Beacon-Assisted Spectrum Access with Cooperative Cognitive Transmitter and Receiver
Spectrum access is an important function of cognitive radios for detecting and utilizing spectrum holes without interfering with the legacy systems. In this paper we propose novel cooperative communication models and show how deploying such cooperati…
Authors: Ali Tajer, Xiaodong Wang
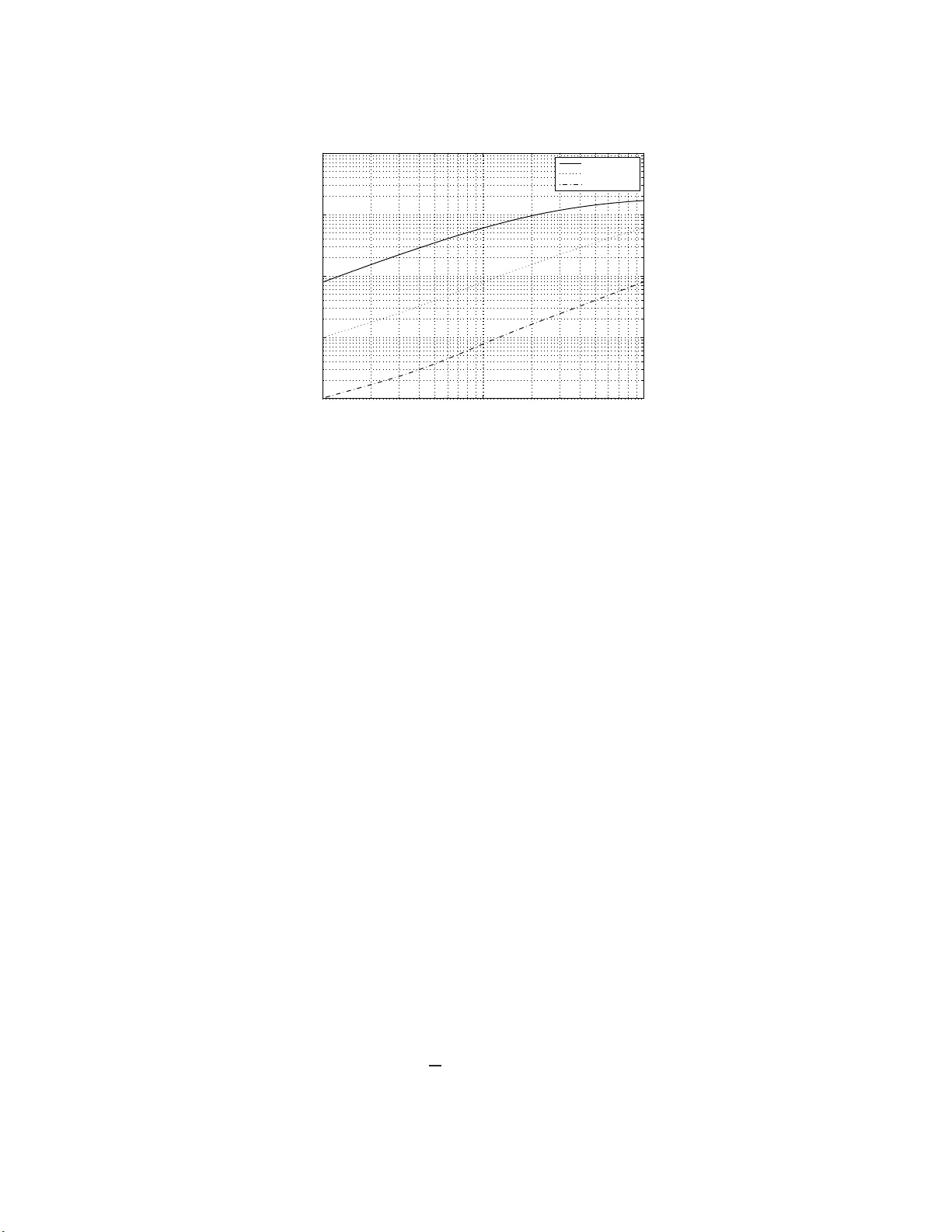
Beacon-Assisted Sp ectrum Access with Co op erative Cognitive T ransmitter and Receiv er Ali T a jer Xiao dong W ang ∗ Abstract Spec tr um access is an imp ortant f unction of cognitive radios for detecting and utilizing sp ectrum ho les without interfering w ith the le g acy s y stems. In this pap er we pr opose novel co opera tiv e communication m o dels and show ho w deploying suc h co oper ations betw een a pair of secondar y transmitter and r eceiv er assists them in iden tifying sp ectrum opp ortunities more reliably . These co opera tions are fac ilita ted by dynamic al ly and opp ortunistic al ly a ssigning one of the seco ndary users as a r ela y to assist the o ther one which results in more efficient sp ectrum hole detection. Also, w e in vestigate the impact of erroneous detection of sp ectrum ho le s and thereo f missing co mm unication oppo rtunities on the capacity of the secondar y channel. The capacity of the secondary users with interfer enc e-avoidi ng sp ectrum access is affected b y 1) how effectively the av ailabilit y of v acant s pectrum is se ns ed by the secondar y transmitter-r eceiv er pa ir, and 2) how corr elated are the p erceptions of the seco ndary transmitter- receiver pair ab out net work sp ectral a ctivit y . W e show that b oth factors are improv ed by us ing the pr opose d co oper a tiv e proto cols. One of the prop osed proto cols requires explicit information exchange in the net work. Such informatio n exchange in practice is prone to wireless channel er rors (i.e., is imper fect) and costs bandwidth los s. W e analyze the effects of such imp erfect information exchange on the capacity as well as the effect of bandwidth cost on the achiev able thro ug hput. The proto cols are also extended to multiuser secondary netw orks. Index T erms: Cognitiv e radio, sp ectrum acce ss, co op erativ e div ersit y , opp ortunistic comm u- nication, c h an n el capacit y . 1 In tro duction Cognitiv e radios ha ve b een introdu ced as a p otent ial solution for alleviating the scarcit y of fre- quency sp ectrum in ov erly crowded environmen ts [1–4]. According to the F ederal Comm un ica tion ∗ The authors are with th e Department of Electrical En gineeri ng, Columbia Universit y , New Y ork, NY 10027 (email: { ta jer, wangx } @ee.colum bia.edu). 1 Commission (F CC), a v ast p ortion of the frequ ency bands is used only sp oradically and fu rther- more, th e usage v aries geographically and temp orally . Suc h inefficien t utilization of sp ectrum, as w ell as the increasing demand for fr equency b ands by the existing and emerging wireless appli- cations, motiv ates opp ortun istic access to licensed bands by unlicensed (secondary) u sers. The notion of cognitiv e radios mak es it p ossible to accommo date self-configuring ad-ho c links w ithin currentl y established wireless comm unication in frastructures. F or accessing v acan t sp ectrum b ands assigned to licensed users, the secondary u s ers con tin uou s ly and activ ely m onito r the sp ectrum in order to efficiently mak e use of the sp ectrum h ole while a voi d ing interference with licensed users (in terference-a v oiding [5] or in terwe av e paradigm [6]) or ha vin g con trolled leve l of interference tem- p erature (in terference-con trolled [5] or u nderla y paradigm [6]). Related studies on sp ectrum access can b e broadly categorized as th ose pr oposing efficient metho ds for lo cating the holes in the sp ectrum [7–9] and those discussing ho w to optimally allo cate the a v ailable unused frequency bands to secondary users [10–13]. T h e w orks in the former catego ry aim at improving the delectabilit y of the unused p ortions of sp ectrum by using p h ysical la yer tec hniques, wh ile those in the latter one dev elop media access cont r ol (MA C) pr oto cols s ee kin g to m aximiz e secondary users’ net wo r k throughpu t. The c h annel access proto cols we prop ose in this pap er fall within the fi rst category mentio n ed ab o v e. These proto cols allo w the secondary transmitter and receiv er to co op erativ ely listen to th e p rimary user instead of h aving indep end en t observ ations. The gains yielded for the detection of unused sp ectrum are due to the dive rs it y gains in tro duced b y the co op erati on. The increase in the channel capacit y is also partly due to th e same dive r s it y gain but is mostly sh aped by redu cing the uncertaint y at the secondary tran s mitte r and receiv er no des ab out eac h other’s observ ation of the s p ectral activit y , whic h is a by-prod uct of the co op eratio n b et w een them. As discussed in [14], discrepancy in s p ectral activit y a wareness at the secondary transmitter and receiv er, which is due to their sp at ial separation and/or imp erfect c hann el sensing, incurs a loss in c h annel capacit y . The u n derlying idea of the co operation mo dels develo p ed is to hav e a one-time broadcast of a b e ac on message and a one-time r ela ying of this message b y one of the secondary users such that b oth enjoy a second order diversit y gain in detecting the b eacon m essag e. This b eacon message is a co dew ord within the co deb ook of the primary u ser, reserv ed sp ecifically for the p urp ose of informing the secondary users of the v acant channel. Besides seeking sp ectrum opp ortu n ities and utilizing them, another ma jor fu nctio n of secondary users is to detect the retur n of p rimary users and agilely v acate the channel. Th e idea of deploying co operativ e d iv ers ity s chemes and their m er its in detecting the retur n of the prim ary users h as also 2 b een in ve stigated as an ind epend en t pr oblem in [15–17]. 2 System Descriptions W e consider a primary transmitter T p and a pair of secondary transm itter T t and receiv er T r users. The secondary u sers con tin uously monitor the c hannel u sed b y the p rimary user, seeking an opp ortunit y to take it ov er wh en it is unused. W e assume that all channels b et w een the primary user and the secondary u sers and those b etw een the secondary users are quasi-static wireless flat fading c hannels which remain unchanged dur ing the transmission of a b loc k of symb ols and c hange to indep endent states afterwa rd s. W e denote the channels b et ween th e primary user an d the secondary transmitter and r ece iver b y γ p,t and γ p,r resp ectiv ely . The channel b et w een the secondary no des are denoted by γ t,r and γ r,t . The physical c h annel b et w een no des i ∈ { p, t, r } and j ∈ { t, r } has an instantaneo u s realizatio n γ i,j = p λ i,j · h i,j , (1) where fading co efficien ts h i,j are assumed to b e ind epend en t, circularly symmetric complex Gaussian random v ariables C N (0 , 1). Th e term λ i,j accoun ts f or p ath loss and shado win g and is give n by λ i,j = S i,j d − ζ i,j , where S i,j represent s the log-normal shado win g effect and d i,j is the physica l distance b et w een no des i, j and ζ > 0 is th e p ath loss exp onent. In [7] it is shown that compared with energy detection metho ds, the d etection of v acan t sp ectrum can b e significan tly impr o ved th r ough transmitting pilot signals by the primary user and d eplo ying coheren t detection at the secondary users. Motiv ated by this fact, in this pap er w e assu me that whenev er a c hann el is released by the pr imary user, it is announ ced to the secondary users by ha ving the p rimary user br oa d ca st a b eacon m essag e. It is notewo r thy that as ev ent u all y w e are ev aluating the netw ork throughpu t, it is v alid to assume that the secondary users are alw a ys willing to access the c hannel and are con tinuously monitoring the c hann el for the b eacon message by the primary user. W e consider N consecutiv e c hannel uses for the transmission of the b eacon message. The b eacon message, sent by th e primary u s er, is denoted by x b = [ x b [1] , . . . , x b [ N ]] T and the receiv ed signals by the s econdary trans m itt er and receiv er are denoted by y t = [ y t [1] , . . . , y t [ N ]] T and y r = [ y r [1] , . . . , y r [ N ]] T , resp ectiv ely . F or the direct transmiss ion from the primary user to the secondary users, as th e baseline in our comparisons, we hav e y t [ n ] = γ p,t x b [ n ] + z t [ n ] , (2) and y r [ n ] = γ p,r x b [ n ] + z r [ n ] , n = 1 . . . , N , (3) 3 where z t and z r denote the zero mean additiv e w h ite Gaussian noise terms with v ariance N 0 . Also w e assume th at all trans m itt ed signals ha ve the same av erage p ow er, i.e., E [ | x b | 2 ] ≤ P p , and denote ρ △ = P p N 0 as the S NR without fading, pathloss and shado win g. Therefore, the instan taneous S NR is giv en by SNR i,j = ρλ i,j · | h i,j | 2 . (4) Throughout the pap er w e say that t wo fu nctions f ( x ) and g ( x ) are exp onential ly equal, denoted b y f ( x ) . = g ( x ) if lim x →∞ log f ( x ) log g ( x ) = 1 . The ordering op erators · ≤ and · ≥ are defin ed accordingly . 3 Co op eration Proto cols W e assum e that the secondary users are inf ormed of the v acancy of the c hann els by having the primary us er br oa d cast a b eacon message a priori known to the secondary us ers. The b eacon message is a reserved codeword in the co deb ook of th e primary user and is dedicated to ann ouncing the av ailabilit y of the channel for b eing accessed by the secondary u sers. W e in tend to devise a co operation m odel suc h th at b oth secondary trans m itt er and receiv er deco de the b eacon message with a second order d iv er s it y gain. Co op erati ve dive rs ity has b een studied and d ev elop ed extensivel y as a means for making com- m un ica tion o ver wireless links more reliable [18–21]. In co op erativ e communicatio n a p oint-to- p oint li n k is assisted by an in termediate no de (rela y) aiming at providing the in tended receiv er b y additional div ersit y gains while the o ve rall resources (frequency band width and p o wer) remain unc h an ged compared to the non-co op erativ e sc hemes. In this pap er w e first dev elop a nov el co op erat ion mo del appropriate for multic ast transmissions and then sho w how to adopt it f or building co op erativ e sp ectrum access schemes. Un lik e the con- v ent ional three no de co op erativ e mo dels wher e the ob jectiv e is to ac hieve a second-order diversit y gain at only the int end ed receiv er, we consider broadcasting the same message to t wo r ece ivers suc h that b oth enjo y second-order div ersit y gains and yet use the same amoun t of resources. T his co operation sc heme is a com bination of opp ortunistic rela y assignment and b it forwarding. While this proto col, lik e most other existing co op eration mo dels, guarantees p erformance enhancement in only h igh enough SNR regimes, w e f u rther m o dify it p r otocol suc h that it exerts co op eration only if it is b enefi cia l. This mo dified proto col, compared to the non-co op erativ e transmission, w ill ensure p erformance impro vemen t o ver all SNR regimes and all c hannel realiza tions. 4 3.1 Co op erativ e Sp ectrum A ccess (CSA) Assume that the b eacon message consists of K information bits and N − K parit y bits giving rise to the cod ing rate K N and requires N c han n el us es in a non-co op erativ e transm iss io n . W e utilize the regenerativ e sc heme of [21] and d ivide the b eacon message into to smaller segmen ts of lengths K ≤ N 1 < N and N 2 △ = N − N 1 and define the level of c o op er ation as α △ = N 1 N . The transmission of the b eacon message is accomplished in t wo steps: 1. Th e primary u ser uses only the first N 1 c hannel u ses (as opp osed to non-co operative that uses all the N channel uses) to broadcast a reserv ed co deb ook in its co deb ook ( x ′ b ) w hen it is willing to release the c hann el. This reserved co dewo rd is a w eak er co dew ord compared to the original b eacon. Mean while, the secondary transmitter and receiv er try to deco de the fi rst segmen t. 2. Durin g the remaining ( N − N 1 ) c hann el u ses, any secondary user who has su ccessfu lly d ecoded the firs t segmen t, immediately constructs N 2 additional extra bits and forwards them to the other secondary user. If b oth happ en to d ecode successfully , b oth will tr y to transm it in the second phase and their transmissions collide. Su c h collision is insignifican t and incurs no loss as it only happ ens when b oth secondary u sers ha v e already su cc essfu lly deco ded the b eacon. If neither of the secondary users is successful in deco ding th e firs t segmen t of the b eacon message, th er e will b e no transmission in th e second p hase and hence (1 − α ) p ortion of the time slot is w asted. Despite such p ossible wa ste, as analyses rev eal, by co op eration a b etter o v erall p erformance can b e ac hiev ed. As sho wn in Section 4, th e com bin at ion of opp ortu nistic rela y assignment and b it forwarding us es essen tially the same amount of resources (p o w er and bandwidth ) as in the n on-coop erativ e approac h , and yet pr o vides a second-order diversit y gain for b oth secondary u sers, whereas if one of the no des is selected a priori and in dep enden tly of the c hann el cond itions, this no de w ill ac h iev e only a fi rst-order diversit y gain. It is also notew orth y th at the C SA proto col can b e extended b ey ond th e scop e of cognitiv e net wo r k s and can b e adop ted in any application in wh ic h a message is inte n ded to b e multic ast to sev eral no des. 3.2 Opp ortunistic C oop erativ e Sp ectrum Ac cess (OCSA) A ttaining a higher diversit y ord er, whic h is a h igh SNR measure, regime do es not necessarily guaran tee p erformance enhancement in th e lo w or eve n mo derate S NR regimes. F or instance, wh en either the source-rela y or the rela y-d estination link is very w eak, coop eration m a y not b e b eneficial. 5 When exc hanging certain information b et ween the primary and the s econdary users is p ossible, we can o v ercome this problem b y mo difying the CS A proto col su c h that co op eration is deploy ed only when deemed b eneficial. Therefore, the proto col b ecomes op p ortu n istic in th e sense it dynamically decides whether to allo w co op eration or not. The cost of this im p ro v emen t is that the primary and the secondary users need to acquire th e qualit y of their outgoing channels. Acquiring such c h an n el gains is not necessarily feasible in all net works, bu t those capable of it can b enefit from deploying the OC S A p rotocol instead of the CSA p rotocol. The discussions on how the r equired information exc hange should tak e place are provided in Section 6.1. T he co op eration is carried out in t wo steps: 1. Th e first step is similar to that of the CSA p rotocol. 2. All the three no des (the primary us er and the pair of s econdary transmitter-receiv er) step in a comp etition for broadcasting additional party bits for x ′ b during the next N 2 c hannel uses. The comp etition is carried out as follo ws. W e first assign the metrics t p △ = | γ p,t | 2 + | γ p,r | 2 , t t △ = | γ p,t | 2 + | γ t,r | 2 and t r △ = | γ p,r | 2 + | γ r,t | 2 to the primary u ser, the secondary tran s mitte r and the secondary r ece iver, resp ectiv ely . Th en the N 2 c hannel uses is allo cate d to (a) the s econdary tr ansmitter if it successfully deco des x ′ b and t t > max { t p , t r } ; (b) the s econdary r ece iver if it su cc essfu lly d ecodes x ′ b and t r > max { t p , t t } ; (c) to the p rimary transmitter if either t p > max { t t , t r } or b oth secondary users fail to deco de x ′ b . As sho wn in the next sections, including th e primary transmitter in the comp etition has the ad- v anta ge of guaran teeing that co oper ation is deplo yed only when it is h elpful. A simple tec hniqu e for iden tifying the winn er in the s ec ond p hase in a distributed wa y (w ith ou t ha ving a cen tral controll er) is to equip eac h primary and secondary user with a bac k off timer, with its initial v alue set inv ersely prop ortional to its corresp ond ing metric t . Therefore the timer of the user with the largest m et r ic t , go es off so oner and will start r ela ying. The id ea of enco ding the bac k off timer by channel gain has also b een used in [22–24]. In multiuser pr imary n et works, the central authority of the net work resp onsib le for of s pectrum co ordinations should b e in c harge of transmitting th e b eacon message. The reason is that individual users are not fully a ware of the net work s pectral activit y and if they act indep endentl y there exists the p ossibilit y that some user mistak enly annou n ces that a sp ectrum is v acan t while s ome other primary user is u tiliz ing it. Such strategy will also av oid ha ving multiple pr imary users transmit b eacon messages concurrent ly , in whic h case these messages collide and are lost. 6 4 Div ersit y A nalysis In th is section w e c haracterize the p erformance of the prop osed p rotocols in terms of the probability of erroneous detection of the b eacon message, whic h we d enote by P ρ ( e ), at th e s ignal-to-noise ratio ρ . The achiev able div ersity gain w hic h measures ho w r apidly the error probability d ec ays with increasing SNR is give n by div ersity order = − lim ρ →∞ log P ρ ( e ) log ρ . 4.1 Non-Co oper ativ e Sc heme As a b asel in e for p erform ance comparisons, we first consider the direct transmission (non-co op erativ e) b y the primary user ov er the c h annels giv en by (2) and (3). W e denote th e even ts that the secondary transmitter and receiv er do not deco de the b eacon message successfully by e t and e r , resp ectiv ely . F or a co ded transm ission w ith coherent d etection, th e pairwise error probability (PEP) th at th e secondary transmitter err oneously d ete cts the b eacon co dewo rd c in fa vo r of the co dew ord ˆ c for the c han n el realization γ p,t is giv en b y [25, (12. 13)] P ρ ( e t | γ p,t ) △ = Pr( c → ˆ c | γ p,t ) = Q q 2 dρ | γ p,t | 2 , (5) where d is the Hamming distance b et w een c and ˆ c . Thr oughout th e diversit y ord er analyses, w e will frequently use the follo w ing t wo resu lts. Remark 1 F or a r e al value a > 0 and the r andom variable u > 0 with pr ob ability density function f U ( u ) we have E u [ Q ( √ au )] = Z ∞ 0 Z ∞ √ au 1 √ 2 π e − v 2 / 2 dv f U ( u ) du = Z ∞ 0 Pr u ≤ v 2 a 1 √ 2 π e − v 2 / 2 dv . (6) Lemma 1 F or inte ger M > 0 and r e al k i > 0 , Z ∞ 0 M Y i =1 1 − e − k i v 2 /ρ 1 √ 2 π e − v 2 / 2 dv . = ρ − M . (7) Pr o of: See App endix A. As a result, f rom (5), (6), and (7) w e can sho w that f or non-co op erativ e transmission we h a ve P NC ρ ( e t ) = E γ p,t Q q 2 dρ | γ p,t | 2 = ρ − 1 , and P NC ρ ( e r ) = ρ − 1 . 7 4.2 CSA Prot ocol The trans m issions are accomplished in N = N 1 + N 2 consecutiv e c hann el uses, where N 1 uses is for the d irect transmission, and N 2 uses for the co operation phase. W e den ote d 1 and d 2 as the hamming distances of the co dew ords sent in the first and second phase and w e hav e d 1 + d 2 = d . In the case only one no de is successful in the first phase, w e denote it by T R ∈ { T t , T r } and also define T ¯ R △ = { T t , T r }\ T R . Ther efore, we get P C ρ ( e ¯ R | γ p, ¯ R , γ R , ¯ R ) = Q q 2 d 1 ρ | γ p, ¯ R | 2 + 2 d 2 ρ | γ R , ¯ R | 2 , (8) and for the case that there is no rela ying we hav e P C ρ ( e t | γ p,t ) = Q q 2 d 1 ρ | γ p,t | 2 , (9) and P C ρ ( e r | γ p,r ) = Q q 2 d 1 ρ | γ p,r | 2 . (10) Theorem 1 F or suffici e ntly lar ge SNR values, we have P C ρ ( e t ) . = P C ρ ( e r ) . = 1 ρ 2 , P C ρ ( e t ) < P NC ρ ( e t ) , and P C ρ ( e r ) < P NC ρ ( e r ) . Pr o of: W e denote the su cc ess and failure of the secondary tran s mitte r in th e first phase by T t : S and T t : F , r espectiv ely . W e also define T r : S and T r : F similarly . By using (8)-(10) and b y expansion ov er all differen t com binations of th e statuses of the secondary u sers, for the secondary transmitter we get P C ρ ( e t ) = P C ρ ( e t | T t : S , T r : S ) | {z } =0 P ρ ( T t : S , T r : S ) (11) + P C ρ ( e t | T t : S , T r : F ) | {z } =0 P ρ ( T t : S , T r : F ) + P C ρ ( e t | T t : F , T r : S ) P ρ ( T t : F , T r : S ) + P C ρ ( e t | T t : F , T r : F ) | {z } =1 P ρ ( T t : F , T r : F ) = Q q 2 d 1 ρ | γ p,t | 2 + 2 d 2 ρ | γ r,t | 2 × Q q 2 d 1 ρ | γ p,t | 2 × 1 − Q q 2 d 1 ρ | γ p,r | 2 + Q q 2 d 1 ρ | γ p,t | 2 × Q q 2 d 1 ρ | γ p,r | 2 (12) 8 = Z ∞ 0 P d 1 | γ p,t | 2 + d 2 | γ r,t | 2 ≤ v 2 2 ρ | {z } ≤ P d 1 | γ p,t | 2 ≤ v 2 2 ρ P d 1 | γ p,r | 2 ≤ v 2 2 ρ e − v 2 / 2 √ 2 π dv × Z ∞ 0 P d 1 | γ p,t | 2 ≤ v 2 2 ρ e − v 2 / 2 √ 2 π dv × " 1 − Z ∞ 0 P d 1 | γ p,r | 2 ≤ v 2 2 ρ e − v 2 / 2 √ 2 π dv # + Z ∞ 0 P d 1 | γ p,t | 2 ≤ v 2 2 ρ e − v 2 / 2 √ 2 π dv × Z ∞ 0 P d 1 | γ p,r | 2 ≤ v 2 2 ρ e − v 2 / 2 √ 2 π dv (13) ≤ Z ∞ 0 1 − e − v 2 2 d 1 ρλ p,t 1 − e − v 2 2 d 1 ρλ p,r e − v 2 / 2 √ 2 π dv | {z } . = 1 ρ 2 (from Lemma 1 and Remark 1) × Z ∞ 0 1 − e − v 2 2 d 1 ρλ p,t e − v 2 / 2 √ 2 π dv | {z } . = 1 ρ (from Lemma 1 and Remark 1) + Z ∞ 0 1 − e − v 2 2 d 1 ρλ p,t e − v 2 / 2 √ 2 π dv | {z } . = 1 ρ (from Lemma 1 and Remark 1) × Z ∞ 0 1 − e − v 2 2 d 1 ρλ p,r e − v 2 / 2 √ 2 π dv | {z } . = 1 ρ (from Lemma 1 and Remark 1) . = 1 ρ 2 + 1 ρ 3 . = 1 ρ 2 , where the tran s itio n from (12) to (13) follo ws from Remark 1. No w, by comparing to the non- co operativ e case, where w e ha ve P NC ρ ( e t ) . = 1 ρ , w e conclude that for su fficien tly large SNR , P C ρ ( e t ) < P NC ρ ( e t ). The same line of argumen t holds for the secondary receiv er. The CS A pr otocol ensu res that for su fficien tly high SNR v alues, the p robabilit y of detecting unused sp ectrum holes is b o osted. Ho wev er, the p erform ance in the low S NR regimes, d epen d s on the instant aneous channel conditions and it migh t happ en that non-co op erativ e sp ectrum access outp erforms th e co op erativ e scheme. 4.3 OCSA Proto col Lik e in the CSA p rotocol, the first N 1 c hannel uses are allocated for direct transmission from the primary user to the secondary u sers. Durin g the remaining time, dep ending on the instan taneous 9 c hannel conditions, the primary user might transm it the additional parit y bits itself or one of the secondary u sers migh t take o ver such transmission. W e denote the transm itting user in the second phase by T R ∈ { T p , T t , T r } . Therefore, the tr ansmission in the second phase is giv en by y t [ n ] = γ R ,t x R [ n ] + z t [ n ] if T R 6 = T t 0 if T R = T t , and y r [ n ] = γ R ,r x R [ n ] + z r [ n ] if T R 6 = T r 0 if T R = T r . As sp ecified by the pr otocol, if neither of the s ec ond ary users deco des the b eacon message success- fully , th e pr imary user will transmit the additional p arit y b its itself. In this case, transm iss io n of the b eacon message is similar to (2)-(3) for the entire channel uses. Theorem 2 F or al l values of SNR , channel r e alizations and level of c o op er ation, we have P OC ρ ( e t ) < P NC ρ ( e t ) , P OC ρ ( e r ) < P NC ρ ( e r ) , and P OC ρ ( e t ) . = P ONC ρ ( e r ) . = 1 ρ 2 . Pr o of: The probability of missing the b eacon message by the s ec ond ary transmitter is P OC ρ ( e t ) = X i ∈{ p,t,r } P OC ρ ( e t | T R = T i ) P OC ρ ( T R = T i ) . (14) Note th at P C ρ ( e t | T R = T t ) = 0. Also w hen T R = T r , according to the proto col we should hav e t r > t p , which pr o vides that | γ r,t | > | γ p,t | . Therefore, from (14) we get P OC ρ ( e t ) = E γ p,t Q q 2 d 1 ρ | γ p,t | 2 + 2 d 2 ρ | γ p,t | 2 P OC ρ ( T R = T p ) + E γ p,t ,γ r,t Q q 2 d 1 ρ | γ p,t | 2 + 2 d 2 ρ | γ r,t | 2 × P OC ρ ( T R = T r ) < E γ p,t Q q 2 dρ | γ p,t | 2 × [ P OC ρ ( T R = T p ) + P OC ρ ( T R = T r )] = P NC ρ ( e t ) . (15) d 1 and d 2 are the hamming d istance s of the co dewo rd s sen t in the first and second phase and w e ha ve d 1 + d 2 = d . By f ollo win g the same line of argument we can accordingly show th at P OC ρ ( e r ) < P NC ρ ( e r ). In order to assess the dive r s it y gain note that P OC ρ ( e t ) = P OC ρ ( e t | T t : F ) P ( T t : F ) 10 0 5 10 15 20 25 10 −6 10 −5 10 −4 10 −3 10 −2 10 −1 10 0 SNR (dB) Beacon Miss−Detection Probability Non−Cooperative − T t Non−Cooperative − T r CSA − T t CSA − T r OCSA − T t OCSA − T r Figure 1: Detectio n error p robabilities and d iv ersity gains of non-co op erativ e, CSA and O CSA sc hemes. + P OC ρ ( e t | T t : S ) | {z } =0 P ( T t : S ) . (16) On the other h and P OC ρ ( e t | T t : F ) = P OC ρ ( e t | T t : F , T r : F ) P ( T r : F ) + P OC ρ ( e t | T t : F , T r : S ) P ( T r : S ) ≤ P ( T r : F ) + P OC ρ ( e t | T t : F , T r : S ) ≤ E γ p,t Q q 2 d 1 ρ | γ p,r | 2 + E γ p,t Q q 2 dρ | γ p,r | 2 . = 1 ρ + 1 ρ . = 1 ρ . (17) Recalling that P ( T t : F ) . = 1 ρ and u sing (16)-(17) pro vides that P OC ρ ( e t ) . = 1 ρ . A similar argument holds for P OC ρ ( e r ). Numerical ev aluations of the p r obabilitie s of erroneous s p ectrum hole detection in different schemes are pro vided in Fig. 1. These error probabilities for th e non-co op erativ e, th e CSA, and the OC S A proto cols are pro vided in (5), (13), and (15), resp ectiv ely . This figure compares the detection p erformance of the p rop osed co op erativ e sc hemes with that of the non-co op erati ve scheme, wh ere it demonstrates that the CS A and the OCSA p rotocols achiev e a s ec ond -order div ersity gain. 11 As exp ected theoretically , at lo w SNR r egimes the CS A proto col migh t not outp erform th e non- co operativ e scheme, w h ereas the OCSA proto col outp erforms the n on-coop erativ e s cheme o ver all SNR regimes. In the ev aluations ab o v e, we hav e set α = 0 . 5 and ha ve considered c h an n el c hann el realizatio ns with parameters ( λ p,t , λ p,r , λ t,r ) = (1 , 2 , 3). In Fig. 1, the err or probabilit y of the user T i for i ∈ { t, r } in the CSA and OCS A pr oto cols is iden tified by CS A- T i and OCSA- T i , resp ectiv ely . 4.4 F alse Alarm Th u s far we ha ve examined the impro vemen ts attained in detecting the v acan t sp ectrum holes. In suc h detection problems, h o wev er, another asp ect that should also b e tak en into consideration is the false alarm probabilit y . In our pr oposed sp ectrum access m odels, false alarm is the even t that the secondary users erron eously consid er a sp ectrum band to b e idle, i.e., they detect the b eacon message while the c hann el is still u s ed by th e pr imary user. This leads to concurr en t transmiss ions b y the prim ary and secondary users wh ic h can p oten tially h arm the transmission of the pr imary user. Due to stringen t constrain ts on av oiding concurrent transmissions, it is imp erativ e to study the probab ility of false alarm as w ell. F or most detection problems, there exists a tension b et wee n the probability of su cce ssf ul detec- tion and the probabilit y of false alarm and it is crucial to maintain a go od balance b et ween these t wo p robabilities su c h that neither of them is sacrificed in fa vo r of the other one. In this p ap er we hav e translated a detection pr oblem into a comm unication problem rested on the basis of exc hanging a b eacon message. T herefore, assessing th e pr obabilit y of erroneously deco ding a non-b eacon message in fa vo r of the b eacon message has the same nature as that of missing a transmitted b eacon and b oth are quan tified in terms of deco ding errors. More sp ecificall y , the probabilit y that for a channel realizati on γ p,t , a non-b eacon cod ew ord ˆ c is mistak enly decod ed as the b eacon message denoted by c (whic h is the false alarm pr ob ab ility) is giv en by P ′ ρ ( e t | γ p,t ) △ = Pr( ˆ c → c | γ p,t ) = Q q 2 dρ | γ p,t | 2 , (18) whic h is equal to th e probabilit y in (5). T herefore, by follo win g the same lines as in Sections 4.2 and 4.3 it is seen that the prop osed coop eration mo dels will also impro ve the pr obabilit y of false alarm w h ic h diminish es as fast as the p robabilit y of missing the b eacon, enjo ying a second order div ersity gains. As a result, deploying the prop osed co operation schemes n ot only incurs no loss in th e pr ob- abilit y of false alarm, bu t also imp ro ves it. Hence, by translating the detection pr oblem in to a comm unication pr oblem, the tension b et wee n the tw o aforemen tioned pr obabiliti es is resolved and they can b e improv ed sim ultaneously . 12 5 Capacit y Analysis In this section w e analyze the effect of erroneous detection of un u s ed c hannel and thereof miss ing comm unication opp ortunities on th e capacit y of the secondary users an d will sho w ho w exploiting the prop osed coop erativ e diversit y proto cols enh ances the capacit y . In the OCS A proto col, eac h user requires to know the gains of its outgoing c hannels to the other users . Acquiring su c h channel gains requires information exc hange ov er th e wireless channel. Therefore, the acquired c hann el gain estimates are not p erfect in practice, wh ic h can affect the capacit y . In this section, we assume th at all c hann el estimates f or the OCSA proto col are p erf ect and defer analyzing the effect of estimation inaccuracy on the channel capacit y to Section 6.2. F or fading c hann els there is alw a ys a n on-ze ro probability that a target rate R cannot b e sup- p orted and there is no meaningful notion of capacit y as a rate of arbitrarily reliable comm unication. Therefore, we resort to lo oking int o the notions of outage capacit y f or slow fading c hann els and ergo dic capacit y for fast fading channels. Capacit y of th e secondary link is in fluenced b y the sp ectral activit y of the primary users an d the efficiency of the secondary users in detecting the un used c hannels. I n an earlier study in [14], it is also demonstrated ho w th e secondary u ser capacit y is affected by d issimilar p erception of secondary users of primary u ser’s sp ectral activit y in their vicinities, where it has b een sho w n th at more correlated p erceptions lead to h igher channel capacit y for the secondary link. W e will sho w that the co op erativ e p rotocols are also effectiv e in increasing suc h correlation. Lo w er and u p p er b ounds on the capacit y of the secondary c hannel, when the receiv ed p o wer at the secondary receiv er is P , are giv en by [14] C U ( P ) = Pr( S t = S r = 1) log 1 + P Pr( S t = S r = 1) , (19) and C L ( P ) = Pr( S t = S r = 1) log 1 + P Pr( S t = 1) − 1 T c . (20) where the states S t , S r ∈ { 0 , 1 } , assigned to the secondary trans m itt er and receiv er r espectiv ely , indicate the p erception of th e secondary users ab out the activit y of th e primary user. S t = 0 and S t = 1 mean that the secondary transmitter has sensed the c han n el to b e busy and id le, resp ectiv ely , and S r is defin ed accordingly . These state v ariables retain their s tates for a p erio d of T c c hannel uses and v ary to an i.i.d. state afterw ard s and as seen ab o ve, T c only affects the lo wer b ound F or fur th er analysis w e assum e that all c hann el c hannels (i.e., h p,t , h p,r , h t,r ) follo w the s ame fading mo del and therefore the states S t and S r ha ve th e same time v ariations as the secondary 13 c hannel h t,r , whic h means that all remain unc hanged for T c c hannel us es and c hange to indep endent states afterw ards. No w, corr esp ond ing to d ifferen t v alues of T c w e will ha ve slo w and fast f ading pro cesses and need to lo ok in to meaningfu l notions of capacit y for eac h of them. 1) F ast fading: Small v alues of T c corresp ond to f ast fading for which a meaningful notion of capacit y is given by ergo dic capacit y and is obtained b y av eraging o ve r all channel fluctuations. C U erg ( ρ ) △ = E γ t,r h C U ( ργ t,r ) i , C L erg ( ρ ) △ = E γ t,r h C L ( ργ t,r ) i . (21) 2) Slow fading: Corresp ondin g to large v alues of T c ≫ 1 w e consider the ǫ -outage capacit y C ǫ as the p erformance measure for wh ic h th e b oun d s are giv en by Pr C U(L) ( ργ t,r ) < C U(L) ǫ ( ρ ) ≤ ǫ. (22) As the ergod ic and outage capacitie s pro vid ed in (21)-(22) dep end on the prob ab ility terms Pr( S t = 1) and Pr( S t = S r = 1), w e need to assess these terms and their v ariations under d ifferen t co op- eration mo dels. Th e states S t and S r dep end not only th e sp ectral activit y in the vicinity of the secondary transmitter and r ec eive r , but also on how su ccessfu lly these u sers sense this s p ectral activit y . W e in tro duce the random v ariables θ t , θ r ∈ { 0 , 1 } to accoun t for mo deling the sp ectral activities. θ t = 1 ( θ r = 1) states that no primary user is us ing the c hannel in the vicinit y of the secondary transmitter (receiv er) and th e channel can b e used b y the secondary users . θ t = 0 and θ r = 0 are d efined accordingly for busy c h annels. Based on the definitions ab o ve and those of S t and S r , whic h in dicat e the p erception of secondary users of the activit y of the primary u ser, we h a ve Pr( S t = 1) = Pr ( θ t = 1)(1 − P ρ ( e t )) , (23) Pr( S t = S r = 1) = Pr ( θ t = θ r = 1) P ρ ( ¯ e t , ¯ e r ) . (24) where e t and e r are the erroneous detection even ts. Note that the terms Pr( θ t = 1) and Pr( θ t = θ r = 1) for the co op er ative and non-coop erativ e schemes are iden tical and the effect of co op eratio n reflects in the terms P ρ ( ¯ e t ) and P ρ ( ¯ e t , ¯ e r ). In th e follo w ing tw o lemmas we sho w how the CSA and the OCS A proto cols imp ro ve th e p robabilit y Pr( S t = S r = 1). Lemma 2 F or sufficiently lar ge SNR we have Pr C ( S t = S r = 1) ≥ Pr NC ( S t = S r = 1) . Pr o of: W e fi rst sh o w that for sufficien tly large SNR , P C ρ ( ¯ e r | ¯ e t ) ≥ P NC ρ ( ¯ e r ) as follo ws. P C ρ ( ¯ e r | ¯ e t ) = P C ρ ( ¯ e r | ¯ e t , T r : S ) | {z } =1 P ( T r : S ) 14 + P C ρ ( ¯ e r | ¯ e t , T r : F | {z } ≡ T t : S , T r : F ) P ( T r : F ) = P ( T r : S ) + P C ρ ( ¯ e r | T t : S , T r : F ) P ( T r : F ) ≥ P NC ρ ( ¯ e r ) P ( T r : S ) + P C ρ ( ¯ e r | T t : S , T r : F ) | {z } . =1 − 1 ρ 2 P ( T r : F ) ≥ P NC ρ ( ¯ e r ) P ( T r : S ) + P NC ρ ( ¯ e r ) | {z } . =1 − 1 ρ P ( T r : F ) = P NC ρ ( ¯ e r ) . (25) On th e other hand, from Theorem 1 we kno w that for sufficien tly large SNR , P C ρ ( ¯ e t ) > P NC ρ ( ¯ e t ), whic h in conjunction with (25 ) provi d es that P OC ρ ( ¯ e t , ¯ e r ) = P C ρ ( ¯ e r | ¯ e t ) P C ρ ( ¯ e t ) ≥ P NC ρ ( ¯ e r ) P NC ρ ( ¯ e t ), whic h is the desired result. Lemma 3 F or al l values of SNR we have Pr OC ( S t = S r = 1) ≥ max Pr C ( S t = S r = 1) , Pr NC ( S t = S r = 1) . Pr o of: W e equiv alen tly sho w that P OC ρ ( ¯ e t , ¯ e r ) ≥ max { P C ρ ( ¯ e t , ¯ e r ) , P NC ρ ( ¯ e t , ¯ e r ) } . By expanding P OC ρ ( ¯ e t , ¯ e r ) o v er all different combinatio n s of the statuses of the secondary users (success/failure) w e get P OC ρ ( ¯ e t , ¯ e r ) = P OC ρ ( ¯ e t , ¯ e r | T t : S , T r : S ) | {z } =1 P ρ ( T t : S , T r : S ) + P OC ρ ( ¯ e t , ¯ e r | T t : S , T r : F ) | {z } = P OC ρ ( ¯ e r | T t : S , T r : F ) P ρ ( T t : S , T r : F ) + P OC ρ ( ¯ e t , ¯ e r | T t : F , T r : S ) | {z } = P OC ρ ( ¯ e t | T t : F , T r : S ) P ρ ( T t : F , T r : S ) + P OC ρ ( ¯ e t , ¯ e r | T t : F , T r : F ) | {z } = P NC ρ ( ¯ e t ) P NC ρ ( ¯ e r ) P ρ ( T t : F , T r : F ) = P ρ ( T t : S , T r : S ) + P ρ ( T t : S , T r : F ) 15 −10 −5 0 5 10 15 20 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 SNR (dB) P(e t c ,e r c ) Non−Cooperative CSA OCSA Figure 2: Comp arin g P ρ ( ¯ e t , ¯ e r ) for differen t sc hemes. × 1 − Q q 2 d 1 ρ | γ p,r | 2 + 2 d 2 ρ max { γ p,r | 2 , | γ t,r | 2 } + P ρ ( T t : F , T r : S ) × 1 − Q q 2 d 1 ρ | γ p,t | 2 + 2 d 2 ρ max { γ p,t | 2 , | γ t,r | 2 } + P ρ ( T t : F , T r : F ) × 1 − Q q 2 dρ | γ p,t | 2 1 − Q q 2 dρ | γ p,r | 2 . (26) By follo wing similar steps we can sh o w that P C ρ ( ¯ e t , ¯ e r ) = P ρ ( T t : S , T r : S ) + P ρ ( T t : S , T r : F ) × 1 − Q q 2 d 1 ρ | γ p,r | 2 + 2 d 2 ρ | γ t,r | 2 + P ρ ( T t : F , T r : S ) × 1 − Q q 2 d 1 ρ | γ p,t | 2 + 2 d 2 ρ | γ t,r | 2 , (27) Comparing (26) and (27) establishes that P OC ρ ( ¯ e t , ¯ e r ) ≥ P C ρ ( ¯ e t , ¯ e r ). Also from (26) w e get P OC ρ ( ¯ e t , ¯ e r ) ≥ P ρ ( T t : S , T r : S ) + P ρ ( T t : F , T r : F ) + P ρ ( T t : S , T r : F ) 1 − Q q 2 dρ | γ p,r | 2 16 + P ρ ( T t : F , T r : S ) 1 − Q q 2 dρ | γ p,t | 2 ≥ P ρ ( T t : S , T r : S ) + P ρ ( T t : F , T r : F ) + P ρ ( T t : S , T r : F ) × 1 − Q q 2 dρ | γ p,r | 2 1 − Q q 2 dρ | γ p,t | 2 + P ρ ( T t : F , T r : S ) × 1 − Q q 2 dρ | γ p,t | 2 1 − Q q 2 dρ | γ p,r | 2 ≥ 1 − Q q 2 dρ | γ p,t | 2 1 − Q q 2 dρ | γ p,r | 2 = P NC ρ ( ¯ e t , ¯ e r ) whic h completes the pro of. Figure 2 illustr at es numerical ev aluations comparing the term P ρ ( ¯ e t , ¯ e r ) for d ifferent s chemes giv en in (25)-(27). As exp ected, for very lo w SNR regimes, C SA exhibits n o gain o ver non- co operativ e sc heme, w hile OCSA outp erforms b oth CSA and n on-coop erativ e sc h emes in all SNR regimes. As seen in the figure, the CSA p rotocol ac hieve s consid er ab le gain in mo derate SNR regimes. F or the n um er ical ev aluations we ha ve assumed the same setup as in Fig. 1. Theorem 3 F or lar ge enough SNR values we have C U , C erg ( ρ ) > C U , NC erg ( ρ ) , and C L , C erg ( ρ ) > C L , NC erg ( ρ ) , C U , C ǫ ( ρ ) > C U , NC ǫ ( ρ ) , and C L , C ǫ ( ρ ) > C L , NC ǫ ( ρ ) . Pr o of: See App endix B. Theorem 4 F or al l SNR r e g imes we have C U , OC erg ( ρ ) > max C U , C erg ( ρ ) , C U , NC erg ( ρ ) , C L , OC erg ( ρ ) > max C L , C erg ( ρ ) , C L , NC erg ( ρ ) , C U , OC ǫ ( ρ ) > max C U , C ǫ ( ρ ) , C U , NC ǫ ( ρ ) , and C L , OC ǫ ( ρ ) > max C L , C ǫ ( ρ ) , C L , NC ǫ ( ρ ) . Pr o of: See App endix C. 17 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 0 0.5 1 1.5 2 2.5 3 3.5 4 4.5 Outage Probability Outage Capacity (bits/sec/Hz) Upper Bound Lower Bound OCSA CSA Non−Cooperative Figure 3: Low er and upp er b ounds on outage capacit y for different sc hemes. Figure 3 d emons trate s numerical ev aluations of the outage capacit y ac h iev ed u nder differen t schemes. F or these ev aluations w e h a ve us ed the capacit y lo w er and u pp er b ounds giv en in (22) and ha ve as- sumed α = 1 2 . F or ev aluating Pr( S t = S r = 1) giv en in (24) we ha ve assumed Pr( θ t = θ r = 1) = 0 . 7 in b oth co op erativ e and n on-coop erativ e sc h emes. W e also hav e assumed SNR =10 dB, and for th e lo w er b oun ds on the outage capacit y we ha ve set T c = 10. It is obs er ved that outage capacit y b ound increases as we allo w higher outage probabilit y . Also, since the gap b et we en th e lo we r an d upp er b ound s for the co op erativ e sc hemes is small, the b ounds seem to b e tigh t. 6 Discussions 6.1 Information Exchan ge In th is section w e discuss ho w the primary and the secondary users acquire the channel state information th at th ey need in the OCS A p rotocol. T he users need to acquire c hannel gains, whic h can b e facilitat ed via emplo ying training-based channel estimation sc hemes and feedb ac k comm unication. S uc h estimations and feedb ac k can b e carried out reliably via a v ery lo w-rate comm unication (b y transmitting f ew pilot symb ols). The information ab out c hann el gains is used only once for initializing th e bac k off timers, which is d u ring the trans iti on of the c hann el access from the primary u ser to th e secondary users and is not n eeded afterwa rd s. It is notew orthy that acquiring su ch c hannel state in f ormatio n is not guarantee d to b e feasible in all n et works, in whic h case the secondary users can deplo y the CS A proto col that d o es not requir e an y information exchange. 18 In the OCSA p rotocol we n ee d the follo wing channel state information. 1) The se c ondary tr ansmitter should know | γ p,t | and the se c ondary r e c ei v er should know | γ p,r | : W e assume th at the prim ary transmitter is p erio dically tr an s mitting training sym b ols to its des- ignated receiv er for training p urp oses. The s ec ond ary u sers can ov erh ea r th ese pilots due to the broadcast nature of the w ireless c hannel and p erio dical ly acquire their desired c hannel states. Ob- taining these c hann el gains is only p ossible when th e primary users transmits training sym b ols to its designated receiv er and these sy mb ols are kn o wn to the secondary users a priori . 2) The se c ondary users should know | γ t,r | = | γ r,t | : This c hann el gain can b e acquired b y h a vin g the secondary users exc hange pilot symb ols. Th is exc hange should b e p erform ed while the primary u ser is still activ e. T o a vo id harming the communi- cation of primary u sers, the p ilot s can b e exc h anged using u ltra-wide b and (UWB) comm unication whic h allo ws the secondary users to comm un icate the lo w-rate pilots well b elo w the n oise lev el of the p rimary user. As the secondary users d o n ot hav e any prior inf ormati on ab out the time of the a v ailabilit y of the c hannel, they should keep exc hanging the p ilo ts according to h o w static the c hannel γ t,r is. Sin ce exc hanging pilot sequences requires a very lo w-rate comm un ica tion, th e pro cess of channel gain estimation can b e p erformed reliably . T h is level of information exchange can b e carried out in all netw orks . W e also assume that the secondary users also exc h an ge the estimates of | γ p,t and | γ p,r | that they h av e obtained in S tep 1. 3) The primary user should know | γ p,t | and | γ p,r | : W e d evise t wo time slots b et we en the time that primary user finishes the transmission of the b eacon, and the time that all users run their bac ko ff timers. Dur ing these t w o time slots, the secondary users feed bac k the v alue of | γ p,t | 2 + | γ p,r | 2 whic h they ha v e already obtained during steps 1 and 2. Note that eac h secondary user will ha ve feedback transmission only if it has successfully deco ded th e b eacon, otherwise its dedicated feedb ac k slot will b e w asted. Also, the p rimary user will not receiv e an y feedbac k only if b oth secondary users fail to deco de the b eacon, in w hic h case its lac k of kn owledge ab out the v alue | γ p,t | 2 + | γ p,r | 2 do es not harm as the secondary users will not step in the comp etitio n phase and an y random initializing of the primary user s ’s bac koff timer suffices to ensu re that the p rimary us er will b e transm itti n g in the second ph ase. 6.2 Imp erfect Channel Estimation The OCSA p r otocol requires the p r imary to know | γ p,t | 2 + | γ p,r | 2 , the secondary transmitter to kno w | γ p,t | 2 + | γ t,r | 2 , and the secondary receiv er to know | γ p,r | 2 + | γ r,t | 2 . In the capacit y analysis in Section 5 we ha ve assumed that all users kno w their corresp onding c hann el state information 19 p erfectly . In practice, ho wev er, estimating and feeding bac k su c h c hann el gains is imp erfect, whic h can p oten tially affect the c hannel capacit y . As discussed in Section 6.1, these c h annel gains are used only for the pu rp ose of determining whic h user should b e assigned as rela y (to transmit the additional parit y bits). Therefore, the effect brought ab out by im p erf ec t channel estimate is the p ossibilit y of selecting a w rong rela y . Note that not any imp erfect estimation would necessarily lead to selecting a wron g rela y , as rela y selection is based on the relativ e order of { t p , t t , t r } and not their exact v alues. F or instance, if t t = max { t p , t t , t r } and w e denote th e estimates of { t p , t t , t r } by { ˜ t p , ˜ t t , ˜ t r } , there is the c hance that ˜ t t = max { ˜ t p , ˜ t t , ˜ t r } to o, in whic h case the estimation errors do not affect the p erformance of the proto col and the capacit y of the secondary link . In the OCSA p rotocol with imp erfect c hann el estimates, for the c hannel realizatio n s leading to the metrics { t p , t t , t r } , we denote the probabilit y of selecting a wr ong rela y by P wr ( t p , t t , t r ). W e also denote the capacit y of the secondary link when th e righ t rela y is selected by C OC ( P ) (which is also the capacit y w ith p erfect c hann el estimates) and wh en a wrong rela y is s elected by b C OC ( P ), where P is the p ow er of the receiv ed signal by th e s econdary receiv er . Therefore, the capacit y when c hannel estimate s are imp erfect is giv en by ˜ C OC ( P ) △ = ¯ P wr ( t p , t t , t r ) C OC ( P ) + P wr ( t p , t t , t r ) b C OC ( P ) . (28) Note that ˜ C OC ( P ) dep ends on { γ p,t , γ p,r , γ t,r } whic h is not explicitly expr essed in the formulat ions for the ease of notations. Errors in estimating c h an n el gains u ltima tely lead to errors in estimating { t p , t t , t r } which are us ed to set the in itia l v alues of the bac ko ff timers. W e d enote suc h estimation errors by w i △ = ˜ t i − t i for i = { p, t, r } where ˜ t i is the estimate of t i , and assume that w i ∼ N (0 , σ 2 ). Therefore, analyzing the effect of imp erfect c h annel estimation on the capacit y of the cognitiv e link translates in to analyzing ho w ˜ C OC ( P ) and σ 2 are related, which is provided in the follo w ing theorem. W e fi r st find an u pp er b ound on the relativ e capacit y loss due to imp erf ect estimates and then sh o w that one ord er of magnitude decrease in the estimation errors, translates int o one order of m ag n itu d e decrease in the capacit y loss, e.g., the capacit y loss due to estimation noise with v ariance σ 2 100 is 1 10 of the capacit y loss due to th e estimation n oise v ariance with σ 2 . Theorem 5 F or i.i.d. channel r e alizations γ p,t , γ p,r , γ t,r and imp erfe ct channel estimates with es- timation noise varianc e σ 2 , 20 1. the r elative c ap acity loss is b ounde d as E γ t,r ,γ p,t ,γ p,r " C OC ( ργ t,r ) − ˜ C OC ( ργ t,r ) C OC ( ργ t,r ) # < 1 3 E t p ,t t ,t r Q | t p − t t | √ 2 σ 2 + Q | t p − t r | √ 2 σ 2 , 2. the c ap acity loss for de cr e asing values of σ 2 de c ays faster than σ , i.e., lim σ → 0 log E γ t,r ,γ p,t ,γ p,r h C OC ( ργ t,r ) − ˜ C OC ( ργ t,r ) C OC ( ργ t,r ) i log σ < 1 3 Pr o of: 1. W e p ro vid e the analysis f or the case that γ p,t , γ p,r , γ t,r are i.i.d. By follo win g the same line of argument w e can fin d an upp er b ound for the non-identica l distributions as we ll. When the c hann el estimates are p erfect, we d enote the rela y selected by the OCS A by T R . T he probabilit y of selecting a wrong rela y b y some simp le manipulations can b e expand ed as follo ws. E t p ,t t ,t r P wr ( t p , t t , t r ) = X i ∈{ p,t,r } E t p ,t t ,t r P ρ T R 6 = T i | t i = max { t p , t t , t r } 3 . (29) On the other h and we hav e E t p ,t t ,t r P ρ T R = T t | t p = max { t p , t t , t r } = E t p ,t t ,t r P ρ ( T t : S ) P ρ ( T r : F ) | {z } 1 − P ρ ( T r : S ) × P ρ ˜ t t > ˜ t p | t p > t t , t r + E t p ,t t ,t r P ρ ( T t : S ) P ρ ( T r : S ) × P ρ ˜ t t > ˜ t p | t p > t t , t r P ρ ˜ t t > ˜ t r | t p > t t , t r | {z } ≤ 1 ≤ E t p ,t t ,t r P ρ ( T t : S ) P ρ ˜ t t > ˜ t p | t p > t t , t r ≤ E t p ,t t ,t r P ρ ˜ t t > ˜ t p | t p > t t , t r 21 = E t p ,t t P ρ ˜ t t > ˜ t p | t p > t t , (30) and similarly E t p ,t t ,t r P ρ T R = T r | t p > t t , t r ≤ E t p ,t r P ρ ˜ t r > ˜ t p | t p > t r . (31) Also it can b e readily verified that E t p ,t t ,t r P ρ T R = T p | t t > t p , t r + E t p ,t t ,t r P ρ T R = T r | t t > t p , t r < E t p ,t t P ρ ˜ t p > ˜ t t | t t > t p , (32) and similarly E t p ,t t ,t r P ρ T R = T p | t r > t p , t t + E t p ,t t ,t r P ρ T R = T r | t r > t p , t t < E t p ,t t P ρ ˜ t p > ˜ t r | t r > t p , (33) By n oti n g that ˜ t i = t i + w i where w i ∼ N (0 , σ 2 ), and denoting the probabilit y densit y functions of t i b y f ( t i ), (29)-(33) pr o vide that E t p ,t t ,t r P wr ( t p , t t , t r ) < 1 3 E t p ,t t P ˜ e t − ˜ e p > t p − t t | t p > t t + 1 3 E t p ,t t P ˜ e p − ˜ e t > t t − t p | t t > t p + 1 3 E t p ,t r P ˜ e r − ˜ e p > t p − t r | t p > t r + 1 3 E t p ,t r P ˜ e p − ˜ e r > t r − t p | t r > t p = 1 3 Z ∞ 0 Z ∞ 0 Q | t p − t t | √ 2 σ 2 f ( t p ) dt p f ( t t ) dt t + 1 3 Z ∞ 0 Z ∞ 0 Q | t p − t r | √ 2 σ 2 f ( t p ) dt p f ( t r ) dt r = 1 3 E t p ,t t ,t r Q | t p − t t | √ 2 σ 2 + Q | t p − t r | √ 2 σ 2 . (34) 22 No w, from (28 ) and (34) w e get E γ t,r ,γ p,t ,γ p,r " C OC ( ργ t,r ) − ˜ C OC ( ργ t,r ) C OC ( ργ t,r ) # = < E t p ,t t ,t r P wr ( t p , t t , t r ) < 1 3 E t p ,t t ,t r Q | t p − t t | √ 2 σ 2 + Q | t p − t r | √ 2 σ 2 , (35) whic h is the desired result. 2. W e start by showing that lim σ → 0 log E t p ,t t h Q | t p − t t | √ 2 σ 2 i log σ = 1 . By some simp lificat ions w e get E t p ,t t Q | t p − t t | √ 2 σ 2 = E γ p,r ,γ t,r Q | γ p,r | 2 − | γ t,r | 2 √ 2 σ 2 , (36) where we ha ve assumed that { γ p,t , γ p,r , γ t,r } are i.i.d. d istributed as N (0 , λ ) w here w e ha v e defined λ △ = λ p,t = λ p,r = λ t,r . Therefore, | γ p,r | 2 and | γ t,r | 2 are distributed exp onen tially with mean 2 λ . It can b e r ea d ily shown that th e random v ariable X △ = | γ p,r | 2 − | γ t,r | 2 is also distributed exp onentia lly with mean 2 λ . Th erefore, from (36) we get E t p ,t t Q | t p − t t | √ 2 σ 2 = E X Q X √ 2 σ 2 . (37) On the other h and, we know that ∀ x > 0 1 √ 2 π x 1 − 1 x 2 e − x 2 / 2 ≤ Q ( x ) ≤ 1 √ 2 π x e − x 2 / 2 , whic h p ro vid es lim x →∞ log 1 √ 2 π x 1 − 1 x 2 e − x 2 / 2 log e − x 2 / 2 | {z } = 1 ≤ lim x →∞ log Q ( x ) log e − x 2 / 2 ≤ lim x →∞ log 1 √ 2 π x e − x 2 / 2 log e − x 2 / 2 | {z } = 1 , or equiv alen tly , for asymptotically large v alues of x , Q ( x ) . = e − x 2 / 2 . 23 F or any given v alue of X , by setting x = X √ 2 σ 2 , for asymptotically large v alues of x (or small v alues of σ ) Q X √ 2 σ 2 . = e − X 2 4 σ 2 . Hence, for asymp totically sm all v alues of σ E X Q X √ 2 σ 2 . = E X e − X 2 4 σ 2 = 1 2 λ Z ∞ 0 e − ( x 2 / 4 σ 2 + x/ 2 λ ) dx = 1 σ · √ π e σ 2 / 4 λ 2 2 λ Q σ λ √ 2 | {z } . =1 . = 1 σ , whic h in conjunction with (37) gives rise to E t p ,t t Q | t p − t t | √ 2 σ 2 = E X Q X √ 2 σ 2 . = 1 σ . (38) Similarly , w e can show that E t p ,t t Q | t p − t r | √ 2 σ 2 . = 1 σ . (39) Hence, E t p ,t t ,t r Q | t p − t t | √ 2 σ 2 + Q | t p − t r | √ 2 σ 2 . = 1 σ . ( 40) (35) and (40) p ro v id e that lim σ → 0 log E γ t,r ,γ p,t ,γ p,r h C OC ( ργ t,r ) − ˜ C OC ( ργ t,r ) C OC ( ργ t,r ) i log σ < lim σ → 0 log E t p ,t t ,t r h Q | t p − t t | √ 2 σ 2 + Q | t p − t r | √ 2 σ 2 i 3 log σ = 1 3 , whic h is the desired result. The numerical ev aluation of E t p ,t t ,t r h Q | t p − t t | √ 2 σ 2 + Q | t p − t r | √ 2 σ 2 i v ersus the v ariance of noise es- timation ( σ 2 ) is dep ict ed in Fig. 4 for for three differen t SNR v alues. W e hav e considered the setup λ p,t = λ p,r = λ t,r = 1 where we can see that when the n oise v ariance is σ 2 = 0 . 01 the capacit y loss will b e less than %1 at ρ = 0 dB, wh ic h is a negligible loss. Also, it is observe d that for any fixed v alue of σ 2 , in crea sin g the SNR results in less capacit y loss. Th is is j ustified by noting that for fixed noise level, more p o w erfu l signal are less prone to estimation errors. 24 10 −2 10 −1 10 0 10 −3 10 −2 10 −1 10 0 10 1 σ Relative Capacity Loss SNR = −10 dB SNR = 0 dB SNR = 10 dB Figure 4: Relativ e capacit y loss v ersus c hannel estimation noise accuracy . 6.3 Throughput Analysis Channel capacit y , b eing an in trins ic c haracteristic of the wir ele ss c hannel, is n ot influenced by ho w effectiv ely the c h annel is utilized or b y how muc h the MAC-lev el co ordinations (e.g., bac koff timers and information exc hange in the OCS A proto col) cost. Therefore, in order to furn ish a fair comparison b et wee n the OCSA pr ot o col and the non-co op erati ve scheme and to incorp orate the MA C-lev el costs of this protocol, w e assess th e ac hiev able throughputs. W e hav e d ev elop ed a thr oughput analysis, wh ic h r ests on th e b asis of our c ap acity analysis, to accoun t for tw o t yp es of throughp ut losses incurr ed by the OCSA proto col. One loss is du e to the time w aste imp osed by the bac koff timers and the other loss is du e to the requir ed feedbac k from the secondary users to the primary user. As as r unning the back off timers an d exc h an ging inform at ion tak e place only one time, if the secondary users access the c hannel for a p erio d sufficien tly larger than those of the bac k off timers and the feedbac k communications, the throughp u t will b e ve r y close to the capacit y and these throughput losses will ha v e a negligible effect. In order to formulate th e throughpu t, wh ic h w e denote by R , w e defin e T CR as the du ratio n that the secondary link will us e th e c hann el and w e denote the time dedicated to the f ee d bac k comm unication b y T FB . Finally , w e denote the initial v alue of the back off timer of user T i b y T i BT whic h is set as T i BT △ = β t i for i ∈ { p, t, r } , where β is a constan t and its u nit dep ends on the unit of t i . Since { t i } are scalars, β has the un its 25 of time. T h erefore, for an y c h an n el realization { γ p,t , γ p,r , γ t,r } , when the rela y is us er T i , the time dela y d u e to back off timers is T i BT and the throughp u t is foun d as R ( γ p,t , γ p,r , γ t,r ) = T CR T CR + T FB + T i BT · ˜ C OC ( ργ t,r ) = T CR T CR + T FB + β t i · ˜ C OC ( ργ t,r ) , (41) where w e hav e tak en in to account that there is a one-time feedbac k transmission and back off timer activ ation. (41) suggests that wh en the duration that the secondary users access the c hann el is considerably longer th an the time required for feedback, i.e., T CR ≫ T FB , the throughp ut loss due to feedbac k will b e negligible. How ever, the same argument do es not apply to the effect of bac koff timers as for ve ry w eak channels (small t i ), β t i can b ecome a non-negligible factor compared to T CR . In the follo wing theorem, we assess the aver age throughp ut loss o ver the p ossible c hann el realizatio ns . Theorem 6 The aver age thr oughput loss due to information exchange and b ackoff timers is upp er b ounde d by E γ t,r ,γ p,t ,γ p,r " ˜ C OC ( ργ t,r ) − R ( γ p,t , γ p,r , γ t,r ) ˜ C OC ( ργ t,r ) # ≤ w 1 1 + w 1 + (1 + w 1 ) e w 2 1+ w 1 − 1 , wher e w 1 △ = T FB T CR and w 2 △ = β T CR λ p,t . Pr o of: First note that f or the n ode T i selected as th e rela y , t i ≥ t p = | γ t,p | 2 + | γ t,r | 2 > | γ t,p | 2 . Therefore, from (41) we get R ( γ p,t , γ p,r , γ t,r ) ˜ C OC ( ργ t,r ) ≥ 1 1 + w 1 + w 2 · 1 | h p,t | 2 . Therefore, E γ t,r ,γ p,t ,γ p,r " R ( γ p,t , γ p,r , γ t,r ) ˜ C OC ( ργ t,r ) # ≥ E γ p,t T CR T CR + T FB + β | γ p,t | 2 = E h p,t " 1 1 + w 1 + w 2 · 1 | h p,t | 2 # 26 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 0 0.5 1 1.5 2 2.5 3 3.5 4 4.5 Outage Probability Outage Capacity (bits/sec/Hz) Non−Cooperative CSA OCSA − w 1 =0, w 2 =0 OCSA − w 1 =0.2, w 2 =0.1 OCSA − w 1 =0.1, w 2 =0.2 OCSA − w 1 =0.2, w 2 =0.2 Figure 5: Th roughput comparison in differen t schemes. = (1 + w 1 ) e − t + w 2 e w 2 1+ w 1 E i − w 2 +(1+ w 1 ) t 1+ w 1 (1 + w 1 ) 2 t = ∞ t =0 = 1 1 + w 1 − w 2 e w 2 1+ w 1 Z ∞ w 2 1+ w 1 e − t t dt ≥ 1 1 + w 1 − w 2 e w 2 1+ w 1 1 − e − w 2 1+ w 1 1 + w 1 w 2 = 1 1 + w 1 − (1 + w 1 ) e w 2 1+ w 1 − 1 , whic h establishes the desires resu lt. F rom the r esult ab o v e, it is consequen tly concluded that for the appr opriate c hoice of β , i.e., by setting β ≪ T CR λ p,t ⇒ w 2 ≪ 1 w e can mak e the effect of the bac k off timers very negligible whic h pro vides that w 2 → 0 and E γ t,r ,γ p,t ,γ p,r " ˜ C OC ( ργ t,r ) − R ( γ p,t , γ p,r , γ t,r ) ˜ C OC ( ργ t,r ) # ≤ w 1 1 + w 1 . As for the effect of feedb ack, there will b e a loss w h ic h is u pp er b ound ed by T CR T CR + T FB . Th is loss will b e also marginal if the p erio d th at th e cognitiv e link is activ e is su ffi cie ntly larger than th e small p erio d of the feedb ac k communication, i.e., T CR ≫ T FB . Figure 5 dep icts the ac h iev able throughpu t b y the OCSA under different assum p tions on feed- bac k loads and bac koff timer settings and compares them to the throughp u t ac h iev able via the non-co operative scheme and the CSA p r otocol. The solid curves rep r esen t the lo we r b ound s on 27 the capacit y foun d in S ect ion 5. F or the non-coop erativ e and the CSA sc hemes, due to havi n g no MA C-la y er bandwidth loss, the through p ut is essen tially equiv alen t to the capacit y , w hereas for the OCS A proto col the throughp ut b ecomes equal to the capacit y wh en w e set w 1 = w 2 = 0. The dashed curv es illustrate the throughp ut of the OCSA proto col for the different c hoices of w 1 , w 2 . W e ha v e considered a similar setup as in th e n u merical ev aluations of Fig. 3. The results pro vide that for the c hoice of w 1 < 0 . 15 and w 2 < 0 . 15, the throughp ut of the OCSA sc heme is higher than that of the CSA scheme and as w 1 and w 2 exceed these lev els, the throughput of the OCSA proto co l falls b elo w th at of the CS A p rotocol. Note that in practical scenarios, it is r ea sonab le to assu m e that w 1 , w 2 < 0 . 15 as w 1 = T FB T CR , whic h is the ratio of th e length of the one-time feedbac k pac ket to the length of the information pac kets and is close t zero. Also, w 2 dep ends on the constan t factor β of the timers wh ic h can b e chosen suc h th at k eeps the v alue of w 2 arbitrarily small. 7 Multiuser Net w ork 7.1 Multiuser CSA Prot ocol (MU-CSA) The co operation pr otocols prop osed in Section 3 and the s ubsequen t analyses in Section 4 consider a cognitiv e net w ork with a single pair of secondary transmitter and r ece iver. In this section we pro vide a direction for generalizing the CSA proto col to a cognitiv e n et work consisting of m u ltiple secondary transmitter-receiv er pairs. The ob jectiv e is to pr o vide al l secondary u s ers with the div ersity gain 2 M for deco ding the b eacon message. W e consider a m ultiuser n et work consisting of M pairs of secondary transmitters and receiv ers denoted b y ( T 1 t , T 1 r ) , . . . , ( T M t , T M r ). The physica l channels b et ween the primary us er and the m th secondary transmitter and receiv er are repr esen ted by γ m p,t , γ m p,r , resp ectiv ely , and γ m t,r denotes the c hannel b et ween ( T m t , T m r ) for m = 1 , . . . , M . As in Section 2 for the c hann el r ea lizations w e ha v e γ m i,j = q λ m i,j h m i,j , (42) where h m i,j , the fading co efficie nts, are indep endent complex Gaussian C N (0 , 1) ran d om v ariables and λ m i,j represent p athloss and shado win g effects.In the CSA proto col, a secondary user acts as rela y b ased on its success in deco ding th e firs t s eg ment of the b eacon. T h e MU-CSA pr otocol consists of t wo steps: 1. Th e primary user broadcasts the first segmen t of the b eacon message dur ing the initial 0 < α < 1 p ortion of the time slot as in the CSA and OCSA proto cols and all the secondary transmitters and receiv ers listen to th e message and at the en d of the transmission try to deco de the message. 28 2. Durin g th e r emaining (1 − α ) p ortion of the time s lot , al l secondary users w h o ha ve suc- cessfully deco ded the first segmen t of the b eacon constru ct the ad d itio n al parit y bits and broadcast th em. Note that there is the p ossibilit y that m ultiple secondary user s hav e b een successful in the fir st phase. S ince all th ese users br oa d ca st identic al information pac k ets, their concurrent transm issions are not considered as collision and r at h er can b e d eemed as a distributed multi p le- antenna transmission. F or maint aining fairness in terms of the amount of resources consumed, the transmission p o w er of in dividual secondary users acting as rela y should n ot exceed P p 2 M in order to k eep the aggregate transm ission p ow er b elo w P p . T here is the issue of syn c hr oniza tion b et ween the successful r ela ys, w hic h they can ensure b y us ing the b eacon they hav e receiv ed as the syn c h ronizat ion reference. 7.2 Div ersity Analysis Next we sho w that in a m u ltiuser cognitiv e net work with th e MU-CSA p rotocol, all secondary users in the enjo y th e diversit y gain of 2 M in detecting the b eacon message. W e define the set T = { ˜ T 1 , . . . , ˜ T 2 M } = { T 1 t , . . . , T M t } S { T 1 r , . . . , T M r } . Also we defi n e M △ = { 1 , . . . , 2 M } and denote the channel b et ween th e secondary users ˜ T m and ˜ T n b y ˜ γ m,n and the channel b et wee n T p and ˜ T m b y ˜ γ p,m . The p robabilit y of missing the b eacon message by the secondary u ser ˜ T m is P C ρ ( e ˜ T m ) = X A ⊆M\{ m } A 6 = ∅ P C ρ ( e ˜ T m | ∀ i ∈ A, ˜ T i : S ; ∀ j / ∈ A, ˜ T j : F ) × P ρ ( ∀ i ∈ A, ˜ T i : S ; ∀ j / ∈ A, ˜ T j : F ) + P C ρ ( e ˜ T m | ∀ i, ˜ T i : F ) | {z } =1 P ρ ( ∀ i, ˜ T i : F ) = X A ⊆M\{ m } A 6 = ∅ Q s 2 d 1 ρ | ˜ γ p,m | 2 + 2 d 2 ρ 2 M X i ∈ A | ˜ γ i,m | 2 | {z } . = 1 ρ | A | +1 (from Lemma 1) × Y j / ∈ A Q q 2 d 1 ρ | ˜ γ p,j | 2 | {z } . = 1 ρ 2 M −| A | (from Lemma 1 ) × Y i ∈ A 1 − Q q 2 d 1 ρ | ˜ γ p,i | 2 | {z } 1 ρ (from Lemma 1) 29 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 0 0.5 1 1.5 2 2.5 3 3.5 4 4.5 5 Outage Probability ( ε ) Outage Capacity (bits/sec/Hz Upper Bound Lower Bound CSA Non−Cooperative Figure 6: Ou tag e capaci ty in a cognitiv e netw ork with 5 pairs of u sers. + Y i ∈{ 1 ,..., 2 M } Q q 2 d 1 ρ | ˜ γ p,j | 2 | {z } . = 1 ρ (from Lemma 1) . = 1 ρ 2 M +1 + 1 ρ 2 M . = 1 ρ 2 M Therefore, all of the secondary users enjoy a diversit y order 2 M in deco ding the b eacon m essag e. The c hannel capacit y can b e obtained similarly as in Section 5 for eac h secondary pair wh en only that pair accesses the channel. F or finding the c hannel capacit y of a sp ecific pair of secondary users we n eed to fin d 1) the probabilit y of detecting the b eaco n b y the secondary transmitter and 2) the pr obabilit y that b oth of secondary trans mitte r and receiv er are su cc essfu l in deco ding to b eacon. Th e lo wer and upp er b ounds on the c hannel capacit y are giv en in (19) and (20) and the capacit y f or the link b et w een ( T m t , T m r ) can b e found by plugging th e v alues of Pr( S T m t = 1) = Pr ( θ T m t = 1) P C ρ ( ¯ e T m t ) , and Pr( S T m t = S T m r = 1) = Pr ( θ T m t = θ T m r = 1) P C ρ ( ¯ e T m t , ¯ e T m r ) . Numerical ev aluations for the lo wer and u pp er b ounds on the secondary u ser capacit y in a cognitiv e net wo rk consisting of 5 pairs of u sers are shown in Fig. 6, whic h depicts th e outage capacit y . F or this ev aluation w e hav e u sed th e same setup as that in S ection 4.3. By comparin g these resu lts with those of a net work with one pair of secondary users it is seen that more gain in terms of c hannel capacit y is ac hiev able for the multi u ser net work whic h is due to opp ortunistic selection of the cognitiv e p air. As th e num b er of secondary u sers pairs increases, the qualit y of the b est 30 secondary u ser is exp ected to b ecome b etter wh ic h justifies the add itio nal gains observed in the m ultiuser cognitiv e netw orks. 8 Conclusions In th is pap er we h av e p rop osed opp ortun istic coop eration proto cols for sup ervised sp ectrum access in cognitiv e n et works where the p rimary and secondary u sers are only allo wed to h a ve orthogonal access to the c hann el and cannot co exist concurrently . The pr imary user broadcasts a b eacon message up on releasing the c hannel and a pair of secondary transmitter and receiv er co operative ly detect th e b eacon message. Th e co op erati on p rotocols are devised s uc h that by a single-time rela ying b oth secondary transmitter and receiv er enjo y second-order diversit y gains in detecting the b eacon message. W e ha ve also quant ified the effect of err oneous d ete ction of v acan t c hannels on the s econdary c hannel capacit y and sho w the adv antag e of the prop osed proto cols for ac hieving higher secondary channel capacit y . One of the prop osed proto cols imp oses information exc hange and bandwidth costs, wh er e we hav e assessed the effect of imp erf ec t information exc hange on the capacit y and the loss due to th e bandwid th cost on the ac hiev able th roughput. T he coop eration mo dels are also extended to multi-user cognitiv e netw orks as we ll. A Pro of of Lemma 1 First we sho w th at for the function A ( M , n ) △ = P M m =0 M m m n ( − 1) m , A ( M , n ) = 0 for ∀ M > n ≥ 0, and A ( M , M ) 6 = 0. W e p ro vide the pro of by indu cti on: 1) F or n = 0 and ∀ M > 0 we ha v e A ( M , 0) = P M m =0 M m ( − 1) m = (1 + ( − 1)) M = 0. 2) Assumption: ∀ M > n > 0 w e ha v e A ( M , n ) = 0. 3) Claim: ∀ M > n + 1 we sh o w that A ( M , n + 1) = 0. A ( M , n + 1) = M X m =0 M m m n +1 ( − 1) m = − M M − 1 X m =0 M − 1 m ( m + 1) n ( − 1) m = − M n X k =0 n k M − 1 X m =0 M − 1 m m k ( − 1) m = − M n X k =0 n k A ( M − 1 , k | {z } M − 1 >n ≥ k ) = 0 . 31 Mo w, we sh o w that A ( M , M ) 6 = 0. Again, by ind uction we h a ve: 1) F or M = 1, A (1 , 1) = − 1. 2) Assumption: A ( M , M ) 6 = 0. 3) Claim: A ( M + 1 , M + 1) 6 = 0. A ( M + 1 ,M + 1) = M +1 X m =0 M + 1 m m M +1 ( − 1) m = − ( M + 1) M X m =0 M m ( m + 1) M ( − 1) m = − ( M + 1) M X k =0 M k M X m =0 M m m k ( − 1) m = − ( M + 1) A ( M , M ) | {z } 6 =0 + M − 1 X k =0 M k A ( M , k ) | {z } =0 6 = 0 . Kno wing the ab o ve r esult and considering the f ollo win g T a ylor series expansion 1 + k x − 1 2 = ∞ X n =0 (2 n )! 2 2 n ( n !) 2 ( − k x ) n , and noting that 1 √ 2 π R ∞ 0 e − av 2 2 dv = 1 2 a − 1 2 w e get Z ∞ 0 1 − e − k v 2 /ρ M 1 √ 2 π e − v 2 / 2 dv = M X m =0 M m ( − 1) m 1 √ 2 π Z ∞ 0 e − v 2 2 (1+2 km/ρ ) dv = 1 2 M X m =0 M m ( − 1) m 1 + 2 k m ρ − 1 / 2 = 1 2 M X m =0 M m ( − 1) m ∞ X n =0 (2 n )! 2 2 n ( n !) 2 ( − 1) n 2 k m ρ n = 1 2 ∞ X n =0 ρ − n (2 n )! 2 n ( n !) 2 ( − k ) n M X m =0 M m m n ( − 1) m = 1 2 ∞ X n =0 ρ − n (2 n )! 2 n ( n !) 2 ( − k ) n A ( M , n ) = 1 2 ∞ X n = M ρ − n (2 n )! 2 n ( n !) 2 ( − k ) n A ( M , n ) . = ρ − M , 32 therefore ρ − M . = Z ∞ 0 M Y i =1 1 − e − min i k i v 2 /ρ 1 √ 2 π e − v 2 / 2 dv ≤ Z ∞ 0 M Y i =1 1 − e − k i v 2 /ρ 1 √ 2 π e − v 2 / 2 dv ≤ Z ∞ 0 M Y i =1 1 − e − min i k i v 2 /ρ 1 √ 2 π e − v 2 / 2 dv . = ρ − M whic h conclud es the lemma. B Pro of of T heorem 3 W e sh o w that for an y P > 0, C U , C ( P ) > C U , NC ( P ) and C L , C ( P ) > C L , NC ( P ) whic h consequen tly pro ves the theorem. First, we r emark that p log(1 + a p ) is non-decreasing in p since ∂ ∂ p C U ( a ) = ∂ ∂ p p log 1 + a p ≥ 0 . The inequalit y ab o v e holds b ecause for the function f ( u ) △ = log u − (1 − 1 u ), f (1 ) = 0 and for u ≥ 1, ∂ f ( u ) ∂ u = 1 u − 1 u 2 ≥ 0 and therefore f ( u ) ≥ 0 for u ≥ 1. Therefore, C U ( P ) as given in (19) is non-decreasing in the probabilit y Pr( S t = S r = 1). By using Lemma 2 it is concluded that for sufficien tly large SNR C U , C ( P ) > C U , NC ( P ), wh ic h in turn, establishes the result f or the upp er b ound. F or the lo w er b ound , as sho wn in (25), for sufficiently large SNR , P C ρ ( ¯ e r | ¯ e t ) ≥ P NC ρ ( ¯ e r ) as sho wn P C ρ ( ¯ e t , ¯ e r ) P NC ρ ( ¯ e t ) P NC ρ ( ¯ e r ) > P C ρ ( ¯ e t ) P NC ρ ( ¯ e t ) , or equiv alent ly Pr C ( S t = S r = 1) Pr NC ( S t = S r = 1) > Pr C ( S t = 1) Pr NC ( S t = 1) . (43) Therefore, for the low er b ound w e get th at for su fficien tly large SNR C L , C ( P ) = Pr C ( S t = S r = 1) log 1 + P Pr C ( S t = 1) − 1 T c > Pr C ( S t = S r = 1) × log 1 + P Pr C ( S t = S r =1) Pr NC ( S t = S r =1) Pr NC ( S t = 1) − 1 T c (44) > Pr NC ( S t = S r = 1) 33 × log 1 + P Pr NC ( S t = 1) − 1 T c = C L , NC ( P ) , (45) where (44) follo ws from (43) and the transition f r om wher e (44) to (45) follo ws from the fact that p log (1 + a p ) is increasing in p . C Pro of of T heorem 4 As shown in App endix B, C U ( P ) is non-decreasing in Pr( S t = S r = 1). By using Lemm a 3 it is readily ve rifi ed that f or the function C U ( P ) C U , OC ( P ) > max C U , C ( P ) , C U , NC ( P ) . F or th e lo wer b oun d, we deplo y th e same app roac h as in the p r oof of Theorem 3 an d fir st sho w that Pr OC ( S t = S r = 1) Pr C ( S t = S r = 1) ≥ Pr OC ( S t = 1) Pr C ( S t = 1) , (46) and Pr OC ( S t = S r = 1) Pr NC ( S t = S r = 1) ≥ Pr OC ( S t = 1) Pr NC ( S t = 1) . (47) The ab o ve inequalities can b e p ro ven by substituting and manipu lating the expansions of Pr C ( e t ) and Pr OC ( e t ) giv en in T heorems 1 , 2 and the expansions of Pr C ( ¯ e t , ¯ e r ) and Pr OC ( ¯ e t , ¯ e r ) (26) and (27). After establishing the ab ov e inequalities, the last step is similar to that of Ap p endix B. References [1] J. Mitola, “Cognitive ra dio: An integrated agent a r c hitecture for softw are defined radio ,” Ph.D. disser- tation, KTH, Sto c kholm, Sweden, December 2000 . [2] S. Haykin, “ Cognitiv e radio: Bra in-empow er e d wir e less communications,” IEEE J. Sele ct. Ar e as Com- mun. , vol. 23 , no. 2, pp. 2 0 1–220, F eb. 2005. [3] N. Devroy e, P . Mitran, and V. T ar okh, “Achiev able ra tes in co g nitiv e radio channels,” IEEE T r ans. Inform. The ory , vol. 52, no. 2, pp. 1 813–1827 , May 200 6. [4] A. Jovicic and P . Viswanath, “Cognitive radio: An information-theoretic pe rspective,” Submitte d to the IEEE T r ans. Inform. The ory , May 2 006, Av aila ble online at h ttp://a rxiv.org/P S cache/cs/p df/ 0 604/ 06041 07v2.p df . [5] N. Devroy e a nd V. T arokh, Co gnitive Wir eless networks . Springe r , 2007, ch. F undamental Limits of cognitive radio netw or ks. 34 [6] A. Goldsmith, S. A. Jafar, I. Mar ic, and S. Sriniv a s a, “Bre aking spectr um g ridlock with cognitive radios: An information theoretic p ersp ectiv e,” 200 8, to Appea r. [7] A. Sahai, N. Hov en, a nd R. T a ndr a, “Some fundamen tal limits on cognitive radio,” Av a ilable online at ht tp:// www.eecs.ber keley .edu/ ∼ sahai/Pap ers/cognitive radio preliminary .p df . [8] D. Slepian, “ Some comments on detection of Gaussia n signals in Gaussian noise,” IEEE T r ans. In fo rm. The ory , vol. 4, pp. 65–6 8, June 1958 . [9] N. A. R. Pr ice, “Detection theory ,” IEEE T r ans. Inform. The ory , vol. 7 , pp. 13 5–139, July 1961 . [10] R. Etkin, A. Parekh, and D. Tse, “Sp ectrum sha r ing for unlicensed bands,” IEEE J. Sele ct. Ar e as Commun. , vol. 25, no. 3 , pp. 51 7 – 528, April 200 7. [11] Q . Z hao, L. T o ng , A. Swami, and Y. Chen, “ Decen tralized cognitive MA C for opp ortunistic sp ectrum access in ad ho c netw orks : A PODMP framework,” IEEE J. Sele ct. Ar e as Commun . , v o l. 25, no. 3, pp. 589–5 99, April 2007 . [12] M. Ag arw al and M. L. Honig, “Sp ectrum sharing on a wideband fading channel with limitted feedback,” in Pr o c. IEEE Int’l Conf. on Co gnitive R adio Oriente d Wir eless Networks & Commun . (Cr ownCom) , Aug. 2007, pp. 72–7 6. [13] L. La i, H. El-Gama l, H. Jiang, and H. V. Poo r, “Cognitive medium ac cess: Ex ploration, exploitation and comp etition,,” Su bmitte d t o IEEE/A CM T r ans. N etworki ng , Av ailable online at h ttp://www.pr inceton. edu/ ∼ llai/cog nitive radiov11.p df . [14] S. A. Ja far and S. Sriniv a sa, “Capac it y limits of cognitive radio with distributed and dynamic sp ectral activity ,” IEEE J. Sele ct. Ar e as Commun. , vol. 2 5, no. 3, pp. 52 9–537, April 20 07. [15] G. Ganesa n and Y. Li, “Co op erative sp ectrum sensing in cognitive radio, pa r t I: Tw o user netw ork s ,” IEEE T r ans. Wir eless Commun. , vol. 7, no. 7, pp. 2204 – 221 3, June 20 07. [16] ——, “Co oper ativ e sp ectrum sensing in c ognitiv e radio, part I I: Two user netw or k s,” IEEE T r ans. Wir eless Commun . , vol. 7, no. 7, pp. 2 214 – 22 22, June 200 7. [17] G. Ganesan, Y. Li, B. Bing , a nd S. Li, “Spa tiotemporal sens ing in cog nitive radio netw orks,” IEEE J. Sele ct . Ar e as Commu n . , vol. 26, no. 1, pp. 5–12 , Jan. 2008 . [18] A. Sendanoris, E. Er k ip, and B. Aazhang , “User co oper ation diversit y part I: System des cription,” IEEE T r ans. Commun. , vol. 51, no. 11, pp. 192 7– 1938, Nov. 20 0 3. [19] ——, “Use r co oper ation diversit y part I I: Implemen tatio n asp ects and per formance analysis,” IEEE T ra ns. Commun . , vol. 51, no. 11, pp. 193 9–1948, Nov. 2 0 03. [20] J . N. La neman, D. N. C. Tse, a nd G. W. W ornell, “ Coop erative diversity in wireles s net works: Efficie n t proto cols and outage behavior,” IEEE T r ans. In fo rm. The ory , vol. 50, no . 1 2, pp. 3 062– 3080, Dec. 2004. 35 [21] T. Hunter and A. Nosr a tinia, “Diversity through co ded co op eration,” IEEE T r ans. W ir eless Commun. , vol. 5, no. 2, pp. 28 3 – 289 , F eb. 2006. [22] A. Bletsas, A. Khisti, D. P . Reed, and A. Lippman, “A simple co op erative diversity metho d based on net work path s election,” IEEE J. S ele ct. Ar e as Commun. , vol. 2 4, no. 3, pp. 65 9–672, Mar . 2006 . [23] A. T a jer and A. Nosra tinia , “Opp ortunistic co op eration via relay selection with minimal informa tion exchange,” in Pr o c. IEEE Int’l Symp. on Info. The ory (ISIT) , Nice, F rance , June 20 07. [24] Y. Chen, Q. Zha o , V. Kr ishnam urthy , and D. Djonin, “T r ansmission scheduling for optimizing sensor net work lifetime: A sto c hastic shortest path approachs,” IEEE T r ans. Signal Pr o c essing , vol. 5 5, no. 5, pp. 2294 –2309, Ma y 20 07. [25] M. K. Simon a nd M.-S. Alouini, D igital Communic ation over F ading Channels: A Unifie d Appr o ach to Performanc e Analysis . New Y ork: Wiley , 2000. 36
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment