A Novel Mathematical Model for the Unique Shortest Path Routing Problem
Link weights are the principal parameters of shortest path routing protocols, the most commonly used protocols for IP networks. The problem of optimally setting link weights for unique shortest path routing is addressed. Due to the complexity of the …
Authors: Changyong Zhang
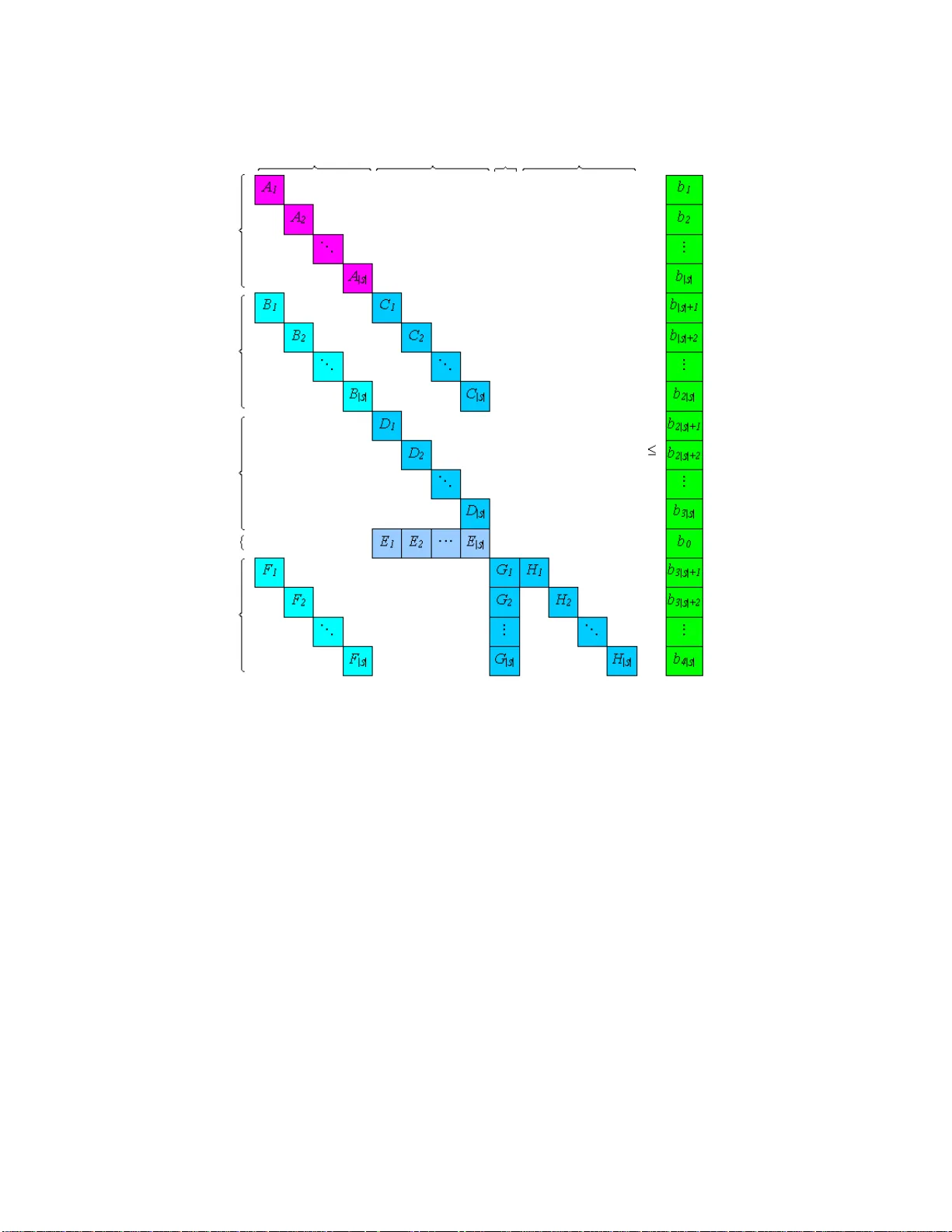
A No v el Mathematical Mo del for the Unique Shortest P ath Routing Problem 1 Changyong Zhang Department of Mathematics, Univ ersity of Southern California 3620 So uth V ermon t Aven ue , KAP 108, Los Angeles, CA 9 0089- 2532, USA, changy oz@ usc.edu Link w eights are the principal pa rameters of shortest path rout ing proto cols, t he most com- monly used proto cols for IP net w orks. The problem of optimally setting link w eigh ts for unique shortest path routing is addres sed. Due to the complexit y of the constrain ts in volv ed, there exist c hallenges to formulate the pro blem prop erly , so that a solution algorithm ma y b e dev elop ed whic h could pro v e to b e more efficien t than those already in existenc e. In this pap er, a no ve l complete form ulatio n with a p olynomial n umber of constraints is first in tro duced and then mathematically pro v ed to b e correct. It is further illustrated that the form ulatio n has adv an ta ges o v er a prior one in terms o f b oth constrain t structure and model size for a prop osed decomp osition metho d to solv e the problem. Key wor ds: Mathematical Modeling, Mo del V erific a t io n, Constrain t Structure, Mo del Size, Decomp osition, Unique Path, Shortest P at h Routing, Link W eigh ts 1. In tro ducti o n Shortest path routing pro to cols suc h as OSPF (Mo y , 1998) are the most widely deploy ed and commonly used proto cols for IP net works . In shortest path routing , each link is assigned a w eigh t and tr a ffic demands are routed along the shortest paths with resp ect to link w eights, based on a shortest path first alg orithm ( Bertsek as and Ga lla ger, 1 992). Link we ig hts are hence the principal parameters and an esse ntial problem is to find an appropriate w eigh t set for shortest path routing. A simple approac h to set link w eigh ts is the hop-coun t method, assigning the w eigh t of eac h link to one. The length of a path is therefore the n um b er of ho ps. Another default approac h recommended b y Cisco is t he in v-cap method, setting the w eigh t of a link in v ersely prop ortional to its capacity , without taking traffic conditions in to consideration. More gen- erally , the w eigh t of a link ma y dep end on and b e related to its transmission capacit y and 1 Some results in this paper ha ve b een presented on the 4th In terna tional Confer ence on Net working (ICN 2005), Reunion Island, April 2005, INF ORMS Annual Meeting 2006 , Pittsburgh, P A, USA, Nov ember 2006, and the 6th In terna tional Cong ress on Industrial and Applied Mathematics (ICIAM 2007 ), Zuric h, Switzerland, J uly , 20 07, resp ectively . 1 its tr affic lo a d. Accordingly , a problem worth in ves tig ating is the task of finding an optimal w eigh t set for shortest pa th rout ing , giv en a net w ork top ology , a pro jected t raffic matrix (F eldmann et al., 2001), and an ob jectiv e function. The problem has tw o instances, dep ending on whether multiple shortest paths or only a unique routing path from an origin no de to a destination no de is allow ed. F or the first instance, a n umber of heuristic me tho ds hav e been intro duced, based on genetic algorithms (Ericsson et al., 2002) and lo cal searc h metho ds (F ortz and Thorup, 2000 ). F or the second instance, the Lagrangian relaxation metho d (Lin and W ang, 199 3) and a lo cal searc h metho d (Ramakrishnan and Ro drigues, 2001 ) hav e been prop osed. These metho ds hav e also resulted in go o d routing p erformances by b eing tested in particular data sets. On the other hand, with these heuristic metho ds, t he problem is no t completely formulated and so in general is not optimally solv ed. It w ould be desirable if in av erage cases optimal solutions could b e obtained for reasonably large data instances from real-world a pplications. F rom a manageme nt p oin t o f vie w, unique - path routing uses m uch simpler routing mec ha- nisms and allow s f o r easier monitoring of traffic flows (Ameur and Gourdin, 2 0 03). Therefore, this pap er fo cuses on the unique-path instance. The problem is referred to as the unique shortest p ath r outing pr o blem . It is a reduction of the integer multi-commodity flo w problem (Ah uja et al., 199 3 ). The problem has b een w ell studied and efforts hav e b een made to form ulate the problem mathematically (Ameur and Gourdin, 2 003; Zha ng and Ro do ˇ sek, 2005). Mathematical mo d- els ha v e also b een dev elop ed for other related problems su ch as net work design and routing problems (Bley and Ko ch, 2002 ; Holm b erg and Y uan, 20 04). Most of these mo dels ha ve form ulated the corresp onding problems completely , whereas t hey ha v e been either demand- based or path-based and ha v e left space to furt her explore the structure pro p erties of the problems, from whic h more efficien t solution metho ds may b e deriv ed. The main goal of this pa p er is to mathematically mo del the problem, whic h w ould yield a new exact solution a ppro ac h fo r real-w orld applications in av erage data instances. In Section 2, the problem definition is first sp ecified. Tw o differen t complete form ula t ions, a new one and an existing one f or comparison, are in tro duced in Section 3. The new form ulat ion is then mathematically pro ved to b e corr ect in Section 4. Differences b etw een the t w o for mulations on b oth constrain t structure and mo del size are discuss ed in Section 5. Conclusions are dra wn in Se ction 6. 2 2. Problem Defi nition The unique shortest path routing problem is sp ecified as follows: Giv en • A net work top ology , which is a directed graph structure G = ( N , L ), where – N is a finite set of no des, eac h of whic h represen ts a router; and – L is a set o f directed links, eac h o f whic h corresp onds to a transmission link; (F o r eac h ( i, j ) ∈ L , i is the starting no de, j is the ending no de, and c ij ≥ 0 is the link capacit y .) • A traffic matrix, whic h is a set o f demands D ; (It is assumed that there is at most one demand b etw een eac h origin-destination pair. F or eac h demand k ∈ D , s k ∈ N is the origin no de, t k ∈ N is the destination no de, a nd d k > 0 is the required bandwidth. Accordingly , S is the set of all orig in no des, T s is the set o f all destination no des of demands originating from no de s ∈ S , and D s is the set of all demands originat ing from no de s ∈ S .) • Lo wer and upp er b ounds of link w eigh ts, whic h are p ositive real num b ers w min and w max , resp ectiv ely; and • An ob jectiv e function, sp ecifically , t o maximize the sum of residual capacities, Find an optimal we ig h t set w ij , ( i, j ) ∈ L , sub ject to • Flo w conserv ation constrain t s: f or each demand, a t each no de, the sum of all incoming flo ws (including the demand bandwidth at the origin node) is equal to the sum of all outgoing flo ws (including the demand bandwidth at the destination no de); • Link capacit y constrain ts: f or eac h link, the load of tr affic flo ws tra nsiting the link do es not exceed the capacity o f the link ; • P ath uniqueness constrain ts: eac h demand has a unique routing path; and • P ath length constraints: for eac h demand, the length o f eac h path assigned to route the demand is strictly less than that of an y other p o ssible a nd unassigned pat h to route the demand. 3 i j h s k t k w ij i j h s k t k w ij ij s i s j h k hj k ij w l l x x k k + ≤ = ∧ = ∑ 0 0 i j h s k t k w ij ij s i s j h k hj k ij w l l x x k k + < = ∧ = ∑ 1 0 ij s i s j k ij w l l x k k + = = 1 Figure 1: Illustration of the path length cons tr a in ts 3. Problem F orm ulation In this section, the problem is ma t hematically form ulated from t wo differen t p ersp ective s, based on t he study of the problem pro p erties. F or comparison, an exis t ing mo del (Z hang and Ro do ˇ sek, 2 005) is in tro duced in mor e detail first. 3.1 A Demand-Based Mo del According to the c haracteristics of unique shortest path routing, the routing path of a demand is the s ho rtest among a ll p ossible paths. F or each link, the routing path of a demand either tra vers es the link or not. Figure 1 illustrat es the relationships b etw een the lengths of the shortest paths and link w eigh ts. P aths in thic k lines are ro uting paths. The path length and path uniqueness constrain ts require that the length o f t he unique shortest path to route a demand is less than that of any other p ossible path fro m the origin no de to the destination no de. With resp ect to the constraints, there are three s cenarios to b e considered: • If t he routing path of demand k trav erses link ( i, j ), the length o f the shortest path from no de s k to no de j is the length of the shortest path from no de s k to no de i plus the w eight of link ( i, j ); 4 • If the ro uting path of demand k does no t tra v erse link ( i, j ) but visits no de j , the length of the shortest path from no de s k to no de j is strictly less than the sum of the length of the shortest path from no de s k to no de i and the w eigh t of link ( i, j ); (Otherwise, there w ould b e at least t wo shortest paths to route demand k .) • If the routing path of demand k neither trav erses link ( i, j ) no r visits no de j , the length of the shortest pat h from no de s k to no de j is less tha n or equal to the sum of the length of the shortest pa th from no de s k to no de i and the w eight of link ( i, j ). Based on the ab ov e observ ations on the relationships b et w een the length of a shortest path and the w eigh t s of links that it tra vers es, the pr o blem can b e mathematically formu la ted as a demand-b ase d mo del (DBM) as follows (by defining one routing decision v ariable for eac h link-demand pair): R outing de cision variables : x k ij ∈ { 0 , 1 } , ∀ k ∈ D , ∀ ( i, j ) ∈ L (1) is equal to 1 if and only if the routing path o f demand k trav erses link ( i, j ). The n um b er of this set of v ariables is |D | |L| . Link weight variab l e s : w ij ∈ [ w min , w max ] , ∀ ( i, j ) ∈ L (2) represen ts the routing cost of link ( i, j ). The n um b er of this set o f v ariables is |L| . Path length va riables : l s i ∈ [0 , + ∞ ) , ∀ s ∈ S , ∀ i ∈ N (3) denotes the length of the shortest path from origin no de s to no de i . Ob viously , l s k t k is the length of the shortest path to route demand k ∈ D and l s s = 0 , ∀ s ∈ S . The num b er of this set of v ariables is |S ||N | . Flow c onservation c onstr aints : X h :( h,i ) ∈L x k hi − X j :( i,j ) ∈L x k ij = − 1 , if i = s k 1 , if i = t k 0 , otherwis e , ∀ k ∈ D , ∀ i ∈ N (4) The n umber o f this set of constraints is | D ||N | . 5 Link c ap acity c onstr aints : X k ∈D d k x k ij ≤ c ij , ∀ ( i, j ) ∈ L (5) The n umber o f this set of constraints is | L| . Path uniqueness c onstr aints : under the com bined restrictions of the flo w conserv a t io n constrain ts and the path length constraints , the constrain ts are satisfied automatically . Path length c onstr aints : l s k j ≤ l s k i + w ij − ε X h :( h,j ) ∈L x k hj − x k ij l s k j ≥ l s k i + w ij − M 1 − x k ij , ∀ k ∈ D , ∀ ( i, j ) ∈ L (6) where ε and M are appropriate constan ts with 0 < ε ≪ M . The nu m b er of this set of constrain ts is 2 |D || L| . By en umerating all p ossible v alues of the r o uting decision v ariables x k ij , k ∈ D , ( i, j ) ∈ L , it can b e v erified that the linearized constrain ts (6) are iden tical to those constrain ts (7) orig inally presen ted in lo gic f orms, as illustrated in Figur e 1. x k ij = 0 ∧ X h :( h,j ) ∈L x k hj = 0 ⇒ l s k j ≤ l s k i + w ij x k ij = 0 ∧ X h :( h,j ) ∈L x k hj = 1 ⇒ l s k j < l s k i + w ij x k ij = 1 ⇒ l s k j = l s k i + w ij , ∀ k ∈ D , ∀ ( i, j ) ∈ L (7) Obje ctive function : max X ( i,j ) ∈L c ij − X k ∈D d k x k ij ! whic h is equiv alen t to min X ( i,j ) ∈L X k ∈D d k x k ij (8) Accordingly , the resulting complete mo del is presen ted as DBM: O ptimiz e (8) S ubj ect to (4) , (5) , (6) , (1) , (2) , (3) In the follo wing, an equiv alen t mo del to DBM, whic h will b e used to ve rif y the correctness of DBM in Section 4, is derive d. 6 A nec essary condition of the unique shortest pat h routing problem is the sub-p ath opti- mality requiremen t, whic h states that an y sub-pat h of a routing pat h is still a unique shortest path (Bley a nd Ko c h, 20 0 2). Specifically , given an origin no de s ∈ S and a no de i ∈ N where i 6 = s , it requires that all demands originating f r o m s and visiting i use the same incoming link to i . Mathematically , it is form ulated as X h :( h,i ) ∈L max k ∈D s x k hi ≤ 1 , i 6 = s, ∀ s ∈ S , ∀ i ∈ N . (9) The ab ov e constrain ts can b e alternative ly presen ted with linear constraints , b y intro- ducing a new v ariable y s ij , s ∈ S , ( i, j ) ∈ L : y s ij ≥ x k ij , ∀ k ∈ D s , ∀ ( i, j ) ∈ L and X h :( h,i ) ∈L y s hi ≤ 1 , i 6 = s, ∀ s ∈ S , ∀ i ∈ N . In DBM, the sub-path optimality constrain ts are not explicitly included. In the following, it is prov ed that the constraints are implied b y the pa th length constraints . Prop osition 1 The p ath length c onstr ain ts in DBM imply the sub-p ath optimality c on- str aints. Pr o of . Supp ose t here are t w o demands k 1 , k 2 ∈ D , and s k 1 = s k 2 = s . Assume they would use t wo disjoin t paths to tra v erse from no de u to no de v . Demand k 1 w ould use path P j = ( j 1 , j 2 ) → ( j 2 , j 3 ) → . . . → ( j n − 1 , j n ) , ( j l , j l +1 ) ∈ L , l = 1 , . . . , n − 1 , where j 1 = u and j n = v , and demand k 2 w ould use path P i = ( i 1 , i 2 ) → ( i 2 , i 3 ) → . . . → ( i m − 1 , i m ) , ( i q , i q +1 ) ∈ L , q = 1 , . . . , m − 1 , where i 1 = u and i m = v . Then, b y the definition of the routing decision v ariables, x k 1 j l j l +1 = 1 and x k 2 j l j l +1 = 0 , ∀ ( j l , j l +1 ) ∈ P j , l = 1 , . . . , n − 1 . As a result, according to constraints (7), on one hand, since ∀ k ∈ D , ∀ ( i, j ) ∈ L , x k ij = 1 ⇒ l s k j = l s k i + w ij , considering demand k 1 , l s v = l s u + l u j n = l s u + l u j n − 1 + w j n − 1 j n = l s u + l u j n − 2 + w j n − 2 j n − 1 + w j n − 1 j n = l s u + l u j 1 + w j 1 j 2 + · · · + w j n − 1 j n = l s u + l P j . (10) 7 On the other ha nd, sinc e ∀ k ∈ D , ∀ ( i, j ) ∈ L , x k ij = 0 ∧ P h :( h,j ) ∈L x k hj = 1 ⇒ l s k j < l s k i + w ij and x k ij = 0 ⇒ l s k j ≤ l s k i + w ij , considering demand k 2 , l s v = l s u + l u j n < l s u + l u j n − 1 + w j n − 1 j n ≤ l s u + l u j n − 2 + w j n − 2 j n − 1 + w j n − 1 j n ≤ l s u + l u j 1 + w j 1 j 2 + · · · + w j n − 1 j n = l s u + l P j . (11) Con tradiction then follo ws b et wee n (10) and (11), whic h means the t w o demands cannot b e r o uted o v er tw o differen t pat hs b et wee n tw o shared no des. It is hence pro ved tha t the sub-path optimality constraints a r e satisfied. By Prop osition 1, DBM is equiv alent to the fo llowing mo del DBM ′ . DBM ′ : O ptimiz e (8) S ubj ect to (4) , (5) , (6) , (9) , (1) , (2) , (3) 3.2 An Origin-Based Mo del In Section 3.1, the unique shortest path routing problem is f orm ulated a s a demand-based mo del, whic h defines one routing decision v ariable for eac h link-demand pair. Based on t he study of solution prop erties of the pro blem, it can b e found that all routing paths of demands originating fr om the same no de constitute a tree, roo ted at the origin no de. Acc o rdingly , a more natural fo rm ulation for the problem is to define one ro uting decision v ariable for each link-origin pair. F or example, in Figure 2, instead of defining three ro uting decision v ariables for link ( i, j ), one for each of the three demands sharing the same origin no de s , the new form ulatio n defines o nly one ro uting decision v ariable fo r link ( i, j ), asso ciated with origin no de s . Based on the ab o ve observ ations, an origi n-b as e d mo del (OBM) for the problem is for- m ulated as follows . R outing de cision variables : y s ij ∈ { 0 , 1 } , ∀ s ∈ S , ∀ ( i, j ) ∈ L (12) is equal to 1 if a nd only if the routing paths of at least one of the demands originating from no de s trav erse link ( i, j ). The n um b er of this s et of v ariables is | S | |L| . 8 s t k3 t k2 t k1 j i Figure 2: Illustration of the origin-based mo del A uxilia ry flow variable s : f s ij ∈ [0 , + ∞ ) , ∀ s ∈ S , ∀ ( i, j ) ∈ L (13) represen ts the load of traffic flows originating from no de s and tr av ersing link ( i, j ). The n um b er of this set of v ariables is |S ||L| . Link weight variab l e s : w ij ∈ [ w min , w max ] , ∀ ( i, j ) ∈ L (14) represen ts the routing cost of link ( i, j ). The n um b er of this set o f v ariables is |L| . Path length va riables : l s i ∈ [0 , + ∞ ) , ∀ s ∈ S , ∀ i ∈ N (15) denotes the length of the shortest path from orig in no de s to no de i . In pa rticular, l s s = 0 , ∀ s ∈ S . The nu mber of this set of v a riables is |S ||N | . Flow c onservation c onstr ai nts : fo r eac h tree, at the ro ot no de, the difference b etw een the sum of outgoing flo ws and the sum of incoming flows is the sum of bandwidths of all demands originating from the ro ot node; at the destination no de of eac h demand orig ina ting from the 9 ro ot node, the difference betw een the sum of incoming flo ws a nd the sum o f outg oing flow s is the bandwidth o f the demand; and the sum o f incoming flo ws is equal to that of outgoing flo ws at any other no de. X h :( h,i ) ∈L f s hi − X j :( i,j ) ∈L f s ij = − d s , if i = s d k , if i = t k , ∀ k ∈ D s 0 , otherwis e , ∀ s ∈ S , ∀ i ∈ N (16) where d s = P k ∈D s d k . The num b er of this set of constraints is |S ||N | . Flow b ound c onstr ai n ts : for each tree, the to tal flo w load ov er eac h link do es not exceed the sum of all demand bandwidths originating from the r o ot no de and it is eq ua l to zero if no demand originating fr o m the ro o t no de is routed ov er the link. f s ij ≤ y s ij X k ∈D s d k , ∀ s ∈ S , ∀ ( i, j ) ∈ L (17) The n umber o f this set of constraints is | S ||L| . Link c ap acity c onstr aints : X s ∈S f s ij ≤ c ij , ∀ ( i, j ) ∈ L (18) The n umber o f this set of constraints is | L| . Path uniqueness c onstr aints : for each tr ee, the n umber of incoming links with non-zero flo ws is equal to zero at the origin no de; the n um b er of incoming links with non-zero flo ws is equal to one at the des tinat io n no de of each demand originating from the ro ot no de; and the n umber of incoming links with non- zero flo ws do es not exceed one at any other node. X h :( h,i ) ∈L y s hi = 0 , if i = s = 1 , if i ∈ T s ≤ 1 , otherwise , ∀ s ∈ S , ∀ i ∈ N (19) The n umber o f this set of constraints is | S ||N | . Path length c ons tr aints : for eac h tree, the length of the unique shortest pat h to ro ute a demand or ig inating from the ro ot no de is less than that o f an y other p o ssible path from the origin no de to the destination no de. y s ij = 0 ∧ X h :( h,j ) ∈L y s hj = 0 ⇒ l s j ≤ l s i + w ij y s ij = 0 ∧ X h :( h,j ) ∈L y s hj = 1 ⇒ l s j < l s i + w ij y s ij = 1 ⇒ l s j = l s i + w ij , ∀ s ∈ S , ∀ ( i, j ) ∈ L (20) 10 The logic constrain ts (20) can b e linearized a s follows: l s j ≤ l s i + w ij − ε X h :( h,j ) ∈L y s hj − y s ij l s j ≥ l s i + w ij − M (1 − y s ij ) , ∀ s ∈ S , ∀ ( i, j ) ∈ L (21) where ε and M are appropriate constan ts with 0 < ε ≪ M . The nu m b er of this set of constrain ts is 2 |S ||L| . Obje ctive function : max X ( i,j ) ∈L c ij − X s ∈S f s ij ! whic h is equiv alen t to min X ( i,j ) ∈L X s ∈S f s ij (22) Accordingly , the resulting complete mo del is presen ted as OBM: O ptimiz e (22) S ubj ect to (1 6) , (1 7) , (18) , (19) , (21) , (1 2) , (1 3) , (14) , (15) 4. Mo d el V erificatio n The correctness of OBM is v erified in this section. The ve rificatio n is divide d into tw o steps. First, DBM is v erified to b e a correct mo del of the unique shortest path routing problem. Second, OBM a nd DBM are mathematically prov ed to b e equiv alent concerning b oth the feasibility and the optimality of the problem, whic h implies that OBM is also a correct mo del of the problem. Since a relaxation of the uniq ue shortest path r outing problem has b een thoroughly studied and a corresp onding demand-ba sed fo r mulation for the relaxed problem has b een recognized a s b eing correct, the ve rificatio n of D BM is built on the correctness of the for- m ulation for the relaxed problem, the inte ge r multi-c ommo dity flow pr oblem (Ah uja et a l., 1993) with sub-path optimalit y condition. Also, the equiv alence b et we en O BM and DBM is demonstrated based on the pro of of the equiv a lence b et wee n t wo corresp onding mo dels of the relaxation, whic h are denoted as RDBM and ROBM, resp ectiv ely . RDBM: O ptimiz e (8) S ubj ect to (4 ) , (5) , (9) , (1) R OBM: O ptimiz e (22) S ubj ect to (16) , (17) , (18) , (19) , (12) , (13) 11 As can b e noted, R DBM is actually a relaxation of DBM ′ , whic h is equiv alent to DBM b y Prop o sition 1. 4.1 Correctness of DBM T o v erify the correctnes s of D BM, that of the equiv alen t mo del DBM ′ is prov ed. Apparen tly , the difference b et we en DBM ′ and RD BM lies in the path length constrain ts (6) and the additional link w eigh t v ariables (2) as well as the path length v ariables (3). In order to v erify that DBM ′ form ulates the unique shortest path routing problem correctly , constrain ts ( 6 ) in DBM ′ are prov ed to represen t correctly the a dditional path length constrain t s. Sp ecifically , the following t wo statemen ts are demonstrated to b e correct. In D BM ′ , the path length constrain ts (6), combin ed with the flow conserv ation constrain ts (4), guaran tee that: 1. The routing path of eac h dem a nd is a shortest path; and 2. The routing path of eac h dem a nd is a unique pa th. The tw o statemen ts are ve rified in Prop osition 2 and Prop osition 3, resp ectiv ely . Prop o- sition 2 is pro v ed b y demonstrating that the length of the routing path of eac h demand is less than or equal to tha t of an y other p ossible path. Th e pro of of Prop osition 3 is built on, with t wo lemm as, t he satisfaction o f the single-path requiremen t b y the relaxed problem RDBM, follow ed b y the pro of that the uniqueness requireme nt is satisfied b y DBM ′ . As the o riginal log ic constraints (7) are iden tical to the linearized constrain ts (6) , the following pro of is based on t he original constrain ts. Prop osition 2 Each r outing p ath r esulting fr om the solution to DBM ′ is a shortest p ath. Pr o of . Assume for demand k , P j = ( j 1 , j 2 ) → ( j 2 , j 3 ) → . . . → ( j n − 1 , j n ) , ( j l , j l +1 ) ∈ L , l = 1 , . . . , n − 1 , where j 1 = s k and j n = t k , is the assigned ro uting path, and P i = ( i 1 , i 2 ) → ( i 2 , i 3 ) → . . . → ( i m − 1 , i m ) , ( i q , i q +1 ) ∈ L , q = 1 , . . . , m − 1 , where i 1 = s k and i m = t k , is an y other possible a nd non-assigned path from s k to t k . Then, by the definition of the ro uting decision v ariables, x k j l j l +1 = 1, ∀ ( j l , j l +1 ) ∈ P j , l = 1 , . . . , n − 1 and ∃ ( i q , i q +1 ) ∈ P i , x k i q i q +1 = 0, q ∈ { 1 , 2 , . . . , m − 1 } . 12 As a result, according to constraints (7), on one hand, since ∀ ( i, j ) ∈ L , x k ij = 1 ⇒ l s k j = l s k i + w ij , l s k t k = l s k j n = l s k j n − 1 + w j n − 1 j n = l s k j 1 + w j 1 j 2 + . . . + w j n − 1 j n = l P j . (23) On the other hand, sinc e ∀ ( i, j ) ∈ L , x k ij = 0 ⇒ l s k j ≤ l s k i + w ij , l s k t k = l s k i m ≤ l s k i m − 1 + w i m − 1 i m ≤ l s k i 1 + w i 1 i 2 + . . . + w i m − 1 i m = l P i . (24) It th us follow s that l P j ≤ l P i from (23) and (24). Hence, the length of the routing path P j is less than or equal to the length o f a ny ot her p ossible path P i to route demand k . It is therefore pro ved that the routing path P j is the shortest one. In order to prov e that D BM ′ satisfies the pat h uniqueness constrain ts, the constrain ts are demonstrated to b e satisfied b y the relaxed problem RD BM first. Lemma 1 No optimal solution to RDBM c ontains flow lo ops. Pr o of . Supp ose x ∗ k ij , k ∈ D , ( i, j ) ∈ L is an optimal solution to RD BM, then all con- strain ts (4), (5), and (9) are s a tisfied b y x ∗ k ij , k ∈ D , ( i, j ) ∈ L . Sp ecifically , X h :( h,i ) ∈L x ∗ k hi − X j :( i,j ) ∈L x ∗ k ij = − 1 , if i = s k 1 , if i = t k 0 , otherwis e , ∀ k ∈ D , ∀ i ∈ N , (25) X k ∈D d k x ∗ k ij ≤ c ij , ∀ ( i, j ) ∈ L , (26) and X h :( h,i ) ∈L max k ∈D s x ∗ k hi ≤ 1 , i 6 = s, ∀ s ∈ S , ∀ i ∈ N . (27) Assume there would exist k l ∈ D and a lo op C : ( j 1 , j 2 ) → · · · → ( j n − 1 , j n ) → ( j n , j n +1 ) , ( j i , j i +1 ) ∈ L , i = 1 , . . . , n and j n +1 = j 1 , suc h that x ∗ k l j i j i +1 = 1 , i = 1 , . . . , n . Ob viously , X h :( h,i ) ∈C x ∗ k l hi − X j :( i,j ) ∈C x ∗ k l ij = 0 , ∀ i ∈ { j 1 , . . . , j n } . (28) Let y ∗ k ij = x ∗ k ij , if k 6 = k l or ( i, j ) / ∈ C 0 , otherwis e , ∀ k ∈ D , ∀ ( i, j ) ∈ L . (29) 13 Then, y ∗ k ij ∈ { 0 , 1 } , ∀ k ∈ D , ∀ ( i, j ) ∈ L and y ∗ k l j i j i +1 = 0 , ∀ ( j i , j i +1 ) ∈ C , i = 1 , . . . , n . In addition, according to (2 5), (28), and (29), X h :( h,i ) ∈L y ∗ k hi − X j :( i,j ) ∈L y ∗ k ij = X h :( h,i ) ∈L x ∗ k hi − X j :( i,j ) ∈L x ∗ k ij = − 1 , if i = s k 1 , if i = t k 0 , ot herwise , ∀ k ∈ D , ∀ i ∈ N , according to (26) and ( 29), X k ∈D d k y ∗ k ij ≤ X k ∈D d k x ∗ k ij ≤ c ij , ∀ ( i, j ) ∈ L , and according to (27) a nd (29), X h :( h,i ) ∈L max k ∈D s y ∗ k hi ≤ X h :( h,i ) ∈L max k ∈D s x ∗ k hi ≤ 1 , i 6 = s, ∀ s ∈ S , ∀ i ∈ N . Hence, y ∗ k ij , k ∈ D , ( i, j ) ∈ L satisfies all constraints ( 4), (5), and (9). It is therefore a feasible solution to RD BM. F urthermore, according t o (29), since ∀ k ∈ D , d k > 0 , X ( i,j ) ∈L X k ∈D d k y ∗ k ij = X ( i,j ) ∈L\C ∨ k ∈D : k 6 = k l d k y ∗ k ij + X ( i,j ) ∈C d k l y ∗ k l ij = X ( i,j ) ∈L\C ∨ k ∈D : k 6 = k l d k y ∗ k ij = X ( i,j ) ∈L\C ∨ k ∈D : k 6 = k l d k x ∗ k ij < X ( i,j ) ∈L\C ∨ k ∈D : k 6 = k l d k x ∗ k ij + X ( i,j ) ∈C d k l x ∗ k l ij = X ( i,j ) ∈L X k ∈D d k x ∗ k ij . Then, x ∗ k ij , k ∈ D , ( i, j ) ∈ L could no t b e an optimal solution to RDBM, whic h results in con tradiction. It hence prov es that no optimal solution to RDBM con tains flo w lo ops. Based on Lemma 1, the path uniqueness constrain ts ar e prov ed to b e satisfied by RDBM in Lemma 2. Lemma 2 The p ath uniqueness c onstr aints ar e satisfie d by RDBM. Pr o of . By Lemma 1, in RDBM, t he flow conserv ation constraints (4) at origin no des are equiv alen t to: X h :( h,i ) ∈L x k hi = 0 a nd X j :( i,j ) ∈L x k ij = 1 , i = s k , ∀ k ∈ D . (30) 14 Similarly , the flo w conserv atio n constraints (4) at destination no des a re equiv alen t to: X h :( h,i ) ∈L x k hi = 1 a nd X j :( i,j ) ∈L x k ij = 0 , i = t k , ∀ k ∈ D . (31) Since x k ij ∈ { 0 , 1 } , ∀ k ∈ D , ∀ ( i, j ) ∈ L , constrain ts ( 3 0) restrict that there is one, and only one, outgoing link with a non- zero flo w from the origin no de of demand k . Similarly , constrain ts (31) restrict that there is one, and only one, incoming link with a non-zero flow in to the destination no de of demand k . In additio n, constraints (4) guarantee that, at each in termediate no de, the num b er of incoming links with non-zero flow s is equal to the num b er of outgoing links with non-zero flows. Hence , for eac h demand k , the num b er of routing paths is no more t ha n o ne. Therefore, the pat h uniqueness constrain ts ar e satisfied. Prop osition 3 The p ath length c onstr aints in DBM ′ r estrict that the r esulting shortest p ath of e ach demand is a unique p ath. Pr o of . Since DBM ′ is a reduction of RDBM, the solution to the routing decision v ariables x k ij , k ∈ D , ( i, j ) ∈ L of DBM ′ is also a solution to those of R DBM. By Lemma 2, there is only one routing path for each demand. Supp o se for demand k , P j = ( j 1 , j 2 ) → ( j 2 , j 3 ) → . . . → ( j n − 1 , j n ) , ( j l , j l +1 ) ∈ L , l = 1 , . . . , n − 1 , where j 1 = s k , j n = t k , is the assigned routing path, and P i = ( i 1 , i 2 ) → ( i 2 , i 3 ) → . . . → ( i m − 1 , i m ) , ( i q , i q +1 ) ∈ L , q = 1 , . . . , m − 1 , where i 1 = s k and i m = t k , is an y other possible a nd non-assigned path from s k to t k . Then, b y the definition of the routing dec ision v ariables, x k j l j l +1 = 1 , ∀ ( j l , j l +1 ) ∈ P j , l = 1 , . . . , n − 1. As a result, according to constrain ts (7), since ∀ ( i, j ) ∈ L , x k ij = 1 ⇒ l s k j = l s k i + w ij , l s k t k = l s k j n = l s k j n − 1 + w j n − 1 j n = l s k j 1 + w j 1 j 2 + . . . + w j n − 1 j n = l P j . (32) As b oth P j and P i are paths b etw een s k and t k , they finally merge at one no de. Assume it is no de r and r = j p = i q , p ∈ { 2 , 3 , . . . , n − 1 , n } , q ∈ { 2 , 3 , . . . , m − 1 , m } . Then, b y the definition of the ro uting decision v aria bles, x k j p − 1 r = 1 a nd x k i q − 1 r = 0 . In addition, on one hand, P h :( h,r ) ∈L x k hr ≤ 1. On the other hand, P h :( h,r ) ∈L x k hr ≥ x k j p − 1 r + x k i q − 1 r = 1. Hence, P h :( h,r ) ∈L x k hr = 1 . 15 As a result, according to constrain ts (7), l s k t k = l s k i m = l s k i m − 1 + w i m − 1 i m = l s k r + w r i q +1 + . . . + w i m − 1 i m < l s k i q − 1 + w i q − 1 r + w r i q +1 + . . . + w i m − 1 i m ≤ l s k i 1 + w i 1 i 2 + . . . + w i m − 1 i m = l P i . (33) It follo ws that l P j < l P i from (32) and (33). It is therefore prov ed that path P j is the unique shortest path to route dem a nd k . Corollary 1 D BM is a c orr e ct mo del o f the unique shortest p a th r outing pr oblem. Pr o of . By Prop osition 2 and Prop osition 3, DBM ′ is a correct mo del of the uniqu e shortest pat h routing problem. Hence, as an equiv a lent model to D BM ′ , DBM is also a correct mo del of the pro blem. 4.2 Correctness of OBM By the pro of of Lemma 2, the flow conserv ation constraints (4 ) are iden tical to: X h :( h,i ) ∈L x k hi = 0 , X j :( i,j ) ∈L x k ij = 1 , if i = s k X h :( h,i ) ∈L x k hi = 1 , X j :( i,j ) ∈L x k ij = 0 , if i = t k X h :( h,i ) ∈L x k hi = X j :( i,j ) ∈L x k ij , otherw ise , ∀ k ∈ D , ∀ i ∈ N . (34) Hence, RDBM is equiv alen t to the following mo del: RDBM ′ : O ptimiz e (8) S ubj ect to (34) , (5) , (9) , (1) Lemma 3 In R O BM, the flow c onse rv a tion c onstr ain ts at origin no des ar e e quiva l e nt to: X h :( h,i ) ∈L f s hi = 0 and X j :( i,j ) ∈L f s ij = X k ∈D s d k , i = s, ∀ s ∈ S . 16 Pr o of . On one hand, according to ( 1 3), if i = s , X h :( h,i ) ∈L f s hi ≥ 0 , ∀ s ∈ S . On the other hand, according to (17) and (19), if i = s , X h :( h,i ) ∈L f s hi ≤ X h :( h,i ) ∈L y s hi X k ∈D s d k ! = X k ∈D s d k X h :( h,i ) ∈L y s hi = 0 , ∀ s ∈ S . Hence, X h :( h,i ) ∈L f s hi = 0 , i = s, ∀ s ∈ S . It can then b e deriv ed directly f r o m (16) that X j :( i,j ) ∈L f s ij = X k ∈D s d k , i = s, ∀ s ∈ S . The conclusion is therefore v erified. By Lemma 3, the flow conserv a tion constraints (16) are iden tical to: X h :( h,i ) ∈L f s hi = 0 , X j :( i,j ) ∈L f s ij = d s , if i = s X h :( h,i ) ∈L f s hi − X j :( i,j ) ∈L f s ij = d k , if i = t k , ∀ k ∈ D s X h :( h,i ) ∈L f s hi − X j :( i,j ) ∈L f s ij = 0 , otherw ise , ∀ s ∈ S , ∀ i ∈ N , (35) where d s = P k ∈D s d k . As a result, ROBM is equiv alent to the fo llo wing mo del: R OBM ′ : O ptimiz e (22) S ubj ect to (3 5) , (1 7) , (18) , (19) , (12) , (1 3) In the followin g , ROBM and RDBM are pro ved to b e equiv alent concerning the feasibilit y of the relaxed pro blem. The pro of is heav ily based o n the ve rificatio n of the equiv alence b et we en the t wo respectiv ely iden tical models, R OBM ′ and RDBM ′ . Prop osition 4 Ther e is a solution to R OBM if RDBM is fe asible. 17 Pr o of . Suppo se x ∗ k ij , k ∈ D , ( i, j ) ∈ L is a f easible solution to R D BM, and so to RD BM ′ . Then, all constrain ts (34), (5), and (9) are satisfied b y x ∗ k ij , k ∈ D , ( i, j ) ∈ L . Let y ∗ s ij = max k ∈D s x ∗ k ij , ∀ s ∈ S , ∀ ( i, j ) ∈ L , (36) and f ∗ s ij = X k ∈D s d k x ∗ k ij , ∀ s ∈ S , ∀ ( i, j ) ∈ L . (37) Ob viously , y ∗ s ij ∈ { 0 , 1 } a nd f ∗ s ij ∈ [0 , + ∞ ), ∀ s ∈ S , ∀ ( i, j ) ∈ L . According to (34), ∀ k ∈ D , if i = s k , P h :( h,i ) ∈L x ∗ k hi = 0 and P j :( i,j ) ∈L x ∗ k ij = 1. Then, according to (37), ∀ s ∈ S , if i = s , X h :( h,i ) ∈L f ∗ s hi = X h :( h,i ) ∈L X k ∈D s d k x ∗ k hi = X k ∈D s d k X h :( h,i ) ∈L x ∗ k hi = 0 , and X j :( i,j ) ∈L f ∗ s ij = X j :( i,j ) ∈L X k ∈D s d k x ∗ k ij = X k ∈D s d k X j :( i,j ) ∈L x ∗ k ij = X k ∈D s d k . Hence, at original no des, constrain ts (35) in R OBM ′ are satisfied b y f ∗ s ij , s ∈ S , ( i, j ) ∈ L . Also, according t o (34), ∀ k l ∈ D , if i = t k l , P h :( h,i ) ∈L x ∗ k l hi − P j :( i,j ) ∈L x ∗ k l ij = 1 and ∀ k ∈ D s k l , k 6 = k l , P h :( h,i ) ∈L x ∗ k hi − P j :( i,j ) ∈L x ∗ k ij = 0. Then, a ccording to (3 7), ∀ k l ∈ D , if s = s k l and i = t k l , X h :( h,i ) ∈L f ∗ s hi − X j :( i,j ) ∈L f ∗ s ij = X h :( h,i ) ∈L X k ∈D s d k x ∗ k hi − X j :( i,j ) ∈L X k ∈D s d k x ∗ k ij = X k ∈D s d k X h :( h,i ) ∈L x ∗ k hi − X k ∈D s d k X j :( i,j ) ∈L x ∗ k ij = X k ∈D s d k X h :( h,i ) ∈L x ∗ k hi − X j :( i,j ) ∈L x ∗ k ij = d k l X h :( h,i ) ∈L x ∗ k l hi − X j :( i,j ) ∈L x ∗ k l ij + X k ∈D s ,k 6 = k l d k X h :( h,i ) ∈L x ∗ k hi − X j :( i,j ) ∈L x ∗ k ij = d k l . 18 Hence, at destination no des, constrain ts ( 35) in ROBM ′ are satisfied by f ∗ s ij , s ∈ S , ( i, j ) ∈ L . Similarly , according to (34), ∀ k ∈ D , if i 6 = s k and i 6 = t k , P h :( h,i ) ∈L x ∗ k hi − P j :( i,j ) ∈L x ∗ k ij = 0. Then, according to ( 3 7), ∀ s ∈ D , ∀ i ∈ N , if i 6 = s and i / ∈ D s , X h :( h,i ) ∈L f ∗ s hi − X j :( i,j ) ∈L f ∗ s ij = X h :( h,i ) ∈L X k ∈D s d k x ∗ k hi − X j :( i,j ) ∈L X k ∈D s d k x ∗ k ij = X k ∈D s d k X h :( h,i ) ∈L x ∗ k hi − X k ∈D s d k X j :( i,j ) ∈L x ∗ k ij = X k ∈D s d k X h :( h,i ) ∈L x ∗ k hi − X j :( i,j ) ∈L x ∗ k ij = 0 . Hence, at other no des, constrain ts (3 5) in R O BM ′ are satisfied by f ∗ s ij , s ∈ S , ( i, j ) ∈ L . According to (36) a nd (3 7), ∀ s ∈ S , ∀ ( i, j ) ∈ L , f ∗ s ij = X k ∈D s d k x ∗ k ij ≤ X k ∈D s d k max k ∈D s x ∗ k ij = max k ∈D s x ∗ k ij X k ∈D s d k = y ∗ s ij X k ∈D s d k . Constrain ts (17) in ROBM ′ are then satisfied by y ∗ s ij , f ∗ s ij , s ∈ S , ( i, j ) ∈ L . According to (37) a nd (5 ), ∀ ( i, j ) ∈ L , X s ∈S f ∗ s ij = X s ∈S X k ∈D s d k x ∗ k ij = X k ∈D d k x ∗ k ij ≤ c ij . Constrain ts (18) in ROBM ′ are th us satisfied b y f ∗ s ij , s ∈ S , ( i, j ) ∈ L . According to (3 4), ∀ k ∈ D , if i = s k , P h :( h,i ) ∈L x ∗ k hi = 0 and so ∀ k ∈ D , ∀ ( h, i ) ∈ L , if i = s k , x ∗ k hi = 0 . Then, a ccording to (36), ∀ s ∈ S , if i = s , X h :( h,i ) ∈L y ∗ s hi = X h :( h,i ) ∈L max k ∈D s x ∗ k hi = X h :( h,i ) ∈L max k ∈D s 0 = 0 . Hence, at original no des, constrain ts (19) in R OBM ′ are satisfied b y y ∗ s ij , s ∈ S , ( i, j ) ∈ L . Also, according to (34), ∀ k l ∈ D , if i = t k l , P h :( h,i ) ∈L x ∗ k l hi = 1. The n, according to (36), ∀ k l ∈ D , if s = s k l and i = t k l , X h :( h,i ) ∈L y ∗ s hi = X h :( h,i ) ∈L max k ∈D s x ∗ k hi ≥ X h :( h,i ) ∈L x ∗ k l hi = 1 . In addition, according to (9), ∀ k l ∈ D , if i = t k l , P h :( h,i ) ∈L max k ∈D s k l x ∗ k hi ≤ 1. Then, according to (36), ∀ k l ∈ D , if s = s k l and i = t k l , X h :( h,i ) ∈L y ∗ s hi = X h :( h,i ) ∈L max k ∈D s x ∗ k hi ≤ 1 . 19 Th us, ∀ k ∈ D , if s = s k and i = t k , X h :( h,i ) ∈L y ∗ s hi = 1 . Hence, at destination no des, constraints (19) in ROBM ′ are satisfied b y y ∗ s ij , s ∈ S , ( i, j ) ∈ L . Similarly , according t o (9), ∀ s ∈ S , ∀ i ∈ N , if i 6 = s , P h :( h,i ) ∈L max k ∈D s x ∗ k hi ≤ 1 . Then, according to (36), ∀ s ∈ S , ∀ i ∈ N , if i 6 = s and i / ∈ T s , X h :( h,i ) ∈L y ∗ s hi = X h :( h,i ) ∈L max k ∈D s x ∗ k hi ≤ 1 . Hence, at other no des, constrain ts (1 9) in R O BM ′ are satisfied by y ∗ s ij , s ∈ S , ( i, j ) ∈ L . Since all constrain t s (35), (17), (18), and (19) in ROBM ′ are satisfied by y ∗ s ij and f ∗ s ij , s ∈ S , ( i, j ) ∈ L , it is a corresp onding feasible solution to R O BM ′ and also to R O BM, of the feasible solution to RD BM, x ∗ k ij , k ∈ D , ( i, j ) ∈ L . Prop osition 5 Ther e is a solution to RDBM if R O BM is fe asib le. Pr o of . Supp o se y ∗ s ij , f ∗ s ij , s ∈ S , ( i, j ) ∈ L is a feasible solution to R OBM, and so to R OBM ′ . Then, all constrain ts (3 5), (17), (18), and (19) are satisfie d b y y ∗ s ij , f ∗ s ij , s ∈ S , ( i, j ) ∈ L . Let x ∗ k ht k = y ∗ s k ht k , ∀ k ∈ D , ∀ ( h, t k ) ∈ L . According to constraints (19) at destination no des, P h :( h,t k ) ∈L y ∗ s k ht k = 1 , ∀ k ∈ D . Hence, ∀ k ∈ D , ∃ h : ( h, t k ) ∈ L , suc h that y ∗ s k ht k = 1 . ∀ k ∈ D , ∀ ( i, j ) ∈ L , if ( i, j ) 6 = ( i, t k ), x ∗ k ij is assigned as follows: Initialize x ∗ k ij ← 0 , ∀ k ∈ D , ∀ ( i, j ) ∈ L , ( i, j ) 6 = ( i, t k ) F or k ∈ D 0 i ← t k Do find h : ( h, i ) ∈ L , suc h that y ∗ s k hi = 1 x ∗ k hi ← 1 i ← h Un til i = s k (38) In the ab ov e ass ig ning pro cess (38), at no de i in eac h iteration of the inner lo op, o n one hand, according to (35 ) , X h :( h,i ) ∈L f ∗ s k hi ≥ X j :( t k ,j ) ∈L f ∗ s k t k j + d k ≥ d k > 0 , ∀ k ∈ D , 20 and according to (17), X h :( h,i ) ∈L f ∗ s k hi ≤ X h :( h,i ) ∈L y ∗ s k hi X k ′ ∈D s k d k ′ = X k ′ ∈D s k d k ′ X h :( h,i ) ∈L y ∗ s k hi , ∀ k ∈ D . Hence, X h :( h,i ) ∈L y ∗ s k hi > 0 , ∀ k ∈ D . On the other hand, according to (19), X h :( h,i ) ∈L y ∗ s k hi ≤ 1 , ∀ k ∈ D . Then, at no de i in eac h iteration of the inner loop, X h :( h,i ) ∈L y ∗ s k hi = 1 , ∀ k ∈ D . Therefore, a t no de i in each iteration of the inner lo op, ∃ h : ( h, i ) ∈ L , suc h t hat x ∗ k hi = y ∗ s k hi = 1 . Moreov er, ∀ k ∈ D , according to (3 5), the pro cess terminates at no de s k . According to (38), o b viously , x ∗ k ij ∈ { 0 , 1 } and x ∗ k ij ≤ y ∗ s k ij , ∀ k ∈ D , ∀ ( i, j ) ∈ L . Then, according to (19 ) at original no des, if i = s k , X h :( h,i ) ∈L x ∗ k hi ≤ X h :( h,i ) ∈L y ∗ s k hi = 0 , ∀ k ∈ D . In addition, the assigning process terminates at no de s k , ∀ k ∈ D , and so if i = s k , X j :( i,j ) ∈L x ∗ k ij = 1 , ∀ k ∈ D . Hence, at original no des, constrain ts (34) in RDBM ′ are satisfied by x ∗ k ij , k ∈ D , ( i, j ) ∈ L . According to (19) a t destination no des, if i = t k , X h :( h,i ) ∈L x ∗ k hi = X h :( h,i ) ∈L y ∗ s k hi = 1 , ∀ k ∈ D . 21 F urthermore, a ccording to (38) , if i = t k , x ∗ k ij = 0, ∀ k ∈ D , ∀ ( i, j ) ∈ L . Then, if i = t k , X j :( i,j ) ∈L x ∗ k ij = 0 , ∀ k ∈ D . Hence, at destination no des, constraints (34) in RD BM ′ are satisfied b y x ∗ k ij , k ∈ D , ( i, j ) ∈ L . According to (38), a t no de i in eac h iteration of the inner lo o p, X h :( h,i ) ∈L x ∗ k hi = X j :( i,j ) ∈L x ∗ k ij = 1 , ∀ k ∈ D , and at any other no de i ′ ∈ N , i ′ 6 = s k , i ′ 6 = t k , X h :( h,i ′ ) ∈L x ∗ k hi ′ = X j :( i ′ ,j ) ∈L x ∗ k i ′ j = 0 , ∀ k ∈ D . Then, if i 6 = s k , i 6 = t k , X h :( h,i ) ∈L x ∗ k hi − X j :( i,j ) ∈L x ∗ k ij = 0 , ∀ k ∈ D . Hence, at other no des, constrain ts (3 4) in RDBM ′ are satisfied b y x ∗ k ij , k ∈ D , ( i, j ) ∈ L . According to (35) a nd (1 8), X k ∈D d k x ∗ k ij = X s ∈S X k ∈D s d k x ∗ k ij ≤ X s ∈S f ∗ s ij ≤ c ij , ∀ ( i, j ) ∈ L . Hence, constrain ts (5) in RDBM ′ are satisfied b y x ∗ k ij , k ∈ D , ( i, j ) ∈ L . According to (38), x ∗ k ij ≤ y ∗ s k ij , ∀ k ∈ D , ∀ ( i, j ) ∈ L . Then, according to (19), if i 6 = s , X h :( h,i ) ∈L max k ∈D s x ∗ k hi ≤ X h :( h,i ) ∈L max k ∈D s y ∗ s k hi = X h :( h,i ) ∈L y ∗ s hi ≤ 1 , ∀ s ∈ S , ∀ i ∈ N . Hence, constrain ts (9) in RDBM ′ are satisfied b y x ∗ k ij , k ∈ D , ( i, j ) ∈ L . Since all constraints ( 34), (5), and (9) in RD BM ′ are satisfied by x ∗ k ij , k ∈ D , ( i, j ) ∈ L , it is a corresp onding feasible solutio n to RDBM ′ , and so t o RDBM, of the feasible solution to R OBM, y ∗ s ij , f ∗ s ij , s ∈ S , ( i, j ) ∈ L . Theorem 1 ROBM and RDBM ar e e quivalen t c onc erning the fe asibi l i ty of the r ela xe d pr ob- lem. Pr o of . The conclusion is deriv ed directly from Prop osition 4 and Prop osition 5. Based on t he pro of of the equiv alence b etw een ROBM and RDBM, the equiv alence b e- t w een OBM and D BM, concerning the f easibilit y of t he unique shortest pa th ro uting problem, is v erified as follows. 22 Prop osition 6 Ther e is a c orr esp onding solution sa tisfying the p ath length c onstr aints in OBM, for e ach solution sa tisfying the p ath length c onstr ain ts in DBM. Pr o of . Suppo se x ∗ k ij , k ∈ D , ( i, j ) ∈ L , w ∗ ij , ( i, j ) ∈ L , and l ∗ s i , s ∈ S , i ∈ N is a feasible solution to DBM and also to DBM ′ b y Prop osition 1 . Since RDBM is a relaxation of DBM ′ , x ∗ k ij , k ∈ D , ( i, j ) ∈ L is then a feasible solution to RDBM a nd satisfies all corr esp onding constrain ts. Let y ∗ s ij = max k ∈D s x ∗ k ij , ∀ s ∈ S , ∀ ( i, j ) ∈ L . Ob viously , y ∗ s ij ∈ { 0 , 1 } , ∀ s ∈ S , ∀ ( i, j ) ∈ L . Also, ∀ s ∈ S , ∀ ( i, j ) ∈ L , there are three cases: • Case 1: x ∗ k ij = 0 a nd P h :( h,j ) ∈L x ∗ k hj = 0 , ∀ k ∈ D s ; • Case 2: x ∗ k ij = 0, ∀ k ∈ D s and ∃ k l ∈ D s , P h :( h,j ) ∈L x ∗ k l hj = 1; • Case 3: ∃ k l ∈ D s , x ∗ k l ij = 1 . F or Case 1, on one hand, ∀ k ∈ D s , constrain ts (6) can be simplified as follows: l s k j ≤ l s k i + w ij and l s k j ≥ l s k i + w ij − M . On the other hand, since y ∗ s ij = max k ∈D s x ∗ k ij = 0 and P h :( h,j ) ∈L y ∗ s hj = 0, constrain ts (21) can b e simplified as follo ws: l s j ≤ l s i + w ij and l s j ≥ l s i + w ij − M . Hence, the simplified cons tr a in ts of (21) ar e identical to those of (6) for Case 1. F or Case 2, on one hand, constraints (6) can b e simplified as follows: l s k l j ≤ l s k l i + w ij − ε and l s k l j ≥ l s k l i + w ij − M , and ∀ k ∈ D s suc h tha t P h :( h,j ) ∈L x ∗ k hj = 0 , l s k j ≤ l s k i + w ij and l s k j ≥ l s k i + w ij − M . On the other hand, since y ∗ s ij = max k ∈D s x ∗ k ij = 0 but P h :( h,j ) ∈L y ∗ s hj = 1, constraints (21) can b e simplified as follo ws: l s j ≤ l s i + w ij − ε and l s j ≥ l s i + w ij − M . 23 Hence, the simplified cons tr a in ts of (21) ar e identical to those of (6) for Case 2. F or Case 3, on one hand, according to the sub-path o ptimalit y constraints, ∀ k ∈ D s , if x ∗ k ij = 0 , P h :( h,j ) ∈L x ∗ k hj = 0 . Then, constraints (6) can b e simplified as follows: l s k l j ≤ l s k l i + w ij and l s k l j ≥ l s k l i + w ij , and ∀ k ∈ D s suc h tha t x ∗ k ij = 0 , l s k j ≤ l s k i + w ij and l s k j ≥ l s k i + w ij − M . On the other hand, since y ∗ s ij = max k ∈D s x ∗ k ij = 1 and P h :( h,j ) ∈L y ∗ s hj = 1, constrain ts (21) can b e simplified as follo ws: l s j ≤ l s i + w ij and l s j ≥ l s i + w ij . Hence, the simplified cons tr a in ts of (21) ar e identical to those of (6) for Case 3. Since for all the t hree case s, y ∗ s ij , s ∈ S , ( i, j ) ∈ L results in the same path length constrain ts for OBM as those resulting from x ∗ k ij , k ∈ D , ( i, j ) ∈ L f or DBM, then, there is a corresp onding feasible solution satisfying the pa th length constrain ts (2 1) in OBM, provided that there is a feasible solution satisfying the path length constrain ts (6) in DBM. Prop osition 7 Ther e is a c orr esp onding solution sa tisfying the p ath length c onstr aints in DBM, for e ach solution s atisfying the p ath length c onstr a i n ts in OBM. Pr o of . Supp ose y ∗ s ij , f ∗ s ij , s ∈ S , ( i, j ) ∈ L , w ∗ ij , ( i, j ) ∈ L , a nd l ∗ s i , s ∈ S , i ∈ N is a feasible solution to OBM. Then since ROBM is a relaxation of O BM, y ∗ s ij , f ∗ s ij , s ∈ S , ( i, j ) ∈ L is also a feasible solution to ROBM and so satisfies all corresp onding constrain ts. According to the assigning pro cess (38), let x ∗ k ij , k ∈ D , ( i, j ) ∈ L b e the corresponding solution to RDBM. ∀ s ∈ S , ∀ ( i, j ) ∈ L , there are three cases: • Case 1: y ∗ s ij = 0 a nd P h :( h,j ) ∈L y ∗ s hj = 0; • Case 2: y ∗ s ij = 0 a nd P h :( h,j ) ∈L y ∗ s hj = 1; • Case 3: y ∗ s ij = 1 . 24 F or Case 1, constrain ts (21) can b e simplified as follo ws: l s j ≤ l s i + w ij and l s j ≥ l s i + w ij − M . According to (38), ∀ k ∈ D s , x ∗ k ij = 0 and P h :( h,j ) ∈L x ∗ k hj = 0 . Then, ∀ k ∈ D s , constrain ts (6) can b e simplified as follo ws: l s k j ≤ l s k i + w ij and l s k j ≥ l s k i + w ij − M . Hence, the simplified cons tr a in ts of (6) are iden tical to those of (21) fo r Case 1. F or Case 2, constrain ts (21) can b e simplified as follo ws: l s j ≤ l s i + w ij − ε and l s j ≥ l s i + w ij − M . According to (3 8), ∀ k ∈ D s , x ∗ k ij = 0 and ∃ k l ∈ D s , P h :( h,j ) ∈L x ∗ k l hj = 1. Then, constrain ts (6) can b e simplified a s follo ws: l s k l j ≤ l s k l i + w ij − ε and l s k l j ≥ l s k l i + w ij − M , and ∀ k ∈ D s suc h tha t P h :( h,j ) ∈L x ∗ k hj = 0 , l s k j ≤ l s k i + w ij and l s k j ≥ l s k i + w ij − M . Hence, the simplified cons tr a in ts of (6) are iden tical to those of (21) fo r Case 2. F or Case 3, constrain ts (21) can b e simplified as follo ws: l s j ≤ l s i + w ij and l s j ≥ l s i + w ij . According to (38), ∃ k l ∈ D s , x ∗ k l ij = 1 and P h :( h,j ) ∈L x ∗ k l hj = 1. In addition, according t o the sub-path optimality constrain ts, ∀ k ∈ D s , if x ∗ k ij = 0 , P h :( h,j ) ∈L x ∗ k hj = 0 . Then, constraints (6) can b e simplified a s follo ws: l s k l j ≤ l s k l i + w ij and l s k l j ≥ l s k l i + w ij , and ∀ k ∈ D s suc h tha t x ∗ k ij = 0 , l s k j ≤ l s k i + w ij and l s k j ≥ l s k i + w ij − M . Hence, the simplified cons tr a in ts of (6) are iden tical to those of (21) fo r Case 3. Since for all the three cases, x ∗ k ij , k ∈ D , ( i, j ) ∈ L results in the s a me path length constrain ts for DBM as those resulting f rom y ∗ s ij , s ∈ S , ( i, j ) ∈ L for OBM, then, there is a corresp onding f easible solution satisfying the path length constrain t s (6) in DBM, provid ed that there is a feasible solution satisfying the path length constrain ts (21) in OBM. 25 Corollary 2 T h e p ath le n gth c onstr a ints in OBM ar e e quival e nt to those in DBM, c o n c ern- ing t he fe asibility of the unique shortest p ath r outing pr oblem. Theorem 2 OB M a n d DBM and e quivalen t c onc erning the fe asibi l i ty of the unique s h ortest p ath r o uting pr oblem. Pr o of . By Prop osition 1, D BM is equiv alen t to DBM ′ . In addition, as discussed at the b egin of Section 4, OBM is a reduction of ROBM and DBM ′ is a reduction of RDBM. Besides the additional link we ig h t v ariables and path length v ariables, the difference b etw een OBM and ROBM are the path length constrain ts (21) and the difference b etw een DBM ′ and RDBM are the path length cons t rain ts (6). By Theorem 1 , R OBM and R D BM are equiv alent concerning the feasibility of t he re- laxed problem. By Corollary 2, the pa th length constrain ts in OBM are equiv alen t to the coun terparts in DBM, and so those in DBM ′ . Therefore, OBM is equiv alen t to DBM ′ , and so DBM, concerning the feasibility of the unique shortest path routing problem. Theorem 3 OB M and DB M and e quivalent c onc erning the optimality of the unique shortest p ath r o uting pr oblem. Pr o of . The conclusion follow s directly f rom Theorem 2 b y constructing the corresp onding optimal solutions b etw een OBM and DBM. Corollary 3 O B M is a c orr e ct mo de l of the unique shortest p ath r o uting pr oblem. 5. Comparisons b etw een the Two F orm ulations Concerning the unique sh o rtest path routing problem, it has b een sho wn that routing per- formances resulting from the prop osed complete formulations are muc h b etter than those deriv ed from the default metho ds, b y testing on 30 randomly generated data instances with com binations of differen t parameter scenarios. The resulting av erage maxim um utilization is 30 . 94% of that fro m using the hop- coun t metho d and 45 . 54% of that from using the inv-cap metho d. It hence demonstrates the significan t gain ac hiev ed b y form ulating the pro blem completely and solving it optimally . Bet w een the tw o complete formulations, compared with DBM, OBM has adv an t a ges on b oth constrain t structure for applying constraint generation algorithms and mo del size. 26 5.1 Constrain t Stru cture The constrain t structures of DBM and OBM are sho wn in Figure 3 and F igure 4, respectiv ely . Figure 3: Constrain t structure o f DBM In Figure 3 , the first row r epresen ts the link capacity constrain t s (5), the next four ro ws corresp ond to the flow conserv a tion constraints (4), and the last f o ur ro ws repres ent the path length constrain ts (6). Accordingly , columns corresp ond t o v ariables. As can b e seen, among the t hree sets of constrain ts, the flow conserv ation constrain ts and the link capacity constrain ts contain only t he routing decision v ariables, whereas the path length constraints couple the routing decis io n v ar ia bles with the link w eight v ariables and the path length v ariables. Hence, constraint generation alg o rithms suc h as the Benders decomp osition metho d (Benders, 1962) m ay b e conside r ed to b e the promising solution approac hes for the problem. The problem can b e decomp osed into one in teger prog ramming master problem and o ne linear pro gramming subproblem. The master problem deals with the flo w conse r v ation constrain ts and the link capacit y constraints, and so con tains the routing decision v ariables only . Accordingly , the subproblem cop es with the path length constrain ts. 27 Figure 4: Constrain t s t ructure of OBM Similarly , in Figure 4 , the first four ro ws represen t t he path uniqueness constraints (19), the next four rows corres p ond to the flow b ound constrain ts (17), the third four ro ws rep- resen t the flo w conserv ation constraints (16), the next row cor r esp o nds to the link capacit y constrain ts ( 1 8), and the la st f o ur ro ws represen t the path length constrain ts (21). Columns corresp ond to v ariables accordingly . As can b e noted, although DBM ha s a simpler constrain t structure, OBM has more flexibilit y to apply decomp osition algorithms to solv e the problem. As shown in Figure 4, with OBM, the problem can b e globally decomp osed into one master problem and tw o subproblems, instead of one master problem and one subproblem as with DBM. The master problem c ontains only the routing decision v ariables and the path uniqueness constraints accordingly . The first subproblem deals w it h t he auxiliary flow v ariables and the second subproblem cop es with t he link w eight v ariables and the path length v ariables. In addition, t he master problem can b e further decomp osed, with one indep enden t 28 subproblem corresp onding to each origin node. 5.2 Mo d el Size Compared with DBM, OBM defines explicitly the auxiliary flow v ariables and the flo w b ound constrain ts accordingly . How ev er, in general, |S | << |D | , and the size of OBM is m uc h smaller than that o f DBM. The mo del sizes of the tw o form ulations ar e as sho wn in T able 1, where #V ariables represen t s the n umber of v ariables and #Co n str aints denotes the n um b er of constraints. More concretely , the mo del sizes o f b oth the o riginal problems and the master problems of the tw o form ulatio ns on a randomly generated data instance with | N | = 50, |L| = 642, |D | = 1000, and |S | = 50 are sho wn in T able 2. As can b e seen from T able 2, with OBM, the n um b er of v ariables of the or ig inal prob- lem decreases from o ver 600 , 000 to 64 , 200 and the num b er of constrain ts drops from o ve r 1 , 000 , 0 00 to less than 38 , 000. In additio n, with OBM, b oth the n um b er of v a r ia bles and the n umber of constraints of the master problem decline 2 0 times. T able 1: Mo del sizes of D BM and OBM Mo del #V aria bles #Constrain ts DBM |D ||L | + |S ||N | + |L| |D ||N | + 2 |D ||L| + | L| OBM 2 |S ||L| + | S ||N | + |L| 2 |S ||N | + 3 | S ||L| + |L| T able 2 : Mo del sizes o f DBM and OBM of a large dat a instance Original Problem Master Problem #V aria bles #Constrain ts #V ariables #Constrain ts DBM 645 , 142 1 , 334 , 6 42 642 , 000 50 , 64 2 OBM 64 , 200 37 , 742 32 , 100 2 , 500 As a conclus io n, compared with DBM, OBM has a smaller mo del size and a more flexible constrain t structure for decomp osition algorithms suc h as the Benders decomp osition metho d to solv e t he problem. 6. Conclus ions With the a im of an exact solution approach to the unique shortest path ro uting problem on a verage data instances arising fr o m real- world applications, t wo complete a nd explic it 29 mathematical form ulat io ns with a p olynomial num b er of constrain ts for the problem are dev elop ed. A demand-based form ulation is first intro duced, based on t he study of the re- lationships b et w een the length of a shortest path and the w eigh ts of links that the path tra vers es. The problem is fur t her formulated as an origin-based mo del b y analyzing solution prop erties of the problem. The tw o formulations are then ma t hematically pro ve d to b e cor- rect a nd to b e equiv a len t concerning b o th the feasibility and the optimality of the problem. Based on the study of the constrain t structures and mo del size s of the t wo form ulations, t he origin-based form ulation is iden tified to be the b etter one fo r decomp osition algorithms suc h as the Benders decomp osition method to solv e the problem. The t w o fo rm ulations may b e generalized to other net w o r k flow a nd net w ork ro ut ing problems. Prosp ectiv e future w ork may lie in inv estigat ing p ossible impro veme nts concerning b oth problem form ulation and solution alg orithm to improv e the efficiency of the solution approac h prop osed. In particular, in v estigations ma y fo cus on p ossible impro ve ments related to three factors: the closeness b etw een the initial solution and the final solution to the master problem, the strength of cuts generated at eac h iteratio n, and the efficiency of an algo rithm to solve the in t eger progr a mming master problem. F or example, redundant constrain ts ma y b e generated to tighten the feasible region of t he initial master problem, strategies suc h a s activ e set metho d ma y b e applied to strengthen the cuts generated from the subproblems, and sc hemes suc h as the Lagrangian relaxation metho d ma y be embedded in to the solution algorithm to improv e the efficiency of solving the master problem at eac h iteratio n. References Ah uja, R. K ., T. L. Magna nti, J. B. Orlin. 1993. Network Flows: The ory, Algorithms, and Applic a tion s . Pren tice Hall. Ameur, W. B., E. G ourdin. 2003. In ternet Routing and Related T op ology Issues. SIAM J. Discr ete Math. 17 18– 4 9. Benders, J. 1 962. P ar titioning Procedures for Solving Mixed-V aria bles Progr a mming Prob- lems. Numer. Math. 4 238– 252. Bertsek as, D ., R. Gallager. 1 992. Data Networks . Pren tice Hall. Bley , A., T. Ko c h. 20 02. In t eger Programming Approache s to Access and Bac kb one IP- net w ork Planning. ZIB-Rep ort 02-41. 30 Ericsson, M., M. G . C. Resende, P . M. P ardalos. 2002. A Genetic Alg orithm for the W eight Setting Problem in OSPF Routing. J. Comb. O ptim. 6 299–333. F eldmann, A., A. Green b erg, C. L und, N. Reingold, J. Rexford, F. T rue. 2001. Deriving T raf- fic Demands for Op eratio nal IP Net w orks: Metho dology and Exp erience. IEEE/ACM T r ans. Netw. 9 265–280. F ortz, B., M. Thorup. 2000. In ternet T raffic Engineering by Optimizing OSPF W eigh ts. Pr o c. of 19th IEEE Conf e r enc e on Computer Communic a tions 519–528. Holm b erg, K., D. Y uan. 2004. Opt imizatio n of In ternet Proto col Netw or k Design and Routing. Networks 43 39 – 53. Lin, F. Y. S., J. L. W a ng . 199 3 . Minimax Op en Shortest Path First Routing Algorithms in Net w orks Supp orting the SMDS Services. Pr o c. of IEEE Interna tion a l Confer enc e on Communic ations 666–67 0. Mo y , J. 1998. OSPF A natomy o f an Internet R outing Pr oto c ol . Addison-W esley . Ramakrishnan, K. G., M . A. Ro drigues. 2001. Optimal Routing in Shortest-P a t h Data Net w ork. B el l L abs T e chnic al Journal 6 117–138. Zhang, C., R . Ro do ˇ sek . 20 05. Mo delling a nd Constrain t Hardness Characterisation of the Unique-P ath OSPF W eigh t Setting Problem. V.S. Sunderam et al., Eds. IC CS 2005, LNCS 3514 . Springer-V erlag, Berlin Heidelb erg. 804– 811. 31
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment