Distributed authentication for randomly compromised networks
We introduce a simple, practical approach with probabilistic information-theoretic security to solve one of quantum key distribution's major security weaknesses: the requirement of an authenticated classical channel to prevent man-in-the-middle attac…
Authors: Travis R. Beals, Kevin P. Hynes, Barry C. S
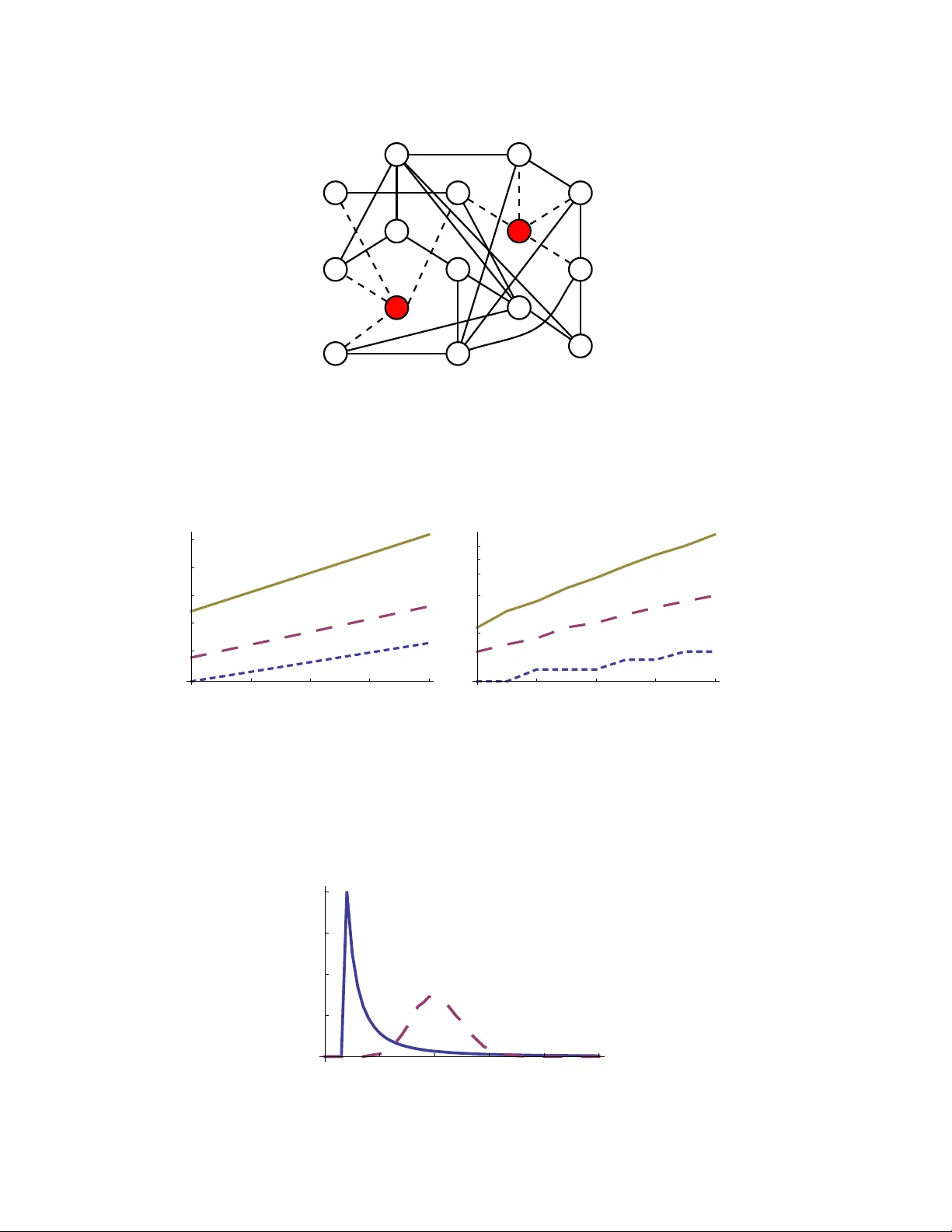
Distributed authen tication for randomly compromised net w orks T ra vis R. Beals 1 , Kevin P . Hynes 2 , and Barry C. Sanders 2 1 Departmen t of Ph ysics, Universit y of California, Berkeley , California 94720, USA 2 Institute for Quan tum Information Science, Universit y of Calgary , Alberta T2N 1N4, Canada E-mail: bsanders@qis.ucalgary.ca Abstract. W e introduce a simple, practical approac h with probabilistic informa- tion-theoretic securit y to solv e one of quantum k ey distribution’s ma jor securit y w eaknesses: the requirement of an authenticated classical channel to preven t man-in- the-middle attac ks. Our sc heme emplo ys classical secret sharing and partially trusted in termediaries to pro vide arbitrarily high confidence in the security of the proto col. Although certain failures elude detection, we discuss preemptiv e strategies to reduce the probability of failure to an arbitrarily small level: probabilit y of such failures is exp onen tially suppressed with increases in connectivit y (i.e., connections p er no de). P A CS n umbers: 03.67.Dd, 89.20.Ff, 89.70.-a, 89.75.-k Distribute d authentic ation for r andomly c ompr omise d networks 2 1. In tro duction The securit y of all public k ey cryptosystems depends on assumptions about the hardness of certain mathematical problems. These assumptions are unpro ven, making public k ey cryptograph y vulnerable to adv ances in cryptanalysis. In 1994, Peter Shor made such an adv ance by developing an efficien t algorithm for prime factorization and discrete logarithms [1]. Shor’s algorithm breaks the most common public k ey cryptosystems but requires a mo derately p o w erful quan tum computer, whic h fortunately do es not y et exist. Giv en the importance of public key cryptograph y to the internet and electronic commerce, it is desirable that a practical information-theoretic secure replacement b e dev elop ed and implemen ted w ell b efore public key cryptosystems b ecome vulnerable to quan tum computers or other attac ks [2, 3]. Quan tum key distribution (QKD), first developed b y Bennett and Brassard [4], pro vides a partial solution when coupled with one-time pad (OTP) encryption. QKD relies on the uncertain ty principle of quan tum mechanics to provide information-theoretic security against ea v esdropping, but unfortunately QKD requires authenticated classical c hannels to prev en t man- in-the-middle (MITM) attacks. Information-theoretic secure proto cols exist for the authen tication of classical c hannels [5, 6, 7], but such proto cols require a shared secret key; this requiremen t is difficult for mutual strangers to satisfy . W e refer to the requiremen t of authenticated channels as the str anger authentic ation pr oblem ; QKD m ust o v ercome this problem to b ecome a feasible, secure alternative to to da y’s cryptographically-secure public key systems. W e prop ose a solution to the stranger authentication problem by enco ding an authen tication key in to multiple shares [8, 9]. These shares are transmitted via multiple paths through a QKD netw ork in which some no des already share secret k eys. Our approac h preven ts MITM attacks with high probabilit y , even if the attac k er controls a large, randomly-selected subset of all the no des. As authenticated QKD in com bination with OTP pro vides information-theoretic security [10], we describe the lev el of securit y of our protocol as pr ob abilistic information-the or etic . By this, w e mean that the securit y of our proto col is sto c hastic; with v ery high probabilit y , the proto col pro vides information- theoretic securit y and with some v ery small probabilit y δ , it fails in suc h a wa y as to allow a sufficiently p o werful adv ersary to p erform undetected MITM attacks. The securit y parameter δ can b e made arbitrarily small by mo dest increases in resource usage. 2. Adv ersary and Netw ork Mo del It is conv enient to mo del net works with prop erties similar to those describ ed ab ov e b y using undirected graphs, where each vertex represen ts a no de or party participating in the netw ork and each edge represents an authenticated public c hannel. Suc h a c hannel could be pro vided b y using a shared secret k ey for authen tication, or b y an y other means pro viding information-theoretic securit y . W e also assume that all parties in the net work Distribute d authentic ation for r andomly c ompr omise d networks 3 are connected to all other parties b y unauthen ticated c hannels that allo w both classical and quantum information. This last p oint can be restated as the assumption that the netw ork of (unauthen ticated) quan tum c hannels is the complete graph. In the case of a geographically large QKD net w ork using presen t-day tec hnology , distance limitations of p oin t-to-p oin t QKD links would make this assumption c hallenging to satisfy , although proto cols ha ve b een prop osed to address this problem under certain circumstances[11, 12]. In the long term, we b elieve quan tum rep eaters [13] will o vercome QKD’s distance limitations. 2.1. A dversarial c ap abilities W e consider an adversary , which w e will call the sne aky sup er c omputer [11]: (i) The adv ersary is computationally un b ounded. (ii) The adversary can listen to, intercept, and alter an y message on an y public c hannel. (iii) The adversary can compromise a randomly-selected subset of the no des in the net work. Compromised no des are assumed to b e under the complete control of the adversary . The total fraction of compromised no des is limited to (1 − t ) or less. This adv ersary w ould b e at least as p o w erful as one with a quantum computer. It can successfully p erform MITM attac ks against public k ey cryptosystems (using the first capability) and against unauthen ticated QKD (using the second capabilit y) but not against a QKD link b et ween t w o uncompromised no des that share a secret k ey for authen tication (since quan tum mechanics allo ws the ea v esdropping to b e detected) [10]. The adv ersary can alwa ys p erform denial-of-service (DOS) attacks b y simply destroying all transmitted information; since DOS attac ks cannot b e prev ented in this adversarial scenario, we concern ourselv es only with securit y against MITM attac ks and do not consider robustness against DOS attacks further. The third capability in this adv ersarial mo del, namely the adversary’s con trol of a random subset of no des, sim ulates a netw ork in which exploitable vulnerabilities are presen t on some no des but not others. As a first appro ximation for a real-w orld net work, w e assume that vulnerable no des are randomly distributed throughout the netw ork. Others hav e considered adversarial mo dels in whic h the adversary cannot compromise no des [14, 15], or can deterministically compromise a small num b er of no des [12]. 2.2. The Network F or the stranger authentication problem, let us represent the netw ork as a graph G , with V ( G ) b eing the set of vertices (no des participating in the netw ork) and E ( G ) b eing the set of edges (secure authenticated c hannels, e.g. QKD links b et w een parties who share secret k eys for authentication). W e denote N = | V ( G ) | as the num b er of Distribute d authentic ation for r andomly c ompr omise d networks 4 v ertices (no des). The set of compromised no des V d is assumed to b e controlled by the adv ersary: | V d | ≤ N (1 − t ). In Section 3, we describe a proto col that allows an arbitrary uncompromised Alice and Bob ( A, B ∈ V ( G ) \ V d ) who do not initially share a direct link (i.e., ( A, B ) / ∈ E ( G )) to communicate with information-theoretic security with very high probabilit y . Sp ecifically , w e sho w that Alice and Bob can generate a shared secret k ey via secret sharing with shares transmitted via m ultiple paths through the graph. Moreo ver Ev e’s probabilit y of learning the secret shared k ey is smaller than δ , whic h Alice and Bob can mak e arbitrarily small. Once Alice and Bob share a secret key , they use it to authenticate a QKD link with eac h other. In other words, w e assume that Alice and Bob can easily acquire an unauthenticated QKD link then use their shared secret key to authen ticate that link. With reference to the adversary’s third capabilit y , we can consider an alternate scenario in whic h the adv ersary is instead able to c ho ose a subset of no des to compromise. If the adv ersary can con trol at most n no des, then n + 1 no de-disjoint paths b etw een Alice and Bob are required to guarantee securit y [12]. 2.3. Other appr o aches W e could mo del existing public key-based netw orks using a similar conv en tion, where edges represent authen ticated (but not necessarily secure) channels used for initial distribution of public keys. Such graphs t ypically hav e a tree top ology , in which most parties are connected only to a single root certificate authorit y (CA), or small n um b er of ro ot certificate authorities. Before participating in a public k ey netw ork, users typically obtain a copy of a certificate (which con tains the CA’s public k ey) from a few certificate authorities. This certificate is then used to v erify the authenticit y of digitally-signed public keys presen ted by other parties, thereby th warting MITM attacks. The pro cess of obtaining the CA’s certificate is often hidden from the user b ecause the certificate is usually bundled with their web bro wser or op erating system. Nonetheless, obtaining an authen tic ro ot CA certificate is a crucial part of the user’s securit y pro cess, as a compromised CA certificate would allow an attac ker to subv ert all future communication p erformed by that user. W e are now able to mak e a few observ ations ab out the existing public key infrastructure. First of all, it relies critically on the honesty and reliabilit y of a small n umber of ro ot CAs. While the ro ot CAs hav e so far pro ved to b e honest, they do o ccasionally make mistak es. Second, public k ey net works of N parties require only O ( N ) authen ticated c hannels to p erform the initial distribution of ro ot CA certificates. Third, the compromise of a single authen ticated channel can result in compromise of all future communication inv olving a particular single user, but the rest of the parties are largely protected. Finally , as is mentioned earlier, public k ey-based systems are vulnerable to our “sneaky sup ercomputer” adv ersary (e.g., an attac k er with a quantum computer) and the consequences of a successful attac k against an y of the ro ot CAs Distribute d authentic ation for r andomly c ompr omise d networks 5 w ould b e severe. T o solv e the stranger authen tication problem, a na ¨ ıv e approac h is represen ted b y a complete graph wherein ev ery v ertex is connected to ev ery other vertex. This approac h has the drawbac k that eac h part y would hav e to hav e a unique secret key shared with eac h other party , implying O ( N 2 ) secret keys in total. Alternativ ely , we could seek to duplicate the tree top ology of public k ey net works and hav e a few cen tral trusted parties to which all others are connected [16]. This has most of the drawbac ks listed ab ov e for public k ey net w orks, as w ell as the additional requirement that the cen tral trusted parties b e actively inv olv ed in ev ery communication (rather than one-time signing of public keys). Clearly , b oth of these na ¨ ıv e approac hes suffer from serious limitations that mak e them impractical for large-scale net w orks. In the subsequen t section, we presen t efficien t proto cols for solving these problems. 3. The Stranger Authen tication Proto col In this section, we describ e the stranger authen tication proto col in the con text of a uniform random graph. W e analyze its securit y and efficiency in the context of this net work top ology , and in Section 3.3, we introduce the p o wer-la w top ology , whic h w e study via numerical sim ulations. Consider a uniform random graph G with N vertices, in which the | E ( G ) | edges are random, in the sense that eac h p ossible edge e ∈ V 2 ( G ) = V ( G ) × V ( G ) is equally lik ely to be a mem b er of the set of edges, E ( G ). F urthermore, we assume that the set of compromised no des V d is a randomly-chosen subset of the total set of vertices, V ( G ). T ak e some arbitrary uncompromised Alice and Bob in G : if Alice and Bob are acquain tances and share a secret k ey (i.e., ( A, B ) ∈ E ( G )), then they can communicate securely using QKD to generate a large k ey for use as a OTP , using their shared secret k ey to authen ticate their QKD exc hange. W e are concerned with the case in whic h Alice and Bob are m utual strangers (i.e., ( A, B ) / ∈ E ( G )). In order for Alice to comm unicate securely with Bob, she first needs to establish a small shared secret key with him to prev ent MITM attac ks. T o obtain a shared secret k ey , Alice and Bob use the following pro cedure: (i) Alice generates a random string of length l : s ∈ { 0 , 1 } l . l is c hosen as described in Fig. 1. (ii) Alice selects all cycle-free paths b etw een her and Bob (w e assume Alice and Bob ha ve a complete and accurate routing table for the graph). Define n to b e the n umber of such paths. (iii) Alice employs a secret sharing scheme [8, 9] to enco de s in to n shares, such that all n shares are required to reconstruct s . (iv) Alice sends Bob one share via eac h cycle-free path. (v) Bob receiv es the shares and combines them to obtain s 0 . Distribute d authentic ation for r andomly c ompr omise d networks 6 ( r , H ( s 3 )) ⊕ s 1 H ( r ) ⊕ s ! 2 Alice Bob Figure 1. Alice and Bob verify that their resp ectiv e secret k eys, s = ( s 1 , s 2 , s 3 ) and s 0 = ( s 0 1 , s 0 2 , s 0 3 ), are in fact the same through the exchange sho wn ab ov e. Alice generates a random n umber r , concatenates it with the hash H ( s 3 ) of s 3 , X ORs this with s 1 and sends the result to Bob. Bob decodes with s 0 1 , verifies that H ( s 3 ) = H ( s 0 3 ), then sends back to Alice the result of bit-wise XORing the hash of r , H ( r ), with s 0 2 . Finally , Alice deco des with s 2 and chec ks to see that the v alue Bob has computed for H ( r ) is correct. Alice and Bob no w kno w s 3 = s 0 3 and can store s 3 for future use. The lengths of s 1 and s 2 scale as O ( − log δ ), where δ is the maximum allow able probability that an attack er who do es not know s can mo dify s 0 and escap e detection. The length of s 3 is therefore only sligh tly less than l (the length of s ). Alice and Bob thus choose l so that the length of s 3 will b e sufficient for their purp oses. Note that with this proto col, Ev e can fo ol Alice and Bob in to accepting s 6 = s 0 with 100 % probability if Ev e kno ws s and s 0 . (vi) Alice and Bob use the proto col describ ed in Fig. 1 to determine if s = s 0 . If so, they are left with a p ortion of s (identified as s 3 ), whic h is their shared secret key . If s 6 = s 0 , Alice and Bob discard s and s 0 and rep eat the proto col. The proto col as describ ed ab ov e is not efficien t, in that the n umber n of cycle-free paths grows rapidly as the size of the graph increases. The protocol can b e made efficien t without muc h loss in securit y , as we sho w later. There are some similarities b etw een our proto col and that describ ed by Dolev et al. [17] for net works of pro cessors with some fault y pro cessors, in that b oth proto cols use secret sharing as a means of pro tecting against no des that deviate from the protocol. The proto cols differ substan tially with resp ect to the adversarial mo dels they address. Dolev et al.’s proto col handles cases wherein the adversary controls a small num b er of no des of his or her choice. In con trast our proto col is designed for a net w ork in which the adversary controls a large fraction of all the no des but cannot choose whic h no des are compromised. 3.1. Se curity Pro vided there exists at least one path b etw een Alice and Bob with no fault y or uncompromised no des, Alice and Bob are authen ticated and acquire a shared secret Distribute d authentic ation for r andomly c ompr omise d networks 7 k ey . MITM attacks are prev ented because eac h no de in the path authenticates the no des b efore and after, thereb y pro viding a chain of authentication. In order for an attac k er (Ev e) to compromise the proto col, the attack er must learn s . As s is enco ded in to m ultiple shares, and all shares are required to reconstruct s , the attac ker m ust learn all the shares in order to learn s . Shares are secured in transmission b y OTP using keys generated b y authenticated QKD, so the only w ay for Eve to learn a share is if she con trols a no de that is part of the transmission path b et ween Alice and Bob for that share. Put another w ay , the proto col is secure unless all share transmission paths b etw een Alice and Bob contain at least one compromised no de. This question can be rephrased in graph-theoretic terms b y asking ho w large E ( G ) m ust b e such that the subgraph G 0 ⊆ G induced by V ( G ) \ V d is connected. As an example, Fig. 2 sho ws a random graph that remains connected even after tw o compromised parties are remo v ed. Recall that t ≡ 1 − | V d | | V ( G ) | is the fraction of uncompromised no des. Th us, b tN c no des and appro ximately t 2 | E ( G ) | edges will remain after the compromised no des are remov ed. Using a result obtained b y Erd˝ os and R´ enyi [18] for connectedness of uniform random graphs, we see that, for a random graph of b tN c v ertices and b t 2 | E ( G ) |c edges in the limit as tN → ∞ , the probabilit y that the graph is connected is p c = e − e − 2 c (1) with c = | E ( G ) | t N − 1 2 log tN . (2) Supp ose w e wish to estimate the num b er of edges, | E ( G ) | , required to limit the probabilit y of compromise to some = 1 − p c . Using the ab ov e result for 1 δ tN exp [ − t ( N − 1)] , w e obtain the follo wing relation: | E ( G ) | ' 1 2 N t log N t . (3) This estimate do es not apply in the case where N is finite and = 0, where it is clear the n umber of edges go es to O ( N 2 ) rather than infinity . It is w orth noting that Eq. (3) gives the appro ximate n um b er of edges required suc h that, with probability 1 − , al l A , B , in V ( G ) \ V d can comm unicate securely . This is a stronger result than if we had shown secure comm unication just for one particular choice of A and B . 3.2. Efficiency and Cost According to the protocol describ ed ab ov e, the n umber of shares n required to p erform the proto col b et ween t wo arbitrary parties (Alice and Bob) will gro w with the total Distribute d authentic ation for r andomly c ompr omise d networks 8 n umber of cycle-free paths b et ween them and th us m uc h faster than the total num b er of parties. This is not lik ely to b e a serious problem for small-to-medium net w orks as the strings b eing sen t need not be large (they are necessary only for the initial authen tication of a QKD proto col) and need only b e sent the first time a giv en pair of parties wish to comm unicate. Nonetheless, it will even tually b ecome a problem as the netw ork grows larger so we seek to reduce this cost by having Alice and Bob use only a subset of the p ossible paths. F ortunately , relatively few paths are required to guaran tee a high degree of security , and the n umber of paths required scales slowly with the size of the graph. W e can estimate the num b er of paths required to keep the probability of compromise δ constan t. (Note that the follo wing calculation is intended as an estimate rather than a rigorous deriv ation.) The probability of a single path of length ` b eing uncompromised is approximately t ` − 1 . Suppose w e ha ve a graph G with the num b er of edges | E ( G ) | c hosen according to Eq. (3), where ≤ δ . The diameter (maximal distance b et ween any pair of nodes) of suc h a graph [19] is d ' log N log h k i (4) with h k i = 2 | E ( G ) | / N (5) the av erage degree of a no de in G . Expression (4) can be understo o d by considering the n umber of nodes at distance d from some starting no de; since eac h no de has on a verage h k i neighbours, w e exp ect to find h k i d no des at this distance. If we wish to find the p shortest (not necessarily indep endent) paths from Alice to Bob, we can estimate the length of the longest of these paths as ` p = log( N p ) log h k i . W e can no w estimate the n umber p of indep enden t paths required to giv e a probabilit y δ that all paths are compromised: p = log δ log (1 − t ` p − 1 ) . (6) Note that the right-hand side of Eq. (6) contains ` p , which dep ends on p ; an iterative pro cess can easily b e used to find a solution for p . W e ha v e estimated the n umber of indep enden t paths (6) required to guarantee a certain degree of security; ho wev er, it will in general b e more practical to choose paths that are not completely indep endent of eac h other. This will result in some reduction of security , which can b e comp ensated for by using additional paths. Another issue is that path choice m ust not b e determined solely by a dishonest party; if path c hoice is left solely to Alice, and a malicious Ev e w an ts to imp ersonate Alice, Ev e can choose paths such that ev ery path contains a compromised no de. One solution is for Bob to initiate a second round of the proto col (using differen t paths) to confirm that he is Distribute d authentic ation for r andomly c ompr omise d networks 9 indeed communicating with Alice; the shared secret keys generated in the tw o rounds are then combined to pro duce a final key . W e use Monte Carlo simulations to test whether our estimate of path requiremen ts is reasonable and to compare the p erformance of uniform random graphs with that of p o w er-law graphs. The path-pic king algorithm used in this sim ulation is based upon Dijkstra’s algorithm [20] for solving the shortest path problem. Initially , all no des are giv en the same cost. The path of least cost (“shortest” path) b etw een Alice and Bob is c hosen, and the cost of all intermediate no des along the path are incremented. A new path of least cost is found, and the pro cess is rep eated un til the desired n um b er of paths are chosen. Duplicate paths are not allow ed. In a real-w orld application, a higher n um b er of paths used would likely be c hosen so as to pro vide a muc h lo wer risk of compromise (smaller δ ); parameter v alues used in this sim ulation are for illustrative purp oses. W e mak e no claims as to the optimality of the path-pic king algorithm used, but note that it giv es a nearly constan t degree of security (i.e., δ is nearly constant) with resource use consistent with the mo dest scaling with N predicted b y our estimates. Simulation details and results are given in the follo wing tw o subsections. One resource w e hav e not y et explicitly discussed is bandwidth used during execution of the proto col. If w e assume that the a v erage num b er of times a giv en user initiates the proto col (i.e., acts as Alice) is fixed, it is clear that this will scale with the num b er of users in volv ed in one instance of the protocol, whic h is given by the pro duct of the path length with the num b er of paths. Using the num b ers from Fig. 3 and T able 1 as an example, w e see that, if N = 32768 and t = 0 . 4, a t ypical user w ould ha ve to act as an intermediate no de ab out 300 times for every time he or she acted as a proto col initiator. As only short k eys ( ∼ 1 kb) are required for authen tication, and the proto col need only b e used the first time t wo m utual strangers wish to communicate, this do es not represent an unreasonable burden on users. Another cost b orne by users is the necessity of establishing ∼ h k i edges (shared secret keys) with other parties in order to join the netw ork and b e able to participate securely . F or security reasons, the k ey exc hanges required w ould ha ve to tak e place offline via some secure means. F ortunately , the num b er of “edges” required is small, scaling as O (log N ), so we b elieve this one-time cost will not be too onerous. New users could b e advised of a minimum connectivity requirement and required to p erform a certain n umber of secure offline k ey exc hanges b efore b eing allo wed to use the net work. 3.3. Network T op olo gies W e ha ve so far only considered a uniform random top ology when discussing the application of the proto col to a netw ork. How ever, in real-world net works, p o wer-la w graphs are common [19]. Here w e consider security in these ubiquitous, naturally- o ccurring netw ork top ologies. P ow er-law graphs are those for which the num b er of no des of degree k is Distribute d authentic ation for r andomly c ompr omise d networks 10 Figure 2. White vertices represent honest parties, whereas shaded v ertices represen t dishonest parties. Dashed edges are those that end on a dishonest part y . The subgraph induced b y the remov al of the shaded v ertices remains connected, so an y tw o honest parties can comm unicate securely using the proto col describ ed in Sec. 3. 512 2048 8192 32 768 N 20 25 30 35 40 X k \ H a L 512 2048 8192 32 768 N 10 20 30 40 50 p H b L Figure 3. P arameters used in generating graphs for all simulations, b oth for the uniform random and truncated pow er-law cases. The y ellow solid line, red long-dashed line, and blue short-dashed line represent v alues for t = 0 . 4, t = 0 . 6, and t = 0 . 8, resp ectiv ely . (a) shows the a v erage num b er of edges p er no de, h k i / 2, as a function of N , the total n um b er of no des, and (b) indicates the num b er of paths p used as a function of the n umber of no des, N . 10 20 30 40 50 k 1000 2000 3000 4000 n k Figure 4. A comparison of the degree distribution (num b er of no des n k with k edges) of the tw o graph types b eing considered with tw o sample graphs for which N = 16384, t = 0 . 8, and | E ( G ) | = 167821. The red dashed line shows the uniform random case while the solid blue line is the truncated pow er-law case. Distribute d authentic ation for r andomly c ompr omise d networks 11 prop ortional to k − γ , where γ is a p ositiv e constan t. When compared to a uniform random graph with the same num b er of no des and edges, p ow er-la w graphs hav e b een sho wn to b e more robust against random remo v al of no des [19]; sp ecifically , the size of the largest connected cluster decreases more slo wly and the av erage path length in this cluster remains smaller (conv ersely , p o wer-la w graphs are more vulnerable than uniform random graphs to targeted no de remo v al). As Alice and Bob must still b e connected within the subgraph induced by V ( G ) \ V d in order to comm unicate securely using our proto col, this feature of p ow er-la w graphs suggests they are more secure against our adv ersary . W e mo dify the p o wer-la w structure sligh tly by imp osing a minim um degree cut-off, k min ; in practice, suc h a cut-off could b e enforced b y requiring all no des to ha ve at least k min connections b efore allowing them to participate in the netw ork. The cut-off is necessary b ecause nodes with low degree are prone to proto col failure by compromise of all immediate neighbours (and, in a p ow er-la w graph, nodes of the lo west allow ed degree are the most common); such failures are suppressed in a truncated p ow er-la w graph. F or example, giv en a node with degree k , the probabilit y that all its neighbours are compromised (nc = neigh b ours compromised) is P nc ( k ) = (1 − t ) k . (7) Let us consider this particular proto col failure mo de, in whic h all of Alice’s immediate neigh b ours are compromised. W e denote the probability of such failure b y δ nc . W e then see that δ nc = P nc ( k Alice ) ≤ P nc ( k min ) = (1 − t ) k min , (8) where k Alice is Alice’s degree and k min is the minimum degree of any no de in the net work. It should b e noted that δ nc represen ts only a p ortion of the total probability that the proto col will fail, δ ; by necessity , δ ≥ δ nc . In the following section, we use Eq. (8) to estimate the minimum degree cut-off k min that should b e imp osed to constrain the probabilit y of such failures to less than some allow ed maximum δ nc . 4. Sim ulation results W e no w discuss the parameters and results of a sim ulation of the stranger authentication proto col. F or each set of parameters, 1000 trials were run, with a new graph and new random choice of (non-compromised and non-adjacent) Alice and Bob for each trial. The n um b er of paths was chosen according to Eq. (6) and the n umber of edges according to Eq. (3), with δ = 0 . 01 used as the target probability of compromise. The v ariation of these parameters with c hanges in t and N is sho wn in Fig. 3. This pro cedure w as follow ed for b oth uniform random and truncated p ow er-la w graphs, with the only difference b eing the t yp e of graph; this allows us to p erform a fair comparison of proto col p erformance on the tw o netw ork top ologies. Distribute d authentic ation for r andomly c ompr omise d networks 12 T o generate uniform random graphs, pairs of no des w ere randomly joined (with no duplicate edges allow ed) un til our quota of edges w as met. T o generate truncated p o w er-law graphs, suitable minimum degrees were c hosen according to Eq. (8) with δ nc = 0 . 002. The resulting v alues of k min w ere 4, 7 and 12 for t v alues of 0.8, 0.6 and 0.4, resp ectiv ely . W e c hose the largest p ossible γ suc h that the resulting n umber of edges in the graph, given b y k = N − 1 X k = k min N C k 1 − γ 2 (9) w as equal to or smaller than the goal num b er from Eq. (3). Degrees were assigned to eac h node such that the degree distribution of the graph w as as close to k − γ as p ossible. No des w ere then randomly joined until all nodes satisfied their assigned degree as closely as p ossible (note that no des were not allo wed to exceed their assigned degree, which o ccasionally prev ented a small num b er of no des from reaching their assigned degree). The result w as a truncated p ow er-la w graph with as many or sligh tly fewer edges than the corresp onding uniform random graph for each set of parameters. W e illustrate the difference b et ween the degree distribution of the truncated p ow er-law and uniform random top ologies, generated according to the metho ds describ ed ab o ve, in Fig. 4. Our sim ulation results are giv en in T able 1 and Fig. 5. T able 1 shows the logarithmic scaling of path length in N suggested by Eq. (4). This indicates that the cost of participating in the netw ork, as outlined in Subsection 3.2, scales reasonably (i.e., sub- exp onen tially). W e see from Fig. 5 that the probabilit y of compromise is appro ximately constan t in the uniformly random case; our numerical sim ulations matc h our predicted results in this regard. Probabilit y of compromise does slowly increase with decreasing t for b oth top ologies. This b ehaviour is inevitable, as δ necessarily go es to 1 as t go es to 0. W e further see that truncated p ow er-la w graphs consistently offered greater securit y than uniform random net works for the adv ersarial model describ ed in Section 2.1. This also confirms our exp ectations; truncated p o wer-la w graphs w ere sho wn to b e more robust against random remo v al of no des. In the alternate adversarial mo del in which the adversary is allo wed to c ho ose the compromised no des, w e expect p o wer-la w graphs to b e somewhat less robust, due to the relative importance of a small n umber of highly connected no des. 5. Conclusion W e hav e sho wn a practical metho d for solving the stranger authentication problem, whic h arises when one attempts to build a large-scale secure communication net work using QKD or cryptographic technology with similar prop erties. This metho d employs secret sharing to make use of m ultiple, partially-trusted paths through a net work. Whereas the reliance on the collective integrit y of man y parties may at first seem surprising, it is preferable to current public key cryptographic strategies of using a ro ot certificate authority who must alwa ys b e trusted: our sc heme a voids this single REFERENCES 13 p oin t of failure b y not requiring an y part y , not even an authorit y , to b e completely trusted. Through the choice of sufficiently man y edges (secure authenticated c hannels) and paths, one can make the p ossibility of compromise v anishingly small. Using b oth n umerical sim ulations and random graph theory , we hav e shown that our protocol—in conjunction with QKD—provides security at reasonable resource costs. Proto col p erformance is shown via n umerical sim ulations to b e b etter in truncated p o w er-law netw orks than in uniform random net works; since real comm unication and so cial net works tend to hav e a p ow er-la w structure, this b o des w ell for p erformance in the real w orld. Giv en that QKD systems are already commercially av ailable, our metho ds could b e implemented to da y . Ac knowledgmen ts W e wish to thank L. Salv ail, D. Stebila, and A. Ro y for v aluable discussions. TRB ac knowledges supp ort from a US Departmen t of Defense NDSEG F ello wship. KPH appreciates financial supp ort from the NSERC Undergraduate Studen t Research Aw ard program. BCS is a CIF AR Asso ciate and ac knowledges financial supp ort from iCORE and NSERC. References [1] Shor P W 1994 Pr o c. of 35th A nnual Symp osium on F oundations of Computer Scienc e 124–134 [2] Paterson K, Pip er F and Schac k R 2007 Quantum Communic ation and Se curity ed Zuk owski M, Kilin S and Kow alik J (IOS Press) pp 175–180 [3] Stebila D, Mosca M and L ¨ utk enhaus N 2009 [4] Bennett C H and Brassard G 1984 Pr o c. of IEEE International Confer enc e on Computers, Systems, and Signal Pr o c essing 175–179 URL http://www.research. ibm.com/people/b/bennetc/chbbib.htm [5] Carter J L and W egman M N 1979 J. of Computer and System Scienc es 18 143–154 [6] W egman M N and Carter J L 1981 J. of Computer and System Scienc es 22 265–279 [7] Stinson D R 1991 A dvanc es in Cryptolo gy — CR YPTO ’91 ( L e ctur e Notes in Computer Scienc e vol 576) pp 74–85 [8] Shamir A 1979 Comm. of the Asso ciation for Computing Machinery 22 612–613 [9] Blakley G R 1979 Pr o c. of the National Computer Confer enc e 48 313–317 [10] Renner R, Gisin N and Kraus B 2005 Phys. R ev. A 72 012332 [11] Beals T R and Sanders B C 2008 Int. Conf. Information The or etic Se curity ( L e ctur e Notes in Computer Scienc e vol 5155) ed Safavi-Naini R pp 29–39 [12] Salv ail L, Peev M, Diaman ti E, All ´ eaume R, L ¨ utk enhaus N and L¨ anger T 2009 REFERENCES 14 [13] Duan L M, Lukin M, Cirac J I and Zoller P 2001 Natur e 414 413–418 [14] Elliott C 2002 New Journal of Physics 4 46 [15] All´ eaume R, Bouda J, Branciard C, Debuisschert T, Dianati M, Gisin N, Go dfrey M, Grangier P , L¨ anger T, Lev errier A, L ¨ utk enhaus N, Painc hault P , Peev M, P opp e A, P ornin T, Rarity J, Renner R, Rib ordy G, Riguidel M, Salv ail L, Shields A, W einfurter H and Zeilinger A 2007 SECOQC white pap er on quantum k ey distribution and cryptography SECOQC-WP-v5 [16] Pasquin ucci A 2005 arXiv:cs/0506003 [17] Dolev D, Dw ork C, W aarts O and Y ung M 1993 J. of the Asso ciation for Computing Machinery 40 17–47 [18] Erd˝ os P and R´ enyi A 1959 Public ationes Mathematic ae 6 290–297 [19] Alb ert R and Barab´ asi A L 2002 R ev. Mo d. Phys. 74 47 [20] Cormen T H, Leiserson C E, Rivest R L and Stein C 2001 Intr o duction to algorithms (MIT Press and McGra w-Hill) REFERENCES 15 No des Uniform Random P ow er-Law t = 0 . 8 t = 0 . 6 t = 0 . 4 t = 0 . 8 t = 0 . 6 t = 0 . 4 128 3 3 3 4 4 3 256 4 4 3 4 4 4 512 4 4 4 4 4 4 1024 4 4 4 4 4 4 2048 4 4 4 4 4 4 4096 5 5 5 4 4 4 8192 5 5 5 4 4 4 16384 5 5 5 4 4 4 32768 5 5 5 4 4 5 T able 1. The length of the 99 th -p ercen tile longest path. æ æ æ æ æ æ æ æ æ à à à à à à à à à ì ì ì ì ì ì ì ì ì 512 2048 8192 32 768 N 0.01 0.02 0.03 ∆ H a L æ æ æ æ æ æ æ æ æ à à à à à à à à à ì ì ì ì ì ì ì ì ì 512 2048 8192 32 768 N 0.005 0.01 0.015 ∆ H b L Figure 5. The fraction ( δ ) of times all paths b etw een Alice and Bob were compromised, as a function of the num b er of no des in the graph, for simulations using (a) uniform random graphs and (b) truncated p ow er-law graphs. The yello w solid line, red long-dashed line, and blue short-dashed line represent v alues for t = 0 . 4, t = 0 . 6, and t = 0 . 8, resp ectively .
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment