A Class of Errorless Codes for Over-loaded Synchronous Wireless and Optical CDMA Systems
In this paper we introduce a new class of codes for over-loaded synchronous wireless and optical CDMA systems which increases the number of users for fixed number of chips without introducing any errors. Equivalently, the chip rate can be reduced for…
Authors: P. Pad, F. Marvasti, K. Alishahi
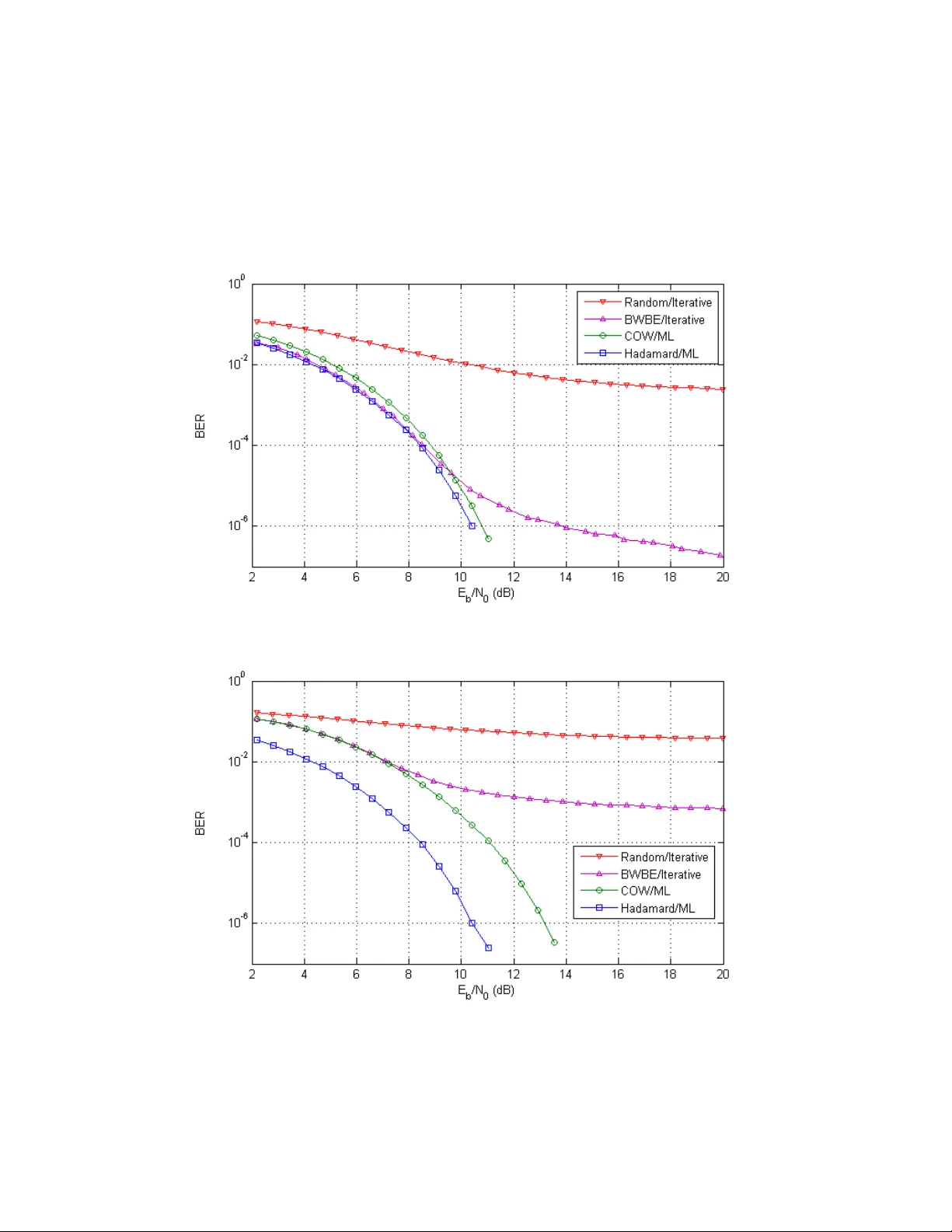
A Class of Errorless Codes for Over-loaded Synchronous Wireless and Optical CDMA Systems P. Pad 1 , F. Marvasti 1 , K. Alishahi 2 , S. Akbari 2 Abstract: In this paper we introduce a new class of codes for over-loaded synchronous wireless and optical CDMA sy stems which increa ses the number of users for fixed number of chips without i ntroducing a ny err ors. E quivalently, the chip ra te can be reduced for a given number of users, which implies bandwidth reduction f or downlink wireless systems. An upper bound for the maximum number of users f or a given number of chips is derived. Also, lower and upper bounds for the sum channel capaci ty of a binary over-loaded CDMA are derived that can predict the e xistence of such ov er-loaded codes. We also propose a simplifie d maximum likelihood m ethod for de coding the se types of over-loade d codes. Although a high perc entage of the over-loading factor 3 degrades the system pe rformance in noisy channels, simula tion results s how that this degradation is not significant. More i mportantly, for moderate values of ܧ ܰ Τ (in t he range of - ͳͲ dB) or hi gher, the proposed code s perform much bet ter than the binary We lch bound equalit y sequence s. I. Introduction In a sy nchronous wireless 4 CDMA s ystem with no additive noise, we can obtain errorless tr ansmission by using orthogonal c odes (Hada mard codes) ; we assume the number of users is less than or equa l to the spreading f actor (under or fully-loaded cases). In t he over-loaded case (when the numb er of users is more than the spreading factor), such orthogonal codes do not exist; the choice of random codes create s interference t hat, in general, c annot be removed c ompletely and creates errors in the Multi-User Detection (MUD) receiver [1-3]. 1 ! Advance d Communica tions Res earch Institut e (ACRI) and Dep artment of E lectrical Engi neering, Sharif Univers ity of Technolog y, Tehr an, Iran. 2 ! Depar tment of M athematica l Sciences, Sharif U niversity of Tec hnology, T ehran, Iran. 3 ! The p ercentage of the nu mber of users divided by the n umber of chips minus 1, i. e., ( ݊ Ȁ݉, െ ͳ ). 4 ! In genera l, by w ireless CDMA, we mean the si gnature c odes (matrix) a nd the input data ar e binar y ሼ ͳǡ െͳ ሽ ; while for optical CD MA systems , the bi nary elements are ሼͲǡͳሽ . id401656 pdfMachine by Broadgun Software - a great PDF writer! - a great PDF creator! - http://www.pdfmachine.com http://www.broadgun.com Likewise, f or under-loaded optical CDM A systems, Optical Orthogonal Codes (OOC) [4-5] can be used. Unlike the connotation of the na me of OOC, the optical codes are not really orthogonal, but by int erference cancellation, we can re move the interference completely. However, for the fully and over-loaded cases, OOC ’ s (wit h minimal cross-correlation value of ߣ ൌ ͳ ) do not exist and similar t o the wireless CDM A, the choice of random codes creates inter ference that, in general, cannot be remov ed completely. When the channel bandwidth is limited, the over-loaded CDMA may be needed. Most of the research i n the over-loaded case is re lated to code design and Multi-Acces s Interference (MAI) cancellation to l ower the proba bility of error. Examples of these types of res earch are ps eudo random spreading ( PN) [6-7] , OCDMA/OCDMA (O /O) [8-9], Multiple-OCDMA (MO) [10], PN/OCDMA (PN/O) [11] signature sets, Serial and P arallel Inter ference C ancellation (SIC and PIC) [ 12-16]. The papers that discuss double orthogonal c odes for inc reasing capacity [17-18] are actually non-binary complex codes (equivalent to ݉ phases for MC-OFDM) and are not really fai r for comparison. The codes with minimum Total Squared Correlation (TSC) 5 [ 20-22] maximize the channel capacity of a CDMA s ystem when the input distribution is Gaussian [23]. But for bi nary input signals, the WBE codes do not necessaril y maximi ze the cha nnel capacity. M oreover, if the WBE codes are binary (BWBE), the optimality is no longer true. Another probl em with WBE codes is that its ML imple mentation i s impractical 6 . In our comparisons of our codes with WBE, we use iterative decoding methods with soft thres holding f or WBE codes. For more details please refer to Section VI on simulation results. None of the signatures and dec oding s chemes that have been proposed in the literature (including the BWB E) guarantee errorle ss communicat ion in an ideal (high Signal-to- Noise Rati o (SNR) and without near-far ef fect) synchronous channe l. In thi s pa per, we plan to i ntroduce Codes for Over-loaded W ireles s (COW) and Codes for Over- 5 ! Or equivale ntly, the Welch Boun d Equalit y (W BE) [19] codes. 6 ! There are some e xceptions th at are discussed i n [29]. loaded Opti cal (COO) CDMA systems [24] which guarantee errorles s communica tion in an ide al cha nnel and propose an MUD sche me f or a specia l class of these codes that is M aximum Likelihood (ML ). We will also compare these codes to BW BE and show that as the ove r-loading factor increases, the proposed COW /COO code s perform much be tter. As a n example , for a s ignature length of Ͷ , we have discovered such c odes with an over- loading factor of about ʹΨ that c an be decode d practically in real ti me, which is al so ML. H owever, we have prov ed t he exis tence of c odes with an over-loading factor of al most ͳͷΨ that need to be disc overed. The complexi ty of the decoding depends on the number of chips and the over-loading factor; but f or a COW/COO code of size ሺͶǡͳͲͶሻ , the ML implementation is a s simple a s ͺ look up tables of size ͵ʹ . The i mplications of thes e findings are tremendous; it implies that using this system, we can accommodate ͳͲͶ use rs for a spreading fact or of Ͷ with low complexity ML decoding, which perf orms significantl y better than BWBE in a n AWGN channe l (when ܧ ܰ Τ is greater than dB). These codes are suitable for synchronous Code Division Multipl exing (CDM) in broadcasting, downlink wireless CDMA, and optical CDMA (assuming chip and frame synch). Alternatively, these codes can be used f or the present downlink CDMA systems with much lower chi p ra te and hence significant bandwidth saving for the operating companies. Using Ͷ chips, we have also derived an upper bound where the over-loading fa ctor cannot be m ore than ,͵ʹͲΨ . By trying to fi nd bounds on t he channel capacity in the absence of additive noise, we can, surprisingly, predict the existence of such codes. Section II covers the nec essary and sufficient conditions for e rrorless transmission in a noiseless ove r-loaded CDMA system along w ith m ethods f or constructing large COW and COO codes with high perce ntage of over-loading factor. Two upper bounds for t he num ber of users f or a given signature length are presented in Secti on III. Channel Capacity evaluation for noiseless CDMA is discussed in Section IV. Methods for decoding are discussed in Section V. Simulation results and discussions are s ummarized in Section VI. Finally, concl usion and f uture work are covered in Section VII. II. P reliminaries-Channel Model A synchronous CDMA system in an AWGN channel is modeled a s ܻ ൌ ۱ۯܺ ܰ ǡ where ۱ is a matrix with signature columns with elements ሼ ͳǡ െͳ ሽ or ሼͲǡ ͳሽ depe nding on the application, ۯ is a dia gonal matrix with entries equal to the user received amplitude, ܺ is a binary user column vec tor with entries ሼ ͳǡ െ ͳ ሽ or ሼͲǡ ͳሽ , ܰ is a white Gaussian noise with a covariance matrix of ߪ ଶ ۷ (whe re ۷ is t he id entity ma trix) and ܻ is the received ve ctor. In case of perfect power control, we can a ssume that ,ۯ ൌ ۷ . Below we will discuss COW and COO codes. II.1 Codes for Over -loaded Wirele ss (COW) CDMA Systems For developing CO W and C OO codes (m atrices), w e first disc uss an i ntuitive geometric interpret ation and then develop the codes m athemati cally. At a given time the multi-user binary data can be represent ed by an ݊ -dimensional vector; these vectors ca n be interprete d as the vertice s of a hyper-cube. E ach use r data is multiplied by a signature of ݉ chips long and fi nally thei r sum mation is transm itted. Thus, the transmitted ݉ -tuple vectors are t he mul tiplicat ion of an ݉ ൈ ݊ matrix (t he columns are the signatures of differe nt users) by the input ݊ -di mensional vectors. Hence, the hyper-cube vertices are mapped ont o points in an ݉ -dimensi onal spac e ( ݉ ൏ ݊ ). As long as the points in the ݉ -dime nsional s pace are dis tinct, the ma pping is one-to-one and theref ore, we can uniquely decode each received ݉ -tuple vector a t the rec eiver; on the other ha nd, if thes e ݉ -tupl e vec tors are not dist inct, the m apping is not one-to- one and the system is not invertible. Cons equently, we look for code s that map the vertices of the ݊ -dimensional hyper-cube to disti nct points in the ݉ -dimensional space . Mos t of the over-loade d c odes discusse d in the lite rature do not have thi s property and thus any MU D c annot be perfe ct. We coin the invertible codes, as mentione d in t he i ntroduction, as COW a nd COO codes for wirele ss a nd optic al applica tions, respe ctively. We first develop systemati c ways to g enerat e COW codes and then exte nd it t o COO codes. Lemma 1 We denote the vertice s ሼͳǡ െͳሽ of an ݊ -dimensi onal hyper-cube with the set F . The nec essary and suffic ient condi tion for the multipli cation of a COW matrix ۱ with element s of F t o be a one -to-one transforma tion is GHI,۱, ת ሼെ ͳǡͲǡͳሽ ൌ ሼͲሽ , where GHI,۱ is the null space of ۱ . Proof : Let ܺ א G HI,۱, ת ሼ െͳǡͲǡͳሽ . Then, ۱ ሺ ʹܺ ሻ ൌ Ͳ a nd ʹܺ is a ሼെ ʹǡͲǡʹሽ -vector. Clearly, ʹܺ ൌ ܺ ଵ െ ܺ ଶ , where ܺ ଵ and ܺ ଶ are ሼͳǡ െͳሽ -vectors. This implies that ۱ܺ ଵ ൌ ۱ܺ ଶ and thus ܺ ଵ ൌ ܺ ଶ . H ence, ܺ ൌ Ͳ and the proof is complet e. ז Corollary 1 If ۱ is a COW mat rix, then a. A new COW mat rix ca n be generate d by multiplying each row or c olumn of the ma trix ۱ by െͳ . b. New COW matrice s can be generated by permuting columns and rows of the matrix ۱ . c. By adding an arbitrary row to ۱ , we obtai n a nother COW matrix. The proof is cl ear. From C orollary 1, we can assume tha t a ll e ntries of the f irst row and the first column of a COW matrix a re ͳ . Theorem 1 Assume that ۱ is an ݉ ൈ ݊ COW ma trix a nd ۾ is an invertible ݇ ൈ ݇ ሼͳǡ െ ͳሽ -matrix, then ۾۪۱ is a ݇݉ ൈ ݇݊ COW ma trix, where ۪ denot es the Kronecker product. Proof : Cle arly, ۾۪۱ is a ሼͳǡ െͳሽ -mat rix. Assume that ܺ is a ሼെͳǡͲǡͳሽ -vector such that ሺ۾۪۱ሻܺ ൌ Ͳ . Then we have ሺ ۾ ିଵ ۪۷ ሻ ሺ۾۪۱ሻܺ ൌ Ͳ and thus ሺ ۷ ۪۱ ሻ ܺ ൌ Ͳ . If ܺ ൌ ሾ ܺ ଵ ڮ ܺ ሿ , then we have ۱ ܺ ଵ ൌ ۱ܺ ଶ ൌ ڮ ൌ ۱ ܺ ൌ Ͳ , where ܺ ’ s are ݊ ൈ ͳ ሼെͳǡͲǡͳሽ -vectors. Thus, by Lemma 1 we ha ve ܺ ଵ ൌ ܺ ଶ ൌ ڮ ൌ ܺ ൌ Ͳ . Hence , no non-zero ሼെͳǡͲǡͳሽ -vector i s in the kernel of ۾۪۱ . Thus, ۾۪۱ i s a ݇ ݉ ൈ ݇݊ CO W matrix. ∎ The existence of COW matric es with much higher pe rcenta ge of the over-loading fac tors are given in the following t heorem: Theorem 2 Assume ۱ is an ݉ ൈ ݊ COW matrix and ۶ ଶ ൌ ቂ ͳ ͳ ͳ െͳ ቃ . We can add ڿ ሺ ݉ െ ͳ ሻ ]^_ ଷ ʹ ۀ colum ns to ۶ ଶ ۪۱ to obtain another COW ma trix. For the proof, ref er to Appendix C. Note 1 ݊Ȁ݉ ՜ λ as ݉ ՜ λ . This observation is a direct result of Theorem 2 since ݊Ȁ݉ is of order ܱ ሺ]^_,݉ሻ . It implies that a s the chip rate increase s, the number of us ers grows much fa ster. Example 1 Applying Step 1 of the proof of Theorem 2 on a ʹ ൈ ʹ Ha damard matrix, we fi rst get a Ͷ ൈ ͷ COW m atrix ( ۱ ସൈହ ) as shown in Tabl e 1 7 (the sign represents ͳ and the െ sign re presents െͳ ). By one more repetition, we find an ͺ ൈ ͳ͵ COW matrix ( ۱ ଼ൈଵଷ ) depic ted i n Tabl e 2. Ac cording to The orem 1, ۱ ଼ൈଵଷ l eads to a Ͷ ൈ ͳͲͶ COW matrix by the Kronecker produc t ۶ ଼ ۪۱ ଼ൈଵଷ (where ۶ ଼ is an ͺ ൈ ͺ Hadamard matrix); this implies that we can have errorles s decoding for ͳͲͶ users with only Ͷ chips ; i.e ., more tha n Ψʹ over-loading f actor (we will i ntroduce a suitable de coder for this code in Section VI). However, re petition of Theorem 2 for ۱ ଼ൈଵ ଷ shows the existe nce of a Ͷ ൈ ͳ Ͷ COW matrix which impl ies a n over-loading fac tor of about Ψͳͷ . A fast algorithm for che cking that a m atrix is COW or not is given in Appendi x B. 7 ! Exhaustive searc h has shown t hat there are n o Ͷ ൈ COW matric es. Table 1. An exa mple of Ͷ ൈ ͷ COW matrix- ۱ ସ ൈ ହ . II.2. COO f or Optic al CDMA We w ould like to e xtend the result s to optical CDMA, i .e. , COO matrices . Theorem 3 If the re is an ݉ ൈ ݊ COW matrix f or the wireless CDMA, then the re is an ݉ ൈ ݊ COO matrix f or the optical CDMA. Proof : Suppose ۱ is a n ݉ ൈ ݊ COW matrix. By Corollary 1, we c an assume that the entries of the first row of ۱ a re all ͳ . Now, we would like to prove that ۲ ൌ ሺ ۸ ۱ ሻ ʹ Τ is a COO matrix, where ۸ is the all ͳ matrix. It is cle ar that ۲ is a ሼͲǡͳሽ -mat rix. Assume ܺ ! ሼെͳǡͲǡͳሽ and ۲ܺ ൌ Ͳ . This yields that ሺ۸ ۱ሻܺ ൌ Ͳ and thus ۱ ܺ ൌ െ۸ܺ . Be cause the entries of the first row of ۱ a re all ͳ , t he first e ntry of ۱ܺ is equal to the first ent ry of ۸ܺ . The above argument shows that the f irst entry of ۸ܺ is Ͳ . T hus ۸ܺ ൌ Ͳ . On the other ha nd ۱ܺ ൌ Ͳ implies t hat ܺ ൌ Ͳ , beca use ۱ is a COW mat rix. This shows t hat ۲ is a COO matrix. ∎ Corollary 2 Similar proof shows t hat, if we ha ve a C OO matrix which has a row with all ͳ ’ s , then we will obta in a COW ma trix by substi tuting the zeros of the COO matrix with െͳ . Example 2 As a specia l case, by Example 1 a nd Theorem 3, we also have a Ͷ ൈ ͳͶ COO matrix. Table 2. An exam ple of ͺ ൈ ͳ͵ COW matrix- ۱ ଼ ൈ ଵଷ . The the orems for CO O matric es are s imilar to the prev ious theore ms relate d to COW matrice s. In a ddition, there are a fe w extra algorithms for the constructi on of COO matrice s as de scribed below. Theorem 4 If ۲ is a n ݉ ൈ ݊ COO mat rix, then ۾۪۲ is a lso a ݇ ݉ ൈ ݇݊ COO mat rix, where ۾ is a n invertible ݇ ൈ ݇ ሼͲǡͳሽ -ma trix. The proof is s imilar to the proof of Theorem 1. Corollary 3 If we set ۾ ൌ ۷ in the above theorem, then the generated COO matrice s are sparse and ha ve low w eights that are suitable for optical transmi ssion due to low power [4]. Theorem 5 Suppose ۯ ൌ ۸ – ۷ is an ݉ ൈ ݉ ma trix, and ܸ ൌ ቂ ͳ ڮ ͳ ᇩ ᇭ ᇭ ᇪ ᇭ ᇭ ᇫ ଶ Ͳ ڮ Ͳ ᇩ ᇭ ᇭ ᇪ ᇭ ᇭ ᇫ ିଶ ቃ , for ݅ ൌ Ͳǡ ڮ ǡ ݀ , where ݀ ൌ ہ ]^_ ଶ ݉ ۂ െ ʹ . If ۰ ൌ ሾ ܸ ܸ ଵ ڮ ܸ ௗ ሿ , t hen ۱ ൌ ሾ ۯ ȁ ۰ w ሿ is an ݉ ൈ ሺ ݉ ݀ ͳ ሻ COO m atrix. Proof : Suppose ۱ܼ ൌ Ͳ , where ܼ is a ሼെͳǡͲǡͳሽ -vector. Call the first ݉ e ntries of ܼ by ܺ and the other ݀ ͳ ent ries by ܻ . Hence , we ha ve ۯܺ ۰ܻ ൌ Ͳ and this im plies that ܺ ൌ െۯ ିଵ ۰ܻ ൌ െ ቀ ۸ ି ଵ െ ۷ቁ ۰ ܻ ൌ െ ۸ ିଵ ۰ܻ ۰ܻ . Obviously, ۰ܻ is a n integer vector, thus it is suffi cient to prove that ۸ ି ଵ ۰ܻ cannot be a non-zero integer vector. To show this we write ۸ ିଵ ۰ܻ ൌ ଵ ି ଵ ͳ ڭ ͳ ʹ ڭ ʹ Ͷ ڭ Ͷ ڮ ڰ ڮ ʹ ௗ ڭ ʹ ௗ ൩ . Since ܻ is a ሼെͳǡͲǡͳ ሽ - vector then each entry of the vector ۸۰ܻ does not excee d ͳ ʹ ڮ ʹ ௗ ൏ ݉ െ ͳ , thus ۸ ି ଵ ۰ܻ ca nnot be a non-zero integer vector. Now, suppose t hat ۸۰ܻ ൌ Ͳ . If ܻ ൌ Ͳ , then ۯܺ ൌ Ͳ . Since ۯ is a n invertible ma trix, we c onclude t hat ܼ ൌ Ͳ . Thus, assume that ܻ ് Ͳ . There exists an index ݅ such that ܽ ʹ ܽ ାଵ ʹ ାଵ ڮ ܽ ௗ ʹ ௗ ൌ Ͳ , ܽ א ሼെͳǡͲ ǡͳሽ f or every ݆ and ܽ ് Ͳ . This implies t hat ܽ is divisible by ʹ , a contradic tion. ∎ Example 3 Using Theorem 5, we get a Ͷ ൈ ͻ COO matrix with the structure discussed in the theorem. In the next s ection we will t ry to fi nd bounds on the number of users for a given spreading fac tor. Note 2 According to Lemma 1 if a matrix is COW, t hen any subset of its columns is also COW . This sta tement i mplies that if some of the us ers go inac tive (we can assume that the y are sending Ͳ i nstead of േͳ ), a t the decoder we only need to know the a ctive users (it is a common a ssumption in M UD [ 1-3]). Typically, in prac tical networks if a us er bec omes inact ive, there a re users in the queue t hat will grab the code. However, i f we ne ed a cla ss of errorless c odes that can de tect ina ctive users f or decoding, w e must find the ሼͳǡ െͳሽ -matrices that opera te injec tively on ሼ െͳǡͲǡͳሽ - vectors. This i s a topic we have covered in [27]. For C OO ma trices we do not have such problems sinc e bit Ͳ is pa rt of the transmitte d data . III. Upper Bounds for the Perc entage of Over -loading Factor Theorem 6 provides an upper-bound for the over-loading fact or for a COW matrix. Theorem 6 If ۱ ൌ ൣܿ ൧ is a COW mat rix with ݊ colum ns (users) and ݉ rows (chips), then ݊ െ݉ ൭ ൫ ൯ ʹ ]^_ ଶ ൫ ൯ ʹ ୀ ൱ where ൫ ൯ ൌ Ǩ Ǩ ሺ ି ሻ Ǩ ȉ Proof : Let the input multiuser data be defined by the random vector ܺ ൌ ሾ ݔ ଵ ǡ ǥ ǡ ݔ ሿ , w here ݔ ’ s are identically independent distribution random v ariables taking െͳ , ͳ with probabilit y ͳ ʹ Τ . Since ݔ ’ s are independe nt, ”ሺܺሻ ൌ ݊ , w here ”ሺܺሻ is t he entropy of ܺ . Now, let the transmitted CDMA random v ector be defined by ܻ ൌ ۱ܺ ൌ ሾݕ ଵ ǡ ڮ ǡ ݕ ሿ . For a given ݆ , ͳ ݆ ݉ , the ݊ term s ܿ ݔ , ݇ ൌ ͳǡ ڮ ǡ ݊ are i ndepende nt random variables taking values െͳ , ͳ with probabi lity ͳ ʹ Τ . He nce ݕ ൌ σ ܿ ݔ ୀଵ is a binomi a l r a n d o m v a r i a b l e w i t h have ”ሺܻ ሻ σ ”൫ݕ ൯ ൌ ୀଵ matrix, then ܺ is a lso a func t i o n o f the proof . Note 3 In Appendix A, we e bette r upper bound. Fig. 1 sh o w s t h i s u p p e r b o u n d f o r t h e n u m b e r o f u s e r s v e r s u s t h e number of chips (spreadi ng f a c t o r ) . cannot have a C DMA system w i t h m o r e t h a n Ultima tely, w hen the jo int p r o b a b i l i t i e s o f a l l t h e maxim um number of use rs w i t h e r r o r l e s s t r a n s m i s s i o n w i l l b e o b t a i n e d . above a rguments, we can obt a i n s i m i l a r u p p e r b o u n d s f o r C O O c o d e s . Fig. 1. The upper bo unds for th e n u m b e r o f u s e r s factor) . The dotted l ine is the b o u n d f r o m T h e o r e m 6 w h i l e t h e s o l i d l i n e i s t h e t i g h t e r b o u n d IV. Channel Capacity for N o i s e l e s s In this sec tion, we shall deve l o p l o w e r a n d u p p e r b o u n d s f o r t h e s u m c h a n n e l c a p a c i t y [25] of a binary ove r-loaded The only inte rferenc e is t h e i s a b i n o m i a l random variable with ”൫ݕ ൯ ൌ െ σ ൫ ൯ ଶ ]^_ ୀ ൯ ൌ ݉ ቀെ σ ൫ ൯ ଶ ]^_ ଶ ൫ ൯ ଶ ୀ ቁ . Now, beca use ۱ is a C O W i s a l s o a f u n ction of ܻ and t hus ”ሺܺ ሻ ൌ ”ሺܻ ሻ ൌ ,݊ , whic h c o m p l e t e s I n A p p e n d i x A , w e e stimate t he entropy of ܻ in another manner and d e r i v e a b e t t e r u p p e r b o u n d . F i g . 1 s hows this upp er bound for the number of use rs v e r s u s t h e n u m b e r o f c h i p s ( s p r e a d i n g factor). This upper bound implies that with Ͷ a C D M A s y s t e m wit h more t han ʹͺ us e rs with errorless tran s m i s U l t i m a t e l y , w h e n t h e j o i n t probabiliti es of all the ݉ eleme nts of ܻ are t a k e n m a x i m u m n u m b e r o f u s e r s with errorles s tra nsmission will be obtained. U s i n g t h e a b o v e a r g u m e n t s , w e c a n o b t ain similar upper bou nds for COO c odes. T h e u p p e r b o u n d s f o r t he number o f users ݊ versus ݉ the number of chips ( s p r e a d i n g f a c t o r ) . T h e d o t t e d l i n e i s t h e bou nd from Theorem 6 wh ile the solid line is the tigh t e r b o u n d derived fro m Appendix A. f o r No iseless CDMA Systems I n t h i s s e c t i o n , w e s h a l l d e v elop lower a nd upper bounds for the sum channe l c a p a c i t y CDMA wi th MUD when the re is no a dditi ve n o i s e T h e o n l y i n t e r f e r e n c e i s the over-loaded us ers. In this ca se, the ch a n n e l i s ൯ ] ^ _ ଶ ൫ ൯ ଶ Ǥ We i s a COW , w h i c h complet es ז a n d derive a b e t t e r u p p e r b o u n d . F i g . 1 s h o w s t h i s u p p e r b o u n d f o r t h e n u m b e r o f u s e r s versus the chips, we r s w i t h e r r o r l e s s t r a nsmis sion. a r e take n the Using the t h e n u m b e r o f c h i p s (spreading f a c t o r ) . T h e d o t t e d l i n e i s t h e b o u n d f r o m T h e o r e m 6 w h i l e t h e s o l i d l i n e i s t h e t i g hter bound I n t h i s s e c t i o n , w e s h a l l d e v e l o p l o w e r a n d u p p e r b o u n d s f o r t h e s u m c h a n n el capa city C D M A w i t h M U D w h e n t h e r e i s n o a d d i t i v e nois e [ 26]. t h e c hannel is determinis tic but not loss less. The interesting result is tha t t he lower bound estimates a re gion f or the number of users ݊ for a given chip rate ݉ such that COW or COO matrice s exist . To de velop the lower bound, we start by the fol lowing assumptions for the wirel ess c ase but results are a lso valid for the opti cal C DMA: For a giv en ݉ and ݊ , let ™ ൌ ሼ ͳǡ െ ͳ ሽ and š ǡ be the set of functions ݂ ™ ՜ Ժ def ined by ݂ ሺ ܺ ሻ ൌ ۻܺ , where ۻ is a n ݉ ൈ ݊ matrix with entrie s ͳ and െͳ and ܺ is the input multiuser vec tor as defined bef ore with e ntries ͳ and - ͳ . Definition : The sum channe l ca pacity f unction Ÿ is de fined as Ÿ ሺ ݉ ǡ ݊ ሻ ൌ ¡¢ א š ǡ ]^_ ଶ ȁ ݂ ሺ ™ ሻ ȁ where ȁ ,, ȁ denotes the number of elements of t he set. The above definition is equivalent to maximizing the mutual information ¥ሺܺ ǡ ܻ ሻ which is equal to th e output entropy (deterministic channe l) over all the input probabilities and over all ݉ ൈ ݊ ܯ matrices ( ܺ and ܻ a re binary ݊ ൈ ͳ and non-bina ry ݉ ൈ ͳ vectors, res pectively). Lemma 2 (i) Ÿሺ݉ǡ ݊ ሻ , ,݊ (ii) Ÿሺ݉ǡ ݊ ሻ , ,݉, ]^_ ଶ ሺ݊ ͳሻ Proof : (i ) is trivial since ȁ ݂ ሺ ™ ሻ ȁ ȁ ™ ȁ ൌ ʹ . For (ii ) note tha t if ܺ ! ™ and ܻ ൌ ሾ ݕ ଵ ڮ ݕ ሿ ൌ ݂ ሺ ܺ ሻ ൌ ۻܺ then ݕ ൌ σ ݉ ݔ ୀଵ is t he sum of െͳ ’ s a nd ͳ ’ s and ca n take ݊ ͳ values. Hence , there are at most ሺ݊ ͳሻ possible vectors f or ܻ . ז Lemma 3 If ݊ is divisible by ݉ , the n Ÿሺ݉ ǡ ݊ሻ , , ݉, ]^_ ଶ ሺ݊ ݉ ሻ – ݉, ]^ _ ଶ ݉ . For the proof, ref er to Appendix D. To get tighter bounds than the ones given in Lemmas 2 and 3, we n eed th e following theorems: Theore m 7 (Channel Capaci ty Low er Bound) Ÿሺ݉ǡ ݊ ሻ , ,݊Ȃ ]^_ ଶ ©ሺ݉ ǡ ݊ሻ, where © ሺ ݉ǡ ݊ ሻ ൌ ൬ ݊ ʹ݆ ൰ ቀ ଶ ቁ ʹ ଶ ቔ ଶ ቕ ୀ Ǥ For the proof, ref er to Appendix E. Theorem 8 (Channel Capacity Upper B ound) Ÿ ሺ ݉ ǡ ݊ ሻ ݉ ൬ ͳ ʹ ]^_ ଶ ݊ ] ^_ ଶ ߣ ൰ ͳ where ߣ is the unique positive solution of the equation ൫ߣ ξ ݊ ൯ ൌ ݉ ݁ ିఒ మ ଶ ʹ ା ଵ Ǥ For the proof, re fer to Appendix F. The pl ots of the c hannel capaci ty upper a nd lowe r bounds with respect to ݊ for a typical value of ݉ ൌ Ͷ is given in Fig. 2(a). Fig. 2(b) is a dual plot with respect to ݉ for a fi xed value of ݊ ൌ ʹʹͲ . Plots o f the channel cap acity l ower bounds with respect to ݉ and ݊ a re given i n Fig. 3. The plot of the lower bound from Lemma 3 i s not shown since the b ound i s lower tha n the one from The orem 7 (see Fig. 2(a)) for ݊ ൏ ͳͲͲͲ , however, f or large ݊ ( ͶͲͲͲ ), i t is a better lower bound. (a) (b) Fig. 2. Lower and u pper bo unds for the sum channel capacity wi th respect to : (a) the number of users ݊ for ݉ ൌ Ͷ , (b) the chi p rate ݉ for ݊ ൌ ʹʹͲ . n th m th Interpreta tion : The lower bou nds show interesting a nd surprising results. T he lower bounds es sentially show two m odes of behavior. In the first m ode, the lower bo unds for the sum cha nnel capacit y (Fig. 2(a) and Fig. 3(a)) are almost linear with res pect to ݊ for a given ݉ , wh ich implies the existence of codes that are almost lossless. Since we know that there exist COW (COO) cod es that can achie ve the sum channel capacity (number of use rs is e qual to the sum channel capa city) without a ny error, the lower bound is ve ry tight in this region. For small values of ݉ s uch as Ͷ , we know that the ma ximum v alue o f ݊ ୫ୟ୶ such t hat a COW ma trix exist s i s ͷ . The sum channel cap acity low er bound f or ݉ ൌ Ͷ is ͶǤʹͳ bi ts, which is within a fra ction of integer f rom ͷ . Also, for ͺ ൈ ͳ͵ CO W matri x, the l ower bound is ͳʹǤͳͶ bit s, which is a gain within a fraction of an intege r from ͳ͵ . We thus conjecture t hat the maximum number of users for a COW/COO matrix for ݉ ൌ Ͷ is around ʹ͵ͻ from Fig. 2(a); right now our es timate from the simula tions and up per bound s is a n integer between 164 and 268. After ݊ increa ses beyond a thres hold value ݊ ୲୦ (F ig. 2(a)), t he channel becomes suddenly l ossy and enters the second mode of behavior. This loss is due to the fa ct that ʹ input points that are mapped to a s ubset of ሺ݊ ͳሻ points ca nnot f ind a ny empty sp ace and a fracti on of them get overlapped (no longer COW or COO condition). Figs. 2(b) and 3(b) show another interesti ng behavior. Initially, the bound increases almost linearly wi th ݉ for a g iven ݊ . This region is related to t he case where the chip (a) (b) Fig. 3. Plots of channel capacit y lower bound s for variou s ݊ and ݉ : (a) l ower bounds vs. number of users ݊ for a given chip rate ݉ , (b) lower bounds vs. ݉ for a given ݊ . rate ݉ is much less than the number of users ݊ . In our case, ݊ behaves like an amplitude or power, while ݉ behaves like frequency. As ݉ increases beyond a threshold ( ݉ ୲୦ i n Fig. 2(b)), the sum channel capacity remains almost constant since the capacity cannot be greater than ݊ (Lemma 2). In fact, ݊ is the supremum of the lower bound in this mode. This mode is the lossless cas e that predicts the existenc e of COW/COO codes. The next section covers a prac tical ML algorithm f or dec oding a c lass of COW codes. V. Maximum Likelihood ( ML ) Decoding for a Class of COW/COO codes The direct ML de coding of COW codes is computationall y v ery expensive for moderate values of ݉ and ݊ . In this section, we prove two lemmas for dec reasing the computat ional com plexity of the ML decoders f or a subclas s of COW codes. Suppose ۲ is a COW/COO ma trix and ܻ ൌ ۲ܺ ܰ is the receive d vector in a noisy channel. We wish to find a vector ܺ ሼͳǡ െ ͳሽ f or wireless systems ( ሼͲǡͳሽ f or optic al systems 8 ) w hich is the best esti mate of ܺ at the rece iver. From now on we prove the lemma s for COW matrices but based on footnote 7 , w e can extend it to COO matri ces. Lemma 4 Suppos e ۲ ൈ ൌ ۾ ൈ ٔ ۱ ൈ where ۾ is an inv ertible ሼͳǡ െ ͳሽ -matrix and ۱ is a COW matrix. The decoding problem of a system with code mat rix ۲ can be reduced t o ݇ decoding problems of a system with the c ode m atrix ۱ . Proof : Suppose ܻ ൌ ۲ ܺ ܰ ൌ ሺ ۾ ٔ ۱ ሻ ܺ ܰ ǡ where ܰ is the Gaussian noise vector with zero mean and a uto-covariance ma trix ߪ ଶ ۷ ( ۷ is the ݇݉ ൈ ݇ ݉ ide ntity matrix). Multiplying both sides by ξ ݇ ሺ ۾ ିଵ ٔ ۷ ሻ , we have ܻ ᇱ ൌ ξ ݇ ሺ ۾ ିଵ ٔ ۷ ሻ ܻ ൌ ξ ݇ ሺ ۷ ٔ ۱ ሻ ܺ ܰԢ where ܰ ᇱ ൌ ξ ݇ ሺ ۾ ିଵ ٔ ۷ ሻ ܰ . This e xpression suggests tha t the first ݉ entries of ܻ ᇱ depend on the first ݊ entries of ܺ and the f irst ݉ entri es of ܰԢ ; the second ݉ entries of ܻ ᇱ depend on the second ݊ entrie s of ܺ a nd the second ݉ e ntries 8 ! For a ሼͲǡͳሽ - vector, we ha ve ʹܻ െ ܹ ൌ ۲ ሺ ʹܺ െ ሾ ͳ ڮ ͳ ሿ ሻ ʹܰ where ܹ ൌ ۲ ȉ ሾ ͳ ڮ ͳ ሿ . Si nce ʹܺ െ ሾ ͳ ڮ ͳ ሿ is a ሼͳǡ െͳ ሽ -vector , ML decoding of ʹܻ െ ܹ is eq uivalent to M L decoding of ܻ . of the noi se vector ܰԢ , a nd so on. Thus, retrieving the ሺ ݅ െ ͳ ሻ ݊ ͳ ǡ ǥ ǡ ݅ ȉ ݊ ent ries of ܺ needs only the knowledge of the ሺ ݅ െ ͳ ሻ ݉ ͳǡ ǥ ǡ ݅ ȉ ݉ ent ries of ܻǯ , for ݅ ൌ ͳǡ ǥ ǡ ݇ . T herefore , the de coding problem f or ܻ is dec oupled to ݇ smalle r decoding problems. ז In ge neral, the ML de coding of the ܻ Ԣ in Lemma 4 result s in a sub-optimum decoder for ܻ . But if we suppose that the matrix ۾ is a Hadama rd one , since the ma trix ξ ݇ ሺ ۾ ିଵ ٔ ۷ ሻ is a unitary matrix, the vec tor ܰԢ is a Gaussian random vector with properties ide ntical to ܰ . Therefore , the ML decodi ng of ܻ Ԣ is equiv alent to ML decoding of ܻ . Since the ML decoding of ܻԢ i s equivalent to the ML dec oding of ݇ ݉ ൈ ͳ vectors, this implie s a dramatic decrea se in the computa tional complexity of the dec oder i n the over-loaded systems. The following lemma introduces another method to significantly reduce the computat ional com plexity of the decoder in over-loaded systems. Lemma 5 If a COW matrix ۱ ൈ is full ra nk, then the decoding problem for a system with code mat rix ۱ c an be done through ʹ ି Eucl idean dis tance mea surements. Proof : From pa rt (b) of Corolla ry 1, we ca n always decompose the COW matrix ۱ ൌ ሾ w ۯ ȁ ۰ሿ such that ۯ i s an ݉ ൈ ݉ invertibl e square mat rix. Assume ܻ ൌ ۱ ܺ ൌ ۯܺ ଵ ۰ܺ ଶ where ܺ ଵ and ܺ ଶ are ݉ ൈ ͳ and ሺ݊ െ ݉ሻ ൈ ͳ vect ors, respec tively. Thus, ܺ ଵ ൌ ۯ ିଵ ܻ െ ۯ ିଵ ۰ܺ ଶ . Hence, we can sea rch a mong ʹ ି possibili ties of ܺ ଶ to find the vec tor ܺ ଵ that belongs to ሼͳǡ െͳሽ . In a noi sy channe l, we look for the speci fic ܺ ଶ that minimizes ԡ ሺ ۯ ିଵ ܻ െ ۯ ିଵ ۰ܺ ଶ ሻ െ ÁÂ_Ãሺۯ ିଵ ܻ െ ۯ ିଵ ۰ܺ ଶ ሻ ԡ , w here ԡ , ԡ represents the Euclidean norm. T he corresponding ܺ ଵ vect or c an be obtaine d by ܺ ଵ ൌ ÁÂ_Ãሺۯ ିଵ ܻ െ ۯ ିଵ ۰ܺ ଶ ሻ , whe re ÁÂ_Ãሺܼ ሻ is obtained by substituti ng the positive e ntries of ܼ by ͳ and the negatives by െͳ . ז Similar to Lemma 4, Lemma 5 leads to significant decrease of t he de coding complexi ty, but is not always optimum. Also, since t he ÁÂ_Ã function maps a vect or to the nea rest ሼ ͳǡ െͳ ሽ -vector, it is not hard to show that if ۯ is a Hadamard matrix, then the proposed method in Lemma 5 is an M L decoder. Now, suppose that ۱ ൈ ൌ ሾ w ۯ ൈ ȁ ۰ ሿ and ۲ ൌ ۾ ൈ ۪۱ , where ۯ and ۾ are invertible matrice s and ۱ is a COW matrix. Combining Lemmas 4 and 5, we introduce a dec oding schem e that has very low computati onal c omplexity, which i s sub-optimum, in g eneral. But if ۯ and ۾ are Hadamard matrices, the overa ll decoder is ML. Tensor Decoding Algorithm: Suppose the rec eived vector at the decode r is ܻ ൌ ۲ܺ ܰ , where ܰ is the noise ve ctor in an AWGN channe l. The decoding algor ithm is given below: Step 1 Multiply both sides by ۾ ିଵ ٔ ۷ . We get ܻ ᇱ ൌ ൣ ܻԢ ଵ ڮ ܻԢ ൧ ൌ ሺ ۾ ିଵ ٔ ۷ ሻ ܻ ൌ ሺ ۷ ٔ ۱ ሻ ܺ ܰ ᇱ ൌ ሺ ۷ ٔ ۱ ሻ ሾ ܺ ଵ ڮ ܺ ሿ ܰ ᇱ ǡ where ܻԢ is the ሺ ݅ െ ͳ ሻ ݉ ͳǡ ǥ ǡ ݅ ȉ ݉ ent ries of ܻԢ a nd ܺ i s the ሺ ݅ െ ͳ ሻ ݊ ͳǡ ǥ ǡ ݅ ȉ ݊ entries of ܺ for ݅ ൌ ͳǡ ǥ ǡ ݇ . Step 2 For ea ch ݅ א ሼ ͳǡ ǥ ǡ ݇ ሽ , acc ording to Lemma 5, multiply ܻԢ by ۯ ିଵ and find the vector ܺ ଶ by minimizing ฮ൫ۯ ିଵ ܻԢ െ ۯ ିଵ ۰ܺ ଶ ൯ െ ÁÂ_Ãሺۯ ିଵ ܻԢ െ ۯ ିଵ ۰ܺ ଶ ሻฮ a nd se t the ve ctor ܺ ଵ to be equa l to ÁÂ_Ãሺۯ ିଵ ܻԢ െ ۯ ିଵ ۰ܺ ଶ ሻ . ܺ ൌ ൣ ܺ ଵଵ ܺ ଶଵ ǥ ܺ ଵ ܺ ଶ ൧ is the output of t he de coder. To se e the power of thi s algorithm, let us take a CDMA system of size (64, 104) with the code matri x ۲ ൌ ۶ ଼ ٔ ۱ ଼ൈଵଷ , where ۶ ଼ denotes an ͺ ൈ ͺ Hadamard matrix and ۱ ଼ൈଵ ଷ is t he m atrix shown in Table 2. Since ۱ ଼ൈଵଷ has a n ͺ ൈ ͺ Hada mard sub- matrix, the dec oding of all the ͳͲͶ users have a complexi ty of about ͺ ൈ ͵ʹ ൌ ʹ ଼ Euclidea n distance ca lculation of ͺ -dimens ional vectors. The de coder is a lso ML. This implies a drastic sa ving compared t o the direct implementa tion of the ML decoder, which needs ʹ ଵସ Euc lidean di stance cal culation of Ͷ dimens ional vec tors. In t he next section, the COW codes with the proposed decoding method is simulated and compa red t o binary W BE and random c odes. VI. Simulation Results For s tudying the behavior of COW codes in the prese nce of noise, we consider three diffe rent CDMA systems in an AWGN channe l. The first one is a system with the chip rate of ݉ ൌ Ͷ and ݊ ൌ ʹ ሺͶǡʹሻ users and the sec ond one is of dimension ሺͶǡͻሻ and the las t one is ሺͶǡͳͲͶሻ . For ea ch system, we compare three c lasse s of codes: random, BWBE, and COW se quences . We use a n it erative dec oder with s oft limiting 9 in the c ase of random and BW BE c odes, which pe rforms bet ter than Parallel Interferenc e Ca ncella tion (PIC) with hard limite rs [28]. For decoding COW codes, we apply the T ensor Decoding Algorithm (which is ML) discus sed i n the previous section. Note tha t we c annot us e ML decoder for the BWBE 10 and random code s since thei r implement ations are impractica l. Thes e dec oding methods with the three diffe rent over-loading f actors are compared with the orthogonal CDMA (Hada mard code of size ሺͶ ൈ Ͷሻ ), which perform s the sa me as a synchronous binary PSK system- Figs. 4-6. As s een in Fig. 4, for a n over-loaded C DMA of size ሺͶǡʹሻ for ܧ Ȁܰ values less than ͳͲ dB, the BWBE c odes perf orm slightly bette r. But when ܧ Ȁܰ increase s beyond ͳͲ dB, the Bit-Error-Rate (BER) of this system saturates. This phenome non is due to the fa ct that the mapping of the BWBE code i s not invertible . Thus when we use B WBE codes, we cannot decrease the BER lower than a threshold value even by increasing ܧ Ȁܰ to infinity (or using a ny scheme of decodi ng). Since the mappings of COW codes are one-to-one and the proposed de coder is ML, the BE R tends to zero as ܧ Ȁܰ increas es. The simul ation result s of Fig. 4 are repea ted in Figs. 5 and 6 for the othe r over-loaded COW c odes ሺͶǡ ͻሻ and ሺͶǡͳͲͶሻ , respecti vely. These figures highlight the fac t that for higher over- loading fac tors, the COW codes with their simple ML decoding outperform other codes with iterati ve decodi ng. BW BE codes perform bette r than random codes due to its minimum T SC property, but t he problem with such codes is that the interference cannot be cance lled totall y and we cannot design opti mum ML 9 F Marvasti, M Ferdowsizadeh, and P P ad , “ Iterative synchronous a nd Asynchr onous Multi -User Detection with O ptimum Soft limiter ” U S Patent applica tion numb er 12/122668 filed on ! 5/17/2008. 10 ! There are some exce ptions that are discussed in [29] . decoders due to t heir c omplexity. It is worth mentioning that in Fig. 6, although the system is about Ψʹ over-loaded, the performance of COW codes is to within ͵ dB of the orthogonal Hadam ard fully-loaded C DMA, while the B WBE code has the s ame performance a s the COW code for ܧ Ȁܰ less dB. But a t higher ܧ Ȁܰ values, the COW c odes cl early outperf orm the BWBE Codes. Fig. 4. Bit-error-r ate versus ܧ Ȁܰ for ͵ classes of codes for a system with Ͷ chips and ʹ users (for comparison, Hadamard codes of size ሺͶ ൈ Ͷሻ is also simu lated). Fig. 5. Bit-error-r ate versus ܧ Ȁܰ for ͵ classes of codes for a system with Ͷ chips and ͻ users (for comparison, Hadamard codes of size ሺͶ ൈ Ͷሻ is also simu lated). Fig. 6. Bit-error-rate versus ܧ Ȁܰ for ͵ classes of codes fo r a system with Ͷ chips and ͳͲͶ users (for comparison, Hadamard codes of size ሺͶ ൈ Ͷሻ is also simu lated). VII. C onclusion In this pa per, we have shown tha t t here e xists a la rge c lass of ሺ݉ ൈ ݊ሻ codes ( ݉ ൏ ݊ ) that are suitable f or over-loade d synchronous CDMA both f or wireless and optic al systems. For a given spreading fact or ݉ , an upper bound for the number of users ݊ has been f ound. For exa mple for ݉ ൌ Ͷ , the upper bound predicts a ma ximum of ݊ ൌ ʹͺ . A tight lower bound and an upper bound for the c hannel capa city of a noiseles s bina ry channel matr ix have been de rived. The lower bound suggests the existence of COW/C OO codes that c an reach the ca pacit y without any err ors. Mathemat ically, we have proved the existence of codes of size ሺͶǡͳͶሻ . However, since the de coding of such over-loaded code s are not practical , we have developed codes of size ሺͶǡͳͲͶሻ that are generated by K ronecker product of a Hadamard matrix by a sm all matrix of s ize ሺͺǡͳ͵ሻ . The dec oding ca n be done by a l ook-up table of size ͵ʹ rows. These types of COW codes outpe rform BW BE c odes and other random codes at high over-loaded factors and probability of errors of approximately less t han ͳͲ ିଷ . We suggest f or future work to get better upper bounds f or the ove r-loaded C DMA systems, more practical c odes a t higher over-loadi ng fa ctors, and better decoding algorithms. Exte nsions to non-binary over-loaded C DMA, as ynchronous C DMA, and channel capacity evalua tions unde r f ading and multipath environment s a re other issues that need f urther rese arch. Also, to incl ude fai rness among use rs, we ne ed to investigate the minimum distance of each COW/ COO code s and i ts random alloca tion. Acknowledgment We would like to sincerely thank t he aca demic staff and the s tudents of Adv anced Communica tions Re search Institute (ACRI), spec ially, Drs J.A. Salehi and M. Na siri- Kenari, M. Ferdowsizade h, A. Amini and V. Aref for t heir helpf ul com ments. Appendix A According to Theorem 3, if we f ind an upper bound for t he number of users ݊ for a giv en number of chips ݉ for the COO c odes, the n this upper bound is al so valid for COW c odes. Suppose ۱ is a COO ma trix, using part c of Corollary 1, we c an add an all row as the 0 th row t o ۱ . If ܺ and ܻ are two vectors in the proof of Theorem 6, then we have ” ሺ ܻ ሻ ൌ ” ሺ ݕ ǡ ݕ ଵ ǡ ݕ ଶ ሻ ” ሺ w ݕ ଷ ǡ ݕ ସ ȁ ݕ ǡ ݕ ଵ ǡ ݕ ଶ ሻ ڮ ” ሺ w ݕ ି ଵ ǡ ݕ ȁ ݕ ǡ ݕ ଵ ǡ ǥ ǡ ݕ ି ଶ ሻ ” ሺ ݕ ǡ ݕ ଵ ǡ ݕ ଶ ሻ ” ሺ w ݕ ଷ ǡ ݕ ସ ȁ ݕ ሻ ڮ ” ሺ w ݕ ି ଵ ǡ ݕ ȁ ݕ ሻ ൌ ” ሺ ݕ ǡ ݕ ଵ ǡ ݕ ଶ ሻ ” ሺ ݕ ǡ ݕ ଷ ǡ ݕ ସ ሻ െ ” ሺ ݕ ሻ ڮ ” ሺ ݕ ǡ ݕ ି ଵ ǡ ݕ ሻ െ ” ሺ ݕ ሻ Ǥ If we denote the maximum value of ” ሺ ݕ ǡ ݕ ଵ ǡ ݕ ଶ ሻ ov er all possible configurations of the first a nd the second rows of ۱ by ܪ͵ and set ܪͳ ൌ ”ሺݕ ሻ , then we have ” ሺ ܻ ሻ ଶ ሺ ܪ͵ െ ܪͳ ሻ ܪͳ . Since ۱ is a COO matrix, ”ሺܻ ሻ ൌ ݊ . Conse quently, ݊ ଶ ሺ ܪ͵ െ ܪͳ ሻ ܪͳ . ܪͳ is the entropy of a binomial r.v. and is depicted in the proof of Theorem 6. For c alcul ating ܪ͵ , le t ൦ ͳ,,, ڮ ڮ ,,,ͳ ͳ,,, ڮ ڮ ,,,ͳ ͳ ڮ ͳ ᇣ ᇤ ᇥ Ͳ ڮ Ͳ ᇣ ᇤ ᇥ , ͳ,,, ڮ ڮ ,,,ͳ Ͳ,,, ڮ ڮ ,,,Ͳ ͳ ڮ ͳ ᇣ ᇤ ᇥ Ͳ ڮ Ͳ ᇣ ᇤ ᇥ ି ି ି ,൪ be 0 th , 1 st and 2 nd rows of ۱ . Thus, we ha ve ” ሺ ݕ ǡ ݕ ଵ ǡ ݕ ଶ ሻ ൌ െ σ Î ሺ ݕ ǡ ݕ ଵ ǡ ݕ ଶ ሻ ]^_ ଶ Î ሺ ݕ ǡ ݕ ଵ ǡ ݕ ଶ ሻ ௬ బ ǡ௬ భ ǡ௬ మ , where Î ሺ ݕ ǡ ݕ ଵ ǡ ݕ ଶ ሻ ൌ σ ቀ షೌష ್ష ቁቀ బ ష భ ష ቁቀ ್ బ ష మ ష ቁቀ ೌ మ ష బ శ భ శ ቁ ଶ . Appendix B For testi ng a matrix to be a COW matrix, a ccording t o L emma 1, t he crudest algorithm i s to c heck ͵ – ͳ vectors for the z ero-vector. Now we introduce a bet ter method t o dec rease this number down t o ሺ͵ ି െ ͳሻȀʹ . Assume that the matrix ۱ ൈ is f ull rank (this i s not a very re stricting condition). Then there are ݉ columns of ۱ that form an invertible ݉ ൈ ݉ matrix. Suppose these columns are t he first ݉ columns of ۱ and c oin the consructed invertible matrix by ۯ and the other columns by ۰ . Thus, ۱ ൌ ሾ w ۯ ȁ ۰ሿ . Using Lemma 1, we know that if ۱ is not a COW matrix, then there exis ts a ሼെͳǡͲǡͳሽ -vector ܺ such that ۱ܺ ൌ ͲǤ Suppose ܺ ൌ ሾ ܺ ଵ ܺ ଶ ሿ such that ۱ܺ ൌ ۯܺ ଵ ۰ܺ ଶ ൌ Ͳ . Thus ܺ ଵ ൌ െ ۯ ିଵ ۰ܺ ଶ . Hence t o check that ۱ is a COW matrix, we should s earch through differe nt possibili ties for ܺ ଶ , i.e., ሼ െͳǡͲǡͳሽ ି (except ሼ Ͳሽ ି ) to see whethe r െۯ ିଵ ۰ܺ ଶ bel ongs to ሼെͳǡͲǡͳሽ or not. This needs ͵ ି െ ͳ se arches, but one half of t hese vectors a re the negatives of the other ha lf, thus we need only ሺ ͵ ି െ ͳ ሻ Ȁʹ se arches. Appendix C We prove this theore m in 3 st eps. Def ine ۲ ൌ ۶ ଶ ۪۱ and Ø ൌ ሼ w ۲ܺ ȁ ܺ א ሼ െͳǡͲǡͳ ሽ ଶ ሽ . Step 1 An interesting observation is that if ܼ א ሼ ͳǡ െ ͳ ሽ ଶ and ܼ ב Ø , then the ma trix augmentation ሾ w ۲ ȁ ܼ ሿ is a COW matrix. The proof of this s tep is trivial. Step 2 We would like to prove that if Ú ൌ ܳ ሼ ͳǡ െͳ ሽ ଶ , w here ܳ is an a rbitrary ʹ݉ ൈ ͳ integer vec tor, then ȁ Ø ת Ú ȁ ʹ ାଵ . To show thi s, suppose t hat ܻ א Ø ת Ú . Then there exis ts a ሼെͳǡͲǡͳሽ -vector ܺ ଶൈଵ ൌ ሾ ܺ ଵ ܺ ଶ ሿ , where ܺ ଵ ǡ ܺ ଶ א ሼ െͳǡͲǡͳሽ and ܻ ൌ ۲ܺ . ܻ ൌ ۲ܺ ൌ ቂ ۱ ۱ ۱ െ۱ ቃ ܺ ଵ ܺ ଶ ൨ ൌ ۱ܺ ଵ ۱ܺ ଶ ۱ܺ ଵ െ ۱ܺ ଶ ൨ and ܻ ൌ ۱ܺ thus ܻ ൌ ܻ ଵ ܻ ଶ ܻ ଵ െ ܻ ଶ ൨ . Since there is a one-to-one c orrespondence bet ween t he set of v ectors ሾ ሺ ܻ ଵ ܻ ଶ ሻ ሺ ܻ ଵ െ ܻ ଶ ሻ ሿ and the set of vectors ሾ ܻ ଵ ܻ ଶ ሿ , the cardinali ty of the two sets a re equal. Denote the ݅ th entry of ܻ ଵ by ሺ ܻ ଵ ሻ , thus we ha ve ሺ ܻ ଵ ሻ ൌ σ ܿ ሺ ܺ ଵ ሻ ୀଵ ൌ ሺ ÞßH,Ãà áHI,^â,Ã^ÃãHI^,HÃÞIÂHÁ,^â,ܺ ଵ ሻ ,ሺ ^ä,ʹሻ . He nce the e ntries of ܻ ଵ are eithe r all odd or all even. Also this holds for ܻ ଶ . Since ܻ א Ú , then for every ݅ , ͳ ݅ ݉ , we have ൜ ሺ ܻ ଵ ሻ ሺ ܻ ଶ ሻ ൌ ܳ േ ͳ ሺ ܻ ଵ ሻ െ ሺ ܻ ଶ ሻ ൌ ܳ ା േ ͳ w . By an ea sy calcula tion the solutions of the above equations are ቐ ሺ ܻ ଵ ሻ ൌ ொ ାொ శ ଶ േ ͳǡ ሺ ܻ ଶ ሻ ൌ ொ ିொ శ ଶ , ሺ ܻ ଵ ሻ ൌ ொ ାொ శ ଶ ǡ ሺ ܻ ଶ ሻ ൌ ொ ିொ శ ଶ േ ͳ w . The above solutions are in two c ategories. Category 1 consists of the solutions which have ʹ choice s f or ሺ ܻ ଵ ሻ and only one choice for ሺ ܻ ଶ ሻ , while category 2 consists of solutions with a s ingle choice f or ሺ ܻ ଵ ሻ and ʹ choic es f or ሺ ܻ ଶ ሻ . Now, for the determination of ȁ Ø ת Ú ȁ , first a ssume that all e ntries of ܻ ଵ are even and ݈ entries of ܻ ଵ ha ve two choices. Hence, the number of ሾ ܻ ଵ ܻ ଶ ሿ vec tors are ʹ ʹ ି ൌ ʹ , be cause the ݈ correspondi ng element s i n ܻ ଶ ha ve only one choice and the othe r ݉ െ ݈ elem ents i n ܻ ଶ have ʹ c hoice s. The same asserti on holds when a ll entries of ܻ ଵ are odd. Thus, ȁ Ø ת Ú ȁ has at most ʹ ʹ ൌ ʹ ା ଵ eleme nts. Step 3 Now, suppose t hat we a dd ݇ columns to ۲ , ݇ ൏ ڿ ሺ ݉ െ ͳ ሻ ]^_ ଷ ʹ ۀ , a nd the resultant matrix, ۳ , is a COW matrix. We wish to prove one can a dd a nother column to ۳ to obtain a COW matrix with ʹ݊ ݇ ͳ columns. Assume that ۳ ൌ ሾ w ۲ ȁ ۴ ሿ , where ۴ ൌ ሾ w ܹ ଵ ȁ w ڮ ȁ ܹ ሿ , a nd ܹ i s a ʹ݉ ൈ ͳ vector, for ݅ ൌ ͳǡ ǥ ǡ ݇ . Let ܺ א ൛ – ͳǡͲǡͳൟ ଶା , ܺ ൌ ሾ ܺ ଵ ܺ ଶ ሿ , where ܺ ଵ is a ʹ݊ ൈ ͳ vector and ܺ ଶ is a ݇ ൈ ͳ vect or. Henc e, ۲ܺ ଵ ൌ ۳ܺ െ ۴ܺ ଶ . By Ste p 2 and the f act that ܺ ଶ has ͵ diff erent possibilitie s, we have ȁ F ת ሼ ͳǡ െ ͳ ሽ ଶ ȁ ൌ σ ȁሼ ۲ ȉ ሼ െͳǡͲǡͳ ሽ ଶ ሽ ת ሼ െ۴ܺ ଶ ሼ ͳǡ െͳ ሽ ଶ ሽȁ ͵ ʹ ା ଵ మ where F ൌ ሼ w ۳ܺ ȁ ܺ א ሼ ͳǡ െͳ ሽ ଶା ሽ . Now, if ͵ ʹ ା ଵ ൏ ȁሼ ͳǡ െ ͳ ሽ ଶ ȁ ൌ ʹ ଶ , then we can add another column to matrix D by applying Step 1. Thus, we can add a t leas t ڿሺ ݉ െ ͳ ሻ ]^_ ଷ ʹ ۀ vectors t o ۲ a nd obtain a bigger COW matrix. ז Appendix D Assume ۶ ൌ ሾ w ܪ ଵ ȁ w ڮ ȁ ܪ ሿ is an ݉ ൈ ݉ Hadamard matrix. Let ۱ ൌ ൦ ww ܪ ଵ ȁ w ڮ ȁ ܪ ଵ ᇩ ᇭ ᇭ ᇪ ᇭ ᇭ ᇫ ተ ڮ ተ w ܪ ȁ w ڮ ȁ ܪ ᇩ ᇭ ᇭ ᇪ ᇭ ᇭ ᇫ w ൪ be an ݉ ൈ ݊ code matrix. If ܺ is a da ta vector, then ۱ܺ ൌ ܽ ଵ ܪ ଵ ڮ ܽ ܪ , where f or e very ݅ , ͳ ݅ ݉ , ܽ can t ake ͳ diffe rent values. Thus, ۱ܺ can have ቀ ͳቁ different values and thus its logarithm is a l ower bound for the s um channe l ca pacity. ז Appendix E Pick ݂ א š ǡ random ly by choosing entries of t he de fining mat rix of ݂ independent ly and uniformly f rom ሼͳǡ െ ͳሽ . For a ny vertex ܺ of the ݊ -dime nsional hyper-cube ™ , one has ñ൫ห݂ ିଵ ൫݂ ሺ ܺ ሻ ൯ห൯ ൌ ñ ቌ ͳ ሺ ሻ ୀ൫ ᇲ ൯ ᇲ א™ ቍ ൌ ñ ቀͳ ሺ ሻ ୀ൫ ᇲ ൯ ቁ ᇲ א™ ൌ Î൫݂ ሺ ܺ ሻ ൌ ݂ ሺ ܺ ᇱ ሻ ൯ ᇲ א™ where ݂ ିଵ , ͳ ሺ ሻ ୀ൫ ᇲ ൯ , and Î are the pre-image s et, conditional if statement, and the probability function, respectively, and ñ is expectation over ݂ . If ܺ and ܺ ᇱ differ in ݇ places, then Î൫݂ ሺ ܺ ሻ ൌ ݂ ሺ ܺ ᇱ ሻ ൯ ൌ ە ۖ ۔ ۖ ۓ Ͳ Ââ,݇ ൌ ʹ݆ ͳ ቌ ቀ ଶ ቁ ʹ ଶ ቍ Ââ,݇ ൌ ʹ݆ w (Note that for ݂ ሺܺ ሻ and ݂ ሺ ܺ ᇱ ሻ to be equal, all of their ݉ entries should be equal which are independent equiprobable events.) Combining the above equations, we get ñ൫ห݂ ିଵ ൫݂ ሺ ܺ ሻ ൯ห൯ ൌ σ ቀ ଶ ቁ ቔ మ ቕ ୀ ቆ ቀ మೕ ೕ ቁ ଶ మೕ ቇ ൌ © ሺ ݉ǡ ݊ ሻ and hence ñ൫ σ ห݂ ିଵ ൫݂ ሺ ܺ ሻ ൯ห א ™ ൯ ൌ ʹ © ሺ ݉ǡ ݊ ሻ . Thus, there e xists an ݂ א š ǡ s uch that σ ห݂ ିଵ ൫݂ ሺ ܺ ሻ ൯ห א ™ ʹ © ሺ ݉ǡ ݊ ሻ . But if ȁ ݂ ሺ ™ ሻ ȁ ൌ ݇ and the pre-images of the ݇ values of ݂ ሺ ™ ሻ have cardinalities ݊ ଵ ǡ ǥ ǡ ݊ , then σ ห݂ ିଵ ൫݂ ሺ ܺ ሻ ൯ห א ™ ൌ σ ݊ ଶ ୀଵ . By Cauchy-S chwartz inequality: ʹ ൌ σ ݊ ൫ σ ݊ ଶ ୀଵ ൯ Φ ൫ σ ͳ ୀ ଵ ൯ Φ ୀଵ ൫ʹ © ሺ ݉ǡ ݊ ሻ ൯ Φ ݇ Φ . Thus, ݇ ʹ Ȁ© ሺ ݉ǡ ݊ ሻ and Ÿ ሺ ݉ ǡ ݊ ሻ ]^_ ଶ ݇ ݊ – ] ^_ ଶ ©ሺ݉ǡ ݊ ሻ . ז Appendix F To prove t he theorem, we ne ed a classical inequality a bout la rge deviations of sim ple random walk: Let ܵ ൌ ߜ ଵ ߜ ଶ ڮ ߜ , where ߜ ଵ ’ s are independent and equal to െͳ , ͳ w ith probability ͳȀʹ . For any O , ,Ͳ , from [30] we have Î ൫ ȁ ܵ ȁ ߣ ξ ݊ ൯ ʹ݁ ష ഊ మ మ . Let ݂ ሺܺ ሻ ൌ ۻܺ be the mapping with the ma ximum image size, i.e., ȁ ݂ ሺ ™ ሻȁ ൌ ʹ େ ሺ ǡ ሻ . Pick ܺ א ™ randomly wit h uniform distribution and let ܻ ൌ ۻܺ ൌ ሾ ݕ ଵ ڮ ݕ ሿ for ݆ , ͳ ݆ ݉ , ݕ ൌ σ ݉ ݔ ୀଵ i s a summati on of ݊ inde pendent random െͳ , ͳ ’ s (because of the randomness of ݔ ’ s) and so according to the random walk property , Î൫หݕ ห ߣ ξ ݊൯ ʹ݁ ష ഊ మ మ . This i mplies t hat if # ൌ ൣെߣ ξ ݊ǡ ߣ ξ ݊൧ , the n Î ሺ ܻ ב # ሻ ൌ Î൫ ݆,ͳ ݆ ݉,หݕ ห ߣ ξ ݊ ൯ ʹ݉݁ ష ഊ మ మ , which means that t here a re at most ʹ ାଵ ݉݁ ష ഊ మ మ points of ݂ሺ™ ሻ outside # . Now, notice tha t ȁ ݂ ሺ ™ ሻ ת # ȁ is at m ost equal to the number of i nteger points in # with a ll coordinates having the same odd or even pa rity as ݊ w hich i s less th an ൫ߣ ξ ݊ ൯ . Combining these two facts, we g et ʹ େ ሺ ǡ ሻ ൌ ȁ ݂ ሺ ™ ሻ ȁ ൌ ȁ ݂ ሺ ™ ሻ ת # ȁ ȁ ݂ ሺ ™ ሻ ת # ȁ ൫ߣ ξ ݊ ൯ ʹ ାଵ ݉݁ ష ഊ మ మ ൌ ʹ൫ߣ ξ ݊ ൯ . The last equality comes from def inition of ߣ given in Theorem 8, which implies that Ÿ ሺ ݉ ǡ ݊ ሻ ݉ ቀ ଵ ଶ ]^_ ଶ ݊ ] ^_ ଶ ߣ ቁ ͳ . ז RERENCES: [1] S. Verdu, Multiuser D etect ion, Cambridge University Press, New York, NY, USA, 1998. [2] A. Kapur and M.K. Varana si, “ Multiuse r detection f or over-loaded CDM A systems, ” IEEE Transactions on Information Theory , vol. 49, no. 7, pp. 1728-1742, Jul. 2003. [3] S. M oshavi, “ Multi -user detec tion for DS-CDMA c ommunica tions, ” IEEE Communications Magazine , vol. 34, no. 10, pp. 124-136, Oc t. 1996. [4] F.R. K. Chung, J .A. Salehi , a nd V.K. Wei , “ Optica l ort hogonal code s: design, analysis and a pplicati ons, ” IEEE Transac tions on Information Theory , vol. 35, no. 3, pp. 595-604, Ma y. 1989. [5] S. Ma shhadi and J .A. Salehi, “ Code -Division Multiple-Access techniques in optical fiber networks — Part III: Optical AND g ate rec eiver structure with generalized optical orthogonal c odes, ” IEEE Transactions on C ommunications , vol. 54, no. 6, pp. 1349-1349, J ul. 2006. [6] S. V erdu and S. Shamai, “ Spectral effic iency of CDMA with random spreading, ” IEEE Transactions on Information Theory , vol. 45, no. 2, pp. 622-640, Mar. 1999. [7] A .J. Grant and P.D . Alexande r, “ Random sequence multi -sets for synchronous code-division multiple-a ccess channe ls, ” IEEE Transac tions on Information Theory , vol. 44, no. 7, pp. 2832-2836, Nov. 1998. [8] F. Vanha verbeke, M. Moene cla ey, a nd H. Sari, “ DS -CDMA with two se ts of orthogonal sprea ding seque nces and iterative dete ction, ” IEE E Communications Letters , vol. 4, no. 9, pp. 289-291, Sep. 2000. [9] H. Sari, F. Vanhaverbeke, and M. Moenec laey, “ Multiple a cce ss us ing two sets of orthogonal signal waveforms, ” IEEE Communications Let ters , vol. 4, no. 1, pp. 4-6, Jan. 2000. [10] F. Va nhaverbeke, M. Moenec lae y, a nd H. Sari, “ Increas ing CDMA c apacity using multiple orthogonal s preading sequenc e s ets and successive interf erence cancel lation, ” in Proc . IEEE International Conf erence on Communications (ICC ’ 02) , vol. 3, pp. 1516-1520, New York, NY, USA, April-May 2002. [11] H. Sari, F. Vanhaverbeke, and M . Moenec lae y, “ Extending the capac ity of multiple acce ss channels, ” IEEE Communications Magazine , vol. 38, no. 1, pp. 74- 82, Jan. 2000. [12] M. Kobayashi, J . Boutros, and G. C aire, “ Succes sive interf erence cance llation with SISO decoding and EM channe l estimat ion, ” IEEE J ournal on Selected Areas in Communications , vol. 19, no. 8, pp. 1450-1460, Aug. 2001. [13] D. G uo, L.K. R asmussen, S. Sun, a nd T. J. Lim, “ A matrix-alge braic approac h to linear pa rallel interf erence c ancel lation in CDMA, ” IEEE Transactions on Communications , vol. 48, no. 1, pp. 152-161, Jan. 2000. [14] G. Xue, J. Weng, T. Le-Ngoc, and S. Tahar, “ Adaptive multistage parallel interference c ancellation for CDMA, ” IE EE Journal on Selected Areas in Communications , vol. 17, no. 10, pp. 1815-1827, Oct. 1999. [15] X. W ang and H.V. Poor, “ Ite rative (turbo) sof t interf erence c ancell ation and decoding for coded CDMA, ” IEEE Tr ansactions on Communicati ons , vol. 47, no. 7, pp. 1046-1061, Jul. 1999. [16] M.C. Reed, C.B. Schlegel, P.D. Alexander, and J.A. Asenstorfe r, “ Iterat ive multiuser dete ction for CDMA with FEC: nea r-single-user performanc e, ” IEEE Transactions on Communications , vol. 46, no. 12, pp. 1693-1699, Dec. 1998. [17] B. Natarajan, C.R. Nassar, S. Shatt il, M. Michelini, and Z. Wu, “ High performance M C-CDMA via carrie r interferometry c odes, ” IEEE Transact ions on Vehicular Technology , vol. 50, no. 6, pp. 1344-1353, Nov. 2001. [18] M. A khavan-Bahabdi, and M. Shiva, “ Double orthogonal codes f or increasing capacity in MC-CDMA systems, ” Wireless and Optical C ommunications Networks , WOCN 2005, pp. 468-471, Mar. 2005. [19] J.L. Massey and T. Mit telholzer, “ Welch ’ s bound and se quence sets for code - division multi ple-access systems, ” in Sequences II, Me thods i n Communicat ion, Security, and Computer Sciences , R. Ca pocelli, A. De Santis, a nd U. Vaccaro, Eds. New York: Springer-Verlag, 1993. [20] L. Wel ch, “ Lower bound on t he ma ximum c ross corre lation of signals (Coressp.), ” IEEE Transactions on Information Theory , vol. 20, no. 3, pp. 397-399, May. 1974. [21] G.N. Karystinos and D.A. Pados, “ Minimum total -squared-correlation design of DS-CDMA bi nary signature sets , ” in Proc. IEEE Global Tele communications CONFERENCE (GL OBE-COM ’ 01) , vol. 2, pp. 801-805, San Antonio, Tex, USA, Nov. 2001. [22] G.N. K arystinos and D. A . Pados, “ New bounds on the total squared c orrelation and optimum design of DS-CDMA bina ry s ignature s ets, ” IEEE T ransactions on Communications , vol. 51, no. 1, pp. 48-51, Jan. 2003. [23] M . Rupf and J . L. Massey, “ Optimum s equence multisets for synchronous code- division multiple-a cce ss c hannels, ” IEEE Transactions on Information Theory , vol. 40, no. 4, pp. 1261-1266, J ul. 1994. [24] P. Pad, F. Marvasti, K. Alisha hi, and S. Akbari, “ Errorless c odes for over-loaded synchronous CDMA s ystems and evaluati on of channe l ca pacity bounds, ” in Proc . IEEE International Symposium on Information Theor y ( ISIT ’ 08) , pp. 1378-1382, Toronto, ON, Canada , Jul. 2008. [25] D. Tse and P. Viswana th, Fundamentals of Wirel ess Communications, Cambridge Univ ersity Press, 2005 . [26] K. Alishahi, F. Marvasti, V. Aref, and P. Pad, “ Bounds on the S um Capacity of Synchronous Binary CDMA Cha nnels, ” arXiv:0806. 1659, Jun. 2008. [27] P. Pad, M. Soltanolkotabi, S. Hadikhanlou, A. Enayati, and F. Marvast i, “ Errorless Codes for Over -loaded CDMA with Ac tive User Dete ction, ” [28] R. van der Hof stad and M.J. Klok, “ Performance of DS-CDMA systems with optimal hard-decision parallel interference cancellation, ” IEEE Transacti ons on Information Theory , vol. 49, no. 11, pp. 2918-2940, Nov. 2003. [29] M.J. Faraji, P. Pad, and F. Marvasti, “ A New Method f or Constructing Large Size WBE Codes with Low Complexity ML Decoder, ” [30] N. Alon and J. Spencer, The Probabilistic Method , John Wiley & Sons, 2002.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment