Hybrid approach for Image Encryption Using SCAN Patterns and Carrier Images
We propose a hybrid technique for image encryption which employs the concept of carrier image and SCAN patterns generated by SCAN methodology. Although it involves existing method like SCAN methodology, the novelty of the work lies in hybridizing and…
Authors: P, uranga H.T, Naveen Kumar S.K
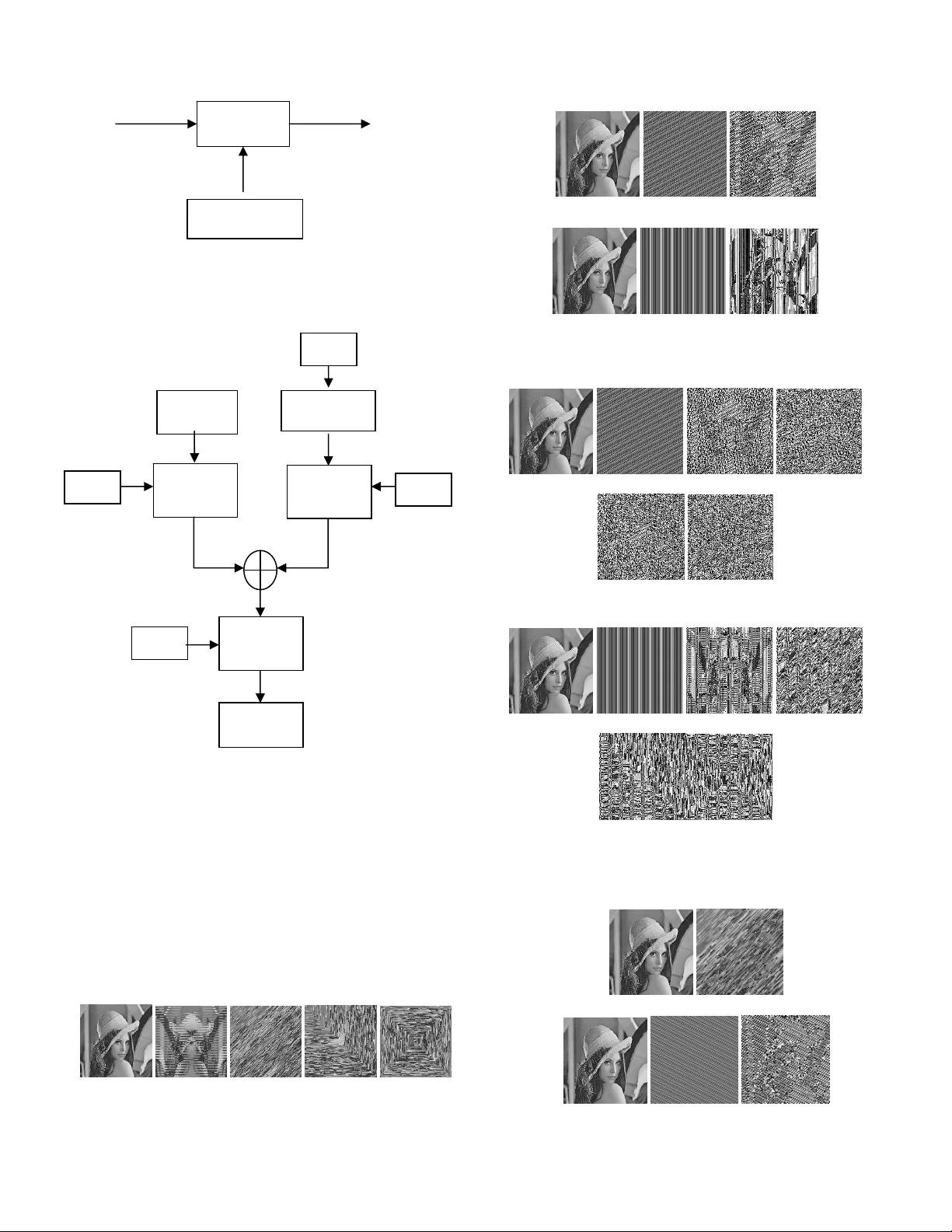
Panduranga H .T. et al. / (IJC SE) Int ernational Journal on C omputer Sci ence and En gineering Vol. 02, No. 02 , 2010, 297-300 Hybrid approach for Image Encryption Using SCAN Patterns and Carrier Images Panduranga H.T Dept. of Electr onics and C ommunicat ion Engineerin g Govt. Enginee ring Colle ge. Hassan, Karnataka, India Naveen Kumar S.K Dept. of Electr onics, PG Ce nter University of Mysore Hassan, Karnataka, India Abstract — We propose a hybrid technique for image encryption which employs the con cept of carrier image and S CAN patterns generated by SCAN methodology. Although it involves exis ting method like SCAN methodology, the novelty of the work lies in hybridizing and carrier image cr eation for e ncryption. H ere the carrier image i s created with the help of alphanumeric k eyword. Each alphanumeric key will be having a unique 8bit value generated by 4 out of 8-code. Th is newly gene rated carrier image is added with original image to obtain encrypted image. The scan methodology is applied to either original image or carrier image, after the addition of original im age and carrier imag e to obtain highly distorted encrypted image. The resulting image is found to be more distorted in hybrid tec hnique. By applyi ng the reverse process we g et the decryp ted image. Keywords-Scan Pattern s; Carri er Image; 4 out of 8 code; Encryption; I. I NTRODUCTION The developm ent of internet provi des a new way for spreading the digital information more conv eniently. Information is an asset that has a value like any other asset. As an asset, information n eeds to be secured from the attacks. Because of the characteristic of digital images, som e security problem comes out beside s the extensive us age of these images. The im portance of securi ng information/image ha s reached its highe st levels in the recent ye ars due to hacker attack and instruction of peopl e’s privacy. Cryptograph y is popularly known as an art and science of secret writing. This enables us to store sensitive info rmation or transmit it across insecure networ ks so that it cannot be read by anyon e except th e intend ed recip ient. Image e ncryption has application i n internet comm unication, vi deo confer encing, telemedi cine, distance educa tion throug h video on dem and, multimedia systems, military and satellite image processing. S.R.M Prasanna an d Y.V. Subba Ra o have presented the method whi ch employ s magnitu de and phase m anipulat ion using car rier im ages [1]. The novelty of this pa per explai ns the concept of carrier im ages for encryption purpose. Here, first apply the 2 D-DFT to ori ginal im age and random ly generat ed carrier im ages, then mani pulation of phase dat a or ma gnitude data or b oth is done in the fre quency dem ine, fi nally encry pted image is obt ained by a pply ing 2D-IDF T to ma nipulated images. Chao-Shen Ch en and Rong-jain Chen proposed an image encrypt ion and decryptio n al gorithm based on SC AN methodolo gy [2]. SC AN is a language -based two dim ensional spatial-assessing methodology wh ich can efficiently specify and generat e a wide range of sca nning pat hs. Here sca nning path sequence fill the orig inal image to generate the encrypted image. In [3] S.S Manicc am and N.G . Bourbaki s have presented a meth od for image and video en cryption, here first stage lossy vi deo compressi on based on frame diffe rence before the encryption . Here they say image encryption is performe d by SCAN-base d perm utation of pi xels and substitution rule which together form an iterated product cipher. Alok a Sinha and Kehar Singh propos ed a new technique to encrypt an im age for secure image transm ission. Here the digital signature of the orthogon al image is added to the encoded versio n of the orig inal image. The encoding of image is don e using Bose -Chaudhu ri Hocquen ghm (BCH) code. The di gital signat ure are created and verifie d by m eans of cryptography [4 ]. We implemented an encryptio n method which involves three step s; first step is constructing a size extended binary image using or iginal image. In second step, applying the existing SCAN pattern s to rearrange the pixels of extended binary image and finally in third step reconstru ct the grayscale image to obtain encr ypted version [5]. We also developed t he concept of generating the carrier im age with t he help of uni que code called a s 4 out of 8 -code, by a dding t he carrier image to origi nal imag e we get the encrypte d image [6]. The rest of the portion is as follows: section two gives idea behind the propose d work. Section three explai ns the brief overview of SCAN patterns. Section four exp lains the brief overview of carrier i mage creation using 4out of8 code . The proposed scheme for image encryption is described in Section five. Experim ental observat ion and res ults are discussed in section six. C onclusion and future disc ussions are m ade in section seven. II. I DEA BEHIND THE PRO POSED WORK As we discussed in t he introduction, t here are several method for im age encryption whi ch deals in their own i deas. In few image encryption algorithms , encrypt ion process depend only on the key words, but in som e other algorithm s they use only carrier image for encryption. A n y h ow , w e h a v e a n i de a t o hybrid the existi ng algorithms to get a new path for encry ption ISSN : 0975-3397 297 Panduranga H .T. et al. / (IJC SE) Int ernational Journal on C omputer Sci ence and En gineering Vol. 02, No. 02 , 2010, 297-300 by taking the advantages of indi vidual met hods. Hence we come up with the concept of h ybridizing SCAN pattern and Carrier im age for Image encry ption to get highly dist orted Images. III. B RIEF OVERVIEW OF SCAN PATTERNS A scanning of a two di mensional array i s an order in which each element of the array is a ccessed exactly once. The SCAN is a formal language -based two dim ensional spatial accessing methodology which can repr esent and generate a large num ber of wide varieties of scan ning paths. SCAN l anguage uses four basic scan patterns. They are c ontinuous ra ster C, continuous diagonal D, cont inuous orthogo nal O, and spiral S. Each basi c pattern has eight transform ations numbered from 0 to 7. For each basic scan pattern, the tran sformations 1, 3, 5, 7 are reverses of transf ormations 0, 2, 4, 6, respectiv ely. The basic scan patterns and trans for mations are shown [2,3]. IV. C ARRIER IMAGE CREATIO N USING 4 OUT OF 8 CODE Here we are defining a new code cal led 4 o ut of 8 c ode. This code i s of 8 bit lengt h with 4 number of one’s an d 4 number of zero’s and we made one c onsideration that each nibble m ust have 2 num ber of ones and 2 num ber of zeros. We listed all 36 possible combination s of the 4 out of 8 code and each code is assigne d to an a lpha num eric character in table 1. Since 26 alphabets (capital letters or small letters) and 10 numerals form s to gi ve 36 alpha numeric characters, this code is more suitable to assign a unique code t o each alphanumeric character. As we enter the different ke ywords, each keyword is taken and rearranged in a matrix form of size equal to the size of original image. If the length of the keyword is very small then the same keyword is repeated till the length is become equal to size of original image. B y using luck up tabl e of the alphanumeric charact er and 4 out of 8 c ode as shown i n table1, a carrier image is created. Dependi ng upon the key word, carri er image is generated an d used in the additio n process to generate a encrypted image. Figure1: Carrier image1, Carrier i mage2, Carrier image3. Figure 1 shows the carrie r images for the different keywords as fallows, key1='Iwant 2EncryptT hisImage' , key2 = 'HybridApp roch128z', ke y3='MyDateOfBirth Is21May1983' SL NO. BIN HEX DEC ALPHA NUMERIC 1 00110011 33 51 A,a 2 00110101 35 53 B,b 3 00110110 36 54 C,c 4 00111001 39 57 D,d 5 00111010 3A 58 E,e 6 00111100 3C 60 F,f 7 01010011 53 83 G, g 8 01010101 55 85 H,h 9 01010110 56 86 I,i 10 01011001 59 89 J,j 11 01011010 5A 90 K, k 12 01011100 5C 92 L,L 13 01100011 63 99 M,m 14 01100101 65 101 N,n 15 01100110 66 102 O,o 16 01101001 69 105 P,p 17 01101010 6A 106 Q,q 18 01101100 6C 108 R,r 19 10010011 93 147 SS 20 10010101 95 149 T,t 21 10010110 96 150 U,u 22 10011001 99 153 V,v 23 10011010 9A 154 W,w 24 10011100 9C 156 X,x 25 10100011 A3 163 Y,y 26 10100101 A5 165 Z,z 27 10100110 A6 166 0 28 10101001 A9 169 1 29 10101010 AA 170 2 30 10101100 AC 172 3 31 11000011 C3 195 4 32 11000101 C5 197 5 33 11000110 C6 198 6 34 11001001 C9 201 7 35 11001010 CA 202 8 36 11001100 CC 204 9 Table 1: 36 possible combination of 4 out of 8 coed alon g with alphanumeric character. V. T HE PROPOSED SCHEME FOR IMAGE ENCRYPTION Encryption of an im age can be done at dif ferent stage or in multiple stages and in multiple ways. If the encryption process is only in single stage then security is less as compare to multist age encryptio n. Fi gure 2 sho ws the bl ock diagra m of existing encryption appro ach using text as a key word and image as keyword. E ncryption process may take different approaches, for exam ple encryp tion may be using o nly SCAN method or only by Phase -Magnit ude mani pulation m ethod or using only carrier im age generat ed by 4 o ut of 8 code . Figure 3 shows t he block diagram of prop osed hybri d approac h whic h contain multiple keywo rds, where key-1 is corresponding to create a carrier image and key- 2, key-3, key-4 along with SCAN encryption proces s are optional. Original Image Encryption Process Encrypted Image Text as a Keys (a) ISSN : 0975-3397 298 Panduranga H .T. et al. / (IJC SE) Int ernational Journal on C omputer Sci ence and En gineering Vol. 02, No. 02 , 2010, 297-300 Figure 2. Block diagram of existing im age encryption approach using (a) text as a key and (b) Image as a key Figure 3. Block diagram of proposed im age encryption approach using SCAN patterns and Carrier Image VI. R ESULTS AND D ISCUSSION Here we have taken “lena.bm p” as a reference image to apply deferent encrypt ion algorithm . Figure 4 shows the different encrypted image when only SCAN encryption process is done for different key s. Figure 5 shows the encry pted images if original image is ad ded with the carrier images for different keywords i.e. key1 i n the block diagram. Figure 6 shows encrypted images usi ng SCAN encryption p rocess at the input of original image and addition of carrier image. Figu re 7 shows encrypted images usi ng SCAN encryption p rocess at different position along with the carrier image. Original C-scan D-scan O-sca n S-scan Figure 4. Original image and encrypte d image with different SCAN pattern s Original Carrier1 Encrypted1 Key for Carrier Image: 'Iwant2EncryptThisImage', Original Carrier2 Encrypted2 Key for Carrier Image: 'HybridApproch128z' Figure 5. Original image, Carrier im age and encrypted image for different keys at key1 Original, Carrier, C-scan+carrier, D -scan+carrier, O-scan+carrier, S- scan+carrier, Key f or Carrier Image: 'Iwant2EncryptThisI mage' Original, Carrier, C-scan+carrier, D -scan+carrier, O-scan+carrier, S- scan+carrier, Key f or Carrier Image: 'HybridApproch128z' Figure 6. Original image, Carrier im age and encrypted image for different keys at key1 and SCAN Patterns (a) (b) Original Image Encryption Process Encrypted Image Image as a Keys (b) Original Image Carrier Image Creation Key 1 SCAN Encryption Process SCAN Encryption Process Key 3 Key 2 Key 4 SCAN Encryption Process Encrypted Image ISSN : 0975-3397 299 Panduranga H .T. et al. / (IJC SE) Int ernational Journal on C omputer Sci ence and En gineering Vol. 02, No. 02 , 2010, 297-300 (c) (d) (e) (f) Key for Carrier Image: 'UniversityOfMysore' Figure 7. First image is the input image and last image is the Encrypted im age in each row. (a)encrypted i m age = dscan (original_image), (b) encrypted image = additi on (original_image, carrier_image), (c) encrypted image = addition (dscan (origin al_image), carrier_ image), (d) encrypted image = addition (origi nal_image, dscan ( carrier_image)) (e) encrypted image =dscan ( add ition (dscan(original_image), dscan ( carrier_image))) VII. C ONCLUSION From the experiment al results we concl ude that the proposed hybr id approach for im age encryption gives very good result as com pare to individual encr yption process. For the sake of simplicity we used onl y few SCAN pattern s and few carrier-keywords, but pr op osed algorithm also works for complex SCAN pattern and com p lex carrier-keywords. As the complexity increases the encrypted im age is more distorted as compare to the result of single stage encryption. In future we want to develop an hybri d algorithm whi ch uses more SCAN patterns, Carrier im ages alo ng with som e bit-manipul ation techniques to provide m o re security to the images. R EFERENCES [1] S.R.M Prasanna, Y.V. Subba Rao and A. Mitra. , “An Image Encryption method with Magnitude and Phase Ma nipulation using carrier images”, IJCS, vol. 1, No 2, pp.132-13 7, 2006. [2] Chao Shen Chen and Rong Jian Ch en, “Image encryption and decry ption using SCAN methodology,” Proc. PDCAT, 2006. [3] S.S. Maniccam and N.G. Bourbakis, “Image and video encry ption using SCAN patterns,” Pattern Recognition, vol. 37, pp. 725-7 37, 2004. [4] Sinha, K. Sing., “A technique for im age encryption using digital signeture”., Optics Communica tion” , 218, pp.229-2 34, 2003. [5] Panduranga H.T, Naveenkumar S.K, “A novel 3-step combinational approach for image encryption”, IJCEIT, vol 03, 2009 [6] Panduranga H.T, Naveenkumar S.K, “A novel im age encryption method using 4outof8 code”, pr oc. CommV’09, pp 460-462, 2009. ISSN : 0975-3397 300
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment