A New Stream Cipher: Dicing
In this paper, we will propose a new synchronous stream cipher named DICING, which can be viewed as a clock-controlled one but with a new mechanism of altering steps. It has satisfactory performance and there have not been found weakness for the know…
Authors: ** *논문에 저자 정보가 명시되지 않음.* (저자 미상) **
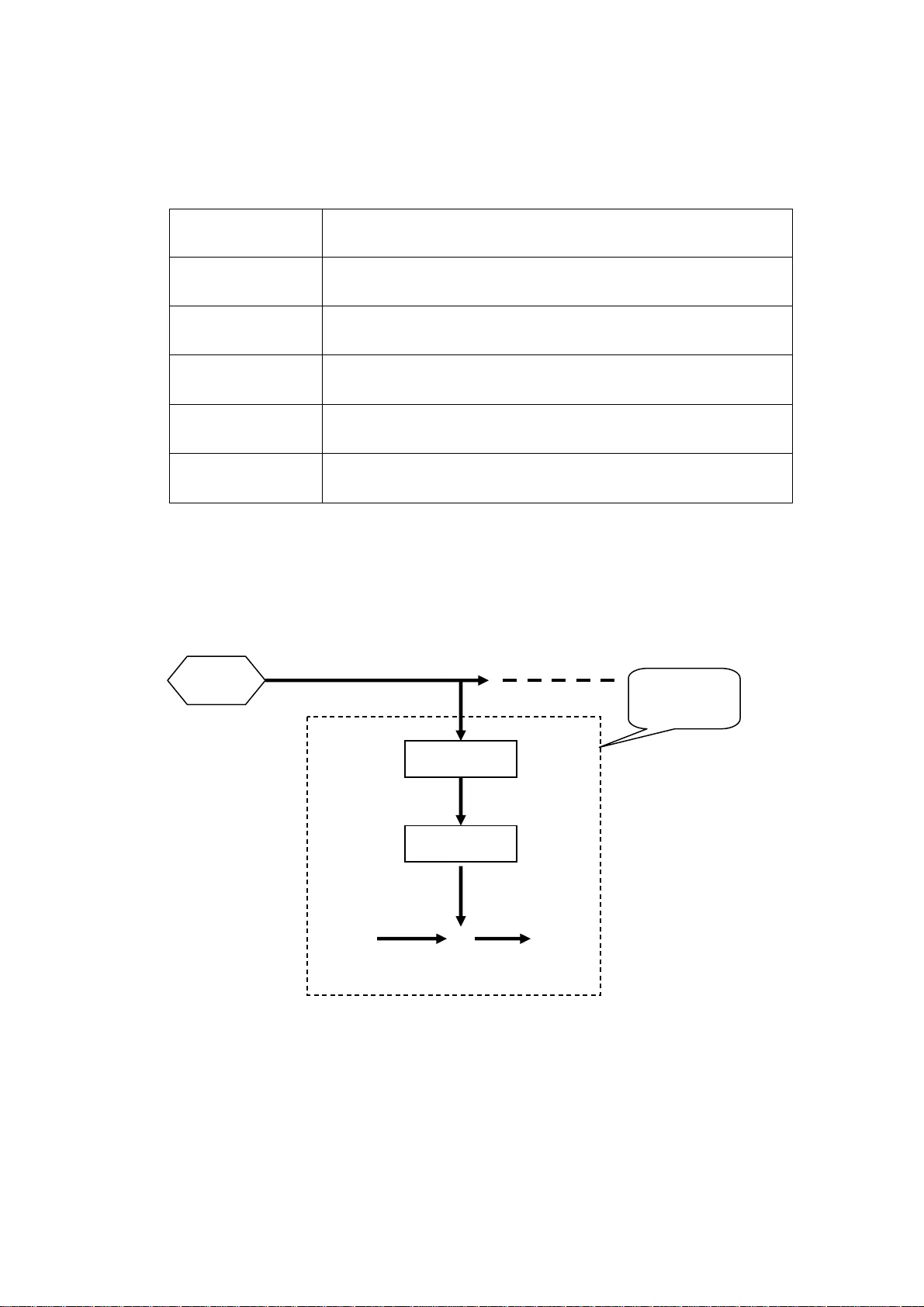
A NEW STREAM CIPHER: DICING Li An-Ping Beijing 10008 5, P .R.China apli0001@sina.com Abstract: In this paper , we will propose a new synchron ous stream cipher named DICING , which can be viewed as a cloc k-controlled one but with a new mechanism of al tering steps. W ith the simple construct ion, DICING has satisfactory performance, faster than AE S about tw o times. For the security , there have not been found weakn ess for the known a ttacks, the key sizes can be 128bits and 256bits respecti vely . . Keywords: stream cipher , LFSR, projector , finite field, correlation attac k, algebraic attack, distingui shing attack. 1. Introductio n In a synchronous stream cipher , the ciphertext is generally m ade by bitwise adding (XOR) the plaintext with a binary seque nce called keystream . In case that the cipher is a bused or the plaintext of some ciphe rtext are know n by som e people, an d so the keystream will become visible for t hem, the analysis for this case is called the plai ntext- known analysis, a secure keys tream should satisfy two basic condit ions: The fi rst is that the origina l key can not b e recovered from the keystream , the second is that the contents of the bits i n the keystream should be unpredictable for an adversary , in other words, for the a dversaries the key stream should lo ok like a random one, i.e. pseudo-random. Clearly , if the keystream sequence is periodic and the per iod is short, then it will be predictable , thus the keystream should have enough lar ge period. It is known that the technique of the linear feedback shift registers (LFSR) is able to generate the lar ger periods of sequences, so LFSRs are often used in the stream ciphers as the com ponent parts. H owever , LFSR also has an obvious weakness tha t the each bit in a LFSR’ s sequence is linearly related to the init ial state, an d so this im plies that the initial state is easy deduced from some of the later bits i n the sequenc e, the famous Berlekam p-Massey’ s algorithm is such a example of the a lgorithms. In the alm ost of known attacks such as corr elation attacks, algebr aic attacks a nd distin guishing at tacks, et c. just exploited the weakness of LFSR. So, LFSR-based stream ciphers should interfere the linear relations in the bits of the LFSRs, the clock-controlled m ethods comes from this consideration. The proposal cipher DICING m ay be taken as a cl ock-controlled one, but wit h a new mechanism of altering steps. It consists of a contr oller and a combiner . In the proposal cipher , we will substitute the LFSR with t he LFSR- like calle d projector (Pr .). A projector consists of an element t σ called state f rom some finite field ) 2 ( m GF and an updating ru le. The rule of updat ing states is that multipl ying t σ with k x , k is an integ er , namely , t k t x σ σ ⋅ = + 1 . ( 1 . 1 ) The finite fields used in here are ) 2 ( m GF , 126 , 127 , 128 or m = . In other word, the operation shift in LFSR now is replaced by multiplying k x in the fiel d ) 2 ( m GF . The key sizes in DICING ca n be 128 bits or 256 bits, and the size of init ial value may be taken as large as 256 bits, a nd the size of out put of DICIN G is 128 bits. In this paper the finite field ) 2 ( GF is simply denote d as F , and [] x F is the polynomial ring of unknown x over the fiel d F . The symbols ⊕ , ⊗ will represent the bitwise addition XOR , bitwise and, that is the operation & in C , and symbols >> , <<, | and ~ stand for the operations right-shift, left-shift , concatenate and complement respec tively . Suppose that ζ is a binary string , denoted by bit i ] [ ζ and bit j i ] , [ ζ the i -th bit and the s egment from i -th bit to j -th bit respectively , and there are the sim ilar expressions byte byte j i i ] , [ , ] [ ζ ζ and word word j i i ] , [ , ] [ ζ ζ measured in bytes and 32-bits words re spectively , and if the meaning is explicit from the context, the low-i ndex bit , byte and wor d will be omitted. 2. Construction As general stream ciphers, the proposal cipher is als o encrypt the plaintext and decrypt t h e ciphertext by adding bitwise a bina ry string called key stream, nam ely , Ciphertext Plain text Keystream = ⊕ ( 2 . 1 ) The keystream generator contai ns two main p arts, a controller H and a combiner C . The controller H is made from two project ors 1 Γ , 2 Γ and two counte rs t D ′ , t D ′ ′ which are a l so called dices. Denoted by t α and t β the states of 1 Γ and 2 Γ in time t respectively , which come from the finite fields 1 E and 2 E respectively , 11 [] / () x px = EF and 22 [] / () x px = EF , ) ( 1 x p and ) ( 2 x p are the primitive polynom ials with degree 127 and 126 respec tively , which expression are given in the List 1. They satisfy the simple recurrence e quations 88 11 ,, 0 , 1 , 2 , . . . ii ii xx i αα β β ++ =⋅ =⋅ = . ( 2 . 2 ) The dices t D ′ and t D ′ ′ are two integers to record the last eight bits of t α and t β respectively . The combiner C also contains tw o projectors 3 Γ and 4 Γ , which are based on the two finite fields 3 E and 4 E respectively , 33 [] / () x px = EF , 44 [] / () x px = EF , ) ( 3 x p and ) ( 4 x p are primitive polyn omials of degree 12 8 given in the List 1. Denot ed by t ω and t τ the states of 3 Γ and 4 Γ in the tim e t respectively , 3 t ω ∈ E and 4 t τ ∈ E . Denoted by ) ( t t t D D D ′ ′ ⊕ ′ = , 1( & 1 5 ) , t aD =+ 1( 4 ) t bD = +> > , they satisfy t b t t a t x x τ τ ω ω ⋅ = ⋅ = + + 1 1 , . ( 2 . 3 ) Besides, we use two mem orizes t u and t v to assemble t ω and t τ respectively , 11 ,, 0 tt t t t t uu vv f o r t ω τ −− =⊕ = ⊕ > , ( 2 . 4 ) The init ial valu es 00 0 ,, u ω τ and 0 v will be specified in t he later . Suppose that K is a finite field ) 2 ( 8 GF , [] / () x px = KF , ) ( x p is an irreducible polynomial of de gree eight, which expression is gi ven in the List 1. W e define S-box 0 () Sx as 127 0 () 5 ( 3 ) , Sx x x = ⋅⊕ ∈ K . ( 2 . 5 ) W e also adopt the representation ) ( 0 ζ S for a bytes string ζ to represent that S-box 0 S substitute each by te of the s tring ζ . The startup includes two subprocesses keysetup and ivsetup , where the basi c material s as the secret key and key-siz e will be input an d the internal states wi ll be initialize d . Besides, in the keysetup we will make a key-defined t he S-box () Sx from 0 () Sx and a dif fusion transform ation L . The pr ocess is as following. For a string ρ of 8 bytes, we defin e an 8-bits vec tor V ρ and a 88 × matrix M ρ : [] [ 8 ] , 0 8 , bit Vi i i i ρ ρ =+ ≤ < ul M TJ T ρ = ⋅⋅ . ( 2 . 6 ) where 8 8 , ) ( × = j i u a T and ,8 8 () li j Tb × = are the upper -triangular matrix and the l ower -triangular matrix respectively , ,, [8 ] , [8 ] , 1, 1 , 0, 0 , bit bit ij ij ij i f i j ij i f i j ai f i j b i f i j if i j if i j ρρ +< +> ⎧⎧ ⎪⎪ == = = ⎨⎨ ⎪⎪ >< ⎩⎩ ( 2 . 7 ) and J is a key-defined permutation matrix, for th e simplicity , here take 1. J = Suppose that K is the secret key , let [ 0, 1 5] [ 1 6, 3 1 ] byte byte KK λ = ⊕ , if | | 256 K = , else [0 ,15 ] byte K λ = , and [0 , 7] , [ 8 ,15 ] byte byte λ λλ λ ′′ ′ == ,define two af fine transformations on K () () , () () , Ax M x B x M x x λλ ′′ ′ == ∈ K . ( 2 . 8 ) Denoted by 1 , VV V λλ ′′ ′ =⊕ and 2 8( , 1 ) VV R O T L V λλ ′′ ′ = ⊕ , and then defin e a new S-box () Sx and a transfor mation L on 4 K , 02 1 () ( ) , AB A A B BA A B A Sx S x V V L AA B A B AB A B A ⊕ ⎛⎞ ⎜⎟ ⊕ ⎜⎟ =⊕ ⊕ = ⎜⎟ ⊕ ⎜⎟ ⊕ ⎝⎠ . (2.9) Suppose that ζ is a string of n bytes, if 4 nk = we also view it as a string of k words, and write () L ζ to represent that L takes on the each word of ζ . Simply , we denote () () QL S ζζ = ⋅ . ( 2 . 1 0 ) In the ivsetup , the second step of the startup, the internal states will be initialize d with the secret key and the initial va lue. In the generating keystream we will e mploy o ne mask of 1 6 bytes, whic h are denoted by η . For a 32-bytes string ζ we define a bytes per mutation φ : () φ ζ φ ζ = , [] [ 4 m o d 3 1 ] ii φ ζζ = , for 03 1 i ≤< , and [31 ] [31 ] φ ζζ = . Let ˆ KK = if 256 K = else ˆ |( ) KK K = ∼ , denoted by ˆˆ (~ [ 16, 31 ] ) | (~ [0,15] ) byte byte KK K = . W e defi ne the functions ˆ ( ) ( ( ) ) , ( ) ( ( ( ))) . F Q G FFF K K ζφ ζ ζ ζ == ⊕ ⊕ ( 2 . 1 1 ) Suppose that IV is the ini tial value of 32-bytes, e is the base of natural logarithm and c the integral part of 57 ! e ⋅ , and ,0 3 i i ξ ≤≤ , are four 32-bytes strings defined as 01 () , ( ) , 1 , 2 , 3 . ii GI V c G c i ξ ξξ − =⊕ = ⊕ = ( 2 . 1 2 ) The internal states are i n itialized respectively as followi ng 00 0 0 1 0 0 2 0 0 3 [ 0, 1 5] [ 16, 31 ] , ( , ) , ( , ) , ( , ) , uv η ξξ ξ α β ξ ω τ ξ ′ =⊕ = = = ( 2 . 1 3 ) where 22 2 [0,126] | [ 128 , 253] ξ ξξ ′ = , i.e. 02 02 [0,126], [ 128 , 253 ]. α ξβ ξ = = If 3 0, ξ = the states 0 ω and 0 τ will be re-set as 00 ˆ (, ) K ωτ = . ( 2 . 1 4 ) . Note For a secret key , there is at most one I V such that 3 0. ξ = After initializing, the process enters the recu rrenc e part of generating keystream , each cycle includes two s ub-processes of updatin g and combinin g. In the updating, all the states are updated from the time 1 t − to th e time t as stated in (2.2) ~ (2.4). Suppose t hat u and v are two 16-bytes strings, which are also viewed as 44 × matrices of bytes in the ordinary way . Denoted by T M the transposition of a m atrix M , the combinin g function is define d as (, ) ( ( ( ) ) ) . T Cuv Q Q u v η = ⊕⊕ ( 2 . 1 5 ) Denoted by t z the keys tream in the tim e t , (0 ) t > , then (, ) tt t zC u v = . ( 2 . 1 6 ) W e have summ arized the whole process in a sket ch as Fig. 1. List of the Primitive Po lynomials used P o l y n o m i a l s E x p r e s s i o n ) ( x p 1 5 6 8 + + + + x x x x ) ( 1 x p 127 8 9 41 3 (1 ) ( 1 ) xx x x + ++ + ) ( 2 x p 126 83 35 7 (1 ) ( 1 ) xx x x + ++ + ) ( 3 x p 128 96 67 32 3 (1 ) ( 1 ) xx x x x + ++ + + ) ( 4 x p 128 96 64 37 7 5 (1 ) ( 1 ) xx x x x x + +++ + + List 1 The Sketch of Encryption Process Initializing Updating states (, ) Cuv K e y s t r e a m P l a i n t e x t ⊕ C i p h e r t e x t Fig.1 3. Security Analysis In this section, we firstly show some results about the periods of the keystream of the stream cipher Dicing, and t hen give an in vestigation with res pect to standard cryptanalytic attacks. This is the recurren ce part Denote () t z π as the period of a s equence t z . Proposition 1 126 127 ( ) ( 2 1) ( 2 1) , t D π = −− ( 3 . 1 ) 126 127 128 ( ) ( ) (2 1 ) (2 1 ) (2 1 ) / 3 tt πω π τ == − − − ( 3 . 2 ) Proof. Not e that polynomia ls ) ( 1 x p and ) ( 2 x p are primitive, and the order of x in the fields 1 E and 2 E are 1 2 127 − and 1 2 126 − respectively , hence 127 126 () 2 1 , () 2 1 tt πα π β = −= − , ( 3 . 3 ) and equation (3.1) is followed for 126 127 (2 1 , 2 1 ) 1 − −= . W rite 1 i k ii x ωω − =⋅ , and let ) 1 2 )( 1 2 ( 126 127 − − = n , 0 i in mk <≤ = ∑ , it is easy to calcula te that for each integer ,1 1 6 cc <≤ , the occurrence times of c in the sum above is 249 123 122 22 2 −− a nd integer 1 occurs one more tim es than the num ber . Thus, 249 123 122 ( 2 2 2 ) 136 1 m =− − ⋅ + , ( 3 . 4 ) and 124 12 5 1 7 00 m n xx ωω ω − ⋅⋅ =⋅ =⋅ ( 3 . 5 ) In the field 3 E or 4 E , the order of x is eq ual to 128 21 − , and 128 124 (2 1 , 2 5 1 7 1 ) 3 − ⋅⋅ − = , t h e f o r m u l a ( 3 . 2 ) i s f o l l o w e d . Note that 11 ,, tt t t t t uu vv ω τ −− ⊕= ⊕ = so we have Corolla ry 1 126 127 128 ( ), ( ) ( 2 1 )( 2 1 )( 2 1 ) / 3 tt uv ππ ≥− − − . ( 3 . 6 ) In the next, we gi ve a discussion for Dicing in res pect to the resistance to t he main know n attacks. W e known that the correlation equatio n s of the com ponents in combining or filter functions sho uld be known is r equired for the correla tion attack, distinguishing attack and al gebraic attac k. In the proposed cipher , the updating of the co mponents t ω and t τ are controlled by Pr .’ s 1 Γ and 2 Γ , and their correlations are not known for the advers aries, so these a ttacks will not be feasible. As Dicing has a lar ger size of internal states, a nd the ir updating oper ations are multiplic ations of the finite fiel d 128 (2 ) GF , and there are no the correspondences between some sm aller isolated parts of the states and the keystream, hence th er e will be no flaws for the time/mem ory/data trade-off att acks and guess-and-determine attacks. The initializat ion and com b ining function s also have protected DICIN G against the chos en-IV attacks, collision attacks and inversion attacks. W ith our reference code, t h ere are not found rem arkable timing gaps for tim ing attack. 4. Implementation In the platform of 32-bi t W indows OS and AMD Athlo n(tm) 64 x2 Dual C o re processor 3600+, 2.00G Borland C+ + 5.0, the perform ance of DICING is as following Report of Performance Sub-processes Tim e or Rate K e y s e t u p 5 2 0 0 cycles I V s e t u p 2 2 8 0 cycles K e y s t r e a m R a t e 1 0 cycles/byte or 1 60 cycles/block List 2 5. The r educed versions and variants of DICING The algorithm DI CING presented above is a very conservative one, t he users who wish to stri ve for a faster rate m ay adopt the reduced versions and variants. In the following are some such ones, and we think the reduc ed one will also have suf ficient security . 1. Simply take t he combining function (, ) ( ) , Cuv Q u v = ⊕ ( 5 . 1 ) and omit the P r . 2 Γ . 2. In the case there are no attacks for condi tional br anching, the combining function m ay be taken as () [ 0 ] 0 , (, ) () [ 0 ] 1 . Qu v i f Cuv Qv u i f α α ⊕ = ⎧ = ⎨ ⊕ = ⎩ ( 5 . 2 ) 3. Furthermore, omit both Pr . 1 Γ and Pr . 2 Γ , and instead, let [1 5 ] [1 5 ] . dice ω τ = ⊕ ( 5 . 3 ) 4. T o obtain a la rger per i od of keystream , the two Pr .’ s , 3 Γ a n d 4 Γ may be rep laced by a Pr . ˆ Γ from a finite field 256 (2 ) GF , i.e. ˆ [] / () x px F , ˆ () p x is a prim itive polynomial of degree 256 . For 32-bit processors, ˆ () p x m a y be taken as 256 224 192 161 128 96 67 32 6 ˆ () ( 1 ) ( 1 ) px x x x x x x x x x = + + + + ++ ++ + . (5.4) The presented algorithm DICING was one of candida tes for eSTREAM [1], [2], but with a little difference from [2] in (2.8) an d (2.9), here the vector 1 V has been moved into S-box () Sx from the transformation () A x . References [1] A.P . Li, A New Stream Cipher: DICING , now available at http://w ww .ecrypt.eu.or g /stream/dicing .html [2] A.P . Li, ------An update for phase2 of eSTREAM, now available at eSTREAM - The ECR YPT S tream Cipher Project - Phase 2
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment