A Basic Framework for the Cryptanalysis of Digital Chaos-Based Cryptography
Chaotic cryptography is based on the properties of chaos as source of entropy. Many different schemes have been proposed to take advantage of those properties and to design new strategies to encrypt information. However, the right and efficient use o…
Authors: David Arroyo, Gonzalo Alvarez, Veronica Fern
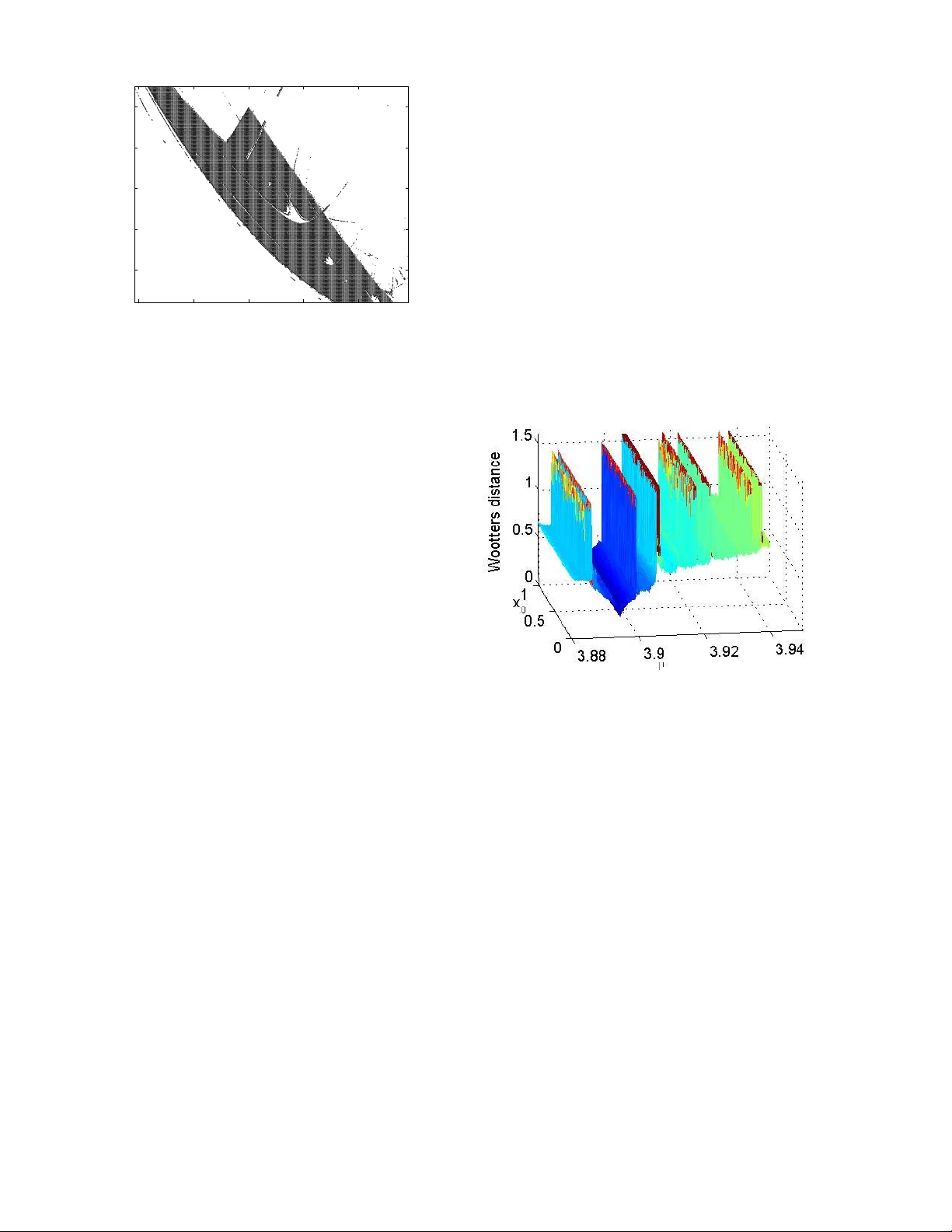
A B ASIC FRAMEWORK FOR THE CR Y PT AN AL YSIS OF DIGIT AL CHA OS -BA SED CR YPT OGRAPHY David Arr oyo 1 , Gonzalo Alvar ez 1 and V er onica F erna ndez 1 1 Instituto de F ´ ısica Aplicada, Consejo Superior de In vestigaciones Cient ´ ıficas, Serrano 144—28006 Madrid, Spain ABSTRA CT Chaotic cryptog raphy is based on the prope rties of chaos as sour ce of en tropy . Many different schemes have been propo sed to take advantage o f those p roperties and to d e- sign new strategies to en crypt info rmation. Howe ver , the right and efficient use of c haos in the context of cr ypto- graphy requires a thoro ugh knowledge about the dynam ics of the selected ch aotic system. Ind eed, if the final encryp - tion s y stem reveals en ough inform ation abo ut the und erly- ing chaotic system it cou ld be po ssible for a cryp tanalyst to get the key , part of the key or some inf ormation some- how equiv alen t to the key just analy zing those d ynamical proper ties leaked b y the cry ptosystem. This p aper sh ows what tho se dyn amical prop erties are an d h ow a cryptan a- lyst can u se them to prove the inadequa cy of an encryp- tion system fo r the secure exch ange of inform ation. This study is pe rformed throu gh the intr oduction of a series o f mathematical tools which should be the basic framework of cryptanalysis in the context of digital c haos-based cryp - tograph y . Index T erms — chao s, cryptograp hy , entr opy , wa velet transform s 1. INTR ODUCTION Chaotic cryptog raphy h as been an impo rtant research area during the last two decades. The properties of chaotic sys- tems have been used in very d ifferent ways to b u ild new cryptosystem s. All of those prop osals ca n be classified into two big families, wh ich are analog ch aos-based cryp- tosystems and digital ch aos-based cryp tosystems. T he first type of chaotic cryptosystem s is based on the chao tic syn- chroniza tion techniqu e [1], wh ereas d igital cha otic cr yp- tosystems ar e designed for digital co mputers. T he scope of this pap er is related to the last type of chaotic cryp- tosystems. Since the p erforma nce and a ccuracy of digi- tal ch aotic cr yptosytem s is a translation of the dy namical The work described in this paper was supported by Ministerio de Educaci ´ on y Ciencia of Spain , research grant SE G2004-02418 , Ministe- rio de Ci encia y T e cnolog ´ ıa of Spain, research grant TSI2007-62657 and CDTI, M inisterio de Industria, T urismo y Comercio of Spain in colla bora- tion with T elef ´ onica I+D, Project SEGUR@ wi th reference CENIT -2007 2004. proper ties of the under lying d ynamical system, the first step in either th eir design or their analysis comes f rom the ev alu ation o f those prop erties. This assessment has as main goal the verification that the selected dynamical system ev olves in a chao tic way in the context d efined by the encr yption strategy . Furthe rmore, it must be confirme d the im possibility of guessing the key or p art of th e key by the examination of th at chaotic b ehavior . Ind eed, chaotic systems exhibit an u nderlyin g regularity which could rep- resent a pr oblem in the con text o f chaotic cryptog raphy . The presen t work presents a set o f m athematical tools for the analysis of the dynam ical proper ties of ch aotic systems and, consequ ently , for the detectio n of design prob lems in digital c haos-based crypto systems. More specifically , this work studies the relationship between the set defined by the initial cond itions an d th e control p arameter of chaotic systems and their temporal e volution. From the poin t of view of th e secur ity conce rns of cr yptogr aphy , this work is a first step to establish a pa radigm of requ irements for the ad equate association of chaotic systems and enc ryption architecture s. 2. CHA OS AND CR YPTOGRAPHY The use of chaotic systems in cryptogr aphy is motivated by the similarity between the need s of cryptog raphy and the main characteristics of chaos. Indeed, every cryptosys- tem , i.e., every encryption system performs the transfor- mation of an input (the pla intext ) in to an output (the ci- phertext or cryptogram ) in suc h a way th at the different inputs and outp uts of the systems are s tatistically indepen - dent. M oreover , th is tran sformation dep ends on an exter- nal paramete r called key o f the cryptosystem. If a cryp - tosystem h as been de signed in a corr ect way , then its out- put is statically in depend ent fro m the key and fro m the input. In o ther words, a good cry ptoystem shows diffu- sion and con fusion properties [2]. T he confu sion pr op- erty me ans that th e temporal evolution o f the output o f the cr yptosystem is statistically in depend ent from the in- put and fr om th e key . Cha otic systems shows an ergod ic behavior and, consequ ently , possess inherently the con- fusion property with resp ect to the initial condition s and the contro l parameter (s). On the other hand , the diffusion proper ty implies tha t an small chan ge in the inpu t of the cryptosystem is tra nslated in to a large m odification in the output. Cha otic systems are characterized by a high sen- siti vity to initial con ditions and the contr ol parameter (s) and thus chao s ca n also be used as a so urce of diffusion. Nev er theless, cha otic systems are su stained by an under- lying regular ity by mean s of the existence of dense unsta- ble perio dic orbits which further constitute the skeleton of chaos [3, p. 413]. Furthermore, chaotic systems generally considered for cr yptogr aphic applications are defined in a parametric way and not all the values of the control param- eter(s) lead to a cha otic behavior . As a r esult, the de sign of a secure and efficient chaos-based cryptosytem requires the selection of an en cryption architecture th at conceals the un derlying regularity of the chosen ch aotic system and, at the same time , gua rantees that the co ntrol parameter (s) used in the en cryption an d decry ption proce sses are those which drive the dynamic al s y stem into a chaotic behavior . Concernin g this last po int, it is hig hly recom mendab le to use dynam ical systems with a large and con tinuous set o f values f or the contr ol par ameter(s) such that evolution in a c haotic way is g uaranteed . Acco rding to all this con- siderations, th e cryptan alysis work can be o nly successful when a chaotic cryptosy stem leaks too m uch info rmation about the dy namics o f the und erlying chaotic system or when the selection of th e con trol parameter (s) is no t done conv en iently . 3. DETECTION OF NON-CHA OTIC BEHA VIOR The scope of this pap er is digital c haos-based cry ptogra- phy and th us th e next work is f ocused on dyna mical sys- tems defined in discrete time. These dynamical system are also called map s and are mathem atically defined b y a dif- ference equation x k +1 = g ( µ, x k ) , (1) where x, g ( x ) ∈ U ∈ R n , be ing U the phase space, and µ is an a rray of co ntrol paramete rs in V ⊂ R p . T his sec- tion is concern ed with the definition of mathema tical tools to decid e whether a dig ital chaotic cryp tosystem defines a goo d framework fo r the selection of the set of co ntrol parameters of the underly ing chaotic map. 3.1. Bifurcation diagram A first m ethod to detec t pro blems related to the definition of the m ethod of selection of values for the ar ray of co ntrol parameters is b ased on the e valuation on the asymptotic temporal ev o lution. The temporal ev olu tion o r orbit of a discrete-time dyn amical sy stem is determ ined f or a certain initial conditio n and a certain set of v alu es for the array of control parameter s as γ ( µ, x 0 ) = { x 0 , x 1 , . . . , x n } . (2) If the co nsidered dynam ical system is a chao tic map, then the orbit d eriv ed fro m any initial condition covers th e whole phase s p ace. Th is character istic can be verified b y plotting γ ( µ, x 0 ) f or x 0 selected r andomly in U and µ taking all the values in V . T his represen tation is called b ifur cation diagram and can be used to de tect v alu es of µ not leading to chaos. As an example, in Fig. 1 the bifurc ation diagram for the logistic map is shown iden tifying those inad equate values of µ . When considering a chao tic cryp tosystem, the p ossibility o f selecting those values of µ associated to a non-ch aotic beh avior implies a degrada tion of the per- forman ce of the crypto system and can be used b y a crypt- analyst [4, 5]. 3.5 3.6 3.7 3.8 3.9 4 0 0.2 0.4 0.6 0.8 1 µ Asymptotic values Figure 1 . Bifur cation diagram of the logistic map. 3.2. The L ya punov exponent One imp ortant rule for the design of chaotic cryp tosys- tems is the ac curate definition of the key space [6, Ru le 5]. Therefo re, cryptanalysis is also concerned with the ev aluation of the preciseness of the definition of the ke y space. A very usefu l tool fo r this assessment is the L ya- punov exponent or LE. Indeed, the LE quantifies the local div ergen ce of a dyn amical system in su ch a way that a pos- iti ve value o f the L E inform s of a chaotic behavior . More rigoro usly , for a phase space defined in R m there exist m L yapun ov exponents and ch aos exists when th e largest L ya punov expon ent is positive. Th e H ´ enon map is a tw o dimensiona l dyn amical system and the con trol p arameter vector is given by µ = [ a, b ] . If the H ´ enon is considered for cryptogr aphic application s, then the encryptio n ar chi- tecture must assure that the selection of a an d b during the en cryption /decryp tion procedu re always guarantees a positive LE (see Fig. 2). Oth erwise, a degrad ation in the perfor mance of the cry ptosystem is o bserved as it occu rs in the crypto sytesm analy zed in [7–9] 4. EXPLOITING THE LEAKING OF THE UNDERL YING CH A O TIC SYSTEM REGULARITY Most chao s-based cryptosystems used either th e initial con - ditions o r the control param eter(s) or b oth as key . There- fore, the security of those pro posals is very depend ent o n the po ssibility of estimating the co ntrol parameter( s) and/or the initial c onditions from the inform ation p rovided b y the −0.4 −0.2 0 0.2 0.4 1.2 1.4 1.6 1.8 2 b a Periodic Unboun ded Figure 2 . Determination of the chao tic r egion of the H ´ enon by means of the L y apunov exponent. cryptosystem . The success of th is estimation process is something to consider in the design of a new cr yptosys- tem. Indeed, if it is known how muc h in formation can be provided to a cryp tanalyst without exposing our encryp- tion system, then it is p ossible to build a secure but also more efficient cryptosy stem. T he inf ormation that can be used by an attacker or cryp tanalyst is either part of an or- bit or th e transfor mation of par t of an or bit of the under- lying ch aotic system . Actually , that part of an or bit or the transform ation of the p art is associa ted to a certain in itial condition and control parameter( s) value. Con sequently , the cryptan alyst work is fo cused on lookin g for o ne-to- one relation ship b etween those samp les of orbits or those transform ation of the samp les of orb its. Next som e math - ematical procedu res for this estimatio n task are sho wn . 4.1. Study of histograms and the return map In som e digital chao s-based cryptosystem s the result of the encryption p rocedu re, i.e. , the different cryptog rams are gi ven directly by the orb it of some chaotic system [10] or by the sampling p rocess on the orbit o f a c haotic sys- tem [11, 12]. In the first case, th e cryptosystem shows a clear security pr oblem, since chaotic maps a re defined us- ing a difference equation which implies th at two consecu- ti ve values of an orbit can be used to estimate th e control parameter v alue [5]. In the second situatio n, the orbit is sampled an d thus it is no t possible a d irect estimation o f the contr ol parameter(s) as befor e. Howe ver , it is possible to associate those sampling values with the con trol param- eter(s) b y eithe r the study o f the return m ap o r by an sta- tistical treatmen t. Indeed , according to Kerckhoffs’ pr in- ciple [13, p. 14], the chaotic map used for a certain digital chaos-based cry ptosystem is known b y anyone and, con- sequently , a cryptanaly st k nows and can study its retu rn map. In [14, 1 5], for exam ple, th is stud y is used to estimate the contro l parameter of the log istic m ap b y m eans of the maximum value of its r eturn ma p. On the othe r ha nd, the statistical treatmen t of sampled orbits is based o n the pos- sibility of re constructing the prob ability distrib u tion func- tions of the orbits by means of the h istograms of their sam - pled version s. If th e chao tic map u sed for en cryption has good characteristics from the statistical poin t o f view , then it is not possible to infer the value of the contro l param- eter(s) from the obtained histograms. Con versely , a bad chaotic map gen erates histogr ams dependin g on the value of the control parameter( s). A way to use this dependency for cryp tanalysis is by the W ootters’ distance [16] between different histogra ms. In this sense, the histogram obtained from the s am pled o rbit leaked b y the cryptosy stem is com - pared to the histog rams generated from a set large enough of control param eter(s). The control parameter that gen- erates the closest histogram to the one ob tained from the sampled orbit i s conside red as an estimation of the control parameter used for the encry ption. Figure 3 illu strates the success of this estimation metho d for the log istic map. Figure 3 . E stimation of the control parameter of the logis- tic map by m eans of the W oo tters’ d istance. The value of µ and the initial condition x 0 used in the generation of the orbit were µ = 3 . 89 47192 an d x 0 = 0 . 998 42379 . 4.2. Analysis of entropy In the c ontext of chaos-based cryp tograp hy the space of cryptog rams has an entr opy determined mostly by th e un- derlying chao tic system. T herefor e, it is very impor tant to verify that the measure of en tropy obtained through the cryptog rams does no t allow to guess segments of th e plain- text o r to get a one-to -one relation ship with respect to the control p arameter(s) of the u nderly ing chao tic system. In this sense, when selecting the chao tic map and the encryp- tion arch itecture, it is highly advisable to e valuate first the entropy of th e orbits genera ted from the map. If this an al- ysis is not done, then it could be possible for the cry pt- analyst to build an attack upon d ifferent mea sures of en- tropy d ependin g on the kind of in formatio n contained in the cry ptogram s. This is the case o f the attac k perfo rmed in [18] on Shanno n’ s measu re of entropy . Other mea- sures of entropy tha t cou ld be usefu l fo r cryptan alysis are the topo logical entropy [19] and the wav elet en tropy [20]. 1000 2000 3000 4000 5000 6000 7000 8000 0.239 0.24 0.241 0.242 0.243 0.244 0.245 0.246 0.247 0.248 w=60 , ∆ =2, L=5 , q=5 Number of samples MRET1 Hénon with variable control parameters Hénon with constant control parameters Figure 4 . First level o f detail o f the Mu ltiResolution En- tropy of Tsallis of the H ´ enon map with fixed and variable control parameters. See [ 17] for mor e details about the proced ure. Related to the topological en tropy , in the co ntext of dig- ital chaos-based cryptosystems, i.e., when dealing with chaotic maps it is advisab le to work with app roximatio ns of the topo logical entropy b ased on the study of p ermu- tations [21], which a llows to develop a theory of discrete chaos [22] with c lear interest for cry ptanalysis [ 23]. On the o ther hand, the use of wa velets for the determination of measures of e ntropy can be an aid in the analysis of the security of ch aos-based cryptosystem s. For examp le, the th eory of wavelets and the figures of entropy defined by Shan non and Tsallis can be combine d to define a M ul- tiResolution Entro py an alysis that allows to identif y changes in the dynamics of a certain dynamical system [17] ( see Fig. 4). The detection of this ch anges can lead to the re- covery of informatio n or the guessing of the ke y or part of the key of a ch aotic crypto system, and it can also b e per- formed throu gh the s tud y o f the permutatio ns of the outpu t sequence of the cryptosystem [24]. 4.3. Analysis of statistical complexity Another way of getting benefit f rom the statistical evalua- tion of the o utput of a chaos-based cryp tosystem is ba sed on the notion of statistical complexity [25]. The statisti - cal com plexity measures the lev el o f local divergence that exists in a dyn amical system with respect to the underly- ing perio dic behavior and, consequ ently , can be used as a causality indicator . In this sense, the s tatistical comp lexity has been proposed as a test fo r the evaluation of the quality of rand om nu mber generato rs [26–28]. Ne vertheless, this is not its only applicatio n in the context of cryptanaly sis, since it can also be used to find one- to-one relationship s with re spect to the co ntrol pa rameters and , as a result, it could b e a hint f or con trol parameters estimation [29]. A s an example, th e statistical complexity of the log istic m ap with respe ct to µ is shown in Fig. 5 and it proves th at the estimation of µ is possible through the statistical complex- ity for certain intervals inside the d efinition space o f the control parameter . 3.5 3.6 3.7 3.8 3.9 4 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 0.45 Jensen−Tsallis complexity µ Figure 5 . Jensen-T sallis statistical complexity of the lo- gistic map for different v alues of µ . 4.4. Symbolic dynamics The stud y of the dynam ics of unimo dal maps thro ugh a discretized version of their p hase space is a well known area of stu dy in the co ntext of the theory of d ynamical systems since the seminal contr ibution of [30 ]. The con- clusions d eriv ed fr om th is work has been used fo r the es- timation of the initial co ndition and the contro l parame ter values that lead to a certain discretized version of an o r- bit associated to an unim odal map [31 , 32], which is the base of the cryptan alysis do ne in [18, 33, 3 4]. Howev er, the theory of sy mbolic dy namics, i.e., the study of tho se dis- cretized versions of orb its of chaotic maps is no t limited to unimo dal maps. In deed, the possibility of ap plying this kind of methodo logy is b ased o n the under lying period ic- ity that sustained chaos. In other words, i f the phase space of a chaotic map is partitione d con venien tly and a symbol is assigned to ea ch o f the derived intervals, the n it is pos- sible to get the unstab le period ic orbits of the system and, consequen tly , to reconstru ct its dynamics [35–38]. This is very interesting from the po int of view of cryptan alysis, since it allows to estimate the control parameter and even, in some situations, the initial con dition used in the genera- tion of a time-series from a given chaotic system [39 , 40]. 5. CONCLUSIONS The present work is a summ ary o f different metho ds based on the th eory of dyn amical system s that can be used to point out some design pro blems in chaos-based cryptosys- tems. The m ain conclu sion derived fro m the set of tools propo sed is that the tests of security of conv entio nal cryp- tograph y are not the only to be consider ed in the context of chaotic cry ptograp hy . Indeed, either th e design or th e anal- ysis of a chaotic cryptosy stem mu st b e done along with a thorou ghly kn owledge a bout the dy namics o f the ch aotic map selected. Otherwise, the r esulting encryp tion scheme could present serious security and efficiency proble ms. 6. REFERENCES [1] L .M. Pec ora and T .L . Carro ll, “Syn chron ization in chaotic systems, ” Phys. Rev . Lett. , vol. 64, no. 8, pp. 821–8 24, 199 0. [2] Clau de Shan non, “Commun ication theo ry o f secrecy systems, ” Bell Sys. T ech. J . , vol. 28, pp. 656–71 5, 1949. [3] Ro bert C. Hilbor n, Cha os and non linear dyna mics , Oxford University Press, 2nd edition edition, 2000. [4] G onzalo Alvarez, F . M ontoya, M. Romera, and G. Pastor, “Cryptanaly sis of a d iscrete chaotic cryp- tosystem using external key , ” P hysics Letters A , vol. 319, pp. 334– 339, 2003. [5] D avid Arroyo , Chengqing Li, Shujun Li, and Gon- zalo Alvarez, “Cryptan alysis of a comp uter cryptog- raphy scheme b ased on a filter b ank, ” p . In Press, Accepted by Chaos, Solitons and Fractals in January 2008. [6] G onzalo Alvarez and Sh ujun Li, “Some ba sic cr yp- tograph ic requirements for chao s-based cryp tosys- tems, ” I nt. J . Bifur c. Chaos , vol. 16, no. 8, pp. 2129 – 2151, 2006 . [7] G . Alvarez, F . Mon toya, M. Rom era, and G. Pastor , “Cryptanaly zing a discrete-time ch aos synchr oniza- tion secure commu nication system, ” Cha os, Solitons & F ractals , vol. 21, no. 3, pp. 689–694 , julio 2004. [8] S. L i, G. Alvarez, G . Chen, and X. Mou, “Breaking a chaos-n oise-based secure commu nication schem e, ” Chaos , vol. 15, no. 1, pp. 13703, marzo 2005. [9] D avid Arroyo, Gonzalo Alvarez, Shuju n Li, Chengqin g Li, a nd Juana N unez, “Cryptanaly sis of a d iscrete-time synchron ous c haotic en cryption sys- tem, ” Physics Letter A , vol. 37 2, n o. 7, pp. 1034– 1039, 2008 . [10] Bingo Wing-Kuen Ling, Char lotte Y u k-Fan Ho, and Peter Kwong-Shun T am, “Chaotic filter bank f or computer crypto graphy , ” Chaos, S olitons and F rac- tals , vol. 34, pp. 817–824 , 2007. [11] E. Alvarez, A. Fern ´ andez, P . Garc ´ ıa, J. Jim’enez, and A. Mar cano, “New approach to chaotic en cryptio n, ” Physics Letters A , v ol. 26 3, pp. 373–37 5, 1999 . [12] A. N. Pisarchik, N. J. Flor es-Carmona, and M. Carp io-V aladez, “Encry ption and d ecryptio n of images with chaotic map lattices, ” Ch aos , vol. 16, no. 3, pp. art. no. 0331 18, 2006. [13] A.J. Menezes, P .C van Oorschot, and S.A. V anstone, Handbo ok of Applied Cr yp tography , CRC Press, 1997. [14] Adrian Skrob ek, “ Approx imation of a cha otic or - bit as a cryptanalytical method on Baptista’ s cipher, ” Physics Letters A , vol. 3 72, no. 6, pp. 849–85 9, 2008. [15] David Arroyo, Rho uma Rhouma , Gon zalo Alvarez, Shujun Li, and V ero nica Fern andez, “ On the security of a new image encry ption scheme based on chaotic map lattices, ” Chao s: An Inter disciplina ry Journal of Nonlinea r S cience , v ol. 18 , pp . 03311 2, 7 pages, 2008. [16] A. P . Majtey , P . W . Lamb erti, M. T . Martin, and A. Plastino, “W ootters’ distance revisited: a new dis- tinguishability criterium, ” Eur . Ph ys. J. D , vol. 32, pp. 413– 419, 2005. [17] L. G. Gamero, A. Plastino, a nd M. E . T orres, “W avelet analysis an d nonlinear dynam ics in a nonextensive setting , ” Physica A : Statistical and Theor etica l Physics , vol. 246, no. 3-4, pp. 487– 509, 1997. [18] Gonzalo Alvarez, Fausto Mo ntoya, M iguel Romera, and Ger ardo Pastor , “Cryp tanalysis of an ergo dic chaotic cipher, ” Physics Letter s A , vol. 31 1, pp. 172– 179, 2003. [19] R. L. Ad ler , A. G. K on heim, and M. H. McAndr ew , “T opologica l entro py , ” T ransactio ns o f the American Mathematical S ociety , vol. 114 , no. 2, pp. 30 9–31 9, 1965. [20] O.A. Rosso, S. Blanco, J. Y o rdanova, V . K olev , A. Figliola, M. Schrmann , and E. Basar, “W avelet entropy: a new tool for ananlysis of short dur ation brain electrical sign als, ” J ourn al of Neur oscien ce Methods , vol. 105, pp. 65–75, 2001. [21] Christoph Bandt, Ger hard Keller , and Bernd Pomp e, “Entropy o f in terval m aps v ia per mutations, ” Non- linearity , vol. 15, pp. 1595–160 2, 2 002. [22] L. K oc arev , J. Szc zepanski, J.M . Amigo, and I. T o- movski, “Discr ete chaos-i: Theory , ” Cir cuits and Systems I: Re g ular P apers, IEEE T ransaction s on , vol. 53, no. 6, pp. 1300–13 09, June 2006. [23] J.M. A migo, L. K oc arev , and J. Szczepanski, “Dis- crete L ya punov expo nent and r esistance to differen- tial cryp tanalysis, ” Cir cuits and Systems II: Expr ess Briefs, IEEE T ransaction s o n , vol. 54 , no. 10, pp. 882–8 86, Oct. 20 07. [24] Y inhe Cao, W en-wen T un g, J. B. G ao, V . A. Pro- topopescu , and L . M. Hively , “Detec ting dy nami- cal chan ges in time series usin g the perm utation en - tropy , ” Phys. Rev . E , vol. 70, no. 4, pp. 04621 7, Oct 2004. [25] M.T . Martin, A. Plastino, an d O.A. Rosso, “Gen - eralized statistical comp lexity m easures: Geometri- cal and an alytical prop erties, ” Physica A: Statistical Mechanics and its Ap plications , vol. 369, no. 2, pp. 439–4 62, 200 6. [26] C.M. Gonz ´ alez, H.A. Larrond o, an d O.A. Rosso, “Statistical complexity measure of pseud orando m b it generato rs, ” P hysica A: Statistical Mechanics and its Application s , vol. 354, pp. 281–30 0, 2005 . [27] H.A. Lar rondo , C.M. Gonzlez, M.T . Martn, A. Plas- tino, and O.A. Rosso, “Intensiv e statistical comp lex- ity m easure o f pseudorandom number generators, ” Physica A: Statistical Mechanics an d its Ap plica- tions , vol. 356, no. 1, pp. 133–138, 2005. [28] H.A. Lar rondo , M.T . Martn, C.M. Gonz lez, A. Plas- tino, and O.A. Rosso, “Random numbe r generato rs and c ausality , ” Physics Letters A , vol. 352, no . 4-5 , pp. 421– 425, 2006. [29] O.A. Rosso, H.A. Larro ndo, M.T . Martin, A. Plas- tino, and M .A. Fuentes, “Distingu ishing no ise from chaos, ” Ph ysical re view letters , vol. 99, pp. 15 4102 –1,15 4102– 4, 200 7. [30] N. Metropo lis, M.L. Stein, and P .R. Stein, “On the limit sets for transfo rmations on the unit interval, ” Journal of Comb inatorial Theory (A) , vol. 15, pp . 25–44 , 197 3. [31] Xiaogang W u , Hanp ing Hu, and Baoliang Zhang, “Parameter estimation o nly from the symbolic se- quences generated by ch aos system, ” Cha os, solitons and F ractals , vol. 22, pp. 359–366, 2004. [32] Gonzalo Alv ar ez, David Ar royo, and Juana Nu nez, “ Application of g ray code to the cryptanaly sis of chaotic crypto systems, ” in 3r d In ternational IEEE Scientific Conference on Physics an d Con- tr o l (PhysCon’ 2007, 3r d - 7th , Septemb er 2007, P otsdam, Germany) , Po tsdam, Germany , 3rd - 7th , September 2007 , IEEE IP A CS. [33] David Arroyo, Gonzalo Alvarez, Shuju n Li, Chengqin g Li, an d V eron ica Fernandez, “Cryptanal- ysis of a ne w chaotic cryptosy stem based on ergod ic- ity , ” http ://arxiv .org/abs/08 06.3183 , Submitted on 19 Jun 2008. [34] Kai W ang, W enjiang Pei, Liu hua Zou, Aiguo Song, and Z henya He, “On the secu rity o f 3d cat map based on symmetric image encry ption scheme , ” Ph ysics Letters A , v o l. 343, pp. 432–439 , 200 5. [35] Matthew B. Kennel and Michael Buhl, “Estimating good discrete partitions fro m ob served data: Sy m- bolic false nearest neighbor s, ” Phys. Rev . Lett. , vol. 91, no. 8, pp. 0841 02, Aug 20 03. [36] Michael Buhl and Matth ew B. K en nel, “Statisti- cally relaxing to generatin g partitions for ob served time-series data, ” Physica l Review E , vol. 71, pp. 04621 3:1–1 4, 20 05. [37] V e nkatesh Rajagopalan and Asok Ray , “Symbolic time series analy sis via wav elet-b ased p artitioning, ” Signal Pr ocessing , vol. 86, pp. 3309–33 20, 2006. [38] Michael Buhl an d Matthew B. K ennel, “Glob ally enumera ting un stable periodic orbits for observed data usin g symb olic dynam ics, ” Chaos: An Inter- disciplinary J ourn al of Non linear Scien ce , vol. 17, no. 3, pp. 03310 2, 2007. [39] Carlo Piccard i, “On para meter estimation of chaotic systems via symbolic time-series analysis, ” Chao s , vol. 16, pp. 043115:1– 10, 2006. [40] Kai W ang, W engjiang Pei, Shaop ing W an g, Y iu- Ming Cheung , and Zhenya He, “Symb olic vector d y- namics ap proach to initial co ndition and contro l pa- rameters e stimation of co upled m ap lattices, ” IEEE T ransactions on Cir cuits and Systems-I: Re gu lar P a- pers , vol. 55 , pp. 1116–11 24, 2008. 3.5 3.6 3.7 3.8 3.9 4 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 0.45 Jensen−Tsallis complexity µ
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment