On (Omega-)Regular Model Checking
Checking infinite-state systems is frequently done by encoding infinite sets of states as regular languages. Computing such a regular representation of, say, the set of reachable states of a system requires acceleration techniques that can finitely c…
Authors: ** - **Axel Legay** – Carnegie Mellon University, Computer Science Department, Pittsburgh
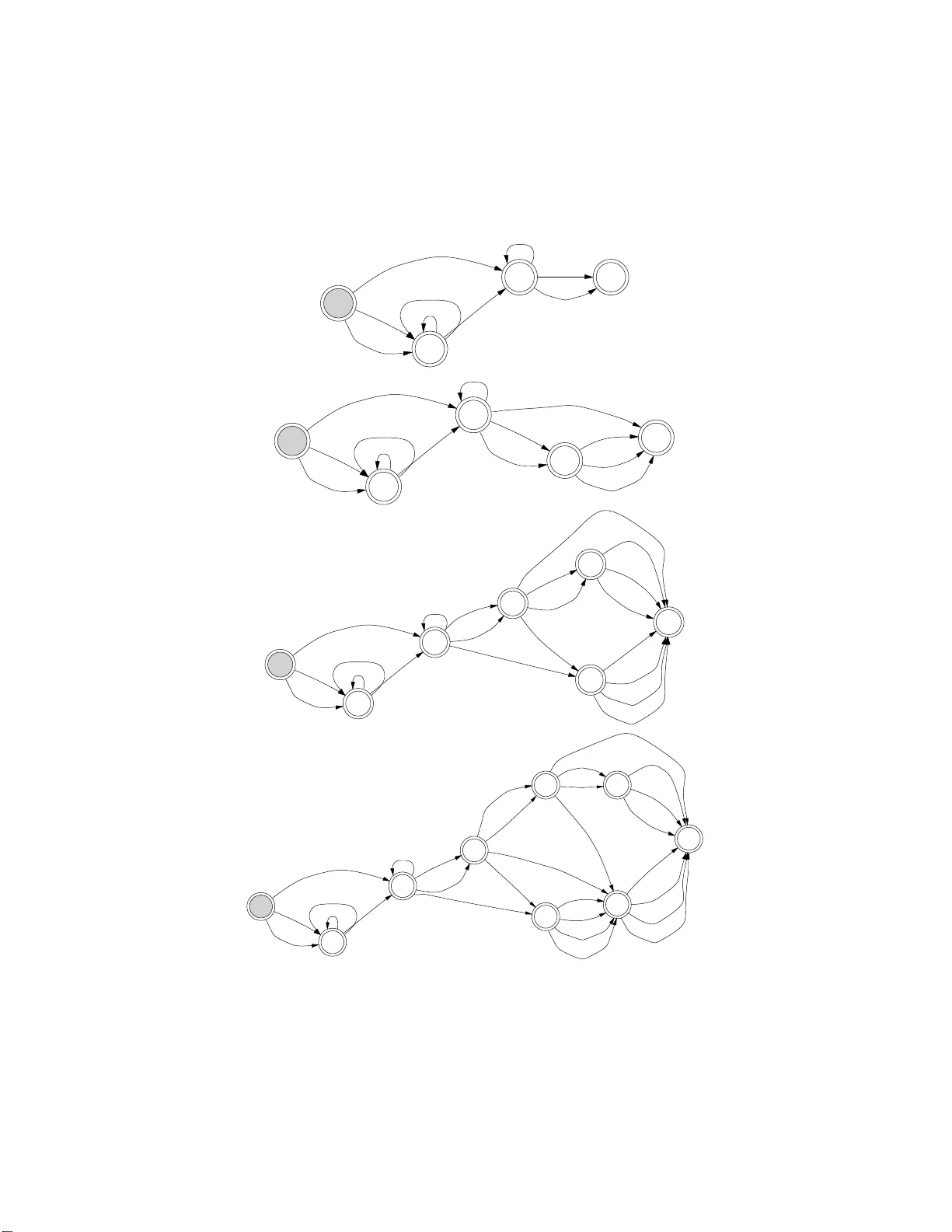
On (Omega-)Regular Mo del Chec king Axel Legay Car n e gie Mellon University Computer Science Department Pittsbugh, USA and Pierre W o lp er Universi´ e de Li ` ege Institut Montefiore, B28 4000 Li` ege, Belgium Chec king infinite-state systems is freque ntly done b y encoding infinite sets of states as regular languages. Co m puting suc h a regular represent ation of, s a y , the set of r eac hable states of a system requires acceleration tec hniques that can finitely compute the effect of an unbounded nu mber of transitions. Among the acceleration tec hniques that hav e b een proposed, one finds b oth sp ecific and gene r ic tec hniques. Sp ecific tec hniques exploit the particular type of system being analyzed, e.g. a system manipulating q ueues or i nt egers, whereas ge neri c te chniques only assume that the transition relation is represen ted b y a finite-state transducer, w hi c h has to b e iterated. In this paper, we in vestigat e the p ossibili t y of using generic tec hniques in cases where only sp ecific tec hniques ha v e been exploited so f ar . Finding that ex i sting generic tec hniques are often not applicable in cases easily handled by sp ecific technique s, we hav e developed a new approach to iterating transducers. Thi s new approach buil ds on earlier work, but exploits a n umber of new concept ual and algorithmic ideas, often induced with the help of experim en ts, that give it a br oad scope, as w ell as go od per f ormances. Categories and Sub ject Descriptors: D.2.4 [ F ormal Metho ds ]: Mo del chec king— Softwar e/Pr o gr am V e rific ation ; F.1.1 [ Automata ]: General T erms: V erification, Theo r y , Algorithms, Implementat i on Additional Key W ords and Phrases: (Omega-)Regular Model Chec king, T ransducers, Extrapola- tion, In finite-State System. Authors’ e-mai l : { legay,pw } @mo ntefiore.ulg.ac.be Authors’ website : http://www.monte fiore.ulg.ac.be/ ∼{ legay,pw } / Axel Leg ay i s supp orted b y a B.A.E.F. grant. The present article is an improv ed v er sion of [Boigelot et al. 2003], [B oi gelot et al. 2004], and [Lega y 2008]. Pe r mission to mak e digital/ha r d copy of all or p ar t of this material witho ut fee f or p ersonal or classro om use provided that the copies are not made or distributed for profit or commerci al adv an tage, the ACM copyrigh t/serve r notice, the title of the publication, and its date appear, and notice is given that cop ying is by perm ission of the ACM, Inc. T o copy otherwise, to republish, to p ost on serv ers, or to redistribute to lists requires prior sp ecific permission and/ or a fee. c 20YY ACM 1529-3785/YY/00-00 01 $5.00 ACM T ransactions on Computational Logic, V ol. V , No. N, 20 Y Y, Pages 1–0 ?? . 2 · A. Legay , and P . Wol p er 1. INTRODUCTION A t the heart of all the techniques that have b een prop osed for explor ing infinite state spaces, is a symbolic r epresentation that can finitely represent infinite sets of sta tes. In ear ly work on the s ub ject, this r epresentation was domain sp ecific, for example linear c o nstraints for s ets of real vectors. F or s everal years now, the idea that a generic finite-automaton ba sed represe ntation co uld be used in many settings has gained gro und, star ting with systems manipulating queues and integers [W olp er and Boig elot 1995 ; Boigelot et al. 199 7; W olp er and Boigelot 19 98; 2 000], then moving to parametric systems [K esten et al. 1997 ], and, finally , reaching systems using r eal v ar ia bles [Boigelo t et al. 19 98; Boigelo t et a l. 200 1; 2 005; Bo igelot and W o lpe r 200 2 ]. F o r exploring an infinite state space, one do es not only need a finite representation of infinite sets, but a lso techniques for finitely co mputing the effect of an un b ounded nu mber of transitions. Such techniques can b e do main s p e c ific or generic. Domain sp ecific tec hniques exploit the sp ecific pro pe rties and repre s entations o f the do- main b eing co nsidered and were, for instance, obtained for q ueues in [Bo ig elot and Go defroid 1996; Boua jjani and Habermehl 1997], for in tegers and reals in [Bo igelot 1999; Boigelo t and W olp er 2 0 02; Boigelot et al. 2003; Boigelot and Herbr eteau 2006; Finkel a nd Lero ux 200 2; Bardin et al. 2004 ; B ardin et al. 2 005], for pus h- down sy s tem in [Finkel e t a l. 199 7; Boua jjani et al. 199 7], a nd fo r lo s sy channels in [Ab dulla and Jonsso n 1996 ]. Generic techniques co nsider finite-a utomata rep- resentations and pr ovide algo rithms that op erate directly on this repres entation, mostly disregar ding the domain for which it is used. Generic techniques a pp e a red first in the context o f the verification of sys tems whose sta tes can b e enco ded by finite wor ds , suc h as para metric systems. The idea used there is that a config uration b eing a finite word, a tra nsition r elation is a relation on finite words, or equiv alently a lang uage of pairs of finite words. If this la nguage is regula r, it can b e represented by a finite state a utomaton, mo re sp ecifically a finite-state tr ansduc er , and the problem then becomes the one of iter- ating such a transducer . Finite state transducers are quite powerful (t he transition relation of a T uring machine can be mo deled by a finite-s tate transducer ), the flip side of the coin b eing that t he iter ation of such a tr ansducer is neither always computable, nor re gular. Nevertheless, there a re a num b e r o f practica lly relev ant cases in which the iteratio n o f finite-s ta te tr ansducers can b e computed and r e- mains finite-state. Identifying such cases a nd developing (partial) algo rithms for iterating finite-sta te transducer s has be e n the topic, refer red to a s “Regular Mo del Checking”, of a s eries of rec ent pap ers [Kesten et al. 1997; Bo ua jjani et al. 20 00; Boigelot et al. 20 03; 20 04; Jonsso n and Nilsson 2 000; Bo ua jjani et al. 200 4; T ouili 2001; Dams et a l. 2 002; Abdulla et al. 2003 ]. The question that initiated the work presented in this pap er is , whether the generic techniques fo r itera ting tra nsducers could b e fruitfully applied in cas es in which domain sp ec ific techniques had b een exc lus ively us e d s o far . In pa r ticular, one of o ur goals was to itera te finite-state tr ansducers repres enting a rithmetic re - lations (see [Boigelo t and W o lpe r 2 0 02] for a sur vey). Beyond mer e curiosity , the motiv ation was to b e able to itera te relations that are not in the form required by the domain sp ecific results, for ins ta nce disjunctive rela tions. Initial res ults were AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Checking · 3 very disapp ointing: the transducer for an arithmetic relation as s imple as ( x, x + 1 ) could no t be iter ated b y existing gener ic techniques. Howev er, look ing for the ro ots of this impo ssibility throug h a mix of experiments and theoretical work, and taking a prag ma tic approa ch to so lving the problems discov er ed, we were a ble to develop an appro ach to iter ating tra nsducers that ea sily handles a rithmetic rela tions, as well as many other ca ses. Interestingly , it is b y using a to ol for manipulating automata (LASH [LASH ]), lo ok ing a t examples b eyond the reach o f man ua l sim ula tion, and testing v ario us a lg orithms that the right intuitions, later to b e v alidated by theo- retical arguments, were developed. The gener al a pproach that ha s b een taken is similar to the one of [T ouili 20 01] in the sens e that, s tarting with a transducer T , we compute powers T i of T and attempt to generaliz e the sequence of tra nsducers obtained in or der to ca ptur e its infinite union. This is done by co mparing succe ssive p owers o f T and attempting to c ha racteriz e the differe nce betw een p ow ers of T as a set of s tates and transitions that are added. If this set o f added states , or incr ement , is alwa ys the same, it can be inser ted in to a lo op in order to capture all pow ers of T . How ever, for ar ithmetic transducers c omparing T i with T i +1 did no t y ield an incr ement that co uld b e rep eated, though comparing T 2 i with T 2 i +1 did. So , a first idea we used is not to alwa ys compare T i and T i +1 , but to extra ct a sequence of samples from the s equence of p owers of the transduce r, and work with this sequence o f s amples. Giv en the binary enco ding used for r epresenting arithmetic rela tions, sampling at p ow er s of 2 works well in this c a se, but the sa mpling approa ch is gener al and different sample sequences ca n b e us ed in other cases . Now, if we only consider sample p ow e r s T i k of the tra nsducers and compute S k T i k , this is not neces sarily equiv alent to computing S i T i . F o rtunately , this pr oblem is easily so lved by consider ing the reflexive trans ducer, i.e., T 0 = T ∪ T I d where T I d is the ident ity transducer , in which case w o rking with a n infinite subsequence of samples is sufficient. Once the automata in the seque nc e be ing cons idered a re constructed and com- pared, a nd tha t a n incr ement c orresp o nding to the difference b etw een successive elements ha s b een identified, the next step is to allow this increment to be rep eated an arbitra ry num b er of times by incorp o rating it into a lo op. There a r e some techn ic al issues a b out how to do this, but no ma jor difficulty . Once the r esult- ing “extra po lated” transducer has b een obta ined, one still needs to chec k that the applied extr ap olation is s afe (contains all elements of the s e quence) and is precis e (contains no more). An easy to check s ufficient condition for the extrap ola tion to be safe is that it remains unchanged when b eing comp osed with itself. Checking preciseness is more delica te, but we hav e developed a pr o cedure that embo dies a sufficient criterio n for doing so . The idea is to chec k that any b ehavior o f the transducer with a g iven num b er k of co pies of the increment, can b e obta ined by comp osing transducers with less than k copies of the increment. This is done by augmenting the tr ansducers to b e chec ked with counters and proving that one can restrict theses co unt e r s to a finite ra ng e, hence a llowing finite-state techniques to be used. T aking adv ant a ge o f the fact tha t our extra p olation technique works on automata, not just o n transducers, we consider co mputing reachable s ta tes b oth by c omputing the clos ur e of the transducer representing the transition relation, and b y repeatedly AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 4 · A. Legay , an d P . Wol p er applying the trans ducer to a set of initial states. The first appro a ch yields a more general ob ject and is e ssential if o ne wishes to extend the metho d to the verification of temp or al pr op erties ([Boua jjani et al. 200 0; Pnueli a nd Sha har 2 000; Ab dulla et al. 200 4 ; Boua jjani e t al. 2004 ]), but the second is often less demanding fr o m a computational p oint of view and can handle case s that ar e out of reach for the first. Precisenes s is not always p oss ible to chec k when working with state sets ra ther than transducers, but this just amounts to saying that what is computed is p o ssibly an ov erappr oximation of the set of reachable states, a situation which is known to be pragmatica lly unproblematic. Going fur ther , the pro blem of using Regular Mo del Checking technique for sys- tems whose states ar e re pr esented by infinite (omeg a) words ha s b e e n addres sed. This ma kes the repr esentation o f se ts of reals po ssible as desc r ib ed in [Boigelo t et a l. 2001; Boig elot e t al. 200 3 ]. T o avoid the hard to implement a lgorithms needed for some op eratio ns on infinite-word automata, only o mega-reg ular sets that can b e defined by weak deterministic B ¨ uchi auto mata [Muller et al. 1986] ar e considered. This is of course restr ictive, but as is sho wn in [Boigelot et al. 2001; 2005], it is suf- ficient to handle sets of re a ls defined in the first-or der theory of linear constr aints. Moreov e r using such a representation leads to alg orithms that ar e very similar to the ones used in the finite word c a se, and a llows us to work with reduced determin- istic a utomata as a normal for m. Due to these adv antages and pr op erties, one can show that the technique dev elop ed for the finite word case can dir ectly b e ada pted to weak deterministic B ¨ uchi automata up to a lgorithmic mo difications. Our technique ha s b ee n implemented in a too l called T(0)RMC (T o o l for (Omega- )Regular Mo del Chec k ing ), which has b een tested on se veral classe s o f infinite-state systems. It is worth mentioning that the ability of T(O)RMC to extr ap olate a sequence of automa ta has other applicatio ns than so lving the ( ω -)Reg ular Reach- ability Pr oblems. As an ex a mple, the to ol has b een used in a se mi- algor ithm to compute the conv ex hull of a set of int eg er vectors [Cantin et a l. 20 07; 200 8 ]. T(O)RMC was also used to compute a s ymbolic repres e nt a tion of the simulation relation b etw een the states of several classes of infinite-s tate systems with the aim of verifying tempo ral prop erties [Bo ua jjani et al. 2004]. Structure of the pap er. The pap er is s tructured a s follows. In Section 2, we recall the elementary definitions on automata theo ry that will b e used thro ugh- out the r est of the pap er. Section 3 intro duces c ounter-wor d automata , a cla ss of counter automata that will b e used by our preciseness technique. Sectio n 4 presents the ( ω -)Regular Mo del Checking framework as well as the problems we wan t to solve. Sections 5 , 6, 7 , 8, and 9 de s crib e our main results. Implementation and exp eriments are discusse d in Section 10. Finally , Sections 11 a nd 12 contain a compar is on with other works on the same topic a nd several directions for future resear ch, resp ectively . 2. BA CKGROUND ON AUTOMA T AA TH EORY In this s ection, we introduce se veral nota tions, co ncepts, and definitions tha t will be used throughout the rest of this pap er. The set of natura l num b ers is denoted by N , and N 0 is used for N \ { 0 } . AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Checking · 5 2.1 Relations Consider a s et S , a set S 1 ⊆ S , and tw o binary 1 relations R 1 , R 2 ⊆ S × S . The identit y relation on S , denoted R S id (or R id when S is clea r from the context) is the set { ( s, s ) | s ∈ S } . The image of S 1 by R 1 , denoted R 1 ( S 1 ), is the set { s ′ ∈ S 1 | ( ∃ s ∈ S 1 )(( s, s ′ ) ∈ R 1 ) } . The c omp osition of R 1 with R 2 , denoted R 2 ◦ R 1 , is the set { ( s, s ′ ) | ( ∃ s ′′ )(( s, s ′′ ) ∈ R 1 ∧ ( s ′′ , s ′ ) ∈ R 2 ) } . The i th p ower of R 1 ( i ∈ N 0 ), denoted R i 1 , is the r e lation o bta ined by c o mp o sing R 1 with itself i times. The zer o-p ower of R 1 , denoted R 0 1 , corresp onds to the identit y r elation. The tr ansitive closur e of R 1 , denoted R + 1 , is g iven b y S i =+ ∞ i =1 R i 1 , its r eflexive tr ansitive closur e , denoted R ∗ , is given by R + 1 ∪ R S id . The domain of R 1 , denoted Dom ( R 1 ), is g iven b y { s ∈ S | ( ∃ s ′ ∈ S )(( s, s ′ ) ∈ R 1 ) } . 2.2 W ords and La nguages An alphab et is a (nonempty) finite set of distinct sy mbo ls. A finite wor d of length n ov er an alphab et Σ is a mapping w : { 0 , . . ., n − 1 }→ Σ. An infinite wor d , also called ω − word, over Σ is a ma pping w : N → Σ. W e denote by the term wor d either a finite w ord or an infinite word, dep ending on the context. The length o f the finite word w is denoted b y | w | . A finite word w of length n is often r epresented by w = w (0) · · · w ( n − 1). An infinite w or d w is often represented by w (0) w (1) · · · . The sets of finite and infinite words over Σ a r e de no ted by Σ ∗ and by Σ ω , resp ectively . W e define Σ ∞ = Σ ∗ ∪ Σ ω . A fi nite-wor d (re s p e ctively infinite-wor d) language ov er Σ is a (p ossibly infinite) set of finite (r esp ectively , infinite) words ov er Σ. Consider L 1 and L 2 , tw o finite-word (re s p. infinite-word) lang uages. The union of L 1 and L 2 , denoted L 1 ∪ L 2 , is the languag e that contains all the w o rds that belo ng either to L 1 or to L 2 . The interse ction o f L 1 and L 2 , denoted L 1 ∩ L 2 , is the language that contains all the words that b elo ng to b oth L 1 and L 2 . The c omplement of L 1 , de- noted L 1 is the la ng uage that co ntains all the words over Σ that do no t b elong to L 1 . W e alos introduce synchr onous pr o duct a nd pr oje ction , whic h ar e tw o o pe r ations needed to define relations betw e e n languages . Definition 2.1. Co ns ider L 1 and L 2 t wo langua ges over Σ. —If L 1 and L 2 are finite-word languages , the s y nchronous pro duct L 1 ¯ × L 2 of L 1 and L 2 is defined a s fo llows L 1 ¯ × L 2 = { ( w (0) , w (0) ′ ) . . . ( w ( n ) , w ( n ) ′ ) | w = w (0) w (1) . . .w ( n ) ∈ L 1 ∧ w ′ = w (0) ′ w (1) ′ . . .w ( n ) ′ ∈ L 2 } . —If L 1 and L 2 are ω -la nguages, the synchronous pro duct L 1 ¯ × L 2 of L 1 and L 2 is defined as follows L 1 ¯ × L 2 = { ( w (0) , w (0) ′ )( w (1) , w (1) ′ ) · · · | w = w (0) w (1) . . . ∈ L 1 ∧ w ′ = w (0) ′ w (1) ′ · · · ∈ L 2 } . The languag e L 1 ¯ × L 2 is defined ov er the alphab et Σ 2 . 1 The term “binary” wil l be dropped in t he rest of the paper. AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 6 · A. Legay , an d P . Wol p er Definition 2 .1 dir ectly gener alizes to synchronous pr o ducts o f mo r e than tw o lan- guages. Given tw o finite (resp ectively , infinite) words w 1 , w 2 (with | w 1 | = | w 2 | if the w ords are finite) and t wo la ng uages L 1 and L 2 with L 1 = { w 1 } and L 2 = { w 2 } , we use w 1 ¯ × w 2 to denote the unique word in L 1 ¯ × L 2 . Definition 2.2. Supp ose L a language over the a lphab et Σ n and a natura l 1 ≤ i ≤ n . The pro jection of L on all its comp onents except comp onent i , denoted Π 6 = i ( L ), is the language L ′ such that Π 6 = i ( L ) = { w 1 ¯ × . . . ¯ × w i − 1 ¯ × w i +1 ¯ × . . . ¯ × w n | ( ∃ w i )( w 1 ¯ × . . . ¯ × w i − 1 ¯ × w i ¯ × w i +1 ¯ × . . . ¯ × w n ∈ L ) } . 2.3 Automata Definition 2.3. An auto ma ton ov er Σ is a tuple A = ( Q, Σ , Q 0 , △ , F ), where — Q is a finite set of st ates , —Σ is a fin ite alphab et, — Q 0 ⊆ Q is the set of initial states , — △ ⊆ Q × Σ × Q is a finite tr ansit ion r elation , and — F ⊆ Q is the set of accepting states (the states in Q \ F ar e the nonac c epting states). Let A = ( Q , Σ , Q 0 , △ , F ) b e an automaton. If ( q 1 , a, q 2 ) ∈ △ , then we say that there is a tr ans ition fro m q 1 (the origin ) to q 2 (the destination ) la b e led by a . W e sometimes abuse the nota tions, and wr ite q 2 ∈ △ ( q 1 , a ) ins tea d of ( q 1 , a, q 2 ) ∈ △ . Two transitions ( q 1 , a, q 2 ) , ( q 3 , b, q 4 ) ∈ △ ar e c onse cu tive if q 2 = q 3 . Given tw o states q , q ′ ∈ Q a nd a finite word w ∈ Σ ∗ , we write ( q , w , q ′ ) ∈ △ ∗ if there e x ist states q 0 , . . . , q k − 1 and w 0 , . . . , w k − 2 ∈ Σ suc h that q 0 = q , q k − 1 = q ′ , w = w 0 w 1 · · · w k − 2 , and ( q i , w i , q i +1 ) ∈ △ for all 0 ≤ i < k − 1. Given tw o states q , q ′ ∈ Q , we s ay that the state q ′ is r e achable from q in A if ( q , a, q ′ ) ∈ △ ∗ . The automaton A is c omplete if for each s ta te q ∈ Q a nd symbol a ∈ Σ, there exists a t least one s ta te q ′ ∈ Q such that ( q , a, q ′ ) ∈ △ . An automato n can easily be completed b y adding an extra nonaccepting state. A fin it e run of A o n a finite word w : { 0 , . . ., n − 1 }→ Σ is a la be ling ρ : { 0 , . . ., n }→ Q such that ρ (0) ∈ Q 0 , and ( ∀ 0 ≤ i ≤ n − 1 )(( ρ ( i ) , w ( i ) , ρ ( i + 1)) ∈ △ ). A finite r un ρ is ac c epting for w if ρ ( n ) ∈ F . An infinite run of A on an infinite word w : N → Σ is a lab eling ρ : N → Q such that ρ (0) ∈ Q 0 , and ( ∀ 0 ≤ i )(( ρ ( i ) , w ( i ) , ρ ( i + 1)) ∈ △ ). An infinite run ρ is ac c epting for w if inf ( ρ ) ∩ F 6 = ∅ , where inf ( ρ ) is the s et o f states that are visited infinitely often by ρ . W e distinguish b etw een finite-wor d automata that are auto ma ta acce pting finite words, and B ¨ uchi automata tha t a re automata accepting infinite words. A finite- word automaton accepts a finite word w if there ex ists an accepting finite run for w in this automaton. A B ¨ uchi automaton accepts an infinite word w if there exis ts an accepting infinite run for w in this automaton. The set of words accepted by A is the language ac c epte d by A , and is deno ted L ( A ). Any lang uage that can b e represented by a finite-word (res pe ctively , B ¨ uchi) automato n is sa id to b e re gular AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Checking · 7 (resp ectively , ω -re gular ). The a uto maton A may behav e nondeterministicaly on a n input word, since it may hav e many initial states a nd the transition r elation may s pe c ify many p os s ible tran- sitions for each s tate and s ymbol. If | Q 0 | = 1 and for all state q 1 ∈ Q and symbo l a ∈ Σ there is at most o ne sta te q 2 ∈ Q such that ( q 1 , a, q 2 ) ∈ △ , then A is deter- ministic . In o rder to emphasize this prope r ty , a deterministic automaton is denoted as a tuple ( Q, Σ , q 0 , δ, F ), where q 0 is the unique initial state and δ : Q × Σ → Q is a partial function deduced fro m the tra nsition relation by setting δ ( q 1 , a ) = q 2 if ( q 1 , a, q 2 ) ∈ △ . Op eratio ns on la nguages dir ectly transla te to op erations on au- tomata, and s o do the notations. One can decide weither the la ng uage accepted by a finite-word or a B ¨ uchi automato n is empt y or not. It is also known that finite-word a utomata are closed under deter- minization, complementation, union, pro jection, a nd intersection [Hop cro ft 1971 ]. Moreov e r , finite-word automa ta admit a minimal form, which is unique up to iso- morphism [Hop croft 19 71]. Though the union, intersection, synchronous pro duct, and pro jectio n of B ¨ uch i au- tomata ca n b e computed efficiently , the complementation op eration requires in- tricate a lgorithms that not only are worst-cas e exp onential, but are also har d to implemen t a nd optimize (see [V a rdi 2 0 07] for a survey). The cor e problem is tha t there are B ¨ uchi automata that do no t admit a deterministic/minimal form. T o working with infinite-word a utomata that do own the same prop erties a s finite- word automata , we will r e strict our selves to we ak automata [Muller et a l. 1 986] defined hereafter. Definition 2.4. F or a B ¨ uchi automaton A = (Σ , Q, q 0 , δ, F ) to b e weak, there has to b e partition of its state set Q into disjoint subsets Q 1 , . . . , Q m such that for each of the Q i , either Q i ⊆ F , or Q i ∩ F = ∅ , and there is a partia l order ≤ o n the sets Q 1 , . . . , Q m such that for every q ∈ Q i and q ′ ∈ Q j for which, for some a ∈ Σ, q ′ ∈ δ ( q , a ) ( q ′ = δ ( q , a ) in the deterministic c a se), Q j ≤ Q i . A weak automaton is thus a B ¨ uchi automaton such that each of the str ongly co n- nected co mpo nents of its graph co nt a ins either only accepting o r only non-acc e pting states. Not all ω -r egular lang uages can be accepted by deterministic weak B ¨ uchi a uto mata, nor even by nondeterministic weak automata . Howev er, ther e are algor ithmic ad- v an ta ges to working with weak a utomata : deterministic weak automa ta can b e complemented simply by inv erting their a ccepting and non-acce pting s tates; and there exists a simple determinization pro cedur e for weak automa ta [Safra 199 2], which pro duces B ¨ uchi a utomata that a r e deterministic, but generally not w ea k. Nevertheless, if the r e presented languag e can be accepted by a de ter ministic weak automaton, the r esult of the de ter minization pro cedure will b e inher ently we ak a c- cording to the definition b elow [Boigelo t et al. 20 01] and thus eas ily tra nsformed int o a weak automaton. AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 8 · A. Legay , an d P . Wol p er Definition 2.5. A B ¨ uchi a utomaton is inher ently we ak if none o f the r e achable strongly connected comp one nts of its transition gr aph con ta in both a ccepting (vis- iting at least one accepting state) a nd no n-accepting (not v isiting any accepting state) cycles. This g ives us a pr agmatic wa y of staying within the r ealm of deterministic weak B ¨ uc hi automata. W e start with sets represented by such automa ta. This is pr e- served by union, intersection, synchronous pro duct, and co mplement a tion op er a- tions. If a pro jection is needed, the r esult is determinized by the known simple pro cedure. Then, either the r e s ult is inherently weak and we can pr o ceed, o r it is not a nd we a re for ced to use the cla ssical a lgorithms for B ¨ uchi automata . The latter cases might never occur, for instance if we a r e w or king with auto ma ta representing sets o f reals definable in the first-o rder theo ry of linear cons traints [Bo ig elot et al. 2001]. A final a dv ant a ge of weak deterministic B ¨ uc hi automata is that they admit a min- imal for m, which is unique up to isomorphism [L¨ o ding 20 01]. 2.4 Relations on Auto mata Sta t e s W e will also us e the following definitions. Definition 2.6. Given tw o automata A 1 = ( Q 1 , Σ 1 , Q 01 , △ 1 , F 1 ) and A 2 = ( Q 2 , Σ 2 , Q 02 , △ 2 , F 2 ), we define —the forward equiv alence relation E f , ⊆ Q 1 × Q 2 , which is an equiv alence relation on s tates o f A 1 and A 2 with ( q 1 , q 2 ) ∈ E f iff L F 1 q 1 ( A 1 ) = L F 2 q 2 ( A 2 ); —the backward equiv alence relation E b ⊆ Q 1 × Q 2 , which is an equiv alence relation on s tates o f A with ( q 1 , q 2 ) ∈ E b iff L q 1 Q 01 ( A 1 ) = L q 2 Q 02 ( A 2 ). Definition 2.7. Given tw o automata A 1 = ( Q 1 , Σ , Q 01 , △ 1 , F 1 ) and A 2 = ( Q 2 , Σ , Q 02 , △ 2 , F 2 ), a relation R ⊆ Q 1 × Q 2 is an isomorphism b etw een A 1 and A 2 if and only if — R is a bijection, —for e ach a ∈ (Σ ∪ { ǫ } ) and q 1 , q 2 ∈ Q 1 , ( q 1 , a, q 2 ) ∈ △ 1 ⇔ ( R ( q 1 ) , a, R ( q 2 )) ∈ △ 2 , —for each ( q , q ′ ) ∈ R , q ∈ Q 01 ⇔ q ′ ∈ Q 02 , —for each ( q , q ′ ) ∈ R , q ∈ F 1 ⇔ q ′ ∈ F 2 . 2.5 T rans ducers In this paper, we w ill co ns ider r elations that are defined o ver sets of w or ds. W e use the following definitions taken from [Nilsson 200 1]. F or a finite-word (resp ectively , infinite-word) lang uage L ov er Σ n , we deno te by ⌊ L ⌋ the finite-word (res pe c tively , infinite-word) rela tion over Σ n consisting of the s et of tuples ( w 1 , w 2 , . . ., w n ) such that w 1 ¯ × w 2 ¯ × . . . ¯ × w n is in L . The a rity of such a relation is n . Note that for n = 1, we hav e that L = ⌊ L ⌋ . The r elation R id is the identity r elation , i.e., R id = { ( w 1 , w 2 , . . ., w n ) | w 1 = w 2 = . . . = w n } . A relation R defined ov er Σ n is ( ω -)r e gu lar if there exis ts a ( ω -)regular languag e L ov er Σ n such that ⌊ L ⌋ = R . AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Checking · 9 0 1 1,1 0,0 2 1,0 0,0 1,1 0,1 1,0 Fig. 1. A transducer for ( x, x + 1) ∪ ( x, x ). The initial state of the automaton is co l ored in gr a y , and the final state is surrounded b y a double circle (this conv en tion wil l be follow ed throughout the rest of th e paper). W e now intro duce transducers that are automata for represe nting ( ω - )regular rela- tions over Σ 2 . Definition 2.8. A transducer ov er Σ 2 is an automato n T ov er Σ 2 given by ( Q, Σ 2 , Q 0 , △ , F ), wher e — Q is the finite set of s t ates , —Σ 2 is the fi n ite alphab et, — Q 0 ⊆ Q is the set of initial states , — △ : Q × Σ 2 × Q is the t ra n s ition r elation , and — F ⊆ Q is the set of accepting states (the states that are not in F are the nonac c epting s ta tes). Given an alphab et Σ, the tr ansducer representing the identit y rela tion over Σ 2 is denoted T Σ id (or T id when Σ is clear from the context). All the concepts and op erations defined for finite automata ca n b e use d with transducer s. The only reason to particularize this class of automata is that some op era tio ns, such as comp osition, ar e sp ecific to r e lations. In the sequel, we use the ter m “transducer ” instead of “automa to n” when using the automato n as a representation of a relation rather than as a repre sentation of a la nguage. W e sometimes abuse the nota tions and write ( w 1 , w 2 ) ∈ T instead of ( w 1 , w 2 ) ∈ ⌊ L ( T ) ⌋ . Given a pa ir ( w 1 , w 2 ) ∈ T , w 1 is the input wor d , and w 2 is the output wor d . The tra ns ducers we consider here are often c alled structur e-pr eserving . Indeed, when following a transition, a sym b ol of the input word is replaced by exactly one symbol of the output word. Example 2.9. If p ositive inte gers ar e enc o de d in binary with an arbitr ary num- b er of le ading 0 ’s al lowe d, and ne gative numb ers ar e r epr esente d using 2 ’s c omple- ment al lowing for an arbitr ary nu mb er of le ading 1 ’s, the tr ansduc er of Figur e 1 r epr esents t he r elation ( x, x + 1) ∪ ( x, x ) (se e [Boigelo t and Wolp er 2002] for a ful l description of t he enc o ding). Given tw o transduce r s T 1 and T 2 ov er the alphab et Σ that represents tw o rela- tions R 1 and R 2 , re sp ectively . The c omp osition of T 1 by T 2 , denoted T 2 ◦ T 1 is the transducer that represe nts the relation R 2 ◦ R 1 . W e denote by T i 1 ( i ∈ N 0 ) the tr a ns- ducer that represents the r elation R i 1 . The tr ansitive closur e o f T is T + = S ∞ i =1 T i ; its re fl exive tra ns itive closur e is T ∗ = T + ∪ T id . The transducer T is r eflexive if and only if L ( T id ) ⊆ L ( T ). Given an automaton A over Σ tha t r epresents a set AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 10 · A. Legay , and P . Wol p er S , we denote by T ( A ) the automa ton repr esenting the image of A by T , i.e., an automaton for the set R ( S ). Let T 1 and T 2 be tw o finite-word (re s p e ctively , B ¨ uchi) tr a nsducers defined over Σ 2 and let A b e a finite-word automaton (resp ectively , B ¨ uchi) automaton de- fined ov er Σ. W e obse r ve that T 2 ◦ T 1 = π 6 =2 [( T 1 ¯ × T Σ id ) ∩ ( T Σ id ¯ × T 2 )] and T ( A ) = π 6 =1 [( A Σ ¯ × Σ) ∩ T ], where A Σ is an a utomaton accepting Σ ∗ (resp ectively , Σ ω ). As a consequence , the comp os itio n of tw o finite-word ((weak) B ¨ uchi) trans ducers is a finite-word transducer. How ever, the comp osition o f tw o deterministic weak B ¨ uc hi transducer is a weak B ¨ uchi tra nsducer whose deter ministic version may not b e weak. A same o bs erv ation ca n b e made ab out the co mpo sition of a transducer with an a utomaton. 3. COUNTER AUTOMA T A W e introduce c ounter-wor d automata , a c lass of a utomata who se states a re aug- men ted by a vector of counters. Count e r-word automa ta are intended to b e used in our pro cedure for chec k ing the prec is eness of a n ex trap olation. All the concepts presented in this section are thus developped for this purp ose. 3.1 Definitions W e start with the definition of a counter automaton. Definition 3.1. A counter-word a utomaton (co un ter auto ma ton for s hort) ov er an a lphab et Σ is a tuple A c = ( n, c , Q, Σ , Q 0 , △ , F ), wher e — n ∈ N is the counter dimension of A , — c = ( c 1 , . . ., c n ) is a ve ctor of c ounters whose values r ange over the n atur al nu m- b ers . A c oun ter valuation v ∈ N n for c is a vector of natural num be r s, where the ith comp onent of v ass ig ns a v alue to c i , — Q is a set of st ates (unless stated other w is e, Q is assumed to b e finite), —Σ is a fin ite alphab et, — Q 0 ⊆ Q is a set of initial s t ates , — △ ⊆ Q × (Σ × N n ) × Q is a finite tra n s it ion r elation , and — F ⊆ Q is a set of accepting states. Let A c = ( n, c , Q, Σ , Q 0 , △ , F ) b e a counter automaton. If ( q 1 , ( a, v ) , q 2 ) ∈ △ , then we say that there is a tr ansition fro m q 1 (the origin ) to q 2 (the destination ) lab eled by a , and ass o ciated to the c ounter valuation v . The initial v alue of ea ch counter is 0, and ea ch time a transitio n is follow ed, the current v alues o f the co un- ters are incr emented with the c o unter v aluation asso ciated to the transition. Given a counter automaton A c = ( n, c , Q , Σ , Q 0 , △ , F ), the m aximal incr ement value o f A c is the smallest d ∈ N such that △ ⊆ Q × (Σ × [0 , d ] n ) × Q . Co unt er a utomata being finite s tructures, the max imal increment v alue ca n alwa ys b e computed by enum e r ating the elements of the transition relation. As finite automata , co unter automata are graphica lly repr esented with edge-lab eled directed gr aphs. W e em- phasize the counter increment vector asso cia ted to ea ch transitio n by pr eceding it with the symbol “+”. AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 11 Our aim is to as s o ciate counter v alua tions to the words accepted by a co unt e r automaton. F or doing so, we first define a notion of a ccepted lang uage that do es not take the co unters into account. W e prop os e the following definition. Definition 3.2. Let A c = ( n, c , Q , Σ , Q 0 , △ , F ) b e a counter automato n. The c ounterless a utomaton corre s p o nding to A c is the finite a utomaton A = ( Q, Σ , Q 0 , △ ′ , F ), wher e △ ′ = { ( q , a, q ′ ) ∈ Q ′ × Σ × Q ′ | ( ∃ v ∈ N n )(( q , ( a, v ) , q ′ ) ∈ △ ) } . Definition 3.3. The language accepted by a counter automa ton A c , denoted L ( A c ), is the lang uage a ccepted by its c o rresp o nding counterless auto maton. If w ∈ L ( A c ), then we say that w is ac c epte d by A c . W e now describ e how and when a counter a utomaton can a ssign counter v alues to the words it accepts. Let A c = ( n, c , Q, Σ , Q 0 , △ , F ) b e a counter automa ton. Assume first tha t A c describ es a s et of finite words. A run o f A c on a finite word w : { 0 , . . ., m − 1 }→ Σ is a la be ling ρ : { 0 , . . . , m } → ( Q × N n ) such that (1) ρ (0) ∈ ( Q 0 × 0 ), and (2) ( ∀ 0 ≤ i ≤ m − 1), ρ ( i + 1 ) = ( q i +1 , v i + 1 ) if and only if ρ ( i ) = ( q i , v i ) a nd there e x ists ( q i , ( w ( i ) , v ) , q i +1 ) ∈ △ with v i + 1 = v i + v . Let ρ ( m − 1) = ( q f × { v } ). If q f ∈ F , then we say that ρ is a n ac c epting run and that w is ac c epte d by A c with the counter v aluation v . Otherwise ρ is r eje cting for w . The automa ton A c being a finite-word automa ton, we can always as s o ciate at least o ne counter v aluatio n to each word w ∈ L ( A c ). O bserve that if the counter- less a utomaton of A c behaves non deterministically on w , then this word may b e asso ciated to several count er v alua tions. There can b e accepting and nonac c epting runs that assign the s ame counter v aluation to w . W e now switch to the c a se o f infinite words. A run o f A c on an infinite word w : N → Σ is a lab eling ρ : N → ( Q × N n ) such that (1) ρ (0) ∈ ( Q 0 × 0 ), and (2) ( ∀ 0 ≤ i ), ρ ( i + 1 ) = ( q i +1 , v i + 1 ) if and only if ρ ( i ) = ( q i , v i ) a nd there exists ( q i , ( w ( i ) , v ) , q i +1 ) ∈ △ with v i + 1 = v i + v . Contrary to the finite- word case, it is genera lly not p ossible to asso c ia te a counter v aluation to ρ . Indeed, there c o uld b e the cas e that the counters are incremented an un b ounded num b er of times. There are how ever sub-cla sses o f infinite-word counter automata for which it is a lwa ys p oss ible to assign a c ounter v alua tion to each of its runs. This is illustra ted with the following de finitio n. Definition 3.4. Let A c = ( n, Q, Σ , Q 0 , △ , F ) b e a weak B ¨ uchi counter automa- ton. W e say that A c is run-b oun de d if for each of its acc epting strongly connec ted comp onents S ⊆ F and sta tes q 1 , q 2 ∈ S , any transition that go es from q 1 to q 2 is asso ciated with the counter v aluation 0 . The s tructure of a r un-b ounded weak B ¨ uc hi co unt e r automaton ensures that for each of its runs, a fter having fo llowed a finite num b er of transitions, the v alues of the counters are no longer incr emented. Hence, o ne can rea son on a finite prefix AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 12 · A. Legay , and P . Wol p er of the run to deduce its counter v aluation. L e t A c = ( n, Q, Σ , Q 0 , △ , F ) b e a run- bo unded weak B¨ uchi c ounter automaton and ρ be o ne of its runs. W e say that ρ is an ac c epting run and tha t w is ac c epte d by A c with the counter v aluation v if a nd only if inf ( ρ ) ∩ ( F × { v } ) 6 = ∅ , where inf ( ρ ) is the set of configur ations that a pp e ar infinitely often in ρ . Other w is e ρ is r eje cting for w . In the rest of this pap er, we will only consider finite-word and r un-b ounded weak B ¨ uc hi counter automaton. W e can now define a notion o f counter langua g e, which takes the counters int o a ccount. Definition 3.5. The c ount er language o f a counter automaton A c , deno ted L ( A c ), is the set of pair s ( w, v ) s uch that w can b e accepted by A c with counter v aluation v . Observe that the c la ss of co unt e r-word automata is particula r with r esp ect to existing cla sses of counter automata 2 such as reversal b ounded co unt er auto mata [Ibarra 197 8], constraint a utomata [Henglein a nd Rehof 19 98], Parikh automata [Klaedtke and Rueß 2 003], or weigh ted automata [Mo hri 2003 ]. Indeed, counter- word automata use the count er part of the automaton to assign co unter v a luations to a word when this word is accepted by the automato n, rather than to restr ict the langua ge accepted by the automa ton. Intro ducing constra ints on the c ounters befo re the word is acc epted 3 generally lea ds to more p ow er ful mo dels 4 for which most pro blems are undecidable. The express iveness of those mo dels is not needed for the practical applications we consider ed in the pap er. 3.2 Graph-Based Op erations In this section, the op eratio ns of intersection a nd comp osition defined for finite automata are extended to counter automata. W e hav e the following definitions. Definition 3.6. Let A c 1 = ( n 1 , c 1 , Q 1 , Σ , Q 01 , △ 1 , F 1 ) and A c 2 = ( n 2 , c 2 , Q 2 , Σ , Q 02 , △ 2 , F 2 ) be tw o finite-word (resp ectively , run-b ounded weak B ¨ uchi) co un ter automata. The c oun ter-interse ction b etw ee n A c 1 and A c 2 , de no ted A c 1 ∩ c A c 2 , is the finite-word (resp ectively , run-b ounded weak B ¨ uc hi) counter automaton A c = ( n 1 + n 2 , c 1 × c 2 , Q, Σ , Q 0 , △ , F ) with L ( A c ) = L ( A c 1 ) ∩ L ( A c 2 ) and L ( A c ) = { ( w, v ) ∈ Σ ∞ × N n 1 + n 2 | ( ∃ ( w , v 1 ) ∈ L ( A c 1 ))( ∃ ( w, v 2 ) ∈ L ( A c 2 ))( v = v 1 × v 2 ) } . Definition 3.7. Let T c 1 = ( n 1 , c 1 , Q 1 , Σ 2 , Q 01 , △ 1 , F 1 ) and T c 2 = ( n 2 , c 2 , Q 2 , Σ 2 , Q 02 , △ 2 , F 2 ) be tw o finite-word (resp ectively , run-b ounded weak B ¨ uchi) co un ter transducers. The c ounter-c omp osition o f T c 1 by T c 2 , deno ted T c 2 ◦ c T c 1 , is the finite-word (resp ectively , run-b ounded weak B ¨ uchi) coun ter tra nsducer T c = ( n 1 + n 2 , c 1 × c 2 , Q, Σ 2 , Q 0 , △ , F ), with L ( T c ) = L ( T 2 ◦ T 1 ) and L ( T c ) = { ( w , v ) ∈ Σ ∞ × N n 1 + n 2 | ( ∃ ( w 1 , v 1 ) ∈ L ( T c 1 ))( ∃ ( w 2 , v 2 ) ∈ L ( T c 2 ))( v = v 1 × v 2 ∧ w = w 2 ◦ w 1 ) } . Definition 3.8. Let T 1 = ( Q 1 , Σ 2 , Q 01 , △ 1 , F 1 ) b e a finite-word (res pe ctively , run-b ounded weak B ¨ uchi) transducer, a nd A c 2 = ( n 2 , c 2 , Q 2 , Σ , Q 02 , △ 2 , F 2 ) b e a finite-word (resp ectively , run-bo unded weak B ¨ uchi) counter auto maton. The 2 As an example, we cannot test t he v alues of the co unters. 3 As an example, one could asso ciate constrain ts on ea ch transition. 4 As an example, m o dels that can recognize nonregular languages [K l aedtk e and Rueß 2003]. AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 13 c ounter-image of A c 2 by T 1 , deno ted T 1 ( A c 2 ), is the finite-word (resp ectively , B ¨ uchi) counter automato n A c = ( n 2 , c 2 , Q, Σ , Q 0 , △ , F ), where L ( A c ) = L ( T 1 ( A c 2 )) and L ( A c ) = { ( w, v 2 ) ∈ Σ ∞ × N n 2 | ( ∃ w 1 ∈ L ( T 1 ))( ∃ ( w 2 , v 2 ) ∈ L ( A c 2 ))( w = w 2 ◦ w 1 ) } . 3.3 Counter-Based Ope rations Let A c be a n-dimensio na l counter automaton ov er the alpha b et Σ, and d its ma x- imal increment v alue. The extende d automaton of A c , de no ted ( A c ) e , is the finite automaton (without co unters) obtained from A c by aug ment ing the lab el of ea ch of its tra ns itions with its co r resp onding counter v aluation. W e hav e the following definition. Definition 3.9. Let A c = ( n, c , Q, Σ , Q 0 , △ , F ) b e a counter a utomaton who se maximal increment v alue is d . The exten de d automaton cor resp onding to A c is the finite automaton A = ( Q, Σ ′ , Q 0 , △ ′ , F ), wher e —Σ ′ = Σ × [0 , d ] n , and — △ ′ = { ( q , a ′ , q ′ ) ∈ Q ′ × Σ ′ × Q ′ | ( ∃ v ∈ N n )(( q , ( a, v ) , q ′ ) ∈ △ ∧ a ′ = a × v ) } . A n-dimensional counter automaton o ver an alphabet Σ and whose maximal incre- men t v alue is d ca n b e viewed as a finite automa ton ov er a n alpha b et Σ × [0 , d ] n and, alternatively , a finite automaton o ver an alphab et Σ × [0 , d ] n can be viewed as a n- dimensional counter automaton ov er an a lphab et Σ a nd whos e ma x imal incr e- men t v alue is d . The alpha be t Σ × [0 , d ] n is referred to as the extende d alphab et o f A c . If A c is a finite-word counter automaton, then we s ay that it is u niversal if and only if L (( A c ) e ) = (Σ × [0 , d ] n ) ∗ . If A c is a run-b ounded weak B ¨ uchi counter automaton, then it is universal if and only if L (( A c ) e ) = (Σ × [0 , d ] n ) ∗ (Σ × 0) ω . Definition 3.10. Co nsider tw o c ounter automata A c 1 and A c 2 of same dimen- sions. The ex t ende d interse ction ( r esp e ctively, union) b etw een A c 1 and A c 2 , de- noted A c 1 ∩ e A c 2 (resp ectively , A c 1 ∪ e A c 2 ), is a co unter automaton A c such that ( A c ) e = ( A c 1 ) e ∩ ( A c 2 ) e (resp ectively , ( A c ) e = ( A c 1 ) e ∪ ( A c 2 ) e ). The extended intersection (resp ectively , union) o f tw o coun ter automata ca n eas - ily be computed by apply ing a class ic a l intersection (resp e c tively , union) algorithm to their extended version. W e also have the following pr op osition. Proposition 3.11 . The extende d interse ction/union of t wo ru n-b ounde d we ak B¨ uchi c ounter automata is a ru n-b ounde d we ak B ¨ uchi c ount er automaton. Definition 3.12. Let A = ( Q, Σ , Q 0 , △ , F ) b e a finite-word (resp ectively , B ¨ uchi automaton), the c ounter- z er o aut omaton cor resp onding to A is the one- dimensional counter automaton A c = (1 , c 1 , Q, Σ , Q 0 , △ ′ , F ), wher e — △ ′ = { ( q , ( a, 0 ) , q ′ ) ∈ Q × (Σ × 0 ) × Q | ( q , a, q ′ ) ∈ △} . The problem o f tes ting the e q uiv alence b etw een counter lang uages is known to be undecidable for man y classes of counter automata [Ibarra 1978], but decidability results exist for so me very particular class es [Ro os 1988 ]. The a lgorithms in volved in those decidabilit y results are kno wn to be of high complexity and difficult to im- plement . Rather tha n trying to extend those results to counter-w or d automa ta, w e AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 14 · A. Legay , and P . Wol p er 0 a,+(2) 1 b,+(3) 2 a,+(2) b,+(4) (a) A 1 0 a,+(2) 1 b,+(2) 2 a,+(3) b,+(4) (b) A 2 Fig. 2. Two finite-wo r d cou nter auto m ata. preferred to prop ose a sufficien t criterio n that can ea sily b e implemen ted with sim- ple automa ta -based manipulatio ns. Our c r iterion is for malized with the following prop osition. Proposition 3.13 . L et A c 1 and A c 2 b e two fin ite-wor d (r esp e ctively, B¨ uchi) c ounter aut omata of same dimension. If L ( A e c 1 ) = L ( A e c 2 ) , then L ( A c 1 ) = L ( A c 2 ) . There are of s ituations where L ( A e c 1 ) 6 = L ( A e c 2 ), while L ( A c 1 ) = L ( A c 2 ). Example 3.14. Consider the two fin ite-wor d c ounter automata A c 1 and A c 2 given in Figur e 2. The aut omaton A e c 1 do es n ot ac c ept the same language as A e c 2 . However L ( A c 1 ) = L ( A c 2 ) . The pro jection op era tion for finite a utomata extends to a c ounter pr oje ction for counter automata. W e have the following definition. Definition 3.15. Let A c = ( n, c , Q, Σ , Q 0 , △ , F ) b e a c ounter automaton. F or 1 ≤ i ≤ n , the pro jection of A c w.r.t. counter c i , deno ted Π 6 = c i ( A c ) is the counter automaton A ′ c = ( n − 1 , c ′ , Q, Σ , Q 0 , △ ′ , F ), where c ′ = ( c 1 , . . ., c i − 1 , c i +1 , . . ., c n ), L ( A c ) = L ( A ′ c ), and L ( A ′ c ) = { ( w, c 1 × c 2 ) ∈ Σ ∞ × N n − 1 | ( ∃ c 3 ∈ N ) (( w, c 1 × c 3 × c 2 ) ∈ L ( A c )) } . In the rest of the pa pe r , we use the shortcut Π ( 6 = { c 1 ,c 2 ,...,c n } ) ( A ) for Π ( 6 = c 1 ) (Π ( 6 = c 2 ) . . . (Π ( 6 = c n ) ( A )) . . . ). W e now pres ent a metho do logy that given a counter a uto maton A , computes an- other counter a uto maton A ′ whose accepting words are those of A that satisfy counter constra ints. W e start with the following definition. Definition 3.16. Let A c be a finite-word (resp ectively , run-bo unded weak B ¨ uchi) n-dimensional c ounter a uto maton and 1 ≤ i , j ≤ n b e an integer. W e define ( A c ) c i >c j to b e the counter automaton o btained fr om A c by remo v ing all the a c c epting runs that do no t assign a gr eater v alue to c i than to c j . The automaton ( A c ) c i >c j may hav e an infinite s et of s ta tes s inc e its languag e may not b e regular . In the rest of the pa pe r , we use the notation ( A c ) ( c 1 > { c 2 ,...,c n } ) to deno te ( . . . (( A c ) c 1 >c 2 ) c 1 >c 3 . . . ) c 1 >c n . AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 15 Let A c be a finite-word (resp ectively , run-b ounded weak B ¨ uchi) n-dimensiona l counter automaton ov er Σ and whose maximal increment v alue is d . . A wa y to compute ( A c ) c 1 >c 2 could b e to build a universal finite-word (res pec tively , run- bo unded weak B ¨ uc hi automato n) A U defined ov er the sa me extended a lpha b e t a s A c and then take the e x tended intersection b etw een ( A U ) c i >c j and A c . F or any word w ∈ Σ ∗ (resp ectively , w ∈ Σ ω ), the auto maton ( A U ) c i >c j contains a ll the accepting runs o n w that satisfy the c ondition c i > c j . Hence, taking the ex tended int er section b etw een ( A U ) c i >c j and A c will remove from A c all the a ccepting r uns that do not satisfy c i > c j . How ever, since there is no b ound on the difference b e- t ween the v alues of c i and c j befo re the w ord is a ccepted, the automaton ( A U ) c i >c j will hav e a n infinite num b er of states. Indeed, there should b e one s tate for each po ssible v alue of c i − c j . T o avoid ha ving to working with infinite-state auto mata, we imp o se a synchronization b etw een the co unters that need to b e co mpa red. As a cons equence, we may not exactly compute ( A c ) c i >c j , but an auto maton whos e language and counter la nguage are subsets o f thos e o f ( A c ) c i >c j . As we will see in Section 9, imp osing this synchronization is sufficient for the applicatio ns we will consider. W e hav e the following definition. Definition 3.17. Let A c = ( n, c , Q, Σ , Q 0 , △ , F ) be a finite-word (resp ectively , run-b ounded w ea k B¨ uchi) counter automato n and a synch ro n ization b ound M ∈ N . Let ∆ c l ( σ ) denotes the difference b etw een the v alue asso ciated to the counter c l in the last and in the first state of the subr un σ of a run ρ on w . The automaton A c is M -synchr onize d with resp ect to the co unters c i and c j if L ( A c ) = L ( A c ) c i >c j , and for each w ∈ L ( A c ) and each accepting run ρ o n w , we hav e k ∆ c j ( σ ) − ∆ c i ( σ ) k ≤ M . Definition 3.18. The finite-word (resp ectively , r un-b ounded weak) counter a u- tomaton A M U = ( n, c , Q , Σ , Q 0 , △ , F ) is M − Univ er sal-synchronized w.r.t. co un- ters c i and c j if and only if it is M − synchronized w.r.t. c i and c j , and L ( A M U ) = Σ ∗ (resp ectively , L ( A M U ) = Σ ω ). Rather than computing ( A c ) c i >c j , we pr op ose to compute a M -synchronized au- tomaton whose languag e and counter langua ge are subsets of those of ( A c ) c i >c j . F o r this, we intersect A c with a M -Universal-synchr onize d aut omaton . Obser ve that we can have a p o s sibly infinite num b er of auto mata which are M − Universal- synchronized w.r.t. c i and c j . Clearly , when taking the extended intersection b e- t ween a counter a utomaton A c and a M -Universal-synchronized a utomaton A M U defined over the same extended alphab et, we o btain a n automato n which is M - synchronized and whose lang uage and co unter langua g e are subsets o f those of A c . The requirement L ( A M U ) = Σ ∗ (resp ectively , L ( A M U ) = Σ ω ) in Definition 3.18 is to make sure that accepting runs a re remov ed fro m A c only if they do not satisfy the constraints ov er c i and c j . 4. THE ( ω )-REGULAR MODEL CHECKING FRAMEWORK In this pape r, we supp os e that sta tes of a system are enco ded by words ov er a fixed alphab et. If the states are enco ded by finite words, then s ets of states ca n be r e pr esented by finite-word automa ta a nd re la tions betw een states b y finite-w or d AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 16 · A. Legay , and P . Wol p er transducers. This setting is r eferred to as R e gular Mo del Che cking [Ke s ten e t al. 1997; W o lp e r and Boig elot 1998]. If the states are enco ded by infinite words, then sets of states ca n b e represe nt ed by deterministic weak B ¨ uchi automata and re- lations b etw een states by deterministic weak B ¨ uc hi transducers. This setting is referred to a s ω -Re gular Mo del Che cking [Boigelot et al. 2 0 04]. F o rmally , a finite automata-bas ed repres entation of a system can b e defined as follows. Definition 4.1. A ( ω -)r e gular system for a system T = ( S, S 0 , R ) is a triple M = (Σ , A, T ), wher e —Σ is a finite alphab et ov er which the sta tes are enco ded as finite (r esp ectively , infinite) words; — A is a deterministic finite-word (resp ectively , deterministic weak B ¨ uchi) automa - ton ov er Σ that r epresents S 0 ; — T is a deterministic finite-word (resp ectively , deterministic weak B ¨ uchi) trans- ducer ov er Σ 2 that repre s ents R . In the res t o f the pap er, T is as sumed to b e reflexive. In the finite-word ca se, an execution o f the system is an infinite seque nc e of same-length finite words ov e r Σ. The Regular Mo del Checking framework was first used to repre s ent para metr ic sys tems [Ab dulla e t a l. 2002; Bo ua jjani a nd T ouili 20 02; Ke sten et al. 199 7; Ab dulla e t al. 1999 ; Boua jjani et al. 2000 ; K esten et al. 2 0 02]. The framework can also b e used to repr esent v arious other mo d- els, which includes linea r in teg er systems [W olp er and Boige lot 1 995; 2000], FIF O - queues systems [B o igelot and Go defr o id 1996], XML sp ecifica tions [Bo ua jjani et al. 2006; T ouili and d’Ors o 200 6 ], and heap a na lysis [Boua jjani et al. 200 5; Boua jjani et al. 2006]. As a n illustration we give details o n how to r epresent para metric systems. Let P b e a pro cess represented by a finite-state s ystem. A par ametric system for P is an infinite family S = { S n } ∞ n =0 of netw orks whe r e for a fix ed n , S n is an inst anc e of S , i.e., a netw ork comp osed of n copies of P that work tog ether in pa rallel. In the Reg ular Mo del Checking fra mework, the finite set of states of each pr o cess is represented as an alpha b et Σ. Each state of an instance of the s ystem can then be enco ded as a finite word w = w (0) . . .w ( n − 1) over Σ, where w ( i − 1) enco des the c urrent state of the i th copy of P . Sets of sta tes of several instances can thu s be repr esented by finite-word automata. Obser ve that the states of an insta nce S n are all enco ded with words of the same length. Consequently , relations b etw een states in S n can b e r epresented by bina r y finite-word relations, and even tually by transducers. Example 4.2. Consider a simple example of p ar ametric network of identic al pr o c esses implementing a token ring algorithm. Ea ch of t hese pr o c esses c an b e either in id le or in critic al mo de, dep ending on whether or not it owns the un ique token. Two neighb oring pr o c esses c an c ommunic ate with e ach other as fol lows: a pr o c ess owning the token c an give it to its right-hand neighb or. We c onsider the alphab et Σ = { N , T } . Each pr o c ess c an b e in one of t he two fol lowing states : AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 17 T (has the token) or N (do es not have the token). Given a wor d w ∈ Σ ∗ with | w | = n (me aning that n pr o c esses ar e involve d in t he exe cution), we assume that the pr o c ess whose states ar e enc o de d in p osition w (0) is t he right-hand neighb or of the one whose st ates ar e enc o de d in p osition w ( n − 1) . The tr ansition re lation c an b e en c o de d as the union of two r e gular r elations that ar e the fol lowing: ( 1 ) ( N , N ) ∗ ( T , N )( N , T )( N , N ) ∗ to describ e the move of the token fr om w ( i ) to w ( i + 1) (with 0 ≤ i ≤ n − 2 ), and ( 2 ) ( N , T )( N , N ) ∗ ( T , N ) to describ e the move of t he token fr om w ( n − 1) t o w (0) . The set of al l p ossible initial states wher e the first pr o c ess has t he t oken is given by T N ∗ . In the infinite-word ca s e, an executio n of the system is an infinite sequence of infinite words over Σ. The ω -Regular Model Chec king framework has been used for handling s y stems with b oth integer and real v ariables [Boigelo t and W olp er 200 2; Boigelot et al. 20 05], s uch as linear hybrid systems with a constant deriv ative (see examples in [Alur e t al. 199 5 ] or in [Boua jjani et al. 2004 ; Legay 200 7]). It is known that verifying pro p er ties o f systems in the ( ω -)Regular Mo del Check- ing fra mework ge ne r ally reduces to so lving the ( ω -)R e gu lar R e achability Pr ob- lems [Pnueli and Shahar 2000 ; Boua jjani e t al. 20 00; Bo igelot et al. 2 004; Ab dulla et al. 2004; Legay 2007; Boua jjani e t a l. 2004 ] that are defined hereafter. Definition 4.3. Let A b e a deterministic finite-word (resp ectively , deterministic weak B ¨ uchi) automaton, a nd T be a reflexive deterministic finite-word (r esp ectively , deterministic weak B ¨ uc hi) transducer . The ( ω -)Regular Reachabilit y P roblems for A and T are the following: (1) Computing T ∗ ( A ) : the goa l is to compute a finite-word (resp ectively , weak B ¨ uc hi) automaton repr esenting T ∗ ( A ). If A repre s ents a se t of sta tes S a nd T a r elation R , then T ∗ ( A ) represe nt s the set of states that can b e rea ched from S by applying R an arbitra ry num b er of times; (2) Computing T ∗ : the goal is to compute a finite-word (resp. weak B ¨ uchi) trans - ducer r epresenting the reflexive tra nsitive closure of T . If T repr esents a subset of a p ow er o f a reachability relation R , then T ∗ represents its closure. The ( ω -)Regular Reachabilit y Pro blems are undecidable [Apt and Ko zen 19 86], but partial solutions exist. Studying those s olutions is the sub ject o f the res t o f this pap er. 5. ON SOL VING ( ω -)REGULAR REACHABILITY PROBLEMS Among the techniques to solve the ( ω -)Regular Reachabilit y P roblems, o ne distin- guishes b etw een domain sp e cific and generic techniques. Domain sp ecific techniques exploit the sp ecific pr op erties and r epresentations of the do ma in b eing co nsidered and were for instance obtained for s ystems with FIFO-queues in [Boigelo t and Go defroid 1996; B o ua jjani a nd Hab er mehl 199 7], for s ystems with integers and reals in [Boigelo t 199 9; B oigelot and W olp er 20 02; Boigelo t et al. 20 03], for push- down sys tems in [Finkel et a l. 1 997; Boua jjani et al. 1997 ], and for lo ssy q ueues AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 18 · A. Legay , and P . Wol p er in [Ab dulla a nd Jonss on 1996 ]. Generic techniques [Ke s ten et al. 1997 ; Boua jjani et al. 20 00; Jo nsson and Nilsson 200 0; Boua jjani et a l. 2004 ; Boigelot et a l. 2003 ; 2004; T ouili 2001 ; Dams et al. 2002; Abdulla et a l. 2003; V ardhan et al. 2004 ; 2005 ] consider automa ta-based represe nt a tions a nd pr ovide algo rithms that op er ate di- rectly on these r epresentations, mos tly disrega rding the do main for which it is used. In this pap er, we prop ose a new g eneric technique to solving the ( ω -)Reachabilit y Problems. W e use the following definition. Definition 5.1. Given a p ossibly infinite seq uence A 1 , A 2 , . . . o f automata , the limit of this sequence is an automaton A ∗ such that L ( A ∗ ) = S L ( A i ). Consider a transducer T a nd a n automa ton A . W e first obser ve that the compu- tations of b oth T ∗ and T ∗ ( A ) can b e reduced to the computation of the limit o f a p ossibly infinite sequence of automata. Indeed, computing T ∗ amounts to com- pute the limit of T id , T 1 , T 2 , T 3 , . . . , a nd computing T ∗ ( A ) amo unt s to compute the limit of A , T 1 ( A ), T 2 ( A ), T 3 ( A ), . . . . W e prop o se a g eneric technique which can compute the limit of a sequence o f automata by extra p olating one of its finite sampling se quenc e , i.e. selected auto ma ta from a finite prefix of the sequence. The extrap olatio n step pro ceeds by comparing successive automata in the sampling s e - quence, trying to iden tify the difference betw e en these in the fo rm of an incr ement , and extr ap olating the re pe tition o f this incr ement by adding lo ops to the la st au- tomaton of the seque nc e . After the extrap olatio n has b een built, one has to chec k whether it corres p o nds to the limit of the sequence. If this is the case, the com- putation terminates, otherwise, another s a mpling sequence has to b e chosen. This is a semi-a lgorithm s ince there is no gua rantee tha t (1) we can find a sampling sequence that can b e extrap ola ted, and (2) the result of the extra p olation will b e the desired closure. The presentation of our solution is org a nized as follows. Section 6 dis c usses the choice o f the sa mpling sequence. Sectio n 7 prese nts a metho dolo gy to detect in- crements. Section 8 pr esents several ex trap olation algo r ithms. Fina lly , Section 9 int r o duces cr iteria to determine the co rrectness of the extrap ola tio n. An imple- men ta tion of tho se results as well as some exp er iments a re pr e sented in Sectio n 10. 6. CHOOSING THE SAMPLING SE QUE NCE Cho osing the sa mpling seq uence is a rather tr icky issue a nd there is no guara nt e e that this can b e do ne in a wa y that ensur e s that the extra p olation step can b e ap- plied. Howev er, there are heuris tics that are very effective for o btaining a sa mpling sequence that can b e extra p o lated. The following lemma s hows that the sa mpling sequence can be selected quite arbitr arily , assuming that T is r eflex ive . Lemma 6.1. L et T b e a r eflexive t r ansduc er and A b e an automaton. If s = s 0 , s 1 , s 2 , . . . is an infinite incr e asing su bse quenc e of the natur al numb ers, then L ( T ∗ ) = S k ≥ 0 L ( T s k ) and, similarly, L ( T ∗ ( A )) = S k ≥ 0 L ( T s k ( A )) . Proof. The lemma follows directly from the fact that for any i ≥ 0, there is a n s k ∈ s such that s k > i a nd that, since T is r eflexive, ( ∀ j ≤ i )( L ( T j ) ⊆ L ( T i )) AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 19 (resp ectively , L ( T j ( A )) ⊆ L ( T i ( A ))). As an example, for the cases of FIFO-queue, pushdown, and par ametric sy s tems, we observed that consider ing sample p oints of the form s k = ak , where a ∈ N is a constant, turns out to b e very useful. F or the case of arithmetic, we observed that the useful sampling p o int s are often of the form s k = a k . Sa mpling se q uences with sampling p oints of the form s k = ak are c a lled line ar , while sampling s equences with sampling po ints of the form s k = a k are called exp onential . Example 6.2. Figur e 3 shows the m inimal tr ansduc er of Example 2.9 c omp ose d with itself 2 , 4 , 8 and 16 times. The differ enc e b etwe en the gr aphs for T 4 and T 8 takes t he form of an incr ement r epr esente d by the set of states { 2 , 6 } in T 8 . This incr ement is re p e ate d b etwe en T 8 and T 16 . Conse quently, T 16 differs fr om T 4 by the addition of two incr ements r epr esente d by the sets { 3 , 8 } and { 2 , 7 } . 7. DETECTIN G INCREMEN TS W e consider a finite seq uence A 1 , A 2 , A 3 , . . . , A n of finite a uto mata that are either all finite-word automa ta or all weak B ¨ uchi automata . Tho se automata are assumed to b e deterministic and minimal. Our goal is to determine whether, for sufficiently large i , the automato n A i +1 differs from A i by some additiona l consta nt finite- state str uc tur e. Our str ategy , cons is ts in comparing a finite nu mber of succ e ssive automata until a suitable increment can b e detected. F o r each i > 0, let A i = ( Q i , Σ , q i 0 , δ i , F i ). T o identif y common parts b etw een t wo successive a utomata A i and A i +1 we fir s t lo ok for states of A i and A i +1 from which identical languag es ar e acc e pted. Pre cisely , we compute a forward equiv a- lence rela tion E i f ⊆ Q i × Q i +1 betw e en A i and A i +1 . Since we are dealing with deterministic minimal automata, the forwards e quiv alence E i f is o ne-to-one (though not total) and ca n ea sily b e computed by pa r titioning the states of the joint a u- tomaton ( Q i ∪ Q i +1 , Σ , q i 0 , δ i ∪ δ i +1 , F i ∪ F i +1 ) according to their accepted langua ge. F o r finite-word automata, this op eratio n is easily carr ied out by Hopc roft’s finite- state minimization pr o cedure [Hop croft 1 971]. F or weak B¨ uchi automata, one uses the v ariant int r o duced in [L¨ o ding 20 01]. R emark 7.1. Note that b ecause the automata are minimal, the parts of A i and A i +1 linked by E f i are isomorphic (see Definition 2.7 ), inco ming transitions b eing ignored. Next, we sear ch for sta tes of A i and A i +1 that are r e a chable fr o m the initial state b y identical languag es. Pr ecisely , we compute a backw ard equiv alence relation E i b ⊆ Q i × Q i +1 betw e en A i and A i +1 . Since A i and A i +1 are deterministic and minimal, the b ackwar ds e quivalenc e E i b can b e computed by forward propag ation, starting from the pair ( q i 0 , q i +1 0 ) and explor ing the par ts of the tr ansition gr aphs of A i and A i +1 that a re isomor phic to each o ther, if transitions leaving these parts are ignored. R emark 7.2. Note that b ecause the automata are minimal, the parts of A i and A i +1 linked b y E i b are iso morphic, outgoing transitions b eing ignored. W e now define a notion of finite-state incr ement b etw een t wo succes s ive au- tomata, in terms of the relations E i f and E i b . AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 20 · A. Legay , and P . Wol p er 3 1 1,0 2 0,0 1,1 0 0,0 1,1 1,0 0,1 0,0 1,1 4 2 1,0 3 0,0 1,1 0 1 0,0 1,0 1,1 0,1 0,0 1,1 1,0 0,1 0,0 1,1 4 3 1,0 5 0,0 1,1 0 1 0,0 1,0 1,1 2 0,1 0,0 1,1 6 1,0 0,0 0,1 1,0 1,1 1,1 0,0 0,1 1,0 0,1 0,0 1,1 5 4 1,0 6 0,0 1,1 0 1 0,0 1,0 1,1 2 0,1 0,0 1,1 7 1,0 0,0 0,1 1,0 1,1 3 1,1 0,0 0,1 8 1,0 0,0 0,1 1,0 1,1 0,0 1,1 0,1 1,0 0,1 0,0 1,1 Fig. 3. T r ansducer of Example 6.2 at p ow ers of tw o. AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 21 Q i +1 H Q i +1 I 0 E i b E i f Q i +1 T Q i b Q i f A i : A i +1 : Fig. 4. Pa r titioning au tomata states. Definition 7.3. Let A i = ( Q i , Σ , q i 0 , δ i , F i ) and A i +1 = ( Q i +1 , Σ , q i +1 0 , δ i +1 , F i +1 ) be t wo minimal finite-word (resp ectively , minimal weak B ¨ uch i) a utomata. Let E i b and E i f be resp ectively , the backw ar d and forward equiv alences computed b etw een A i and A i +1 . The automaton A i +1 is incr emental ly lar ger tha n A i if the relatio ns E i f and E i b cov er a ll the states of A i . In o ther words, for each q ∈ Q i , there must exist q ′ ∈ Q i +1 such that ( q , q ′ ) ∈ E i b ∪ E i f . If A i +1 is incr ementally larger than A i , the incr ement consists o f the sta tes that are matched neither by E i f , nor by E i b . Definition 7.4. Let A i = ( Q i , Σ , q i 0 , δ i , F i ) and A i +1 = ( Q i +1 , Σ , q i +1 0 , δ i +1 , F i +1 ) be t wo minimal finite-word (resp ectively , minimal weak B ¨ uch i) a utomata. Let E i b and E i f be resp ectively , the backw ar d and forward equiv alences computed b etw een A i and A i +1 . If A i +1 is incr ementally larger than A i , then (1) the set Q i can b e partitioned into { Q i b , Q i f } , s uch that —The set Q i f contains the states q cov er ed by E i f , i.e ., fo r which ther e exists q ′ such that ( q , q ′ ) ∈ E i f ; —The set Q i b contains the r emaining states. (2) The set Q i +1 can b e partitioned int o { Q i +1 H , Q i +1 I 0 , Q i +1 T } , whe r e —The he ad p art Q i +1 H is the image by E i b of the set Q i b ; —The tail p art Q i +1 T is the ima ge by E i f of the set Q i f , dis mis s ing the states that b elong to Q i +1 H (the in tention is to hav e a n unmo dified head part); —The incr ement Q i +1 I 0 contains the states that do not be long to either Q i +1 H or Q i +1 T . Definitions 7.3 and 7.4 are illustrated in Figure 4. Our ex pe c tation is that, when moving from one automaton to the next in the sequence, the increment will alwa ys be the s ame. W e formalize this prop erty with the following definition. Definition 7.5. Let S I = A i , A i +1 , . . . , A i + k and for each 0 ≤ j ≤ k , le t A i + j = ( Q i + j , Σ , q i + j 0 , δ i + j , F i + j ) b e a finite-word (resp ec tively , weak B¨ uchi) automa ta. F o r ea ch 0 ≤ j < k , let E i + j b and E i + j f be resp ectively , the ba ckw ard a nd the AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 22 · A. Legay , and P . Wol p er forward equiv alences co mputed b etw een A i + j and A i + j +1 . The sequence S I is an incr emental ly gr owing s equence if —F o r each 0 ≤ j ≤ k , A i + j is minimal; —F o r each 0 ≤ j ≤ k − 1, A i + j +1 is incr ementally larger than A i + j ; —F o r ea ch 1 ≤ j ≤ k − 1, the he ad increment Q i + j +1 I 0 , which is detected b etw een A i + j and A i + j +1 , is the ima ge b y E i + j b of the increment Q i + j I 0 . Consider a subsequence S I = A i , A i +1 , . . . , A i + k of A 1 , . . . , A n that grows incre- men ta lly . F or 2 ≤ j ≤ n , the tail pa rt Q i + j T of A i + j will then c onsist of j − 1 co pie s of its head incr ement Q I i + 0 plus a part that we will name the tail-end s et . Precis ely , Q i + j T can b e partitioned int o { Q i + j I 1 , Q i + j I 2 , . . . , Q i + j I j − 1 , Q i + j T f } , whe r e —F o r each 1 ≤ ℓ ≤ j − 1, the tail incr ement Q i + j I ℓ is the image by the relation E i + j − 1 f ◦ E i + j − 2 f ◦ · · · ◦ E i + j − ℓ f of the he ad incr ement Q i + j − ℓ I 0 ; —The tail-end s et Q i + j T f contains the remaining elements of Q i + j T . Given an automaton A i + j in the sequence S I , we define its gr owing de c omp osition w.r.t. S I , denoted GROW ( S I ) ( A i + j ), to b e the o rdered list { Q i + j H , { Q i + j I 0 , . . . , Q i + j I j − 1 } , Q i + j T } . It is e asy to see that the head increment Q i + j I 0 of A i + j and all its tail increments Q i + j I ℓ , ℓ ∈ [1 , j − 1] app earing in its tail part Q i + j T are images of the head increment Q i +1 I 0 detected b etw een A i and A i +1 by a co mbination of forward and backward equiv alences. This observ atio n e x tends to all the automata in S I . Consequently the tra nsition graphs internal 5 to all increments of a ll the automa ta in the s equence a re isomorphic to that of Q i +1 I 0 , and hence are isomor phic to each other. In the rest o f the thesis, this isomor phism r elation b etw een t wo increments is called the incr ement isomorphism rel ation . Obser ve als o that, since w e are working with minimal automata, for each j ∈ [1 , k − 1] we have the fo llowing: —The head part Q i + j +1 H is the ima ge by E i + j b of the hea d part Q i + j H . Co nsequently , the in ter na l transition graphs of the hea d parts of a ll the automata in the se quence S I are is omorphic to each other. This isomor phis m relatio n is c alled the he ad isomorphi s m r elation ; —The tail-end set Q i + j +1 T f is the image by E i + j f of the tail-end set Q i + j T f . Conse- quently , the internal trans ition graphs o f the ta il-end sets o f all the automa ta in the seq uence S I are isomorphic to each other . This isomor phis m r elation is called the tail-end set isomorphism r elation . The situation is illustrated in Figure 5. Our inten tion is to extrap olate the last automaton o f an incrementally grow- ing sequence o f automata by a dding more incr ements, following a regular patter n. In o rder to do this, we need to compare and characterize the tr a nsitions le aving different increments. 5 The transi tion graph only con tains transitions bet ween s tates of the incremen t. AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 23 Q i b Q i +3 H Q i +3 I 0 Q i +2 H Q i +2 I 0 Q i +1 H Q i +1 I 0 E i +2 b E i +1 b E i f Q i +1 T f E i b E i +1 b E i +2 f Q i +3 I 2 E i +2 f E i +1 f Q i +2 T f E i +1 f Q i +2 I 1 E i +2 f Q i +3 T f E i +2 b Q i +2 T Q i +3 T Q i f Q i +3 I 1 Q i +1 T A i : A i +1 : A i +2 : A i +3 : Fig. 5. Automata i n an increment all y gro wing sequenc e. Definition 7.6. Let A i + k = ( Q i + k , Σ , q i + k 0 , δ i + k , F i + k ) b e the last automaton of an incrementally growing sequence of automa ta S I = A i , A i +1 , . . . , A i + k . Assume that GROW ( S I ) ( A i + k ) = { Q i + k H , { Q i + k I 0 , . . . , Q i + k I k − 1 } , Q i + k T f } . Then, a n increment Q i + k I α (0 ≤ α ≤ k − 1) is sa id to b e c ommun ic ation e quivalent to an incr ement Q i + k I β (0 ≤ β ≤ k − 1) if and only if, for each pair o f corresp o nding states (by the increment isomor phism) ( q , q ′ ), q ∈ Q i + k I α and q ′ ∈ Q i + k I β , and a ∈ Σ, w e hav e that, either — δ i + k ( q , a ) ∈ Q i + k I α and δ i + k ( q ′ , a ) ∈ Q i + k I β , hence leading to corr esp onding states by the e x isting increment isomor phism b etw een Q i + k I α and Q i + k I β , or — δ i + k ( q , a ) a nd δ i + k ( q ′ , a ) are b oth undefined, or — δ i + k ( q , a ) a nd δ i + k ( q ′ , a ) bo th leading to the same s tate of the tail end Q i + k T f , or —there exists some γ > 0 s uch that δ i + k ( q , a ) and δ i + k ( q ′ , a ) lead to corres po nding states by the increment isomo rphism be t ween Q i + k I α + γ and Q i + k I β + γ (0 ≤ α + γ , β + γ ≤ k − 1). The definition easily generalizes to increments of different automata . Example 7.7. Consider t he aut omaton of Figur e 6, whose set of states is given by { 0 , 1 , 2 , 3 , 4 , 5 } . Assu me that Q c ontains thr e e incr ements that ar e Q I 0 = { 1 } , Q I 1 = { 2 } , and Q I 2 = { 3 } . The incr ements Q I 0 and Q I 1 ar e c ommu nic ation stable. The pr op ert y do es not hold for Q I 0 and Q I 2 sinc e a tra n sition lab ele d with c is not define d fr om states 3 . AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 24 · A. Legay , and P . Wol p er 0 1 c 2 a 3 c a 4 c a 5 x Fig. 6. An automat on for Definition 7.6. F o r the s a me re asons, we also need to c o mpare the tra nsitions leaving the head part of different automata in the sequence. Definition 7.8. Let A i + k − 1 = ( Q i + k − 1 , Σ , q i + k − 1 0 , δ i + k − 1 , F i + k − 1 ) and A i + k = ( Q i + k , Σ , q i + k 0 , δ i + k , F i + k ) b e the tw o la st a utomata o f a n incrementally growing se- quence of automata S I = A i , A i +1 , . . . , A i + k . Assume that GROW ( S I ) ( A i + k − 1 ) = { Q i + k − 1 H , { Q i + k − 1 I 0 , . . . , Q i + k − 1 I k − 2 } , Q i + k − 1 T f } and GROW ( S I ) ( A i + k ) = { Q i + k H , { Q i + k I 0 , . . . , Q i + k I k − 1 } , Q i + k T f } . W e say that A i + k − 1 and A i + k are c ommun ic ation stable if and only if for each pair of corresp onding states (by the increment iso morphism) ( q, q ′ ), q ∈ Q i + k − 1 H and q ′ ∈ Q i + k H , and a ∈ Σ, we hav e that, either — δ i + k − 1 ( q , a ) ∈ Q i + k − 1 H and δ i + k ( q ′ , a ) ∈ Q i + k H , hence lea ding to cor resp onding states b y the exis ting head isomorphism betw e e n Q i + k − 1 H and Q i + k H , or — δ i + k − 1 ( q , a ) a nd δ i + k ( q ′ , a ) are b oth undefined, or — δ i + k − 1 ( q , a ) = q i + k − 1 f ∈ Q i + k − 1 T f and δ i + k ( q ′ , a ) = q i + k f ∈ Q i + k T f , hence leading to corres p o nding states by the exis ting tail-end set isomorphis m b etw een Q i + k − 1 T f and Q i + k T f , or — δ i + k − 1 ( q , a ) ∈ Q i + k − 1 I x and δ i + k ( q ′ , a ) ∈ Q i + k I x , hence lea ding to corre s po nding states by the exis ting inc r ement isomorphism b etw een Q i + k − 1 I x and Q i + k I x (0 ≤ x ≤ k − 1). 8. EXTRAPOLA TION ALGORITHMS T o extrap ola te a p ossibly infinite sequence of minimal finite-word (resp ectively , minimal weak B ¨ uchi) automata A 1 , A 2 , . . . we tr y to extract and extrap ola te one of its finite incrementally g rowing sampling seq uences S I = A s 0 , . . . , A s k . The “candidate” ex trap olation for A 1 , A 2 , . . . is then g iven by the extr ap olation o f the sequence S I . Let A e 0 = A s k be the la st auto maton of S I . In order to e x trap olate S I , we simply insert an extra increment betw een the hea d part of A e 0 and its head increment Q e 0 I 0 , and define its outgoing transitions in order to ma ke this extra incre- men t communication equiv a lent to Q e 0 I 0 . By rep eatedly applying this ex trap olation step we obtain an e x trap olated infinite sequence of automata A e 0 , A e 1 , . . . which is assumed to b e the infinite e x tension of the sampling sequence S I . F ormally , the extr ap olate d se quenc e of origin A e 0 is the infinite s equence o f minimal automa ta A e 0 , A e 1 , . . . such that —F o r each i ≥ 0 , A s 0 , A s 1 , . . . , A s k − 1 , A e 0 , A e 1 , . . . , A e i grows increment a lly; —F o r each i > 0, A e i is communication stable with A e 0 ; —F o r each i > 0, the head increment detected betw een A e i − 1 and A e i is communi- cation equiv alent to Q e 0 I 0 . AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 25 a a a a y x ′ x ′ x ′ y ′ y ′ y ′ x b b b Q e 0 H Q e 0 I 0 Q e 0 I 1 Q e 0 I 2 Q e 0 I 3 Fig. 7. Illustration of the ex tr ap olation pro cedure for finite-word automata. The limit A e ∗ of the e xtrap olated se q uence of orig in A e 0 is thus an ex trap olation of the limit of A 1 , A 2 , . . . . In this s ection, we present pr o cedures to build a finite representation fo r A e ∗ . F or technical reaso ns, the cases of finite-word a nd weak B ¨ uc hi automata ar e co nsidered se pa rately . 8.1 Finite-wo rd Auto m a t a Assume A e 0 to be a finite-word automaton. W e pro p o se to build a finite repr e - sentation o f A e ∗ by adding to A e 0 new tr ansitions that simulate the existence of additional increments. Consider the automaton A e 0 with GRO W ( S I ) ( A e 0 ) = { Q e 0 H , { Q e 0 I 0 , . . . , Q e 0 I k − 1 } , Q e 0 T f } . Suppo se the ex istence of a tra nsition lab eled by a fro m a s tate x of Q e 0 I 0 to a state x ′ of Q e 0 I 3 . Since, the incr ement Q e 1 I 0 added b etw een A e 0 and A e 1 is communication equiv alent to Q e 0 I 0 , there must exis t a transition t lab eled by a from the state iso morphic to x in Q e 1 I 0 to the s tate isomorphic to x ′ in Q e 1 I 2 . Our construction simulates t in A e 0 by adding a transitio n t ′ lab eled by a from x to the state isomorphic to x ′ in Q e 0 I 2 . This co nstruction can be rep eated for the addition of a second increment. The simulation of “more than tw o increments” is do ne by adding transitions betw een states of Q e 0 I 0 . Due to the comm unica tio n equiv alence prop erty , a similar principle has to be a pplied for outgoing transitions from Q e 0 H . The situa tion is illustrated in Figur e 7 wher e a par t of A e 0 has b een represented. The da shed transitions in the figur e are the transitio ns added during the extrap ola tio n pro cess. F o rmally , a finite r epresentation of A e ∗ can b e built fro m A e 0 with the co nstruc- tion underlined in the following prop os ition. Proposition 8.1. L et A e 0 define d over Σ b e a minimal finite-wor d automaton which is the last automaton of an incr ement al ly gr owing se qu enc e of automata S I . Assume that GRO W ( S I ) ( A e 0 ) = { Q e 0 H , { Q e 0 I 0 , . . . , Q e 0 I k − 1 } , Q e 0 T f } . One c an c ompute a finite-wor d automaton A e ∗ that re pr esent s the limit of the extra p olate d se quenc e of origin A e 0 . Proof. Let δ b e the transitio n re la tion o f A e 0 . The automaton A e ∗ can b e built from A e 0 by augmenting δ using the following r ule: F o r eac h state q ∈ Q e 0 H ∪ Q e 0 I 0 and a ∈ Σ, if δ ( q , a ) leads to a s tate q ′ in an increment Q I j , 1 ≤ j ≤ k − 1, then fo r each 0 ≤ ℓ < j , add a tra nsition AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 26 · A. Legay , and P . Wol p er 0 1 x 2 a 3 c 4 b a a 5 a 6 y (a) A e 0 0 1 x b a c 2 a b c 3 b c 4 b a a 5 a 6 y (b) A e ∗ Fig. 8. Automata f or Example 8.2. y x ′ x ′ x ′ y ′ y ′ y ′ x a, +(3) a, +(0) a, +(2) a, +(1) b, +(0) b, +(1) b, +(2) Q e 0 H Q e 0 I 0 Q e 0 I 1 Q e 0 I 2 Q e 0 I 3 Fig. 9. Illustration of the extrap olation algorithm for finite-w or d automata with the addition of coun ter v alues. ( q , a, q ′′ ), where q ′′ is the sta te c o rresp o nding to q ′ (b y the incr e ment isomorphism) in Q e 0 I ℓ . The added transitio ns, which include lo ops (trans itions to Q e 0 I 0 itself ) allow A e ∗ to simulate the runs of any of the A e i ( i ≥ 0). Conv e r sely , it is a lso easy to s ee all accepting runs genera ted using the added trans itio ns corresp o nd to accepting r uns of some A e i . Example 8.2. Consider the minimal finite-wor d automaton A e 0 given in Fi gu r e 8(a), with Q e 0 H = { 0 } , Q e 0 I 0 = { 1 } , Q e 0 I 1 = { 2 } , Q e 0 I 2 = { 3 } , Q e 0 I 3 = { 4 } , and Q e 0 T f = { 5 , 6 } . Apply ing t he c onstruction of Pr op osition 8.1 t o A e 0 gives the automaton A e ∗ in Figur e 8(b). W e no w show that it is p oss ible to a dd a counter c to A e ∗ in such a way that when a word is a ccepted, the v alue of c is the smallest index i of the automaton A e i of the extrapola tion sequence b y which the w o rd is in fact accepted. Our construction AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 27 0 1 x,+(0) b,+(3) a,+(1) c,+(2) 2 a,+(0) b,+(2) c,+(1) 3 b,+(1) c,+(0) 4 b,+(0) a,+(0) a,+(0) 5 a,+(0) 6 y,+(0) Fig. 10. Automaton for Example 8.4. lab els each transition added to A e 0 with a v alue that repres ents the num b er of increments sim ulated by this transition. In Figure 9 we sk etch the construction for the automaton given in Figure 9. Proposition 8.3. L et A e 0 = ( Q, Σ , Q 0 , δ, F ) b e a minimal fin ite- wor d automa- ton which is the last automaton of a finite incr emental ly gr owing se quenc e of au- tomata S I . A ssume that GRO W ( S I ) ( A e 0 ) = { Q e 0 H , { Q e 0 I 0 , . . . , Q e 0 I k − 1 } , Q e 0 T f } and let A e 0 , A e 1 , . . . b e the extra p olate d se quenc e of origin A e 0 . One c an c ompute a fi nite- wor d c ount er au t omaton A e ∗ c such that (1) L ( A e ∗ c ) = S i ≥ 0 L ( A e i ) , (2) for e ach ( w, i ) ∈ L ( A e ∗ c ) , w ∈ L ( A e i ) , and (3) for e ach i ≥ 0 , w ∈ L ( A e i ) , 0 ≤ j ≤ i exists such that ( w, j ) ∈ L ( A e ∗ c ) . Proof. Let δ b e the trans itio n r elation of A e 0 . The one-dimensiona l c o unter automaton A e ∗ c is given b y (1 , c , Q , Σ , Q 0 , △ , F ), with △ defined as follows: —Start with △ = {∅} ; —F o r each ( q , a, q ′ ) ∈ δ , add ( q , ( a, 0 ) , q ′ ) to △ ; —F o r each state q ∈ Q e 0 H ∪ Q e 0 I 0 and a ∈ Σ, If δ ( q , a ) leads to a state q ′ in an incr ement Q I j , 1 ≤ j ≤ k − 1 , then for each 0 ≤ ℓ < j , add to △ a transition ( q , ( a, j − l ) , q ′′ ), where q ′′ is the state corres p o nding to q ′ (b y the incr ement isomorphism) in Q e 0 I ℓ . Let A e 0 c be the co unter-zero a utomaton corre s po nding to A e 0 . W e directly see that for ea ch i > 0, w ∈ L ( A e i ) \ L ( A e 0 ), 1 ≤ j ≤ i exists such that ( w , j ) ∈ L ( A e ∗ c ) \ L ( A e 0 c ). Indeed, since w / ∈ L ( A e 0 ), any a c cepted run on w must pas s by states of one o f the added increments and j cannot b e equal to 0. Example 8.4. Figur e 10 pr esents the r esult of applying the c onstru ction of Pr op o- sition 8.3 to Automaton A e 0 of Example 8.2. 8.2 W eak B¨ uchi Automata Assume now A e 0 to b e a deterministic weak B ¨ uchi auto ma ton. In such a case, a finite repr esentation of the extr ap olated sequence of or igin A e 0 cannot be computed with the construction of Prop ositio n 8.1. AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 28 · A. Legay , and P . Wol p er 0 1 x 2 a 3 c a 4 c a 5 y b (a) A e 0 0 1 x a c 2 a c 3 c a 4 c a 5 y b (b) A e ∗ Fig. 11. A weak B ¨ uchi automaton and its extrap olation with the construction of Prop osition 8.1 . Example 8.5. Consider the minimal we ak B¨ uchi automaton A e 0 given in Figur e 11(a), with Q e 0 H = { 0 } , Q e 0 I 0 = { 1 } , Q e 0 I 1 = { 2 } , Q e 0 I 2 = { 3 } , and Q e 0 T f = { 4 , 5 } . Applying the c onstru ction of Pr op osition 8.1 to A e 0 gives t he automaton A e ∗ in Figur e 11(b). This automaton ac c epts the wor d xa ω which c annot b e ac c epte d by one of the aut omata A e i in the ex tr ap olate d se quenc e of origin A e 0 . The example ab ov e shows that applying the co ns truction o f P rop osition 8.1 to A e 0 may introduce new c ycles from states o f Q e 0 I 0 to themselves. Since the ac cepting runs of the A e i can only go thro ugh a finite numb er of incr ements, it is essential to make these cyc les nonaccepting. The pro blem can easily b e solved, a s stated with the following prop os itio n. Proposition 8.6. L et A e 0 define d over Σ b e a minimal we ak B ¨ u chi au t omaton which is t he last element of an incr ement al ly gr owing se qu enc e of au t omata S I . Assume that GRO W ( S I ) ( A e 0 ) = { Q e 0 H , { Q e 0 I 0 , . . . , Q e 0 I k − 1 } , Q e 0 T f } . One c an c ompute a we ak B¨ uchi aut omaton A e ∗ that r epr esents the limit of the extr ap olate d se quenc e of origin A e 0 . Proof. Let δ b e the tr ansition r e lation of A e 0 . The automaton A e ∗ that re pr e- sents the limit of the extr ap olated seq uence whose origin is A e 0 can b e built from A e 0 by augmenting its set of states and transitions with the following rules: (1) Build an iso morphic copy A I 0 c opy of the automaton formed b y the s tates in Q e 0 I 0 , the transitions be tw e en them, and the outgoing transitio ns from these states to sta tes in Q e 0 I 1 , Q e 0 I 2 , . . . , Q e 0 I k − 1 , and Q e 0 T f ; (2) Make all the states of A I 0 c opy nonaccepting; (3) F or each state q ∈ Q e 0 I 0 ∪ Q e 0 H and a ∈ Σ, if δ ( q , a ) leads to a state q ′ in a n increment Q e 0 I j , 1 ≤ j ≤ k − 1, then (a) F or each 1 ≤ ℓ < j , add a tr a nsition ( q , a, q ′′ ), where q ′′ is the state corres p o nding to q ′ (b y the increment isomo rphism) in Q e 0 I ℓ . Also, a dd a transition ( q , a, q ′′ ), where q ′′ is the state corres po nding to q ′ in A I 0 c opy ; (b) If q ∈ Q I 0 , then let q c opy be the state cor resp onding to q in A I 0 c opy . F or each 1 ≤ ℓ < j , add a transition ( q c opy , a, q ′′ ), whe r e q ′′ is the state c orre- sp onding to q ′ (b y the increment isomorphism) in Q e 0 I ℓ . Also , add a transi- tion ( q c opy , a, q ′′ ), where q ′′ is the s ta te corre s po nding to q ′ in A I 0 c opy . AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 29 0 1 x 2 a c 3 c 6 a c a 4 c a 5 y a c c a c b Fig. 12. A w eak B¨ uc hi automaton for Example 8.7 . 6 4 0 8 1 0 1 2 0 2 1 3 0 1 1 0 7 2 5 0 1 0 1 2 1 (a) A e 0 6 4 0 8 1 0 1 2 0 2 1 3 0 1 1 0 7 2 5 0 1 9 0 1 0 1 2 1 0 1 0 1 (b) A e ∗ 1 0 1 0 11 1 0 2 1 4 2 1 12 2 3 2 5 0 1 0 6 1 0 7 0 9 1 0 8 1 1 10 0 0 1 0 1 1 (c) A e ∗ 2 Fig. 13. B ¨ uch i automata for the proof of Prop osition 8.8 . The construction in the pro po sition ab ov e follows fro m the one given in Pr o p osition 8.1. The only slig ht diff e r ence is in the duplicatio n of the head increment, whic h is needed to make sure that new cy cles added to A e 0 are nonaccepting. Example 8.7. The automaton in Figur e 12 is the r esult of applying the c on- struction of Pr op osition 8.6 to Automaton A e 0 of Example 8.5. AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 30 · A. Legay , and P . Wol p er Proposition 8.8. L et A e ∗ b e t he r esult of applying the c onstruct ion of Pr op o- sition 8.6 to A e 0 , the last automaton of a finite incr emental ly gr owing se quenc e of deterministic we ak B¨ uchi automata. The au t omaton A e ∗ may not b e we ak deter- ministic. Proof. Consider the minimal w eak B¨ uchi a utomaton A e 0 given in Figur e 1 3 (a), with Q e 0 H = { 6 , 4 } , Q e 0 I 0 = { 7 } , Q e 0 I 1 = { 5 } , and Q e 0 T f = { 0 , 1 , 2 , 3 , 8 } . Applying the co nstruction of Prop os ition 8.6 to A e 0 gives the nondeterministic weak B ¨ uchi automaton A e ∗ in Figure 13(b). In this automaton, the state lab eled by 9 is the duplication o f Q e 0 I 0 . The re sult of determinizing A e ∗ 1 is the deterministic co - B ¨ uc hi automaton A e ∗ 2 that is given in Figur e 13 (c). It is easy to see that this automa- ton is not inherently weak and, co nsequently , cannot b e turned to a weak B ¨ uchi automaton. F o llowing what has been do ne for the cas e of finite-word automata, we now prop ose to a dd a counter c to A e ∗ in such a w ay that when a word is accepted, the v alue of c is the smallest index i of the automaton A e i of the extra p o lated sequence by whic h the word is in fact a c c epted. Proposition 8.9. L et A e 0 = ( Q, Σ , Q 0 , δ, F ) b e a m inimal we ak B ¨ uchi automa- ton which is t he last element of an incr emental ly gr owing se quenc e of automata S I . Assume that GROW ( S I ) ( A e 0 ) = { Q e 0 H , { Q e 0 I 0 , . . . , Q e 0 I k − 1 } , Q e 0 T f } and let A e 0 , A e 1 , . . . b e the extr ap olate d se quen c e of origin A e 0 . One c an c ompute a ru n-b ounde d we ak B¨ uchi c ounter automaton A e ∗ c such that (1) L ( A e ∗ c ) = S i ≥ 0 A e i , (2) for e ach ( w , i ) ∈ L ( A e ∗ c ) , w ∈ L ( A e i ) , and (3) for e ach w ∈ L ( A e i ) , j ≤ i ex ists su ch that ( w , j ) ∈ L ( A e ∗ c ) . Proof. Let δ b e the trans itio n r elation of A e 0 . The one-dimensiona l c o unter automaton A e ∗ c is giv en b y (1 , c , Q ′ , Σ , Q 0 , △ , F ) , with Q and △ defined as follows: (1) Start with △ = {∅} ; (2) F or each ( q , a, q ′ ) ∈ δ , a dd ( q , ( a, 0 ) , q ′ ) to △ ; (3) Build an iso morphic copy A I 0 c opy of the automaton formed b y the s tates in Q e 0 I 0 , the transitions be tw e en them, and the outgoing transitio ns from these states to states in Q e 0 I 1 , Q e 0 I 2 , . . . , Q e 0 I k − 1 , a nd Q e 0 T f . All the transitions ar e asso c ia ted with the counter increment 0; (4) Make all the states of A I 0 c opy nonaccepting; (5) F or each state q ∈ Q e 0 I 0 ∪ Q e 0 H and a ∈ Σ, if δ ( q , a ) leads to a state q ′ in a n increment Q e 0 I j , 1 ≤ j ≤ k − 1, then (a) F or each 1 ≤ ℓ < j , add to △ a transition ( q , ( a, j − l ) , q ′′ ), where q ′′ is the state cor resp onding to q ′ (b y the increment iso morphism) in Q e 0 I ℓ . Also, add a trans ition ( q , ( a, j ) , q ′′ ), where q ′′ is the state cor resp onding to q ′ in A I 0 c opy ; (b) If q ∈ Q I 0 , then let q c opy be the state cor resp onding to q in A I 0 c opy . F or each 1 ≤ ℓ < j , add to △ a transition ( q c opy , ( a, j − l ) , q ′′ ), where q ′′ is the state cor resp onding to q ′ (b y the increment iso morphism) in Q e 0 I ℓ . Also, add a tra nsition ( q c opy , ( a, j ) , q ′′ ), where q ′′ is the s tate corresp onding to q ′ in A I 0 c opy . AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 31 0 1 x,+(0) 2 a,+(0) c,+(1) 3 c,+(0) 6 a,+(1) c,+(2) a,+(0) 4 c,+(0) a,+(0) 5 y,+(0) a,+(0) c,+(1) c,+(0) a,+(1) c,+(2) b,+(0) Fig. 14. Automaton for Example 8.10. Let A e 0 c be the co unt e r -zero automa to n corres po nding to A e 0 . F ro m the obser v a- tions ab ov e, w e directly see that for each i ∈ N 0 w ∈ L ( A e i ) \ L ( A e 0 ), 1 ≤ j ≤ i exists such that ( w, j ) ∈ L ( A e ∗ c ) \ L ( A e 0 c ). Example 8.10. Figur e 14 pr esent s the r esult of applying t he c onstru ction of Pr op osition 8.9 to Automaton A e 0 of Example 8.5. 9. SAFETY AND PR ECISENESS After having co nstructed a finite automaton A e ∗ representing the extrap ola tion of a sequence A 1 , A 2 , . . . of auto ma ta, it remains to check whether it ac curately corres p o nds to what we rea lly in tend to compute, i.e., S i> 0 A i . This is done by fir st chec king that the extrap olatio n is safe , in the s ense that it captures all b e haviors of S i> 0 A i , and then chec king that it is pr e cise , i.e., that it ha s no more b ehaviors than S i> 0 A i . W e chec k b oth prop erties using sufficient conditions. W e develop separately these conditions for the tw o ( ω -)Reg ula r Reachability Problems. R emark 9.1. As we already ment io ned in the intro duction, the a bilit y to ex- trap olate an infinite sequence of auto ma ta ha s other a pplications than solving the ( ω -)Regular Rea chabilit y Pro blems (s e e [Boua jjani e t al. 20 04; Cantin et al. 2 0 08] for exa mples). Dep ending on the problem b eing consider ed, we may hav e to use other correctnes s criteria than those that are pro po sed in this pap er . 9.1 T rans itive Cl o sure of a T ransducer Consider a refle x ive deterministic finite-w o rd (resp e c tively , deterministic weak B ¨ uc hi) transducer T and let T e 0 be the la st ele ment of an incr ementally g rowing sam- pling sequence S I of p owers of T . Assume that T e 0 is the orig in o f a n e x trap o- lated sequence T e 0 , T e 1 , . . . . The limit o f this sequence is the transducer T e ∗ with L ( T e ∗ ) = S ∞ i =0 L ( T e i ) that has b een computed by applying the constr uction of Prop os itio n 8 .1 (r esp ectively , Propo sition 8.6 ) to T e 0 . W e provide sufficient criteria to test whether L ( T ∗ ) = L ( T e ∗ ). W e first determine w he ther T e ∗ is a safe ex trap olation of T , i.e., whether L ( T ∗ ) ⊆ L ( T e ∗ ). F or this, we pro po se the following r esult. Proposition 9.2. L et T 1 and T 2 b e two r eflexive tr ansduc ers define d over t he same alphab et. If L ( T 2 ◦ T 2 ) ⊆ L ( T 2 ) and L ( T 1 ) ⊆ L ( T 2 ) , then L ( T ∗ 1 ) ⊆ L ( T 2 ) . AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 32 · A. Legay , and P . Wol p er Proof. W e show by induction that fo r ea ch i > 0, L ( T i 1 ) ⊆ L ( T 2 ). The base cases, i.e., L ( T 0 1 ) ⊆ L ( T 2 ) and L ( T 1 ) ⊆ L ( T 2 ), ho ld by hypothesis. Supp ose now that i > 1 a nd that the result holds for any k < i . It is ea s y to see that L ( T i 1 ) ⊆ L ( T 2 ). Indeed, L ( T i 1 ) = L ( T i − 1 1 ◦ T 1 ) ⊆ L ( T 2 ◦ T 1 ) ⊆ L ( T 2 ◦ T 2 ) ⊆ L ( T 2 ). The first inclusion holds by induction, the second b ecause L ( T 1 ) ⊆ L ( T 2 ), and the third is b y hypothesis. By construction, L ( T ) ⊆ L ( T e ∗ ) and, more over, T is r eflexive. Co nsequently , Prop os itio n 9.2 states that if L ( T e ∗ ◦ T e ∗ ) ⊆ L ( T e ∗ ), then T e ∗ is a safe e x trap- olation of T ∗ . This criterio n is o nly sufficient since their co uld exist tw o words w, w ′ ∈ L ( T e ∗ ) suc h that w , w ′ 6∈ L ( T ∗ ) and w ◦ w ′ 6∈ L ( T e ∗ ). In practice, c hecking the condition expre s sed by Pr op osition 9.2 requires to complement T e ∗ . Indeed, this condition is equiv alent to chec king whether the language accepted by the au- tomaton which is the int e r section of the automaton for T e ∗ ◦ T e ∗ and the one for the c omplement of T e ∗ is empty or not. When working with weak automata, T e ∗ is by construction weak but generally not deterministic (see Pro p o sition 8.8 ). Our approach co nsists in deter minizing T e ∗ , and then chec k ing whether the resulting transducer is inherently weak. In the p ositive case, this tra nsducer can b e turne d int o a weak deterministic one and eas ily b e complemented by in verting the sets of accepting and nonaccepting states. Other wise a B ¨ uchi complemen tatio n algor ithm has to b e applied. W e no w turn to determine whether T e ∗ is a precise extrap ola tio n o f T , i.e., whether L ( T e ∗ ) ⊆ L ( T ∗ ). F or this, we aga in provide a par tial solutio n in the form of a sufficient criterion. The “precisenes s” problem amounts to proving that any word accepted by T e ∗ , or equiv alently by some T e i , is als o ac cepted by an iteratio n T j of the tra nsducer T . The idea is to chec k that this can b e pr oved inductiv ely . The prop erty is true by co nstruction for the transduce r T e 0 from which the extra po - lation sequence is built. If we can also prove that, if the prop erty holds for all T e j with j < i , then it a ls o holds for T e i , we are done. F or this, we prop ose the following theorem. Theorem 9.3. L et T and T e ∗ b e two tr ansduc ers and T e 0 b e a p ower of T . As- sume an infin ite se qu en c e of tr ansduc ers T e 0 , T e 1 , . . . , and let L ( T e ∗ ) = S ∞ i =0 L ( T e i ) . If ∀ w, ∀ i > 0 [ w ∈ L ( T e i ) \ L ( T e 0 ) ⇒ ∃ 0 ≤ j, j ′ < i, w ∈ L ( T e j ◦ T e ′ j )] , (1) then L ( T e ∗ ) ⊆ L ( T ∗ ) . Proof. The proo f is b y induction: we show that for e ach i ≥ 0 , L ( T e i ) ⊆ L ( T ∗ ). The base case, i.e., L ( T e 0 ) ⊆ L ( T ∗ ), ho lds by hyp o thesis. Supp os e now that i > 0 and that the res ult ho lds for any j < i . W e show that L ( T e i ) ⊆ L ( T ∗ ). Consider a word w ∈ L ( T e i ). If w ∈ L ( T e 0 ), then the r esult holds. If w / ∈ L ( T e 0 ) then, by C o ndition (1) there exist j, j ′ < i , w ′ ∈ L ( T e j ), w ′′ ∈ L ( T e j ′ ) such that w = w ′ ◦ w ′′ . Since, by inductive hypo thesis w ′ , w ′′ ∈ L ( T ∗ ), n 1 , n 2 ∈ N exist such that w ′ ∈ L ( T n 1 ) and w ′′ ∈ L ( T n 2 ). W e thus hav e w ∈ L ( T n 1 + n 2 ). Theorem 9.3 reduces the pro ble m of chec king the precis eness o f T e ∗ to the one of testing whether Condition (1) is sa tis fied or not. W e now g o one step further and reduce this test to automata-bas ed manipulations. AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 33 Lemma 9.4. L et T e 0 b e t he last element of an incr ement al ly gr owing sampling se quenc e S I of tr ansduc ers, and T e 0 c b e the c ount er-zer o au t omaton c orr esp onding to T e 0 . Assu me t hat T e 0 is the origin of an ext r ap olate d se quenc e T e 0 , T e 1 , . . . and let T e ∗ c 1 , T e ∗ c 2 , T e ∗ c 3 b e t hr e e c opies of the c oun ter tra n sduc er T e ∗ c which is obtaine d by applyi n g the c onstruction of Pr op osition 8.3 (r esp e ctively, Pr op osition 8.9) to T e 0 . If L ( π ( 6 = { c 2 ,c 3 } ) [( T e ∗ c 1 ∩ c ( T e ∗ c 2 ◦ c T e ∗ c 3 )) c 1 > { c 2 ,c 3 } )]) = L ( T e ∗ c ) \ L ( T e 0 c ) , (2) then ∀ w, ∀ i > 0 [ w ∈ L ( T e i ) \ L ( T e 0 ) ⇒ ∃ 0 ≤ j, j ′ < i, w ∈ L ( T e j ◦ T e ′ j )] . Proof. Obse r ve that the counter languag e of π ( 6 = { c 2 ,c 3 } ) [( T e ∗ c 1 ∩ c ( T e ∗ c 2 ◦ c T e ∗ c 3 )) c 1 > { c 2 ,c 3 } is the counter la nguage of T e ∗ c from wher e one has removed all the pairs ( w , i ) for which there is no t ( w ′ , j < i ) , ( w ′′ , j ′ < i ) ∈ L ( T e ∗ c ) with w = w ′ ◦ w ′′ . F or each i and ea ch word w , if w ∈ L ( T e i ) \ L ( T e 0 ) then, by Pro p osition 8.3 (resp ectively , Prop os itio n 8 .9), there exis ts k > 0 ∈ N such that ( w, k ≤ i ) ∈ L ( T e ∗ c ) \ L ( T e 0 c ). Since Condition (2) holds, ther e exist j, j ′ ∈ N with j, j ′ < k ≤ i and tw o words w ′ , w ′′ such that ( w ′ , j ) ∈ L ( T e ∗ c ) and ( w ′′ , j ′ ) ∈ L ( T e ∗ c ), with w = w ′ ◦ w ′′ . By Prop os itio n 8.3 (re sp ectively , Pro p osition 8.9), w ′ ∈ L ( T e j ) and w ′′ ∈ L ( T e j ′ ) and w ∈ L ( T e j ◦ T e j ′ ). W e can now s tate our ma in result. Theorem 9.5. L et T b e a tr ansduc er, T e 0 the last element of an incr emen- tal ly gr owing sampling se quenc e S I of p owers of T , and T e 0 c the c oun t er-zer o au- tomaton c orr esp onding to T e 0 . Assume t hat T e 0 is the origin of an extr ap olate d se quenc e T e 0 , T e 1 , . . . and let T e ∗ b e t he tr ansduc er t hat has b e en obtaine d by ap- plying the c onstruction of pr op osition 8.1 (r esp e ctively, Pr op osition 8.6) to T e 0 . L et T e ∗ c 1 , T e ∗ c 2 , T e ∗ c 3 b e thr e e c opies of the c ounter tr ansduc er T e ∗ c which is obtaine d by applying the c onst ruction of Pr op osition 8.3 (r esp e ctively, Pr op osition 8.9) to T e 0 . If L ( π ( 6 = { c 2 ,c 3 } ) [( T e ∗ c 1 ∩ c ( T e ∗ c 2 ◦ c T e ∗ c 3 )) c 1 > { c 2 ,c 3 } )]) = L ( T e ∗ c 1 ) \ L ( T e 0 c ) , then L ( T e ∗ ) ⊆ L ( T ∗ ) . Proof. By Prop o sition 8.1 (resp ectively , Prop os itio n 8 .6), we have L ( T e ∗ ) = S ∞ i =0 L ( T e i ). According to Lemma 9 .4, since L ( π ( 6 = { c 2 ,c 3 } ) [( T e ∗ c 1 ∩ c ( T e ∗ c 2 ◦ c T e ∗ c 3 )) c 1 > { c 2 ,c 3 } )]) = L ( T e ∗ c ) \ L ( T e 0 c ) , we hav e ∀ w, ∀ i > 0 [ w ∈ L ( T e i ) \ L ( T e 0 ) ⇒ ∃ 0 ≤ j, j ′ < i, w ∈ L ( T e j ◦ T e ′ j )] . It follows from Theorem 9.3 tha t L ( T e ∗ ) ⊆ L ( T ∗ ). Condition (2) can b e implemen ted as follows : —Observe that, since L ( π ( 6 = { c 2 ,c 3 } ) [( T e ∗ c 1 ∩ c ( T e ∗ c 2 ◦ c T e ∗ c 3 )) c 1 > { c 2 ,c 3 } )]) is disjoint from, chec king L ( π ( 6 = { c 2 ,c 3 } ) [( T e ∗ c 1 ∩ c ( T e ∗ c 2 ◦ c T e ∗ c 3 )) c 1 > { c 2 ,c 3 } )]) = L ( T e ∗ c ) \ L ( T e 0 c ) is equiv- alent to chec k L ( π ( 6 = { c 2 ,c 3 } ) [( T e ∗ c 1 ∩ c ( T e ∗ c 2 ◦ c T e ∗ c 3 )) c 1 > { c 2 ,c 3 } )] ∪ e T e 0 c ) = L ( T e ∗ c ), AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 34 · A. Legay , and P . Wol p er which av oid to co mpute L ( T e ∗ c ) \ L ( T e 0 c ). Computing L ( T e ∗ c ) \ L ( T e 0 c ) is a hard problem, which requires the ability to distinguish be tw e en ac cepting a nd nona c- cepting runs that assig n the same counter v aluation to a g iven word. —There are a lgorithms to co mpute ∩ c , ◦ c , and π ( 6 = { c 2 ,c 3 } ) . Those algo rithms di- rectly fo llow from the definitions g iven in Section 3 . Observe that if T is weak, then the counter automaton for T e ∗ c 1 ∩ c ( T e ∗ c 2 ◦ c T e ∗ c 3 ) is run-b ounded weak. —W e do not compute the one-counter automaton for ( T e ∗ c 1 ∩ c ( T e ∗ c 2 ◦ c T e ∗ c 3 )) c 1 > { c 2 ,c 3 } , but a M -synchronized counter automato n whose la ng uage and counter languag es may b e subsets of tho se of ( T e ∗ c 1 ∩ c ( T e ∗ c 2 ◦ c T e ∗ c 3 )) c 1 > { c 2 ,c 3 } . W e follow the metho d- ology described in Sec tion 3, and compute the extended-in tersec tion b etw een the automaton T e ∗ c 1 ∩ c ( T e ∗ c 2 ◦ c T e ∗ c 3 ) and tw o finite-word (resp ectively , run-b ounded weak B ¨ uchi) M -Universal-synchronized counter automa ta, one which is sync hr o- nized w.r .t. counters c 1 and c 2 , a nd the other one w.r.t. counters c 1 and c 3 . Assume that Σ 2 is the alphab et of T and d is the maximal increment v alue of T e ∗ c . The extended alphab et of T c is Σ × [0 , d ], and the one o f T e ∗ c 1 ∩ c ( T e ∗ c 2 ◦ c T e ∗ c 3 ) is th us Σ 2 × [0 , d ] 3 (see constr uctions for ◦ c and ∩ c ). In our ex per iments (see [Legay 2 007] fo r details ), we worked with counter automa ta whos e extended a l- phab et is Σ 2 × [0 , d ] 3 , a nd such that c 1 is M -sync hr onized with res pe c t to c 2 and c 3 , with M = 2 × d . This choice turned out to b e the b est compro mise for our exp erimental results [Legay 20 07; T(O)RMC ], where we clea r ly o bserved a synchronization b etw een the counters. —W e reduce the pro blem of c he cking the equiv alence b etw een the co unter lang uages of the tw o mem b er s of the equality to the one o f checking the equiv alence b etw een the languages of their extended automata (see Pro p o sition 3.1 3). Observe that, if L ( T ∗ ) = L ( T e ∗ ), then the tra nsducers T e i ( i ≥ 0) may consti- tute new elements in an ex tension of the sa mpling sequence S i , i.e., if S I = T s 0 , T s 1 , . . . , T s k with T s k = T e 0 , then the extension is T s 0 , T s 1 , . . . , T s k , T s k +1 , T s k +2 , . . . , with T s k + i = T e i for each i ≥ 0. Co ndition (1) is thus par ticularly de- signed to ho ld fo r sa mpling sequences where e a ch transducer can b e obtained by a single comp ositio n o f tra nsducers that a pp ear b efor e in the se q uence. Indeed, the conditio n can b e read as follows: e ach tr ansduc er T e i in the extende d sampling se quenc e is the c omp osition of two tr ansduc ers T e j and T e j ′ that app e ar b efor e in this se quenc e . If more than one c omp osition is needed, then the condition may not be satisfied even if L ( T e ∗ ) = L ( T ∗ ). Condition (1 ) ca n be adapted to work with other sampling sequences. This is illustra ted w ith the fo llowing exa mple. Example 9.6. If e ach tr ans du c er in t he sampling se quenc e is obtaine d by c om- p osing n tra ns du c ers t hat app e ar b efor e in the se quenc e, then one c an t est whether the fol lowing c ondition holds ∀ w, ∀ i > 0 [ w ∈ L ( T e i ) \ L ( T e 0 ) ⇒ ∃ 0 ≤ j 1 , . . . , j n < i, w ∈ L ( T e j 1 ◦ . . . ◦ T e j n )] , (3) r ather t han t o t est whether Condition (1) holds. Theorem 9.5 easily extends to other sampling sequences. AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 35 9.2 Limit o f a Sequence of R eachable Sets This s ection lifts the r esults obtained in the previous se ction to the c a se where one computes the limit of a sequence of rea chable states. W e consider a reflex- ive finite-word (resp ectively , deterministic weak B¨ uchi) tra nsducer T and a deter- ministic finite-word (r esp ectively , deterministic weak B ¨ uchi) automato n A . Let A e 0 be the last automato n o f a n incr ementally growing sampling seque nc e S I of A , T 1 ( A ), T 2 ( A ), T 3 ( A ), and as sume that A e 0 is the origin o f an ex trap olated sequence A e 0 , A e 1 , . . . . The limit of this sequence is the automa to n A e ∗ with L ( A e ∗ ) = S ∞ i =0 L ( A e i ) that has b een computed b y apply ing the construction of Prop os itio n 8.1 (resp ectively , Pr op osition 8 .6) to A e 0 . W e pr ovide sufficient cr ite- ria to tes t whether L ( T ∗ ( A )) = L ( A e ∗ ). W e fir st determine whether A e ∗ is a sa fe extra p olation of T ∗ ( A ), i.e., whether L ( T ∗ ( A )) ⊆ L ( A e ∗ ). F or this, we prop ose the following result. Proposition 9.7. L et A 1 and A 2 b e two au t omata define d over the same al- phab et Σ and with L ( A 1 ) ⊆ L ( A 2 ) . L et T b e a r eflexive t ra n s duc er over Σ 2 . If L ( T ( A 2 )) ⊆ L ( A 2 ) t hen L ( T ∗ ( A 1 )) ⊆ L ( A 2 ) . Proof. By hypo thesis, we have L ( A 1 ) ⊆ L ( A 2 ). W e show by induction that for ea ch i > 0, L ( T i ( A 1 )) ⊆ L ( A 2 ). The base ca ses, i.e., L ( A 1 ) ⊆ L ( A 2 ) a nd L ( T ( A 1 )) ⊆ L ( A 2 ), hold by hypothesis. Supp ose now that i > 1 a nd tha t the result holds for any j < i . It is easy to see that L ( T i ( A 1 )) ⊆ L ( A 2 ). Indeed, L ( T i ( A 1 )) = L ( T ( T i − 1 ( A 1 ))) ⊆ L ( T ( A 2 )) ⊆ L ( A 2 ). The fir st inclusio n holds by induction and the second bec a use L ( T ( A 2 )) ⊆ L ( A 2 ). Prop os itio n 9.7 states that checking whether A e ∗ is a safe extr ap olation of S ∞ i =0 T i ( A ) can be done by chec king w he ther L ( T ( A e ∗ )) ⊆ L ( A e ∗ ). It is worth ment io ning that this criter ion is o nly sufficient. Indeed, their could exist a word w ∈ L ( A e ∗ ) such that w 6∈ L ( T ∗ ( A )) and w 6∈ L ( T ( A e ∗ )). W e now turn to determine whether A e ∗ is a precise extrap ola tion of T ∗ ( A ), i.e., whether L ( A e ∗ ) ⊆ L ( T ∗ ( A )). As in Section 9.1, we use an inductive a rgument, which is formalized with the following theorem. Theorem 9.8. L et T b e a tr ansduc er and A, A e ∗ b e two automata. L et A e 0 = T k ( A ) , and c onsider an infinite se quen c e of automata A e 0 , A e 1 , . . . , with L ( A e ∗ ) = S ∞ i =0 L ( A i ) . If ∀ w, ∀ i > 0 [ w ∈ L ( A e i ) \ L ( A e 0 ) ⇒ ∃ 0 ≤ j < i, w ∈ L ( T ( A e j ))] , (4) then L ( A e ∗ )) ⊆ L ( T ∗ ( A ) . Proof. The pro of is by induction: w e show that for each i ≥ 0, L ( A e i ) ⊆ L ( T ∗ ( A )). The ba se cas e, i.e., L ( A e 0 ) ⊆ L ( T ∗ ( A )), ho lds by hyp o thesis. Sup- po se now that i > 0 and that the result holds for any j < i . W e show that L ( A e i ) ⊆ L ( T ∗ ). Consider a word w ∈ L ( A e i ). If w ∈ L ( A e 0 ), then the r esult holds. Ass ume now that w / ∈ L ( A e 0 ). B y Condition (4), there exists j < i such that w ∈ L ( T ( A e j )). Since, T is reflexive and by inductiv e hypothesis, there exis ts n such that L ( A e j ) ⊆ L ( T n ( A )). W e thus hav e w ∈ L ( T n +1 ( A )). AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 36 · A. Legay , and P . Wol p er W e no w go one step further and re duce the verification of Co ndition (4) to simple automata-bas ed manipulations. Lemma 9.9. L et T b e a r eflex ive tr ansduc er and A b e an automaton. L et A e 0 b e the last automaton of an incr emental ly gr owing sampling se quenc e S I of A , T 1 ( A ) , T 2 ( A ) , T 3 ( A ) , and assume t hat A e 0 is the origin of an extr ap olate d se quenc e A e 0 , A e 1 , . . . and let A e ∗ c 1 , A e ∗ c 2 b e two c opies of the c ount er automaton A e ∗ c that is ob- taine d by app lying the c onst ruction of Pr op osition 8.3 (r esp e ctively, Pr op osition 8.9) to ( A e 0 ,GR OW ( S I ) ( A e 0 ) ). L et A e 0 c b e the c ounter-zer o automaton c orr esp onding to A e 0 . If L ( π ( 6 = c 2 ) [( A e ∗ c 1 ∩ c T ( A e ∗ c 2 )) c 1 >c 2 )]) = L ( A e ∗ c ) \ L ( A e 0 c ) , (5) then ∀ w, ∀ i > 0 [ w ∈ L ( A e i ) \ L ( A e 0 ) ⇒ ∃ 0 ≤ j < i, w ∈ L ( T ( A e j ))] . Proof. Obse r ve that the counter languag e of π ( 6 = c 2 ) [( A e ∗ c 1 ∩ c T ( A e ∗ c 2 )) c 1 >c 2 is the counter lang uage of A e ∗ c from where o ne has removed all the pairs ( w , i ) for which there is no pair ( w ′ , j < i ) ∈ L ( A e ∗ c ) with w ∈ L ( T ( A w ′ )) (wher e A w ′ is an automaton whose la nguage is { w ′ } ) hav e b een r emov ed. F o r each i and ea ch w o rd w , if w ∈ L ( A e i ) \ L ( A e 0 ) then, by Prop os ition 8 .3 (resp ectively , Prop os itio n 8.9 ), there exis ts k > 0 ∈ N such tha t ( w , k ≤ i ) ∈ L ( A e ∗ c ). Since Condition (5 ) holds , there exists j ∈ N with j < k ≤ i ∈ N and a w ord w ′ such tha t ( w ′ , j ) ∈ L ( T e ∗ c ) with w = L ( T ( A w ′ )). By Pr o p osition 8.3 (resp ectively , P rop ositio n 8.9), w ′ ∈ L ( A e j ) and w ∈ L ( T ( A e j )). Finally , we obtain our main result. Theorem 9.10. L et T b e a r eflexive t r ansduc er and A b e an automaton. L et A e 0 b e the last automaton of an incr emental ly gr owing sampling se quenc e S I of A , T 1 ( A ) , T 2 ( A ) , T 3 ( A ) , and assume that A e 0 is the origin of an ex tr ap olate d se quenc e A e 0 , A e 1 , . . . L et A e ∗ b e the automaton that has b e en obtaine d by applying the c onstruction of Pr op osition 8.1 ( r esp e ctively, Pr op osition 8.6) to A e 0 , and let A e ∗ c 1 , A e ∗ c 2 b e two c opies of the c ounter automaton A e ∗ c that is obtaine d by applying the c onst ruction of Pr op osition 8.3 (r esp e ctively, Pr op osition 8.9) to A e 0 . L et A e 0 c b e t he c oun ter-zer o aut omaton c orr esp onding to A e 0 . If L ( π ( 6 = c 2 ) [( A e ∗ c 1 ∩ c T ( A e ∗ c 2 )) c 1 >c 2 )]) = L ( A e ∗ c ) \ L ( A e 0 c ) , then L ( A e ∗ ) ⊆ L ( T ∗ ( A )) . Proof. By Pr op osition 8.1 (resp ectively , Pr op osition 8.6), we have L ( A e ∗ ) = S ∞ i =0 L ( A e i ). According to Lemma 9 .9, since L ( π ( 6 = c 2 ) [( A e ∗ c 1 ∩ c T ( A e ∗ c 2 )) c 1 >c 2 )]) = L ( A e ∗ c ) , we hav e ∀ w, ∀ i > 0 [ w ∈ L ( A e i ) \ L ( A e 0 ) ⇒ ∃ 0 ≤ j < i , w ∈ L ( T ( A e j ))] . It follows from Theorem 9.9 tha t L ( A e ∗ ) ⊆ L ( T ∗ ( A )). AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 37 Theorem 9 .1 0 states a sufficient criterion to chec k whether A e ∗ is a pr ecise extra p- olation of T ∗ ( A ). This criterio n amounts to test whe ther Co nditio n (4) holds. F or this, we pro ceed like for Condition (2). Observe that, if L ( T ∗ ( A )) = L ( A e ∗ ), then the automata A e i ( i ≥ 0) may con- stitute new elements in an extension of the sa mpling sequence S I , i.e., if S I = A s 0 , A s 1 , . . . , A s k with A s k = A e 0 , then the extensio n is A s 0 , A s 1 , . . . , A s k , A s k +1 , A s k +2 , . . . , with A s k + i = A e i for each i ≥ 0. Condition (4) is thus par ticularly de- signed to hold for sampling sequence s where each element can b e obtained fro m the previous one b y a single application of the transducer T . Indeed, the condition can be rea d a s follows: e ach automaton A e i in t he extende d sampling se quenc e c an b e obtaine d by applying T to an element t hat app e ars b efor e in the se quenc e . If more applications of T are needed, then we may have to ada pt the co nditio n. This is illustrated with the following example. Example 9.11. If e ach element in the sampling se quenc e is o bt aine d by applying the tr ansduc er T k > 1 times to the pr evious element in the se quenc e, then one c an test whether the fol lowing c ondition holds ∀ w, ∀ i > 0 [ w ∈ L ( A e i ) \ L ( A e 0 ) ⇒ ∃ 0 ≤ j < i, w ∈ L ( T k ( A e j ))] . (6) r ather t han t o che ck Condition (4). This obser v ation states for sa mpling sequences where the num b er of applications of T needed to build each element from the previous one is c o nstant. In [Legay 2007], we pro p o sed another appro a ch that consis ts in asso cia ting to ea ch state of the sys tem an integer v ariable that co unt s the num b er o f a pplications o f the reachabilit y rela tion ne e de d to reach this s ta te fro m the initial set of s tates. Using this “co unter v ariable”, we can pr op ose a pr eciseness criter ion whose induction is based on the num b er of a pplications of the reachability relatio n rather than on the po sition in the sampling sequence. Con tra ry to the techniques presented in this section, the counters ar e no longer intro duced dur ing the ex trap olation pro cess , but are present in all the steps of the computation. This is a “key point” to ensure the precisenes s when consider ing a nonlinear sampling s e quence, but this clearly influence the ex trap olation pro ces s and the increments detection. As o bserved in [Legay 2007], this a pproach is of particular in terest when dealing with s y stems that manipulate in teg e r /rea l v ar iables. How ever, the solution in [Legay 2007 ] is not a pana cea. Indeed, as a n example, it is known tha t the tra ns itive clos ure of the relation { ( x, 2 x ) } in basis 2 is r egular, but the tra nsitive closure of the relation { (( x, y ) , (2 x, y + 1)) } is not r egular. 10. IMPLEMENT A TION AND E XPERIMENT S This section briefly discusses a n implemen tatio n of o ur results as well as the exp e r- imen ts that hav e b een c o nducted. 10.1 Heuristics Implemen ting the technique pres e nt ed in this pa p er requires p otentially co stly com- po sition and determinization pro cedures. In [Bo igelot et al. 2 003; 2004 ; Legay 200 7], AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 38 · A. Legay , and P . Wol p er we pr o p osed tw o heuristics that, in s ome situa tio ns, r e duce d to computation time from days to se conds. Exp erimental results, which are presented in Chapter 7 of [Legay 2007], show that those heur istics ar e particula r ly useful when working with arithmetic systems. 10.2 The T(O)RMC T o olset The r esults pres ented in this pap er hav e b een implemented in the T(O)RMC (states for T o ol for ( ω -)R e gular Mo del Che cking ) to olset [Legay 20 08], which re lies o n the LASH T o olset [LASH ] for automata manipulations . The L ASH to olset is a to ol for representing infinite sets and ex ploring infinite state spaces. It is bas ed o n finite-s tate representations, which rely o n finite au- tomata for repres ent ing and ma nipulating infinite sets o f v alues ov er v ar ious da ta domains. The to o l is comp ose d of se veral C functions gr oup ed in to pack ages . The LASH to olset implements s everal sp ecific a lgorithms for solving the ( ω -)regula r reachabilit y problems of se veral classes of infinite-s ta te systems, which include FIF O -queue systems [Boigelot and Go defroid 199 6; Boigelo t et a l. 199 7], systems with integer v ar iables [Boig e lot 2003 ], and linear hybrid systems [Boigelot et al. 2003; Boigelot and Herbreteau 2006]. T(O)RMC extends the LASH to ols e t with the generic algor ithm prese nted in this pap er. Contrary to the sp ecific algo rithms o f LASH, the algorithm of T(O)RMC is applicable to any system that can be re pr esented in the ( ω -)Regular Mo del Checking framework. This makes it p oss ible to handle c la sses of infinite-sta te systems that are beyond the s cop e of specific algo rithms, e.g., parametric systems. T(O)RMC is divided into three pack ag es, which are briefly describ ed herea fter. (1) The t r ansduc er p ackage tha t pr ovides data str uctures and algo rithms to ma- nipulate transducers (comp ositio n, image computation, . . . ). The pack a g e also provides several heuristics to improv e the efficie ncy of the op erations. (2) The extr ap olation p ackage for detecting increments in a seq uence o f automa ta, and extrap olating a finite sa mpling sequence. The to ol allows the user to precise (1) which sampling strategy has to b e used, and (2) ho w to build the successive elements in the infinite s equence. (3) The c orr e ctness p ackage that pr ovides data str uctures and algorithms to check the corr ectness of the extrap olation for several classes of pro blems. The pack a ge also contains all the data structures and alg o rithms to manipulate counter-word automata. T(O)RMC can be used to compute a n e x trap olation of a p os sibly infinite s equence of automa ta S = A 1 , A 2 , . . . . F or this, the us e r has to provide the following tw o functions: —A function named SAMPLING that takes as arg ument s tw o integers i and j . Each time T(O)RMC calls the function, it sets i a nd j to the indexes of tw o automata A i and A j , such that A j is incrementally lar ger than A i . The function returns an automaton A k which is assumed, by the user, to be the next automaton in a sampling sequence whose t wo last ele ments are A i and A j . —A function named CHECK that takes as arg ument an a utomaton A e ∗ . If the AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 39 function r eturns yes, then T(O )RMC a ssumes that A e ∗ is the extra p olation ex- pec ted by the user. This is this function that implements the chec ks for safety and pr eciseness. T o extra po late the infinite sequence of automata S , T(O)RMC b ehaves as follows: (1) T(O)RMC co mputes finite prefix es of S until it finds tw o a utomata A i and A j such that A j is incr ementally larger than A i . (2) T(O)RMC then tries to compute an incre mentally g rowing sampling sequence S I , assuming that the tw o first elements of this sequence are A i and A j . The automata ar e added o ne by one to the s ampling s e quence, using the function SAMPLING . E ach time a new a uto maton is added, the to ol checks whether S I is still incrementally growing. If no, then T(O)RMC go es back to p o int (1) and consider a prefix of a lo nger size. I f yes, then T(O)RMC extra p o lates S I and pro duces an automa ton A e ∗ . This extrap olation is followed by a call to the function CHECK on A e ∗ . If the function returns yes, then the co mputation terminates, a nd A e ∗ is the a uto maton re tur ned by the to ol. If the function returns no, then the to ol tries to increase S I by adding o ne more a utomaton. 10.3 A br i e f Overview of the Exp eriments The T(O )RMC to olset has b een applied to more than 100 ca se studies. This section only br ie fly reca ps the clas ses of problems for which T(O )RMC has b een used so far. Details ab o ut the exp er iment s (including p erfor mances in ter ms of time a nd memory , which v ary from examples to examples) can b e found in Chapter s 7 a nd 13 of [Leg ay 2007]. W e firs t used T(O )RMC to compute a n automata- based repres entation o f the set of re a chable states of several infinite-states systems, including par ametric sys- tems, FIFO-queue systems, a nd systems manipulating integer v ariables. Others exp eriments co ncerned the co mputation of the transitive closure of several arith- metic relations. It is w orth mentioning that the disjunctiv e na tur e o f some relations sometimes preven ts the direct us e of sp ecific domain-based techniques [Finkel and Leroux 2002 ; Bo igelot and Herbr e teau 20 06]. W e also applied T(O)RMC to the challenging pro blem o f analyz ing linear hybrid sys tems. One of the ca se studies consisted of co mputing a precise r epresentation of the set of rea chable sta tes of several versions of the le aking gas bu rner . T o the b est of our knowledge, only the techn iq ue in [Boigelot and Herbreteau 2006 ] was able to handle the cases we co n- sidered. Among the other exp eriments, w e should also men tion the computation of the s et of rea chable states of an a ugmented version of the IEE E Ro ot Conten tion Proto co l [Leg ay 2007], which has been p oint out to b e a hard problem [Simons and Sto elinga 200 1]. The ability o f T(O )RMC to compute the limit of an infinite se- quence of a uto mata has other applications. As an example, the to ol has be e n used in a semi-alg orithm to compute the convex hull of a set of integer vectors [Ca nt in et al. 200 7; 200 8]. T(O )RMC was also used to co mpute a symbolic repr esenta- tion o f the simulation r elation b etw een the states of se veral class es of infinite-sta te systems [Boua jjani et al. 200 4]. The ma in g oal o f T(O)RMC is not p erfo r mance improvemen t, but to allow exper - imen ta tion with automata seq uence extrap o lation in a v ar iety of con tex t that g o es beyond ( ω -)r e gular mo del chec king problems. As such T(O)RMC is slow er than AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 40 · A. Legay , and P . Wol p er to ols that are sp ecific to solving such mo del checking problems for the a rithmetic domain (e.g. F AST [Ba r din et al. 2006 ], LIRA [Be cker e t al. 20 0 7], LASH), but is p e rfectly comp etitive when handling other reg ular mo del chec king cas es (par a- metric systems, FIFO-queue systems, ...) [RMC ; V ar dhan and Visw ana tha n 2006]. T(O)RMC relies on LASH for automata manipulations. The LASH to o lset is ori- ent e d tow ar ds exp erimentation. It is thus less efficie nt for ma nipula ting automata representing sets of r e al/integer num b ers than LIRA a nd F AST that ar e oriented tow ards per formances. 11. A BRIE F COMP ARISON WIT H OTHER W OR K S In this section, we briefly compa re our appro ach with other generic techniques for solving the ( ω -)Regular Reachability Problems. The Regula r Mo del Checking framework has first b een prop osed in [K e sten et al. 1997] as a uniform paradig m for algo r ithmic verification of parametr ic systems. The contributions in [Kesten et al. 199 7] ar e an a utomata-base d repr esentation of parametric systems and an algo rithm to co mpute the tr ansitive closure of the finite- word transducer repres entin g the r eachabilit y rela tion of such systems. One ma jor difference with our work is that the constr uction in [Kesten e t al. 1997] can only be applied to a very sp ecific class of finite-word transducer s . In [Boua jjani et al. 2000 ; Ab dulla et al. 2 003], Nilsso n et al. pr o p osed sev- eral simulation-based techniques that, given a finite-word transducer T , compute a finite-state repre s entation for T + . The core idea of thos e techniques is to iter - ately compute the success ive unions T ≤ 1 , T ≤ 2 , T ≤ 3 , . . . (where T ≤ i = S i n =1 T n ) and collapsing prog ressively their states ac c ording to an equiv alence r elation, which is induced by the simulation relations. The results of [B o ua jjani et a l. 20 00; Ab dulla et al. 20 0 3] have b e e n implemented in a tool called the RMC toolset (sta tes for T o ol for Regular Mo del Checking) [RMC ], a nd tested on several parametric and queue systems for which go o d results have b een obtained [Nilsso n 2005]. Unfortunately , it seems that the relatio ns us ed to merge the s tates of the successive unions ha ve b een designed to handle para metric a nd queue systems only . T o the b est o f our k nowl- edge, the RMC to olset cannot be used with o ther cla sses o f systems such as linear int eg er systems. In [Dams et al. 2002], Dams , La khnech, a nd Steffen pro po sed a non-implemented simulation-based technique to compute T + . This technique is similar to those prop os e d in [Boua jjani et al. 200 0 ; Ab dulla et al. 200 3 ]. In [T ouili 2 001; 2003], T ouili pr op osed a nother extr ap olation-ba sed technique to solve the Regular Reac ha bility Pr oblems. The results presented in this paper share some notions with those in [T ouili 2001; 200 3]. Indee d, the co re idea in the work of T ouili is to compute a n extrap olatio n of a finite-word transducer by c o mparing a finite prefix of its successive p owers, trying to detect incr e ment s b etw een them. One ma jor drawback of T ouili’s w or k, which is not implemented, is that no efficien t metho d is pr ovided to detect the increments. The r e is no metho dolog y to test whether the extra p o lation is precis e or no t. It is howev er easy to see that our preciseness criterion directly adapts to T ouili’s extra po lation pro cedure. In [V a rdhan e t a l. 2004 ; V ardha n 2006 ], V a rdhan et al. apply machine lear ning techn iq ues from [Angluin 1987 ; Rivest and Shapire 1993] to learn a finite-word AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 41 0 1 a 2 x (a) A 1 0 1 a 2 c 3 x (b) A 2 0 1 a 2 c d 3 c 4 x (c) A 3 Fig. 15. Automata for Example 12.1. automaton that r e presents the set of reachable states of a regular system. The results in [V ardhan et a l. 200 4; V ar dhan 2006 ] hav e b een implemented in a to o l called LEVE R [V ar dhan and Viswanathan 2006], which has b een applied to FIF O - queue a nd linear in teger systems. A drawback with th is appro ach is tha t it requires the addition of witness v ar iables that may break the regularity of the set of reachable states. W e als o mention that in [Hab ermehl and V o jnar 200 4 ], Hab ermehl et al. also pr op osed to use a learning- based approa ch to compute the set of r e achable states of several para metr ic systems. Finally , ev en if they do not c o nsider exactly the same pr oblem as us , it is relev ant to mention a series of rec e nt work [Boua jjani et al. 20 04; B oua jjani et a l. 200 5] that combine abstr action-bas e d techniques with automa ta -based cons tr uctions to verifying r eachabilit y prop erties . Those works hav e b een shown to b e particularly efficient for par ametric a nd queue systems [Bo ua jjani e t a l. 2004 ] as well a s for systems manipulating p ointers [B oua jjani et al. 200 5]. On the o ther hand, one dedicated abs traction is needed for each c la ss of system, while our extrap ola tion- based tec hnique is des ig ned to b e applicable on any system that can be represented by a ( ω -)regular system. 12. CONCLUSION AND FUTURE W OR K In this pa p e r , we ha ve in tro duced an extra p o lation-based technique for solving the ( ω -)Regular Reachabilit y Pr oblems. The a pproach consists in co mputing the limit of an infinite sequence of minimal finite-word (r esp ectively , minimal weak B ¨ uc hi) automata by extrap olating a finite sampled prefix of this sequenc e , i.e., selected automata fro m a pr efix of the se quence. The technique do es not guarantee that a result will b e obtained, and co rrectness o f the guessed extrap ola tion needs to b e chec ked o nce it is obtained. Our r esults have b een implemented in a to ol called T(O)RMC, which has b een applied to several case studies. One p oss ible dir ection for future work w ould b e to ex tend the increment detection pro cedure descr ibe d in Section 7. Indeed, as it is illus trated with the following example, the pro cedure is not able to detect all p ossible forms of increment. Example 12.1. Consider t he finite-wor d automata given in Figur e 15. The au- tomaton A 2 differs fr om the automaton A 1 by the addition of an incr ement, which is r epr esente d by state 1 . If we c omp ar e A 2 and A 3 , we se e the addition of one mor e incr ement. Cle arly, A 3 differs fr om A 1 by the addition of two incr ements r ep- r esente d by st ates 1 and 2 . Unfortunately, in A 3 , the incr ement dete cte d b et we en A 2 and A 3 (state 2 of A 3 ) is the origin of a tr ansition whose destination is t he incr ement dete cte d b etwe en A 1 and A 2 (state 1 of A 3 ). Such a situ ation c ann ot b e AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 42 · A. Legay , and P . Wol p er c aptur e d with the te chnique intr o duc e d in Se ction 7. W e co uld also inv estigate whether it is p oss ible to detect the rep etition of dif- ferent increment pa tter ns in the same auto ma ton. As a n example, the auto ma ta representing ab , aabb , aaabbb , ... differ b y the rep etitions of the sy mbols a and b . If we separa tely close those rep etitions, we will obtain a n auto ma ton tha t r epresents a + b + . This lang uage, which is a n ov er approximation of the “corr ect” c losure (i.e., a n b n ( n ∈ N 0 )), ma y be sufficien t for practica l applications. Another in ter esting di- rection would be to extend our results to other classes of automa ta, whic h includes tree and pushdown automata. Another interesting direction would b e to extend our r e sults to other cla sses of systems such as visibly pushdown sys tems [Alur and Ma dhusudan 20 04]. W e could isolate a class of s ystems for whic h we can alw ays co mpute a safe and precise extrap olatio n. Finally , it would b e of interest to extend ( ω -)Regular Mo del Checking to the verification of Op en systems . As opp os ed to state-transition s y stems, op en systems are s ystems whos e b ehavior dep ends on an exter nal environment. In a series of fairly recent pap ers, symbolic g ames [Ab dulla et al. 2003 ; de Alfaro et a l. 200 1; Bouyer et al. 20 05] ha ve b een prop osed as a general framework to sp ecifying finite- state Op en systems [Adler et al. 20 06; de Alfar o and Henzinger 2001; de Alfaro et a l. 2 005]. W e belie ve that our work could help to extending this approa ch to infinite-state op en systems. Thanks W e thank Berna rd B o igelot for a fruitful co llab oratio n on preliminary versions of this work. W e also thank Marcus Nilsso n, Julien d’Orso, Parosh Abdulla, Sba stien Jo dogne, Ela d Shahar , Ma rtin Steffen, T ayssir T o uili, and Mahesh Viswanathan for answering many questions rega r ding their works and case studies. REFERENCES Abdulla, P. A. , Bouajjani, A. , a n d d’Orso, J. 2003. Deciding monotonic games. In Pr o c. 12th Int. Confer enc e for Computer Scienc e L o gic (CSL) . Lecture Notes in Computer Science, vol. 2803. Spri nger, 1–14. Abdulla, P. A. , Bouajjani, A. , Jonsson, B. , and Nilsson, M . 1999. Handling global condi- tions in parameterized system ve r ification. In Pr o c. 11th Int. Confer e nc e on Computer Aide d V e rific ation (CA V) . Lecture N otes in Computer Science, vol. 1633. Spr i nger, 134–145. Abdulla, P. A. and Jonsson, B. 1996. V eri fying programs with unreli able channels. Information and Computation 127, 2 ( June), 91–101. Abdulla, P. A. , Jonsson, B. , M a ha t a, P. , and d’Orso, J. 2002. Regular tree mo del chec king. In Pr o c. 14th Int. Confer enc e on Computer Aide d V erific ation (CA V) . Lecture Notes in Computer Science, v ol. 240 4. Springer, 555 –568. Abdulla, P. A. , Jonsson, B. , Nilsson, M. , and d’Orso, J. 2003. Al gorithmic i mprov emen ts in regular mo del chec king. In Pr o c. 15th Int. Confer enc e on Computer A ide d V erific ation (CA V) . Lecture Not es in Compute r Science, v ol. 2725. Springer, 236–24 8. Abdulla, P. A. , Jonsson, B. , Nilsson, M. , d’Orso, J. , and Saksena, M. 2004. Regular m odel c hecking for ltl(mso). In Pr o c. 16th Int. Confer enc e on Computer Aide d V erific ation (CA V) . Lecture Not es in Compute r Science, v ol. 3114. Springer, 348–36 0. Adler, B. T. , de Alf aro, L. , da S il v a, L. D. , F aella , M. , Lega y, A. , Ram an, V. , and R oy, P. 2006. Ticc: A tool f or interface compatibility and composition. In Pr o c. 18th Int. Confer enc e on AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 43 Computer Aide d V erific ation (CA V) . Lecture Notes i n Computer Science, v ol. 4144. Springer, 59–62. Alur, R. , Courcoubetis, C. , Halbw achs, N. , Henzing er, T. A. , Ho, P. , Nicollin, X. , Oliv- ero, A. , Sif akis, J. , an d Yovine, S. 19 95. The algorithmic analysis of h ybri d systems. The o- r etic al Computer Sc ienc e 138, 1, 3–34. Alur, R. an d Madhusudan, P. 2004. Visi bly pushdown languages. In Pr o c. 36th Int. ACM Symp osium on The ory of Computing (STOC) . ACM, 20 2–211. Angluin, D. 1987. Learning regular sets from queries and coun terexamples. Information and Computation 75, 2, 87–106. Apt, K. R. a n d Kozen, D. 1986. Limits for automatic verification of finite-state concurren t systems. Information Pr o c essing L et ter 22, 6, 307–309. Bardin, S. , Finkel, A. , and Ler oux , J . 2004. F aster acceleration of coun ter automata i n practice. In Pr o c. 10th Int. Confer enc e on T o ols and Algorithms for the Construction and Ana ly sis of Systems (T ACAS) . Lecture Notes in Computer Sc i ence, v ol. 2988 . Springer, 576–5 90. Bardin, S. , Finkel, A. , Leroux, J. , and Schnoeb e len , P. 200 5. Flat acceleration in symbolic model chec king. In Pr o c. 3th Int. Confer enc e on Automate d T e chnolo gy for V erific ation and Ana lysi s (A TV A) . Lecture Notes in Computer Scienc e, vol. 3707. Springer, 474–488. Bardin, S. , Ler oux, J. , and Point, G. 2006. F ast extend ed r elease. In Pr o c. 18th Int. Confer- enc e on Computer Aid ed V erific ation (CA V) . Lecture Notes in Computer Science, vol. 4144. Springer, 63–66. Becker, B. , Dax, C. , Eisinger, J. , a n d Klaedtke, F. 2007. LIRA: Handling constrain ts of linear arithmetics ov er the in tegers and the reals. In Pr o c. 19th Int. Confer enc e on Computer Aide d V e rific ation (CA V) . Lecture N otes in Computer Science, vol. 4590. Spr i nger-V erl ag, 307–310. Boigelot, B. 1999. Symb olic M etho ds for Exploring Infinite State Sp ac es . Collection des publi- cations de la F acult ´ e des Sciences Appliqu ´ ees de l’Universit ´ e de Li ` ege, Li ` ege, Belgium. Boigelot, B. 2003. On iterating linear transformations ov er reco gnizable sets of in tegers. The o- r etic al Computer Sc ienc e 309, 1-3, 413–468. Boigelot, B. and Godefro id, P. 1996. Sym b oli c v erification of comm unication protocols with infinite state spaces using qdds (extend ed abstract ). In Pr o c. 8th I nt . Confer enc e on Computer Aid ed V erific ation (CA V) . Lecture Notes in Computer Science, vol. 1102. Springer, 1–12. Boigelot, B. , Godefroid, P. , Willems, B. , a nd Wolper, P. 1997. The pow er of qdds (ext ended abstract). In Pr o c. 4th Int. Symp osium on Stati c A nalysis (SAS) . Lecture Notes in Comput er Science, v ol. 130 2. Springer, 172 –186. Boigelot, B. and Herb reteau, F. 200 6. The pow er of hybrid acce l eration. In Pr o c. 18th Int. Confer enc e on Computer Aide d V erific ation (CA V) . Lecture Notes in Compute r Science, vol. 4144. Spri nger, 438–451. Boigelot, B. , Herb reteau, F. , and Jodogne, S. 2003. Hybrid acceleration using real vector automata (extended abstract) . In Pr o c. 15th Int. Confer enc e on Computer A ide d V e rific ation (CA V ) . Lecture Notes i n Computer Sc i ence, vol. 272 5. Springer, 193 –205. Boigelot, B. , Jodogne, S . , and W olper, P. 2001. On the use of weak automata for deciding linear arithmetic with intege r and real v ari ables. In Pr o c. Int. Jo i nt Confer enc e on Automate d R e asoning (IJCAR) . Lecture Notes in Computer Science, vol. 2083. Springer- V erlag, Si ena, Italy , 611– 625. Boigelot, B. , Jodogne, S. , and Wolper, P. 2005. An effective decision pro cedure for li near arithmetic o ver th e intege r s and reals. ACM T r ansactions on Computational L o gic 6, 3, 614– 633. Boigelot, B. , Lega y, A. , and Wolper, P. 2003. Iterating transducers i n the large (extended abstract). In Pr o c. 15 t h Int. Confer enc e on Computer Aide d V erific ation (CA V) . Lecture Notes in Computer Science. Spri nger, 223–235. Boigelot, B. , Lega y, A. , and Wolper, P. 2004. Omega-regular mo del che cking. In Pr o c. 10th Int. Confer enc e on T o ols and Algorithms for the Construction and Analysis of Sy stems (T ACAS) . Lecture Notes i n Comput er Science, vol. 298 8. Springer, 561 –575. AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 44 · A. Legay , and P . Wol p er Boigelot, B. , Rassar t, S. , and Wolper, P. 1998. On the expressive ness of real and int eger arithmetic automata (extended abstract). In Pr o c. 25th Int. Col lo quium on Automata, L an- guages and Pr o gr amming (ICALP) . Lecture Notes in Computer Science, v ol. 1443. Springer, 152–163. Boigelot, B. and Wolper, P. 2002. Representing ar ithmetic const r aint s wi th finite aut omata: An ov erview. In Pr o c. 18th Int. Confer enc e on lo gic Pr o gr amming (ICLP) . Lecture Notes in Computer Science, vo l . 2401. Springer, 1–19. Bouajjani, A. , Esp arza, J. , an d Maler, O. 1997. Reac habil i t y an al ysis of pushdo wn automata: Application to mo del-chec king. In Pr o c. 8th Int. Confer enc e on Concurr ency The ory (CON- CUR) . Lecture Notes i n Comput er Science, v ol. 1243. Springer, 135– 150. Bouajjani, A. and Habermeh l, P. 19 97. Symbolic reac hability analysis of fifo c hannel systems with nonregular sets of configurations (extended abstract). In Pr o c. 24th Int. Col lo quium on Au t omata, L anguages and Pr o gr amming (ICALP) . Lecture Notes in Computer Science, vol. 1256. Spri nger, 560–570. Bouajjani, A. , Haberm ehl, P. , Moro, P. , an d Vojnar, T. 2005. V erifying programs with dynamic 1-selector-link ed structures in r egular model c heck i ng. In Pr o c. 11th Int. Confer enc e on T o ols and Algorithms f or the Construction and Ana ly sis of Syste ms (T A CA S) . Lecture Notes i n Computer Sc i ence, v ol. 3440 . Springer, 13–2 9. Bouajjani, A. , Habermehl, P. , R oga lewicz, A. , and V ojnar, T. 2006. Abstract regular tree model chec king of complex dynamic data structures. In Pr o c. 13th Int. Sy mp osium on Static Ana lysi s (SAS) . Lect ur e N otes in Computer Science, vol. 4134. Springer, 52–70. Bouajjani, A. , Habermehl, P. , and Vojnar, T. 2004. Abstract r egular m odel chec king. In Pr o c. 16th Int. Confer enc e on Computer Aide d V erific ation (CA V) . Lecture Notes in Computer Science, v ol. 311 4. Springer, 372 –386. Bouajjani, A. , J on sson, B. , Nilsson, M. , and Touili, T. 2000. Regular mo del chec king. In Pr o c. 12th Int. Confer enc e on Computer Aide d V erific ation (CA V) . Lecture Notes in Computer Science, v ol. 185 5. Springer-V erlag, 403–418. Bouajjani, A. , Lega y, A. , and W olper, P. 2004. Handling liveness prop erties in (omega- )regular mo del c hecking. In Pr o c . 6th Int. Workshop on V erific ation of Infinite State Systems (INFINITY) . Electronic Notes in Theoretica l Computer Science, vol. 138( 3). Elsevier Science Publishers. Bouajjani, A. a nd Touili, T. 2002. Extrap olating tree transfor mations. In Pr o c. 14th Int. Confer enc e on Computer Aide d V erific ation (CA V) . Lecture Notes in Compute r Science, vol. 2404. Spri nger, 539–554. Bouyer, P. , Ca ssez, F. , Fleur y, E. , an d Larsen, K. G. 2005. Synthesis of optimal strate- gies using hytec h. In Pro c. 1st In t. W orkshop on Game in Design and V erification (GD V 04). Ele ctr onic Notes in The or etica l Computer Sci enc e 119 , 11–3 1. Cantin, F. , Lega y, A. , and W olper, P. 2007. Computing con vex h ull s by automata iteration. In Pr o c. 1th Int. Confer enc e automata: F r om Mathematics to Applic ations (AUTOMA THA) . T o appear. Cantin, F. , Lega y, A. , and Wolper, P. 2008. Computing conv ex hull by automata iteration. In Pr o c. 13 t h Int. Confer enc e on Implementation and Applic ation on Automa t a (CIAA) . Lecture Notes i n Computer Sc i ence, v ol. 5148 . Springer, 112– 121. Dams, D. , Lakhnech, Y. , and S teffen, M. 2002. Iterating transducers. Journal of Lo gic and Algebr aic Pr o gr amming (JLAP) 52-53 , 109–127. de Alf aro, L. , da Sil v a, L. D. , F aella, M. , Lega y, A. , Ro y, P. , and Sorea, M. 2005. Sociable int er f aces. In Pr o c 5th Int. Confer ence on F r ontiers of Combining Systems (FROCOS) . Lecture Notes i n Computer Sc i ence, v ol. 3717 . Springer, 81–1 05. de Alf aro, L. and Henzinger, T. A. 2001. In terface theories for component-based design. In Pr o c. 1st Int. Workshop on Emb e dde d Systems (EMSOFT) . Lecture Notes in Computer Science, v ol. 221 1. Springer, 148 –165. de Alf a ro, L. , Henzinger, T. A. , a n d Majumdar, R. 2001. Symbolic algorithms for infinite- state games. In Pr o c. 12th Int. Confer ence on Concurr ency The ory (CO NCUR) . Lecture N otes in Computer Science, vol. 2154 . Springer, 536– 550. AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY. On (Omega-)Regular Model Check ing · 45 Finkel, A. and Leroux, J . 2002. How to comp ose presburger-accelerations: Applications to broadcast proto cols. In Pr o c. 22r d Int. Confer enc e on F oundations of Softwar e T e chnolo gy and The or etic al Computer Scienc e (FSTTCS) . Lecture N otes in Computer Science, vol. 2556. Springer, 145–156. Finkel, A. , Willems, B. , and Wol per, P. 1997. A dir ect symbolic approach to model chec k- ing pushdo wn systems. In Pr o c. 2nd Int. Workshop on V e rific ation of Infinite State Systems (INFINITY) . Elect r onic Notes in Theoretical Comput er Science, v ol . 9. Elsevier Science Pub- lishers. Habermehl, P. and Vojnar, T. 2004. Regular m odel chec king usi ng i nference of regular l an- guages. In Pr o c. 6th Int. Workshop on V erific ation of Infinite State Syst ems (INFINITY) . Electronic Notes in The or etical Computer Science, v ol. 138(3 ). Elsevier Science Publi s hers. Henglein, F. and Rehof, J. 1998. Constrain t automata and the complexity of r ecursive sub- t yp e ent ai lment . In Pr o c. 25th Int. Col lo quium on Automata, L anguages and Pr o gr amming (ICALP) . Lec ture Notes in Computer Science, vol. 1443. Springer, 616–627. Hopcroft, J. E. 1971. An n log n algorithm f or minimizing states in a finite automaton. The ory of Machines and Computation , 189–196. Ibarra, O. H. 1978. Rev er sal-b ounded multicoun ter machines and their decision problems. Jo ur- nal of the ACM 25, 1, 116–133. Jonsson, B. and Nilsson, M. 2000. T ransitive closures of regular relations for verifying infinite- state systems. In Pr o c. 6th Int. Confer enc e on T o ols and Algo ri thms for the Construction and Analysis of Systems (T A CA S) . Lecture Notes in Computer Science, vo l . 1785. Springer, 220–234. Kesten, Y. , Maler, O. , Ma rcus, M. , Pnueli, A. , an d Sh ahar, E. 1997. Symbolic mo del c hecking wi th ri c h assertional languages. In Pr o c. 9th Int. Confer e nc e on Computer Aide d V e rific ation (CA V) . Lecture N otes in Computer Science, vol. 1254. Spr i nger, 424–435. Kesten, Y. , Pnueli, A. , Sha har, E. , an d Zuck, L. D. 2002. Net work inv ari an ts in action. In Pr o c. 13th Int. Confer enc e on Concurr ency The ory (CONCUR ) . Lecture Notes in Computer Science, v ol. 242 1. Springer, 101 –115. Klaedtke, F. and Rueß, H. 2003. Monadic second-order logics with cardinalities. In Pr o c. 30th Int. Col lo quium on Au t omata, La ng uages and Pr o gr amming (ICALP) . Lecture Notes in Computer Science, vo l . 2719. Springer-V erl ag, 681–696. LASH. The Li` ege Automat a- based Sym b oli c Handler (LASH). Av ail able at http://w ww.montefiore.ulg.ac.be/~boigelot/research/lash/ . Lega y, A. 2007. Generic T e chniques for the V erific ation of Infinite-State Systems . Collection des publications de la F acult ´ e des Sciences Appliqu´ ees de l’Universit ´ e de Li` ege, Li` ege, Belgium. Lega y, A. 2008. T(o)rmc: A to ol for (omega-)regular model chec king. In Pr o c. 20th Int. Confer- enc e on Computer Aid ed V erific ation (CA V) . Lecture Notes in Computer Science, vol. 5123. Springer, 548–551. L ¨ oding, C. 2001. Efficient minim ization of deterministic weak ω − automata. Information Pr o- c essing L e t ters 79, 3, 105–109. Mohri, M. 2003. Edit-distance of weigh ted automata: General de finitions an d algorithms. Inter- national Journal on F oundations of Computer Scienc e 14, 6, 95 7–982. Muller, D. E. , Saoudi, A. , and Schupp, P. E. 1986. Al ternating automata, t he we ak monadic theory of the tree and its complexity . In Pr o c. 13th Int. Col lo quium on Automata, L anguages and Pr o g r amming . Springer-V erlag, Rennes, 275–283 . Nilsson, M. 20 01. Regular mo del ch ecking. M. S. thesis, Uppsala Uni v er s ity . Nilsson, M. 20 05. Regular mo del ch ecking. Ph.D. thesis, Uppsala Unive r sity . Pnueli, A. a nd Sha har, E. 2000. Liveness and acceleration in parameterized verification. In Pr o c. 12th Int. Confer enc e on Computer Aide d V erific ation (CA V) . Lecture Notes in Computer Science, v ol. 185 5. Springer, 328 –343. Rivest, R. L. and Shapire, R. E. 1993. Inference of finite automata usi ng homing sequences. Information and Computation . RMC. The regular model c hecking to ol (RMC). Av ailable at http://w ww.it.uu.se/research/docs/fm/apv/rmc . AC M T ransactions on Co m putational Logic, V ol. V, No. N, 20YY. 46 · A. Legay , and P . Wol p er R oos, R. S. 1988. Deciding equiv alence of deterministic one-coun ter automata in p olynomial time with applications t o learning. Ph.D . thesis, Smith Coll ege. Safra, S. 1992. Exp onen tial determinization for ω -automata with strong-fairness acceptance condition. In Pr o ce e dings of t he 24th ACM Sy mp osium on The ory of Computing . Victoria. Simons, D. P. L. and S toelinga, M. 2001. Mecha ni cal verification of the ieee 1394a ro ot con tention protocol using uppaal2k. International Journal on Softwar e T o ols for T e chnolo gy T r ansfer (STTT) 3, 4, 469–485. T(O)RMC. The T(O) RM C to olset. Av ail able at http://w ww.montefiore.ulg.ac.be/ legay/TORMC /index-tormc.html . Touili, T. 2001. Regular mo del chec king using widening technique s . Ele ctr onique Notes in The or etic al Computer Scienc e 50, 4. Touili, T. 2003. Analyse symbolique de syst ` emes infinis bas ´ ee sur les automates: Application ` a la v´ erification de syst` emes pa r am´ etr ´ es. Ph.D. th esi s, U nive r sit´ e de P ar i s 7. Touili, T. and d’Orso, J . 2006. Regular hedge mo del c hecking. In Pr o c. 4th Int. IFIP Confer enc e on The or etic al Computer Scienc e (TCS06) . V ardhan, A. 2006. Learning to verify systems. Ph.D. thesis, Univerist y of Illinois. V ardhan, A. , Sen, K. , Visw ana than , M. , and Agha, G . 2004. Actively learning to ve r ify safet y f or fifo automata. In Pr o c. 24r d Int. Confer enc e on F oundations of Softwar e T echno lo gy and The or etic al Computer Scienc e (FSTTCS) . Lecture N otes in Computer Science, vol. 3328. Springer, 494–505. V ardhan, A. , Sen , K. , Visw anat h an, M. , a nd Agha, G . 2005. Using language i nference to v er i fy omega-regular pr operties. In Pr o c. 11th Int. Confer enc e on T o ols and Algorithms f or the Construction and Analysis of Sy stems (T ACAS) . Lecture Notes in Computer Scien ce, vo l . 3440. Spri nger, 45–60. V ardhan, A. and Visw ana than, M. 2006. Leve r : A to ol for learning based verification. In Pr o c. 18th Int. Confer enc e on Computer A ide d V eri fica t ion (CA V) . Lecture Notes in Computer Science, v ol. 414 4. Springer, 471 –474. V ardi, M. Y. 2007. F rom c hurc h and prior to psl. Av ail able at http://w ww.cs.rice.edu/ vardi/papers /index.html . W olper, P. and Boigelot, B. 1995. An automata-th eoretic approach to presburger arithmet i c constrain ts (extended abstract). In Pr o c. 2nd Int. Sy mp osium on Static Analysis (SAS) . Lec- ture N otes in Comput er Science, v ol. 983. Springer, 21–32 . W olper, P. and Boigelot, B. 1998. V erif ying systems wi th infinite but regular state spaces. In Pr o c. 10th Int. Confer enc e on Computer Aide d V erific ation (CA V) . Lecture Notes in Computer Science, v ol. 142 7. Springer-V erlag, 88–97. W olper, P. and Boigelot, B. 2000. On the construction of automata fr om l inear ari thmetic constrain ts. In Pr o c. 6th Int. Confer enc e on T o ols and Algorithms for the Construction and Ana lysi s of Systems (T A CAS) . Lecture Notes in Comput er Science, v ol. 1785 . Springer, 1–19. AC M T ransacti on s on Computati onal Logic, V ol. V, No. N, 20YY.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment