in Control (Bretscher & Cohn) (non-random) Th Tk B Bacterium Virus Infected Cell (non-random) Th Tk B Bacterium Virus Infected Cell Tk B Bacterium Virus Infected Cell Signal 1 Signal 2 Signal 1 Signal 1 Signal 2 Signal 2 3. APC in control (La fferty & Cunningham) APC (random) (non-random) Th Tk B Bacterium Virus Infected Cell APC (random) (non-random) Th Tk B Bacterium Virus Infected Cell (non-random) Th Tk B Bacterium Virus Infected Cell Tk B Bacterium Virus Infected Cell Signal 1 Signal 2 Signal 1 Signal 1 Signal 2 Signal 2 4. Infectious non self in con trol (Janeway) Bacteria APC (random) (non-random) Th Tk B Bacterium Virus Infected Cell Bacteria APC (random) (non-random) Th Tk B Bacterium Virus Infected Cell APC (random) (non-random) Th Tk B Bacterium Virus Infected Cell (non-random) Th Tk B Bacterium Virus Infected Cell Tk B Bacterium Virus Infected Cell Signal 1 Signal 0 Signal 2 Signal 1 Signal 1 Signal 0 Signal 0 Signal 2 Signal 2 5. Danger in Contr ol (Matzinger) Distress Bacteria APC (random) (non-random) Th Tk B Bacterium Virus Infected Cell Distress Bacteria APC (random) (non-random) Th Tk B Bacterium Virus Infected Cell Bacteria APC (random) (non-random) Th Tk B Bacterium Virus Infected Cell APC (random) (non-random) Th Tk B Bacterium Virus Infected Cell (non-random) Th Tk B Bacterium Virus Infected Cell Tk B Bacterium Virus Infected Cell Signal 1 Signal 0 Signal 2 Signal 1 Signal 1 Signal 0 Signal 0 Signal 2 Signal 2 Virus? APC 6. Multiplication o f effect (Matzinger) Distress Bacteria APC (random) (non-random) Th Tk B Bacterium Virus Infected Cell Signal 1 Signal 0 Signal 2 Signal 3 Signal 1 Signal 1 Signal 0 Signal 0 Signal 2 Signal 2 Signal 3 Signal 3 Figure 2: Dan ger Theory vie wed as i mm une sig nals. The Da nger Theory is not without i ts limitatio ns. As mentioned, the e xact nature of the danger signal is still unclear. Also, there is someti mes d anger that sho uld not be responded to (cuts, t ransplants). In fact, in the cas e of transplants i t is of ten necessar y to rem ove th e antigen - presenting c ells from t he tran splanted o rgan. Finall y, the fact that autoimmu ne diseases do still, if ra rely, happen, has yet to be fully reconciled with the Danger Theor y . 3 THE DANGER THEORY AND SOME ANALOGIES TO ARTIFICIAL IMMUNE SYSTEMS Danger theor y clearly has many facet s and intricacies, and we ha ve touched on o nly a fe w. It might be i nstructive to list a number of co nsideratio ns for an Arti ficial I mmune System practitio ner regardin g the suitabilit y o f the danger model for their application. The basic c onsideration is whether negative selection is important. If so , then these points may be re levant: • Negative selection is bound to be imperfect, and therefore a utoreactions (f alse positives) are inevitable. • The self/non-self bo undary i s blurred since self and non-self anti gens often share co mmon regions. • Self changes over time. Therefore, one can expe ct problems with memor y c ells, which la ter turn o ut to be inaccurate o r even autoreactive. If these point s are sufficie nt to make a practitioner consider incorpo rating the Da ng er theory into t heir model, then the follo wing consideratio ns may be instructive: 1. A dan ger model requires an antigen -presenting cell, which can pre sent an approp riate danger signal. 2. ‘Danger’ is an e motive ter m. T he signal may have nothing to do with danger (see, for example, our discussion on data mining applicatio ns in section 5). 3. The approp riate danger si gnal can be positive (presence o f signal) or negativ e (absence). 4. The danger zone in biology is s patial. In Artificial Immune S ystem application s, some other measure of proximity (for instance tempor al) may be used. 5. If there i s an analogue of an immune response, it should not lead to further d anger signa ls. In bio logy, killer cells cause a normal cell death, not danger. 6. Matzinger propo ses pri m ing killer cells via a ntigen- presenting c ells for greater effect. D epending on the immune system used (it only makes sense for spatially d istributed models) this proposal may be relevant. 7. There are a variety of considerati ons that are less directly related to the danger model. For exam ple, migration – how many a ntibodies receive signal one/two f ro m a given antig en-presenting cel l? In addition, the da nger theor y r elies o n conce ntrations, i.e. continuous not binary matc hing. There are also a co uple of p oints that might tempt a practitioner to alter the da nger m ode l as p resented here. For example, th e danger m o del has quite a number of elements. Given that the a ntigen-presenti ng cell mediates the danger si gnal, we mig ht b e ab le t o simplify the model – for example, do we still need a T helper cell? In addition, there are some danger signals that might in some sense be ‘appropriate’ and thus should not trigger an immune respo nse. In such c ases, a method for avo iding the danger pathway must be found. A biological example is transpla nted organs, in which antigen -presenting cells are removed. 4 THE DANGER THEORY AND ANOMALY DETECTION An intriguing ar ea for the app lication of Arti ficial Immune Systems i s the d etection of ano malies suc h as computer viruses, fraudulen t transactions or hardware faults. T he u nderlying metaphor seems to fit part icularly nicely her e, as there is a system ( self) that has to be protected against intruders (non-self). T hus if natural immune s ystems h ave enabled biological sp ecies to survive, ca n we no t create Artificia l Immune S ystems to do the same t o o ur co mputers, machines e tc? Presu m ably those syste ms wo uld then have the same b eneficial prope rties as natural immune syste ms like error tolerance, distribution, adaptatio n and self-mo nitoring. A re cent overview o f bi ologicall y insp ired ap proaches to this area can be found in W illiamson [22 ]. In this sectio n we will p resent indicat ive examples of such artificial systems, expla in t heir current shortco mings and show how the Danger Theory might help overco me so me of these. One o f the first such app roaches is pre sented by Forre st et al [11 ] and exte nded b y Hofme yr and Forrest [13]. T his work is co ncerned with bui lding an A rtificial Immune System that i s able to d etect non-self in the area of network securit y where n on-self is def ined as an undesired co nnection. A ll co nnections a re modelled as binary strin gs a nd there i s a set of kno wn good and b ad connections, which is used to train a nd evaluate the algorithm. T o build the Artificial I mmune System, rando m binar y strings are crea ted called d etectors. These detectors then undergo a maturation phase where they are prese nted with good, i.e. self, connectio ns. If they match any of these they are eliminated otherwise they become mature, but not a ctivated. If during t heir further lifetime t hese mature detec tors match anythi ng else, exceeding a certa in thresh old value, t hey b ecome activated. This is then rep orted to a human operator who decides whether there is a true anomaly. If so the detectors are promoted to memory detector s wit h an indefinite life spa n and mi ni mum acti vation threshold. Thus, this is similar to the secondar y respo nse in the natural immune s ystem, for instance a fter immunisation. An approach such as the above is known in Artificial Immune Systems a s negati ve selectio n as only th o se detectors (antibodie s) that do not match live o n. It is thought that T cells mature in similar fa shion in the thymus such that onl y those survive and mature t hat do not match any se lf cells after a cer tain amount of ti me. An alternati ve approac h to negative selec tion is t hat of positive selectio n a s used fo r instance by Forrest et al [9] and b y Soma yaji and Forrest [22]. T hese systems are a reversal of the n egati ve selection algorit hm described above with the difference t hat detectors for self are evolved. From a performance point of view there are advantages a nd disadvantages for both methods. A suspect non-self string would have to be c ompared with all self-detectors to establis h that it is non-sel f, whilst with negative selection the first matching detecto r would stop the comparison. O n the ot her hand, for a self-string this is reversed givin g po sitive se lection t he upper hand. Thus, performance de pends on the s elf t o non -self ratio, which should generally favour positive selection. However, there is a nother difference between the two appro aches: the nature o f false a larms. Wit h negative selection inadequate detectors will result in false negatives ( m issed intrusi ons) whilst with positive selection t here will be false p ositives ( false alar ms). T he preference betw een the two in this case i s likel y to be problem specific. Both ap proaches have been extended further [10] including b etter co-stimulation methods and activation thresholds to reduce the n umber o f false alar ms, multiple antibody sub-populations f o r i mproved diversity and coverage and i mproved parti al matching rule s. R ecently, similar appr oaches have also been used to det ect hardware faults (B radle y and Tyrrell [ 1]), network intrusion (Ki m and Bentley [16 ]) and fault tolerance (Burgess [5] ). What are t he remai ning c hallenges for a succe ssful use o f Artificial I mmune Systems for anomaly detection? Firstly, self a nd non-self will usually e volve a nd change during the li fetime o f t he s ystem. Hence, to b e effective, any syste m used must be rob ust and fle xible eno ugh to cope with c hanging circumstances. Based o n t he performance of their natural counterp arts, Artificial Immune Systems should be well suited to provi de these qualities. Secondly, appropriate repre sentations of self and good matching rules have to be de veloped. M ost research so far has bee n co ncentrated in t hese two areas and good ad vances have been made so far [8]. However, as po inted out b y Ki m and Bentley [15] , scaling is a pro blem with negative select ion. As the syst ems to be protected grow larger and larger so does sel f a nd non -self and it beco mes more and more pro blematic to find a se t of detectors th at pr ovides adequate coverage whilst bei ng computationall y ef ficient. It is inef ficient, i f not impossible, to map the e ntire non-self u niverse, particularl y as i t will be changi ng o ver ti me. T he same applies to positive selection an d trying to map all of sel f. Moreover, the app roaches so far have another disadvantage: A respo nse requires infectio n beyond a certain t hreshold and hu man inter vention co nfirming this. Although one might ar gue that the op erator s ees fe wer alarms tha n in an u naided syste m, this c learly is not yet the ideal situation o f an auto nomous syste m preventing al l damage. Apart from t he re source i mplication of a human component, a n unduly lon g delay might be caused b y t his necessity pro longing t he time the s ystem is exp osed. This situation might be further aggr avated b y t he fact that t he labels self and non-self are o ften ambig uous and expert knowledge might be required t o apply them correctl y. How can these pr oblems b e overco me? We believe that applying ideas f rom the Dang er T heory can help buildi ng better Arti ficial Immune Syst ems by pr oviding a differen t way o f grounding and r emoving t he necessi ty to map sel f or non-self. To ac hieve t his self-non-self discri m inatio n will still be useful but it is no longer essential. This is because non- self no longer c auses an i mmune respo nse. Instead, it will be danger signa ls that trigger a reacti on. What could such d anger signals be? They s hould show up after limited in fection to minimise da mage and hence have to be quickl y and au tomatically measurable. Suitable signals could includ e: • Too low or to o high memory usa ge. • Inapprop riate disk activity. • Unexpected frequency o f fil e changes as m easured for example b y checksums or file size. • SIGABRT signal from a bnormally ter minated UNIX processes. • Presence of non -self. Of cour se, it would als o be p ossible to use ‘po sitive’ signals, as discussed in the p revious section, such as the absence of so me normal ‘health’ si gnals. Once the danger signal has be en transmitted, the immune system can then react to those antigens, for example, executables or co nnections, which are ‘near’ the emitter of the danger signal. Note that ‘near ’ does not nece ssarily mean geographica l o r physical clos eness, s omething t hat might make sense for connec tions a nd their I P add resses but pr obably not for co mputer executab les in ge neral. In essence, the p hysical ‘ near’ that the Da nger T heory requires for t he immu ne system is a p roxy mea sure for causality. He nce, we can substitute it with more appropriat e ca usality measure s such a s similar execution start times, con current ru ntimes or acce ss of the same resources. Consequentl y, those ant ibodies or detectors that match (first signal) t hose a ntigens w ithin a radiu s, def ined by a measure such as the ab ove (seco nd signal), will proliferate. H aving thereb y identified the dangerou s components, further confirmat ion could then b e sought b y sending it to a special part of the s ystem si mulating another attack. T his would ha ve the further ad vantage of not having to send all detectors to confirm danger. In conclusion, usin g these ideas fro m the Da nger T heory has provided a b etter grounding o f da nger labels in comparison to self / non-self, wh ilst at the same time relying less on human competence. 5 THE DANGER THEORY AND OTHER ARTIFICIAL IMMUNE SYST EM APPLICATIONS It is not immediately obvious how the Danger Theory could be of use to data minin g probl ems such as the movie prediction prob lem d escribed in Ca yzer a nd Aickelin [7], bec ause the notions o f self and non-self are not used. I n e ssence, in da ta mining a ll of the system is self. Mo re precisely, it is not an issue what is s elf or no n- self as t he d esigner of the dat abase has co m plete contro l over this aspec t. However, if t he label s self and non-self w ere to be replaced b y in teresting and non-interesting data for example, a distinction would prove b eneficial. In this case, the immu ne system is be ing applied as a classifier. If one can t hen further as sume that i nteresting d ata is located ‘close’ or ‘near’ to other interest ing data, ideas from the Dan ger Theo ry can come into play a gain. T o d o so, it is necessar y to define ‘clo se’ / ‘near’. W e could use: • Physical closeness, for instance dista nce in the database as measured by an app ropriate metric. • Correlation of d ata, as measured by statistical tools. • Similar entry ti mes into the databas e. • File size. A danger signal co uld t hus be interpreted as a valuable piece of infor m atio n t hat has bee n uncovered. Hence, those antibo dies are stimulat ed that match d ata that is ‘close’ this va luable piece of infor mation. Taking this idea further, we might d efine the dan ger signal as a n indica tion of user in terest. Gi ven t his definition, we can speculate about v arious scenarios in which the da nger signal could b e of use. One such scenario is outl ined below for illustra tive purposes. Imagine a user bro wsing a s et o f do cuments. Each document ha s a set of featur es (for i nstance keywords, title, auth or, date etc). Imag i ne further that t here is an immune syste m i mplemented as a ‘ watcher’, whose antibodies match d ocument feat ures. ‘I nteresting’ documents are those, whose fea tures are matched by the immune syste m. When a user either e xplicit ly or i mplicitly indicates interest in the current doc ument, a “danger” signal is raised. This causes signal t wo to b e passed, along with signal o ne, to a ntibodies matching a ny anti gen, i.e. document featur e, in the dang er zone, i.e. this d ocument. Stimulated antibodi es become effectors, and thus the immune system lear ns to become a goo d filter when searching for o ther intere sting d ocuments. Interesting documents c ould be br ought to the user ’s at tention ( the exact mechanis m is not relevant here). The importa nt thing is t hat the user’s id ea of an ‘intere sting’ document may cha nge over time and so it is important t hat the immune syst em adapt s in a timely way to s uch a changing definition of ( non-) self. Meanwhile, ever y document b rowsed b y the user (whether interesting o r n ot) will be presented to th e antibodies a s ‘signal o ne’. Uninteresting document features will therefore give rise to si gnal o ne without signal t w o, which wi ll tolerate t he autoreactive antibodies. The net effect is to pro duce a set of antibodies t hat match only interesting document features. As mentioned, t his e xample i s p urely illustrative but i t does sho w t hat ideas fro m the Danger theor y may have implications fo r Artificial I mmune S ystem applications in domains where the relevance of ‘danger’ is far fro m obvious. 6 CONCLUSIONS To conclude, t he Danger Theory is not about the w ay Artificial Im mune Systems rep resent data. Instead, it provides ideas about whi ch data the Artificial I mmune Systems s hould repr esent and d eal with. T hey should focus on dan gerous, i.e. interesting dat a. It could be argued that t he s hift from no n-self to d anger is merely a symbolic label cha nge that achieves nothing. W e do not believe thi s to be the case, since d anger is a grounded signal, and non-self is (typically) a set o f feature vectors with no further i nformation a bout t heir mea ning. The d anger s ignal helps us to i dentify which s ubset of feature vectors is of i nterest. A suitably defined danger signal thus overco mes many o f the limitatio ns of self-non- self selection. It restricts the do m ai n o f non-self to a manageable size, re m o ves t he need to screen against all self, and deals adapt ively with scenarios where self (or non-self) changes over time. The challenge i s clearly t o d efine a suitable danger signal, a cho ice that might prove as critical as the c hoice of fitness functio n for an evolutionar y algorithm. I n addition, the p hysical distance in t he biological syste m should be translated into a suitable prox y measure for si milarity o r causality i n an Artificial I mmune S ystem. We have made some s uggestions i n thi s pape r abo ut how to tac kle t hese challenges i n a variet y of do mains, but the pr ocess is not likely to b e trivial. Nevert heless, if t hese c hallenges ar e met, t hen f uture Artificial I mmune Syste m applicatio ns might deri ve considerab le be nefit, and ne w insights, from the Danger Theo ry. Acknowle dgements We would l ike to tha nk the two anon ymous revie wers, whose co mm ent s greatly impro ved this paper. References [1] Br adley D, T yrell A, T he Architecture for a Hardware Immune Syste m, Proce edings of t he 20 02 Congress on Evolution ary Computation , 2002. [2] Fo rrest H. Ben nett III , John R. Ko za, J essen Yu, William Mydlowec, A utomatic Synthesis, Placement, a nd Routing of an Ampli fier C ircuit b y Means of Genet ic Progra mming. Evolvab le Systems: From Bio logy to Hardware, Th ird International Confe rence, ICES 2000: 1-10, 2000 [3] D. W. Bradley, Andre w M. Tyrrell, I mmunotronics: Hardware Fa ult T olerance I nspired b y t he I mmune System. Evo lvabl e S ystems: Fro m Biol ogy to Hardwa re, Th ird International Conference , ICES 2000: 1 1-20, 2000 [4] Br etscher P, Cohn M, A t heory of self-nonself discrimination, Sci ence 1 69, 1042-1049, 1970 [5] Bur gess M: Co mputer Immunolo gy, Proceed ings of LISA XII , 28 3-297, 1998 . [6] Bur net F, The Clonal Selection Theory of Acqu ired Immunit y , Vanderbilt University Press, Nas hville, TN, 19 59. [7] Cayzer S, Ai ckeli n U, A Recommender Sy stem based on t he I mmune Ne twork, Proce edings of t he 2002 Congress on Evoluti onary Computatio n , 2002. [8] Das gupta D, M ajumdar N, Nino F, Artificial Immune Syste ms: A Bib liography, Comp uter Science D ivision, University of Memphis, Techni cal Report No. CS-02-001, 2 001. [9] Fo rrest S, Hofmeyr S, So m ay aji A, Longstaff T, A sense of self for Unix processe s, Pro ceedings of t he 1996 IEEE Sym posium on Resear ch in Securit y and Privacy , 1 20-128, 1996. [10] Forrest S, http://w ww.cs.unm.ed u/~immsec/, 200 2. [11] Forrest S, Per elson A, Allen L, C herukuri R, Self- non-self discri mination i n a co mputer, Pr oceedings of the 19 94 I EEE Sy mposium on Research in Securit y and Privacy , 202 -212, 1994. [12] Goldsby R, Ki ndt T, Osbo rne B, Kuby Immun ology , Fourth Edition, W H Freeman, 2 000. [13] Hofmeyr S, Forre st S, Architecture for an Artificial Immune S ystem, Evo lutionary Computati on 8(4), 443-47 3, 2000. [14] Janeway C, The i mmune S ystem evol ved to discriminated i nfectious nonself fro m no ninfectious self, Immunol ogy Today 13 , 11-16, 1992. [15] Kim J, Bentley P, An evaluation of negati ve selection i n an art ificial immu ne for network intrusion det ection, Pro ceedings of the 200 1 Genetic and Evoluti onary Comput ation Conference , 1330 - 1337, 2001 . [16] Kim J, B entley P, Towards an Artificial Immune System for Network Intrusion Dete ction: An Investigation o f Dynamic Clonal Selection. Proceedin gs of the 20 02 Congress on Evolutiona ry Comput ation , 2002. [17] Lafferty K , Cunningham A, A new analysis of allogeneic interactions. A u stralian Journal of Experiment al Biology and Medical Scien ces . 53 :27- 42, 1975 [18] Matzinger P , http://cmmg.bio sci.wayne.edu/asg/ polly.html [19] Matzinger P, The Danger Model in It s Historical Context, Scan dinavian Journal of I mmunology , 54: 4-9, 20 01. [20] Matzinger P, To lerance, Danger and the Exte nded Family, Annual Review of Immunolog y , 1 2:991- 1045, 1994 . [21] Langman R (editor), Self non-self d iscrimination revisited, S eminars in Immu nology 12, Issue 3 , 2000. [22] Somayaji A, Forrest S, Automated response using system-call delays, Pro ceedin gs of t he ninth USENIX Secu rity Symposi um , 185-197, 2000 . [23] Williamson M, B iologicall y inspir ed appr oaches to computer security, HP Labs Technical Reports HPL-2002 -131, 2000 (available from http://www.hpl. hp.com/techrepo rts/2002 /HPL- 2002 -131.html ).
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment