Entanglement-Assisted Quantum Convolutional Coding
We show how to protect a stream of quantum information from decoherence induced by a noisy quantum communication channel. We exploit preshared entanglement and a convolutional coding structure to develop a theory of entanglement-assisted quantum conv…
Authors: ** - Mark M. Wilde - Todd A. Brun - (공동 저자: 기타 연구진) **
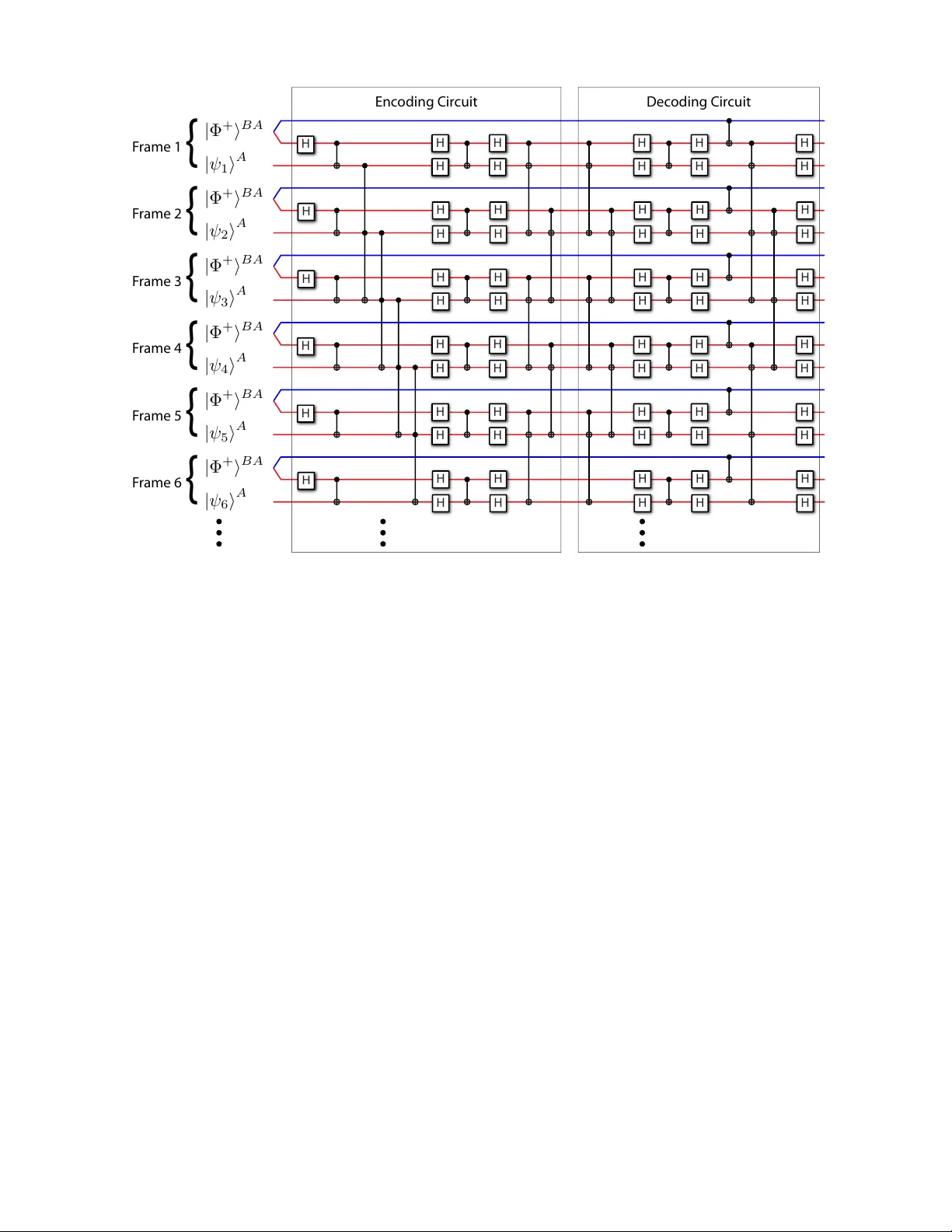
En tanglemen t-assisted quan tum con v olutional co ding Mark M. Wilde ∗ and T o dd A. Brun † Communic ation Scienc es Institute, Dep artment of Ele ctric al Engine ering, University of Southern California, L os Angeles, California 90089 USA W e sho w how to protect a stream of quantum information from decoherence induced by a noisy quan tum comm unication c hannel. W e exploit preshared entanglemen t and a conv olutional co ding structure to dev elop a theory of entanglemen t-assisted quantum con volutional coding. Our con- struction pro duces a Calderbank-Shor-Steane (CSS) entanglemen t-assisted quantum conv olutional co de from tw o arbitrary classical binary conv olutional co des. The rate and error-correcting prop- erties of the classical conv olutional co des directly determine the corresp onding prop erties of the resulting entanglemen t-assisted quantum conv olutional co de. W e explain how to enco de our CSS en tanglement-assisted quantum conv olutional co des starting from a stream of information qubits, ancilla qubits, and shared entangled bits. P ACS num bers: Keywords: quantum conv olutional codes, entanglemen t-assisted quan tum con volutional co des, quantum in- formation theory , entanglemen t-assisted quantum codes I. INTR ODUCTION Quan tum error correction theory [1–6] stands as the piv otal theoretical tool that will make reliable quantum computing and quantum communication p ossible. An y future quan tum information pro cessing device will op- erate faithfully only if it emplo ys an error correction sc heme. This scheme can b e an active scheme [4], a pas- siv e scheme [7 – 9], or a com bination of b oth tec hniques [10 – 14]. Mermin pro claims it a “miracle” that quantum error correction is even p ossible [15]. V arious obstacles such as the no-cloning theorem [16], measurement destroying a quan tum state, and contin uous quantum errors seem to p ose an insurmountable barrier to a proto col for quantum error correction. Despite these obstacles, Shor demon- strated the first quantum error-correcting co de that re- duces the negative effects of decoherence on a quantum bit [1]. Shor’s code ov ercame all of the ab ov e difficul- ties and established the basic principles for constructing a general theory of quantum error correction [4–6]. Gottesman formalized the theory of quantum block co ding by establishing the stabilizer formalism [4]. The stabilizer formalism allows one to imp ort self-orthogonal classical blo c k co des for use in quantum error correction [6]. This technique has the b enefit of exploiting the large b ody of research on classical co ding theory [17] for use in quantum error correction, but the self-orthogonalit y constrain t limits the classical blo c k co des that we can imp ort. Bo wen w as the first to extend the s tabilizer formal- ism by providing an example of a co de that exploits en- tanglemen t shared b etw een a sender and a receiver [18]. The underlying assumption of Bow en’s co de is that the ∗ Electronic address: mwilde@gmail.com † Electronic address: tbrun@usc.edu sender and receiver share a set of noiseless ebits (en- tangled qubits) b efore quantum comm unication b egins. Man y quan tum protocols such as telep ortation [19] and sup erdense co ding [20] are “entanglemen t-assisted” pro- to cols b ecause they assume that noiseless ebits are av ail- able. Brun, Dev etak, and Hsieh generalized Bo wen’s ex- ample by constructing a theory of stabilizer co des that emplo ys ancilla qubits and shared ebits for enco ding a quan tum error-correcting co de [21, 22]. The so-called en tanglement-assisted stabilizer formalism subsumes the stabilizer formalism as the theory of active quan tum error correction. The ma jor benefit of the entanglemen t-assisted stabi- lizer formalism is that we can construct an en tanglement- assisted quantum co de from t wo arbitrary classical bi- nary blo c k co des or from an arbitrary classical quater- nary blo ck co de. The rates and error-correcting prop er- ties of the classical co des translate to the resulting quan- tum co des. The entanglemen t-assisted stabilizer formal- ism may b e able to reduce the problem of finding high- p erformance quantum co des approaching the quantum capacit y [23 – 27] to the problem of finding go od classical linear co des approaching the classical capacit y [28]. Another extension of the theory of quan tum error cor- rection protects a p otentially-infinite stream of quantum information against the corruption induced by a noisy quan tum communication channel [29 – 35]. These quan- tum conv olutional co des p ossess sev eral adv an tages ov er quan tum blo ck co des. A quantum conv olutional co de t ypically has lo w er encoding and deco ding complexity and sup erior co de rate when compared to a blo c k co de that protects the same n um b er of information qubits [35]. F orney et al. hav e determined a metho d for imp orting an arbitrary classical self-orthogonal quaternary co de for use as a quantum conv olutional co de [34, 35]. The tech- nique is similar to that for imp orting a classical blo ck co de as a quantum blo ck co de [6]. One limitation of this tec hnique is that the self-orthogonality constrain t is more T yp eset by REVT E X 2 restrictiv e in the conv olutional setting. Eac h generator for the quantum con volutional co de must commute not only with the other generators, but it must comm ute also with any arbitrary shift of itself and any arbitrary shift of the other generators. F orney et al. p erformed spe- cialized searches to determine classical quaternary co des that satisfy the restrictive self-orthogonalit y constraint [35]. In this paper, w e dev elop a theory of en tanglement- assisted quantum conv olutional co ding for a broad class of co des. Our ma jor result is that we can pro duce an en tanglement-assisted quantum conv olutional co de from t wo arbitr ary classical binary conv olutional co des. The resulting quantum con v olutional codes admit a Calderbank-Shor-Steane (CSS) structure [2, 3, 36]. The rates and error-correcting prop erties of the tw o binary classical conv olutional co des directly determine the cor- resp onding properties of the en tanglement-assisted quan- tum conv olutional co de. Our techniques for enco ding and deco ding are also an expansion of previous tec hniques from quantum con vo- lutional coding theory . Previous techniques for enco d- ing and deco ding include finite-depth op erations only . A finite-depth op eration propagates errors to a finite n um- b er of neigh b oring qubits in the qubit stream. W e in- tro duce an infinite-depth op eration to the set of shift- in v arian t Clifford op erations and explain it in detail in Section VI. W e must b e delicate when using infinite- depth op erations because they can propagate errors to an infinite num ber of neigh b oring qubits in the qubit stream. W e explain our assumptions in detail in Section VI I for including infinite-depth op erations in our entanglemen t- assisted quantum con volutional co des. An infinite-depth op eration giv es more flexibility when designing enco ding circuits—similar to the wa y in which an infinite-impulse resp onse filter gives more flexibility in the design of clas- sical con volutional circuits. It also is the key op eration enabling us to imp ort arbitrary classical conv olutional co des for entanglemen t-assisted quantum co ding. Our CSS en tanglement-assisted quantum conv olu- tional co des divide in to t w o classes based on certain prop erties of the classical c odes from which we pro duce them. These prop erties of the classical co des determine the structure of the enco ding and deco ding circuit for the code, and the structure of the encoding and deco ding circuit in turn determines the class of the entanglemen t- assisted quantum conv olutional co de. 1. Co des in the first class admit b oth a finite-depth enco ding and deco ding circuit. 2. Co des in the second class hav e an enco ding circuit that employs b oth finite-depth and infinite-depth op erations. Their decoding circuits hav e finite- depth op erations only . W e structure our w ork as follows. Section I I re- views the stabilizer formalism for quan tum blo ck co des, en tanglement-assisted quan tum codes, and conv olutional stabilizer codes. W e review the imp ortan t isomorphism that allows us to work with matrices of binary p olyno- mials rather than infinite tensor pro ducts of Pauli ma- trices. Section II I reviews finite-depth Clifford op er- ations for use in encoding and deco ding [31 – 33]. W e outline the operation of an en tanglement-assisted quan- tum con volutional co de and present our main theorem in Section IV. This theorem shows ho w to pro duce a CSS entanglemen t-assisted quan tum conv olutional co de from t wo arbitrary classical binary conv olutional co des. The theorem gives the rate and error-correcting prop- erties of a CSS entanglemen t-assisted quantum conv olu- tional co de as a function of the parameters of the classical con volutional co des. Section V completes the pro of of the theorem for our first class of entanglemen t-assisted quan tum conv olutional co des. In Section VI, we intro- duce an infinite-depth enco ding op eration to the set of shift-in v arian t Clifford op erations and discuss its effect on b oth the stabilizer and the logical op erators for the information qubits. Section VI I completes the proof of our theorem for the second class of entanglemen t- assisted quantum conv olutional co des. W e discuss the implications of the assumptions for the differen t classes of en tanglemen t-assisted quan tum con volutional co des while developing the constructions. Our hop e is that our theory will pro duce high-p erformance quan tum con- v olutional co des by importing high-p erformance classical con volutional co des. I I. REVIEW OF THE ST ABILIZER F ORMALISM The stabilizer formalism is a mathematical framework for quantum error correction [4, 37]. This framew ork has man y similarities with classical co ding theory , and it is ev en p ossible to imp ort a classical co de for use in quan- tum error correction by employing the CSS construc- tion [2, 3, 36]. W e briefly review the stabilizer theory for quantum block codes, en tanglemen t-assisted quantum blo c k co des, and quan tum conv olutional co des (see Refs. [35, 38] for a more detailed review). A. Stabilizer F ormalism for Quantum Blo c k Co des The following four matrices I ≡ 1 0 0 1 , X ≡ 0 1 1 0 , Y ≡ 0 − i i 0 , Z ≡ 1 0 0 − 1 , in the P auli group Π = { I , X, Y , Z } are the most im- p ortan t in formulating a quantum error-correcting co de. Tw o crucial prop erties of these matrices are useful: each matrix in Π has eigenv alues equal to +1 or − 1, and any t wo matrices in Π either commute or anticomm ute. Ma- trices in Π act on a tw o-dimensional complex vector, or equiv alen tly , a single qubit. 3 In general, a quantum error-correcting co de uses n ph ysical qubits to protect a smaller set of information qubits against decoherence or quantum noise. An n -qubit quan tum error-correcting co de emplo ys elements of the P auli group Π n . The P auli group Π n consists of n -fold tensor pro ducts of P auli matrices: Π n = e iφ A 1 ⊗ · · · ⊗ A n : ∀ j ∈ { 1 , . . . , n } , A j ∈ Π , φ ∈ { 0 , π / 2 , π , 3 π/ 2 } . (1) W e lib erally omit the tensor pro duct symbol in what fol- lo ws so that A 1 · · · A n ≡ A 1 ⊗ · · · ⊗ A n . The ab ov e t wo crucial prop erties for the single-qubit Pauli group Π still hold for the Pauli group Π n (up to an irrelev ant phase for the eigenv alue prop erty). Matrices in Π n act on a 2 n - dimensional complex vector, or equiv alen tly , an n -qubit quan tum register. W e can phrase the theory of quantum error correction in purely mathematical terms using elemen ts of Π n . Con- sider a matrix g 1 ∈ Π n that is not equal to ± I . Matrix g 1 then has tw o eigenspaces eac h of size 2 n − 1 . W e can iden tify one eigenspace with the eigenv alue +1 and the other eigenspace with eigenv alue − 1. Consider a matrix g 2 ∈ Π n differen t from g 1 that comm utes with g 1 . Ma- trix g 2 also has t wo eigenspaces each of size 2 n − 1 and iden tified similarly by its eigenv alues ± 1. Both g 1 and g 2 ha ve simultaneous eigenspaces b ecause they comm ute. These matrices together hav e four different eigenspaces, eac h of size 2 n − 2 and iden tified b y the eigen v alues ± 1 , ± 1 of g 1 and g 2 resp ectiv ely . W e can contin ue this pro cess of adding more commuting and indep endent matrices to a set S . The matrices in S are indep enden t in the sense that no matrix in S is a product of tw o or more other ma- trices in S . Adding more matrices from Π n to S contin- ues to divide the eigenspaces of matrices in S . In general, supp ose S consists of n − k indep endent and commuting matrices g 1 , . . . , g n − k ∈ Π n . These n − k matrices then ha ve 2 n − k differen t eigenspaces each of size 2 k and iden- tified by the eigenv alues ± 1, . . . , ± 1 of g 1 , . . . , g n − k resp ectiv ely . Consider that the Hilb ert space of k qubits has size 2 k . A dimension count immediately suggests that w e can enco de k qubits into one of the eigenspaces of S . W e typically enco de these k qubits into the simul- taneous +1-eigenspace of g 1 , . . . , g n − k . This eigenspace is the c o desp ac e . An [ n, k ] quantum error-correcting code enco des k information qubits into the simultaneous +1- eigenspace of n − k matrices g 1 , . . . , g n − k ∈ Π n . The rate of an [ n, k ] co de is the ratio of information qubits to ph ysical qubits: k /n . The operation of an [ n, k ] quan tum error-correcting co de consists of four steps. Figure 1 highligh ts these steps. First, a unitary op eration U enco des k qubits and n − k ancilla qubits into the simultaneous +1-eigenspace of the matrices g 1 , . . . , g n − k . The sender transmits the n enco ded qubits by using the noisy quantum communi- cation channel n times. The receiver p erforms quan tum measuremen ts of the n − k matrices g 1 , . . . , g n − k . These measuremen ts learn only ab out errors that may o ccur and do not disturb the enco ded quantum information. N oise Enc o ding U E r r or D iagnosis and R ec o v er y | ψ | 0 R FIG. 1: The op eration of a general stabilizer co de. Thin lines denote quantum information and thic k lines denote classical information. Slan ted bars denote multiple qubits. A sender emplo ys a unitary enco ding op eration U to enco de a set of information qubits in the state | ψ i with the help of ancilla qubits each in the state | 0 i . The sender transmits the encoded qubits ov er the noisy quantum communication channel. The receiv er p erforms quan tum measurements to diagnose which error has o ccurred. He finally p erforms a recov ery op eration R to reverse the error from the channel. Eac h measuremen t giv es a bit result equal to +1 or − 1, and the result of all the measurements is to pro ject the n -qubit quan tum register into one of the 2 n − k differen t eigenspaces of g 1 , . . . , g n − k . Supp ose that no error o c- curs. Then the measurements pro ject the n qubits into the simultaneous +1-eigenspace and return a bit vector consisting of n − k ones. No w supp ose that a quantum error in an error set E occurs. The error tak es the en- co ded quantum state out of the codespace and into one of the other 2 n − k − 1 orthogonal eigenspaces. The mea- suremen ts can detect that an error has o ccurred b ecause the result of the measurements is a bit vector differing from the all ones vector. The receiver may b e able to iden tify uniquely which error has o ccurred if it satisfies the follo wing quantum error correction conditions: ∀ E a , E b ∈ E ∃ g i ∈ S : g i , E † a E b = 0 or E † a E b ∈ S . The first condition states that errors are detectable if they an ticommute with one of the generators in S , and the second condition states that errors ha ve no effect on the enco ded state if they are in S . If the receiver can iden tify whic h error o ccurs, he can then apply unitary op eration R that is the inv erse of the error. He finally p erforms a deco ding unitary that deco des the k informa- tion qubits. W e commen t briefly on the encoding operation U . The enco ding op eration U is a sp ecial type of unitary matrix called a Clifford op eration. A Clifford op eration U is one that preserves elements of the Pauli group under con- jugation: A ∈ Π n ⇒ U AU † ∈ Π n . The CNOT gate, the Hadamard gate H , and the phase gate P suffice to implemen t any unitary matrix in the Clifford group [4]. A quan tum co de with the CSS structure needs only the CNOT and Hadamard gates for enco ding and deco ding. 4 The matrix for the CNOT gate acting on tw o qubits is CNOT = 1 0 0 0 0 1 0 0 0 0 0 1 0 0 1 0 , (2) the matrix for the Hadamard gate H acting on a single qubit is H = 1 √ 2 1 1 1 − 1 , (3) and the matrix for the phase gate P acting on a single qubit is P = 1 0 0 i . (4) F or the CNOT gate, the first qubit is the “control” qubit and the second qubit is the “target” qubit. The standard basis for elements of the tw o-qubit P auli group Π 2 is as follo ws Z I I Z X I I X , (5) b ecause any element of Π 2 is a pro duct of the ab o ve four matrices up to an irrelev an t phase. The standard basis for Π 1 is X and Z for the same reasons. The CNOT gate transforms the standard basis of Π 2 under conjugation as follows Z I I Z X I I X → Z I Z Z X X I X , (6) where the first qubit is the control and the second qubit is the target. The Hadamard gate H transforms the stan- dard basis of Π 1 under conjugation as follows: Z X → X Z , (7) and the phase gate P transforms the standard basis as follo ws: Z X → Z Y . (8) App endix of Ref. [38] details an algorithm that deter- mines an encoding circuit consisting of CNOT, H , and P gates for an y stabilizer co de or an y entanglemen t-assisted stabilizer code (we review en tanglemen t-assisted codes in the next section). Another asp ect of the theory of quantum error cor- rection is later useful for our purp oses in quantum con- v olutional co ding. This asp ect concerns the information qubits and the op erators that change them. Consider that the initial unenco ded state of a quantum error- correcting co de is a simultaneous +1-eigenstate of the matrices Z k +1 , . . . , Z n where Z i has a Z matrix op erating on qubit i and the iden tity I on all other qubits. There- fore, the matrices Z k +1 , . . . , Z n constitute a stabilizer for the unenco ded state. The initial unenco ded logical op er- ators for the information qubits are Z 1 , X 1 , . . . , Z k , X k . The enco ding op eration U rotates the unenco ded sta- bilizer matrices Z k +1 , . . . , Z n and the unencoded logi- cal operators Z 1 , X 1 , . . . , Z k , X k to the enco ded stabi- lizer ¯ Z k +1 , . . . , ¯ Z n and the enco ded logical operators ¯ Z 1 , ¯ X 1 , . . . , ¯ Z k , ¯ X k resp ectiv ely . The encoded matrices ¯ Z k +1 , . . . , ¯ Z n are resp ectiv ely equiv alen t to the matrices g 1 , . . . , g n − k in the ab ov e discussion. The enco ded op er- ators ob ey the same comm utation relations as their un- enco ded counterparts. W e w ould violate the uncertaint y principle if this inv ariance do es not hold. Therefore, each of the enco ded logical operators commutes with elemen ts of the stabilizer S . Let A denote an arbitrary logical op- erator from the ab o ve set and let ¯ Z i denote an arbitrary elemen t of the stabilizer S . The operator A ¯ Z i (or equiv a- len tly ¯ Z i A ) is an equiv alen t logical op erator b ecause A ¯ Z i and A hav e the same effect on an enco ded state ¯ ψ : ¯ Z i A ¯ ψ = A ¯ Z i ¯ ψ = A ¯ ψ . (9) W e mak e extensive use of the ab ov e fact in our work. The logical op erators also provide a useful wa y to char- acterize the information qubits. Gottesman show ed that the logical op erators for the information qubits provide a straightforw ard w a y to characterize the information qubits as they progress through a quantum circuit [4]. As an example of this technique, he develops quantum tele- p ortation in the stabilizer formalism. The logical op era- tors at the b eginning of the proto col are X 1 and Z 1 and b ecome X 3 and Z 3 at the end of the proto col. The quan- tum information in qubit one telep orts to qubit three b ecause the logical op erators act on only qubit three at the end of the proto col. W e use the same idea through- out this pap er to determine if our deco ding circuits hav e truly deco ded the information qubits. It is p ossible to produce a stabilizer code from t wo classical binary blo ck co des by employing the CSS con- struction. The elements of the stabilizer group of a CSS stabilizer co de comm ute if and only if the co dew ords of one classical co de are orthogonal to the co dewords of the other classical code with respect to the binary inner prod- uct. The co des that we can import must satisfy this con- dition b ecause the commuting condition is essential in form ulating a quantum co de. The entanglemen t-assisted stabilizer formalism finds a clever wa y around this restric- tion by exploiting entanglemen t shared b et ween sender and receiver. 5 B. En tanglement-Assisted Stabilizer F ormalism for Quan tum Blo c k Co des The entanglemen t-assisted stabilizer formalism is a significan t extension of the standard stabilizer formal- ism that incorporates shared en tanglemen t as a re- source for enco ding [21, 22]. Sev eral references pro- vide a review of this technique and generalizations of the basic theory to blo c k [39] and conv olutional [38] en tanglement distillation proto cols, contin uous-v ariable co des [40], and entanglemen t-assisted op erator co des for discrete-v ariable [13, 14] and con tin uous-v ariable systems [41]. An entanglemen t-assisted code employs ebits or Bell states in addition to ancilla qubits for quan tum redun- dancy . W e express the state | Φ + i of an ebit shared b e- t ween a sender Alice and a receiver Bob as follows: Φ + ≡ | 00 i AB + | 11 i AB √ 2 . (10) The adv an tage of the entanglemen t-assisted stabilizer formalism is that it allows us to exploit the error- correcting prop erties of an arbitrary set of Pauli matrices. They do not necessarily hav e to form a comm uting set. In particular, this construction allows us to pro duce a quan tum blo ck co de from t wo arbitrary classical binary blo c k co des by employing the CSS construction. Two high-p erformance classical blo ck co des lead to a high- p erformance en tanglement-assisted quantum co de. The en tanglement-assisted metho d allo ws us to exploit the full error-correcting p o wer of classical co ding theory . An [ n, k ; c ] en tanglemen t-assisted code uses c ebits and n − k − c ancilla qubits to encode k information qubits. It op erates as follo ws. The sender and receiv er share c ebits b efore quantum communication b egins. The sender en- co des her k information qubits with the help of n − k − c ancilla qubits and her half of the c ebits. She p erforms an enco ding op eration U on her n qubits and sends them o ver a noisy quantum comm unication channel. The noisy c hannel affects these n qubits only and does not affect the receiver’s half of the c ebits. The receiv er com bines his half of the c ebits with those he receives from the noisy quantum channel. He p erforms measurements on all n + c qubits to diagnose an error that may o ccur on the n qubits. He learns which error o ccurs and p erforms a reco very op eration that eliminates the error. Figure 2 illustrates the op eration of an entanglemen t-assisted sta- bilizer co de. Supp ose we hav e an arbitrary set of P auli matrices in Π n whose error-correcting properties w e w ould lik e to ex- ploit. W e do not necessarily know b eforehand ho w many ebits we require for the Pauli matrices to form a com- m uting set, and w e would lik e a metho d to determine the minimum num ber of ebits. Sev eral metho ds exist [13, 14, 21, 22, 38], but the algorithm in the App endix of Ref. [38] determines the minimum num ber of ebits re- quired for the code, the encoding and deco ding circuit for the co de, and the measurements the receiver performs to N oise Enc o ding U E r r or D iagnosis and R ec o v er y R | ψ | 0 FIG. 2: The op eration of a general en tanglemen t-assisted sta- bilizer co de. The sender enco des a set of information qubits with the help of ancilla qubits and her half of a set of shared ebits. She sends her enco ded qubits ov er a noisy quantum comm unication channel. The entanglemen t-assisted commu- nication paradigm assumes that the receiv er’s half of the shared ebits remain noiseless throughout this pro cess. The receiv er combines the noisy qubits with his half of the shared ebits. He p erforms measurements on all of the qubits to di- agnose which error o ccurs and reverses the effect of this error b y p erforming a recov ery op eration. diagnose errors. It essentially “kills three birds with one stone.” The algorithms we employ in this work are simi- lar to the algorithm in Ref. [38], but they are quite a bit more complicated b ecause of the conv olutional nature of our co des. 1. R ate of an Entanglement-Assiste d Quantum Co de W e can in terpret the rate of an entanglemen t-assisted quan tum con volutional co de in three differen t w ays [21, 22, 38]. Suppose that an entanglemen t-assisted quan tum co de encodes k qubits in n qubits with the help of c ebits. 1. The “entanglemen t-assisted” rate assumes that en- tanglemen t shared betw een sender and receiver is free. Bennett et al. make this assumption when deriving the entanglemen t-assisted capacit y of a quan tum channel for sending quan tum information [26, 27]. The entanglemen t-assisted rate for the ab o v e example is k /n . 2. The “trade-off ’ rate assumes that entanglemen t is not free and a rate pair determines p erformance. The first n um b er in the pair is the num b er of noise- less qubits generated p er channel use, and the sec- ond n um b er in the pair is the n umber of ebits consumed p er c hannel use. The rate pair for the ab o v e example is ( k/n, c/n ). Quantum informa- tion theorists hav e computed asymptotic trade-off curv es that b ound the rate region in whic h achiev- able rate pairs lie [42]. Brun et al.’s construction for an en tanglement-assisted quan tum block code min- imizes the num ber c of ebits given a fixed n umber k and n of information qubits and enco ded qubits resp ectiv ely [21, 22]. 6 3. The “catalytic rate” assumes that bits of entangle- men t are built up at the exp ense of transmitted qubits [21, 22]. A noiseless quantum channel or the enco ded use of noisy quantum channel are tw o differen t w ays to build up entanglemen t b et ween a sender and rece iv er. The catalytic rate for the ab o v e co de is ( k − c ) /n . Whic h interpretation is most reasonable dep ends on the con text in which we use the co de. In any case, the parameters n , k , and c ultimately gov ern p erformance, regardless of which definition of the rate we use to inter- pret that p erformance. C. Stabilizer F ormalism for Quantum Con volutional Co des W e review the theory of conv olutional stabilizer co des b y considering a set of Pauli matrices that stabilize a stream of enco ded qubits. W e follow with the most im- p ortan t part of this review—the isomorphism from the set of P auli sequences to the mo dule ov er the ring of binary p olynomials [30, 31, 35]. W e name it the P auli- to-binary (P2B) isomorphism. The P2B isomorphism is imp ortan t b ecause it is easier to p erform manipulations with vectors of binary p olynomials than with P auli se- quences. W e review the notation and basic definitions first. A P auli sequence A is a countably infinite tensor pro duct of P auli matrices A i : A = ∞ O i =0 A i . The weigh t of a P auli sequence is the n umber of Pauli matrices in the coun tably-infinite tensor product that are not equal to the identit y matrix. A Pauli sequence has finite supp ort if its weigh t is finite. Let Π Z + denote the set of all Pauli sequences and let F (Π Z + ) denote the set of P auli sequences with finite supp ort. Definition 1. A r ate- k /n quantum c onvolutional c o de c onsists of a b asic set G 0 of n − k gener ators and al l of their n -qubit shifts [29, 30, 35]. The gener ators in G 0 c ommute with e ach other and with al l of their n -qubit shifts. The p ar ameters k and n satisfy 0 ≤ k ≤ n and the b asic set G 0 is as fol lows: G 0 = n G i ∈ F (Π Z + ) : 1 ≤ i ≤ n − k o . A fr ame of the c o de c onsists of n qubits. The operation of a rate- k /n quan tum con volutional co de b egins with the sender enco ding a stream of infor- mation qubits. Figure 3 of Ref. [38] illustrates the basic op eration of a quan tum conv olutional co de. The sender enco des n − k ancilla qubits and k information qubits per frame [31, 33] and transmits the enco ded qubits o ver a noisy quantum channel. The ab ov e stabilizer G 0 and all of its shifts act lik e a parit y chec k matrix for the quan tum con volutional co de. The receiver measures the genera- tors in the stabilizer to determine an error syndrome. It is imp ortant that the generators in G 0 ha ve finite weigh t so that the receiver can perform the measurements and pro duce an error syndrome. It is also imp ortan t that the generators hav e a blo c k-band form so that the re- ceiv er can p erform the measurements online as the noisy enco ded qubits arrive. The receiv er pro cesses the error syndrome with a metho d such as the Viterbi algorithm [43] or an y other deco ding algorithm [44] to determine the most likely error for each frame of quantum data. The receiver p erforms a unitary that reverses the errors. He finally pro cesses the enco ded qubits with a deco d- ing circuit to recov er the original stream of information qubits. 1. The P2B Isomorphism W e now review the P2B isomorphism from the set of phase-free Pauli sequences to the mo dule ov er the ring of binary polynomials [30, 35, 38]. W e illustrate it by example (see Ref. [38] for a more rigorous developmen t.) Supp ose the following tw o basic generators sp ecify a rate-1/3 quan tum conv olutional co de [34, 35]: · · · I I I I I I X X X Z Z Z X Z Y Z Y X I I I I I I · · · (11) The vertical bars indicate that we shift by multiples of three to obtain the other generators in the quantum con- v olutional co de. Observ e that the ab o ve tw o generators comm ute with all of their three-qubit shifts. The P2B isomorphism is a mapping from the ab o ve stabilizer generators to a matrix whose en tries are binary p olynomials. The left side of the matrix is the “Z” matrix and the right side of the matrix is the “X” matrix. W e consider the entries in the first frame of the stabilizer generators in (11) for now and map these entries to a matrix with binary en tries. The first frame of the first generator in (11) has “X” en tries only and the first frame of the second generator in (11) has “Z” entries only . The binary matrix corresp onding to the entries in the first frame is as follows: H 0 = 0 0 0 1 1 1 1 1 1 0 0 0 . The vertical bar now indicates the separation of the “Z” matrix on the left and the “X” matrix on the right. A “Y” entry maps to a “1” in both the “Z” and “X” matrix. Let us consider the entries in the second frame of (11). They map to the following binary matrix: H 1 = 0 1 1 1 1 0 1 0 1 0 1 1 . W e form a matrix of binary p olynomials by incorp orat- ing the delay transform or D -transform. The following 7 binary p olynomial matrix H ( D ) fully sp ecifies the quan- tum conv olutional co de: H ( D ) = H 0 + H 1 · D = 0 D D 1 + D 1 + D 1 1 + D 1 1 + D 0 D D . The ab o ve description of a quan tum con volutional co de with a binary p olynomial matrix is p o werful b ecause it allo ws us to p erform manipulations with finite polynomi- als rather than with countably-infinite sequences of Pauli matrices (classical conv olutional co ding theory exploits the same idea [44]). The first and second rows of H ( D ) capture all of the information ab out the first and second generators in (11) and all of their three-qubit shifts. W e obtain the nl -shift of either of the ab ov e generators by m ultiplying the corresp onding row in H ( D ) by D l . 2. The Shifte d Symple ctic Pr o duct The shifted symplectic pro duct provides a wa y to determine the commutativ e prop erties of any conv olu- tional stabilizer co de [30, 38] (See Ref. [38] for a detailed discussion of the shifted symplectic pro duct with exam- ples). Let z 1 ( D ) and z 2 ( D ) denote the first and second resp ectiv e rows of the “Z” matrix of H ( D ). Let x 1 ( D ) and x 2 ( D ) b e the first and second resp ective rows of the “X” matrix of H ( D ). Let h 1 ( D ) = ( z 1 ( D ) | x 1 ( D )) , h 2 ( D ) = ( z 2 ( D ) | x 2 ( D )) , denote the first and second respective rows of H ( D ). The v ectors h 1 ( D ) and h 2 ( D ) sp ecify the first and sec- ond resp ectiv e generators in (11). W e define the shifted symplectic pro duct of h 1 ( D ) and h 2 ( D ) as follows: ( h 1 h 2 ) ( D ) = z 1 D − 1 · x 2 ( D ) + x 1 D − 1 · z 2 ( D ) , where · denotes the binary inner pro duct and addition is binary . The shifted symplectic pro duct ( h 1 h 2 ) ( D ) v anishes in the abov e case. The shifted symplectic pro ducts ( h 1 h 1 ) ( D ) and ( h 2 h 2 ) ( D ) also v anish. The shifted symplectic pro duct b etw een tw o vectors of binary p oly- nomials v anishes if and only if their corresp onding Pauli sequences commute [30, 38]. Time reversal (substituting D − 1 for D ) ensures that the shifted symplectic product c hecks commutativit y for every shift of the tw o Pauli se- quences b eing compared. The cases where the shifted symplectic pro duct do es not v anish (where the tw o Pauli sequences anticomm ute for one or more shifts) are im- p ortan t for constructing entanglemen t-assisted quantum con volutional co des. 3. R ow and Column Op er ations W e can p erform row op erations on binary p olynomial matrices for quan tum con volutional co des. A ro w op er- ation is merely a “mental” op eration that has no effect on the states in the co despace or on the error-correcting prop erties of the co de. W e hav e three t yp es of row op er- ations: 1. An elementary ro w op eration multiplies a ro w times an arbitrary binary p olynomial and adds the re- sult to another ro w. This additive inv ariance holds for any co de that admits a description within the stabilizer formalism. Additive co des are inv ariant under multiplication of the stabilizer generators in the “P auli picture” or under ro w addition in the “binary-p olynomial picture.” 2. Another t yp e of ro w operation is to m ultiply a ro w by an arbitrary pow er of D . Ollivier and Tillic h discuss such row op erations as “m ultiplica- tion of a line by D ” and use them to find enco ding op erations for their quantum con volutional co des [30]. Grassl and R¨ otteler use this type of op era- tion to find a sub co de of a given quantum con vo- lutional co de with an equiv alen t asymptotic rate and equiv alen t error-correcting prop erties [31]. W e use this type of row op eration in each of our three classes of entanglemen t-assisted quantum conv olu- tional co des. 3. W e also employ ro w operations that multiply a ro w b y an arbitrary polynomial (not necessarily a p ow er of D ). W e only use these operations when the re- ceiv er p erforms a measurement to diagnose an er- ror. This t yp e of ro w op eration o ccurs when w e ha ve generators with infinite weigh t that we would lik e to reduce to finite w eight so that the receiv er can p erform measuremen ts in an online fashion as qubits arrive from the noisy channel. W e use this type of row op eration in our second and third classes of entanglemen t-assisted quantum conv olu- tional co des. A ro w op eration do es not change the shifted symplec- tic pro duct when all generators commute. A row op era- tion do es change the shifted symplectic pro duct of a set of generators that do not comm ute. It is a con venien t to ol for constructing our entanglemen t-assisted quantum con volutional co des. W e can also p erform column op erations on binary p oly- nomial matrices for quantum con volutional co des. Col- umn op erations change the error-correcting prop erties of the co de and are imp ortan t for realizing a p eriodic en- co ding circuit for the code. W e ha v e tw o t yp es of column op erations: 1. An elementary column op eration multiplies one col- umn by an arbitrary binary p olynomial and adds the result to another column. W e implement el- emen tary column op erations with gates from the shift-in v arian t Clifford group [31, 33]. 8 2. Another column op eration is to multiply column i in both the “X” and “Z” matrix b y D l where l ∈ Z . W e p erform this op eration b y delaying or adv ancing the pro cessing of qubit i by l frames relative to the original frame. A column op eration implemented on the “X” side of the binary p olynomial matrix has a corresp onding effect on the “Z” side of the binary p olynomial matrix. This corresp onding effect is a manifestation of the Heisenberg uncertain ty principle b ecause comm utation relations re- main inv ariant with respect to the action of quantum gates. The shifted symplectic pro duct is therefore in- v arian t with respect to column op erations from the shift- in v arian t Clifford group. W e describ e p ossible column op erations for implemen ting encoding circuits in the next section. I II. FINITE-DEPTH CLIFFORD OPERA TIONS One of the main adv an tages of a quantum con volu- tional co de is that its enco ding circuit has a p eriodic form. W e can enco de a stream of quantum information with the same physical routines or devices and therefore reduce enco ding and deco ding complexity . Ollivier and Tillich were the first to discuss enco ding circuits for quan tum con volutional co des [29, 30]. They pro vided a set of necessary and sufficient conditions to de- termine when an enco ding circuit is noncatastrophic. A noncatastrophic enco ding circuit do es not propagate un- corrected errors infinitely through the deco ded informa- tion qubit stream. Classical conv olutional co ding theory has a well developed theory of noncatastrophic enco ding circuits [44]. Grassl and R¨ otteler later sho wed that Ollivier and Tillic h’s conditions for a circuit to b e noncatastrophic are too restrictiv e [31 – 33]. They found subco des of quan- tum conv olutional co des that admit noncatastrophic en- co ders. The noncatastrophic enco ders are a sequence of Clifford circuits with finite depth. They developed a for- malism for encapsulating the p erio dic structure of an en- co ding circuit b y decomp osing the enco ding circuit as a set of elementary column operations. Their deco ding cir- cuits are exact inv erses of their enco ding circuits b ecause their deco ding circuits p erform the encoding op erations in reverse order. Definition 2. A finite-depth op er ation tr ansforms every finite-weight stabilizer gener ator to one with finite weight. W e review the finite-depth op erations in the shift- in v arian t Clifford group [31 – 33]. The shift-in v arian t Clif- ford group is an extension of the Clifford group op era- tions mentioned in Section I I A. W e describ e how finite- depth op erations in the shift-inv ariant Clifford group af- fect the binary p olynomial matrix for a co de. Each of the follo wing op erations acts on ev ery frame of a quan- tum conv olutional co de. 1. The sender performs a CNOT from qubit i to qubit j in every frame where qubit j is in a frame de- la yed by k . The effect on the binary p olynomial matrix is to multiply column i by D k and add the result to column j in the “X” matrix and to multi- ply column j by D − k and add the result to column i in the “Z” matrix. 2. A Hadamard on qubit i swaps column i in the “X” matrix with column i in the “Z” matrix. 3. A phase gate on qubit i adds column i from the “X” matrix to column i in the “Z” matrix. 4. A controlled-phase gate from qubit i to qubit j in a frame delay ed by k m ultiplies column i in the “X” matrix by D k and adds the result to column j in the “Z” matrix. It also m ultiples column j in the “X” matrix by D − k and adds the result to column i in the “Z” matrix. 5. A controlled-phase gate from qubit i to qubit i in a frame delay ed by k m ultiplies column i in the “X” matrix by D k + D − k and adds the result to column i in the “Z” matrix. W e use finite-depth op erations extensively in this work, but we employ only the ab o ve Hadamard and CNOT gates because our en tanglement-assisted quan tum con v o- lutional co des hav e the CSS structure. Figure 4 gives an example of an entanglemen t-assisted quantum conv olu- tional co de that employs several finite-depth op erations. The circuit enco des a stream of information qubits with the help of ebits shared b etw een sender and receiver. Multiple CNOT gates can realize an elemen tary col- umn operation as describ ed at the end of Section I I. Sup- p ose the elemen tary column op eration multiplies column i in the “X” matrix by f ( D ) and adds the result to col- umn j . P olynomial f ( D ) is a summation of some finite set { l 1 , . . . , l n } of p o wers of D : f ( D ) = D l 1 + · · · + D l n . W e can realize f ( D ) b y p erforming a CNOT gate from qubit i to qubit j in a frame dela yed by l i for eac h i ∈ { 1 , . . . , n } . IV. CSS ENT ANGLEMENT-ASSISTED QUANTUM CONVOLUTIONAL CODES An en tanglement-assisted quan tum con v olutional co de op erates similarly to a standard quantum conv olutional co de. The main difference is that the sender and receiver share entanglemen t in the form of ebits. An [[ n, k ; c ]] en tanglement-assisted quan tum con volutional c ode en- co des k information qubits p er frame with the help of c ebits and n − k − c ancilla qubits p er frame. Fig- ure 3 highlights the main features of the op eration of an en tanglement-assisted quan tum conv olutional co de. The 9 M easur emen t and R ec o v er y D ec oding U Enc oding Noise | ψ 1 A | ψ 2 A | ψ 3 A U R R D D { F r ame 1 F r ame 3 Φ + B A | 0 A Φ + B A | 0 A Φ + B A | 0 A { { F r ame 2 FIG. 3: (Color online) An entanglemen t-assisted quantum conv olutional co de op erates on a stream of qubits partitioned in to a countable num ber of frames. The sender enco des the frames of information qubits, ancilla qubits, and half of shared ebits with a rep eated, o verlapping enco ding circuit U . The noisy c hannel affects the sender’s enco ded qubits but does not affect the receiv er’s half of the shared ebits. The receiver p erforms ov erlapping measurements on b oth the enco ded qubits and his half of the shared ebits. These measurements produce an error syndrome which the receiv er can pro cess to determine the most lik ely error. The receiver reverses the errors on the noisy qubits from the sender. The final deco ding circuit op erates on all qubits in a frame and recov ers the original stream of information qubits. sender enco des a stream of quan tum information using b oth additional ancillas and ebits. The sender p erforms the enco ding op erations on her qubits only (i.e., not in- cluding the halv es of the ebits in possession of the re- ceiv er). The enco ding op erations ha ve a p erio dic struc- ture so that the same op erations act on qubits in differen t frames and give the co de a memory structure. The sender can p erform these enco ding op erations in an online man- ner as she places more qubits in the unenco ded qubit stream. The sender transmits her enco ded qubits ov er the noisy quantum communication channel. The noisy c hannel do es not affect the receiv er’s half of the shared ebits. The receiv er combines the receiv ed noisy qubits with his half of the ebits and p erforms measurements to diagnose errors that ma y o ccur. These measurements ma y ov erlap on some of the same qubits. The receiver then diagnoses errors using a classical technique such as Viterbi error estimation [43], reverses the errors that the c hannel in tro duces, and finally p erforms an online deco d- ing circuit that outputs the original information qubit stream. Our main theorem b elow allo ws us to import tw o arbitrary classical con volutional co des for use as a CSS entanglemen t-assisted quantum conv olutional co de. Grassl and R¨ otteler w ere the first to construct CSS quan- tum con volutional codes from tw o classical binary con v o- lutional co des that satisfy an orthogonality constraint— the p olynomial parit y chec k matrices H 1 ( D ) and H 2 ( D ) of the tw o classical co des are orthogonal with resp ect to the shifted symplectic pro duct [33]: H 1 ( D ) H T 2 D − 1 = 0 . (12) The resulting symplectic co de has a self-orthogonal parit y-chec k matrix when we join them together using the CSS construction. Our theorem generalizes the work of Grassl and R¨ otteler because w e can imp ort tw o arbi- tr ary classical binary conv olutional co des—the co des do not necessarily hav e to ob ey the self-orthogonality con- strain t. The theorem giv es a direct wa y to compute the amount of entanglemen t that the co de requires. The num b er of ebits required is equal to the rank of a particular matrix deriv ed from the c hec k matrices of the tw o classical co des. It generalizes an earlier theorem that determines the amoun t of en tanglemen t required for an entanglemen t- assisted quantu m blo ck co de [13]. Theorem 1 also pro vides a formula to compute the per- formance parameters of the entanglemen t-assisted quan- tum con volutional co de from the p erformance parame- ters of the t wo classical co des. This formula ensures that high-rate classical con volutional codes produce high- rate en tanglemen t-assisted quan tum conv olutional codes. Our constructions also ensure high p erformance for the “trade-off” and “catalytic” rates b y minimizing the n um- b er of ebits that the co des require. W e b egin the pro of of the theorem in this section and complete it in different wa ys for each of our tw o classes of en tanglement-assisted quan tum con v olutional co des in 10 Sections V and VI I. The pro ofs detail ho w to enco de a stream of information qubits, ancilla qubits, and shared ebits into a co de that has the CSS structure. Theorem 1. L et H 1 ( D ) and H 2 ( D ) b e the r esp e ctive che ck matric es c orr esp onding to nonc atastr ophic, delay- fr e e enc o ders for classic al binary c onvolutional c o des C 1 and C 2 . Supp ose that classic al c o de C i enc o des k i in- formation bits with n bits p er fr ame wher e i = 1 , 2 . The r esp e ctive dimensions of H 1 ( D ) and H 2 ( D ) ar e thus ( n − k 1 ) × n and ( n − k 2 ) × n . Then the r esulting entanglement-assiste d quantum c onvolutional c o de en- c o des k 1 + k 2 − n + c information qubits p er fr ame and is an [[ n, k 1 + k 2 − n + c ; c ]] entanglement-assiste d quan- tum c onvolutional c o de. The c o de r e quir es c ebits p er fr ame wher e c is e qual to the r ank of H 1 ( D ) H T 2 D − 1 . Let us begin the pro of of the abov e theorem b y constructing an en tanglement-assisted quan tum con v olu- tional co de. Consider the following quantum chec k ma- trix in CSS form: H 1 ( D ) 0 0 H 2 ( D ) . (13) W e lab el the ab ov e matrix as a “quan tum chec k matrix” for no w b ecause it do es not necessarily corresp ond to a comm uting stabilizer. The quantum chec k matrix corre- sp onds to a set of Pauli sequences whose error-correcting prop erties are desirable. The follo wing lemma begins the pro of of the abov e the- orem. It details an initial decomp osition of the ab o ve quan tum c hec k matrix for each of our tw o classes of en tanglement-assisted quantum conv olutional co des. Lemma 1. Elementary r ow and c olumn op er ations r elate the quantum che ck matrix in (13) to the fol lowing matrix E ( D ) F ( D ) 0 0 0 0 I 0 . wher e E ( D ) is dimension ( n − k 1 ) × ( n − k 2 ) , F ( D ) is ( n − k 1 ) × k 2 , the identity matrix is ( n − k 2 ) × ( n − k 2 ) , and the nul l matrix on the right is ( n − k 2 ) × k 2 . We give a definition of E ( D ) and F ( D ) in the fol lowing pr o of. Pr o of. The Smith form [44] of H i ( D ) for each i = 1 , 2 is H i ( D ) = A i ( D ) I 0 B i ( D ) , (14) where A i ( D ) is ( n − k i ) × ( n − k i ), the matrix in brac k ets is ( n − k i ) × n , and B i ( D ) is n × n [44]. Let B ia ( D ) b e the first n − k i ro ws of B i ( D ) and let B ib ( D ) b e the last k i ro ws of B i ( D ): B i ( D ) = B ia ( D ) B ib ( D ) . The ( n − k i ) × ( n − k i ) identit y matrix in brac k ets in (14) indicates that the inv ariant factors of H i ( D ) for each i = 1 , 2 are all equal to one [44]. The in v ariant factors are all unit y for b oth chec k matrices b ecause the chec k ma- trices corresp ond to noncatastrophic, delay-free encoders [44]. The matrices A i ( D ) and B i ( D ) are a pro duct of a sequence of elementary row and column op erations re- sp ectiv ely [44]. Prem ultiplying H i ( D ) by A − 1 i ( D ) giv es a chec k ma- trix H 0 i ( D ) for eac h i = 1 , 2. Matrix H 0 i ( D ) is a chec k matrix for co de C i with equiv alen t error-correcting prop- erties as H i ( D ) b ecause ro w operations relate the t wo matrices. This new c heck matrix H 0 i ( D ) is equal to the first n − k i ro ws of matrix B i ( D ): H 0 i ( D ) = B ia ( D ) . The inv ariant factors of H 1 ( D ) H T 2 D − 1 are equiv a- len t to those of H 0 1 ( D ) H 0 T 2 D − 1 b ecause they are re- lated b y row and column op erations [44]: H 1 ( D ) H T 2 D − 1 = A 1 ( D ) H 0 1 ( D ) H 0 T 2 D − 1 A T 2 D − 1 . (15) W e no w decomp ose the ab ov e quan tum c heck matrix in to a basic form using elementary row and column op- erations. The row operations hav e no effect on the error- correcting prop erties of the co de, and the column op era- tions corresp ond to elements of an enco ding circuit. W e later sho w how to incorp orate ebits so that the quantum c heck matrix forms a v alid commuting stabilizer. P erform the row operations in matrices A − 1 i ( D ) for b oth chec k matrices H i ( D ). The quantum chec k matrix b ecomes B 1 a ( D ) 0 0 B 2 a ( D ) . (16) The error-correcting prop erties of the ab o v e generators are equiv alen t to those of the generators in (13) b ecause ro w op erations relate the tw o sets of generators. The matrix B 2 ( D ) corresp onds to a sequence of elemen tary column op erations B 2 ,i ( D ): B 2 ( D ) = B 2 , 1 ( D ) · · · B 2 ,l ( D ) = l Y i =1 B 2 ,i ( D ) . The inv erse matrix B − 1 2 ( D ) is therefore equal to the ab o v e sequence of op erations in reverse order: B − 1 2 ( D ) = B 2 ,l ( D ) · · · B 2 , 1 ( D ) = 1 Y i = l B 2 ,i ( D ) . P erform the elementary column op erations in B − 1 2 ( D ) with CNOT and SW AP gates [31]. The effect of each elemen tary column op eration B 2 ,i ( D ) is to p ostmultiply the “X” matrix by B 2 ,i ( D ) and to p ostm ultiply the “Z” matrix by B T 2 ,i D − 1 . Therefore the effect of all ele- men tary op erations is to p ostm ultiply the “Z” matrix by B T 2 D − 1 b ecause 1 Y i = l B T 2 ,i D − 1 = l Y i =1 B 2 ,i D − 1 ! T = B T 2 D − 1 . 11 The quan tum chec k matrix in (16) b ecomes B 1 a ( D ) B T 2 D − 1 0 0 0 I 0 . (17) Let E ( D ) b e equal to the first n − k 1 ro ws and n − k 2 columns of the “Z” matrix: E ( D ) ≡ B 1 ,a ( D ) B T 2 ,a D − 1 , and let F ( D ) b e equal to the first n − k 1 ro ws and last k 2 columns of the “Z” matrix: F ( D ) ≡ B 1 ,a ( D ) B T 2 ,b D − 1 . The quantum chec k matrix in (17) is then equiv alen t to the follo wing matrix E ( D ) F ( D ) 0 0 0 0 I 0 , (18) where eac h matrix ab o v e has the dimensions stated in the theorem ab o ve. The ab ov e op erations end the initial set of op erations that eac h of our tw o classes of entanglemen t-assisted quan tum con volutional co des emplo ys. W e outline the remaining op erations for each class of co des in what fol- lo ws. V. ENT ANGLEMENT-ASSISTED QUANTUM CONV OLUTIONAL CODES WITH FINITE-DEPTH ENCODING AND DECODING CIR CUITS This section details entanglemen t-assisted quantum con volutional co des in our first class. Co des in the first class admit an enco ding and deco ding circuit that em- plo y finite-depth op erations only . The chec k matrices for co des in this class hav e a prop ert y that allo ws this type of enco ding and deco ding. The following lemma gives the details of this prop ert y , and the pro of outlines how to enco de and deco de this class of en tanglement-assisted quan tum conv olutional co des. Lemma 2. Supp ose the Smith form of H 1 ( D ) H T 2 D − 1 is H 1 ( D ) H T 2 D − 1 = A ( D ) Γ ( D ) 0 0 0 B ( D ) , wher e A ( D ) is an ( n − k 1 ) × ( n − k 1 ) matrix, B ( D ) is an ( n − k 2 ) × ( n − k 2 ) matrix, Γ ( D ) is a diagonal c × c matrix whose entries ar e p owers of D , and the matrix in br ackets has dimension ( n − k 1 ) × ( n − k 2 ) . Then the r esulting entanglement-assiste d quantum c on- volutional c o de has b oth a finite-depth enc o ding and de- c o ding cir cuit. Pr o of. W e b egin the pro of of this theorem by contin uing where the pro of of Lemma 1 ends. The crucial assump- tion for the ab o ve lemma is that the inv ariant factors of H 1 ( D ) H T 2 D − 1 are all p ow ers of D . The Smith form of E ( D ) in (18) therefore b ecomes A − 1 1 ( D ) A ( D ) Γ ( D ) 0 0 0 B ( D ) A − 1 2 ( D ) , b y employing the hypothesis of Lemma 2 and (15). The rank of b oth H 1 ( D ) H T 2 D − 1 and E ( D ) is equal to c . P erform the in verse of the ro w operations in A − 1 1 ( D ) A ( D ) on the first n − k 1 ro ws of the quantum c heck matrix in (18). Perform the inv erse of the column op erations in matrix B ( D ) A − 1 2 ( D ) on the first n − k 2 columns of the quantum c heck matrix in (18). W e ex- ecute these column operations with Hadamard, CNOT, and SW AP gates. These column op erations hav e a cor- resp onding effect on columns in the “X” matrix, but we can exploit the identit y matrix in the last n − k 2 ro ws of the “X” matrix to counteract this effect. W e p erform ro w op erations on the last n − k 2 ro ws of the matrix that act as the in verse of the column op erations, and therefore the quant um chec k matrix in (18) b ecomes Γ ( D ) 0 F 1 ( D ) 0 0 F 2 ( D ) 0 0 0 0 0 0 0 0 0 0 0 0 I 0 0 0 I 0 , where F 1 ( D ) and F 2 ( D ) are the first c and n − k 1 − c resp ectiv e rows of A − 1 ( D ) A 1 ( D ) F ( D ). W e p erform Hadamard and CNOT gates to clear the en tries in F 1 ( D ) in the “Z” matrix ab ov e. The quantum chec k matrix b ecomes Γ ( D ) 0 0 0 0 F 2 ( D ) 0 0 0 0 I 0 0 0 0 0 0 0 I 0 0 0 0 0 . (19) The Smith form of F 2 ( D ) is F 2 ( D ) = A F ( D ) Γ F ( D ) 0 B F ( D ) , where Γ F ( D ) is a diagonal matrix whose en tries are p o w ers of D , A F ( D ) is ( n − k 1 − c ) × ( n − k 1 − c ), and B F ( D ) is k 2 × k 2 . The Smith form of F 2 ( D ) takes this particular form because the original c hec k matrix H 2 ( D ) is noncatastrophic and column op erations with Laurent p olynomials c hange the inv ariant factors only up to p o w- ers of D . P erform row op erations corresp onding to A − 1 F ( D ) on the second set of n − k 1 − c ro ws with F 2 ( D ) in (19). P erform column op erations corresponding to B − 1 F ( D ) on columns n − k 2 + 1 , . . . , n with Hadamard, CNOT, and SW AP gates. The resulting quantum chec k matrix has the follo wing form: Γ ( D ) 0 0 0 0 0 Γ F ( D ) 0 0 0 0 0 0 I 0 0 0 0 0 0 0 0 0 0 I 0 0 0 0 0 0 0 . (20) 12 W e hav e no w completed the decomp osition of the original quantum chec k matrix in (13) for this class of en tanglement-assisted quantum con volutional co des. It is not p ossible to p erform row or column op erations to decomp ose the ab ov e matrix an y further. The problem with the ab o v e quantum chec k matrix is that it do es not form a v alid quantum con volutional co de. The first set of rows with matrix Γ ( D ) are not orthogonal under the shifted symplectic pro duct to the third set of rows with the identit y matrix on the “X” side. Equiv alently , the set of P auli sequences corresp onding to the ab ov e quan- tum chec k matrix do not form a comm uting stabilizer. W e can use entanglemen t shared b etw een sender and re- ceiv er to solv e this problem. Entanglemen t adds columns to the ab ov e quantum chec k matrix to resolve the issue. The additional columns corresp ond to qubits on the re- ceiv er’s side. W e next show in detail how to incorp orate ancilla qubits, ebits, and information qubits to obtain a v alid stabilizer code. The result is that w e can exploit the error-correcting prop erties of the original co de to protect the sender’s qubits. Consider the follo wing chec k matrix corresp onding to a commuting stabilizer: I I 0 0 0 0 0 0 I 0 0 0 0 0 0 0 0 I 0 0 0 0 0 0 0 0 0 0 0 0 I I 0 0 0 0 0 0 0 0 , (21) where the identit y matrices in the first and third sets of rows each hav e dimension c × c , the identit y matrix in the second set of rows has dimension ( n − k 1 − c ) × ( n − k 1 − c ), and the identit y matrix in the fourth set of rows has dimension ( n − k 2 − c ) × ( n − k 2 − c ). The first and third sets of c ro ws stabilize a set of c ebits shared b etw een Alice and Bob. Bob p ossesses the “left” c qubits and Alice p ossesses the “right” n qubits. The second and fourth sets of ro ws stabilize a set of 2 ( n − c ) − k 1 − k 2 ancilla qubits that Alice p ossesses. The stabilizer therefore stabilizes a set of c ebits, 2 ( n − c ) − k 1 − k 2 ancilla qubits, and k 1 + k 2 − n + c information qubits. Observ e that the last n columns of the “Z” and “X” matrices in the ab ov e stabilizer are similar in their lay out to the en tries in (20). W e can dela y the ro ws of the ab o ve stabilizer by an arbitrary amount to obtain the desired stabilizer. So the ab ov e stabilizer is a sub co de of the follo wing stabilizer in the sense of Ref. [31]: Γ ( D ) Γ ( D ) 0 0 0 0 0 0 Γ F ( D ) 0 0 0 0 0 0 0 0 I 0 0 0 0 0 0 0 0 0 0 0 0 I I 0 0 0 0 0 0 0 0 . The stabilizer in (21) has equiv alen t error-correcting prop erties to and the same asymptotic rate as the ab ov e desired stabilizer. The ab o v e stabilizer matrix is an aug- men ted version of the quan tum chec k matrix in (20) that includes entanglemen t. The sender p erforms all of the enco ding column op erations detailed in the pro ofs of this lemma and Lemma 1 in reverse order. The result of these op erations is an [[ n, k 1 + k 2 − n + c ; c ]] entanglemen t- assisted quantum conv olutional co de with the same error- correcting properties as the quantum c hec k matrix in (13). The receiv er decodes the original information-qubit stream by p erforming the column op erations in the or- der presented. The information qubits app ear as the last k 1 + k 2 − n + c in each frame of the stream (corresponding to the k 1 + k 2 − n + c columns of zeros in b oth the “Z” and “X” matrices ab o ve). Example 1. Consider a classic al c onvolutional c o de with the fol lowing che ck matrix: H ( D ) = 1 + D 2 1 + D + D 2 . We c an use H ( D ) in an entanglement-assiste d quantum c onvolutional c o de to c orr e ct for b oth bit-flip err ors and phase-flip err ors. We form the fol lowing quantum che ck matrix: 1 + D 2 1 + D + D 2 0 0 0 0 1 + D 2 1 + D + D 2 . (22) This c o de fal ls in the first class of entanglement- assiste d quantum c onvolutional c o des b e c ause H ( D ) H T D − 1 = 1 . We do not show the de c omp osition of the ab ove che ck matrix as outline d in L emma 2, but inste ad show how to enc o de it starting fr om a str e am of information qubits and ebits. Each fr ame has one ebit and one information qubit. L et us b e gin with a p olynomial matrix that stabilizes the unenc o de d state: 1 1 0 0 0 0 0 0 0 1 1 0 . A lic e p ossesses the two qubits on the “right” and Bob p os- sesses the qubit on the “left.” We lab el the midd le qubit as “qubit one” and the rightmost qubit as “qubit two.” A lic e p erforms a CNOT fr om qubit one to qubit two in a delaye d fr ame and a CNOT fr om qubit one to qubit two in a fr ame delaye d by two. The stabilizer b e c omes 1 1 0 0 0 0 0 0 0 1 1 D + D 2 . A lic e p erforms Hadamar d gates on b oth of her qubits. The stabilizer b e c omes 1 0 0 0 1 D + D 2 0 1 0 1 0 0 . A lic e p erforms a CNOT fr om qubit one to qubit two in a delaye d fr ame. The stabilizer b e c omes 1 0 0 0 D D + D 2 0 1 D 1 0 0 . 13 | ψ 1 A | ψ 2 A | ψ 3 A | ψ 4 A | ψ 5 A | ψ 6 A | Φ + B A | Φ + B A | Φ + B A | Φ + B A | Φ + B A | Φ + B A { { { { { { F r ame 1 F r ame 2 F r ame 3 F r ame 4 F r ame 5 F r ame 6 H H H H H H H H H H H H FIG. 4: (Color online) The finite-depth encoding circuit for the en tanglement-assisted quan tum con v olutional co de in Ex- ample 1. The ab ov e op erations in reverse order give a v alid deco ding circuit. A lic e p erforms a CNOT fr om qubit two to qubit one in a delaye d fr ame. The stabilizer b e c omes 1 0 0 0 D 1 + D + D 2 0 1 + D 2 D 1 0 0 . A lic e p erforms a CNOT fr om qubit one to qubit two. The stabilizer b e c omes 1 0 0 0 1 + D 2 1 + D + D 2 0 1 + D 2 1 + D + D 2 1 0 0 . A r ow op er ation that switches the first r ow with the se c- ond r ow gives the fol lowing stabilizer: 0 1 + D 2 1 + D + D 2 1 0 0 1 0 0 0 1 + D 2 1 + D + D 2 . The entries on Alic e’s side of the ab ove stabilizer have e quivalent err or-c orr e cting pr op erties to the quantum che ck matrix in (22). Figur e 4 il lustr ates how the ab ove op er ations enc o de a str e am of ebits and information qubits for our example. 4. Discussion Co des in the first class are more useful in practice than those in the second b ecause their enco ding and deco ding circuits are finite depth. An uncorrected error propa- gates only to a finite n umber of information qubits in the deco ded qubit stream. Co des in the first class therefore do not require any assumptions ab out noiseless enco ding or deco ding. The assumption ab out the inv ariant factors in the Smith form of H 1 ( D ) H T 2 D − 1 holds only for some clas- sical chec k matrices. Only a sub class of classical co des satisfy this assumption, but it still expands the set of a v ailable quantum co des b ey ond those whose chec k ma- trices H 1 ( D ) and H 2 ( D ) are orthogonal. W e need fur- ther techniques to handle the classical co des for which this assumption does not hold. The follo wing sections pro vide these further tec hniques to handle a larger class of en tanglement-assisted quantum conv olutional co des. VI. INFINITE-DEPTH CLIFFORD OPERA TIONS W e now in troduce a new t yp e of op eration, an infinite- depth op eration, to the set of op erations in the shift- in v arian t Clifford group a v ailable for enco ding and de- co ding quantum conv olutional co des. W e require infinite- depth op erations to expand the set of classical conv olu- tional codes that we can imp ort for quan tum con volu- tional co ding. Definition 3. An infinite-depth op er ation c an tr ansform a finite-weight stabilizer gener ator to one with infinite weight (but do es not ne c essarily do so to every finite- weight gener ator). A deco ding circuit with infinite-depth op erations on qubits sent ov er the noisy channel is undesirable b ecause it spreads uncorrected errors infinitely into the deco ded information qubit stream. But an enco ding circuit with infinite-depth operations is acceptable if we assume a comm unication paradigm in which the only noisy pro- cess is the noisy quantum channel. W e later sho w several examples of circuits that include infinite-depth op erations. Infinite-depth operations ex- pand the p ossibilities for quantum con volutional circuits in muc h the same w ay that incorporating feedbac k ex- pands the possibilities for classical conv olutional circuits. W e illustrate the details of several infinite-depth op er- ations for use in an entanglemen t-assisted quantum con- v olutional co de. W e first pro vide some sp ecific examples of infinite-depth op erations and then show ho w to realize an arbitrary infinite-depth op eration. W e consider b oth the stabilizer and the logical op era- tors for the information qubits in our analysis. T racking b oth of these sets of generators is necessary for determin- ing the proper deco ding circuit when including infinite- depth op erations. 14 A. Examples of Infinite-Depth Op erations Our first example of an infinite-depth op eration in- v olves a stream of information qubits and ancilla qubits. W e divide the stream into frames of three qubits where eac h frame has t wo ancilla qubits and one information qubit. The following t w o generators and each of their three-qubit shifts stabilize the qubit stream: · · · I I I I I I Z I I I Z I I I I I I I · · · (23) The binary p olynomial matrix c orresponding to this sta- bilizer is as follows: 1 0 0 0 1 0 0 0 0 0 0 0 . (24) W e obtain any Pauli sequence in the stabilizer by m ulti- plying the ab ov e rows by a p ow er of D and applying the in verse of the P2B isomorphism. The logical op erators for the information qubits are as follows: · · · I I I I I I I I X I I Z I I I I I I · · · They also admit a description with a binary p olynomial matrix: 0 0 0 0 0 1 0 0 1 0 0 0 . (25) W e refer to the ab ov e matrix as the “information-qubit matrix.” 1. Enc o ding Supp ose we would like to enco de the ab ov e stream so that the following generators stabilize it: · · · I I I I I I X X X Z Z I X X I I I I · · · , or equiv alen tly , the following binary p olynomial matrix stabilizes it: 0 0 0 1 1 0 D + 1 D + 1 1 0 0 0 . (26) W e enco de the ab ov e stabilizer using a combination of finite-depth op erations and an infinite-depth op eration. W e p erform a Hadamard on the first qubit in eac h frame and follo w with a CNOT from the first qubit to the sec- ond and third qubits in each frame. These op erations transform the matrix in (24) to the following matrix 0 0 0 1 1 0 1 1 1 0 0 0 , { { { { { { Frame 1 Frame 2 Frame 3 Frame 4 Frame 5 Frame 6 FIG. 5: An example of an infinite-depth operation. A se- quence of CNOT gates acts on the third qubit of every frame. This infinite-depth op eration effectiv ely m ultiplies the third column of the “X” side of the binary p olynomial matrix b y the rational polynomial 1 / (1 + D ) and multiplies the third column of the “Z” side of the binary p olynomial matrix b y 1 + D − 1 . or equiv alen tly transform the generators in (23) to the follo wing generators: · · · I I I I I I X X X Z Z I I I I I I I · · · The information-qubit matrix b ecomes 0 0 0 1 0 1 0 0 1 0 0 0 . W e now p erform an infinite-depth op eration: a CNOT from the third qubit in one frame to the third qubit in a delay ed frame and rep eat this op eration for all follow- ing frames. Figure 5 shows this op eration acting on our stream of qubits with three qubits p er frame. The ef- fect of this op eration is to translate the ab ov e stabilizer generators as follows: · · · I I I I I I X X X Z Z I I I X I I I I I X I I I · · · The first generator abov e and each of its three-qubits shifts is an infinite-w eight generator if the ab o ve sequence of CNOTs acts on the en tire coun tably-infinite qubit stream. W e represent the ab o ve stabilizer with the bi- nary r ational p olynomial matrix 0 0 0 1 1 0 1 1 1 / (1 + D ) 0 0 0 , (27) 15 where 1 / (1 + D ) = 1 + D + D 2 + . . . is a rep eating frac- tion. The op eration is infinite-depth because it translates the original finite-w eight stabilizer generator to one with infinite w eight. It is p ossible to p erform a row op eration that multi- plies the first row by D + 1. This op eration gives a sta- bilizer matrix that is equiv alent to the desired stabilizer in (26). The receiver of the enco ded qubits measures the finite-w eight stabilizer generators in (26) to diagnose er- rors. These measuremen ts do not disturb the information qubits b ecause they also stabilize the enco ded stream. The ab o v e enco ding op erations transform the information-qubit matrix as follows: 0 0 0 1 0 1 + D − 1 0 0 1 / (1 + D ) 0 0 0 . (28) The infinite-depth op eration on the third qubit has an effect on the “Z” or left side of the information-qubit matrix as illustrated in the second row of the ab ov e ma- trix. The effect is to multiply the third column of the “Z” matrix by f D − 1 if the op eration multiplies the third column of the “X” matrix by 1 /f ( D ). This cor- resp onding action on the “Z” side o ccurs b ecause the comm utation relations of the Pauli op erators remain in- v arian t under quantum gates, or equiv alen tly , the shifted symplectic pro duct remains in v arian t under column op- erations. The original shifted symplectic pro duct for the logical op erators is one, and it remains as one b ecause f (( D − 1 ) − 1 ) /f ( D ) = 1. 2. De c o ding W e p erform finite-depth op erations to deco de the stream of information qubits. Begin with the stabilizer and information-qubit matrix in (27) and (28) resp ec- tiv ely . P erform a CNOT from the first qubit to the sec- ond qubit. The stabilizer b ecomes 0 0 0 0 1 0 1 0 1 / (1 + D ) 0 0 0 , and the information-qubit matrix do es not change. P er- form a CNOT from the third qubit to the first qubit in the same frame and in a dela yed frame. These gates m ultiply column three in the “X” matrix by 1 + D and add the result to column one. The gates also multiply column one in the “Z” matrix by 1 + D − 1 and add the result to column three. The effect is as follows on b oth the stabilizer 0 0 0 0 1 0 0 0 1 / (1 + D ) 0 0 0 , (29) and the information-qubit matrix 0 0 0 1 0 0 1 0 1 / (1 + D ) 0 0 0 . (30) W e can m ultiply the logical op erators by an y element of the stabilizer and obtain an equiv alent logical op era- tor [4]. W e p erform this multiplication in the “binary- p olynomial picture” by adding the first row of the sta- bilizer in (29) to the first row of (30). The information- qubit matrix b ecomes 0 0 0 1 0 0 1 0 0 0 0 0 , (31) so that the resulting logical op erators act only on the first qubit of every frame. W e hav e successfully deco ded the information qubits with finite-depth op erations. The information qubits telep ort coheren tly [45, 46] from b e- ing the third qubit of each frame as in (25) to b eing the first qubit of each frame as in (31). W e exploit the ab o v e metho d of enco ding with infinite-depth op erations and deco ding with finite-depth op erations for the class of en tanglement-assisted quan tum con v olutional co des in Section VI I. B. General Infinite-Depth Op erations W e discuss the action of a general infinite-depth op- eration on tw o weigh t-one “X” and “Z” Pauli sequences where each frame has one Pauli matrix. Our analysis then determines the effect of an infinite-depth op eration on an arbitrary stabilizer or information-qubit matrix. The generators in the “Pauli picture” are as follows: · · · I I X Z I I · · · , (32) or as follows in the “binary-p olynomial picture”: 0 1 1 0 . An infinite-depth 1 /f ( D ) op eration, where f ( D ) is an arbitrary polynomial, should transform the abov e matrix to the following one: 0 f D − 1 1 /f ( D ) 0 . A circuit that p erforms this transformation preserv es the shifted symplectic pro duct b ecause f D − 1 · 1 /f D − 1 = 1. The circuit should op erate on a few qubits at a time and should b e shift-inv ariant—the same device or physical routines implement it. First p erform the long division expansion of binary ra- tional polynomial 1 /f ( D ). This expansion has a particu- lar rep eating pattern with p erio d l . F or example, supp ose that f ( D ) = 1 + D + D 3 . Its long-division expansion is 1 + D + D 2 + D 4 + D 7 + D 8 + D 9 + D 11 + . . . and exhibits a rep eating pattern with p eriod seven. W e wan t a circuit that realizes the following Pauli generators · · · I Z I I I Z X Z X I X I I I X I I I · · · , (33) 16 where the pattern in the X matrices is the same as the rep eating p olynomial 1 /f ( D ) and contin ues infinitely to the right, and the pattern on the Z matrices is the same as that in f D − 1 and terminates at the left. The ab o v e P auli sequence is equiv alen t to the following binary ra- tional p olynomial matrix: 0 1 + D − 1 + D − 3 1 / 1 + D + D 3 0 . W e now discuss a metho d that realizes an arbitrary rational p olynomial 1 /f ( D ) as an infinite-depth op era- tion. Our metho d for enco ding the generators in (33) from those in (32) consists of a “sliding-windo w” tech- nique that determines transformation rules for the cir- cuit. The circuit is an additive, shift-in v arian t filtering op eration. It resembles an infinite-impulse resp onse fil- ter b ecause the sequence it pro duces extends infinitely . In general, the num ber N of qubits that the enco ding unitary op erates on is as follows N = deg ( f ( D )) − del ( f ( D )) + 1 , where deg ( f ( D )) and del ( f ( D )) are the resp ectiv e high- est and lo west p ow ers of p olynomial f ( D ). Therefore, our exemplary enco ding unitary op erates on four qubits at a time. W e delay the original sequence in (32) by three frames. These initial frames are “scratch” frames that give the enco ding unitary enough “ro om” to gener- ate the desired Paulis in (33). The first set of transfor- mation rules is as follows I I I I I I X Z → I Z I I I Z X Z , (34) and generates the first four elemen ts of the pattern in (33). No w that the enco ding unitary has acted on the first four frames, we need to shift our ey es to the right b y one frame in the sequence in (33) to determine the next set of rules. So we shift the ab o ve outputs by one frame to the left (assuming that only identit y matrices lie to the right) and determine the next set of transformation rules that generate the next elements of the sequence in (33): I I I Z X Z I I → I I I Z X Z X I . Shift the ab ov e outputs to the left by one frame to de- termine the next set of transformation rules: I Z X Z X I I I → I Z X Z X I X I . W e obtain the rest of the transformation rules by con tin- uing this sliding pro cess, and we stop when the pattern in the sequence in (33) b egins to rep eat: X Z X X I X X I X I X I X I I X I I I I I I I I → X Z X X I X X I X I X I X I I X I I I I X I I X . { F rame 1 F rame 2 F rame 3 F rame 4 F rame 5 F rame 6 { { { { { { { F rame 7 F rame 8 FIG. 6: Another example of an infinite-depth op eration. An infinite-depth op eration acts on qubit i in every frame. This particular infinite-depth op eration multiplies column i on the “X” side of the binary p olynomial matrix b y 1 / 1 + D + D 3 and multiplies column i on the “Z” side of the binary p oly- nomial matrix by 1 + D − 1 + D − 3 . The ab o ve set of rules determines the enco ding uni- tary and only a few of them are actually necessary . W e can multiply the rules together to form equiv alent rules because the circuit obeys additivit y (in the “binary- p olynomial picture”). The rules b ecome as follows after rearranging in to a standard form: Z I I I X I I I I Z I I I X I I I I Z I I I X I I I I Z I I I X → Z I I Z X I I I I Z I I I X I I I I Z Z I I X I I I I Z X I X X . A CNOT from qubit one to qubit four and a CNOT from qubit three to qubit four suffice to implemen t this cir- cuit. W e rep eatedly apply these op erations shifting by one frame at a time to implement the infinite-depth op- eration. W e could hav e observed that these gates suffice to implement the “Z” transformation in the first set of transformation rules in (34), but we wan ted to show ho w this metho d generates the full perio dic “X” sequence in (33). Figure 6 shows how the abov e enco ding unitary acts on a stream of quantum information. W e can determine the enco ding unitary for an ar- bitrary rational p olynomial 1 /f ( D ) using a similar metho d. Supp ose that del ( f ( D )) = n and supp ose n 6 = 0 as in the ab ov e case. First delay or adv ance the frames if n > 0 or if n < 0 resp ectiv ely . Determine the CNOT 17 gates that transform the “Z” Pauli sequence 1 0 to D n f D − 1 0 . These CNOT gates form the enco ding circuit that trans- form b oth the “X” and “Z” Pauli sequences. W e p er- form the enco ding unitary , shift by one frame, p erform it again, and keep rep eating. Our metho d enco des any ar- bitrary p olynomial 1 /f ( D ) on the “X” side and f D − 1 on the “Z” side. W e can implemen t the “time-reversed” p olynomial 1 /f D − 1 on the “X” side by first delaying the frames b y m = deg ( f ( D )) − del ( f ( D )) frames and p erform- ing the circuit corresp onding to 1 /D m f D − 1 . These op erations implement the circuit D m /D m f D − 1 = 1 /f D − 1 . C. Infinite-Depth Op erations in Practice W e assume ab o ve that each of the infinite-depth op- erations acts on the entire countably-infinite stream of qubits. In practice, each infinite-depth op eration acts on a finite n umber of qubits at a time so that the enco d- ing and deco ding circuits op erate in an “online” manner. Therefore, eac h infinite-depth op eration appro ximates its corresp onding rational p olynomial. This approximation do es not pose a barrier to implementation. W e can im- plemen t eac h of the ab ov e infinite-depth operations by padding the initial qubits of the information qubit stream with some “scratch” qubits. W e first transmit these “scratc h” qubits that contain no useful quantum infor- mation so that the later information qubits enjoy the full protection of the co de. These scratch qubits do not affect the asymptotic rate of the code and merely serve as a con- v enience for implementing the infinite-depth op erations. F rom now on, we adhere to describing infinite-depth op- erations with binary rational p olynomials b ecause it is more conv enien t to do so mathematically . D. En tanglement-Assisted Quan tum Conv olutional Co des with Infinite-Depth Op erations In the section that follows, our en tanglement-assisted quan tum conv olutional co des hav e infinite-depth op era- tions in their enco ding circuits. This p ossibility is ac- ceptable b ecause the entanglemen t-assisted communica- tion paradigm assumes that noiseless encoding is p ossible and that the receiver’s half of the ebits are noiseless. W e later briefly discuss the effects of relaxing this assumption in a realistic system. Our deco ding circuits in the second class of co des per- form finite-depth op erations. Some of our deco ding cir- cuits are not the exact inv erse of their corresp onding en- co ding circuits, but the deco ding circuits in v ert the effect of the encoding circuits because they pro duce the original stream of information qubits at their output. VI I. ENT ANGLEMENT-ASSISTED QUANTUM CONV OLUTIONAL CODES WITH INFINITE-DEPTH ENCODING AND FINITE-DEPTH DECODING CIRCUITS This section details co des whose enco ding circuits hav e b oth infinite-depth and finite-depth op erations. W e therefore assume that enco ding is noiseless to eliminate the possibility of enco ding errors spreading infinitely in to the enco ded qubit stream. Their deco ding circuits re- quire finite-depth op erations only . Just as with the previous class, this class of co des is determined by the properties of their corresp onding clas- sical c hec k matrices, as described in the following lemma. Lemma 3. Supp ose the Smith form of E ( D ) do es not admit the form fr om L emma 2. Then the entanglement- assiste d quantum c onvolutional c o de has an enc o ding cir- cuit with b oth infinite-depth and finite-depth op er ations. Its de c o ding cir cuit has finite-depth op er ations. Pr o of. W e p erform all of the op erations from Lemma 1. The Smith form of E ( D ) is in general as follows A E ( D ) Γ 1 ( D ) 0 0 0 Γ 2 ( D ) 0 0 0 0 B E ( D ) , where A E ( D ) is ( n − k 1 ) × ( n − k 1 ), Γ 1 ( D ) is an s × s diagonal matrix whose entries are pow ers of D , Γ 2 ( D ) is a ( c − s ) × ( c − s ) diagonal matrix whose entries are arbitrary polynomials, and B E ( D ) is ( n − k 2 ) × ( n − k 2 ). P erform the ro w op erations in A − 1 E ( D ) and the column op erations in B − 1 E ( D ) on the quantum chec k matrix in (18). Counteract the effect of the column op erations on the identit y matrix in the “X” matrix by p erforming row op erations. The quantum chec k matrix in (18) b ecomes Γ 1 ( D ) 0 0 F 1 ( D ) 0 Γ 2 ( D ) 0 F 2 ( D ) 0 0 0 F 3 ( D ) 0 0 0 0 0 0 0 0 0 0 I 0 , where F 1 ( D ), F 2 ( D ), and F 3 ( D ) are the resp ectiv e s , c − s , and n − k 1 − c rows of A − 1 E ( D ) F ( D ). The Smith form of F 3 ( D ) is as follo ws F 3 ( D ) = A F 3 ( D ) Γ F 3 ( D ) 0 B F 3 ( D ) , where A F 3 ( D ) is ( n − k 1 − c ) × ( n − k 1 − c ), Γ F 3 ( D ) is an ( n − k 1 − c ) × ( n − k 1 − c ) diagonal matrix whose en- tries are pow ers of D , and B F 3 ( D ) is k 2 × k 2 . The en tries of Γ F 3 ( D ) are p ow ers of D b ecause the original chec k ma- trix H 2 ( D ) is noncatastrophic and column and ro w op- erations with Lauren t p olynomials change the inv ariant factors only by a pow er of D . P erform the row op erations 18 in A − 1 F 3 ( D ) and the column op erations in B − 1 F 3 ( D ). The quan tum chec k matrix b ecomes Γ 1 ( D ) 0 0 F 0 1 a ( D ) F 0 1 b ( D ) 0 Γ 2 ( D ) 0 F 0 2 a ( D ) F 0 2 b ( D ) 0 0 0 Γ F 3 ( D ) 0 0 0 0 0 0 0 0 0 0 0 0 I 0 , where F 0 1 a ( D ), F 0 1 b ( D ), F 0 2 a ( D ), F 0 2 b ( D ) are the matrices resulting from the column op erations in B − 1 F 3 ( D ). Per- form row op erations from the entries in Γ F 3 ( D ) to the ro ws ab ov e it to clear the entries in F 0 1 a ( D ) and F 0 2 a ( D ). Use Hadamard and CNOT gates to clear the entries in F 0 1 b ( D ). The quantum chec k matrix b ecomes Γ 1 ( D ) 0 0 0 0 0 Γ 2 ( D ) 0 0 F 0 2 b ( D ) 0 0 0 Γ F 3 ( D ) 0 0 0 0 0 0 0 0 0 0 0 0 I 0 . W e can reduce F 0 2 b ( D ) to a low er triangular form with an algorithm consisting of column op erations only . The algorithm op erates on the last k 2 + k 1 − n + c columns. It is similar to the Smith algorithm but does not in v olv e ro w op erations. Consider the first ro w of F 0 2 b ( D ). P erform column op erations b etw een the different elements of the ro w to reduce it to one non-zero entry . Swap this non- zero en try to the leftmost p osition. Perform the same algorithm on elements 2 , . . . , k 2 + k 1 − n + c of the second ro w. Con tin ue on for all ro ws of F 0 2 b ( D ) to reduce it to a matrix of the following form F 0 2 b ( D ) → c − s z }| { L ( D ) k 1 + k 2 − n + s z}|{ 0 , where L ( D ) is a low er triangular matrix. The ab ov e quan tum chec k matrix b ecomes Γ 1 ( D ) 0 0 0 0 0 0 Γ 2 ( D ) 0 0 L ( D ) 0 0 0 0 Γ F 3 ( D ) 0 0 0 0 0 0 0 0 0 0 0 0 0 0 I 0 . W e hav e completed decomp osition of the first set of s ro ws with Γ 1 ( D ), the third set of n − k 1 − c rows with Γ F 3 ( D ), and ro ws n − k 1 + 1 , . . . , n − k 1 + s with the iden tity matrix on the “X” side. W e now consider an algorithm with infinite-depth op- erations to enco de the following submatrix of the abov e quan tum chec k matrix: Γ 2 ( D ) L ( D ) 0 0 0 0 I 0 . (35) W e b egin with a set of c − s ebits and c − s information qubits. The following matrix s tabilizes the ebits I I 0 0 0 0 0 0 0 I I 0 , and the following matrix represen ts the information qubits 0 0 I 0 0 0 0 0 0 0 0 I , where all matrices hav e dimension ( c − s ) × ( c − s ) and Bob p ossesses the c − s qubits on the “left” and Alice p ossesses the 2 ( c − s ) qubits on the “right.” W e track b oth the stabilizer and the information qubits as they progress through some enco ding op erations. Alice p er- forms CNOT and Hadamard gates on her 2 ( c − s ) qubits. These gates multiply the middle c − s columns of the “Z” matrix by L ( D ) and add the result to the last c − s columns and multiply the last c − s columns of the “X” matrix b y L T D − 1 and add the result to the middle c − s columns. The stabilizer b ecomes I I L ( D ) 0 0 0 0 0 0 I I 0 , and the information-qubit matrix b ecomes 0 0 I 0 0 0 0 0 0 0 L T D − 1 I . Alice performs infinite-depth operations on her first c − s qubits corresp onding to the rational p olynomials γ − 1 2 , 1 D − 1 , . . . , γ − 1 2 ,c − s D − 1 in Γ − 1 2 D − 1 . The stabi- lizer matrix b ecomes I Γ 2 ( D ) L ( D ) 0 0 0 0 0 0 I Γ − 1 2 D − 1 0 , and the information-qubit matrix b ecomes 0 0 I 0 0 0 0 0 0 0 L T D − 1 Γ − 1 2 D − 1 I . Alice’s part of the ab ov e stabilizer matrix is equiv alent to the quan tum c heck matrix in (35) by row op erations (prem ultiplying the second set of rows in the stabilizer b y Γ 2 ( D ).) Bob can therefore mak e stabilizer measuremen ts that hav e finite w eight and that are equiv alen t to the desired stabilizer. W e no w describ e a method to deco de the ab o ve en- co ded stabilizer and information-qubit matrix so that the information qubits app ear at the output of the deco ding circuit. Bob p erforms Hadamard gates on his first and third sets of c − s qubits, p erforms CNOT gates from the first set of qubits to the third set of qubits corresp ond- ing to the entries in L ( D ), and p erforms the Hadamard gates again. The stabilizer b ecomes I Γ 2 ( D ) 0 0 0 0 0 0 0 I Γ − 1 2 D − 1 0 , (36) and the information-qubit matrix b ecomes 0 0 I 0 0 0 0 0 0 L T D − 1 L T D − 1 Γ − 1 2 D − 1 I . 19 Bob finishes deco ding at this p oint b ecause w e can equiv- alen tly express the information-qubit matrix as follo ws 0 0 I 0 0 0 0 0 0 0 0 I , b y multiplying the last c − s rows of the stabilizer by L T D − 1 and adding to the last c − s ro ws of the information-qubit matrix. The ov erall pro cedure for enco ding is to b egin with a set of c ebits, 2 ( n − c ) − k 1 − k 2 ancilla qubits, and k 1 + k 2 − n + c information qubits. W e p erform the infinite- depth op erations detailed in the paragraph with (35) for c − s of the ebits. W e then p erform the finite-depth op er- ations detailed in the pro ofs of this lemma and Lemma 1 in reverse order. The resulting stabilizer has equiv alen t error-correcting prop erties to the quantum chec k matrix in (13). The receiv er deco des b y first p erforming all of the finite-depth op erations in the enco ding circuit in reverse order. The receiver then deco des the infinite-depth op er- ations b y the pro cedure listed in the paragraph with (36) so that the original k 1 + k 2 − n + c information qubits p er frame are a v ailable for pro cessing at the receiving end. A. Sp ecial Case of Entanglemen t-Assisted Co des with Infinite-Depth Enco ding Circuits and Finite-Depth Deco ding Circuits W e now detail a sp ecial case of the ab o ve co des in this final section. These co des are interesting b ecause the information qubits teleport coheren tly to other physical qubits when enco ding and deco ding is complete. Lemma 4. Supp ose that the Smith form of F ( D ) in (18) is F ( D ) = A F ( D ) Γ F ( D ) 0 B F ( D ) , wher e A F ( D ) is ( n − k 1 ) × ( n − k 1 ) , Γ F ( D ) is an ( n − k 1 ) × ( n − k 1 ) diagonal matrix whose entries ar e p owers of D , and B F ( D ) is k 2 × k 2 . Then the r esult- ing entanglement-assiste d c o de admits an enc o ding cir- cuit with b oth infinite-depth and finite-depth op er ations and admits a de c o ding cir cuit with finite-depth op er ations only. The information qubits also telep ort c oher ently to other physic al qubits for this sp e cial c ase of c o des. Pr o of. W e p erform all the op erations in Lemma 1 to ob- tain the quan tum chec k matrix in (18). Then p erform the ro w op erations in A − 1 F ( D ) and the column op erations in B − 1 F ( D ). The quantum chec k matrix b ecomes E 0 ( D ) Γ F ( D ) 0 0 0 0 0 0 0 I 0 0 , where E 0 ( D ) = A − 1 F ( D ) E ( D ). The Smith form of E 0 ( D ) is E 0 ( D ) = A E 0 ( D ) Γ 1 ( D ) 0 0 0 Γ 2 ( D ) 0 0 0 0 B E 0 ( D ) , where A E 0 ( D ) is ( n − k 1 ) × ( n − k 1 ), Γ 1 ( D ) is an s × s diagonal matrix whose entries are pow ers of D , Γ 2 ( D ) is a ( c − s ) × ( c − s ) diagonal matrix whose entries are arbitrary p olynomials, and B E 0 ( D ) is ( n − k 2 ) × ( n − k 2 ). No w p erform the row op erations in A − 1 E 0 ( D ) and the column op erations in B − 1 E 0 ( D ). It is p ossible to counter- act the effect of the ro w operations on Γ F ( D ) by p er- forming column op erations, and it is p ossible to coun ter- act the effect of the column op erations on the identit y matrix in the “X” matrix by p erforming row op erations. The quan tum chec k matrix b ecomes Γ 1 0 0 Γ 0 1 0 0 0 0 Γ 2 0 0 Γ 0 2 0 0 0 0 0 0 0 Γ 0 3 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 I 0 0 , where Γ 0 1 , Γ 0 2 , and Γ 0 3 represen t the resp ective s × s , ( c − s ) × ( c − s ), and ( n − k 1 − c ) × ( n − k 1 − c ) diag- onal matrices resulting from counteracting the effect of ro w op erations A − 1 E 0 ( D ) on Γ F ( D ). (W e suppress the D argumen t in all of the matrices in the ab ov e equation.) W e use Hadamard and CNOT gates to clear the entries in Γ 0 1 ( D ). The quantum chec k matrix b ecomes Γ 1 0 0 0 0 0 0 0 Γ 2 0 0 Γ 0 2 0 0 0 0 0 0 0 Γ 0 3 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 I 0 0 . The first s rows with Γ 1 and rows n − k 1 − c + 1 , . . . , n − k 1 − c + s with the identit y matrix on the “X” side stabilize a set of s ebits. The n − k 1 − c ro ws with Γ 0 3 and the n − k 2 − c ro ws with identit y in the “X” matrix stabilize a set of 2 ( n − c ) − k 1 − k 2 ancilla qubits (up to Hadamard gates). The s and k 2 − n + k 1 columns with zeros in b oth the “Z” and “X” matrices corresp ond to information qubits. The decomp osition of these ro ws is now complete. W e need to finish processing the c − s rows with Γ 2 ( D ) and Γ 0 2 ( D ) as en tries and the c − s rows of the iden tit y in the “X” matrix. W e construct a submatrix of the ab ov e quan tum chec k matrix: Γ 2 ( D ) Γ 0 2 ( D ) 0 0 0 0 I 0 . (37) W e describ e a pro cedure to enco de the ab ov e en tries with c − s ebits and c − s information qubits using infinite- depth op erations. Consider the following stabilizer ma- trix I I 0 0 0 0 0 0 0 I I 0 , (38) 20 where all identit y and null matrices are ( c − s ) × ( c − s ). The ab ov e matrix stabilizes a set of c − s ebits and c − s information qubits. Bob’s half of the ebits are the c − s columns on the left in both the “Z” and “X” matrices and Alice’s half are the next c − s columns. W e also trac k the logical op erators for the information qubits to v erify that the circuit encodes and deco des properly . The information-qubit matrix is as follows 0 0 I 0 0 0 0 0 0 0 0 I , (39) where all matrices are again ( c − s ) × ( c − s ). Alice p er- forms Hadamard gates on her first c − s qubits and then p erforms CNOT gates from her first c − s qubits to her last c − s qubits to transform (38) to the following stabi- lizer I 0 0 0 I 0 0 I Γ 0 2 ( D ) I 0 0 . The information-qubit matrix in (39) b ecomes 0 Γ 0 2 D − 1 I 0 0 0 0 0 0 0 0 I . Alice then p erforms infinite-depth op erations on her last c − s qubits. These infinite-depth operations corre- sp ond to the elements of Γ − 1 2 ( D ). She finally performs Hadamard gates on her 2 ( c − s ) qubits. The stabilizer b ecomes I I Γ − 1 2 ( D ) Γ 0 2 ( D ) 0 0 0 0 0 0 I I 0 , (40) and the information-qubit matrix b ecomes 0 0 0 0 0 Γ − 1 2 ( D ) 0 Γ 0 2 D − 1 Γ 2 D − 1 0 0 0 . (41) The stabilizer in (40) is equiv alen t to the following sta- bilizer by row op erations (prem ultiplying the first c − s ro ws by Γ 2 ( D )): Γ 2 ( D ) Γ 2 ( D ) Γ 0 2 ( D ) 0 0 0 0 0 0 I I 0 . (42) The measurements that Bob p erforms hav e finite weigh t b ecause the row op erations are multiplications of the ro ws by the arbitrary p olynomials in Γ 2 ( D ). Alice thus enco des a co de equiv alent to the desired quantum chec k matrix in (37) using c − s ebits and c − s information qubits. W e now discuss deco ding the stabilizer in (40) and in- formation qubits. Bob p erforms CNOTs from the first c − s qubits to the next c − s qubits. The stabilizer b e- comes 0 I Γ − 1 2 ( D ) Γ 0 2 ( D ) 0 0 0 0 0 0 I 0 0 , (43) and the information-qubit matrix do es not change. Bob uses Hadamard and finite-depth CNOT gates to m ul- tiply the last c − s columns in the “Z” matrix by Γ 0 2 D − 1 Γ 2 ( D ) and add the result to the middle c − s columns. It is p ossible to use finite-depth op erations b e- cause the en tries of Γ 0 2 ( D ) are all p ow ers of D so that Γ 0 2 D − 1 = Γ 0 − 1 2 ( D ). The stabilizer in (43) b ecomes 0 0 Γ − 1 2 ( D ) Γ 0 2 ( D ) 0 0 0 0 0 0 I 0 0 , and the information-qubit matrix in (41) b ecomes 0 0 0 0 Γ 0 2 D − 1 Γ − 1 2 ( D ) 0 Γ 0 2 D − 1 0 0 0 0 . W e premultiply the first c − s rows of the stabilizer by Γ 0 2 D − 1 and add the result to the second c − s ro ws of the information-qubit matrix. These ro w op erations from the stabilizer to the information-qubit matrix result in the information-qubit matrix having pure logical op- erators for the middle c − s qubits. Perform Hadamard gates on the second set of c − s qubits. The resulting information-qubit matrix is as follows 0 Γ 0 2 D − 1 0 0 0 0 0 0 0 0 Γ 0 2 D − 1 0 , (44) so that the information qubits are av ailable at the end of decoding. Pro cessing ma y dela y or adv ance them with resp ect to their initial lo cations b ecause the ma- trix Γ 0 2 D − 1 is diagonal with p ow ers of D . W e can de- termine that the information qubits telep ort coheren tly from the last set of c − s qubits to the second set of c − s qubits in every frame by comparing (44) to (39). The ov erall pro cedure for enco ding is to b egin with a set of c ebits, 2 ( n − c ) − k 1 − k 2 ancilla qubits, and k 1 + k 2 − n + c information qubits. W e p erform the infinite- depth op erations detailed in (37-42) for c − s of the ebits. W e then p erform the finite-depth op erations detailed in the pro ofs of this lemma and Lemma 1 in reverse order. The resulting stabilizer has equiv alen t error-correcting prop erties to the quan tum chec k matrix in (13). The receiv er deco des b y first p erforming all of the finite-depth operations in reverse order. The receiver then deco des the infinite-depth op erations by the pro ce- dure listed in (43-44) so that the original k 1 + k 2 − n + c information qubits p er frame are av ailable for pro cessing at the receiving end. Example 2. Consider a classic al c onvolutional c o de with the fol lowing che ck matrix: H ( D ) = 1 1 + D . We c an use the ab ove che ck matrix in an entanglement- assiste d quantum c onvolutional c o de to c orr e ct for b oth bit flips and phase flips. We form the fol lowing quantum che ck matrix: 1 1 + D 0 0 0 0 1 1 + D . (45) 21 We first p erform some manipulations to put the ab ove quantum che ck matrix into a standar d form. Perform a CNOT fr om qubit one to qubit two in the same fr ame and in the next fr ame. The ab ove matrix b e c omes D − 1 + 1 + D 1 + D 0 0 0 0 1 0 . Perform a Hadamar d gate on qubits one and two. The matrix b e c omes 0 0 1 0 D − 1 + 1 + D 1 + D 0 0 . Perform a CNOT fr om qubit one to qubit two. The ma- trix b e c omes 0 0 1 0 D − 1 + 1 + D D − 1 0 0 . Perform a r ow op er ation that delays the first r ow by D . Perform a Hadamar d on b oth qubits. The stabilizer b e- c omes 1 + D + D 2 1 0 0 0 0 1 0 . The ab ove matrix is now in standar d form. The matrix F ( D ) = 1 as in (18) so that its only invariant factor is e qual to one. The c o de fal ls into the se c ond class of entanglement-assiste d quantum c onvolutional c o des. We b e gin enc o ding with one ebit and one information qubit p er fr ame. The stabilizer matrix for the unenc o de d str e am is as fol lows: 1 1 0 0 0 0 0 0 0 1 1 0 , and the information-qubit matrix is as fol lows: 0 0 0 0 0 1 0 0 1 0 0 0 . Perform a Hadamar d on qubit two and a CNOT fr om qubit two to qubit thr e e so that the ab ove stabilizer b e- c omes 1 0 0 0 1 0 0 1 1 1 0 0 , and the information-qubit matrix b e c omes 0 0 0 0 1 1 0 0 1 0 0 0 . Perform an infinite-depth op er ation c orr esp onding to the r ational p olynomial 1 / 1 + D + D 2 on qubit thr e e. F ol- low with a Hadamar d gate on qubits two and thr e e. The stabilizer matrix b e c omes 1 1 1 / 1 + D + D 2 0 0 0 0 0 0 1 1 0 , (46) and the information-qubit matrix b e c omes 0 0 1 / 1 + D + D 2 0 0 0 0 0 0 0 1 1 + D − 1 + D − 2 . (47) Perform the finite-depth op er ations ab ove in r everse or der so that the stabilizer b e c omes D − 1 1 1+ D + D 2 1+ D 1+ D + D 2 0 0 0 0 0 0 1 1 1 + D , and the information-qubit matrix b e c omes 0 D − 1 + D − 2 1+ D + D 2 1 1+ D + D 2 0 0 0 0 0 0 0 D − 1 + D − 2 D − 1 . The ab ove stabilizer is e quivalent to the desir e d quantum che ck matrix in (45) by a r ow op er ation that multiplies its first r ow by 1 + D + D 2 . The r e c eiver de c o des by p erforming the finite-depth enc o ding op er ations in r everse or der and gets the stabi- lizer in (46) and the information-qubit matrix in (47). The r e c eiver p erforms a CNOT fr om qubit one to qubit two and fol lows with a CNOT fr om qubit two to qubit thr e e in the same fr ame, in an advanc e d fr ame, and in a twic e-advanc e d fr ame. Final ly p erform a Hadamar d gate on qubits two and thr e e. The stabilizer b e c omes 0 0 0 0 0 0 0 0 1 / 1 + D + D 2 0 0 0 , and the information-qubit matrix b e c omes 0 0 0 0 1 0 0 1 1 / 1 + D + D 2 0 0 0 . The r e c eiver de c o des the information qubits suc c essful ly b e c ause a r ow op er ation fr om the first r ow of the stabi- lizer to the first r ow of the information-qubit matrix gives the pr op er lo gic al op er ators for the information qubits. Figur e 7 details the ab ove enc o ding and de c o ding op er- ations for this entanglement-assiste d quantum c onvolu- tional c o de. B. Discussion This second class of co des as sumes that noiseless en- co ding is av ailable. W e require this assumption b ecause the enco ding circuit employs infinite-depth enco ding op- erations. If an error do es o ccur during the encoding process, it can propagate infinitely through the encoded qubit stream. The result of a single enco ding error can distort b oth the enco ded quantum information, the syndromes that result from measurements, and the final recov ery op erations based on the syndromes. W e may b e able to relax the noiseless encoding as- sumption if nearly noiseless enco ding is av ailable. The 22 | ψ 1 A | ψ 2 A | ψ 3 A | ψ 4 A | ψ 5 A | ψ 6 A | Φ + B A | Φ + B A | Φ + B A | Φ + B A | Φ + B A | Φ + B A { { { { { { F r ame 1 F r ame 2 F r ame 3 F r ame 4 F r ame 5 F r ame 6 H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H H Enc o ding C ir cuit D ec o ding C ir cuit FIG. 7: (Color online) The enco ding and deco ding circuits for the entanglemen t-assisted quan tum conv olutional co de in Example 2. The third series of gates in the ab o ve enco ding circuit is an infinite-depth op eration. The other op erations in the enco ding circuit are finite-depth. The deco ding circuit has finite-depth op erations only . probabilit y of an error w ould hav e to be negligible in order to ensure that the probabilit y for a catastrophic failure is negligible. One wa y to low er the probability of an enco ding error is to enco de first with a quantum blo c k co de and then further enco de with our quan tum con volutional coding metho d. Man y classical co ding sys- tems exploit this technique, the most p opular of which is a Reed-Solomon enco der follow ed by a con volutional enco der. VI II. CONCLUSION AND CURRENT WORK This w ork develops the theory of entanglemen t-assisted quan tum conv olutional co ding. W e show sev eral metho ds for imp orting t w o arbitrary classical binary conv olutional co des for use in an entanglemen t-assisted quantum con- v olutional co de. Our metho ds outline different wa ys for enco ding and deco ding our entanglemen t-assisted quan- tum conv olutional co des. W e introduce the notion of an infinite-depth op eration for enco ding circuits. W e use these infinite-depth op era- tions in both enco ding and deco ding. These op erations are acceptable if w e assume that noiseless pro cessing is a v ailable b oth at the sender’s end and on the receiver’s half of shared ebits. Our first class of co des employs only finite-depth op er- ations in their enco ding and deco ding pro cedures. These co des are the most useful in practice b ecause they do not hav e the risk of catastrophic error propagation. An error that o ccurs during encoding, measurement, recov- ery , or deco ding propagates only to a finite n um b er of neigh b oring qubits. Our second class of co des uses infinite-depth op erations during enco ding. This assumption is reasonable only if noiseless encoding is av ailable. The metho d of concate- nated co ding is one wa y to approach nearly noiseless en- co ding in practice. W e suggest sev eral lines of inquiry from here. Our co des are not only useful for quantum communication, but should also b e useful for priv ate classical commu- nication b ecause of the well-kno wn connection b etw een a quan tum channel and priv ate classical c hannel [25]. It may make sense from a practical standp oint to b e- gin inv estigating the p erformance of our co des for en- co ding secret classical messages. The commercial suc- cess of quantum key distribution for the generation of a priv ate shared secret key motiv ates this in vestigation. It is also in teresting to determine which entanglemen t- assisted codes can correct for errors on the receiv er’s side. 23 Co des that p ossess this property will b e more useful in practice. The authors thank Hari Krovi and Markus Grassl for useful discussions. They thank Shesha Ragh unathan and Markus Grassl for useful comments on the manuscript. MMW ac knowledges supp ort from NSF Grant CCF- 0545845, and T AB ac knowledges supp ort from NSF Gran t CCF-0448658. [1] P . W. Shor, “Scheme for reducing decoherence in quan- tum computer memory ,” Phys. R ev. A , vol. 52, no. 4, pp. R2493–R2496, Oct 1995. [2] A. M. Steane, “Error correcting codes in quantum the- ory ,” Phys. R ev. Lett. , vol. 77, no. 5, pp. 793–797, Jul 1996. [3] A. R. Calderbank and P . W. Shor, “Goo d quan tum error- correcting co des exist,” Phys. R ev. A , vol. 54, no. 2, pp. 1098–1105, Aug 1996. [4] D. Gottesman, “Stabilizer co des and quantum error cor- rection,” Ph.D. dissertation, California Institue of T ech- nology , 1997. [5] A. R. Calderbank, E. M. Rains, P . W. Shor, and N. J. A. Sloane, “Quan tum error correction and orthogonal geom- etry ,” Phys. R ev. Lett. , vol. 78, no. 3, pp. 405–408, Jan 1997. [6] A. Calderbank, E. Rains, P . Shor, and N. Sloane, “Quan- tum error correction via co des ov er gf(4),” IEEE T r ans. Inf. The ory , v ol. 44, pp. 1369–1387, 1998. [7] P . Zanardi and M. Rasetti, “Noiseless quan tum co des,” Phys. R ev. L ett. , v ol. 79, no. 17, pp. 3306–3309, Oct 1997. [8] ——, “Error av oiding quantum co des,” Mo dern Physics L etters B , vol. 11, pp. 1085–1093, 1997. [9] D. A. Lidar, I. L. Chuang, and K. B. Whaley , “Decoherence-free subspaces for quantum computation,” Phys. R ev. L ett. , v ol. 81, no. 12, pp. 2594–2597, Sep 1998. [10] D. Kribs, R. Laflamme, and D. P oulin, “Unified and gen- eralized approach to quan tum error correction,” Physic al R eview L etters , vol. 94, no. 18, p. 180501, 2005. [11] D. W. Kribs, R. Laflamme, D. Poulin, and M. Lesosky , “Op erator quantum error correction,” Quantum Infor- mation & Computation , vol. 6, pp. 383–399, 2006. [12] D. Poulin, “Stabilizer formalism for operator quantum error correction,” Physic al R eview L etters , vol. 95, no. 23, p. 230504, 2005. [13] T. B run, I. Dev etak, and M.-H. Hsieh, “General en tanglement-assisted quantum error-correcting codes,” in IEEE International Symp osium on Information The- ory , June 2007. [14] M.-H. Hsieh, I. Dev etak, and T. A. Brun, “General en tanglement-assisted quantum error-correcting codes,” arXiv:0708.2142 , 2007. [15] N. D. Mermin, Quantum Computer Scienc e . Cambridge Univ ersity Press, 2007. [16] W. K. W o otters and W. H. Zurek, “A single quantum cannot b e cloned,” Natur e , v ol. 299, pp. 802–803, 1982. [17] F. J. MacWilliams and N. J. A. Sloane, The The ory of Err or-Corr e cting Co des . North Holland, 1983. [18] G. Bow en, “En tanglement required in achieving en tanglement-assisted c hannel capacities,” Phys. R ev. A , v ol. 66, no. 5, p. 052313, Nov 2002. [19] C. H. Bennett, G. Brassard, C. Cr´ ep eau, R. Jozsa, A. P eres, and W. K. W ootters, “T elep orting an unknown quan tum state via dual classical and einstein-p o dolsky- rosen channels,” Phys. R ev. L ett. , vol. 70, no. 13, pp. 1895–1899, Mar 1993. [20] C. H. Bennett and S. J. Wiesner, “Communication via one- and tw o-particle op erators on einstein-p o dolsky- rosen states,” Phys. R ev. L ett. , vol. 69, no. 20, pp. 2881– 2884, Nov 1992. [21] T. A. Brun, I. Devetak, and M.-H. Hsieh, “Catalytic quan tum error correction,” arXiv:quant-ph/0608027 , Au- gust 2006. [22] ——, “Correcting quantum errors with entanglemen t,” Scienc e , vol. 314, no. 5798, pp. pp. 436 – 439, Octob er 2006. [23] S. Llo yd, “Capacit y of the noisy quan tum channel,” Phys. R ev. A , vol. 55, no. 3, pp. 1613–1622, Mar 1997. [24] P . W. Shor, “The quantum channel capacity and coher- en t information,” in Le ctur e Notes, MSRI Workshop on Quantum Computation , 2002. [25] I. Devetak, “The priv ate classical capacity and quantum capacit y of a quantum channel,” IEEE T r ans. on Inf. The ory , v ol. 51, pp. 44–55, January 2005. [26] C. H. Bennett, P . W. Shor, J. A. Smolin, and A. V. Thap- liy al, “Entanglemen t-assisted classical capacity of noisy quan tum channels,” Phys. R ev. L ett. , vol. 83, no. 15, pp. 3081–3084, Oct 1999. [27] ——, “En tanglement-assisted capacity of a quantum c hannel and the reverse shannon theorem,” IEEE T r ans. on Inf. The ory , v ol. 48, pp. 2637–2655, 2002. [28] T. M. Cov er and J. A. Thomas, Elements of Information The ory . Wiley-Interscience, 1991. [29] H. Ollivier and J.-P . Tillic h, “Description of a quantum con volutional co de,” Phys. R ev. L ett. , vol. 91, no. 17, p. 177902, Oct 2003. [30] ——, “Quantum con volutional co des: fundamentals,” arXiv:quant-ph/0401134 , 2004. [31] M. Grassl and M. R¨ otteler, “Noncatastrophic enco ders and enco der inv erses for quantum conv olutional co des,” in IEEE International Symp osium on Information The- ory (quant-ph/0602129) , 2006. [32] ——, “Quan tum conv olutional codes: Encoders and structural prop erties,” in F orty-F ourth A nnual Al lerton Confer enc e , 2006. [33] ——, “Constructions of quan tum conv olutional codes,” in IEEE Int. Symp. on Inf. The ory , 2007. [34] G. D. F orney and S. Guha, “Simple rate-1/3 con volu- tional and tail-biting quantum error-correcting co des,” in IEEE International Symp osium on Information The- ory (arXiv:quant-ph/0501099) , 2005. [35] G. D. F orney , M. Grassl, and S. Guha, “Conv olutional and tail-biting quantum error-correcting co des,” IEEE T r ans. Inf. The ory , v ol. 53, pp. 865–880, 2007. [36] M. A. Nielsen and I. L. Chuang, Quantum Computation and Quantum Information . Cambridge Universit y Press, 2000. [37] D. Gottesman, “Class of quantum error-correcting co des saturating the quan tum hamming bound,” Phys. R ev. A , v ol. 54, no. 3, pp. 1862–1868, Sep 1996. 24 [38] M. M. Wilde, H. Krovi, and T. A. Brun, “Conv olutional en tanglement distillation,” , 2007. [39] Z. Luo and I. Devetak, “Efficiently implemen table co des for quan tum k ey expansion,” Phys. Rev. A , vol. 75, no. 1, p. 010303, 2007. [40] M. M. Wilde, H. Krovi, and T. A. Brun, “Entanglemen t- assisted quantum error correction with linear optics,” Phys. R ev. A , vol. 76, p. 052308, 2007. [41] M. M. Wilde and T. A. Brun, “Protecting quantum in- formation with entan glement and noisy optical mo des,” In pr ep ar ation , 2007. [42] I. Devetak, A. W. Harrow, and A. Winter, “A resource framew ork for quantum shannon theory ,” arXiv:quant- ph/0512015 , 2005. [43] A. J. Viterbi, “Error b ounds for con volutional co des and an asymptotically optimum deco ding algorithm,” IEEE T r ans. Inf. The ory , v ol. 13, pp. 260–269, 1967. [44] R. Johannesson and K. S. Zigangirov, F undamentals of Convolutional Co ding . Wiley-IEEE Press, 1999. [45] A. Harro w, “Coherent communication of classical mes- sages,” Phys. Rev. L ett. , vol. 92, p. 097902, Marc h 2004. [46] M. M. Wilde, H. Krovi, and T. A. Brun, “Coherent com- m unication with contin uous quantum v ariables,” Phys. R ev. A , vol. 75, no. 6, p. 060303(R), 2007.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment