Hiding Information in Retransmissions
The paper presents a new steganographic method called RSTEG (Retransmission Steganography), which is intended for a broad class of protocols that utilises retransmission mechanisms. The main innovation of RSTEG is to not acknowledge a successfully re…
Authors: ** Wojciech Mazurczyk, Miłosz Smolarczyk, Krzysztof Szczypiorski – Warsaw University of Technology
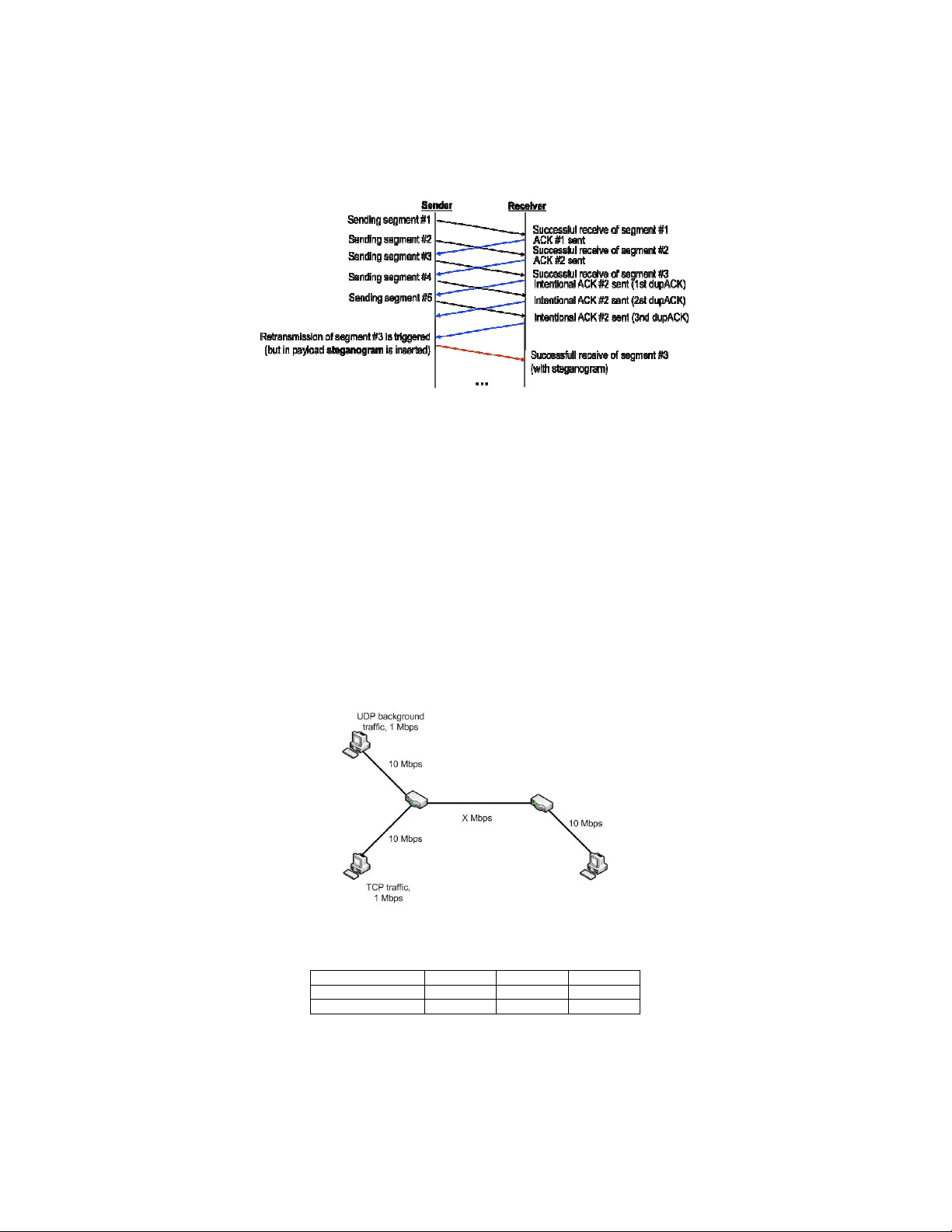
Hid ing I n fo rmation in Retransm iss io n s Wojc iech Mazu rczyk, Miłosz Smo larczy k, and K rzysz t of Szc zypiorski Wa rsaw U ni vers it y of Tec hnology , I nstitute of Te leco mm un i c ations Wars aw, Po land, 00- 665 , ul. No wow iejs k a 15/19 Abstra c t. T he pa per pr esents a new steganog r ap hic m ethod calle d RSTEG (Retra nsmissio n Steg an og raphy), which i s intended fo r a b roa d class of protoco ls that utilises retra nsm ission me chanism s. T he m ain i nnov atio n of RSTEG i s to n ot ac knowledge a successf ull y recei ve d p acke t in order to intent ionally in vo ke retra ns m issio n. T he retransm it ted packet carries a st egan ogram instea d of user data in the pay l o ad field. RST EG i s presen t ed in the broa d context of network ste g ano grap hy, an d th e util isa t ion o f RS T E G for T C P (Tr ansport Co ntrol Pro toc o l) retransm iss i o n me chanism s is d esc ribe d in de t ail. S i m ulation results are als o presen t e d with the m ain aim t o mea sure a nd c ompa re the steg anog raphic band width of the propo sed me t hod for diffe rent T CP re tr an smi ssio n mecha nis ms a s we ll as to dete r m ine the influe nce o f RST E G on the netw ork retransm issions leve l . Key w ord s: RST EG, stega n o graph y , retransm ission mec hanis m 1. Classification o f Network Steganography a nd R ela ted Wor k Comm un i cation network steganography is a metho d of hid ing sec r et data in the norma l data t rans missio ns of users so th at it id eally cannot be detected by thir d pa rties. Ma n y new m ethods ha ve bee n prop os ed an d analysed, including th os e in [22], [14] and [1 3]. Netwo rk steg anography methods may b e v iewed as a threat to network sec urit y , as they may be used as a too l for co nfidential info rmation leak a ge, for ex ample. Fo r thi s rea son , it is impo rt an t to identif y po ssi b i lit ies fo r cov ert co mm unication, as kno wledge o f inf orma t ion hiding pro ce d ures may be used to deve l op countermeas ures. Netw ork stega nograp h y m ay be classified [11] into th ree b road gro ups (Fig. 1): - Stegan og ra p hic m ethods that mo dify pack ets (M P) , includ i ng netwo rk protocol heade rs or pay l oa d fields. - Stegan og ra p hic m et hod s t ha t mo dif y th e struct u r e o f pack et stream s (MS) , fo r exam ple, by affecting the order of packe ts, mo difyin g inter- packet delay or introdu cing inten t iona l losse s. - Hy b rid stegano gr aph i c me t hods (HB) t hat mod i fy bo t h t he co ntent o f p acke t s and t heir timing and orde ri ng . Fig. 1 A netwo rk stegano graphy c l assif icati on Exam ples o f me thods for each g r ou p and their chara cteris t ic f e atures are de s crib ed in Tab l es 1-3. Ta ble 1. Exam ples and char acteristic fea ture s o f steg ano g ra p hic MP m et ho ds M P Metho ds Exam pl es o f stegano g raphic me th od s Fea tures M ethods that mo di fy pro tocol- sp ecific fields Metho ds base d on th e mo di fic ation of I P, TC P, and UDP he aders fie lds [13]. Yield rela t iv ely high steganograph i c capa cit y . Im pleme ntation and detec t ion is rela t ively straightfo rward. D rawbacks include p otential los s of pro t oco l f unctionality . M ethods that mo di fy packet pa yload Wate r ma rking algo rithm s ([4], [2]), sp eec h codec stega nograp hic t ech niques. Gene rally y i eld lo wer steg anograp hic capa cit y a nd a re h arder to im pleme nt and detec t. Drawb acks include pote ntial deterio ration of transm issi o n qualit y , e.g., if app l ied to VoIP (Vo ice over I P). M i xe d techn i ques HICC UPS (Hidden Comm unic atio n Sy ste m for Co rr up ted Netwo r ks, [20]). Offe r hi gh st eg anogr ap hic capacity , b ut the imp lementation is mo re diffic ul t than othe r me thods due to t he required low- l eve l hardwa re access. F o r th e same reason , stega nal ysis is harder to p erform . Dra wbacks i nc l ude inc r ea s ed frame error rate . Ta ble 2. Exam ples and char acteristic fea ture s o f steg ano g ra p hic MS m etho ds Exam pl es o f MS m ethods Fea tures Metho ds that aff ect the sequenc e orde r of packe ts [9]. • Se nder-rece i v er s y nchronisa ti o n r equire d. • Lower stega nograp hic capacity and h arde r to detec t t ha n m ethods that uti l ise proto c o l - s pe cific fields. • Straig htf o rward imp lementation . • Drawba c ks include d elay s t ha t may affect transm ission quality . Metho ds t ha t mo dify inte r- p a cket dela y [1]. Metho ds that in tr o d uce intentio nal l osse s by skipping seque nce n umbe r s at the sender [ 17]. Ta ble 3. Exam ples and char acteristic fea ture s o f steg ano g ra p hic HB metho ds Exam pl es o f H B me th od s Fea tures LACK ( Lo st Audio PaCK ets Stegan ography ) [12]. • Modify both packets a nd th eir tim e de pendenc ies. • High stega nographic c ap ac i t y . • H ard to dete ct. • Sender-receive r synch r onisatio n not required . • Str a i gh t forw ard imp lementation . • D raw back s include a los s i n co n nectio n qu ality . RST E G (which is p rese nted in details in this p ape r). I n t he co ntext of the ab ov e c lass i fic ation of ne twor k steg ano g r aphy me t ho ds, we p ropo se a ne w h yb rid me t ho d calle d RST E G (R etransm ission Steganograp h y), wh i ch i s intende d for a broa d cla ss o f protoc o l s th at uti lis e retra nsm i ssion mec h anisms . T h e ma in i nnov atio n o f RS T E G is to not ackn owl e dge a successf ull y rec eived packe t in order to intentio nall y in vo ke retran s mis sion. The retr ansmitted pack et of user data then carr ies a stegan ogram i n the pay l oa d fi eld. Currently , there are fe w propo s ed steganog raphic metho ds that co uld i nco rporate retransmissio n m echanisms . Handel et al. [6] pro posed a ste gano graphic m ethod fo r Eth ernet C SMA /CD (Ca rrier Se nse Mu ltiple Acce ss/Collision Detec tion), which use s a retransm ission mec hanism a fte r c o l lisions. I f f r ame collisions occ ur, then a jam signal is issued, and t he senders back off fo r a ran d om a mo unt o f time. I n o rder to se nd a single hidden bit, a back -off delay of either z ero or a maxim u m value is used so t hat the h idden data rate is on e bi t pe r frame . The rece i ver extracts a stega n ogr am by an alys in g the o rder of the f r ame arriv als a f ter collisions. K rätzer et al. [8] pro po sed a steg anograp hic me tho d fo r t h e 802 .11 pro toco l , which tr an sm i ts h i dden info rm a t ion throug h th e retransm issi on of frame s. T h e sen der enco des hi dde n d ata by du plica ti ng fr ames transm itted t o a rece i ver . T he receive r deco des the hidden data by detecting t he duplic ations . T he rest of the paper is dedicate d to presen tin g the RSTE G st eganog r aphic m ethod. Sec tion 2 describes RST E G in d e t ail as well as comm u nicatio n scenarios in whic h i t m ay be used. Pe rforman ce i ssu es involve d in using th e me thod are also discussed. I n Section 3, res ults f r om an app l icatio n of RS T E G to a T C P protocol sim ulation are p r ese nted. Se ction 4 co ncludes our wor k and indicates po ssib l e future re sea r ch. 2. General Idea of RSTEG and Communication Scenarios RST E G can b e used for all pr oto cols that utilise r etransm issions at d iff erent layers o f OS I R M . A ge neric retransm ission m echanism bas ed on timeo u ts is p rese nted in Fig. 2. RST E G m ay be app lied a l so to other retransm ission me chanism s i n T CP, s uch as FR/R (Fast R et ransm i t a nd Rec overy) [18] o r S ACK (Se lectiv e Ack n ow led ge ment) [10]. Fig. 2. G eneric re t ran smission me ch an i sm b ased on timeo u ts (l eft) ; RST E G (right) I n a simp li f ied situation, a t y pic al protocol that use s a retrans mission m e cha nism based on tim eouts oblig ates a r ec ei v er to ackno wledge each rec eived packet. Whe n the pack et is not succes s f ull y rece ived, n o ackno wledgme nt is sent afte r t he timeo ut e xpires, and so the pac ke t is retra nsm it ted (Fig. 2). As me nt ioned in Sec t ion 1, RST E G u ses a retransm ission mec hanism to ex ch ange st e ganog r am s. Both a sender and a r e c ei v er a r e aware of the stega nograph i c procedure . T he y r eliably e x change packets durin g their co nnection; that is, they transfe r a f il e . At som e point during the c onnection af ter successf ull y receiv ing a packe t , the receive r intenti o nall y does not issue an ack nowle d gment me ssa ge . In a no r ma l si tuation, a sen der is oblig ated to retrans mit the lost pa cke t when the t im eframe within whic h p acket ack nowle d gemen t s hould have b een rec eived ex p i res. I n th e co nte xt of RS T EG, a sender re place s orig in al pay l oa d wi th a stega nogram instead of sending the s ame packe t ag ain. When t h e r etransm itted pack et re ache s th e receiver, he/she ca n th en extract hidden inf ormatio n ( Fig . 2). Fo u r poss i ble hidden comm unication sce nar i os m ay be consi de red in the c ontex t of RSTEG (Fig . 3). Note that for f ew scena ri o s p resented in Fig.3 p acke t sender and pa cket re ceive r are not tak i ng pa rt in hidde n comm u nicatio n. Only a part o f their c omm u nicatio n path is utilised by interme diate nod es, whic h are SS (Steg anogram Sender) and SR (Steg anog ram Receiver) . Sc enario (1) is mo st commo n: the se nder, who i s Stegano gram Sender ( SS), and the rec eive r, who is the Steganogram Rece i ver (SR), enga ge in a co nnection and s im ult a neously excha n ge stegano grams . T h e co n ve r sation path is the s ame as the hidde n data p at h. RST EG for this scen ario wo rks as fo l lows: (1-1) En d-to -end co n nection is estab lished be tween send er and recei v er, and the packe ts are exc h ange d. (1-2) At som e point, the rec eive r does no t ack n owle dge a succes sfu lly ac qu ired p ac k et. (1-3) Afte r t he retra ns m issio n t imer expires, the pa cket i s retr a nsm i tted, and in it s pay load, a stega n og ram is inserted. (1-4) T h e recei v er is ab le to disting uish a re t ransm itt e d p acket, so w hen it r eac hes the rece i ve r, he/she ex tr acts a steg an ogram . I n t he next three s cenar ios (2-4 in F ig. 3 ), only p art of t h e conn ect e d e nd-to- end pa th is u sed fo r hidden comm u nicatio n as a result of actions underta ken by interme diate nodes; t he se nder a nd /or rec eiver are, in princ i p l e, unawa re of t he steg anograph i c data excha n ge. I n sce nar i o ( 2), one interm ediate node is invo l ved in h i dde n com m unica t ion with t he orig i nal pa cket sender (SS). T he steganog r aphic proce dure fo r thi s sce na r io wo r ks as follo ws: (2-1) While the con nectio n l asts, o ne packet is selec ted by the sender and is ma r k ed f o r hid de n comm u nicatio n. (2-2) When mod i f ied packet reac hes the SR, t he SR co p i es a p ay l oa d and d rops the pac k et . Now b oth the SS and SR kno w that the retran smis sion of t his pack et will be us ed fo r c ov ert c omm unicati on . (2-3) When the retransm ission tim eout e xpires , the pa cke t is re tra ns m it ted b y th e sende r, and its o r iginal payloa d is r ep l aced with a steg anog ra m . (2-4) When th e m odified retransm i tted packe t reach es the SR, t he SR ex t racts a st ega n og r am an d i nser t s t he orig inal pay l o ad that was cop ied ear l ier and then s ends it to the rece i ve r . Fig. 3 H i dden comm unication scena rios for RST E G I n scenar i o (3), th e re is also one interme diate node in vo l v ed i n h i dden comm unicatio n (the SS), and the SR is loc ated in the rec eive r. T he steganogr aphic proce dure for this sc enario w o r ks as fo llows: (3-1) While t he co n ne ction l asts, o ne packe t is se l ected by the interm ediate node (SR) an d is ma r ked for hidden comm unication . (3-2) When t he pa cket succ ess fully r eac h es t he rece i ve r (S R ), the SR intentio nall y does n ot issue an ackno wledgement. (3-3) When the retran smis sion timeo ut e x pires, the pac ket i s retran s m i tted by the se nder. (3-4) When the retran smitte d packet rea ches SS , its pay load is rep lace d wi th a steg anogram. (3-5) When the m odi fie d, retransm i tted pa cket reac hes SR, th e SR e xtracts a steg an ogram . I n scenar i o (4), t wo inter m ediate nodes are i nv olved in hi dde n communica tion and are util ising ex isti ng end- to-en d connection be t ween sende r and rec ei ve r. RST E G for this scen ari o wo r ks as f o l lows: (4-1) While the con nectio n l asts, o ne pack et is selec ted by t he SS and is m arked for hidde n c omm u nicati o n. (4-2) When the m od i fie d pack et reac hes t he SR, the SR copies the payload a n d drop s t he pac ket. No w both the SS and SR k now that retransm ission of this pa cket will be used fo r covert comm unic ation. (4-3) When the retran smis sion timeo ut e x pires, t he p acke t i s retran s m i tted by the sender. (4-4) When retra ns m it ted pack et reache s the SS, its pay load is rep lace d wi th stega nog r am. (4-5) When the mo d ifie d retransm itt ed packet rea ches t he SR, the SR ex tracts the steganogr am and inserts the orig inal pay l o ad that was cop ied ear l ier and send s it to the re ce i ve r. Of the a bove scen ario s, sce n ario (1 ) i s e asie st to i m plemen t ; scen ario s (2) - ( 4) re quire con t rol o ver the int erm ediate n ode us ed for hidden comm u nication and th at all pa cke ts tra ve rse throu gh it duri ng connection . On the other hand scen arios (2), ( 3) an d, in particula r, (4) are har der to detec t than ( 1). Th e t y pical loc ation of the node use d f o r stega nal y si s is nea r t he sen der or rec eive r o f the packets . Thu s, in scena rios i n whic h on l y p ar t of the com municatio n path is used, it m ay be ha rder to uncov er. T h e pe r formanc e of RS T E G depen ds o n m any facto rs, such as the details of the com m unication procedure (in pa rt icu l ar the size of t he packe t pay l oad, t he rate at which segm ents are gen erat ed , an d so on). No r eal-world stega nograp hic m eth o d i s per fect; wha t ev er the m ethod, t he hidden info r m ation ca n be potentially discovered . I n ge n eral, t he m ore hidde n inf orma t ion is in se r ted into the data s tr eam , th e g r ea t er the c han ce that it will be detec ted, fo r e xamp l e, by scanning the data flow o r by s ome other stegan al ysis me thods. M oreover , t he mo re packe ts that are use d to send c ov ert d a ta , t he h i g her the retransm ission rate w i ll b e, which allows easie r de t ection. T hat is why the p roc edure of inserting hi dden da t a ha s to be ca refull y cho s en an d co ntrolled in order to m inim ise the chan ce of detec t ing inser ted data. Additio n all y , p acket los ses in tr o d uced b y the networ k m ust be c aref ull y m onitore d. Becau se RSTEG use s leg i timate t raff i c , it thus increa ses ove rall pack et l o sses. To ensure that the t o t al pack et loss introduced b y the netwo rk and by RS T E G i s n ot too high if comp ared with othe r connec t ion s in the sam e netwo r k , the l ev el of th e retransm issions used for steg an og r ap hic p u rposes m ust b e c ontro l led and d y n a m icall y adapted. 3. RSTEG in TCP Protoco l: F u nctioning, Detecti on a nd Experimental Results Ap ply i ng R ST E G to TC P is the natural cho ice f o r I P networks , as a v ast amou n t of I nternet t raff ic ( abo ut 80 - 90%) is bas ed on this pro tocol. For T C P, th e f ollo wing retransmis si on m ec hanis m s are define d: • RTO (Re transm is sion T i meo uts) [1 5] in which se g m ent loss d etec ti on is b ased o n RT O ti m er expir ation. Res ults f rom [16] sho w that 60-88 % of al l retra nsm i ssi ons o n t he In t ern et wer e caused by RT O m echanism. I n RT O , a se gment is considere d lo st i f the rece i v er does not rec eive an acknowle dgement seg ment (ACK) afte r t he spec i fie d p eri o d of time , after which it is retrans m it ted. T h e RT O ti m er value varie s i n T CP implem entatio n a cro ss diffe r en t o perating systems, and it de pe n ds ma i nl y o n R T T (Ro und Trip Tim e) and its v ariation. If the RTO time r is set to too low o f a v alue, i t may cau se too m any s pu ri ou s retr a ns m i ssion s; other wise, the sender will b e waitin g too lo ng to retransm it a lost seg me nt, which m ay cause t hro u ghp u t de crease . • FR/R (Fa st Ret r an sm i t/R ecove ry) is b as ed on de t ecting duplicate ACKs (that i s, ACKs with th e sam e acknowle dgement numbe r). A rece i ve r ackno wledges all seg me nts de l ive red in ord er . Whe n segme nts arri v e out of order, th e rec eiv er mu st not i ncr ease t he ack n owledgem ent numbe r so as to avo id data gaps but i nste ad s e nd s ACKs w i th unchan ged ack nowledgem ent numb er v alues, which are calle d dup l icate ACK s (du pA CKs). Usually , a segm ent is c onsidere d l o st afte r the re ceip t o f three d up l icate ACKs. Issuing duplic at e ACK s by the receiv er is often a result of o ut-of-o rder segment deliv er y . If t he number of dup licate ACK s that tri gg ers retra ns m issio n i s too sma ll, it can ca use t o o m an y r etransm i ssio ns an d ca n d eg r ade netw ork perfo rmance . • SAC K (Se l ectiv e Acknow l edgem ent) i s bas ed on Fast R e t ransm it/ Rec ove ry. I t uses an exte nded ACK optio n that c ontains blo cks ed ge s t o deduce which receive d blo cks of data are non-co n tiguous . Wh en retransm ission is t rigg ered, on l y m issing segmen t s are retransm it ted. Th is fea ture o f SACK dec r eases netwo r k load . 3.1 RSTEG Inser ti on and Extra ct i n g Proce d ures f o r TCP T h e intentional retrans m i ssions due to R STEG should be kept at a reasonable level to a vo i d detection. To ac hie ve this go al, i t is n ece ssary to de t ermine the av erage n umbe r of n a t ural re transm issi on s in T CP-ba sed Intern et t raff ic as we ll as to k now ho w intentiona l ret ransm issions affec t the netwo r k retransm i ssi on rate. Usua l l y netwo r k re tr an s m i s sions a r e caused by network ov erl o ad, exc essive delays or reorde ri ng o f p ack ets [16], and their num ber is es t im ated to acc ount for up to 7% of all Interne t traf fic [16, 7, 3] . RST E G can be a pplied t o all retran smis sion m echanism s prese nted above . I t r eq uires mo di fica tion to b oth a sender and a receiv er. A sender shou ld co ntr ol the insertion proce dure and de cide whe n a rece i v er shou l d invok e a retransm i ssio n. T h e sender is also respo nsible to keep the numb er of retransm issi o ns at a n on -suspicio us l ev el. T h e r ec ei v er’s ro le is to detec t when the send er indic ates tha t intent ional retr an sm i ssion sh ould b e trig gered. T h en, when the r etransm itted segm ent arrives , t he rece i ve r shou l d be ab le to extrac t the st eg an ogram . T h e send er mus t be able t o m ark segme nts selecte d for h idden comm unica t ion (that is, r etransm ission request segm ents) so t he rece i ve r wou l d k now which segm ents r e trans m issio ns should b e i nvoked and which segm ents will con t a i n steg anog r am s. Ho we ver , m a rked TCP segm ent shou l d no t dif fer from t ho se sen t durin g a con nectio n . T h e follo win g proced u re for ma r k ing sender segm ents is pr oposed . L et us ass um e t hat the sende r and rec eiver share a secre t Steg-Key ( SK ). For each fra gment chose n f o r stega nogr aphic c omm unicati on , the follo wing h ash func ti o n ( H ) is used to calc ulate the I dentify i n g Se quence ( IS ): (3-1) No t e th at Seque nce N umbe r and TCP Check sum denote v alu e s from t he c hosen T C P hea der fields in s e gm ents, || is the bits con ca tenation functio n, a nd C B i s a con t rol bit t ha t allows t he r e ceiv er to distinguish a r etrans m ission request segm ent fr om a segment with a steg an ogra m . Fo r e ve r y TCP segme nt use d fo r hi dden comm unic ations, the resulting IS will hav e differ ent v alue due to the var iety of v alues in th e Seque nce Number an d TCP Chec ksum heade r fie l ds. All IS bits (or o nl y selecte d one s) are distri b ut e d by t he sen der a cro ss a segm ent’s pay l oad field in a predef ined m anner. The rec eive r must analy se each incom i ng segme nt; b ase d on S K and va lues from t he T C P heade r, the rec eive r calculate s two v alues of IS , n am el y , o ne w i th CB = 1 and one with C B = 0 . Th en the rec eiver checks if a nd which IS is p resent inside the r ece i v ed segm en t . Pr oblem s may a r ise when the segm en t t hat i nfo r m s the rec eiver of a n ecessit y to in v oke an intentio nal retransm ission (which contains user data together with the IS ) is lost d ue to n etwo rk conditions. I n t ha t cas e, a norm al retransm ission i s trig gered, and th e rece i v er i s n ot awa re t hat the segm ent with h idd en d ata will b e sen t . Ho wever, in this ca s e , the sender believe s that r etransm ission was i nvoked in ten t ionally by the receiver, a nd so he/she issues the segm ent wit h steg a nogram and t he IS . I n t his scenario , user data will be lost, and t he cov er co nnection m ay be disturbed. I n ord er to addres s th e situation i n which the receiv er reads a segm ent with a n unexp ected st e ganogram , the rec eiver sh ould no t ack n owle d g e re ceptio n o f this segme n t until he/she rece i ves the segm ent with u ser data. When t he ACK is not sent to t he sender, anothe r retra nsmission is in v ok ed. T he se nder is awa re of the data delive ry fa ilure, but he/she do es no t kn ow which segmen t to retransm it, so he/she first issues a segm ent with user data. If delive r y confirmatio n is still m i ssing , t hen the se gm ent with steg anogram is sen t . The situation continues until t he se nder rece i v es the cor rect ACK . T his m echa ni sm of corr ecting ste ga n o gram netw ork losses is il lus trated in Fig. 4 . Fo r e xamp l e, con s ider the sc enario in which we invok e 0. 5% intenti ona l retransm issions . I f 5% is lost, it me ans that the abov e -describ ed me ch an i sm w i ll take place only fo r 0 .025% of steg anog r am segmen t s, and thus it will be use d rarely . Fig. 4 RT O-bas ed RSTEG s eg me nt recove ry exam ple T h e abov e RS T E G m ay be app lied t o the retra nsm issi on mech anisms pre s en t ed abov e as follows : • RTO-ba sed RSTEG: T he sender m arks a segment selecte d fo r hidden comm unic a t ion by di stributing the I S ac ross i ts pa y l oa d. After su ccessf ul segme nt de l i ve r y , the r eceive r does no t iss ue a n A C K me ssa ge . When the R T O ti m er expire s, t he sende r sends a stegan ogram inside t he retrans m i tted segm ent’s pay l o ad (see Fig. 2). The rece i ve r extr acts the st eg an ogram and se nds the app ro p r iate ackno wledgement. • FR/R-bas ed RSTEG: T he sender mark s t he seg ment selecte d fo r hidden com mu nicati o n by distributing the I S acro ss i ts pay l oad. After suc ce s s ful segm ent deliv ery, t he rece i v er starts to issue duplica te A CK s t o trig ger retransm i ssion. Whe n the ACK counter at th e sen der side ex ceeds specif ied ) || || || ( CB Check sum TCP Number Sequence SK H IS = va lue, the seg ment is retran smitte d (see F i g . 5). Pay load of the retransm itt ed se gment co ntai ns a stega nogram . The rece i ve r extrac ts the steg anogram and se n ds an app ro p r iate ackno wledgeme nt. • SACK ba sed RSTEG: T he sce nario is exactly the sa m e a s F R/R, but in the cas e of SA C K , it is poss ible tha t m an y segmen ts are retransm itt e d b ecause of po tential n o n -co ntiguou s d a t a deliv ery . Fig. 5 FR /R-b ased RSTE G 3.2 An Exper i m ental Eva l ua ti on o f t h e I n fl u ence o f RST EG on TCP Co nnec ti ons Sim ulations w ere generate d u sing ns- 2 Sim ulator ve r . 2.33 [21] with the fo l low ing mo di ficatio ns. T he adaptatio n of ns-2 Si m ulator to RST E G required onl y modifica ti o n s of th e rece i ver . The receiv ing func t ion alit y of th e se gm ents wa s m odif ied to in tentiona lly no t issue AC Ks (in the case of RTO ) or to no t i ncre ase th e ackno wledgement numbe r (in t he cas es of FR/R and SA C K). T h e decision regarding which segm ent wo uld be treated as lost is m ade random l y according to a parame t e r that sp ecifies the intentiona l retrans m i ssio n s fr equ ency . T h e netwo r k topo l o gy was m at c h ed to fit I nternet traff ic retransm issio n st atistics. Sim ulation scen ar io con sists of two traff ic sources (T CP and UDP) and the bo t tleneck link be tween inte r me diate d ev i ces suc h as rou t ers (see Fig. 6). Each traf fic source is con nected with a 10 Mbp s l ink to the in term ediate d ev ice. The rec ei ve r is also co nnected to it s rou t e r w ith 10 Mbp s link. The UDP traffic so urce and t he b andwidth of the link b etwee n int erm ediate de vices ( X ) are cho sen to in trod uce cer tain netwo rk retra ns m issio n prob abilities ( NR P ); d ue to netwo rk ov erload, NR P is abo ut 3 or 5% . Ta ble 4 su mma rises the ba ndwidths of the bo ttl e neck links that are used for sim ulati on p ur poses . Fig. 6 RST EG sim ulation scena rio Ta ble 4 . T h e ch ose n bandwidth fo r bottlenec k lin k ( X ) for diffe rent T CP retra ns m issio n m echanisms t o ac hie ve 3% and 5% N R P NR P / T C P retrans. RTO FR/R SA C K 3% 1.985 Mbps 1.985 Mbps 1. 985 Mbps 5% 1.8 Mbps 1.8 Mbps 1. 9 Mb ps T h e sim ulation res ult s are ba sed on c omp aring retransm issions for a netwo rk wit h R ST EG ap plied to T CP traffic as w ell as fo r a netwo r k w ithout RST E G ret ran smissions. Network traff i c was measured f or 9 minutes, starting af ter 1 m in ute fr om t he beg inning of the sim u lation. Th e R ST E G in tent ional retrans missio n prob abili ty ( IR P ) was cha nged f r om 0 to 5% with in t erm ediary steps at 0%, 0.5%, 1% , 2% , 3%, 4% and 5% . I n th e abov e simula ti o n scena rio, two p ara me ters were mea su red f or RS T E G : • Stegano graphic Bandw idt h ( S B ) is de fined as t he am ount of the stega nogr am transmitte d using RST E G du ring o ne s econ d [Bps] . Fo r different retrans m i ssion mec hanisms i n t he TCP protoco l, this pa ram et er can be use d to e stimate whi ch mec h anism y i elds the high est S B and is mos t suitable f r om a RST E G util isation point o f v iew. S B depends ma i nly on the size o f the segm en t an d the numb er o f in tentional retra nsm issi o ns i nv oked , and so it m ay be e xpressed as (3-2) where N S – the n um ber of s eg me nts used fo r h idden com mu nicati on S S – the size o f segment pay l oad T – the duratio n of t he co nn ectio n • Retransm i ssions Differenc e ( R D ) is def i ne d a s the d i ffer ence be tween r etransm issio ns i n a netwo rk afte r app l y in g RST E G and in a netwo rk befor e app l y i ng RS TEG . T his pa r amete r ca n be used to es ti m ate the influen ce that RST EG has o n the T CP retransm i ssio ns rate. T hus, it c an il lus trate ho w to ch oo se the co rr ect intentiona l retransm i ssio n probability t o l im it the risk of detec tion. Fo r examp le, if the network retransm i ssio n p rob ability is 5%, 1% of in tentiona l retra ns m i ssion s are int roduce d by R ST E G , whic h cause s the ov erall retra nsm ission rate to increa se to 7% , with R D = 2% . T h e results fo r TCP retr ansmissio n m echanisms when NR P = 3% and NR P = 5% are presente d in Fig. 7- 10. 0 0.5 1 1.5 2 2.5 3 3.5 4 4.5 5 0 1000 2000 3000 4000 5000 6000 7000 8000 9000 I R P [% ] S B [B ps ] RT O FR/R SACK Fig. 7 S B f or T CP retra ns m i ssi on mec hanism s when NR P = 3% and IR P v aries 0 0.5 1 1 .5 2 2.5 3 3.5 4 4.5 5 0 1 2 3 4 5 6 7 8 I R P [% ] R D [% ] RT O FR/R SACK ] [ Bps T S N S S S B ⋅ = Fig. 8 R D fo r T CP retransm ission mec hanisms whe n NR P = 3% and IR P v aries 0 0.5 1 1 .5 2 2.5 3 3.5 4 4.5 5 0 1000 2000 3000 4000 5000 6000 7000 I R P [% ] S B [B ps ] RT O FR/R SACK Fig. 9 S B f or T CP retra ns m i ssi on mec hanism s when NR P = 5% and IR P v aries 0 0.5 1 1.5 2 2.5 3 3 .5 4 4.5 5 0 1 2 3 4 5 6 7 I R P [% ] R D [% ] RT O FR/R SACK Fig. 10 R D fo r TCP re t ran s miss ion mecha nis m s when NR P = 5% and IR P va ries T ables 5 and 6 sum ma ri se the sim ul atio n results. Ta ble 5. Sim ulati o n r esu l ts when NR P = 3% RTO FR/R SACK IR P [% ] S B [Bps] σ SB R D [ % ] σ RD S B [Bps] σ SB R D [ % ] σ RD S B [Bps] σ SB R D [ % ] σ RD 0.5 1 454 112.5 1. 25 0.0971 1 530 92.8 1. 25 0.129 2 1 530 9 2. 8 1. 29 0.0778 1.0 2 821 164.3 2. 45 0.1356 2 999 141.1 2.54 0. 1302 2 999 141.1 2. 54 0 .1183 2.0 4 802 183.4 4. 26 0.150 3 5 395 171.3 4. 67 0.177 3 5 395 171.3 4. 62 0.144 5 3.0 5 982 96.4 5. 54 0. 0754 7 113 1 06.6 6. 12 0.1384 7 113 10 6.6 6. 17 0 .0896 4.0 6 306 100.7 6. 21 0.091 1 8 128 157.3 7. 03 0.111 9 8 128 157.3 7. 18 0.135 5 5 6 320 81.5 6. 72 0. 0800 8 865 62.0 7 . 73 0.0830 8 865 62. 0 8. 07 0.0754 Ta ble 6. Sim ulati o n r esu l ts when NR P = 5% RTO FR/R SACK IR P [% ] S B [Bps] σ SB R D [ % ] σ RD S B [Bps] σ SB R D [ % ] σ RD S B [Bps] σ SB R D [ % ] σ RD 0.5 5 457 677 0. 77 0. 0680 5 474 694 0 . 75 0.0666 6 119 1 020 0 . 96 0 .0938 1.0 6 068 1 288 1. 46 0.092 9 6 277 1 497 1. 61 0.073 6 7 119 2 020 1. 90 0.101 9 2.0 7 169 2 389 2. 75 0.1186 7 699 2 919 3 . 15 0.147 3 8 726 3 627 3. 44 0 .1092 3.0 7 848 3 068 3. 62 0.101 4 8 692 3 912 4. 28 0.098 2 9 998 4 899 4. 71 0.132 3 4.0 8 173 3 393 4. 24 0.0881 9 406 4 626 5 . 14 0.139 0 10 88 6 5 787 5. 67 0 .1115 5 8 304 3 524 4. 74 0.1216 9 863 5 083 5 . 81 0.110 1 11 54 9 6 450 6. 50 0 .0929 Bas ed o n the re sults pre sented a bov e, one can conclude t ha t fo r low inte nti o nal retransm ission probab il it y va lues (0 – 0.5% for NR P = 5 % a nd 0 – 1% fo r N R P = 5% ), the re sulting S B va l ue s for a ll re transm issio n me ch anism s are sim il ar, and theref ore, it is not impo rtant wh ich of th e retra nsm i ssio n m echa nis m s (that is, RT O , FR/R or SACK ) is u sed. The highe r IR P is, the gre ater is the diff erence in steg anog raphic bandw i dth. I t i s n ot surpr i sing that R ST EG b ase d o n SACK a nd FR/R m echani sm s y ield hig her ste gano graphic bandwidth than RT O- bas ed RS T EG, as the forme r are mo re ef fectiv e retrans m i ssion me chanism s. T h at i s, und er the sam e IR P , they achiev e gr eater S B . Ho we ve r, hig her s teg an og raphic b a ndwidth f or RST EG b ase d o n SACK a nd FR / R me ch anism s incre ases the retransm ission d i ff erence v alues in co mp arison to RTO- based R ST EG. T h is m a y increa se t he lik elihoo d of detectio n of R ST EG. Th us, retra nsm issi o n mec hanisms f o r which R D va lues are lowe r are fav ourable in terms of steganalysis . RT O- b ased RSTEG achieved the lowe st s tega nograp hi c b andwidth but sim ultane o u sly i ntrod uced th e low est R D . Co nsidering this a nalys is and kno win g that RT O is the mo st freque nt retransm ission mec hanism used for T CP on th e I nternet (60-88% ) sug g ests that RT O-base d R STEG is a fav ourable ch o i ce for T C P p r otocol i f th e ri sk of disclosure m ust be m i ni m ized. If det ectio n issues are om it ted, SACK-b ased RSTE G shou l d b e chosen to max i m ise the a mount of steg anogram t hat is sen t . Rega r ding RTO-base d RSTE G and its ap prop r iateness b ased o n T CP pr otocol, Fig . 10 an d 11 pre sent a compa rison of S B and R D when IR P = 3% and IR P = 5% . 0 0.5 1 1 .5 2 2.5 3 3.5 4 4.5 5 0 1000 2000 3000 4000 5000 6000 7000 I R P [% ] S B [B ps ] RT O: NR P =3% RT O: NR P =5% Fig. 1 1 S B f or RT O -ba s ed RST E G as IR P va ries 0 0.5 1 1 .5 2 2.5 3 3.5 4 4.5 5 0 1 2 3 4 5 6 7 I R P [% ] R D [% ] RT O: NR P =3% RT O: NR P =5% Fig. 12 R D fo r RTO-base d RS T E G as IR P v aries Res ults from Fig. 11 an d 12 show that an i ncr ease i n the nu mber of retransm issi ons intro duced in a networ k lowers the i nf l uence t ha t RST E G has on netwo rk retransmissions . That is, they ar e harder to detec t , al tho ugh the stega nograp hic ban dwidth is low er. A n increa se in ne twork retra ns m i ssio ns m eans that it is easie r to h ide int en tiona l retra nsm i ssion s among unin tent ional retransm issions. 3.3 RSTEG D ete ction Retra nsmis si o n s in I P networks are a “ natura l ph enom enon” , a nd so int en tiona l retra nsm issi on s in troduc ed by RST E G are not easy t o de t ec t if th ey are kept at a rea sonab l e lev el. T he ex pe ri menta l resu l ts pre sente d h ere show that RTO-b ased RST EG is a favo urable T CP retransm issi on m echa nis m i n term s of st eg analysis. More over , i f the se nder can obs erve the ave r age r e t ransm ission rate in a netwo r k, then h e/she can also choo se an IR P so as to li m it th e ri sk o f detectio n. One p ossib le detectio n metho d is st atistica l steg an al ys i s ba sed o n the n etwo rk retra ns m issi on rate. I f fo r ce rt ain T CP connection s, the retra nsm issi on rate is sig ni fic antly h igher than fo r othe rs, then pote ntial usa ge of RST E G may be detected. Such a steg ana l ysis m ethod in vo l ve s the mo nitoring of T C P retransm issi o n r a t es fo r a l l co nnections in a sub- n etwork . Ho wev er, there is a solution th at makes the steg analysis of RST E G as a pplied to T CP pro t ocol eas ier to pe r form . T he p r opose d s teganaly sis me t ho d m ay be imp lemented wit h a pas si ve w arden [ 5] ( o r some other netwo rk node r espo n sible for steg anograp h y u sage d etec ti o n ). Pas si v e w ard en m ust be ab le to mo nitor all the T CP tr affic and for each TCP co nnection it must store sent segme nts for the g i v en perio d of time , which depe n ds on the retrans miss ion time r i. e. pass i ve warde n m ust stor e t he segme nt until it is ack n o wled g ed b y th e rece i ve r so t he retra nsm issio n i s no t po ssible any mo re. When there is a retransm issio n i ssue d, p assi v e warde n com pares orig inall y sent seg me nt wit h retransm it ted one a nd if the pay l o a d differs RSTEG i s detecte d and the segm ent i s droppe d. H oweve r , it sho ul d be noted th at t he r e may b e ser iou s p erf o r ma n ce issues i nv olved if passive warde n mo nit o rs all the TC P con nections and m ust store a l arg e numbe r of the segm ents. On the other hand , it mu st be no t e d t hat ba s e d on results p rese nted i n [19 ] up t o 0.09 % (1 in 1100) of T CP segm ents may b e corrupted due to network deli ve r y . As a r e sult , an imp erfect copy of a s egme nt may be sen t to the rece i ve r. Afte r rec eption o f t he in v alid segm ent, v erificatio n is p erfo rmed ba sed on the v alue in the TCP Chec ksum fi eld, and the need to retransm it is signalle d to the sender. Thus , in t his scenario , t he o riginal segm ent and th e retransm i tted one wil l dif fer fr om each other. O cc ur rences of t his ef fect in I P networ ks m ask the use of RST E G . T hus, t he stega nalys i s metho d s describe d abov e may fail, becau se the warden will drop retransm i tted segm ents when diffe rence s amo n g segments ar e disco vered, a n d as a result, user data wil l be lo st. I t i s worth noting th at ev en for th e l o w rates o f i nt en tiona l retransm ission (0. 09% ) t ha t are required to ma sk RST E G , if we a ss ume t hat the T CP s egmen t s are g e nerated at a rate of 200 se gmen t s/s, with the con nectio n lasting 5 minutes and the segm ent’s pay l o ad size being 1000 by tes, t hen t his results in S B = 180 B ps, which i s a rather high ba n dwidth, con sidering the other st e ga nograp hic me thods p resented in Sec ti o n 1. T o summa r ise, meas ures t o detect RST E G have bee n p r op osed and can b e uti lised, but if t he rate of int en tiona l retra nsm i ssion s is ve r y low, th e n the dete ctio n of hidden comm u nic ations m a y be diff i cu l t. 4. Conclusions and Future Wo r k RST E G i s a h y b r id n etwo rk steganog raphic method based o n the classif ication p r e sented earlier in this pape r . T h e stega nographic ban dwidth i t can provide may b e comp arable for me t hods th at mod i fy packets onl y , and i ts ba ndwidth i s high er than that o f me th od s that only modify th e structure o f pack et streams. I n this pap er, we ha v e foc us ed on pre senting the f ram ework guiding t his ste ga nographic metho d and hav e show ed h ow it m ay be applied and detecte d in t he c ontex t of T C P protocol, which m ay be use ful in dev eloping detec ti o n mea sures . A mo re deta i led eva l uation of RS T E G performa nce for other p r ot o cols with r e transm issio ns and in o t her laye rs of the T C P/ IP stack is nee ded. T he simula tion results show that in order to m i nimis e t he risk o f dete ction, RTO-b ased retra ns m ission s should be used by RSTEG, and in tent ional retransm i ssions sho uld be kep t to a re asonab l e le ve l. Howeve r, in orde r to maxim i se stegano graphic ba ndwidth, S ACK -ba sed RST EG is mo re app r op ri a te. Applic ation of RST E G to TCP pro tocol is a log i cal choice for I P networks, but a s sho w n i n this pap er, it can be detected, especially i f intenti o n al r e t ransm issio ns are issued exc essi ve l y . Neverthele ss, R STEG ca n be als o used fo r other pro t ocols t ha t util i se retra nsm ission mec h anisms , in partic ular for wireless netwo rks. We believ e that RST E G in this en v ironmen t may be ha rder to de t ect; ho wever, t h i s claim requires a mo r e detailed an alys i s. Analy t ical a nd expe r i m ental results co ncerning this issu e wil l be presented by the authors in for thcom ing papers. REFE R ENCES 1. Berk , V., G i a ni, A ., Cy be n ko, G.: D ete ction of Co ve rt Channel Enco ding in Netwo rk Packe t Delays, Tec h. Rep . T R 2005-5 36, Dep artment of Comp uter S ci e nce, Da rt mo uth C ollege , Nov . 2005 , URL : htt p : //www .i sts .dartmo uth.edu/li brary /1 49.pdf 2. Che n, B. , Wo rnell, G . : Quantiza tion index m od ulation: A cla ss of pr ovab l y good m eth o d s fo r digital waterm arking an d in form ati on e mbedd i ng , I EEE T rans. I n fo. The ory , v ol. 4 7, no . 4 , pp . 1423–1443 , May 2001. 3. Che n, C., Mang ru lka r, M ., R am os, N., and Sark ar, M.: Trends in TCP / I P Retransm issions an d Rese t s, Tec hnical Report, URL : http://www- cse . ucs d.edu/classes/wi01/cse 222 /pro jects/repo rts/tcp-flag s - 13. pdf 4. Co x, I . , K i lian, J. , L eig hton, F., Sham oo n, T . : Secu r e sprea d spec t rum wa termark i ng for m ulti med i a, I EE E T ransac t ions on I mage Processing 6(12): 1997, pp . 1673– 168 7 . 5. Fisk , G ., Fisk, M., Pap ad opo u l os , C ., Neil, J., E lim i na t ing stega nography i n I nternet tr aff i c wi th activ e warde ns, 5th I nternatio nal Wo r kshop o n Info r ma t ion Hiding , Le cture No t es in C o mp uter Scie nc e, 2578, pp.18–35, 2002. 6. Ha ndel, T ., San dfo rd, M.: Hiding Data in the OSI Netw o rk Model, Proc. 1st I nternational Wo r k sh o p. Info r mation H iding, 1996 pp . 23 –3 8. 7. In t ern et Traffic Rep ort URL : http://www . inte rnettraff icr eport.com /30 day . ht m 8. Kr ätzer, C ., Dittm ann, J. , L an g, A., Kühne, T.: WL AN Steganog raphy: a First P ractical Rev iew, Proc . 8th A CM Multim edia and Se curit y Wo rkshop., Septembe r 2006. 9. Ku n dur, D., Ah san, K., 2003: Practic al I nternet Stega nography : Data H i di ng in I P, Pro ceedings of the Texa s Workshop on Se curity of I n form atio n S ystems, Apr il 2nd, 2003 10. Mathis, M., Mahdav i, J., Floy d, S., Rom an ow, A. : TC P Selective Acknowledgme nt Optio n s, I E TF RFC 2018, Octo be r 199 6 11. Maz urcz y k, W., Lubac z, J., Sz czyp i orski, K.: H iding Data in VoI P I n Proc of: Th e 26th Army Scie nc e Co nference (ASC 2008) , Or lando, Florida, U SA, Dec embe r 1-4 , 2008 12. Maz urcz y k ,W., Szc zyp i orsk i , K., Ste ganog r aphy of VoIP St reams , I n: R. Mee rsm a n a nd Z. T ari (Eds.) : OTM 20 08, Part II - L e cture No tes in Com puter Science ( LN CS) 5332, S pringe r- V erlag B e rlin Heide l b er g , Pr oc. o f T he 3rd I nterna tional Sy mposium o n I nforma ti on Security (I S ' 0 8), Mon t errey , Mex ico, Novembe r 10-11, 2008, pp . 100 1-1018 13. Murdoc h, S., Le wis, S .: Em b edding Cov ert Channe l s into T C P/ I P, Proc . : 7th I nt ernatio n al W orkshop on I n fo r mation H iding 2005, L NC S: 3727, 2005, str . 247-26 1, Springer- Verlag, Heidelbe rg 14. Petitco l as, F., Anders on, R . , Kuhn , M.: I nf o r ma tion Hiding – A S urvey : IEEE Sp ecial I ssue on Prote ction of Multim edia Con t ent, July 1999 15. Pos tel, J.: Tr ansmissio n Control Pro t ocol, I E T F RFC 793, Se ptember 1981 16. Rewask ar, S., Ka ur, J., Sm i th, F.: A Per fo rm a nce Stud y of L o ss Detectio n/Recovery in Real-wo rld TCP Imp le men tations, I n P r o c. of the I EEE I nternatio n al Conf erence o n N etwork Pro t ocols, ICN P 2007, Octob er 16- 19, 2007, Bei jing, China, I SBN 1-4244- 1 588- 8, pp. 256-265 17. Servetto , S., Vetter li, M.: C o mm unication U sing Phantom s: Cov ert Channe l s in t he I nternet. I n Proc . of I EE E I nterna t ion al Sympos iu m on I n formation T h eory, June 2001. 18. Stevens, W.: T C P Slow Sta rt, Co ngestion A vo idance, Fa st Retransm i t, a nd Fast R e cove r y Algorithms, I E TF RFC 2001 , Jan uary 1997 19. Stone, J., Pa rt ridg e, C.: When the CRC and TCP che ck sum disa gree. I n Proc. o f SI GCOMM 2 000 , Sep t embe r 2000 20. Szczy piorski, K .: HI CCUPS: Hidden Com m unication S ystem for C orrup ted Netwo r ks. I n Pro c. of: ACS' 2 003, October 22 - 24, 2003, Miedzy zdr oje, Po land, pp. 31- 40 21. T h e Netw ork Simula t o r Webp age: http://www.isi .edu/nsnam / ns/ns-b uild. htm l 22. Zand er, S., A rm itag e, G., Branch P . : A S urvey o f Covert C ha nnels and Counterme asu r es in Com puter Netwo r k Proto cols. I EE E Comm unica t ion s Surveys & Tutorials, 3rd Quarte r 2007, Volum e: 9, I ssu e: 3, pp. 44-57, I SSN: 1553-87 7X
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment