WiFi Epidemiology: Can Your Neighbors Router Make Yours Sick?
In densely populated urban areas WiFi routers form a tightly interconnected proximity network that can be exploited as a substrate for the spreading of malware able to launch massive fraudulent attack and affect entire urban areas WiFi networks. In t…
Authors: ** Hu et al. (구체적인 저자명은 논문 원문에 명시되어 있지 않음) **
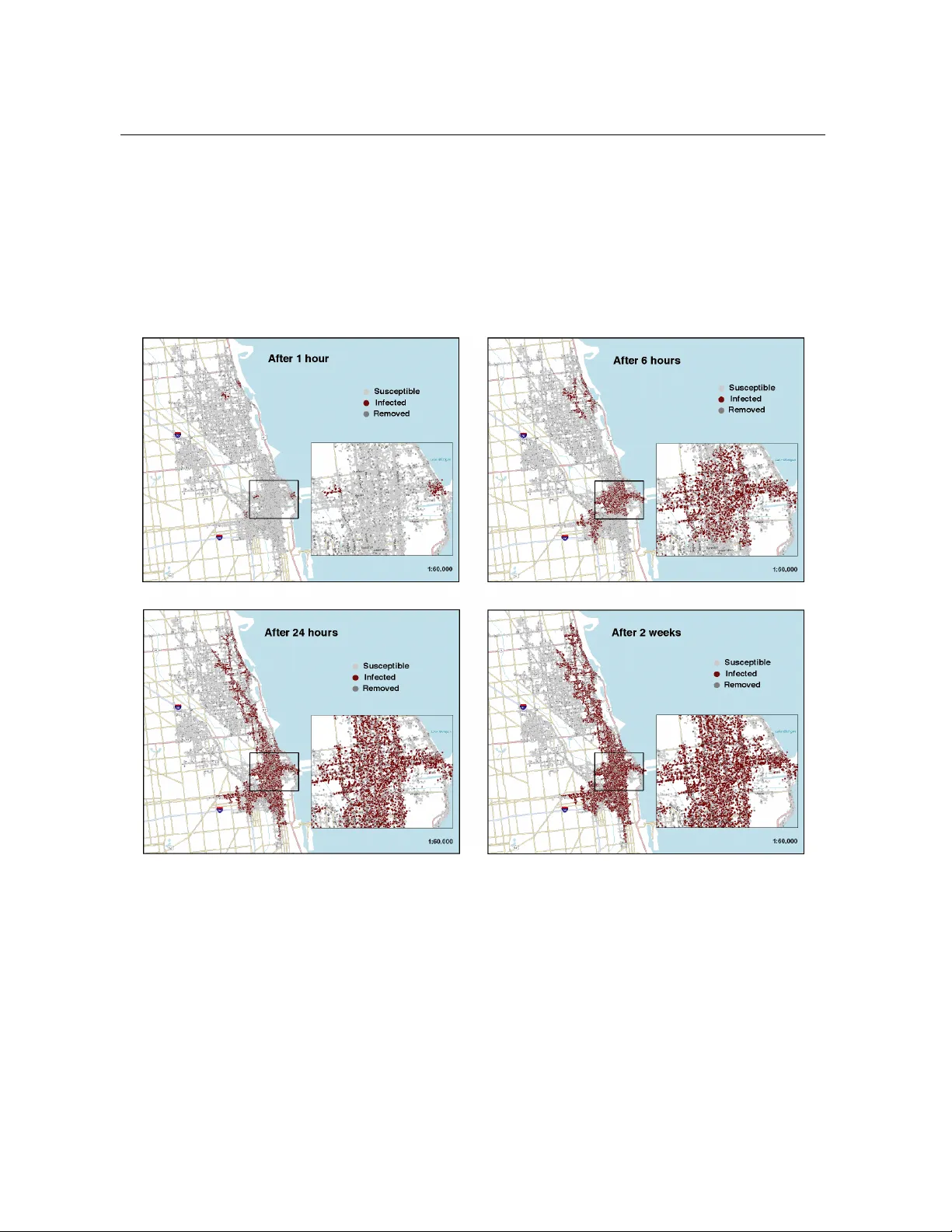
W iFi Epidemiology: Can Y our Neighbors’ Router Make Y ours Sick? Hao Hu 1 , 2 , Ste ven Myers 2 , ∗ , V ittoria Colizza 2 , 3 , Alessandro V espignani 2 , 3 October 24, 2018 1 Department of Physics, Indiana Uni versity , Bloomington, IN 47405, USA 2 School of Informatics, Indiana Uni versity , Bloomington, IN 47406, USA 3 Complex Netw orks Lagrange Laboratory , Institute for Scientific Interchange (ISI), T orino 10133, Italy ∗ e-mail: samyers@indiana.edu In densely populated urban areas W iFi r outers form a tightly inter connected pr oximity network that can be exploited as a substrate f or the spreading of malware able to launch massive fraudulent attack and affect entire urban areas WiFi networks. In this paper we consider several scenarios f or the deployment of malware that spr eads solely over the wireless channel of major urban areas in the US. W e develop an epidemiological model that tak es into consideration pr ev alent security flaws on these routers. The spr ead of such a contagion is simulated on r eal-world data for geo-referenced wireless routers. W e un- cover a major weakness of W iFi networks in that most of the simulated scenarios show tens of thousands of r outers infected in as little time as two weeks, with the majority of the infections occurring in the first 24 to 48 hours. W e indicate possible containment and pre vention measur e to limit the ev entual harm of such an attack. Correspondence and requests for material should be addressed to S.M. (samyers@indiana.edu) or A.V . (alexv@indiana.edu). 1 Hu et al. The use of W iFi routers is becoming close to mainstream in the US and Europe, with 8.4% and 7.9% of all such respecti ve households having deployed such routers by 2006 1 , and a W iFi market e xpected to grow quickly in the next few years as more ne w digital home devices are being shipped with W iFi technology . In 2006 alone 200 million W iFi chipsets were shipped worldwide, representing nearly half of the 500 million cumulati ve total 2 . As the W iFi deploy- ment becomes more and more pervasi v e, the larger is the risk that massi ve attacks exploiting the W iFi security weaknesses could af fect lar ge numbers of users. Recent years hav e witnessed a change in the designers behind a malw are attack and in their moti v ations, corresponding to the ev er increasing sophistication needed to bypass newly de veloped security technologies. Malware creators hav e shifted from programmer enthusiasts attempting to get peer credit from the “hacker” community , to organized crime engaging in fraud and money laundering through dif ferent forms of online crime. In this context W iFi routers represent v aluable targets when compared to the PC’ s that malware traditionally infect, as they hav e sev eral dif fering properties representing strong incentiv es for the attacks. They are the perfect platform to launch a number of fraudulent attacks 3,4,5,6 that pre vious security technologies hav e reasonably assumed were unlikely 7 . Unlike PCs, they tend to be always on and connected to the Internet, and currently there is no software aimed at specifically detecting or prev enting their infection. Further , as routers need to be within relati vely close proximity to each other to communicate wirelessly , an attack can no w take advantage of the increasing den- sity of W iFi routers in urban areas that creates large geographical networks where the malware can propagate undisturbed. Indeed, man y W iFi security threats ha ve been downplayed based on the belief that the physical proximity needed for the potential attack to occur would represent an obstacle for attackers. The presence no wadays of large ad-hoc networks of routers make these vulnerabilities considerably more risky than pre viously belie ved. Here we assess for the first time the vulnerability of W iFi networks of dif ferent US cities by simulating the wireless propagation of malw are, a malicious worm spreading directly from wireless router to wireless router . W e construct an epidemiological model that takes into ac- 2 Hu et al. count sev eral widely known and prev alent weaknesses in commonly deployed W iFi routers’ security 3,8 , (e.g., default and poor password selection and cracks in the WEP cryptographic protocol 9 ). The W iFi proximity networks o ver which the attack is simulated are obtained from real-world geographic location data for wireless routers. The infection scenarios obtained for a v ariety of US urban areas are troublesome in that the infection of a small number of routers in most of these cities can lead to the infection of tens of thousands of routers in a week, with most of the infection occurring in the first 24 hours. W e address quantitati vely the behavior of the spreading process and we provide specific suggestions to minimize the W iFi netw ork weakness and mitigate an e ventual attack. Results and Discussion W iF i networks . W iFi routers, e ven if generally deployed without a global or ganizing princi- ple, define a self-org anized proximity communication network. Indeed, any two routers which are in the range of each other’ s W iFi signal can e xchange information and may define an ad-hoc communication network. These networks belong to the class of spatial or geometric networks in that nodes are embedded in a metric space and the interaction between two nodes strongly depends on the range of their spatial interaction 10,11,12,13 . In this perspecti ve, one might wonder if the actual deployment of W iFi routers is suf ficient at the moment to generate lar ge connected networks spanning sizeable geographic areas. This problem, equiv alent to the percolation of giant connected component in graph theory 14,15 , is ho wev er constrained by the urban area’ s topology and demographic distrib ution dictating the geographical locations of W iFi routers. H ere we consider WiFi networks as obtained from the public worldwide database of the W ireless Geographic Logging Engine (W iGLE) web- site 16 . The database collects data on the worldwide geographic location of wireless routers and counts more than 10 million unique networks on just under 600 million observations 17 , providing good coverage of the wireless networks in the United States and in North Central Europe. The data provide a wealth of information that include, among other things, the routers’ geographic locations (expressed in latitude LAT and longitude LON ) and their encryption sta- 3 Hu et al. tuses. In particular , we focused on the wireless data extracted from se ven urban areas or regions within the United States – Chicago, Boston, Ne w Y ork City , San Francisco Bay Area, Seattle, and Northern and Southern Indiana. Starting from the set of vertices corresponding to geo- referenced routers in a gi ven region, we construct the proximity network 10,11,12,13 by drawing an edge between any two routers i and j located at ~ p i = ( LO N i , LAT i ) and ~ p j = ( LO N j , LAT j ) , respecti vely , whose geographical distance d ( ~ p i , ~ p j ) is smaller than the maximum interaction radius R int (i.e., d ( ~ p i , ~ p j ) ≤ R int ), as shown in Figure 1A. In the W iFi networks, the maxi- mum interaction radius R int strongly depends on the local en vironment of an y specific router . In practice, R int ranges from 15m for a closed office with poor transmission to approximately 100m outdoors 18 . For simplicity , we assume that R int is constant, independent of the actual location of a gi ven router , and we consider four dif ferent values of the maximum interaction radius — R int ∈ { 15m, 30m, 45m, 100m } — analyzing the resulting networks for each of the seven regions under study . A more detailed account of the network construction procedure and the filtering methods used to minimize potential biases introduced by the data collection mechanisms are described in the Materials and Method section. In Figure 1B we report an illustration of the giant component of the network obtained in the Chicago area for different values of R int . It is possible to observe that despite the clear geographical embedding and the city constraints, a large network of more than 48,000 routers spans the do wntown area for R int set to 45 meters. The degree distributions of the giant com- ponents, reported in Figure 1C, are characterized by an exponential decrease 12 with a cutoff clearly increasing with the interaction radius, since a larger range increases the number k of nodes found within the signal area. V ery similar properties are observed in all the networks analyzed. It is important to stress that the metric space embedding exerts a strong prev entati ve force on the small-world behavior of the W iFi networks, since the limited W iFi interaction rules out the possibility of long range connections. Infecting a Router . The infection of a susceptible router occurs when the malware of an al- ready infected router is able to interface with the susceptible’ s administrativ e interface o ver the 4 Hu et al. wireless channel. T wo main technologies aim at pre v enting such infection through i) the use of encrypted and authenticated wireless channel communication through the WEP and WP A cryp- tographic protocols, and ii) the use of a standard password for access control. The encryption should provide a higher lev el of security , as it needs to be bypassed before a potential attacker could attempt to enter the router’ s password. Most users do not currently employ their routers encryption capabilities – indeed the encryption rates in the considered cities vary from 21% to 40% of the population. For the purposes of this work we assume that WP A is not vulnerable to attack 1 , and therefore any router that uses it is considered immune to the worm. Because of cryptographic fla ws in WEP , this protocol can alw ays be brok en given that the attacker has access to enough encrypted communication. This can be achiev ed by waiting for the router to be used by legitimate clients, or by deploying more advanced activ e attacks. Bypassing WEP encryption is therefore feasible and only requires a gi ven amount of time. Once the malware has bypassed any cryptographic protocol and established a communica- tion channel, it may then attempt to bypass the passw ord. A lar ge percentage of users do not change their password from the default established by the router manufacturer , and these pass- words are easily obtainable. F or legal reasons it is difficult to measure exactly what this percent- age is, so here we use as a proxy the percentage of users who do not change their routers def ault SSID. For all the other routers, we assume that 25% of them can have the passw ord guessed with 65,000 login attempts, based on the e vidence provided by security studies 19 which sho wed that ≈ 25% of all users passwords are contained in a dictionary of 65,000 words. W e then pessimistically assume, based on pre vious worms, that another 11% of passwords are contained in a larger library of approximately a million words 20 . No backof f mechanism exists on the routers that prev ents systematic dictionary attacks. In case the password is not found in either dictionary , the attack cannot proceed. Alternati vely , if the password has been ov ercome, the attacker can upload the worm’ s code into the router’ s firmw are, a process that typically takes just a fe w minutes. In the Material and Methods section we report a list of the typical time 1 This is not completely accurate, see supplementary discussion for a more in depth discussion. 5 Hu et al. scales related to each step of the attack strategy . Construction of the epidemic model . The construction of the wireless router network defines the population and the related connectivity pattern over which the epidemic will spread. In or- der to describe the dynamical ev olution of the epidemic (i.e., the number of infected routers in the population as a function of time) we use a framew ork analogous to epidemic modeling that assumes that each indi vidual (i.e. each router) in the population is in a gi v en class depending on the stage of the infection 21 . Generally , the basic modeling approaches consider three classes of indi viduals: susceptible (those who can contract the infection), infectious (those who contracted the infection and are contagious), and recovered (those who recovered or are immune from the disease and cannot be infected). In our case the heterogeneity of the W iFi router population in terms of security attributes calls for an enlarged scheme that takes into account the dif ferences in the users’ security settings. W e consider three basic le vels of security and identify the cor- responding classes: routers with no encryption, which are obviously the most e xposed to the attack, are mapped into a first type of susceptible class S ; routers with WEP encryption, which provides a certain le vel of protection that can be ev entually ov ercome with enough time, are mapped into a second type of susceptible class denoted S WEP ; routers with WP A encryption, which are assumed to resist any type of attacks, correspond to the removed class R . This clas- sification ho wev er needs to be refined to take into account the password settings of the users that range from a def ault password to weak or strong passwords and finally to non-crackable passwords. For this reason, we can think of the non-encrypted class S as being subdivided into four subclasses. First, we distinguish between the routers with default password S nop ass and the ones with password S pass 1 . The latter contains routers with all sorts of passw ords that undergo the first stage of the attack which employs the smaller dictionary . If this strategy fails, the routers are then classified as S pass 2 and undergo the attack which emplo ys the larger dictio- nary . Finally , if the password is unbreakable, the router is classified as R hidden . The last class represents routers whose password cannot be bypassed. Howe v er , their immune condition is hidden in that it is known only to the attacker who f ailed in the attempt, while for all the others 6 Hu et al. the router appears in the susceptible class as it was in its original state. This allo ws us to model the unsuccessful attack attempts of other routers in the dynamics. WEP encrypted routers have the same properties in terms of passw ord, b ut the password relev ance starts only when the WEP encryption has been broken on the router . At this stage of the attack it can be considered to be in the non-encrypted state, and therefore no subclasses of S WEP hav e to be defined. In addition to the above classes, the model includes the infected class ( I ) with those routers which ha ve been infected by the malware and ha v e the ability to spread it to other routers. The model dynamics are specified by the transition rates among dif ferent classes for routers under attack. T ransitions will occur only if a router is attack ed and can be described as a reaction process. For instance the infection of a non-encrypted router with no password is represented by the process S nop ass + I → 2 I . The transition rates are all expressed as the in verse of the av erage time needed to complete the attack. In the above case the a verage time of the infection process is τ = 5 minutes and the corresponding rate β for the transition S nop ass + I → 2 I is β = τ − 1 . Similarly the time scale τ WEP needed to break a WEP encryption will define the rate β WEP ruling the transition from the S WEP to the non-encrypted class. In the Materials and Methods section we report in detail all the transition processes and the associated rates defining the epidemic processes. One of the most common approaches to the study of epidemic processes is to use deter - ministic differential equations based on the assumption that individuals mix homogeneously in the population, each of them potentially in contact with e very other 21 . In our case, the static non-mobile nature of wireless routers and their geographical embedding make this assumption completely inadequate, sho wing the need to study the epidemic dynamics by explicitly consider - ing the underlying contact pattern 22,23,24,25,26 . F or this reason, we rely on numerical simulations obtained by using an individual-based modeling strategy . At each time step the stochastic dis- ease dynamics is applied to each router by considering the actual state of the router and those of its neighbors as defined by the actual connectivity pattern of the network. It is then possible to measure the e volution of the number of infected individuals and keep track of the epidemic 7 Hu et al. progression at the lev el of single routers. In addition, gi ven the stochastic nature of the model, dif ferent initial conditions can be used to obtain different e v olution scenarios. As multiple seed attacks are likely we report simulations with initial conditions set with 5 infected routers randomly distributed within the population under study . Single seed attacks and different number of initial seeds hav e similar ef fects. The initial state of each router is directly gi v en by the real W iFi data or is obtained from estimates based on real data, as detailed in the Material and Methods section. Finally , for each scenario we perform av erages ov er 100 realizations. Spr eading of synthetic epidemics . According to the simulation procedure outlined abo ve we study the behavior of synthetic epidemics in the sev en urban areas we used to characterize the properties of W iFi router networks. The urban areas considered are quite di v erse in that they range from a relativ ely small colle ge town as W est Laf ayette (Indiana) to big metropolis such as Ne w Y ork city and Chicago. In each urban area we focus on the giant component of the network obtained with a gi ven R int that may v ary consistently in size. Here we report the results for a typical epidemic spreading scenario in which the time scales of the processes are chosen according to their av erage estimates. The best and worst case scenarios could also be obtained by considering the combination of parameters that maximize and minimize the rate of success of each attack process, respectiv ely . The networks used as substrate are obtained in the intermediate interaction range of 45m. The four snapshots of Figure 2 provide an illustration of the e volution of a synthetic epi- demic in the Chicago area; sho wn in red are the routers which are progressi vely infected by malware. The striking observ ation is that the malw are rapidly propagates on the W iFi network in the first fe w hours, taking control of about 37% of the routers after two weeks from the in- fection of the first router . The quantitati v e evidence of the potential impact of the epidemic is reported in Figure 3A-B, where the av erage profile of the density of infected routers is reported for all the urban areas considered in the numerical e xperiment, together with the corresponding fluctuations. While it is possible to notice a considerable difference among the v arious urban 8 Hu et al. areas, in all cases we observ e a sharp rise of the epidemic within the first couple of days and then a slo wer increase, which after two weeks lea ves about 10% to 55% of the routers in the giant component controlled by malware. The similar time scale in the rise of the epidemic in dif ferent urban areas is not surprising as it is mainly determined by the time scale of the specific attacks considered in the malware spreading model. In general the sharp rise of the epidemic in its early stages is due to the non-encrypted routers which are infected in a v ery short time. The slo wer progression at later stages is instead due to the progressi v e infection of WEP routers whose attack time scale is about one order of magnitude longer . Single realization results clearly sho w the effect of the interplay of dif ferent time scales in volved in the spreading phenomenon. A more complicated issue is understanding the dif ferent attack (infection) rates that the epi- demic attains in dif ferent urban area networks. The pervasi v eness of the epidemic can be seen as a percolation effect on the W iFi network 27,28 . The WP A encrypted routers and those with unbreakable passwords represent obstacles to the percolation process and define an effecti v e percolation probability that has to be compared with the intrinsic percolation threshold of the network 28,29,30 . The lar ger the ef fectiv e percolation probability with respect to the threshold, the larger the final density of infected routers. On the other hand, the epidemic thresholds of the networks are not easy to estimate because they are embedded in the particular geometries of the cities’ geographies. In random netw orks, lar ge a verage de gree and large degree fluctuations fa vor the spreading of epidemics and tend to reduce the network percolation threshold 26,31 . Fig- ure 3C-D sho ws an appreciable statistical correlation between the attack rate and these quan- tities. On the other hand, there are many other network features that affect the percolation properties of the networks. First, the cities have dif ferent fractions of encrypted routers. While these fraction are not e xtremely dissimilar , it is clear that gi v en the non-linear effect close to the percolation threshold, small differences may lead to large difference in the final attack rate. F or instance, San Francisco, with the largest fraction of encrypted routers corresponding to about 40% of the population, e xhibits the smallest attack rate amongst all the urban areas considered. Second, the geometrical constraints imposed by the urban area geography may hav e a large im- 9 Hu et al. pact on the percolation threshold, which can be rather sensiti ve to the local graph topology . For instance, network layouts with one dimensional bottlenecks or locally very sparse connectivity may consistently lo wer the attack rate by sealing part of the network, and thus protecting it from the epidemic. Indeed, a fe w WP A routers at k ey bottlenecks can make entire subnetworks of the giant component impenetrable to the malware. The present results offer general quantitati ve conclusions on the impact and threat of fered by the W iFi malware spreading in different areas, whereas the impact of specific geographical properties of each urban area on the epidemic pattern will be the object of further studies. Conclusions Based on this w ork, we note that there is a real concern about the wireless spread of W iFi based malware. This suggests that action needs to be taken to detect and pre vent such out- breaks, as well as more thoughtful planning for the security of future wireless de vices, so that such scenarios do not occur or worsen with future technology . For instance, given the increas- ing popularity of 802.11n, with its increased wireless communications range, the possibility for larger infections to occur is heightened, due to the lar ger connected components that will emerge. Further , man y de vices such as printers, and D VR systems no w ship with 802.11 radios in them, and if they are programmable, as man y are, the y become vulnerable in manners similar to routers. Lastly , it is highly likely that we will only see the proliferation of more wireless standards as time goes by , and all of these standards should consider the possibility of such epidemics. There are two prev enti ve actions that can be easily considered to successfully reduce the rates of infection. First, force users to change default passwords, and secondly the adoption of WP A, the cryptographic protocol meant to replace WEP that does not share its cryptographic weaknesses. Unfortunately , the dangers of poorly chosen user passwords hav e been widely publicized for at least two decades no w , and there has been little e vidence of a change in the public’ s beha vior . In addition, there are many barriers to public adoption of WP A on wireless routers. The use of only one device in the home that does not support WP A, but that does 10 Hu et al. support the more widely implemented WEP , is sufficient to encourage people to use WEP at home. Howe ver , unlike the more traditional realm of internet malware, the lack of a small world contagion graph implies that small increases in the deployment of WP A or strong passwords can significantly reduce the size of a contagion graph’ s largest connected component, significantly limiting the impact of such mal ware. In future work we plan a detailed study of the percolation threshold of the giant component as a function of the proportion of WP A immune nodes in order to provide quantitati v e estimates for the systems’ immunization thresholds. Materials and Methods W iF i Data and Networks . WiFi data is do wnloaded from the W iGLE website 16 for se ven urban areas in the US and is processed in order to eliminate potential biases introduced by data collection. Records that appear as pr obe in their type classification are remov ed from the dataset since they correspond to wireless signals originating from non-routers. Such records represent a very small percenta ge of the total number in ev ery city considered. For example, in the Chicago urban area there were 4433 pr obe records, corresponding to 3.7% of the total. A preliminary spatial analysis of the data for each urban area re veals the presence of sets of se veral W iFi routers sharing an identical geographic location. In order to av oid biases due to ov errepresentation of records, we check ed for unique BSSID (i.e., MA C address) and assume that each of these locations could contain at most n overlapping routers, where n was fixed to 20 to provide a realistic scenario, such as a building with sev eral hotspots. F or the Chicago urban area, this procedure led to the elimination of 3194 records, which represent 2.7% of the total number of W iFi routers. More importantly , we adopt a randomized procedure to redefine the position of each router in a circle of radius R ran centered on the GPS coordinates provided by the original data. This procedure is applied to approximate the actual location of each router which would be otherwise localized along city streets, due to an artifact of the wardri ving data collection method 16,32 . The ne wly randomized positions for the set of routers completely determine the connecti vity pattern of the spatial W iFi network and its giant component substrate for the epidemic simulation. Re- 11 Hu et al. sults presented here are obtained as 5 av erages over se veral randomization procedures. T able 1 reports the main topological indicators of the giant components of each urban area extracted from the W iFi network b uilt assuming R int = 45 m. Epidemic model . Figure 4 sho ws the flo w diagram of the transmission model. Initial conditions set the number of routers belonging to each of the follo wing compart- ments: S nopass (routers with no encryption and def ault password), S pass 1 (routers with no en- cryption and user set password), S WEP (routers with WEP encryption), and R (routers with WP A encryption, here considered immune). The classes S pass 2 and R hidden are void at the beginning of the simulations since they represent follo wing stages of the infection dynamics. Encrypted routers are identified from original data, and the fraction of R out of the total number of encrypted routers is assumed to be 30% , in agreement with estimates on real world WP A usage. Analogously , we assume that the non-encrypted routers are distributed according to the follo wing proportions: 50% in class S nopass and 50% in class S pass 1 . The infection dynamics proceeds as follo ws. A router with no encryption enters the infec- tious class with unitary rate β if attacked. The attack to a router in class S pass 1 is characterized by a transition rate β 1 and has two possible outcomes: with probability (1 − p 1 ) the router is infected and enters I , whereas with probability p 1 it enters S pass 2 since the attacker is not able to ov ercome the password and the infection attempt requires additional time and resources. Once in class S pass 2 , it can become infectious with probability (1 − p 2 ) if the attack is successful, or otherwise the router enters R hidden with probability p 2 because the password has not been bypassed. This process occurs with a transition rate β 2 . WEP encrypted routers follow the same dynamics once the encryption is broken and the y enter S pass 1 with transition rate β W EP . The numerical simulations consider the discrete nature of the individuals and progress in discrete time steps. W e assume that t he attack er will tar get the router, among its neighbors, with the lo west security settings. In addition, we do not allo w simultaneous attacks, so that each infected router will choose its next target only among those routers which are not already under attack. Once an attack has started, the attacker will keep trying to bypass the security setting 12 REFERENCES Hu et al. of the same target until the attempt is finally successful or not. In both cases, the attacker will then mov e to another target. The simulation’ s unitary time step is defined by the shortest time scale among all processes in volv ed, i.e. the time τ needed to complete an attack to a non- encrypted router with no password. This automatically defines as unitary the transition rate β associated to the reaction S nop ass + I → 2 I , gi ven β τ = 1 . T ypical time scales for the other processes are: τ 1 = 6 – 15 minutes to bypass a password in the smaller dictionary , τ 2 = 400 – 1000 minutes to bypass a passw ord in the lar ger dictionary , τ W EP = 2880 – 5760 minutes to crack the WEP encryption. The corresponding transition rates can be analogously defined as probabilities expressed in terms of their ratio with β that defines the unitary rate. Simulations run for 4,032 time steps, corresponding to 20,160 minutes (i.e., 2 weeks). At each time step we measure the global attack rate defined as the number of infectious I ( t ) at time t o ver the total population of the netw ork discounted by the number of recov ered, N − R . In this way , we can tak e into account for the dif ferences of the encryption percentages observed in dif ferent urban areas. Gi ven the stochasticity of the process, the numerical simulations are repeated 100 times changing initial conditions and assuming different configurations of the randomized network. A verage v alues and corresponding confidence intervals are also measured. Acknowledgments H.H. thanks the Institute for Scientific Interchange in T urin for its hospitality during the time this work was completed. A.V . is partially supported by the NSF award IIS-0513650. Refer ences 1. Mercer , D. (2006) Home Network Adoption: W i-F i Emer ges As Mass Market Phenomenon (Market Report). http://www .strategyanalytics.net/default.aspx?mod=ReportAbstract V iewer&%a0=2909. 13 REFERENCES Hu et al. 2. T elecoms Europe website. (2007) W i-fi c hipset shipments r eac h 200m in 2006 – r eport . http://www .telecomseurope.net/article.php?id article=3549. 3. Stamm, S., Ramzan, Z., and Jak obsson, M. (2006) Drive-by pharming (T echnical Report 641, Indiana Uni versity). 4. Ollmann, G. (2006) The pharming guide (T echnical report, Ne xt Generation Security Soft- ware Ltd.). 5. Jakobsson, M. and Myers, S. editors. (2007) Phishing and Countermeasures: Undertand- ing the Incr easing Pr oblem of Electr onic Identity Theft (W ile y). 6. Soghoian, C. (2007) A deceit-augmented man in the middle attack against Bank of Amer- ica’ s SiteK e y service . http://paranoia.dubfire.net/2007/04/deceit-augmented-man-in-middle-attack.html. 7. Myers, S. and Stamm, S. (2007) T rawler phishing (Submitted to Computer and Communi- cations Security Conference). 8. Tsow , A., Jakobsson, M., Y ang, L. and W etzel, S. (2006) J ournal of Digital F or ensic Pr ac- tice , 1 , Special Issue 3. 9. Bittau, A., Handley , M. and Lackey , J. (2006) SP ’06: Pr oceedings of the 2006 IEEE Symposium on Security and Privacy (S&P’06) (W ashington, DC, USA. IEEE Computer Society), 386 – 400 10. Dall, J. and Christensen, M. (2002) Phys. Rev . E , 66 , 016121. 11. Nemeth, G. and V attay , G. (2003) Phys. Rev . E , 67 , 036110. 12. Herrmann, C., Barth ´ elemy , M. and Prov ero, P . (2003) Phys. Rev . E , 68 , 026128. 13. Helmy , A. (2003) IEEE Comm. Lett. , 7 , 490 – 492. 14 REFERENCES Hu et al. 14. Molloy , M. and Reed B. (1995) Random Struct Alg. , 6 , 161 – 179. 15. Bollobas, B. and Riordan, O. (2006) P er colation (Cambridge Uni versity Press). 16. W iGLE: W ireless Geographic Logging Engine. http://www .wigle.net/. 17. W iGLE General Stats, first accessed on Febrary , 2007. http://www .wigle.net/gps/gps/main/stats/. 18. Gast, M. (2005) 802.11 W ir eless Networks: The Definitive Guide, Second Edition (O’Reilly). 19. Klein, D. V . (1990) Pr oceedings of the second USENIX W orkshop on Security , 5 – 14. 20. Jeff, J., Alan, Y ., Ross, B. and Alasdair , A. (2000) The memorability and security of pass- wor ds – some empirical results (T echnical Report No. 500, Computer Laboratory , Univ er- sity of Cambridge). http://www .ftp.cl.cam.ac.uk/ftp/users/rja14/tr500.pdf 21. Anderson, R. M. and May , R. M. (1992) Infectious Diseases of Humans: Dynamics and Contr ol (Oxford Uni v . Press, Oxford). 22. W atts, D. J. and Strogatz, S. H. (1998) Natur e , 393 , 440 – 442. 23. Barab ´ asi, A. L. and Albert, R. (1999) Science , 286 , 509 – 512. 24. Keeling, M. J. (1999) Pr oc. R. Soc. Lond. B , 266 , 859 – 867. 25. Moore, C. and Newman, M. E. J. (2000) Phys. Re v . E , 61 , 5678 – 5682. 26. Pastor -Satorras, R. and V espignani, A. (2001) Phys. Rev . Lett. , 86 , 3200 – 3203. 27. Grassberger , P . (1983) Math. Biosci. , 63 , 157 –172. 28. Ben-A vraham, B. and Ha vlin, S. (2000) Diffusion and Reactions in F ractals and Disor der ed Systems (Cambridge Uni versity Press). 15 REFERENCES Hu et al. 29. Cohen, R., Erez, K., Ben-A vraham, D. and Havlin, S. (2000) Phys. Rev . Lett. , 85 , 4626 – 4628. 30. Callaway , D. S., Ne wman, M. E. J., Strogatz, S. H. and W atts, D. J. (2000) Phys. Re v . Lett. , 85 , 5468 – 5471. 31. Lloyd, A. L. and May , R. M. (2001) Science , 292 ,1316 – 1317. 32. W ardri ving. http://www .wardri ving.com/. 16 T ABLES AND FIGURES Hu et al. T able and Figur e captions T able 1. Properties of the giant components of the W iFi networks for R int = 45m: size of the giant component N , percentage of encrypted routers f encr , maximum degree k max , av erage de- gree h k i , degree fluctuations h k i 2 / h k i . The results presented are obtained as a v erages ov er 5 dif ferent randomization procedures to redefine the location of each router . Figure 1. (A) : Construction of W iFi networks. Gi v en two routers i and j located at ~ p i = ( LO N i , LAT i ) and ~ p j = ( LO N j , LAT j ) , we place an edge between them if their distance d ( ~ p i , ~ p j ) is smaller than the maximum interaction radius R int . (B) : Map representation of the giant components of the WiFi network in the Chicago area as obtained with different values of R int . (C) : The degree distribution for dif ferent values of the interaction radius R int sho w an exponential decay and a cutoff which depends on R int . The result is obtained as averages ov er 5 dif ferent randomization procedures to redefine the location of each router . Figure 2. Illustration of the spread of a wireless worm through Chicago in several time slices. In this series, the result is based on 1 randomization procedure for the location of each router and the maximum interaction radius R int is set to 45 meters. Figure 3. (A) : Attack rate versus time for the giant component of all the sev en urban areas, keeping R int = 45 m . (B) : The av erage and 90% C. I. for three prototypical cases. (C) : The correlation between the final attack rate and average degree. (D) : The correlation between the final attack rate and degree fluctuations. Figure 4. Compartmental Flows for the Epidemic Model. 17 T ABLES AND FIGURES Hu et al. City N f encr k max h k i h k i 2 h k i NYC 36807 25.8% 109 23.9 31.3 Boston 15899 21.7% 116 21.3 35.7 Seattle 3013 26.0% 49 11.9 16.7 Chicago 50084 33.7% 154 20.3 33.6 N.IN 2629 24.3% 87 18.4 29.9 S.IN 998 11.0% 32 10.4 14.1 SF Bay 3106 40.1% 31 9.6 12.8 T able 1. 18 T ABLES AND FIGURES Hu et al. Figure 1. 19 T ABLES AND FIGURES Hu et al. Figure 2. 20 T ABLES AND FIGURES Hu et al. Figure 3. 21 T ABLES AND FIGURES Hu et al. Figure 4. 22
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment