Diversity-Multiplexing Tradeoff in Fading Interference Channels
We analyze two-user single-antenna fading interference channels with perfect receive channel state information (CSI) and no transmit CSI. We compute the diversity-multiplexing tradeoff (DMT) region of a fixed-power-split Han and Kobayashi (HK)-type s…
Authors: Cemal Akcaba, Helmut Boelcskei
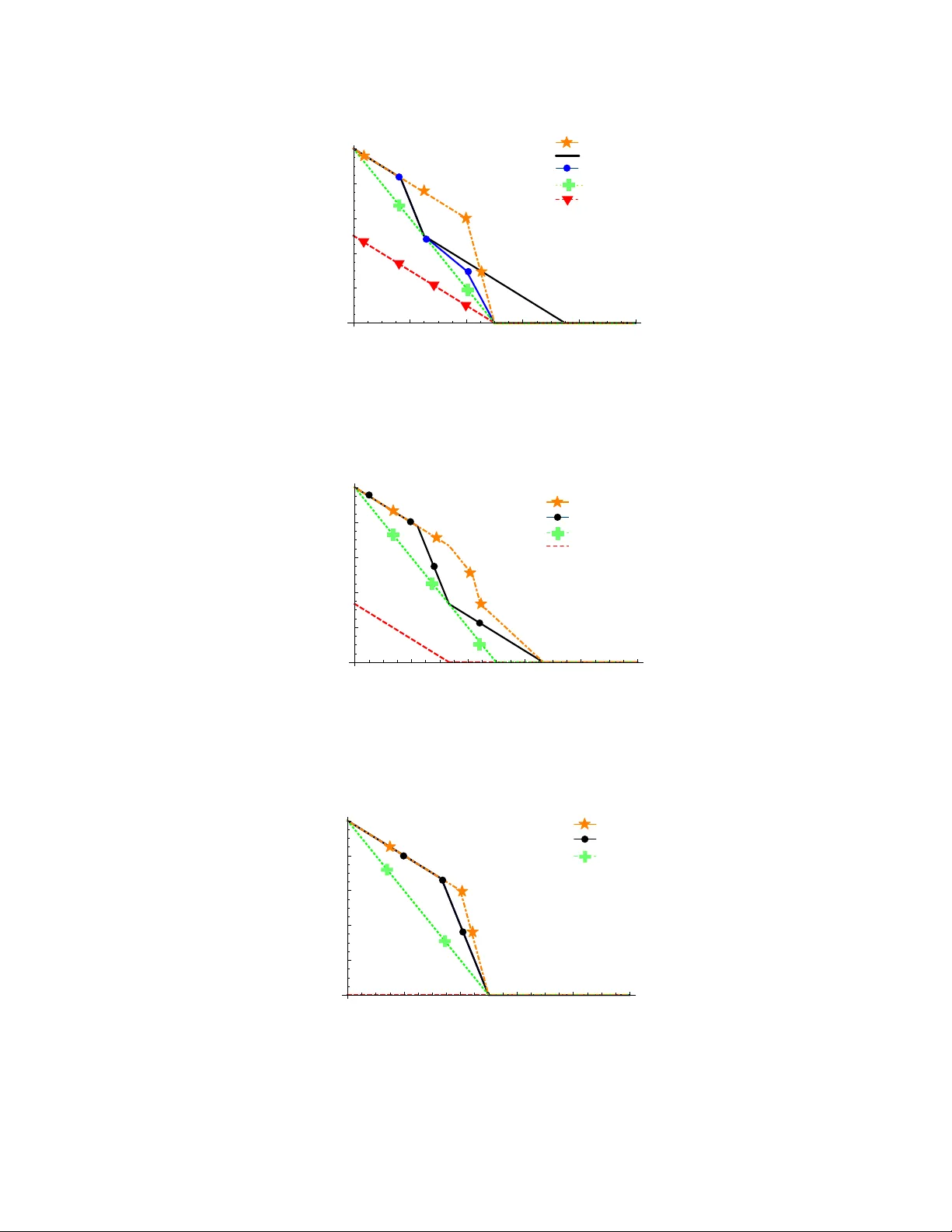
1 Di v ersity-Multiplexing T radeof f in F ading Interference Channels Cemal Akc ¸ aba and Helmut B ¨ olcskei Abstract W e analyze two-user single-antenna fading interference channels with perfect receive channel state information (CSI) and no transmit CSI. W e compute the div ersity-multiplexing tradeoff (DMT) re gion of a fixed-po wer-split Han and K obayashi (HK)-type superposition coding scheme and provide design criteria for the corresponding superposition codes. W e demonstrate that this scheme is DMT -optimal under moderate, strong, and v ery strong interference by sho wing that it achieves a DMT outer bound that we deriv e. Further , under v ery strong interference, we show that a joint decoder is DMT -optimal and “decouples” the fading interference channel, i.e., from a DMT perspectiv e, it is possible to transmit as if the interfering user were not present. In addition, we sho w that, under very strong interference, decoding interference while treating the intended signal as noise, subtracting the result out, and then decoding the desired signal, a process known as “stripping”, achieves the optimal DMT region. Our proofs are constructive in the sense that code design criteria for achieving DMT -optimality (in the cases where we can demonstrate it) are provided. I . I N T R O D U C T I O N The interference channel (IC) models the situation where M unrelated transmitters communicate their separate messages to M independent recei vers, each of which is assigned to a single transmitter . Apart from a few special cases [ 1 ], [ 2 ], [ 3 ], the capacity region of the IC remains unknown. Recently , for the interference-limited regime, Etkin et al. [ 4 ], [ 5 ] characterized the capacity region of the IC to within one bit. Later , T elatar and Tse [ 6 ] generalized this result to a wider class of ICs. The The authors are with the Communication T echnology Laboratory , ETH Zurich, 8092 Zurich, Switzerland (email: { cakcaba | boelcskei } @nari.ee.ethz.ch). Part of this paper will appear in the Proc. of the IEEE Int. Symposium on Information Theory (ISIT), Seoul, Korea, Jun. 2009, av ailable: http://arxiv .org/abs/0903.2226v2 March 8, 2022 DRAFT 2 techniques used in [ 4 ], [ 5 ], [ 6 ] rely on perfect channel state information (CSI) at the transmitter . Shang et al. deriv ed the noisy-interference sum-rate capacity for Gaussian ICs in [ 7 ], while Raja et al. [ 8 ] characterized the capacity re gion of the tw o-user finite-state compound Gaussian IC to within one bit. Annapureddy and V eera v alli [ 9 ] showed that the sum capacity of the two-user Gaussian IC, under weak interference, is achiev ed by treating interference as noise. In [ 10 ], Akuiyibo and L ´ ev ˆ eque deriv ed an outer bound on the di versity-multiple xing tradeof f (DMT) region for the two-user IC based on the results of Etkin et al. [ 5 ]. In this paper , we in vestigate the achie vability of this outer bound and we analyze the DMT region realized by a fixed-po wer-split Han and K obayashi (HK)-type superposition coding scheme. For the sake of simplicity of exposition, we restrict our attention to the two-user case throughout the paper . Furthermore, we assume that the recei vers ha ve perfect CSI whereas the transmitters only know the channel statistics. W e would like to point out that the schemes used in [ 5 ] make explicit use of transmit CSI and so does the scheme in [ 10 ], which immediately implies that the results reported in [ 10 ] serve as an outer bound on the DMT region achiev able in the absence of transmit CSI, the case considered here. The contributions in this paper can be summarized as follo ws: • For general interference lev els, we compute the DMT region of a two-message, fixed-po wer- split HK-type superposition coding scheme and provide design criteria for the corresponding superposition codes. For the case where the multiplexing rates of the two transmitters are equal, we demonstrate that the two-message, fixed-po wer-split HK-type superposition coding scheme achiev es the optimal DMT of the two-user IC under moderate , str ong , and very str ong interfer ence . For asymmetric rates, i.e., when the multiple xing rates of the two transmitters are not equal, we prov e that the two message, fixed-po wer-split HK scheme is also DMT -optimal in the str ong and very str ong interfer ence regimes. • Under very str ong interfer ence , a joint decoder , i.e., a decoder that jointly decodes the trans- mitted messages of both transmitters at each receiver , “decouples” the fading IC, i.e., from a DMT perspectiv e, the achie vable performance is equi valent to that of a system with two isolated single-user links. • For very str ong interfer ence , we show that a stripping decoder , which decodes interference while treating the intended signal as noise, subtracts the result out, and then decodes the intended signal is DMT -optimal. W e furthermore show that the optimal DMT can be achie ved if each of the two transmitters employs a code that is DMT -optimal on a single-input single-output March 8, 2022 DRAFT 3 (SISO) channel. Notation: The superscripts T and H stand for transpose and conjugate transpose, respectiv ely . x i represents the i th element of the column vector x , and λ min ( X ) denotes the smallest eigen v alue of the matrix X . I N is the N × N identity matrix, and 0 denotes the all zeros matrix of appropriate size. All logarithms are to the base 2 and ( a ) + = max( a, 0) . X ∼ C N (0 , σ 2 ) stands for a circularly symmetric complex Gaussian random variable (R V) with variance σ 2 . f ( ρ ) . = g ( ρ ) denotes exponential equality of the functions f ( · ) and g ( · ) , i.e., lim ρ →∞ log f ( ρ ) log ρ = lim ρ →∞ log g ( ρ ) log ρ . The symbols ˙ ≥ , ˙ ≤ , ˙ > , and ˙ < are defined analogously . System model: W e consider a two-user f ading IC where two transmitters communicate information to two receiv ers via a common channel. The fading coef ficient between transmitter i ( i = 1 , 2) and recei ver j ( j = 1 , 2) is denoted by h ij and is assumed to be C N (0 , 1) . T ransmitter i ( T i ) chooses an N -dimensional codew ord x i ∈ C N , k x i k 2 ≤ N , from its codebook, and transmits ˇ x i = √ P i x i in accordance with its transmit power constraint k ˇ x i k 2 ≤ N P i . In addition, we account for the attenuation of transmit signal i at receiv er j ( R j ) through the real-v alued coefficients η ij > 0 . Defining y i and z i ∼ C N ( 0 , I N ) as the N -dimensional recei ved signal vector and noise vector , respecti vely , at R i , the input-output relations are giv en by y 1 = η 11 h 11 ˇ x 1 + η 21 h 21 ˇ x 2 + z 1 (1) y 2 = η 12 h 12 ˇ x 1 + η 22 h 22 ˇ x 2 + z 2 . (2) Setting η 2 11 P 1 = η 2 22 P 2 = S N R and η 2 21 P 2 = η 2 12 P 1 = S N R α with α ∈ [0 , ∞ ] simplifies the exposition of our results, and the comparison to [ 5 ] and [ 10 ]. The resulting equiv alent set of input-output relations is y 1 = √ S N R h 11 x 1 + √ S N R α h 21 x 2 + z 1 (3) y 2 = √ S N R α h 12 x 1 + √ S N R h 22 x 2 + z 2 . (4) W e assume that both recei vers kno w the signal-to-noise ratio (SNR) v alue S N R and the parameter α , and R i ( i = 1 , 2) kno ws h i = [ h 1 i h 2 i ] T perfectly , whereas the transmitters only know the channel statistics for the channels h ij ( i, j = 1 , 2) , the SNR value, and the interference parameter α . The data rate of T i scales with SNR according to R i = r i log S N R , where the multiplexing rate r i obeys March 8, 2022 DRAFT 4 0 ≤ r i ≤ 1 . As a result, for T i to operate at multiplexing rate r i , we need a sequence of codebooks C i ( S N R , r i ) , one for each S N R , with |C i ( S N R , r i ) | = 2 N R i code words { x 1 i , x 2 i , . . . , x 2 N R i i } . In the follo wing, we will need the multiplexing rate vector r = [ r 1 r 2 ] T . P erformance metric: The error probability corresponding to maximum-lik elihood (ML) decoding of T i at R i under the assumption that the correctly decoded interference T j has been remov ed is denoted by P [ E ii | h i ] for i, j = 1 , 2 and i 6 = j . The corresponding av erage (with respect to (w .r .t.) the random channel) error probability is P ( E ii ) , E h i { P [ E ii | h i ] } . The notation x j i → x k i designates the ev ent of mistakenly decoding the transmitted codeword x j i for the codew ord x k i . The average (w .r .t. the random channel) error probability corresponding to decoding of T i at R i incurred by a particular communication scheme χ is denoted by P ( E χ i ) for i = 1 , 2 . Throughout the paper , as done in [ 10 ], we use the performance metric P ( E χ ) = max { P ( E χ 1 ) , P ( E χ 2 ) } . The DMT realized by a communication scheme χ is then characterized by d χ ( r ) = − lim S N R →∞ log P ( E χ ) log S N R . (5) As discussed in [ 11 ], [ 12 ], the recei ver that minimizes the error probability for each T i is the individual ML r eceiver at R i for i = 1 , 2 , which we define next. Definition 1: An individual ML r eceiver for T i at R j for i, j = 1 , 2 treats the signal from T k for k = 1 , 2 , k 6 = i , as discrete noise with known structure (i.e., codebooks) and carries out an ML detection of the message of T i [ 11 ], [ 12 ]. In the following, we denote the error probability of an indi vidual ML receiv er for T i at R j by P E I M L ij for i, j = 1 , 2 . The corresponding av erage (w .r .t. the random channel) error probability is denoted by P ( E I M L ij ) , E h j P E I M L ij . The DMT realized by the strate gy of employing an individual ML r eceiver for T i at each recei ver R i for i = 1 , 2 is giv en by d I M L ( r ) = − lim S N R →∞ log max P ( E I M L 11 ) , P ( E I M L 22 ) log S N R . (6) Since the individual ML r eceiver minimizes the error probability for each T i at R i for i = 1 , 2 , we hav e that the DMT d I M L ( r ) is an outer bound on the DMT realized by any communication scheme χ , i.e., d I M L ( r ) ≥ d χ ( r ) . (7) March 8, 2022 DRAFT 5 I I . A C H I E V A B L E D M T F O R J O I N T D E C O D I N G A simple achiev able rate region for the IC is obtained by having each recei ver perform joint decoding of the messages from both transmitters. Hence, there are no private messages, i.e., there are no messages that should only be decoded at one recei ver , and the messages of both transmitters are said to be public . W e formally define the joint decoder or joint ML decoder for IC next. Definition 2: A joint ML decoder for IC at R j ( j = 1 , 2 ) carries out joint ML detection on the messages from both transmitters ( T i for i = 1 , 2 ). For the joint ML decoder for IC at R j , one does not declare an error if the estimate of the signal from T i does not match the transmitted signal from T i for i, j = 1 , 2 and i 6 = j . The error probability of this receiv er is denoted by P E J D j . Then, P E J D j is the probability that only T j or both T i and T j for i, j = 1 , 2 and i 6 = j are decoded incorrectly . The corresponding average (w .r .t. the random channel) error probability is denoted by P E J D j , E h j P E J D j . The achiev able DMT of the joint ML decoder for IC is characterized next. Theor em 1: The DMT corresponding to joint decoding at each receiv er is giv en by d J D ( r ) = min i =1 , 2 , 3 d J D i ( r ) (8) where d J D i ( r ) = (1 − r i ) + , for i = 1 , 2 (9) d J D 3 ( r ) = (1 − r 1 − r 2 ) + + ( α − r 1 − r 2 ) + . Denote j ∗ = arg min i =1 , 2 , 3 d J D i ( r ) . Let Γ i ( r ) = [ γ 1 i ( r ) γ 2 i ( r )] T be functions 1 such that d J D j ∗ ( r ) = d J D i (Γ i ( r )) for i = 1 , 2 , 3 . If a sequence (in SNR) of codebooks with block length N ≥ 2 satisfies k ∆ x i k 2 ˙ ≥ S N R − γ i i ( r )+ , (10) λ min ∆ X ij (∆ X ij ) H ˙ ≥ S N R − γ 1 3 ( r ) − γ 2 3 ( r )+ (11) for all pairs of codewords x n i i , x ˜ n i i ∈ C i ( S N R , r i ) s.t. x n i i 6 = x ˜ n i i , x n j j , x ˜ n j j ∈ C j ( S N R , r j ) s.t. x n j j 6 = x ˜ n j j for i, j = 1 , 2 and i 6 = j , where ∆ x i = x n i i − x ˜ n i i , ∆ x j = x n j j − x ˜ n j j , and ∆ X ij = [∆ x i ∆ x j ] , 1 W e note that the functions Γ i ( r ) might not be unique. March 8, 2022 DRAFT 6 and λ min (∆ X ij (∆ X ij ) H ) denotes the smallest nonzero eigen value of ∆ X ij (∆ X ij ) H , for some 2 > 0 , then P E J D obeys P E J D . = S N R − d J D ( r ) . (12) Pr oof: W e first identify a lower bound on P E J D , which constitutes an upper bound on the DMT of the joint ML decoder for IC , and then sho w , using an appropriate upper bound on P ( E J D ) , that the SNR exponents of the upper and lower bounds on P ( E J D ) match at high SNR. Hence, the upper bound on the DMT of the joint ML decoder for IC is achiev able. W e define the outage ev ents corresponding to decoding T i at R i (in the absence of a signal from T j ) and to jointly decoding T i and T j at R i for i, j = 1 , 2 and i 6 = j by O J D i 1 , { h i : I ( x i ; y i | x j , h i ) < R i } (13) O J D i 2 , { h i : I ( x i , x j ; y i | h i ) < R 1 + R 2 } . (14) W e define an outage ev ent at R i for the IC as O J D i , 2 [ k =1 O J D ik (15) for i = 1 , 2 . W e would like to point out that the definition of the outage event in (15) is different from the corresponding outage e vent definition in multiple access channels (MA Cs) [ 11 ], [ 13 ] as the outage e vent corresponding to decoding of T i at R j is absent in (15) . W e note that only T j being decoded in error at R i for i 6 = j , although being a standard error event for the MA C, is not (and should not ) be defined as an error e vent for the IC. As long as the decision on T i at R i is correct, from the point of view of the IC, there is no error to be declared. The probability of outage yields a lo wer bound on the error probability of the joint ML decoder for IC . As in [ 10 ], we define the total outage probability of the IC as P O J D , max P O J D 1 , P O J D 2 . (16) Using a standard argument along the lines of [ 11 ], [ 13 ], we can see that assuming that both transmitters employ i.i.d. Gaussian codebooks results in no loss of optimality in terms of DMT 2 W e note that is allowed to be different in (10) and (11). March 8, 2022 DRAFT 7 performance. W e can therefore ev aluate (13) and (14) as O J D i 1 ( r ) , h i : log 1 + S N R | h ii | 2 < R i O J D i 2 ( r ) , h i : log 1 + S N R α | h j i | 2 + S N R | h ii | 2 < R 1 + R 2 . In the following, we will also need the definitions of the no-outage ev ents, according to ¯ O J D i 1 ( r ) , h i : log 1 + S N R | h ii | 2 ≥ R i ¯ O J D i 2 ( r ) , h i : log 1 + S N R α | h j i | 2 + S N R | h ii | 2 ≥ R 1 + R 2 with i, j = 1 , 2 and i 6 = j . W e can no w establish the asymptotic beha vior of O J D i . By the union bound, we hav e P O J D i ≤ 2 X k =1 P O J D ik ( r ) . (17) Obviously , it holds that P O J D i . = max k =1 , 2 P O J D ik ( r ) . (18) It is shown in [14] and [10] that P O J D i 1 ( r ) . = S N R − d J D i 1 ( r ) (19) P O J D i 2 ( r ) . = S N R − d J D i 2 ( r ) (20) with d J D i 1 ( r ) = (1 − r i ) + (21) d J D i 2 ( r ) = (1 − r 1 − r 2 ) + + ( α − r 1 − r 2 ) + (22) for i = 1 , 2 . W e point out that (21) and (22) define four SNR exponents d J D ij ( r ) for i, j = 1 , 2 . The outage ev ent corresponding to jointly decoding the signals from both transmitters at R 1 is identical to the outage ev ent corresponding to jointly decoding the signals from both transmitters at R 2 . Hence, the corresponding SNR exponents of the outage probabilities of these ev ents, namely , d J D 12 ( r ) and d J D 22 ( r ) , are exactly the same. The total outage probability of the IC then behav es according to P O J D = max P O J D 1 , P O J D 2 . (23) March 8, 2022 DRAFT 8 From (18), it follo ws that P O J D i . = max k =1 , 2 P O J D ik ( r ) . = S N R − min k =1 , 2 d J D ik ( r ) . (24) Hence, combining (23) and (24), we get P O J D . = max i =1 , 2 S N R − min k =1 , 2 d J D ik ( r ) (25) . = S N R − d J D ( r ) (26) where d J D ( r ) = min i =1 , 2 , 3 d J D i ( r ) (27) with d J D i ( r ) = (1 − r i ) + for i = 1 , 2 (28) d J D 3 ( r ) = (1 − r 1 − r 2 ) + + ( α − r 1 − r 2 ) + . W e note that (25) can be simplified by eliminating either d J D 12 ( r ) or d J D 22 ( r ) as explained earlier . This is precisely what we hav e done in going from (25) to (26). W ith (24) we arriv ed at a lo wer bound on the error probability of the joint ML decoder for IC at R i . This lo wer bound, by definition, giv es an upper bound on the DMT region. W e next try to find an upper bound on the error probability that has the same exponential beha vior as this lo wer bound. T o this end, consider next the error probability corresponding to the joint ML decoder for IC . W e first define the relev ant error ev ents. Let x n i i and x n j j with n i ∈ { 1 , 2 , . . . , 2 N R i } , n j ∈ { 1 , 2 , . . . , 2 N R j } ( i, j = 1 , 2 and i 6 = j ) be the code words transmitted by T i and T j , respectiv ely . The results of (joint ML) decoding of T i and T j at R i are denoted by x ˜ n i i and x ˜ n j j , respecti vely , with ˜ n i ∈ { 1 , 2 , . . . , 2 N R i } , ˜ n j ∈ { 1 , 2 , . . . , 2 N R j } for i, j = 1 , 2 and i 6 = j . W e hav e the error events corresponding to T i only and T i and T j being decoded in error at R i as E J D i 1 , { ˜ n i 6 = n i , ˜ n j = n j } (29) E J D i 2 , { ˜ n i 6 = n i , ˜ n j 6 = n j } (30) for i, j = 1 , 2 and i 6 = j . W e will also need the total error probability defined as E J D i , [ k =1 , 2 E J D ik . (31) March 8, 2022 DRAFT 9 W e denote j ∗ = arg min i =1 , 2 , 3 d J D i ( r ) . Let Γ i ( r ) = [ γ 1 i ( r ) γ 2 i ( r )] T be functions 3 such that d J D j ∗ ( r ) = d J D i (Γ i ( r )) for i = 1 , 2 , 3 . W e recall that d J D i 2 ( r ) = d J D 3 ( r ) for i = 1 , 2 , by definition. W e next find an upper bound on the probability of the ev ents E J D i 1 as follows: P E J D i 1 = P E J D i 1 , O J D i 1 (Γ i ( r )) + P E J D i 1 , ¯ O J D i 1 (Γ i ( r )) ≤ P O J D i 1 (Γ i ( r )) + P E J D i 1 | ¯ O J D i 1 (Γ i ( r )) (32) and for the e vents E J D i 2 according to: P E J D i 2 = P E J D i 2 , O J D i 2 (Γ 3 ( r )) + P E J D i 2 , ¯ O J D i 2 (Γ 3 ( r )) ≤ P O J D i 2 (Γ 3 ( r )) + P E J D i 2 | ¯ O J D i 2 (Γ 3 ( r )) . (33) W e start by deriving an upper bound on the av erage (w .r .t. the random channel) pairwise error probability (PEP) of each error e vent E J D ik for i = 1 , 2 and k = 1 , 2 . Assuming, without loss of generality , that we hav e an E J D i 2 type ev ent, the probability of the ML decoder mistakenly deciding in fa vor of the codeword X ˜ n i ˜ n j ij = [ x ˜ n i i x ˜ n j j ] when X n i n j ij = [ x n i i x n j j ] (with x n i i , x ˜ n i i ∈ C i ( S N R , r i ) and x j , x ˜ n j j ∈ C j ( S N R , r j ) , i, j = 1 , 2 and i 6 = j ) was actually transmitted, can be upper-bounded according to E h i n P h X n i n j ij → X ˜ n i ˜ n j ij io (34) ≤ E h i ( exp " − k ∆ X ij ˜ h i k 2 4 #) (35) ≤ E h i ( exp " − λ min k ˜ h i k 2 4 #) (36) = E h i exp − λ min S N R | h ii | 2 + S N R α | h j i | 2 4 (37) where ˜ h i = [ √ S N R h ii √ S N R α h j i ] T for i, j = 1 , 2 and i 6 = j and λ min is the smallest nonzero eigen value of ∆ X ij (∆ X ij ) H . 3 W e note that the functions Γ i ( r ) might not be unique. March 8, 2022 DRAFT 10 Noting that the no outage e vent ¯ O J D i 2 (Γ 3 ( r )) entails S N R | h ii | 2 + S N R α | h j i | 2 ≥ S N R γ 1 3 ( r )+ γ 2 3 ( r ) − 1 , (32) implies an upper bound on P E J D i 2 according to: E h i P E J D i 2 ˙ ≤ (38) P O J D i 2 (Γ 3 ( r )) + S N R N ( r 1 + r 2 ) exp " − λ min S N R γ 1 3 ( r )+ γ 2 3 ( r ) 4 # . Here, we used the definitions R i = r i log S N R for i = 1 , 2 and exp[ − λ min 4 ( S N R γ 1 3 ( r )+ γ 2 3 ( r ) − 1)] . = exp[ − λ min 4 S N R γ 1 3 ( r )+ γ 2 3 ( r ) ] . Gi ven that λ min ˙ ≥ S N R − γ 1 3 ( r ) − γ 2 3 ( r )+ with > 0 , by assumption, we obtain E h i P E J D i 2 ˙ ≤ P O J D i 2 (Γ 3 ( r )) + S N R N ( r 1 + r 2 ) exp − S N R 4 (39) . = P O J D i 2 (Γ 3 ( r )) (40) . = S N R − d J D j ∗ ( r ) (41) as the second term on the right-hand-side (RHS) of (39) decays exponentially in SNR whereas the first term decays polynomially . Eq. (41) follows by the definition of the function Γ 3 ( r ) . A similar analysis for the E J D i 1 -type error ev ent results in E h i P x n i i → x ˜ n i i ≤ E h i exp − S N R | h ii | 2 k ∆ x i k 2 4 (42) which, upon in voking (10) and using the f act that ¯ O J D i 1 (Γ i ( r )) entails S N R | h ii | 2 ≥ S N R γ i i − 1 , yields E h i P E J D i 1 ˙ ≤ P O J D i 1 (Γ i ( r )) + S N R N r i exp − S N R 4 (43) . = P O J D i 1 (Γ i ( r )) (44) for i = 1 , 2 . T o complete the proof, we note that E h i P E J D i ≤ 2 X k =1 E h i P E J D ik (45) ˙ ≤ P O J D i 1 (Γ i ( r )) + P O J D i 2 (Γ 3 ( r )) (46) = 2 S N R − d J D j ∗ ( r ) . = S N R − min i =1 , 2 , 3 d J D i ( r ) . March 8, 2022 DRAFT 11 Recalling that P E J D = max i =1 , 2 E h i P E J D i , we upper-bound P E J D according to P E J D = max i =1 , 2 E h i P E J D i (47) ˙ ≤ max i =1 , 2 S N R − min j =1 , 2 , 3 d J D j ( r ) (48) . = S N R − d J D ( r ) . (49) Since (49) giv es an upper bound that matches the lower bound in (26), the proof is complete. Discussion: The strategy of the joint ML decoder for IC forces us to decode the message from the interfering user T j at R i for i, j = 1 , 2 and i 6 = j together with the intended message from T i in its entirety . W e can relax this constraint and allow only part of the interfering signal T j to be decoded at R i for i, j = 1 , 2 and i 6 = j . This is precisely the idea behind the Han-K obayashi communication scheme, which we analyze in Section III. I I I . A C H I E V A B L E D M T O F T W O - M E S S A G E F I X E D - P O W E R - S P L I T H A N - K O B A Y A S H I S C H E M E S The Han-K obayashi (HK) rate region [ 15 ] remains the best known achiev able rate re gion for the Gaussian IC [ 3 ], [ 16 ]. The original HK strategy lets each transmitter split its message into two messages, allows each recei ver to decode part of the interfering signal, and uses fiv e auxiliary R Vs Q, U 1 , U 2 , W 1 , and W 2 , all defined on arbitrary finite sets. The auxiliary R V U i carries the pri vate message of T i , whereas the auxiliary R V W i carries the public message of T i destined for both receiv ers. The R V Q is for time-sharing. The general HK rate region is usually prohibitiv ely complex to describe [17]. In the following, we analyze the DMT of a two-message, fixed-po wer-split superposition HK scheme where T i transmits the N -dimensional ( N ≥ 2 ) vector x i = u i + w i with u i and w i representing the pri v ate and the public message, respectiv ely . The power constraints for u i and w i are k u i k ≤ r N S N R 1 − p i , k w i k ≤ √ N 1 − r 1 S N R 1 − p i ! so that k x i k ≤ k u i k + k w i k = √ N . Here, 0 ≤ p i < 1 accounts for the exponential order of the po wer allocated to the priv ate message. The power split is assumed fixed and is independent of the channel realizations. When both the pri vate and the public messages are allocated maximum power , March 8, 2022 DRAFT 12 we hav e k w i k 2 k u i k 2 . = S N R 1 − p i . W e emphasize that any p i < 1 constitutes a valid po wer split. W e will demonstrate later that schemes with p i < 0 yield zero div ersity order , and, hence, do not contribute to the DMT region as the priv ate message codebook is vanishing in size with increasing SNR. The case p i = −∞ corresponds to public messages only , and was treated in section II. W e assume that T i transmits at rate R i = r i log S N R where the rates for the priv ate and the public messages, respectiv ely , are S i = s i log S N R and T i = t i log S N R with r i = s i + t i , s i , t i ≥ 0 , and 0 ≤ r i ≤ 1 . The codebooks corresponding to the priv ate and the public message parts are denoted as C u i ( S N R , s i ) and C w i ( S N R , t i ) , respecti vely , and satisfy |C u i ( S N R , s i ) | = S N R N s i and |C w i ( S N R , t i ) | = S N R N t i . Clearly , C x i ( S N R , r i ) = C u i ( S N R , s i ) ×C w i ( S N R , t i ) with |C x i ( S N R , r i ) | = S N R r i . In the following, we will need the pri vate message multiplexing rate vector s = [ s 1 s 2 ] T and the SNR exponent vector p = [ p 1 p 2 ] T of the priv ate messages. Definition 3: A joint ML decoder for the two-messa ge, fixed-power-split HK scheme at R j ( j = 1 , 2 ) carries out joint ML detection on the public messages from both transmitters ( T i for i = 1 , 2 ) and the priv ate message from T j . For the joint ML decoder for the two-messag e, fixed- power-split HK scheme at R j , one does not declare an error if the estimate of the public message of T i does not match the transmitted message for i, j = 1 , 2 and i 6 = j . The error probability of this recei ver at R j is denoted by P E H K j for j = 1 , 2 . The av erage error probability of this receiv er is denoted by P E H K j , E h j { P [ E j ] } for j = 1 , 2 . W e employ a joint ML decoder for the two-message , fixed-power-split HK scheme at each R j ( j = 1 , 2 ). The SNR exponent of P ( E H K ) = max { P E H K 1 , P E H K 2 } and the conditions on the superposition codes for achie ving this SNR exponent are characterized next. Theor em 2: The achie vable DMT for the tw o-message, fix ed-power -split HK scheme is giv en by d H K ( r ) = max s , p d ( r , s , p ) (50) with the optimization carried out subject to the constraints s i + t i = r i , with s i , t i ≥ 0 0 ≤ p i < 1 , i = 1 , 2 and d ( r , s , p ) = min k =1 , 2 l =1 , 2 ,..., 6 ( d kl ( r , s , p )) March 8, 2022 DRAFT 13 d i 1 ( r , s , p ) = ( p i − s i ) + , if p j < 1 − α (1 − α − p j + p i − s i ) + , if p j ≥ 1 − α d i 2 ( r , s , p ) = (1 − r i + s i ) + , if p j < 1 − α (2 − α − p j − r i + s i ) + , if p j ≥ 1 − α d i 3 ( r , s , p ) = (1 − r i ) + , if p j < 1 − α (2 − α − p j − r i ) + , if p j ≥ 1 − α d i 4 ( r , s , p ) = ( p i − s i − r j + s j ) + + ( α − s i − r j + s j ) + , if p j < 1 − s i − r j + s j ( p i − s i − r j + s j ) + , if p j ≥ 1 − s i − r j + s j and p j < 1 − α (1 − α − p j + p i − s i − r j + s j ) + , if p j ≥ 1 − s i − r j + s j and p j ≥ 1 − α d i 5 ( r , s , p ) = 1 − 2 P k =1 r k + 2 P l =1 s l + + α − 2 P k =1 r k + 2 P l =1 s l + , if p j < 1 − 2 P k =1 r k + 2 P l =1 s l , 1 − 2 P k =1 r k + 2 P l =1 s l + , if p j ≥ 1 − 2 P k =1 r k + 2 P l =1 s l and p j < 1 − α 2 − α − p j − 2 P k =1 r k + 2 P l =1 s l + , if p j ≥ 1 − 2 P k =1 r k + 2 P l =1 s l and p j ≥ 1 − α March 8, 2022 DRAFT 14 d i 6 ( r , s , p ) = (1 − r i − r j + s j ) + + ( α − r i − r j + s j ) + , if p j < 1 − r i − r j + s j (1 − r i − r j + s j ) + , if p j ≥ 1 − r i − r j + s j and p j < 1 − α (2 − α − p j − r i − r j + s j ) + , if p j ≥ 1 − r i − r j + s j and p j ≥ 1 − α with i, j = 1 , 2 and i 6 = j . Define the codeword difference vectors ∆ u i = √ S N R 1 − p i ( u ı u i i − u ˆ ı u i i ) , ∆ w i = w ı w i i − w ˆ ı w i i , and ∆ x i = x ı x i i − x ˆ ı x i i with u ı u i i , u ˆ ı u i i ∈ C u i ( S N R , s i ) , w ı w i i , w ˆ ı w i i ∈ C w i ( S N R , t i ) and x ı x i i , x ˆ ı x i i ∈ C x i ( S N R , r i ) , for i = 1 , 2 . Further , define ∆ A ij = [∆ u i ∆ w j ] , ∆ B ij = [∆ w i ∆ w j ] , and ∆ C ij = [∆ x i ∆ w j ] for i, j = 1 , 2 and i 6 = j . Denote the optimizing values of s , t , and p obtained by solving (50) as s ∗ , t ∗ , and p ∗ , respectiv ely . W e let [ k ∗ l ∗ ] = arg min k =1 , 2 l =1 , 2 , 3 , 4 , 5 , 6 ( d kl ( r , s , p )) . (51) Further , let the functions 4 Υ nm ( r ) = [ υ 1 nm ( r ) υ 2 nm ( r )] T and Ψ nm ( s ∗ ) = [ ψ 1 nm ( s ∗ ) ψ 2 nm ( s ∗ )] T be such that d k ∗ l ∗ ( r , s ∗ , p ∗ ) = d nm (Υ nm ( r ) , Ψ nm ( s ∗ ) , p ∗ ) for all n = 1 , 2 and m = 1 , 2 , . . . , 6 . If there e xists a sequence (in SNR) of superposition codes satisfying k ∆ u i k 2 ˙ ≥ S N R − ψ i i 1 ( s ∗ )+ k ∆ w i k 2 ˙ ≥ S N R − υ i i 2 ( r )+ ψ i i 2 ( s ∗ )+ k ∆ x i k 2 ˙ ≥ S N R − υ i i 3 ( r )+ λ min (∆ A ij (∆ A ij ) H ) ˙ ≥ S N R − ψ i i 4 ( s ∗ ) − υ j j 4 ( r )+ ψ j j 4 ( s ∗ )+ λ min (∆ B ij (∆ B ij ) H ) ˙ ≥ S N R − 2 P k =1 υ k k 5 ( r )+ 2 P j =1 ψ j j 5 ( s ∗ )+ λ min (∆ C ij (∆ C ij ) H ) ˙ ≥ S N R − υ i i 6 ( r ) − υ j j 6 ( r )+ ψ j j 6 ( s ∗ )+ (52) 4 W e note that the functions Υ nm ( r ) and Ψ nm ( s ∗ ) might not be unique. March 8, 2022 DRAFT 15 for ev ery pair of codewords in each codebook for i, j = 1 , 2 , i 6 = j , and for some 5 > 0 , then we hav e P ( E H K ) . = S N R − d H K ( r ) . (53) Pr oof: The public message is to be decoded at both receiv ers, whereas the priv ate message is to be decoded only at the intended recei ver . As stated before and discussed in [ 14 ], there is no loss of optimality in assuming i.i.d. Gaussian inputs in obtaining an outer bound on the DMT . Hence, we restrict ourselves to the case where all codebooks are i.i.d. Gaussian, i.e., u i ∼ C N ( 0 , S N R p i − 1 I N ) (54) w i ∼ C N ( 0 , 1 − p 1 / ( S N R 1 − p i ) 2 I N ) (55) with 0 ≤ p i < 1 . Since we are interested in the high-SNR asymptotics, we can take 1 − q 1 S N R 1 − p i 2 ≈ 1 so that (55) becomes w i ∼ C N ( 0 , I N ) . (56) The set of achiev able rates { S i , T i , T j } for i, j = 1 , 2 , i 6 = j at R i , gi ven the channel realization h i , can be characterized as R i H K , { S i , T i , T j } : S i ≤ log 1 + S N R p i | h ii | 2 1 + S N R α + p j − 1 | h j i | 2 (57) T i ≤ log 1 + S N R | h ii | 2 1 + S N R α + p j − 1 | h j i | 2 (58) T j ≤ log 1 + S N R α | h j i | 2 1 + S N R α + p j − 1 | h j i | 2 (59) S i + T i ≤ log 1 + S N R | h ii | 2 1 + S N R α + p j − 1 | h j i | 2 (60) S i + T j ≤ log 1 + S N R p i | h ii | 2 + S N R α | h j i | 2 1 + S N R α + p j − 1 | h j i | 2 (61) T i + T j ≤ log 1 + S N R | h ii | 2 + S N R α | h j i | 2 1 + S N R α + p j − 1 | h j i | 2 (62) S i + T i + T j ≤ log 1 + S N R | h ii | 2 + S N R α | h j i | 2 1 + S N R α + p j − 1 | h j i | 2 (63) 5 W e note that the ’ s in (52) are allowed to be different. March 8, 2022 DRAFT 16 S i , T i , T j ≥ 0 (64) for i, j = 1 , 2 and i 6 = j . F or a set S of quadruples { S 1 , T 1 , S 2 , T 2 } , let Q ( S ) be the set of rate pairs ( R 1 , R 2 ) such that R 1 = S 1 + T 1 and R 2 = S 2 + T 2 . Then, the set R ∗ , Y R 1 H K \ R 2 H K (65) is an achiev able rate region for the IC operating under a HK scheme with fixed power split p . By definition, no decoding error is made at R i if the pri vate and the public message of T i are decoded correctly but the public message of T j is decoded incorrectly [ 17 ]. Therefore, as the recei ver R i is not interested in the messages from T j , it does not make sense to declare an outage because the channel between the unintended transmitter T j and the receiv er R i for i, j = 1 , 2 i 6 = j , is not good enough to support the transmission rate T j . Hence, the outage event corresponding to decoding the public message of the unintended transmitter , (59), and its counterpart for R j are unnecessary from the point of vie w of the respectiv e receiv ers. An outage ev ent for R i is therefore defined by O i ( r , s , p ) , 6 [ j =1 O ij ( r , s , p ) (66) where O i 1 ( r , s , p ) , h i : log 1 + S N R p i | h ii | 2 1 + S N R α + p j − 1 | h j i | 2 < S i (67) O i 2 ( r , s , p ) , h i : log 1 + S N R | h ii | 2 1 + S N R α + p j − 1 | h j i | 2 < T i (68) O i 3 ( r , s , p ) , h i : log 1 + S N R | h ii | 2 1 + S N R α + p j − 1 | h j i | 2 < S i + T i (69) O i 4 ( r , s , p ) , h i : log 1 + S N R p i | h ii | 2 + S N R α | h j i | 2 1 + S N R α + p j − 1 | h j i | 2 < S i + T j (70) O i 5 ( r , s , p ) , h i : log 1 + S N R | h ii | 2 + S N R α | h j i | 2 1 + S N R α + p j − 1 | h j i | 2 < T i + T j (71) March 8, 2022 DRAFT 17 O i 6 ( r , s , p ) , h i : log 1 + S N R | h ii | 2 + S N R α | h j i | 2 1 + S N R α + p j − 1 | h j i | 2 < S i + T i + T j (72) for i, j = 1 , 2 and i 6 = j . W e also define the complementary ev ents ¯ O ik ( r , s , p ) for k = 1 , 2 , . . . , 6 as follows: ¯ O i 1 ( r , s , p ) , h i : log 1 + S N R p i | h ii | 2 1 + S N R α + p j − 1 | h j i | 2 ≥ S i (73) ¯ O i 2 ( r , s , p ) , h i : log 1 + S N R | h ii | 2 1 + S N R α + p j − 1 | h j i | 2 ≥ T i (74) ¯ O i 3 ( r , s , p ) , h i : log 1 + S N R | h ii | 2 1 + S N R α + p j − 1 | h j i | 2 ≥ S i + T i (75) ¯ O i 4 ( r , s , p ) , h i : log 1 + S N R p i | h ii | 2 + S N R α | h j i | 2 1 + S N R α + p j − 1 | h j i | 2 ≥ S i + T j (76) ¯ O i 5 ( r , s , p ) , h i : log 1 + S N R | h ii | 2 + S N R α | h j i | 2 1 + S N R α + p j − 1 | h j i | 2 ≥ T i + T j (77) ¯ O i 6 ( r , s , p ) , h i : log 1 + S N R | h ii | 2 + S N R α | h j i | 2 1 + S N R α + p j − 1 | h j i | 2 ≥ S i + T i + T j (78) for i, j = 1 , 2 and i 6 = j . It is shown in [ 10 ] that P [ O ik ( r , s , p )] . = S N R − d ik ( r , s , p ) , i = 1 , 2 , k = 1 , 2 , . . . , 6 , where d i 1 ( r , s , p ) = ( p i − s i ) + , if p j < 1 − α (1 − α − p j + p i − s i ) + , if p j ≥ 1 − α (79) March 8, 2022 DRAFT 18 d i 2 ( r , s , p ) = (1 − r i + s i ) + , if p j < 1 − α (2 − α − p j − r i + s i ) + , if p j ≥ 1 − α (80) d i 3 ( r , s , p ) = (1 − r i ) + , if p j < 1 − α (2 − α − p j − r i ) + , if p j ≥ 1 − α (81) d i 4 ( r , s , p ) = ( p i − s i − r j + s j ) + + ( α − s i − r j + s j ) + , if p j < 1 − s i − r j + s j ( p i − s i − r j + s j ) + , if p j ≥ 1 − s i − r j + s j and p j < 1 − α (1 − α − p j + p i − s i − r j + s j ) + , if p j ≥ 1 − s i − r j + s j and p j ≥ 1 − α (82) d i 5 ( r , s , p ) = 1 − 2 P k =1 r k + 2 P l =1 s l + + α − 2 P k =1 r k + 2 P l =1 s l + , if p j < 1 − 2 P k =1 r k + 2 P l =1 s l , 1 − 2 P k =1 r k + 2 P l =1 s l + , if p j ≥ 1 − 2 P k =1 r k + 2 P l =1 s l and p j < 1 − α 2 − α − p j − 2 P k =1 r k + 2 P l =1 s l + , if p j ≥ 1 − 2 P k =1 r k + 2 P l =1 s l and p j ≥ 1 − α (83) March 8, 2022 DRAFT 19 d i 6 ( r , s , p ) = (1 − r i − r j + s j ) + + ( α − r i − r j + s j ) + , if p j < 1 − r i − r j + s j (1 − r i − r j + s j ) + , if p j ≥ 1 − r i − r j + s j and p j < 1 − α (2 − α − p j − r i − r j + s j ) + , if p j ≥ 1 − r i − r j + s j and p j ≥ 1 − α (84) with i, j = 1 , 2 and i 6 = j . W e define the total outage probability of the IC as the maximum of the probabilities of outage for the two receiv ers, that is, P [ O ( r , s , p )] , max ( P [ O 1 ( r , s , p )] , P [ O 2 ( r , s , p )]) . (85) W e note that this definition is compatible with our previous definitions. For a giv en rate tuple r , we would like to minimize this probability ov er all choices of s and p , i.e., P O H K ( r ) , min s , p P [ O ( r , s , p )] (86) subject to r i = s i + t i (87) s i , t i ≥ 0 (88) 0 ≤ p i < 1 , for i = 1 , 2 . (89) W e will next sho w that P O H K ( r ) obeys the following exponential behavior in S N R P O H K ( r ) . = S N R − d H K ( r ) (90) where d H K ( r ) = max s , p min ( d 1 ( r , s , p ) , d 2 ( r , s , p )) (91) subject to s i + t i = r i 0 ≤ s i ≤ r i 0 ≤ t i ≤ r i 0 ≤ p i < 1 , for i = 1 , 2 , (92) March 8, 2022 DRAFT 20 and where the d i ( r , s , p ) are giv en by d 1 ( r , s , p ) = min i =1 , 2 ,..., 6 d 1 i ( r , s , p ) (93) d 2 ( r , s , p ) = min i =1 , 2 ,..., 6 d 2 i ( r , s , p ) . (94) T o see this, we note that P O H K ( r ) can be bounded as follows min s , p max ( P [ O 1 k ( r , s , p )] , P [ O 2 l ( r , s , p )]) ≤ P O H K ( r ) ≤ min s , p max 6 X i =1 P [ O 1 i ( r , s , p )] , 6 X j =1 P [ O 2 j ( r , s , p )] ! (95) where the inequality holds for all k = 1 , 2 , . . . , 6 and l = 1 , 2 , . . . , 6 . In the high SNR limit the RHS of (95) is dominated by the SNR exponent giv en by max s , p min min i =1 , 2 ,..., 6 d 1 i ( r , s , p ) , min j =1 , 2 ,..., 6 d 2 j ( r , s , p ) . (96) The upper and lower bounds on P O H K ( r ) can be made to have the same SNR e xponent upon selection of the appropriate v alues for k and l in the left-hand-side (LHS) of (95). W e no w arri ved at a lo wer bound on the error probability of the joint ML decoder for the two-message, fixed-power-split HK scheme . Follo wing [ 11 ], we decompose the error probability of the joint ML decoder for the two-messag e, fixed-power-split HK scheme at R i into sev en disjoint error ev ents. As noted earlier , one of these e vents is irrelev ant for the IC. Denoting the decisions on the priv ate and public message of T i and the public message of T j at R i by u ˆ ı u i i , w ˆ ı w i i , and w ˆ ı w j j , respectively , we end up with the follo wing six error ev ents when the transmitted codewords are u ı u i i , w ı w i i , and w ı w j j for i, j = 1 , 2 and i 6 = j : E H K i 1 , ˆ ı u i 6 = ı u i , ˆ ı w i = ı w i , ˆ ı w j = ı w j (97) E H K i 2 , ˆ ı u i = ı u i , ˆ ı w i 6 = ı w i , ˆ ı w j = ı w j (98) E H K i 3 , ˆ ı u i 6 = ı u i , ˆ ı w i 6 = ı w i , ˆ ı w j = ı w j (99) E H K i 4 , ˆ ı u i 6 = ı u i , ˆ ı w i = ı w i , ˆ ı w j 6 = ı w j (100) E H K i 5 , ˆ ı u i = ı u i , ˆ ı w i 6 = ı w i , ˆ ı w j 6 = ı w j (101) E H K i 6 , ˆ ı u i 6 = ı u i , ˆ ı w i 6 = ı w i , ˆ ı w j 6 = ı w j . (102) March 8, 2022 DRAFT 21 The total error e vent at R i is simply the union of the abov e events, i.e., E H K i , 6 [ k =1 E H K ik . (103) W e let [ k ∗ l ∗ ] = arg min k =1 , 2 l =1 , 2 , 3 , 4 , 5 , 6 ( d kl ( r , s , p )) . (104) Further , let the functions 6 Υ nm ( r ) = [ υ 1 nm ( r ) υ 2 nm ( r )] T and Ψ nm ( s ∗ ) = [ ψ 1 nm ( s ∗ ) ψ 2 nm ( s ∗ )] T be such that d k ∗ l ∗ ( r , s ∗ , p ∗ ) = d nm (Υ nm ( r ) , Ψ nm ( s ∗ ) , p ∗ ) for all n = 1 , 2 and m = 1 , 2 , . . . , 6 . Next, we deri ve an upper bound on E H K i and show that the SNR exponent of this bound matches the SNR exponent of the outage probability P O H K ( r ) . W e start by deriving an upper bound on P E H K ik according to P E H K ik = P E H K ik , O ik (Υ ik ( r ) , Ψ ik ( s ∗ ) , p ∗ ) + P E H K ik , ¯ O ik (Υ ik ( r ) , Ψ ik ( s ∗ ) , p ∗ ) (105) ≤ P [ O ik (Υ ik ( r ) , Ψ ik ( s ∗ ) , p ∗ )] + (106) P E H K ik | ¯ O ik (Υ ik ( r ) , Ψ ik ( s ∗ ) , p ∗ ) , (107) for i = 1 , 2 and k = 1 , 2 , . . . , 6 . Ne xt, we deriv e an upper bound on P E H K ik | ¯ O ik (Υ ik ( r ) , Ψ ik ( s ∗ ) , p ∗ ) using the union bound and the PEP . For the ev ent E H K i 1 , the receiv er can cancel the contribution of w i and w j out as they hav e been decoded correctly . The resulting equiv alent signal model is then y = √ S N R h ii u i + √ S N R α h j i u j + z . (108) T reating u j as noise with u j ∼ C N ( 0 , S N R − (1 − p j ) I N ) results in an upper bound on the error probability as the worst noise under a cov ariance constraint is Gaussian [ 18 ]. The equiv alent noise n = z + √ S N R α h j i u j is therefore Gaussian with n ∼ C N ( 0 , (1 + S N R − (1 − p j )+ α | h j i | 2 ) I N ) . Recall 6 W e note that the functions Υ nm ( r ) and Ψ nm ( s ∗ ) might not be unique. March 8, 2022 DRAFT 22 that we assumed that R j kno ws h j i perfectly . W e are no w in a position to upper-bound the PEP according to E h i { P [ u i → ˜ u i ] } ≤ E h i exp − k h ii ( u i − ˜ u i ) k 2 S N R 4(1 + S N R − (1 − p j )+ α | h j i | 2 ) . Since ∆ u i = √ S N R 1 − p i ( u i − ˜ u i ) , we get E h i { P [ u i → ˜ u i ] } ≤ E h i exp − k h ii (∆ u i ) k 2 S N R p i 4(1 + S N R − (1 − p j )+ α | h j i | 2 ) . (109) Next, we use the fact that ¯ O i 1 (Υ i 1 ( r ) , Ψ i 1 ( s ∗ ) , p ∗ ) entails S N R p i | h ii | 2 1+ S N R − (1 − p j )+ α | h j i | 2 ≥ S N R ψ i i 1 ( s ∗ ) where i, j = 1 , 2 and i 6 = j and apply the union bound to upper-bound P E H K i 1 | ¯ O i 1 (Υ i 1 ( r ) , Ψ i 1 ( s ∗ ) , p ∗ ) according to E h i P E i 1 | ¯ O i 1 (Υ i 1 ( r ) , Ψ i 1 ( s ∗ ) , p ∗ ) ≤ S N R N s i exp " − S N R ψ i i 1 ( s ∗ ) k ∆ u i k 2 4 # . (110) Since k ∆ u i k 2 ˙ ≥ S N R − ψ i i 1 ( s ∗ )+ , with > 0 , by assumption, we further hav e E h i P E H K i 1 ˙ ≤ P [ O i 1 (Υ i 1 ( r ) , Ψ i 1 ( s ∗ ) , p ∗ )] + S N R N s i exp [ − S N R ] (111) ˙ ≤ P [ O i 1 (Υ i 1 ( r ) , Ψ i 1 ( s ∗ ) , p ∗ )] . (112) For the ev ent E H K i 2 , the receiv er can cancel the contributions of the correctly decoded messages u i and w j out. Follo wing steps similar to those leading to (109), we obtain E h i { P [ w i → ˜ w i ] } ≤ E h i exp − k h ii ∆ w i k 2 S N R 4(1 + S N R − (1 − p j )+ α | h j i | 2 ) . Next, an application of the union bound to P E H K i 2 | ¯ O i 2 (Υ i 2 ( r ) , Ψ i 2 ( s ∗ ) , p ∗ ) yields E h i P E H K i 2 | ¯ O i 2 (Υ i 2 ( r ) , Ψ i 2 ( s ∗ ) , p ∗ ) ≤ (113) S N R N t i exp " − S N R υ i i 2 ( r ) − ψ i i 2 ( s ∗ ) k ∆ w i k 2 4 # March 8, 2022 DRAFT 23 as the ev ent ¯ O i 2 (Υ i 2 ( r ) , Ψ i 2 ( s ∗ ) , p ∗ ) entails S N R | h ii | 2 1 + S N R α + p j − 1 | h j i | 2 ≥ S N R υ i i 2 ( r ) − ψ i i 2 ( s ∗ ) . (114) Since k ∆ w i k 2 ˙ ≥ S N R − υ i i 2 ( r )+ ψ i i 2 ( s ∗ )+ , with > 0 , by assumption, we further hav e E h i P E H K i 2 ˙ ≤ P [ O i 2 (Υ i 2 ( r ) , Ψ i 2 ( s ∗ ) , p ∗ )] + S N R N t i exp [ − S N R ] (115) ˙ ≤ P [ O i 2 (Υ i 2 ( r ) , Ψ i 2 ( s ∗ ) , p ∗ )] . (116) For the e vent E H K i 3 , the receiv er can cancel the contribution of the correctly decoded message w j out. W e define x ˆ ı x i i = u ˆ ı u i i + w ˆ ı w i i , and recall that x ı x i i = u ı u i i + w ı w i i . The PEP of deciding in fav or of x ˆ ı x i i when x ı x i i was actually transmitted can be upper-bounded as E h i { P [ x i → ˜ x i ] } ≤ E h i exp − k h ii ∆ x i k 2 S N R 4(1 + S N R − (1 − p j )+ α | h j i | 2 ) where ∆ x i = x ı x i i − x ˆ ı x i i (as defined before). Next, applying the union bound, we get E h i P E H K i 3 | ¯ O i 3 (Υ i 3 ( r ) , Ψ i 3 ( s ∗ ) , p ∗ ) ≤ S N R N r i exp " − S N R υ i i 3 ( r ) k ∆ x i k 2 4 # since the ev ent ¯ O i 3 (Υ i 3 ( r ) , Ψ i 3 ( s ∗ ) , p ∗ ) entails S N R | h ii | 2 1 + S N R α + p j − 1 | h j i | 2 ≥ S N R υ i i 3 ( r ) . (117) As k ∆ x i k 2 ˙ ≥ S N R − υ i i 3 ( r )+ , for > 0 , by assumption, we further hav e E h i P E H K i 3 ˙ ≤ P [ O i 3 (Υ i 3 ( r ) , Ψ i 3 ( s ∗ ) , p ∗ )] + S N R N r i exp [ − S N R ] (118) ˙ ≤ P [ O i 3 (Υ i 3 ( r ) , Ψ i 3 ( s ∗ ) , p ∗ )] . (119) For the e vent E H K i 4 , the recei ver can cancel out the contribution of the correctly decoded message w i . Denoting A ij = [ √ S N R 1 − p i u ı u i i w ı w j j ] , ˜ A ij = [ √ S N R 1 − p i u ˆ ı u i i w ˆ ı w j j ] , ˜ h = [ √ S N R p i h ii √ S N R α h j i ] T , March 8, 2022 DRAFT 24 and recalling that ∆ A ij = A ij − ˜ A ij , the PEP corresponding to deciding in fav or of ˜ A ij when A ij was actually transmitted is upper-bounded according to E h i n P h A ij → ˜ A ij io ≤ E h i ( exp " − k ∆ A ij ˜ h k 2 4(1 + S N R α − (1 − p j ) | h j i | 2 ) #) ≤ E h i exp − λ min S N R p i | h ii | 2 + S N R α | h j i | 2 4(1 + S N R α − (1 − p j ) | h j i | 2 ) ≤ exp h − λ min S N R ψ i i 4 ( s ∗ )+ υ j j 4 ( r ) − ψ j j 4 ( s ∗ ) i where λ min is the smallest nonzero eigen value of ∆ A ij (∆ A ij ) H . As λ min ˙ ≥ S N R − ψ i i 4 ( s ∗ ) − υ j j 4 ( r )+ ψ j j 4 ( s ∗ )+ (120) with some > 0 , by assumption, we hav e E h i P E H K i 4 ˙ ≤ P [ O i 4 (Υ i 4 ( r ) , Ψ i 4 ( s ∗ ) , p ∗ )] + S N R N ( s i + t j ) exp [ − S N R ] ˙ ≤ P [ O i 4 (Υ i 4 ( r ) , Ψ i 4 ( s ∗ ) , p ∗ )] . For the ev ent E H K i 5 , the receiv er cancels out the contributions of the correctly decoded u i . Denoting B ij = [ w ı w i i w ı w j j ] , ˜ B ij = [ w ˆ ı w i i w ˆ ı w j j ] , ˜ h = [ √ S N R h ii √ S N R α h j i ] T , and recalling that ∆ B ij = B ij − ˜ B ij , we hav e E h i n P h B ij → ˜ B ij io ≤ E h i ( exp " − k ∆ B ij ˜ h k 2 4(1 + S N R − (1 − p j )+ α | h j i | 2 ) #) ≤ E h i exp − λ min S N R | h ii | 2 + S N R α | h j i | 2 4(1 + S N R − (1 − p j )+ α | h j i | 2 ) ≤ exp − λ min S N R 2 P k =1 υ k k 5 ( r ) − 2 P j =1 ψ j j 5 ( s ∗ ) where λ min is the smallest nonzero eigen value of ∆ B ij (∆ B ij ) H . As λ min ˙ ≥ S N R − 2 P k =1 υ k k 5 ( r )+ 2 P j =1 ψ j j 5 ( s ∗ )+ (121) March 8, 2022 DRAFT 25 with some > 0 , by assumption, we hav e E h i P E H K i 5 ˙ ≤ P [ O i 5 (Υ i 5 ( r ) , Ψ i 5 ( s ∗ ) , p ∗ )] + S N R N ( t 1 + t 2 ) exp [ − S N R ] ˙ ≤ P [ O i 5 (Υ i 5 ( r ) , Ψ i 5 ( s ∗ ) , p ∗ )] . Finally , for the ev ent E H K i 6 , all codew ords are in error , so that there is nothing to cancel out. Denoting C ij = [ x ı x i i w ı w j j ] , e C ij = [ x ˆ ı x i i w ˆ ı w j j ] , ˜ h = [ √ S N R h ii √ S N R α h j i ] T , and recalling that ∆ C ij = C ij − ˜ C ij , we obtain E h i n P h C ij → e C ij io ≤ E h i ( exp " − k ∆ C ij ˜ h k 2 4(1 + S N R − (1 − p j )+ α | h j i | 2 ) #) ≤ E h i exp − λ min S N R | h ii | 2 + S N R α | h j i | 2 4(1 + S N R − (1 − p j )+ α | h j i | 2 ) ≤ exp h − λ min S N R υ i i 6 ( r )+ υ j j 6 ( r ) − ψ j j 6 ( s ∗ ) i where λ min is the smallest nonzero eigen value of ∆ C ij (∆ C ij ) H . As λ min ˙ ≥ S N R − υ i i 6 ( r ) − υ j j 6 ( r )+ ψ j j 6 ( s ∗ )+ (122) with some > 0 , by assumption, we hav e E h i P E H K i 6 ˙ ≤ P [ O i 6 (Υ i 6 ( r ) , Ψ i 6 ( s ∗ ) , p ∗ )] + S N R N ( r i + t j ) exp [ − S N R ] ˙ ≤ P [ O i 6 (Υ i 6 ( r ) , Ψ i 6 ( s ∗ ) , p ∗ )] . Next, we upper-bound E h i P E H K i , i = 1 , 2 , as follows E h i P E H K i ≤ 6 X k =1 E h i P E H K ik (123) ˙ ≤ 6 X k =1 P [ O ik (Υ ik ( r ) , Ψ ik ( s ∗ ) , p ∗ )] (124) . = max k =1 , 2 ,..., 6 P [ O ik (Υ ik ( r ) , Ψ ik ( s ∗ ) , p ∗ )] (125) . = P O H K ( r ) . (126) March 8, 2022 DRAFT 26 The error probability for the two-message, fixed power -split-HK scheme is giv en by P E H K . = max i =1 , 2 E h i P E H K i (127) . = max P O H K ( r ) , P O H K ( r ) (128) . = P O H K ( r ) (129) where (129) follo ws from the definition of P O H K ( r ) . From the outage lo wer bound (86) , we hav e that P O H K ( r ) ˙ ≤ P E H K ˙ ≤ P O H K ( r ) (130) and therefore, P E H K . = P O H K ( r ) . (131) Remark 1: It turns out that the total outage probability can be described in a more simple f ashion by recognizing that the constraints (80) and (83) are redundant. An inspection of (80) and (81) immediately yields that d i 3 ( r , s , p ) ≤ d i 2 ( r , s , p ) so that (80) can be eliminated. Finally , (83) can be eliminated as follo ws: • whenev er p j < 1 − 2 P k =1 r k + s j , then d i 6 ( r , s , p ) ≤ d i 5 ( r , s , p ) . • whenev er p j ≥ 1 − 2 P k =1 r k + s j and ? p j ≥ 1 − 2 P k =1 r k + 2 P l =1 s l , then d i 6 ( r , s , p ) ≤ d i 5 ( r , s , p ) . ? p j < 1 − 2 P k =1 r k + 2 P l =1 s l , then d j 1 ( r , s , p ) ≤ d i 5 ( r , s , p ) with i, j = 1 , 2 and i 6 = j . It is interesting to observe that analogues of the eliminations carried out in the last step abov e were reported in [ 17 ]. W e note that the elimination of (80) and (83) is equiv alent (in terms of DMT) to eliminating conditions (68) and (71) in the characterization of the total outage e vent in (66) . This, in March 8, 2022 DRAFT 27 turn, is equi valent (in terms of DMT) to eliminating (59) and (62) from the characterization of the achie v able rate region R ∗ . No w , it can be shown that the HK rate re gion described in [ 17 ] e v aluates precisely to the rate region R ∗ in (65) without the constraints (59) and (62) when the distributions of the inputs are assumed to be i.i.d. Gaussian in [17]. I V . A C H I E V A B L E D M T O F T H E I N T E R F E R E N C E C H A N N E L W e would lik e to recall that the joint decoder and the two-message, fix ed-po wer-split HK scheme correspond to dif ferent power -splits between pri vate and public messages (at the transmitters), dif ferent code design criteria, and dif ferent decoding algorithms. As already mentioned, the joint decoder can be viewed as a special case of the two-message, fixed-po wer-split HK scheme where there are no pri v ate messages. For a giv en rate tuple r , obviously , either d H K ( r ) or d J D ( r ) dominates. Therefore, the maximum achie vable DMT of the fixed-power -split HK scheme is giv en by d ( r ) = max d H K ( r ) , d J D ( r ) (132) and can be achiev ed by using the appropriate power -split, code designs, and decoding algorithm as follo ws: • If d H K ( r ) ≤ d J D ( r ) , employ a family of codebooks satisfying the code design criteria in Theorem 1, and use the joint ML decoder for IC . • If d H K ( r ) > d J D ( r ) , employ a family of codebooks satisfying the code design criteria, the po wer-split p ∗ , and the joint ML decoder for two-message , fixed-power-split HK scheme in Theorem 2. In the next section, we show that the fixed-po wer-split HK scheme is DMT -optimal for certain interference lev els. Specifically , we call ICs with 1 > α ≥ 2 / 3 , 2 > α ≥ 1 , and α ≥ 2 moderate , str ong and very str ong ICs in the sense of [ 5 ], respecti vely . Next, we will sho w that the fixed-po wer- split HK scheme is DMT -optimal under moderate , str ong and very str ong interference for symmetric multiplexing rates, i.e., for r = r 1 = r 2 . V . D M T - O P T I M A L I T Y In this section, we deri ve an outer bound on the DMT region of the IC that is tighter than the outer bound deriv ed in [ 10 ] for some interference lev els. It turns out that for symmetric multiple xing rates, i.e., when r = r 1 = r 2 , the two-message, fixed-po wer-split HK scheme achiev es this outer March 8, 2022 DRAFT 28 bound for all α ≥ 2 / 3 . Hence, for α ≥ 2 / 3 , the two-message, fixed-power -split HK scheme is DMT -optimal for symmetric multiplexing rates. For α < 2 / 3 , unfortunately , the two-message, fixed-po wer-split HK scheme does not reach our outer bound. For asymmetric rate requirements, i.e., when r 1 6 = r 2 , we show that the two-message, fixed-po wer-split HK scheme is DMT -optimal for α ≥ 1 . W e proceed by presenting our outer bound. A. Outer bound on DMT W e consider outer-bounding the capacity region of the IC by providing R 2 with the side infor- mation x 1 . As R 2 kno ws the fading coefficient h 12 perfectly (by assumption), it can cancel the interference out completely , leaving a one-sided IC as depicted in Fig. 1. Further , we assume that a genie rev eals the fading coef ficient h 21 to T 2 . It is shown in [4], [5] that the capacity region of the IC is contained in the following region R 1 E T W , D 1 , S N R α | h 21 | 2 < 1 D 2 , S N R α | h 21 | 2 ≥ 1 (133) where D 1 , ( S 1 , T 1 , S 2 , T 2 ) : S 1 + T 1 ≤ log 1 + S N R | h 11 | 2 + 1 S 2 + T 2 ≤ log 1 + S N R | h 22 | 2 + 1 D 2 , ( S 1 , T 1 , S 2 , T 2 ) : S 1 + T 1 ≤ log 1 + S N R | h 11 | 2 + 1 S 1 + T 1 + T 2 ≤ log 1 + S N R | h 11 | 2 + S N R α | h 21 | 2 + 1 S 2 ≤ log 1 + S N R 1 − α | h 22 | 2 | h 21 | 2 + 1 S 2 + T 2 ≤ log 1 + S N R | h 22 | 2 + 1 . For a set S of quadruples { S 1 , T 1 , S 2 , T 2 } , let Q ( S ) be the corresponding set of rate pairs such that R 1 = S 1 + T 1 and R 2 = S 2 + T 2 . W e recall that S i = s i log S N R , T i = t i log S N R , and R i = r i log S N R for i = 1 , 2 . Then, the set R ∗ E T W , Y R 1 E T W (134) March 8, 2022 DRAFT 29 is an outer bound on the achiev able rate region for the IC, i.e., we hav e R ∗ E T W ⊇ R † (135) where R † is any achiev able rate region of the IC. Next, we define the ev ents A , h 21 : S N R α | h 21 | 2 < 1 ¯ A , h 21 : S N R α | h 21 | 2 ≥ 1 and O E T W 1 i ( r , s ) , h i : log 1 + S N R | h ii | 2 + 1 < S i + T i for i = 1 , 2 O E T W 13 ( r , s ) , h 1 : log 1 + S N R | h 11 | 2 + S N R α | h 21 | 2 + 1 < S 1 + T 1 + T 2 O E T W 14 ( r , s ) , h 2 : log 1 + S N R 1 − α | h 22 | 2 | h 21 | 2 + 1 < S 2 . Since any achie vable rate region for the IC is contained in R ∗ E T W , it follows that the error probability of any scheme communicating ov er the IC is lower -bounded by P O E T W ( r ) , min s P O E T W 1 ( r , s ) (136) where the minimization is carried out subject to r i = s i + t i (137) s i , t i ≥ 0 (138) s i , t i ≤ r i (139) for i = 1 , 2 with O E T W 1 ( r , s ) , K 1 ( r , s ) [ K 2 ( r , s ) (140) and K 1 ( r , s ) , [ i =1 , 2 O E T W 1 i ( r , s ) ! \ A (141) K 2 ( r , s ) , [ i =1 , 2 , 3 , 4 O E T W 1 i ( r , s ) ! \ ¯ A . (142) March 8, 2022 DRAFT 30 Next, we compute P O E T W 1 ( r , s ) . W e note that O E T W 1 ( r , s ) , K 1 ( r , s ) S K 2 ( r , s ) can equi v alently be characterized as: O E T W 1 ( r , s ) = [ i =1 , 2 O E T W 1 i ( r , s ) ! [ [ i =3 , 4 O E T W 1 i ( r , s ) \ ¯ A ! . It follows that we can upper-bound P O E T W 1 ( r , s ) according to P O E T W 1 ( r , s ) ≤ 2 X i =1 P O E T W 1 i ( r , s ) + 4 X i =3 P h O E T W 1 i ( r , s ) \ ¯ A i . (143) W e can also lower -bound P O E T W 1 ( r , s ) according to P O E T W 1 i ( r , s ) ≤ P O E T W 1 ( r , s ) (144) for i = 1 , 2 . Further , for i = 3 , 4 , we hav e P h O E T W 1 i ( r , s ) \ ¯ A i ≤ P O E T W 1 ( r , s ) . (145) W e only need to compute the SNR exponents of the upper and lower bounds to obtain the SNR exponent of P O E T W 1 ( r , s ) . It is sho wn in [10] that P O E T W 1 i ( r , s ) . = S N R − d E T W 1 i ( r , s ) (146) where d E T W 1 i ( r , s ) = (1 − r i ) + for i = 1 , 2 , and P O E T W 13 ( r , s ) . = S N R − d E T W 13 ( r , s ) (147) P O E T W 14 ( r , s ) . = S N R − d E T W 14 ( r , s ) (148) with d E T W 13 ( r , s ) = (1 − r 1 − r 2 + s 2 ) + + ( α − r 1 − r 2 + s 2 ) + d E T W 14 ( r , s ) = (1 − α − s 2 ) + , if s 2 > 0 and α < 1 1 , if s 2 = 0 0 , if s 2 > 0 and α ≥ 1 . (149) March 8, 2022 DRAFT 31 Combining (146)-(148) with (144)-(145) and (143), it follo ws that P O E T W 1 ( r , s ) . = S N R − d E T W 1 ( r , s ) (150) where d E T W 1 = min i =1 , 2 , 3 , 4 d E T W 1 i ( r , s ) . (151) The SNR exponent of P O E T W ( r ) is then obtained as P O E T W ( r ) = min s S N R − d E T W 1 ( r , s ) (152) = S N R − max s d E T W 1 ( r , s ) (153) where the optimization is carried out subject to r i = s i + t i (154) s i , t i ≥ 0 (155) s i , t i ≤ r i . (156) The error probability lower bound (153) is in general difficult to e v aluate. Howe ver , we show in the next subsection that in some cases, this bound can be ev aluated very easily . h 11 h 22 h 21 y 2 y 1 w 1 w 2 x 2 x 1 Fig. 1. One-sided interference channel March 8, 2022 DRAFT 32 B. The case α ≥ 1 It follows immediately from the outer bound (153) that the joint ML decoder for IC achiev es the optimal DMT of the IC for all interference lev els α ≥ 1 . W e denote the minimizing value of s in (153) by s † and note that the DMT outer bound in Section V -A can be simplified according to d E T W 1 ( r , s † ) = d J D ( r ) . (157) Upon inspection of (149) , we see that choosing any s 2 > 0 results in d E T W i 4 ( r , s ) = 0 for α ≥ 1 . Hence, for any s 2 > 0 , we have d E T W 1 ( r , s ) = 0 . For s 2 = 0 , we get d E T W 1 i ( r , s ) = (1 − r i ) + for i = 1 , 2 (158) d E T W 13 ( r , s ) = (1 − r 1 − r 2 ) + + ( α − r 1 − r 2 ) + (159) d E T W 14 ( r , s ) = 1 . (160) Therefore, d E T W 1 ( r , s † ) is equiv alent to d J D ( r ) by inspection of (8) and (158)-(160). C. The case 1 > α ≥ 2 / 3 For the case 1 > α ≥ 2 / 3 and for general multiplexing rates for the two transmitters, proving optimality of the two-message, fixed-po wer-split HK scheme remains elusi ve. Howe ver , we can sho w that the two-message, fixed-po wer-split HK scheme is DMT -optimal for r 1 = r 2 = r . The maximum DMT of the two-message, fixed-po wer-split HK scheme is achie ved for 1 ≥ α ≥ 2 / 3 as follo ws: • for r < α/ 2 , use the joint ML decoder for IC according to Theorem 1 • for r ≥ α/ 2 , use the joint ML decoder for the two-message , fixed-power-split HK scheme according to Theorem 2 with p i = 1 − α and s i = r − α/ 2 for i = 1 , 2 . W e recall that in the case of symmetric multiplexing rates ( r 1 = r 2 = r ), we hav e that s = s i for i = 1 , 2 . It turns out that the DMT outer bound in (153) can be maximized according to • for r < α/ 2 , set s = 0 . • for r ≥ α/ 2 , set s = r − α / 2 . W ith these choices of optimizing values, an inspection of the DMT outer bound in (153) and the achie vable region (132) yields that the two regions are equi valent. Hence, for 1 ≥ α ≥ 2 / 3 and r 1 = r 2 = r , we hav e shown that the fixed-po wer-split HK scheme achie ves the optimal DMT . March 8, 2022 DRAFT 33 V I . V E RY S T RO N G I N T E R F E R E N C E W e recall that channels with α ≥ 2 are called very str ong interfer ence channels in the sense of [ 5 ]. W e shall see that the condition α ≥ 2 enables each transmitter-recei ver pair to communicate as if the interference were not present. In this section, we restrict to α ≥ 2 and show that the joint decoder and a stripping decoder , which decodes interference while treating the intended signal as noise, subtracts the result out, and then decodes the desired signal, are optimal for the IC under very strong interference. A. Joint decoder Consider the steps (32) and (33) in the proof of the achiev able DMT of joint decoding. W e can upper-bound P E J D ik as P E J D ik = P E J D ik , O J D ik ( r ) + P E J D ik , ¯ O J D ik ( r ) ≤ P O J D ik ( r ) + P E J D ik | ¯ O J D ik ( r ) (161) for k = 1 , 2 . W e will see that this approach leads to stricter design criteria, but in exchange enables us to decouple the IC as we will demonstrate shortly . Using (37) in (161) and noting that ¯ O J D ik ( r ) entails S N R | h ii | 2 + S N R α | h j i | 2 ≥ S N R r 1 + r 2 − 1 , we can upper-bound E h i P E J D i 2 according to E h i P E J D i 2 ˙ ≤ (162) P O J D i 2 ( r ) + S N R N ( r 1 + r 2 ) exp − λ min S N R r 1 + r 2 4 . W e recall that λ min is the smallest eigen value of ∆ X ij (∆ X ij ) H . Hence, if λ min ˙ ≥ S N R − r 1 − r 2 + for some > 0 , we hav e that E h i P E J D i 2 ˙ ≤ P O J D i 2 ( r ) . (163) Similarly , using (42) in (161) and noting that O J D i 1 entails S N R | h ii | 2 ≥ S N R r i − 1 , we get E h i P E J D i 1 ˙ ≤ P O J D i 1 ( r ) + S N R N r i exp − S N R r i k ∆ x i k 2 4 . (164) If k ∆ x i k 2 ˙ ≥ S N R − r i + for some > 0 for ev ery pair of codew ords, the second term on the RHS of (164) decays exponentially , leaving the polynomially decaying term, according to E h i P E J D i 1 ˙ ≤ P O J D i 1 ( r ) . (165) March 8, 2022 DRAFT 34 Inserting (163) and (165) into (45), we get E h i P E J D i ≤ 2 X k =1 E h i P E J D ik (166) ˙ ≤ P O J D i 1 ( r ) + P O J D i 2 ( r ) (167) . = S N R − (1 − r i ) + + S N R − (1 − r 1 − r 2 ) + − ( α − r 1 − r 2 ) + (168) for i = 1 , 2 . W e simplify (168) for α ≥ 2 to get E h i P E J D i ˙ ≤ S N R − (1 − r i ) + . (169) W e recall that P ( E ii ) is the average ML error probability under the assumption that the perfectly decoded interference has been removed. W e note that P ( E ii ) is a lower bound on E h i P E J D i . Further , by the outage bound on P ( E ii ) [14], P ( E ii ) is lower -bounded according to S N R − (1 − r i ) + ˙ ≤ P ( E ii ) ˙ ≤ E h i P E J D i ˙ ≤ S N R − (1 − r i ) + . Hence, we get P ( E ii ) . = E h i P E J D i . = S N R − (1 − r i ) + . (170) This shows that under very strong interference, the IC is effecti vely decoupled , in the sense that, it is possible to achie ve the performance of two point-to-point SISO systems without interference, provided that we employ a family of codebooks that satisfy k ∆ x i k 2 ˙ ≥ S N R − r i + (171) λ min ∆ X ij (∆ X ij ) H ˙ ≥ S N R − r 1 − r 2 + (172) for all pairs of codewords x n i i , x ˜ n i i ∈ C i ( S N R , r i ) s.t. x n i i 6 = x ˜ n i i , x n j j , x ˜ n j j ∈ C j ( S N R , r j ) s.t. x n j j 6 = x ˜ n j j for i, j = 1 , 2 and i 6 = j , where ∆ x i = x n i i − x ˜ n i i , ∆ x j = x n j j − x ˜ n j j , and ∆ X ij = [∆ x i ∆ x j ] , and λ min (∆ X ij (∆ X ij ) H ) denotes the smallest nonzero eigen v alue of ∆ X ij (∆ X ij ) H , for some 7 > 0 , with a po wer-split according to p i = −∞ for i = 1 , 2 and the recei ver algorithm corresponding to the joint decoder described earlier . Hence, the joint decoder is DMT -optimal under very strong interference. What is more, as shown next, a stripping decoder achiev es the DMT performance of the joint decoder , and therefore, is also DMT -optimal. 7 W e note that is allowed to be different in (10) and (11). March 8, 2022 DRAFT 35 B. Stripping decoder In this section, we take N = 1 ; we will see later that optimal performance can be achiev ed for N ≥ 1 , in contrast to the fixed-po wer-split HK scheme. In the following, we use the short-hand x i for the first element of the transmit signal v ector x i , y i for the first element of the recei ve signal vector y i , and X i for C i ( S N R , r i ) . W e write P [ E ij | h j ] for i, j = 1 , 2 and i 6 = j for the ML decoding error probability of decoding T i at recei ver R j under the assumption that T j is treated as noise. W e define the respecti ve a verage ML decoding error probability as P ( E ij ) = E h j { P [ E ij | h j ] } . W e assume throughout that the transmit symbols are equally likely for both transmitters, and hence P [ x i ] = 1 |X i | for i = 1 , 2 . In the follo wing, we sho w that a stripping decoder achiev es the DMT outer bound in [ 10 ] gi ven by d ( r ) ≤ min { (1 − r 1 ) + , (1 − r 2 ) + } . (173) Theor em 3: For the fading IC with I/O relation (3)-(4), we hav e P ( E ) . = S N R − min { (1 − r 1 ) + , (1 − r 2 ) + } (174) provided that ∆ x i = x j i − x k i satisfies | ∆ x i | 2 ˙ ≥ S N R − r i + for e very pair x j i , x k i in each codebook X i , i = 1 , 2 , and for some > 0 . Pr oof: In the following, we show that a stripping decoder achiev es the optimal DMT region. W e start by decoding T 2 at R 1 while treating T 1 as noise, i.e., we have the effecti ve I/O relation y 1 = √ S N R α h 21 x 2 + ˜ z (175) where ˜ z is the ef fectiv e noise term with v ariance 1 + S N R | h 11 | 2 . W e ne xt note that the w orst case (in terms of mutual information and hence outage probability) uncorrelated (with the transmit signal) additi ve noise under a variance constraint is Gaussian [ 18 , Theorem 1]. In the follo wing, we use the corresponding worst case outage probability to exponentially upper-bound P ( E 21 ) , i.e., we set ˜ z ∼ C N (0 , 1 + S N R | h 11 | 2 ) . W e start by normalizing the received signal according to y 1 p 1 + S N R | h 11 | 2 = r S N R α 1 + S N R | h 11 | 2 h 21 x 2 + z (176) March 8, 2022 DRAFT 36 where z ∼ C N (0 , 1) . W e can now upper-bound P [ E 21 | h 1 ] as P [ E 21 | h 1 ] = X x 2 ∈X 2 P [ x 2 ] P [ E 21 | h 1 , x 2 ] (177) = 1 |X 2 | |X 2 | X i =1 P |X 2 | [ j =1 j 6 = i x i 2 → x j 2 | h 1 (178) ≤ |X 2 | P h x ˜ i 2 → x ˜ j 2 | h 1 i (179) ≤ |X 2 | Q s S N R α | h 21 | 2 | ∆ x 2 | 2 2(1 + S N R | h 11 | 2 ) ! , (180) where n x ˜ i 2 , x ˜ j 2 o denotes the (or “a” in the case of multiple pairs with the same distance) pair of symbols with minimum Euclidean distance among all possible pairs of different symbols. W e now define the outage ev ent O ii associated with decoding T i at R i ( i = 1 , 2 ) in the absence of interference and its complementary e vent ¯ O ii as follows O ii , h ii : log 1 + S N R | h ii | 2 < R i (181) ¯ O ii , h ii : log 1 + S N R | h ii | 2 ≥ R i . (182) W e note that this definition is consistent with the definition of P ( E ii ) . Similarly , we define the e vent O ij associated with decoding T i at R j while treating T j as noise ( i, j = 1 , 2 and i 6 = j ) and its complementary ev ent ¯ O ij as follows O ij , h j : log 1 + S N R α | h ij | 2 1 + S N R | h j j | 2 < R i ¯ O ij , h j : log 1 + S N R α | h ij | 2 1 + S N R | h j j | 2 ≥ R i . Next, we upper-bound P ( E 21 ) according to P ( E 21 ) = E h 1 { P [ E 21 | h 1 ] } = E h 1 P [ O 21 ] P [ E 21 | h 1 , O 21 ] + P ¯ O 21 P E 21 | h 1 , ¯ O 21 (183) ≤ P [ O 21 ] + E h 1 P E 21 | h 1 , ¯ O 21 (184) ≤ P [ O 21 ] + S N R r 2 Q r S N R r 2 | ∆ x 2 | 2 2 ! (185) March 8, 2022 DRAFT 37 where (183) follows from Bayes’ s rule and (184) is obtained by upper -bounding P [ E 21 | h 1 , O 21 ] and P ¯ O 21 by 1 . Finally , (185) follo ws by using the fact that ¯ O 21 entails S N R α | h 21 | 2 1+ S N R | h 11 | 2 ≥ 2 R 2 − 1 , and in voking R 2 = r 2 log S N R , |X 2 | = S N R r 2 , and S N R 1 in (180). It can be shown that P [ O 21 ] . = S N R − ( α − 1 − r 2 ) + for α ≥ 2 [ 10 ]. Further , since | ∆ x 2 | 2 ˙ ≥ S N R − r 2 + , for > 0 , by assumption, we can further simplify the above as the second term in (185) decays exponentially in SNR whereas the first term decays polynomially , i.e., we get E h 1 { P [ E 21 | h 1 ] } ˙ ≤ P [ O 21 ] . = S N R − ( α − 1 − r 2 ) + . (186) W e proceed to analyze decoding of T 1 at R 1 and start by defining ¯ x 2 as the result of decoding T 2 at R 1 . Note that we do not need to assume that T 2 was decoded correctly at R 1 . W e begin by upper-bounding P [ E 11 | h 1 ] gi ven ¯ x 2 : P [ E 11 | h 1 , ¯ x 2 ] = X x 1 ∈X 1 X x 2 ∈X 2 P [ x 1 ] P [ x 2 ] P [ E 1 | h 1 , x 1 , x 2 , ¯ x 2 ] (187) = 1 |X 1 ||X 2 | |X 1 | X i =1 |X 2 | X k =1 P |X 1 | [ j =1 j 6 = i x i 1 → x j 1 | h 1 , x k 2 , ¯ x 2 (188) ≤ |X 1 | |X 2 | |X 2 | X k =1 P h x ˜ i 1 → x ˜ j 1 | h 1 , x k 2 , ¯ x 2 i , (189) where n x ˜ i 1 , x ˜ j 1 o denotes the (or “a” in the case of multiple pairs with the same distance) pair of symbols with minimum Euclidean distance among all possible pairs of different symbols. Next, we further upper -bound P [ E 11 | h 1 , ¯ x 2 ] by considering two e vents; namely , when R 1 decodes T 2 correctly and when it does not: P [ E 11 | h 1 , ¯ x 2 ] ≤ |X 1 | |X 2 | |X 2 | X k =1 P ¯ x 2 = x k 2 | h 1 , x k 2 P h x ˜ i 1 → x ˜ j 1 | h 1 , x k 2 , ¯ x 2 , ¯ x 2 = x k 2 i + P ¯ x 2 6 = x k 2 | h 1 , x k 2 P h x ˜ i 1 → x ˜ j 1 | h 1 , x k 2 , ¯ x 2 , ¯ x 2 6 = x k 2 i , (190) where P h x ˜ i 1 → x ˜ j 1 | h 1 , x k 2 , ¯ x 2 , ¯ x 2 = x k 2 i is the probability of mistakenly decoding x ˜ i 1 for x ˜ j 1 gi ven that T 2 transmitted x k 2 and R 1 decoded T 2 correctly , i.e., ¯ x 2 = x k 2 . The quantity P ¯ x 2 = x k 2 | h 1 , x k 2 March 8, 2022 DRAFT 38 is the probability of decoding T 2 correctly giv en that x k 2 was transmitted. By upper -bounding P ¯ x 2 = x k 2 | h 1 , x k 2 and P h x ˜ i 1 → x ˜ j 1 | h 1 , x k 2 , ¯ x 2 , ¯ x 2 6 = x k 2 i in (190) by 1 , we arriv e at P [ E 11 | h 1 , ¯ x 2 ] ≤ |X 1 | |X 2 | |X 2 | X k =1 P h x ˜ i 1 → x ˜ j 1 | h 1 , x k 2 , ¯ x 2 , ¯ x 2 = x k 2 i + |X 1 | |X 2 | |X 2 | X k =1 P ¯ x 2 6 = x k 2 | h 1 , x k 2 . (191) Next, noting that 1 |X 2 | |X 2 | P k =1 P ¯ x 2 6 = x k 2 | h 1 , x k 2 ≤ P [ E 21 | h 1 ] and in voking the corresponding upper bound (180) in (191), we get P [ E 1 | h 1 , ¯ x 2 ] ≤ |X 1 | Q r S N R | h 11 | 2 | ∆ x 1 | 2 2 ! + |X 1 ||X 2 | Q s S N R α | h 21 | 2 | ∆ x 2 | 2 2(1 + S N R | h 11 | 2 ) ! . (192) The first term on the RHS of (192) follows from the first term on the RHS of (191), since gi ven ¯ x 2 = x k 2 , the interference is subtracted out perfectly , lea ving an effecti ve SISO channel without interference. W e are now in a position to upper-bound P ( E 11 ) : P ( E 11 ) = E h 1 { P [ E 11 | h 1 ] } ≤ E h 1 { P [ E 11 | h 1 , ¯ x 2 ] } (193) ≤ E h 1 ( |X 1 | Q r S N R | h 11 | 2 | ∆ x 1 | 2 2 !) + E h 1 ( |X 1 ||X 2 | Q s S N R α | h 21 | 2 | ∆ x 2 | 2 2(1 + S N R | h 11 | 2 ) !) . (194) Here, (193) follows since the error probability incurred by using the stripping decoder constitutes a natural upper bound on E h 1 { P [ E 11 | h 1 ] } . W e upper-bound (194) by splitting each of the two terms into outage and no outage sets using Bayes’ s rule to arrive at P ( E 11 ) = E h 1 { P [ E 11 | h 1 ] } ≤ P [ O 11 ] + S N R r 1 Q S N R r 1 | ∆ x 1 | 2 2 + P [ O 21 ] + S N R r 1 + r 2 Q S N R r 2 | ∆ x 2 | 2 2 . (195) March 8, 2022 DRAFT 39 The second and fourth terms on the RHS of (195) follow from (194) since ¯ O 11 and ¯ O 21 entail S N R | h 11 | 2 ≥ 2 R 1 − 1 and S N R α | h 21 | 2 1+ S N R | h 11 | 2 ≥ 2 R 2 − 1 , respecti vely , and since R i = r i log S N R , |X i | = S N R r i for i = 1 , 2 , and S N R 1 . Giv en that the minimum Euclidean distances in each codebook, | ∆ x 1 | 2 and | ∆ x 2 | 2 , obey | ∆ x 1 | 2 ˙ ≥ S N R − r 1 + and | ∆ x 2 | 2 ˙ ≥ S N R − r 2 + , for some > 0 , by assumption, we get P ( E 11 ) = E h 1 { P [ E 11 | h 1 ] } ˙ ≤ P [ O 11 ] + P [ O 21 ] (196) . = S N R − (1 − r 1 ) + + S N R − ( α − 1 − r 2 ) + (197) . = S N R − min { (1 − r 1 ) + , ( α − 1 − r 2 ) + } . (198) Similar deriv ations for decoding at R 2 lead to P ( E 22 ) ˙ ≤ S N R − min { (1 − r 2 ) + , ( α − 1 − r 1 ) + } . (199) W e note that the error probability of decoding T i at R i is exponentially lower -bounded by P [ O ii ] for i = 1 , 2 [14]. Hence, P ( E ii ) is sandwiched according to S N R − (1 − r i ) + ˙ ≤ P ( E ii ) ˙ ≤ S N R − min { (1 − r i ) + , ( α − 1 − r j ) + } (200) for i, j = 1 , 2 and i 6 = j . The proof is concluded by first upper-bounding P ( E ) = max { P ( E 11 ) , P ( E 22 ) } (201) as P ( E ) ˙ ≤ max n S N R − min { (1 − r 1 ) + , ( α − 1 − r 2 ) + } , S N R − min { (1 − r 2 ) + , ( α − 1 − r 1 ) + } o . = S N R − min { (1 − r 1 ) + , (1 − r 2 ) + } (202) where (202) is a consequence of the assumption α ≥ 2 . Secondly , P ( E ) can be lower -bounded using the outage bounds on the individual error probabilities: S N R − min { (1 − r 1 ) + , (1 − r 2 ) + } ˙ ≤ P ( E ) . (203) Since the S N R exponents in the upper bound (202) and the lower bound (203) match, we can conclude that P ( E ) . = S N R − min { (1 − r 1 ) + , (1 − r 2 ) + } (204) March 8, 2022 DRAFT 40 which establishes the desired result. Remark 2: W e can immediately conclude from Theorem 3 that using a sequence of codebooks that is DMT -optimal for the SISO channel for both users results in DMT -optimality for the IC under very strong interference. Remark 3: If r 1 = r 2 = r and we use sequences of codebooks C ( S N R , r ) satisfying the conditions of Theorem 3 for both users, then we have P ( E 11 ) . = P ( E 22 ) . = S N R − (1 − r ) + (205) as a simple consequence of (200). This means that in the special case, where each T i transmits at the same multiplexing rate r , we hav e the stronger result that the single user DMT , i.e., the DMT that is achiev able for a SISO channel in the absence of any interferers, is achiev able for both users. In effect, under very strong interference and when the two users operate at the same multiplexing rate, the interference channel effecti vely gets decoupled . For a stripping decoder and r 1 6 = r 2 , we can, in general, not arrive at the same conclusion as the SNR exponents in (200) do not necessarily match. V I I . S U B O P T I M A L S T R A T E G I E S In the follo wing, we in vestigate the DMT performance of treating the IC as a combination of tw o MA Cs and sharing transmission time between the two transmitters. These strate gies are suboptimal; in fact, it can be shown that the two-message, fixed-po wer-split HK scheme always outperforms these schemes. Ne vertheless, we analyze these two schemes as they are of some practical importance. A. Achievable DMT for tr eating the IC as a combination of two MACs A simple achie vable rate re gion for the IC is obtained by treating the IC as a MA C at each recei ver R j for j = 1 , 2 . Next, we formally define the strategy of treating the IC as a combination of two MA Cs. Definition 4: A MA C at R i is obtained by requiring the messages from both transmitters T j , j = 1 , 2 , to be decoded at R i for i = 1 , 2 . Definition 5: A joint ML decoder for MA C at R j ( j = 1 , 2 ) carries out joint ML detection on the messages from both transmitters ( T i for i = 1 , 2 ). The ML error probability and the av erage March 8, 2022 DRAFT 41 ML error probability of this receiv er are denoted by P E M AC j and P E M AC j , E h j P E M AC j , respecti vely . The following theorem provides the achiev able DMT for the strategy of treating the IC as a combination of two MA Cs. Theor em 4: The DMT corresponding to treating the IC as a MA C at each recei ver is given by d M AC ( r ) = min i =1 , 2 k =1 , 2 , 3 d M AC ik ( r ) (206) where d M AC i 1 ( r ) = (1 − r i ) + d M AC i 2 ( r ) = ( α − r j ) + , for i, j = 1 , 2 and i 6 = j d M AC i 3 ( r ) = (1 − r 1 − r 2 ) + + ( α − r 1 − r 2 ) + . Denote [ i ∗ k ∗ ] = arg min i =1 , 2 k =1 , 2 , 3 d M AC ik ( r ) . (207) Let Ξ ik ( r ) = [ ξ 1 ik ( r ) ξ 2 ik ( r )] T be functions 8 such that d M AC i ∗ k ∗ ( r ) = d M AC ik (Ξ ik ( r )) (208) for i = 1 , 2 , k = 1 , 2 , 3 . If a sequence (in SNR) of codebooks with block length N ≥ 2 satisfies k ∆ x i k 2 ˙ ≥ S N R − min { ξ i i 1 ( r ) ,ξ i j 2 ( r ) } + (209) λ min ∆ X ij (∆ X ij ) H ˙ ≥ S N R − ξ 1 i 3 ( r ) − ξ 2 i 3 ( r )+ (210) for all pairs of codewords x n i i , x ˜ n i i ∈ C i ( S N R , r i ) s.t. x n i i 6 = x ˜ n i i , x n j j , x ˜ n j j ∈ C j ( S N R , r j ) s.t. x n j j 6 = x ˜ n j j for i, j = 1 , 2 and i 6 = j , where ∆ x i = x n i i − x ˜ n i i , ∆ x j = x n j j − x ˜ n j j , and ∆ X ij = [∆ x i ∆ x j ] , and λ min (∆ X ij (∆ X ij ) H ) denotes the smallest nonzero eigen value of ∆ X ij (∆ X ij ) H , for some 9 > 0 , then P ( E ) obeys P ( E ) . = S N R − d M AC ( r ) . (211) 8 W e note that the functions Ξ ik ( r ) might not be unique. 9 W e note that is allowed to be different in (209) and (210). March 8, 2022 DRAFT 42 Pr oof: W e first identify an upper bound on the DMT and then show , using an appropriate lo wer bound, that this DMT is, indeed, achie vable. W e define the outage e vents corresponding to decoding of T i , decoding of T j , and jointly decoding of T i and T j at R i for i, j = 1 , 2 and i 6 = j by O M AC i 1 , { h i : I ( x i ; y i | x j , h i ) < R i } (212) O M AC i 2 , { h i : I ( x j ; y i | x i , h i ) < R j } (213) O M AC i 3 , { h i : I ( x i , x j ; y i | h i ) < R 1 + R 2 } . (214) W e define an outage ev ent for the MA C at R i as O M AC i , 3 [ k =1 O M AC ik . (215) W e define the total outage probability for treating the IC as a combination of MA Cs as P O M AC , max P O M AC 1 , P O M AC 2 . (216) Using a standard argument along the lines of [ 11 ], [ 13 ], we can see that assuming that both transmitters employ i.i.d. Gaussian codebooks results in no loss of optimality in terms of DMT performance. W e can therefore ev aluate (212)-(214) as O M AC i 1 ( r ) , h i : log 1 + S N R | h ii | 2 < R i O M AC i 2 ( r ) , h i : log 1 + S N R α | h j i | 2 < R j O M AC i 3 ( r ) , h i : log 1 + S N R α | h j i | 2 + S N R | h ii | 2 < R 1 + R 2 with i, j = 1 , 2 and i 6 = j . In the follo wing, we will also need the definitions of the no-outage ev ents, according to ¯ O M AC i 1 ( r ) , h i : log 1 + S N R | h ii | 2 ≥ R i ¯ O M AC i 2 ( r ) , h i : log 1 + S N R α | h j i | 2 ≥ R j ¯ O M AC i 3 ( r ) , h i : log 1 + S N R α | h j i | 2 + S N R | h ii | 2 ≥ R 1 + R 2 March 8, 2022 DRAFT 43 with i, j = 1 , 2 and i 6 = j . W e can now establish the asymptotic behavior of O M AC i . By the union bound, we hav e P O M AC i ≤ 3 X k =1 P O M AC ik ( r ) (217) . = max k =1 , 2 , 3 P O M AC ik ( r ) . (218) It is shown in [14] and [10] that P O M AC i 1 ( r ) . = S N R − d M AC i 1 ( r ) (219) P O M AC i 2 ( r ) . = S N R − d M AC i 2 ( r ) (220) P O M AC i 3 ( r ) . = S N R − d M AC i 3 ( r ) (221) with d M AC i 1 ( r ) = (1 − r i ) + (222) d M AC i 2 ( r ) = ( α − r j ) + (223) d M AC i 3 ( r ) = (1 − r 1 − r 2 ) + + ( α − r 1 − r 2 ) + (224) for i, j = 1 , 2 and i 6 = j . W e point out that (222) and (223) define six SNR e xponents d M AC ik ( r ) , i.e., for i = 1 , 2 and k = 1 , 2 , 3 . The outage event corresponding to jointly decoding the signals from both transmitters at R 1 is identical to the outage e vent corresponding to jointly decoding the signals from both transmitters at R 2 . Hence, the corresponding SNR exponents of the outage probabilities of these ev ents, namely , d M AC 13 ( r ) and d M AC 23 ( r ) , are exactly the same. The total outage probability corresponding to treating the IC as a combination of MA Cs then satisfies P O M AC = max P O M AC 1 , P O M AC 2 . (225) From (218), it follo ws that P O M AC i . = max k =1 , 2 , 3 P O M AC ik ( r ) . = S N R − min k =1 , 2 , 3 d M AC ik ( r ) . (226) Hence, combining (225) and (226), we get P O M AC . = max i =1 , 2 S N R − min k =1 , 2 , 3 d M AC ik ( r ) (227) . = S N R − d M AC ( r ) (228) March 8, 2022 DRAFT 44 where d M AC ( r ) = min i =1 , 2 k =1 , 2 , 3 d M AC ik ( r ) . (229) W e note that (227) can be simplified by eliminating either d M AC 13 ( r ) or d M AC 23 ( r ) as e xplained earlier . W ith (226) we arriv ed at a lower bound on the error probability of the joint ML decoder for MAC at R i . This lo wer bound, by definition, giv es an upper bound on the DMT region. W e next try to find an upper bound on the error probability that has the same exponential beha vior as this lo wer bound. T o this end, consider next the error probability corresponding to the joint ML decoder for MA C . W e first define the relev ant error ev ents. Let x n i i and x n j j with n i ∈ { 1 , 2 , . . . , 2 N R i } , n j ∈ { 1 , 2 , . . . , 2 N R j } ( i, j = 1 , 2 and i 6 = j ) be the code words transmitted by T i and T j , respectiv ely . The results of (joint ML) decoding of T i and T j at R i are denoted by x ˜ n i i and x ˜ n j j , respecti vely , with ˜ n i ∈ { 1 , 2 , . . . , 2 N R i } , ˜ n j ∈ { 1 , 2 , . . . , 2 N R j } for i, j = 1 , 2 and i 6 = j . W e hav e the error ev ents corresponding to T i only , T j only , and T i and T j being decoded in error at R i as E M AC i 1 , { ˜ n i 6 = n i , ˜ n j = n j } (230) E M AC i 2 , { ˜ n i = n i , ˜ n j 6 = n j } (231) E M AC i 3 , { ˜ n i 6 = n i , ˜ n j 6 = n j } (232) for i, j = 1 , 2 and i 6 = j . W e will also need the total error probability defined as E M AC i , [ k =1 , 2 , 3 E M AC ik . (233) W e denote [ i ∗ k ∗ ] = arg min i =1 , 2 k =1 , 2 , 3 d M AC ik ( r ) . (234) Let Ξ ik ( r ) = [ ξ 1 ik ( r ) ξ 2 ik ( r )] T be functions 10 such that d M AC i ∗ k ∗ ( r ) = d M AC ik (Ξ ik ( r )) (235) for i = 1 , 2 , k = 1 , 2 , 3 . 10 W e note that the functions Ξ ik ( r ) might not be unique. March 8, 2022 DRAFT 45 W e next find an upper bound on the probability of the ev ents E M AC ik as follows: P E M AC ik = P E M AC ik , O M AC ik (Ξ ik ( r )) + P E M AC ik , ¯ O M AC ik (Ξ ik ( r )) ≤ P O M AC ik (Ξ i ( r )) + P E M AC ik | ¯ O M AC ik (Ξ i ( r )) . (236) W e start by deriving an upper bound on the av erage (w .r .t. the random channel) pairwise error probability (PEP) of each error e vent E M AC ik for i = 1 , 2 and k = 1 , 2 , 3 . Assuming, without loss of generality , that we hav e an E M AC i 3 type error e vent, the probability of the ML decoder mistakenly deciding in fav or of the codeword X ˜ n i ˜ n j ij = [ x ˜ n i i x ˜ n j j ] when X n i n j ij = [ x n i i x n j j ] (with x n i i , x ˜ n i i ∈ C i ( S N R , r i ) and x n j j , x ˜ n j j ∈ C j ( S N R , r j ) , i, j = 1 , 2 and i 6 = j ) was actually transmitted, can be upper-bounded according to E h i n P h X n i n j ij → X ˜ n i ˜ n j ij io (237) ≤ E h i ( exp " − k ∆ X ij ˜ h i k 2 4 #) (238) ≤ E h i ( exp " − λ min k ˜ h i k 2 4 #) (239) = E h i exp − λ min S N R | h ii | 2 + S N R α | h j i | 2 4 (240) where ˜ h i = [ √ S N R h ii √ S N R α h j i ] T for i, j = 1 , 2 and i 6 = j and λ min is the smallest nonzero eigen value of ∆ X ij (∆ X ij ) H . Noting that the no outage ev ent ¯ O M AC i 3 (Ξ i 3 ( r )) entails S N R | h ii | 2 + S N R α | h j i | 2 ≥ S N R ξ 1 i 3 ( r )+ ξ 2 i 3 ( r ) − 1 , (236) implies an upper bound on P E M AC i 3 according to: E h i P E M AC i 3 ˙ ≤ (241) P O M AC i 3 (Ξ 3 ( r )) + S N R N ( r 1 + r 2 ) exp " − λ min S N R ξ 1 i 3 ( r )+ ξ 2 i 3 ( r ) 4 # . Here, we used the definitions R i = r i log S N R for i = 1 , 2 and exp[ − λ min 4 ( S N R ξ 1 i 3 ( r )+ ξ 2 i 3 ( r ) − 1)] . = exp[ − λ min 4 S N R ξ 1 i 3 ( r )+ ξ 2 i 3 ( r ) ] . Giv en that λ min ˙ ≥ S N R − ξ 1 i 3 ( r ) − ξ 2 i 3 ( r )+ with > 0 , by assumption, we March 8, 2022 DRAFT 46 obtain E h i P E M AC i 3 ˙ ≤ P O M AC i 3 (Ξ i 3 ( r )) + S N R N ( r 1 + r 2 ) exp − S N R 4 (242) . = P O M AC i 3 (Ξ i 3 ( r )) . = S N R − d M AC i ∗ k ∗ ( r ) (243) as the second term on the RHS of (242) decays exponentially in SNR whereas the first term decays polynomially . Eq. (243) is a consequence of the definition of the function Ξ i 3 ( r ) . A similar analysis for the E M AC i 1 -type error ev ent results in E h i P x n i i → x ˜ n i i ≤ E h i exp − S N R | h ii | 2 k ∆ x i k 2 4 (244) which, upon in voking k ∆ x i k 2 ˙ ≥ S N R − min { ξ i i 1 ( r ) ,ξ i j 2 ( r ) } + and using the fact that ¯ O M AC i 1 (Ξ i 1 ( r )) entails S N R | h ii | 2 ≥ S N R ξ i i 1 ( r ) − 1 , yields E h i P E M AC i 1 ˙ ≤ P O M AC i 1 (Ξ i 1 ( r )) + S N R N r i exp " − S N R ξ i i 1 ( r ) − min { ξ i i 1 ( r ) ,ξ i j 2 ( r ) } + 4 # (245) . = P O M AC i 1 (Ξ i 1 ( r )) . = S N R − d M AC i ∗ k ∗ ( r ) (246) for i = 1 , 2 . A similar analysis for the E M AC i 2 -type error ev ent results in E h i n P h x n j j → x ˜ n j j io ≤ E h i exp − S N R α | h j i | 2 k ∆ x j k 2 4 (247) which, upon in voking k ∆ x j k 2 ˙ ≥ S N R − min { ξ j j 1 ( r ) ,ξ j i 2 ( r ) } + March 8, 2022 DRAFT 47 and using the fact that ¯ O M AC i 2 (Ξ i 2 ( r )) entails S N R α | h j i | 2 ≥ S N R ξ j i 2 ( r ) − 1 , yields E h i P E M AC i 2 ˙ ≤ P O M AC i 2 (Ξ i 2 ( r )) + S N R N r j exp " − S N R ξ j i 2 ( r ) − min { ξ j j 1 ( r ) ,ξ j i 2 ( r ) } + 4 # (248) . = P O M AC i 2 (Ξ i 2 ( r )) . = S N R − d M AC i ∗ k ∗ ( r ) (249) for i, j = 1 , 2 and i 6 = j . T o complete the proof, we note that E h i P E M AC i ≤ 3 X k =1 E h i P E M AC ik (250) ˙ ≤ 3 X k =1 P O M AC ik (Ξ ik ( r )) (251) = 3 S N R − d M AC i ∗ k ∗ ( r ) . = S N R − d M AC ( r ) . W e finally get P E M AC = max i =1 , 2 E h i P E M AC i (252) ˙ ≤ S N R − d M AC ( r ) . (253) Since (253) gi ves an upper bound that matches the lower bound in (228) , the proof is complete. B. T ime sharing W e assume that the transmitters are orthogonalized in time or frequency such that each T i ( i = 1 , 2 ) uses a fraction θ i of the channel resources with θ 1 + θ 2 = 1 and 0 ≤ θ i ≤ 1 . Then, T i enjoys an ef fecti ve SISO channel θ i fraction of time or frequency , and the effecti ve transmission rate of T i is gi ven by R i /θ i = ( r i /θ i ) log S N R . Let P E T S i be the average ML error probability for decoding T i at R i for the time sharing system. It is sho wn in [14] that P E T S i . = S N R − (1 − r i /θ i ) + , if θ i > 0 1 , if θ i = 0 (254) for i = 1 , 2 . The achiev able DMT of this strategy is then P E T S = max P E T S 1 , P E T S 2 . March 8, 2022 DRAFT 48 W e can optimize over the parameters θ i to get the best possible DMT of this strategy according to P E OT S , min θ 1 ,θ 2 max P E T S 1 , P E T S 2 (255) subject to θ 1 + θ 2 = 1 0 ≤ θ i ≤ 1 for i = 1 , 2 . N U M E R I C A L R E S U LT S Figs. 2-5 show the DMT achiev ed by the fixed-po wer-split HK scheme (HK) in comparison to the outer bound we deri ved in (153) (ETW), the outer bound in [ 10 ] (AL08), to treating interference as noise (TIAN), and to time-sharing (TS) for symmetric rates r = r 1 = r 2 and for α = 1 / 2 , α = 2 / 3 , α = 1 , and α = 1 . 5 , respectiv ely . Fig. 2 sho ws the achiev able DMT regions and the outer bounds for α = 0 . 5 . In this case, we see that the two-message, fixed-po wer-split HK scheme (HK) is only DMT -optimal for multiplexing rates r < 1 / 4 , and falls short of achie ving the outer bound (153) (ETW) and the outer bound in [ 10 ] (AL08) for multiplexing rates r ≥ 1 / 4 . It is interesting to note that the outer bound (153) is better than the outer bound in [ 10 ] for multiplexing rates r < 0 . 45 , whereas for r > 0 . 45 the opposite is true, i.e., the outer bound [10] is tighter than the outer bound (153). Figs. 3-4 depict the achiev able DMT regions and the outer bounds for α = 2 / 3 and α = 1 , respecti vely . In these cases, we see that the two-message, fixed-po wer-split HK scheme (HK) is DMT -optimal and achiev es the DMT outer bound in (153) . W e also observe that the outer bound (153) is tighter than the outer bound in [10] for all multiplexing rates. In Fig. 5, we plot the outer bounds and the achiev able DMT regions for the interference lev el α = 1 . 5 . The two-message, fixed-power -split HK scheme achiev es the DMT outer bound (153) , and therefore, is DMT -optimal for α = 1 . 5 . W e note that for α = 1 . 5 , the outer bound (153) and the outer bound in [10] are identical. V I I I . C O N C L U S I O N S W e characterized the optimal DMT of the two-user fading IC for the cases of moderate , str ong , and very str ong interference. Further , we prov ed that a tw o-message, fix ed po wer-split HK superposition March 8, 2022 DRAFT 49 0.2 0.4 0.6 0.8 1.0 0.2 0.4 0.6 0.8 1.0 d ( r ) r TIAN HK AL08 TS ETW Fig. 2. Symmetric rate DMT for α = 1 / 2 and for various schemes. 0.2 0.4 0.6 0.8 1.0 0.2 0.4 0.6 0.8 1.0 r d ( r ) TIAN TS AL08 HK, ETW Fig. 3. Symmetric rate DMT for α = 2 / 3 and for various schemes. 0.2 0.4 0.6 0.8 1.0 0.2 0.4 0.6 0.8 1.0 r d ( r ) TS AL08 HK, ETW Fig. 4. Symmetric rate DMT for α = 1 and for various schemes. March 8, 2022 DRAFT 50 0.2 0.4 0.6 0.8 1.0 0.2 0.4 0.6 0.8 1.0 r d ( r ) TS HK, AL08, ETW Fig. 5. Symmetric rate DMT for α = 1 . 5 and for various schemes. coding scheme achiev es the optimal DMT of the two-user fading IC under moderate , str ong , and very str ong interference. W e provided code design criteria for the corresponding superposition codes. A complete characterization of the optimal DMT of the two-user f ading IC under weak interference remains an open question. R E F E R E N C E S [1] H. Sato, “The capacity of the gaussian interference channel under strong interference, ” IEEE T rans. Inf. Theory , vol. 27, no. 6, pp. 786–788, Nov . 1981. [2] A. Carleial, “ A case where interference does not reduce capacity , ” IEEE Tr ans. Inf. Theory , vol. 21, no. 5, pp. 569–570, Sep. 1975. [3] I. Sason, “On achie vable rate regions for the Gaussian interference channel, ” IEEE T rans. Inf. Theory , vol. 50, no. 6, pp. 1345–1356, Jun. 2004. [4] R. Etkin, D. N. C. Tse, and H. W ang, “Gaussian interference channel capacity to within one bit: The symmetric case, ” in Pr oc. IEEE Inf. Theory W orkshop (ITW) , Oct. 2006, pp. 601–605. [5] ——, “Gaussian interference channel capacity to within one bit, ” IEEE T rans. Inf. Theory , vol. 54, no. 12, pp. 5534–5562, Dec. 2008. [6] ˙ I. E. T elatar and D. N. C. Tse, “Bounds on the capacity re gion of a class of interference channels, ” in Pr oc. IEEE Int. Symposium on Information Theory (ISIT) , Jun. 2007, pp. 2871–2874. [7] X. Shang, G. Kramer, and B. Chen, “Outer bound and the noisy-interference sum-rate capacity for Gaussian interference channels, ” in Proc. 42nd Annual Conference on Information Sciences and Systems (CISS) , Mar . 2008, pp. 385–389. [8] A. Raja, V . M. Prabhakaran, and P . V iswanath, “The two user Gaussian compound interference channel, ” in Pr oc. IEEE Int. Symposium on Information Theory (ISIT) , Jul. 2008, pp. 569–573. [9] V . S. Annapureddy and V . V . V eerav alli, “Gaussian interference networks: Sum capacity in the low interference regime, ” in Pr oc. IEEE Int. Symposium on Information Theory (ISIT) , Jul. 2008, pp. 255–259. [10] E. Akuiyibo and O. L ´ ev ˆ eque, “Diversity-multiple xing tradeoff for the slow fading interference channel, ” in Proc. IEEE Int. Zurich Seminar on Commun. , Mar . 2008, pp. 140–143. March 8, 2022 DRAFT 51 [11] D. N. C. Tse, P . V iswanath, and L. Zheng, “Div ersity-multiplexing tradeoff in multiple access channels, ” IEEE Tr ans. Inf. Theory , vol. 50, no. 9, pp. 1859–1874, Sep. 2004. [12] S. V erd ´ u, Multiuser Detection . Cambridge, UK: Cambridge University Press, 1998. [13] P . Coronel, M. G ¨ artner , and H. B ¨ olcskei, “Di versity-multiplexing tradeof f in selectiv e-fading multiple-access MIMO channels, ” in Pr oc. IEEE Int. Symposium on Information Theory (ISIT) , Jul. 2008, pp. 915–919. [14] L. Zheng and D. N. C. Tse, “Diversity and multiplexing: A fundamental tradeoff in multiple-antenna channels, ” IEEE T rans. Inf. Theory , vol. 49, no. 5, pp. 1073–1096, May 2003. [15] T . Han and K. Kobayashi, “ A new achiev able rate region for the interference channel, ” IEEE T rans. Inf. Theory , vol. 27, no. 1, pp. 49–60, Jan. 1981. [16] G. Kramer, “Re view of rate regions for interference channels, ” in Pr oc. IEEE Int. Zurich Seminar on Commun. , Feb. 2006, pp. 162–165. [17] H.-F . Chong, M. Motani, H. Garg, and H. El Gamal, “On the Han–Kobayashi region for the interference channel, ” IEEE T rans. Inf. Theory , vol. 54, no. 7, pp. 3188–3195, Jul. 2008. [18] B. Hassibi and B. Hochwald, “How much training is needed in multiple-antenna wireless links?” IEEE T rans. Inf. Theory , vol. 49, no. 4, pp. 951–963, Apr . 2003. March 8, 2022 DRAFT
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment