Success Exponent of Wiretapper: A Tradeoff between Secrecy and Reliability
Equivocation rate has been widely used as an information-theoretic measure of security after Shannon[10]. It simplifies problems by removing the effect of atypical behavior from the system. In [9], however, Merhav and Arikan considered the alternativ…
Authors: Chung Chan
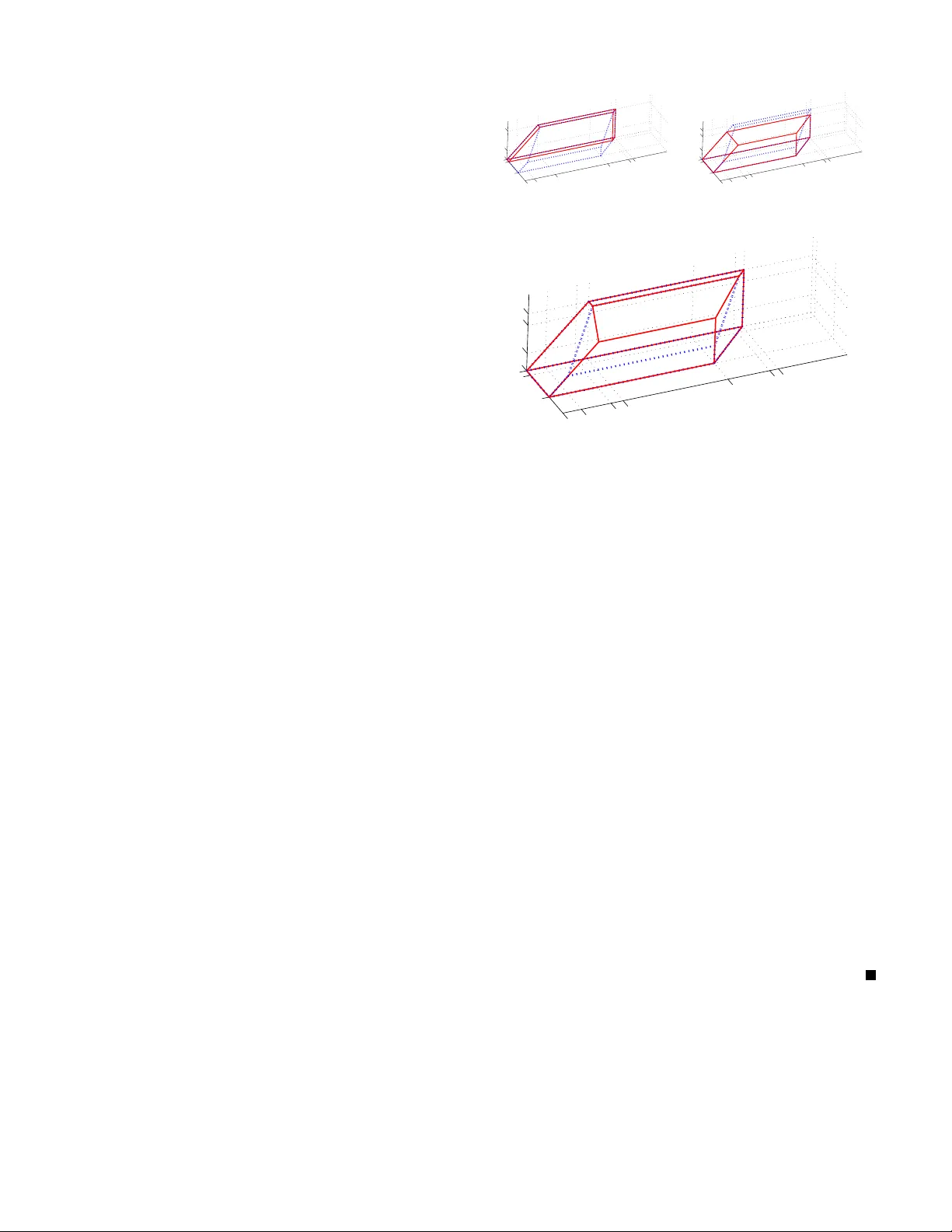
1 Success Exponent of W iretapper : A T radeof f between Secrec y and Reliability Chung Chan Abstract —Equivoca tion rate has been widely used as an informa tion-theoretic measur e of security after Shann on[ 12 ]. It simplifies problems by remo ving the effect of atypical beh a vior from the system. In [ 11 ], h owe ver , Merhav and Arikan consid - ered the alternativ e of using guessing exponent to analyze the Shannon’s ci pher system. Because guessin g exponent captures the atypical beha vior , the strongest e xpressible notion of secr ecy requires the more stringent condition that the size of th e key , instead of its entr opy rate, to b e equ al t o th e size of the message. 1 The relationship b etween equivocation and guessing exponent are also i n vestigated in [ 8 ][ 9 ] but it is unclear which is a better measure, and whether there is a unifying measure of security . Instead of using equivoca tion rate or guessing exponent, we study the wiretap channel in [ 2 ] using the success exponent, defined as the exponent of a wiretapper successfully learn the secret after making an exponential number of guesses to a sequential verifier that give s yes/no answer to each guess. By extending the coding scheme i n [ 2 ][ 6 ] and the con verse proof in [ 4 ] with th e new Overlap L emma V .2 , we obtain a t radeoff between secrecy and reliability expressed in t erms of lower bounds on the error and su ccess exponen ts of authorized an d respectiv ely un authorized decoding of the transmitted messages. From th is, we obtain an inn er bound to the region of strongly achiev able publ ic, private and guessing rate triples for which the exponent s are strictly positive. T he closure of this region is equivalent to the closur e of the region in Theorem 1 of [ 2 ] wh en we treat equivocation rate as the guessing rate. Howev er , it is unclear i f the inner bou nd is tight. A C K N O W L E D G M E N T I would like to tha nk Professor Lizhong Zheng for his guidanc e and v a luable com ments; Jing Sheng fo r his inspiring discussion that eventually leads to th e proof of Prop osi- tion VII.3 ; a nd above all, my family for their support and encour agements. I . I N T RO D U C T I O N The basic m odel of a cryp tograph ic/secrecy system inv o lves a send er Alice who wants to send a message S a s secretl y a s possible to the intend ed receiver Bob. The basic mo del of a cryp tanalytic attack, on th e other h and, inv olves a cr ypt- analyst/wiretapp er Eve wh o a ttempts to learn the secret as much as po ssible based on h er observation Z . How secretly a message is sent, or how much informa tion is leaked, must therefor e b e quantified be fore one ca n de sign and optimize a Manuscript written on May 28, 2008. Chung Chan ( chungc@mi t.edu ) is with the Laboratory of Information and Decisio n Systems, Department of Electrica l Engineering and Computer Science , Massachusetts Institute of T echn ology . 1 This is the conditi on for a finite system to achie ve perfect secrec y as pointed out by Shannon[ 12 ]. P S f r a g r e p l a c e m e n t s { S ( n ) } { ˆ S ( n ) } rate H ( S | Z ) secrecy system Eve genie in prob. − − − − → { S ( n ) } { Z ( n ) } Fig. 1. Genie-a ided corre ction channel cryptog raphic system or a c ryptanaly tic attack for the resp ec- ti ve pu rposes. The aposteriori probability f unction P S | Z is a sufficient statistics of the security of the system as it gives all the possible values of the secret an d their associated p robabilities for every possible realization of th e wire tapper’ s observation. In particular, th e important n otion of a system b eing perfectly secure, refe rred to as perfect secr ecy by Shannon [ 12 ], can be characte rized as the aposteriori prob ability equ al to the prior, i.e. P S | Z = P S . In oth er words, Eve’ s observation is indepen dent of the secret, or equivalently , the system is at the same level of security whether Z is observed or not. It is co n venient to sum marize the ap osteriori proba bility function by the index called equivoc ation H ( S | Z ) . It is roughly the amo unt of infor mation the wir etapper need s to gather in addition to Z to perfectly recover S . On e precise o perationa l meaning of equiv ocation, as illustrated in Fig. 1 , is the minimum ach iev able rate f or sour ce codin g an iid sequence of S ( n ) with th e iid sequ ence of Z ( n ) as side in formatio n at the decoder . 2 T o achieve perfect secr ecy , it is necessary and sufficient to have H ( S | Z ) = H ( S ) . Alice can also try t o protect the secret up to an equiv ocation H ( S | Z ) below H ( S ) if perfect secrecy is co stly an d u nnecessary . The amount o f additional in formatio n E ve need s to gather to break the system m ay n ot r eflect how difficult it is to obtain them. For examp le, getting just on e b it of inf ormation from Alice or som eone who know the secret may require significant effort in the search f or that p erson, fo llowed by len gthy interrog ation. In some situations, Eve does no t play a pa ssi ve role of receiving additional infor mation that is concisely stated (i.e. max imally comp ressed by a gen ie), but instead plays an activ e role in id entifying an d extracting re le vant informatio n from d isorganized sources. Thu s, on e shou ld question wh ether equiv o cation is applicable for the case o f interest, albeit its mathematical conv e nience. A n atural altern ativ e m easure o f secu rity , as in vestigated 2 This is the correction data model original ly proposed by Shannon[ 12 ] exc ept that the genie does not need to know Z nor any decision feedback from Bob . 2 by Mer hav and Arikan[ 11 ], is ro ughly the ability that E ve perfectly learn the secret fro m yes/no answers to “Is the secr et equal to ...?” ty pe o f question s. In the mo del, E ve seq uentially verify her guesses of the secret by asking yes/no questions. The number of gu esses and verification s she n eeds to make until she is within some pro bability o f g uessing the secret co rrectly indicates her effort and ab ility to extract inform ation about the secret. So metimes the system itself provides such a verifier which help c orrect careless mistakes made by the authorized user . This potentially leak s info rmation to unauthor ized users who also have access to the verifier , ju st as in the case of a login system. A s a system designer, he m ay be inter ested to know h ow many wro ng passwords should be allowed for eac h session so that the chances of successfully breaking into the account is reasonab ly small. Although this success pro bability does not have a way to expr ess the no tion of perfect secrecy in general (See Example A.1 ), it is a n atural fit for this pr oblem as it provides th e numb er of trials as an ad ditional p arameter to optimize . In the seq uel, we will consider th e wiretap ch annel pr oblem in [ 2 ]. A key result from [ 2 ] is the sing le letter characterizatio n of the secrecy cap acity , d efined as the maximu m r ate at which the secr et can be transmitted to Bob by a b lock cod ing scheme with arb itrarily small err or pro bability an d the equiv o cation rate equal to th e message rate. T ransmitting at rate above this secrecy capacity , on e faces the trade- off a lower equiv ocation rate. Transmitting at rate below the secr ecy capac ity , however , equiv o cation r ate is cap ped at the message rate. Th ere seems to be little point in fur ther reducin g th e rate b elow secrecy capacity . I f o ne also car es ab out delay , i.e. how fast the erro r probab ility conv e rges to zero, further r educing th e rate below secrecy capacity can b e b eneficial. What is the tradeo ff then? Secrecy comes with a co st of reliability of the author ized decodin g. T o ch aracterize which l ev el of secrecy and reliability are simultaneously achiev ab le for each rate, we will use the stand ard notion of err or exponents for Bob and Eve in deco ding the ir messages as a measure of reliability . For secrecy , we will u se the exponen t of the succ ess probab ility , or success exponent f or short, that Eve learns the secret with in an exponential number o f guesses. The rest of the p aper will be organized as f ollows. Sec- tion III defines the wiretap chan nel problem we consider . Section IV describes the p roposed coding scheme. Section V explains the computation o f the success exponent u sing a technique we call the Overlap Lemma V .2 . Section VI explains the compu tation o f the error e xponen ts using the Packing Lemma[ 3 ]. Fin ally , the desired lower bou nds on the expon ents will be stated in Section VII . Section VII I gives the con clusion and some o pen pro blems. For readers who would like to skip to the main result, Section II provid es a br ief summ ary o f notations. I I . P R E L I M I N A R I E S Calligraphic font denotes a set, e .g. A , which is always assumed finite unless oth erwise stated. 2 A and A c denote the power set and co mplemen t of A r espectiv ely . A ∪ B , A ∩ B and A \ B den otes the usual set operation s, w hich are the P S f r a g r e p l a c e m e n t s X ∈ X Y ∈ Y Z ∈ Z Alice Eve Bob channel W b W e Fig. 2. W iretap channel model union, intersectio n, and difference respectively . Avg a ∈A (or Avg a for short) denote the averaging operatio n 1 |A| P a ∈A . R , R + and Z + denotes the set of real nu mbers, non -negative real numb ers, and positive integers. Occasionally withou t ambiguity , a positiv e integer L will also be used to d enote the set { 1 , . . . , L } as in l ∈ L . Bold letter such as x d enotes an n -sequ ence { x ( i ) } n i =1 = ( x (1) , . . . , x ( n ) ) ; and u ◦ x denotes element-wise concaten ation { ( u ( i ) , x ( i ) ) } n i =1 . San ser if f ont is used for rando m variables and stoch astic function s, e.g. X , f and W b . P ( Y ) X denotes the set of all possible condition al probability distrib u tions P Y | X of a rando m variable Y taking values fro m Y , den oted as Y ∈ Y , given a random variable X ∈ X . The (con ditional) probab ility distribution will also be vie wed as a ro w vector ( matrix). e.g. P X P Y | X denotes th e matrix multiplication , which gives the marginal distribution P Y . P X ◦ P Y | X denotes the d irect produ ct, which gives the joint distribution P X , Y of the pair ( X , Y ) in this case. P n X denotes the n -th d irect pr oduct such that P X ( x ) = Q n i =1 P X ( x i ) . For any subset A ⊂ X , P X ( A ) = P x ∈A P X ( x ) . E ( X ) den ote the expectatio n of X . δ v ar ( P, Q ) denotes the variation distance ( 25 ) between P and Q . Follo wing the n otations in [ 3 ] for the method of types , P x and P y | x denotes the ty pe ( 6 ) a nd r espectively cano nical condition al typ e ( 8 ). ‘Canon ical’ re fers to th e constrain t (fo r conv enience) th at P y | x ( y | x ) = 1 / |Y | if P x ( x ) = 0 for all ( x, y ) ∈ X × Y . T ( n ) Q or T Q for short d enotes the class of n - sequences of ty pe Q . T V ( x ) d enotes the V -shell of x . P n ( X ) denotes th e set of all types for seq uences in X n . V n ( Q, Y ) ( V n ( Q ) or V n for short) d enotes the set of all canon ical condi- tional types V fo r sequences in Y n . I ( Q, V | P ) , D ( V k W | Q ) , and H ( V | P ) are the cond itional mutual information ( 29 ), div ergence ( 10 ) and entropy ( 11 ) respectively . I ( x ∧ y ) ( 2 0 ) denotes the empirical mutual infor mation. Eq uiv alently , we write T X := T P X and T Y | X := T P Y | X , which are n on-emp ty if the c orrespon ding distributions are valid (cond itional) ty pes. | T Y | X | denote | T P Y | X ( x ) | with x ∈ T X . T o express in equality in the expo nent for f unctions in n , we use a n . 6 b n to denote lim sup n →∞ 1 n log a n is no larger than lim inf n →∞ 1 n log b n . A p iecewise fun ction will be expressed in ter ms of | a | + := max { 0 , a } and | a | − := min { 0 , a } . I I I . P R O B L E M F O R M U L A T I O N A. T ransmission mod el Fig. 2 illustrates a sing le use of the discrete memo ryless wiretap chan nel ( W b , W e ) u sing the dummy rand om variables X , Y and Z . Alice sends a random variable X throu gh the chan- nel. P X ∈ P ( X ) is the prob ability distribution functio n/vector 3 P S f r a g r e p l a c e m e n t s f W n b W n e φ b φ e ψ encoder channels decoder s attack X ∈ X n Y ∈ Y n Z ∈ Z n m ∈ M l ∈ L ( ˆ M b ∈ M ˆ L b ∈ L ˆ M e ∈ M ˆ L 1 ∈ L . . . ˆ L λ ∈ L Fig. 3. Tra nsmission model of X over the finite set X , such that P X = Pr { X = x } ( x ∈ X ) and P X ( A ) = Pr { X ∈ A} ( A ⊂ X ) . The chann el is den oted by the pair ( W b ∈ P ( Y ) X , W e ∈ P ( Z ) X ) o f con ditional pr obability distributions. W e write W b ( X ) and W e ( X ) as the channel o utput Y an d resp. Z observed by Bob and resp. Eve. The co nditional distribution P Y | X ( y | x ) := Pr { Y = y | X = x } equals W b ( y | x ) for all ( x, y ) ∈ X × Y , and similarly for P Z | X . For the case of interest, all sets X , Y and Z are finite an d the co rrelation between Y and Z given X need not be specified. T o transmit informatio n throug h this ch annel, we will co n- sider the (data) transmission m odel illustrated in Fig . 3 with block leng th n . Following [ 2 ], we con sider n uses of th e channel w ith stochastic en coding , and d eterministic dec oders at the receivers. As p ointed o ut in [ 2 ], stocha stic en coding , i.e. random ization in the en coder durin g transmission , in creases secrecy by adding noise as a ph ysical barrier to eavesdropping while determ inistic decodin g do es not lose o ptimality for th e case of interest. As s hown in F ig. 3 , Ali ce chooses a public/common message m out o f a set of M possible messages to con vey to both Bob and Eve, and a private/secr et/co nfiden tial message l ∈ L only to Eve. ( l ∈ L is a short-han d notation for l ∈ { 1 , . . . , L } .) Since the m essage m for Eve is a degrad ed version of the message ( m, l ) to Bob, this is ide ntical to the asymmetric br oad casting of degr a ded messag e sets [ 3 ] except for the additional secrecy co ncern. In the transmission phase , Alice first passes the messag e throug h a stochastic encoder denoted b y the c onditiona l p rob- ability distribution f ∈ P ( X n ) M × L . W e write f ( m, l ) as the output codeword, which is denoted by the dummy rand om n - sequence X := { X ( i ) } n i =1 in Fig. 3 . The encoder can be vie wed as an artificial channe l, thro ugh wh ich th e output codeword X of the message ( m, l ) must satisfy Pr { X = x } = f ( x | m, l ) . It effectively add s addition al noise to m ake it h ard for Eve to learn the secr et. This artificial noise a lso affects Bob since he does no know it a p riori. Alice then transmits the ran dom codeword X thro ugh n u ses of the wiretap channel. The n -th e xtension of the wiretap chan- nel is character ized by the n -th direct power ( W n b , W n e ) , where W n b ( y | x ) = Q n i =1 W b ( y ( i ) | x ( i ) ) and similarly for W n e . Bob uses his channe l output Y to decode both the public and priv ate messages with a determin istic decoder φ b : Y n 7→ M × L . Φ b : M × L 7→ 2 Y n denotes th e decision r e gio n so th at ( 1 ) φ b ( y ) = ( m, l ) ⇐ ⇒ y ∈ Φ b ( m, l ) Similarly , E ve uses her channel output Z to decode the p ublic message with dec oder φ e : Z n 7→ M and decision r egion Φ e : M 7→ 2 Z n . She, h owe ver, also gen erates an unord ered set o f λ ≤ L distinct guesses of the secret using a list dec oder ψ : Z n 7→ {A ⊂ L : |A| = λ } , which is a co rr espon dence . The decision region Ψ : L 7→ 2 Z n satisfies ( 2 ) l ∈ ψ ( z ) ⇐ ⇒ z ∈ Ψ( l ) The triple ( f , φ b , φ e ) will be called an ( n -block ) wir etap channel code , while the list decod er ψ will be called the list decodin g attack (with d eterministic list size). The quad ruple ( f , φ b , φ e , ψ ) will be called an ( n - block) transmission (model) for the wiretap chann el. B. Achievable rate and exponen t triples The perfo rmance o f a wir etap channe l c ode with respect to a list deco ding attack is evaluated based on the fo llowing fault ev ents. Definition III.1 ( Fault ev ents) . Le t E b ( m, l ) , E e ( m, l ) an d S e ( m, l ) be the fault events tha t Bob dec odes ( m, l ) wr ong, Eve decodes m wrong, and Eve successfully guesses l respec- ti vely when ( m, l ) is th e public and p riv ate message p air . i. e. E b ( m, l ) := { φ b ( W n b ( f ( m, l ))) 6 = ( m, l ) } E e ( m, l ) := { φ e ( W n e ( f ( m, l ))) 6 = m } S e ( m, l ) := { l ∈ ψ ( W n e ( f ( m, l ))) } The correspo nding (average) fault pr ob abilities ( over the mes- sage set M × L ), e b , e e and s e can b e co mputed as follows. ( 3a ) ( 3b ) ( 3c ) e b = Avg m ∈ M ,l ∈ L X x ∈X n W n b (Φ c b ( m, l ) | x ) f ( x | m, l ) e e = Avg m ∈ M ,l ∈ L X x ∈X n W n e (Φ c e ( m ) | x ) f ( x | m, l ) s e = Avg m ∈ M ,l ∈ L X x ∈X n W n e (Ψ( l ) | x ) f ( x | m, l ) where Φ c b ( m, l ) and Φ c e ( m ) are the co mplemen ts of the Φ b ( m, l ) and Φ e ( m ) respec ti vely; and Avg m ∈ M ,l ∈ L denotes 1 M L P m ∈ M ,l ∈ L . When th ere is ambiguity , we will write e b ( f , φ b , W b ) etc. to explicitly state its depe ndencies. W e study th e asym ptotic proper ties when the sizes M and L of the message sets and λ of E ve’ s guessing list grow exponentially while the fault pr obabilities decay expo nentially in n . The exponen tial rates are defined as follows. Definition III.2. Consider a sequence o f n -block transmis- sions ( f ( n ) , φ ( n ) b , φ ( n ) e , ψ ( n ) ) ( n ∈ Z + ) over the wir etap chan- nel ( W b , W e ) , the public message rate R M , private message 4 rate R L and the gu essing rate R λ are defined as, ( 4a ) ( 4b ) ( 4c ) R M := lim inf n →∞ 1 n log M ( n ) R L := lim inf n →∞ 1 n log L ( n ) R λ := lim sup n →∞ 1 n log λ ( n ) The exponents of the fault probabilities ( 3 ) are defined as, ( 5a ) ( 5b ) ( 5c ) E b := lim inf n →∞ − 1 n log e ( n ) b E e := lim inf n →∞ − 1 n log e ( n ) e S e := lim inf n →∞ − 1 n log s ( n ) e where e ( n ) b and alike deno tes e b ev aluated with respect to the n -block transmission. For simplicity , the superscript ( n ) will be omitted hereafte r if ther e is no ambiguity . In the code d esign pha se pr ior to the tr ansmission phase, Alice chooses ( f , φ b , φ e ) withou t kn owledge of ψ and then Eve ch ooses ψ knowing A lice’ s choice. In par ticular, Eve chooses ψ to minimize S e so that her success pro bability s ( n ) e decays to zero as slo wly as p ossible, while Alice choo ses ( f , φ b , φ e ) to make E b , E e and S e large so th at th e error probab ilities e ( n ) b and e ( n ) e decay to zero fast for reliability , and the pro bability s ( n ) e of successful attack by Eve decays to zero fast for secrecy . Th e tradeoff between secrecy a nd r elia bility for Alice can be expressed in ter ms of the set of ach iev able rate and exponent triples defined as follows. Definition III.3 ( Achiev ab le rate an d expon ent trip les) . The rate trip le ( R 1 , R 2 , R 3 ) ∈ R 3 + , where R + := { a ∈ R : a ≥ 0 } , is achievable if there exists a sequ ence of w iretap cha nnel codes ( f , φ b , φ e ) with rates, R M ≥ R 1 and R L ≥ R 2 such that fo r a ny sequen ce o f list deco ding attac k ψ w ith guessing rate R λ ≤ R 3 , the prob abilities e b , e e and s e conv erge to zer o as n → ∞ . The exponent triple ( E 1 , E 2 , E 3 ) ∈ R 3 + is achievable with respect to the rate trip le if in addition that, E b ≥ E 1 and E e ≥ E 2 and S e ≥ E 3 If the achiev able exponents are strictly po siti ve, the rate triple is said to be str ong ly achievable . In the sequ el, we will obtain an in ner bou nd to the set of achievable exponen t triples in the form of parameterized single-letter lo we r bo unds, o ne f or each exponen t. 3 From this, 3 In response to the question of using ave rage instead of maximum error probabil itie s (ov er the message set), we would like to point out that the partic ular inner bound to be deri ved also holds w hen e b and e e are defined as the corresponding maximum error probabilit ies and s e as the avera ge success probabil ity . It follo ws from the usual argu ment of successi vely expurga ting worst half of the codew ords as in [ 6 ], which turns out to preserve the desired ove rlap pr operty of the code an d hence the bound for the success exponent . (see Sec tion V ) If one defined s e as the maximum probabi lity ho weve r , the problem becomes degenerat e since there is an obvious strategy for Eve to achie ve s e = 1 . an inner bound to the set of strongly achiev able rate triples will be obtain ed, the clo sure of which co incides with the closure o f the achiev ab le region in Theo rem 1 of [ 2 ] whe n the guessing rate is treated as equ iv ocation rate. I V . C O D I N G S C H E M E The cod ing scheme ( i.e. the sp ecification of the sequence of wiretap channel codes ( f , φ b , φ e ) , see Fig. 3 ) considered here is a merge of the schemes in [ 2 ] an d [ 6 ] using th e method of types developed by Csisz ´ ar[ 3 ]. W e will descr ibe each key compon ent o f the co de in su ccession an d explain how each of them simp lifies the analysis o f th e fault events (see De finition III.1 ) . A. Constant comp osition cod e As a first step, ou tput o f the stochastic encoder is restricted to constant composition code [ 3 ] defin ed as fo llows. Let N ( x | x ) deno te the n umber of occur rences of symbol x ∈ X in the n -sequence x ∈ X n . The type or empirical distrib ution P x of x is de fined as the probab ility mass function , ( 6 ) P x ( x ) := N ( x | x ) n ∀ x ∈ X Let P n ( X ) := { P x : x ∈ X n } deno te th e set of all p ossible types of an n -seque nce in X n . The type class T ( n ) Q := { x : P x = Q } or T Q for short denotes the set of all n -sequen ces x ha v ing type Q ∈ P n ( X ) . An n -block co nstant composition code θ o n X is an or de r ed tup le of cod ewor ds all fr o m the same typ e class on X . i.e. ∃ Q ∈ P n ( X ) , θ ⊂ T Q . Suppose θ is th e constant composition cod e o f typ e Q fo r the stoch astic enc oder f . Then, f ( x | m, l ) = 0 for a ll x / ∈ θ . From ( 3a ), ( 7 ) e b = Avg m ∈ M ,l ∈ L X c ∈ θ W n b (Φ c b ( m, l ) | c ) f ( c | m, l ) and similarly for other pro babilities in ( 3 ). T o further simplif y the expressions, define the canonical c onditiona l type P y | x of y given x as, ( 8 ) P y | x ( y | x ) := 1 / |Y | , N ( x | x ) = 0 N ( x, y | x , y ) N ( x | x ) , otherwise for all x ∈ X , y ∈ Y , wh ere N ( x , y | x , y ) is the num ber of oc- currenc es of the p air ( x, y ) in the n -sequence { ( x ( i ) , y ( i ) ) } n i =1 of pairs. The canonical conditional type of y g iv en x exists and is unique by definition. 4 Howe ver, with a cano nical cond itional type V giv en x specified, ther e can be m ore than o ne y satisfying it. 5 If V : X 7→ Y is the con ditional typ e of y giv en x , y is said to lie in T V ( x ) , ref erred to as the V -shell of x or th e co nditiona l typ e class of V g iv en x . In othe r 4 This is a minor modification of the condition al type defined in Defini- tion 1.2.4 of [ 3 ], according to which y may have a continuum of conditiona l types V giv en x since V ( y | x ) can be arbi trary when N ( x | x ) = 0 . 5 For e xample, the binary seq uences 1100 and 0011 have the sa me cano nical conditi onal type giv en 1111 , i.e. . 5 . 5 . Similarly , 1111 has the same canonic al conditional type whether it is gi ven 1100 or 0011 , i.e. 0 1 . 5 words, T V ( x ) is the set of all y ∈ Y n with condition al typ e V gi ven x . Writing W n b ( y | c ) as the p roduc t Q x,y W b ( y | x ) N ( x ,y | c , y ) , Lemma 1.2. 6 of [ 3 ] gives , f or all y ∈ T V ( c ) , ( 9a ) ( 9b ) W n b ( y | c ) = ex p {− n [ D ( V k W b | Q ) + H ( V | Q )] } = W n b ( T V ( c ) | c ) | T V ( c ) | ∵ ( 9a ) is unifor m where the cond itional information d iver gence D ( V k W b | Q ) and conditio nal entr op y H ( V | Q ) ar e defined as, ( 10 ) ( 11 ) D ( V k W | Q ) := X ( x,y ) ∈X ×Y Q ( x ) V ( y | x ) ln V ( y | x ) W ( y | x ) H ( V | Q ) := X ( x,y ) ∈X ×Y Q ( x ) V ( y | x ) ln 1 V ( y | x ) The key imp lication is that W n b ( y | c ) dep ends o n y only throug h the condition al ty pe P y | c and cha nnel output W n b ( c ) is uniform ly distributed within every V -shell T V ( c ) . Let V n ( Q, Y ) := { P y | x : x ∈ T Q , y ∈ Y n } ( V n ( Q ) or V n for sho rt) b e the set of all possible cano nical con ditional types of y given c . T his set d epends on c only thr ough th e typ e Q of c . 6 { T V ( c ) : V ∈ V n ( Q ) } is a p artitioning of Y n for e very c ∈ θ because every y h as a u nique canon ical conditio nal type giv en c . W e can the refore partitio n the probab ilities by V n ( Q ) as follows. From ( 7 ), e b = Avg m,l X c ∈ θ X V ∈ V n W n b (Φ c b ( m, l ) ∩ T V ( c ) | c ) f ( c | m, l ) = X V ∈ V n X c ∈ θ W n b ( T V ( c ) | c ) Avg m,l | Φ c b ( m, l ) ∩ T V ( c ) | | T V ( c ) | f ( c | m, l ) where the last eq uality is du e to the piecewise unifor m distribution of th e channel output W n b ( c ) implied by ( 9 ). By Lemma 1.2. 6 of [ 3 ], 7 ( 12 ) W n b ( T V ( c ) | c ) ≤ exp {− nD ( V k W b | Q ) } Thus, e b can be upp er bo unded as, ( 13 ) e b ≤ X V ∈ V n ( Q ) exp {− nD ( V k W b | Q ) } × × X c ∈ θ Avg m ∈ M ,l ∈ L | Φ c b ( m, l ) ∩ T V ( c ) | | T V ( c ) | f ( c | m, l ) B. T ransmission of ju nk data and prefix DMC In the previous section, the use of constan t com position code simp lifies the pro bability ( 3a ) to ( 1 3 ) and similar ly for other pr obabilities in ( 3 ). In this section, we shall specif y 6 For exa mple, if y = 011 is in the V -shell of c = 011 , then permutation y ′ = 110 of y is in the V -shell of the same permut ation c ′ = 110 of c . In general , if V is a canonica l type of s ome sequence y ∈ Y n gi ven c ∈ θ then the V -shel l of another co de word c ′ ∈ θ must cont ain a sequence y ′ ∈ Y n , namely the sequence obtained from y by the same permutation of c ∈ θ to c ′ ∈ θ . Thus, the set of all possible canonical conditio nal types are the same if the condition ing sequenc es ha ve the same type. 7 The ke y step in the deri vat ion is that V n ( T V ( c ) | c ) ≤ 1 implies | T V ( c ) | ≤ exp { nH ( V | Q ) } by ( 9 ) with W b replac ed by V . the structu re of the sto chastic enco der f and its unifo rm random ization over junk data as fo llows. Consider indexing the cod ew o rds in θ as c j lm by j ∈ J , l ∈ L and m ∈ M . i.e. ( 14 ) θ := { c j lm } j ∈ J,l ∈ L,m ∈ M Set f ( m, l ) = c J lm where the jun k data J is a random variable Alice choo ses unifo rmly ra ndomly fr om { 1 , . . . , J } . The condition al pro bability f is, ( 15 ) f ( c | m, l ) = ( 1 J , if c ∈ { c j lm : j ∈ J } 0 , otherwise This appr oach of providing secrecy , illustrated in E xample A.2 in the Appe ndix, will be called transmission of ( uniformly random) junk d ata be cause J is not m eant to b e a message although it is en coded like one. 8 Substituting this into the upper bound of e b in ( 13 ) an d similarly for the other fault probab ilities gives the fo llowing expressions. Lemma IV .1 (Co nstant com position code, tran smission of junk d ata) . U sing n -blo ck constant composition code θ in ( 14 ) of type Q ∈ P ( X ) and the transmission of j unk data appr o ach ( 15 ) , the p r obabilities in ( 3 ) can b e uppe r bou nded a s fo llows, ( 16a ) ( 16b ) ( 16c ) e b ≤ X V ∈ V n ( Q ) exp {− nD ( V k W b | Q ) } Avg j,l,m | Φ c b ( m,l ) ∩ T V ( c jlm ) | | T V ( c jlm ) | e e ≤ X V ∈ V n ( Q ) exp {− nD ( V k W e | Q ) } Avg j,l,m | Φ c e ( m ) ∩ T V ( c jlm ) | | T V ( c jlm ) | s e ≤ X V ∈ V n ( Q ) exp {− nD ( V k W e | Q ) } Avg j,l,m | Ψ( l ) ∩ T V ( c jlm ) | | T V ( c jlm ) | wher e Avg j,l,m is over j ∈ J , l ∈ L and m ∈ M . Note that the random ization in the encode r is equ i valent to the av e raging over the message augm ented with jun k data. Another appr oach of ra ndomizatio n introd uced in [ 2 ] is the prefix discr e te memoryless chan nel (prefix DMC) , which is character ized by the co nditional probab ility distribution ˜ V ∈ P ( X ) ˜ X from some finite set ˜ X . Th e stoc hastic enco der first maps ( m, l ) into an n -sequ ence in ˜ X n , which is then fed throug h the extended prefix DMC ˜ V n before being transmitted throug h th e chan nel. T o combin e this with the transmission of junk d ata ap proach , let ˜ f be the origin al stochastic encoder defined in ( 15 ) excep t that X is rep laced by ˜ X , and θ is a constant co mposition code with ty pe Q on ˜ X . Then, the new encoder is, f ( x | m, l ) := X c ∈ θ ˜ V n ( x | c ) ˜ f ( c | m, l ) ∀ m ∈ M , l ∈ L, x ∈ X n This is illustrated in Fig. 4(a) . The p refix DMC can b e viewed as part o f the wiretap channel instead of th e encod er as in Fig. 4(b) bec ause the wiretap chan nel ( W b , W e ) prefixed with any discrete mem ory- less c hannel ˜ V is just ano ther wir etap chan nel ( ˜ V W b , ˜ V W e ) , 8 It turns out that J can al so be reliably decode d by Bob with lo wer le vel of secrecy . Thus, one may choose J to be meaningful pri vate data to achie ve a ne w notion of unequal securit y pr otection . Howe ver , it suffices for our case of intere st to treat J as meaningless. 6 P S f r a g r e p l a c e m e n t s θ ˜ V n W n b W n e codebo ok prefix DM C trans. of junk stochastic enco der f wiretap channe l ( m, l ) J ∈ J ˜ X ∈ ˜ X n X Y Z (a) original model P S f r a g r e p l a c e m e n t s θ ( ˜ VW b ) n ( ˜ VW e ) n augmen ted message prefixed wiretap ch annel ( m, l , J ) ˜ X X Y Z (b) equi v alent m odel Fig. 4. Stochast ic encoding with transmission of junk data and prefix DMC where the produ ct ˜ V W b is the matrix multiplication . Thus, any p erforma nce metric, say e ( W b , W e ) , that on e o btains without pr efix discrete m emoryless chann el can be con verted to the per forman ce metric with prefix ing discrete memoryle ss channel as e ( ˜ V W b , ˜ V W e ) . Because o f this simplicity in extending any pe rforman ce metrics with p refix DM C, we will leave this pr efix ing pr o - cedure to the very end an d use the enco der defin ed in ( 15 ) for th e main a nalysis . For a simple com parison between th e prefix DMC a nd transmission o f junk data a pproach , r eaders can refer to Ex ample A.2 and A.3 in the Appe ndix. C. Ran dom code con struction an d MMI decoding As a summ ary , encod er f en codes the pu blic and private messages m and resp ectiv e ly l , and the junk data J into a codeword c J lm in the constant composition code θ of type Q . The code word is then transmitted thro ugh th e wiretap channel ( W b , W e ) , to which a pr efix a DMC { ˜ V } will be added in the end. Th e fault pro babilities simplify to ( 16 ), with ( W b , W e ) replaced by ( ˜ V W b , ˜ V W e ) for the pre fix DMC. It remain s to specify how the code book θ and decod ers ( φ b , φ e ) should be constructed . Csisz ´ ar a nd K ¨ orner[ 2 ] consider maximal cod e co nstruction with typical set decoding for the wiretap channel. Th is can not be used here s ince typical s et decoding fails to gi ve e x ponen tial decay rate for the error probabilities. W e will adop t the r a ndom code construction scheme with ma ximum mu tual information (MMI) decodin g in [ 6 ] instead. As a prelimin ary fo r th e rando m code constru ction, som e finite set U is cho sen. The wiretap chan nel is trivially ex- tended with an additio nal inpu t symbo l from U to ( W b ∈ P ( Y ) U ×X , W e ∈ P ( Z ) U ×X ) , where ( 17 ) W b ( y | u, x ) := W b ( y | x ) W e ( y | u, x ) := W e ( y | x ) for all ( u , x ) ∈ U × X . In the form o f the stoc hastic tran sition function , W b ( u, x ) := W b ( x ) and W e ( u, x ) := W e ( x ) , wh ich means that the extended chann el simply ign ores the ad ditional input symbol. Thus, this tri vial extension is purely conceptual and does not chang e the o riginal p roblem. As the first step in the rand om code constructio n, a typ e Q 0 ∈ P n ( U ) on U is chosen for the constraint length n . Then, each o f the set Θ 0 := { U m } m ∈ M of n -sequences is unifor mly randomly and indepen dently (u.i.) cho sen fro m the type class T Q 0 . i.e . P U m ( u ) = ( 1 | T Q 0 | , u ∈ T Q 0 0 , o therwise ∀ m ∈ M Next, a cond itional type Q 1 ( ∈ V n ( Q 0 , X )) is chosen. For each U m generated , consid er its Q 1 -shell T Q 1 ( U m ) . Each of the set Θ 1 ( m ) := { X j lm } j ∈ J,l ∈ L of n -sequ ences is chosen u.i. from T Q 1 ( U m ) . i.e. P X jlm | U m ( x | u ) = ( 1 | T Q 1 ( u ) | , x ∈ T Q 1 ( u ) 0 , otherwise for all ( j, l , m ) ∈ J × L × M , u ∈ T Q 0 . Finally , U m := { U ( i ) m } n i =1 and X j lm := { X ( i ) j lm } n i =1 are combined into one codeword C j lm := U m ◦ X j lm , wh ere ◦ denotes th e element-wise con catenation. i.e. ( 18 ) U m ◦ X j lm = { ( U ( i ) m , X ( i ) j lm ) } n i =1 The i -th term C ( i ) j lm := ( U ( i ) m , X ( i ) j lm ) is transmitted in the i - th u se of the (extended ) wir etap channel. The random code Θ is defined as the order ed structure { C j lm } j ∈ J,l ∈ L,m ∈ M . Its type is denoted as Q ∈ P n ( U , X ) where Q ( u, x ) := Q 0 ( u ) Q 1 ( x | u ) (( u, x ) ∈ U × X ) . W e write Q = Q 0 ◦ Q 1 wher e ◦ d enotes the dir ect p r oduct. Definition IV .1 ( Random cod e) . Th e rando m code Θ of type Q := Q 0 ◦ Q 1 ( Q 0 ∈ P n ( U ) , Q 1 ∈ V n ( Q 0 , X )) for th e extended wiretap chan nel ( 17 ) is d efined as follows, Θ := { C j lm } j lm C j lm := U m ◦ X j lm Θ 0 := { U m } m u.i. ← − − T Q 0 Θ 1 ( m ) := { X j lm } j lm u.i. ← − − T Q 1 ( U m ) In words, it is the set o f codewords C j lm indexed b y the messages j ∈ J , l ∈ L an d m ∈ M . Each c odeword consists of an n -sequence U m that belon g to the ran dom codeboo k Θ 0 , and an n -seq uence X j lm that belon gs to the r andom codebo ok Θ 1 ( m ) . T he codewords from Θ 0 are selected u .i. from th e type class T Q 0 and the codewords from Θ 1 ( m ) are selected u.i. from the Q 1 -shell T Q 1 ( U m ) of U m . This ap proach of r andom code constru ction is well-known in the asymmetric broad casting channel setting. Θ 0 is used to partition X n into cells/clou ds { T Q 1 ( U m ) } m that are intended to be well distinguisha ble throug h th e ch annels of both Bob and Eve, and Θ 1 ( m ) are the set of codewords selected fro m the co ntaining cell that are intended to b e well distinguishable by Bob but not necessarily so by Eve. Th e ad dition of in put symbol from U g iv es an ad ditional degree of f reedom in optimizing the av erage p erform ance of the cod e. 7 It is important to n ote that, unlike th e r andomn ess in the stochastic encoding , the ran domn ess in the codeb ook is known to all pa rties (Alice, Bob and Eve). The random ization happen s in the code design phase be fore the public a nd p riv ate messages are gener ated for th e tran smission phase. W ith the structure of the codebo ok defined, we c an now complete the specification of the codin g scheme with the maximum mutual information (MMI) decoder for Bob and Eve. Consider a particular realizatio n θ of the rand om code Θ . Let I ( Q, V ) d enote th e mutual informa tion , ( 19 ) I ( Q, V ) := H ( QV ) − H ( V | Q ) see ( 11 ) Then, I ( c ∧ y ) , r eferred to as the emp irical mutual informa tion between x and y , ar e defined as, ( 20 ) I ( x ∧ y ) := I ( P x , P y | x ) see ( 19 ),( 6 ),( 8 ) Suppose Bob observes y ∈ Y n throug h his channe l. He searches for th e codew or d c ∈ θ that maximizes the em pirical mutual info rmation I ( c ∧ y ) . 9 If ther e is a uniqu e c j lm that achieves the ma ximum, he declar es m as the public message and l as the priv ate message . Mo re precisely , ( 21 ) φ b ( y ) = ( m, l ) ⇐ ⇒ ∃ !( m, l , j ) , I ( c j lm ∧ y ) = max c ∈ θ I ( c ∧ y ) Similarly , supp ose Eve rec eiv es z . She searches for th e un ique u m that a chieves the m aximum max u ∈ θ 0 I ( u ∧ z ) . 10 i.e. ( 22 ) φ e ( z ) = m ⇐ ⇒ ∃ ! m, I ( u m ∧ z ) = max u ∈ θ 0 I ( u ∧ z ) W e will no t n eed to assume any structur e f or ψ other than the fact it has to be a determ inistic list decoder with fixed list size λ . 11 The coding sch eme without p refix DMC can now be summarized as follows. Definition IV .2 ( Coding sche me) . The coding scheme without prefix DMC for a realization θ of the ra ndom code in Defini- tion IV .1 is d efined as follows. Encodin g: Alice gener ates the junk data J unifo rmly randomly from { 1 , . . . , J } and en codes the co mmon message m ∈ M and secret l ∈ L into ( u m , x J lm ) ∈ θ . She only transmits X J lm throug h th e chan nel. The encoding fu nction is therefor e, f ( x | m, l ) := ( 1 J x ∈ { x j lm } j ∈ J 0 , othe rwise , or equivalently f ( m, l ) := x J lm ∈ θ 1 ( m ) , ∀ m ∈ M , l ∈ L Decoding : If Bob r eceiv es y , he finds a codeword c ∈ θ th at maximizes the empirical m utual information I ( c ∧ y ) and use 9 Note that the optimal decoding rule is the maximum likeliho od decodin g instead . MMI decoding is adopte d here for simplicity . 10 One may think that Eve can search for the unique c j lm that achie ves the maximum max c ∈ θ I ( c ∧ z ) , and declare m as the public message. Because of the suboptimality of the MMI decoding and the random code construction, this choice turns out to be unfa vorable . 11 It is clear , howe ver , that the opt imal ψ is an extension of the maximum lik elihood decoding rule with λ estimates instead of one. its location in θ to decode ( m, l ) . T he deco ding f unction can be defined as, φ b ( y ) = ( m, l ) ⇐ ⇒ ∃ !( m, l , j ) , I ( c j lm ∧ y ) = max c ∈ θ I ( c ∧ y ) Similarly , Eve loc ates the mutual infor mation maxim izing codeword in θ 0 to decod e m as fo llows, φ e ( z ) = m ⇐ ⇒ ∃ ! m, I ( u m ∧ z ) = max u ∈ θ 0 I ( u ∧ z ) The enc oder an d deco ders are function s o f th e co deboo k θ , i.e. f [ θ ]( m, l | c ) , φ b [ θ ]( y ) and Φ b [ θ ]( z ; θ ) etc.. Howe ver, fo r notational simplicity , the depend ence on θ will be omitted . Using the r andom c oding scheme, we can furthe r boun d the fault prob abilities ( 16 ) with th e expected fault p robab ilities over the rand om code ensem ble a s follows. From ( 16a ), the expectation of e b over the random code Θ is, E ( e b (Θ)) ≤ X V ∈ V n ( Q ) exp {− nD ( V k W b | Q ) } × × β ( V , Θ , Φ c b ):= z }| { E Avg j ∈ J,l ∈ L,m ∈ M | Φ c b ( m, l ) ∩ T V ( C j lm ) | | T V ( C j lm ) | ! ≤ | V n ( Q ) | max V ∈V n ( Q ) exp {− nD ( V k W b | Q ) } β (Θ , Φ c b ) ≤ ( n + 1) |X | |Y | s ( W b , Θ , Φ c b ):= z }| { max V ∈ V n ( Q ) exp {− nD ( V k W b | Q ) } β (Θ , Φ c b ) where the last inequality is du e to the T ype Counting Lemma | V n ( Q ) | ≤ ( n + 1) |X | |Y | . 12 The expectation of e e and s e can be upper bound ed similarly . By the union b ound, Pr e b (Θ) > 3 E ( e b (Θ)) or e e (Θ) > 3 E ( e e (Θ)) or s e (Θ) > 3 E ( s e (Θ)) ≤ Pr { e b (Θ) > 3 E ( e b (Θ)) } + Pr { e e (Θ) > 3 E ( e e (Θ)) } + Pr { s e (Θ) > 3 E ( s e (Θ)) } which is < 1 due to th e Markov inequality Pr( A > α E ( A )) < 1 /α for non-n egati ve random variable A and α > 0 . Thus, the comp lement of th e event has positive prob ability , which implies existence of a realization θ of Θ such that the fault probab ilities can be bo unded simultan eously as follows, ( 23a ) ( 23b ) ( 23c ) e b ( θ ) ≤ 3( n + 1) |X | |Y | s ( W b , Θ , Φ c b ) e e ( θ ) ≤ 3( n + 1) |X | |Y | s ( W e , Θ , Φ c e ) s e ( θ ) ≤ 3( n + 1) |X | |Y | s ( W e , Θ , Ψ ) where s is defined as fo llows, ( 24a ) ( 24b ) β ( V , Θ , Φ) := E Avg j ∈ J,l ∈ L,m ∈ M | Φ( m, l ) ∩ T V ( C j lm ) | | T V ( C j lm ) | ! s ( W , Θ , Φ) := max V ∈ V n ( Q ) exp {− nD ( V k W | Q ) } β ( V , Θ , Φ) and Φ e ( m, l ) := Φ e ( m ) , Ψ ( m, l ) := Ψ( l ) ar e the trivial extensions for all ( m, l ) ∈ M × L . T o com pute the d esired exponents, we con sider a seq uence of random codes defined as follows. 12 This follows from the definition ( 8 ) that there are at most n + 1 possible v alues for each entry of a canonical conditio nal type. (see T ype Counting Lemma 2.2 of [ 3 ].) 8 Definition IV .3 (Seq uence of rand om c odes) . { Θ ( n ) } or simply Θ d enotes a sequen ce of rand om co des Θ ( n ) (see Definition IV .1 ) of typ e Q ( n ) = Q ( n ) 0 ◦ Q ( n ) 1 ( Q ( n ) 0 ∈ P n ( U ) , Q ( n ) 1 ∈ V n ( Q ( n ) 0 , X )) that c on verges to distribution Q = Q 0 ◦ Q 1 ( Q 0 ∈ P ( U ) , Q 1 ∈ P ( X ) U ) in variation distance. i.e. δ v ar ( Q ( n ) , Q ) → 0 , where ( 25 ) δ v ar ( P, Q ) := max A⊂X P ( A ) − Q ( A ) Furthermo re, J ( n ) grows exponen tially at the junk data rate ( 26 ) lim n →∞ 1 n log J ( n ) = R J ≥ 0 If on e can find γ b ( V , Q ) con tinuous in Q ◦ V in variation distance such that, lim inf n →∞ − 1 n log β ( V ( n ) , Θ ( n ) , (Φ ( n ) b ) c ) ≥ γ b ( V , Q ) for any Q ( n ) ◦ V ( n ) conv erging to Q ◦ V in variation distance, then Bob’ s erro r exponen t ( 5a ) can be lower b ounded as, E b ( θ ) = lim inf n →∞ − 1 n log s ( V ( n ) , Θ ( n ) , (Φ ( n ) b ) c ) ≥ min V ∈ P ( Y ) U ×X D ( V k W b | Q ) + γ b ( V , Q ) and similarly for other expo nents E e and S e in ( 5 ). Lemma IV .2. If γ b ( V , Q ) , γ e ( V , Q ) a nd γ ( V , Q ) ar e continu- ous in the join t distribution Q ◦ V (with respect to the variation distance ( 25 ) ) and lo wer bou nd the exponent, lim inf n →∞ − 1 n log β ( V , Θ , Φ) for random code Θ and the cases Φ equa l to Φ c b , Φ c e and Ψ r espectively , th en ther e exists a r e alization θ of Θ such th at ( 27a ) ( 27b ) ( 27c ) E b ( θ ) ≥ min V ∈ P ( Y ) U ×X D ( V k W b | Q ) + γ b ( V , Q ) E e ( θ ) ≥ min V ∈ P ( Z ) U ×X D ( V k W e | Q ) + γ e ( V , Q ) S e ( θ ) ≥ min V ∈ P ( Z ) U ×X D ( V k W e | Q ) + γ ( V , Q ) In the sequel, we will compu te γ b , γ e and γ to obtain the desired lower bou nds of the expon ents. V . S U C C E S S E X P O N E N T From Lem ma IV .2 , to obtain a lower b ound of the achiev- able 13 success exponent S e ( 5c ), it su ffices to comp ute a lower bound γ ( V ) on the expo nent of th e expected a verag e fraction β ( V , Θ , Ψ) fo r any Ψ satisfying the guessing ra te ( 4c ). Consider first some r ealization θ o f th e ran dom code Θ in Definition IV .1 . β ( V , θ , Ψ) = 1 J | T V ( c 111 ) | Avg l,m X j ∈ J | Ψ( l ) ∩ T V ( c j lm ) | by ( 24a ) since | T V ( c j lm ) | d epends on c j lm only through its type Q (an d n ). T he fractio n can be made small if P j | Ψ( l ) ∩ T V ( c j lm ) | on the R.H.S. is made small fo r each l and m . Imag ine Ψ ( l ) 13 Achie vabl e here doe s not refer to achie v able by Eve, but achi e vable by Alice as defined in Definition III.3 . P S f r a g r e p l a c e m e n t s T V ( c 111 ) T V ( c 111 ) T V ( c 211 ) T V ( c 211 ) T V ( c 311 ) T V ( c 311 ) Ψ(1) Ψ(1) Not well spread W ell spread Fig. 5. Effe cti veness of s tochast ic en coding as a net that Eve uses to cover the shells { T V ( c j lm ) : j ∈ J } owned b y Alice as m uch as possible. Roug hly speakin g, since the n et cann ot b e too large d ue to th e list size constraint, Alice should spread o ut the shells as much as possible to minim ize her loss. W e will refer to this h euristically desired p roperty of θ tha t th e V -shells { T V ( c j lm ) : j ∈ J } spread out for ev e ry V , m and l as the overlap pr op erty . 14 This is illustrated in Fig. 5 , in which the co nfiguration on th e left h as P 3 j =1 | Ψ(1) ∩ T V ( c j 11 ) | three times larger than the one on the r ight. Intuitively , random code has the overlap pr operty on a verage since it uniform ly spac es ou t the co dew ords. This is made precise with the following Overlap Lemma . Lemma V .1 (Overlap) . Let X j ( j = 1 , . . . , J ) be a n n - sequence uniformly an d independ ently d rawn fr om T ( n ) Q ⊂ X n . F or a ll J ∈ Z + , δ > 0 , n ≥ n 0 ( δ, |X ||Z | ) , z ∈ Z n , Q ∈ P n ( X ) , V ∈ V n ( Q, Z ) such that ⌊ ex p { nI ( Q, V ) }⌋ ≥ J , we have, Pr X j ∈ J 1 { z ∈ T V ( X j ) } ≥ exp( nδ ) ≤ exp( − exp( nδ )) wher e 1 is the indicato r function and n 0 is some inte ger -v alued function that depend s only on δ and |X ||Z | . In words, the lemma states that the ch ance o f ha ving exponentially ( exp( nδ ) ) many shells (from { T V ( X j ) : j ∈ J } ) overlapping at a spot ( z ) is do ubly expon entially d ecaying ( exp( − e x p( nδ )) ), provided th at the shells are n ot enou gh to fill th e entire space ( T QV ⊂ Z n ) they can p ossibly reside. (i.e. J ≤ ⌊ exp { nI ( Q, V ) }⌋ ) For the case o f interest, we will prove the following mo re general form of the lemma with condition ing. Lemma V . 2 (Overlap (with cond itioning)) . Let Q := Q 0 ◦ Q 1 ( Q 0 ∈ P n ( U ) , Q 1 ∈ V n ( Q 0 , X )) be a joint type, U be a random v ariable distrib uted over T Q 0 , and X j ( j = 1 , . . . , J ) be an n -sequ ence unifo rmly a nd independ ently drawn fr om T Q 1 ( U ) ⊂ X n . F or a ll J ∈ Z + , δ > 0 , n ≥ n 0 ( δ, |U ||X | ) , 14 Though not e xplicitly stated, this not ion of o verlap prope rty is also e vident in [ 2 ] for the typica l case when V is close to W e . (See Lemma 2 of [ 2 ]) For the purpose of computing the expo nent, we extend it to the atypi cal case of V and relax the extent that the shells have to spread out by allowi ng subexp onentia l amount of ove rlap. 9 z ∈ Z n , Q := Q 0 ◦ Q 1 , V ∈ V n ( Q, Z ) such that ⌊ exp { nI ( Q 1 , V | Q 0 ) }⌋ ≥ J , we ha ve, ( 28 ) Pr X j ∈ J 1 { z ∈ T V ( U ◦ X j ) } ≥ exp( nδ ) ≤ exp {− exp( nδ ) } wher e ◦ d enotes element-wise conca tenation ( 18 ) , and ( 29 ) I ( Q 1 , V | Q 0 ) := H ( Q 1 | Q 0 ) − H ( V | Q 0 ◦ Q 1 ) = H ( Q 1 | Q 0 ) − H ( V | Q ) denotes the conditio nal mutu al in formation . (cf. ( 19 ) ) Pr oof: For notation al simplicity , con sider the case when exp( nδ ) an d exp { nI ( Q 1 , V | Q 0 ) } are integers. 15 Consider some subset J of { 1 , . . . , J } with |J | = exp( nδ ) . Since the events z ∈ T V ( U ◦ X j ) ( j = 1 , . . . , J ) ar e cond itionally mutually indepen dent given U = u ∈ T Q 0 , Pr n z ∈ \ j ∈J T V ( U ◦ X j ) o = X u ∈ T Q 0 P U ( u ) Pr { z ∈ T V ( u ◦ X j ) } exp( nδ ) ≤ exp − n [ I ( Q 1 , V | Q 0 ) − δ 2 ] e xp( nδ ) for n ≥ n ′ 0 ( δ, |U ||X | ) , where the last inequ ality is by Lemma A.1 using the uniform distribution of X j and Lemma 1.2.5 of [ 3 ] on the card inality bo unds of condition al type class. Since exp { nI ( Q 1 , V | Q 0 ) } ≥ J , the nu mber of distinct choice s of J is, J exp( nδ ) ≤ exp( nI ( Q 1 , V | Q 0 )) exp( nδ ) ≤ exp { [log e + n ( I ( Q 1 , V | Q 0 ) − δ )] exp( nδ ) } where the last inequality is b y Lemma A.2 . By the union bound , L.H .S. of ( 28 ) is uppe r bound ed b y the produc t o f the last two expressions, i. e. J exp( nδ ) Pr z ∈ \ j ∈J T V ( U ◦ X j ) Substituting the p reviously derived b ounds for each term giv es the desired up per bo und exp( − exp( nδ )) when n ≥ n 0 ( δ, |U ||X | ) . Consider now a seq uence of r andom codes Θ ( n ) defined in Definition IV .3 . Th e desired bo und on the exponent o f β ( V , Θ , Ψ) can be com puted as fo llows using th e Overlap Lemma. Lemma V .3 (Su ccess exponen t) . Consider the rando m code sequence Θ defined in Defin ition IV .3 . F o r a ny seq uence o f list decodin g attack ψ satisfying the guessing rate R λ ( 4c ) , lim inf n →∞ − 1 n log β ( V , Θ , Ψ) ≥ | R L − R λ + | R J − I ( Q 1 , V | Q 0 ) | − | + 15 The case whe n exp( nδ ) and I ( Q 1 , V | Q 0 ) are not int ege rs can be deri ved by taking their cei lings or floors and groupi ng the frac tional increments into some dominati ng terms. wher e | a | + := max { 0 , a } a nd | a | − := min { 0 , a } . Pr oof: By the Overlap Lemma V .2 , f or any δ > 0 an d n ≥ n 0 ( δ ) , Pr X j ∈J k ( V ) 1 { z ∈ T V ( C j lm ) } ≥ exp( nδ ) Θ 0 = θ 0 ≤ exp {− exp( nδ ) } where Θ 0 is the co debook { U m } m ∈ M , θ 0 is an ar bitrary realization, and {J k ( V ) } k ∈ K V is a partitioning of { 1 , . . . , J } defined as, J k ( V ) := { ( k − 1) J V + 1 , . . . , min { k J V , J }} J V := ⌊ exp { nI ( Q 1 , V | Q 0 ) }⌋ K V := ⌈ J /J V ⌉ The expectation o f the sum of indicators on the left can then be bound ed as follows, E X j ∈J k ( V ) 1 { z ∈ T V ( C j lm ) } Θ 0 = θ 0 ≤ exp( nδ ) · 1 + J · exp {− exp( nδ ) } ≤ exp( n 2 δ ) where the last inequ ality is tru e for n ≥ n 0 ( δ, R J , |U ||X | ) b y ( 26 ). Since T V ( C j lm ) is conta ined by T Q 1 V ( U m ) , X z ∈ Ψ( l ) E X j ∈J k ( V ) 1 { z ∈ T V ( C j lm ) } Θ 0 = θ 0 = X z ∈ Ψ( l ) ∩ T Q 1 V ( u m ) E X j ∈J k ( V ) 1 { z ∈ T V ( C j lm ) } Θ 0 = θ 0 ≤ exp( n 2 δ ) | Ψ ( l ) ∩ T Q 1 V ( u m ) | By linearity of expectation , E X j ∈J k ( V ) | Ψ( l ) ∩ T V ( C j lm ) | Θ 0 = θ 0 ≤ exp( n 2 δ ) | Ψ( l ) ∩ T Q 1 V ( u m ) | Summing both sides over k ∈ K V , E X j ∈ J | Ψ( l ) ∩ T V ( C j lm ) | Θ 0 = θ 0 ≤ exp( n 2 δ ) K V | Ψ( l ) ∩ T Q 1 V ( u m ) | Summing both sides over l ∈ L and apply ing th e list size constraint on Ψ in Lem ma A.3 to the R.H.S., E X j ∈ J,l ∈ L | Ψ( l ) ∩ T V ( C j lm ) | Θ 0 = θ 0 ≤ exp( n 2 δ ) K V λ | T Q 1 V ( u m ) | A veraging both sides over m ∈ M , d i viding by th e constant J L | T V ( C j lm ) | and taking th e expectation over all possible realizations of θ 0 giv es, β ( V , Θ , Ψ) ≤ exp( n 2 δ ) K V λ J L | T Q 1 V ( u 1 ) | | T V ( c 111 ) | T o compu te the desire d exponent f rom the last inequ ality , denote the inequ ality in the expo nent . 6 as follows, ( 30 ) a n . 6 b n ⇐ ⇒ lim sup n →∞ 1 n log a n ≤ lim inf n →∞ 1 n log b n 10 Then, K V . 6 exp { n | R J − I ( Q 1 , V | Q 0 ) | + } , J . 6 exp { nR J } by ( 26 ), L . > exp { nR L } by ( 4b ), λ . 6 exp { nR λ } by ( 4c ), an d | T Q 1 V ( u 1 ) | / | T V ( c 111 ) | is . 6 exp { nI ( Q 1 , V | Q 0 ) } . Combining these, β ( V , Θ , Ψ) is . 6 the following expre ssion, exp { n [ R L − R λ + [ R J − I ( Q, V | Q 0 )] − | R J − I ( Q, V | Q 0 ) | + ] } T o obtain the desired bou nd, simp lify th is with the id entity | a | − ≡ a − | a | + , and the fact that β ( V , Θ , Ψ) ≤ 1 . V I . E R RO R E X P O N E N T S The desired e rror exponents can be obtained directly from the achiev ability result in [ 6 ] by g roupin g ( j, l ) ∈ J × L as one private message for Bob. This is be cause the error exponent that Bob deco des th e private message wrong lower bound s the expo nent that Bob dec odes th e secret wron g. 16 For completen ess, we provide a similar der iv ation in this section. Readers familiar with [ 6 ] and may skip to the next section. In essence of Lemma IV .2 , the erro r expo nents for Bob and Eve can be obtain ed by lower boun ding the expon ents of th e fractions β ( V , Θ , Φ c b ) and r espectiv ely β ( V , Θ , Φ c e ) . Th us, the objective is to prove the following lemma. Lemma VI.1 ( Error exponents) . Consider the sequence of random code Θ in Definition IV .3 , and the MMI deco der (decision re g ion map ) φ b ( Φ b ) ( 21 ) and φ e ( Φ e ) ( 22 ) for Bo b and r e spectively E ve. Then , lim inf n →∞ − 1 n log β ( V , Θ , Φ c b )) ≤ I ( Q 1 , V | Q 0 ) − R J − R L + | I ( Q 0 , Q 1 V ) − R M | − + lim inf n →∞ − 1 n log β ( V , Θ , Φ c e )) ≤ | I ( Q 0 , Q 1 V ) − R M | + A. Expon ent for Bo b In essence of Lemma IV .2 , the erro r expone nt for Bob can be obtained by lower b ound ing the exponent of the fraction, β ( V , Θ , Φ c b ) = E Avg j ∈ J,l ∈ L,m ∈ M | Φ c b ( m, l ) ∩ T V ( C j lm ) | | T V ( C j lm ) | ! where Θ is th e sequence of rand om cod es in Definition IV .3 and Φ b is the decision region of the MMI decod er φ b in ( 21 ). Φ c b ( m, l ) ∩ T V ( C j lm ) is the set of b ad ob servations in the V - shell o f C j lm that le ad to erro r if C j lm is transmitted. W ith the MMI decoder ( 21 ), this co rrespon ds to the set of y ∈ T V ( C j lm ) th at has I ( C j lm ∧ y ) no larger than I ( C j ′ l ′ m ′ ∧ y ) for som e misleading codeword C j ′ l ′ m ′ where j ′ ∈ J and ( l ′ , m ′ ) ∈ L × M \ { l , m } . i.e. Φ c b ( m, l ) ∩ T V ( C j lm ) = { y ∈ T V ( C j lm ) ∩ T V ′ ( C j ′ l ′ m ′ ) : ( j ′ , l ′ , m ′ ) ∈ W (1) b ( m ) ∪ W (2) b ( m, l ) , V ′ ∈ V b ( V ) } 16 Since Bob can also decode the junk data as reliably as the secret, one may potent ially transmit meaningful data instead of the junk provi ded that the data is uniformly random and nee d not be secured at the same lev el as the secret. where V b ( V ) := { V ′ ∈ V n ( Q ) : I ( Q, V ′ ) ≥ I ( Q, V ) } W (1) b ( m ) := { ( j ′ , l ′ , m ′ ) : j ′ ∈ J, l ′ ∈ L, m ′ ∈ M \ { m }} W (2) b ( m, l ) := { ( j ′ , l ′ , m ) : j ′ ∈ J, l ′ ∈ L \ { l }} (The dependence on V , m and l will be omitted if there is no ambiguity .) V b is th e set of pr ob lematic con ditional type that can lead to err or . ( W (1) b , W (2) b ) for ms a p artition of the set of ind ices for the misleadin g codewor ds . In p articular, W (1) b correspo nds to the indices o f misleading codew or ds that result in decoding the public message wrong if the observation lies in a problematic V ′ -shell of the mislead ing c odeword. Similarly , W (2) b correspo nds to the ind ices of misleading co dew ords that result in decoding the pr iv ate message wro ng but decod ing the public m essage corr ectly . 17 By the un ion bo und, | Φ c b ( m, l ) ∩ T V ( C j lm ) | ≤ X V ′ ∈V b X ( j ′ l ′ m ′ ) ∈ W (1) b | T V ( C j lm ) ∩ T V ′ ( C j ′ l ′ m ′ ) | + X V ′ ∈V b X ( j ′ l ′ m ′ ) ∈ W (2) b | T V ( C j lm ) ∩ T V ′ ( C j ′ l ′ m ′ ) | Consider the second sum mation wh ere U m ′ = U m because m ′ = m . Since T V ( C j lm ) ∩ T V ′ ( C j ′ l ′ m ′ ) is conta ined by T Q 1 V ( U m ) ∩ T Q 1 V ′ ( U m ) ⊂ T QV ∩ T QV ′ the summ and is zero if QV 6 = QV ′ or Q 1 V 6 = Q 1 V ′ by the unique ness o f (canonic al cond itional) ty pes. Since the premise imp lies I ( Q 0 , Q 1 V ) = I ( Q 0 , Q 1 V ′ ) , we can im pose this constraint (temporarily) in the secon d summation without affecting the sum. Under this equa lity constraint, h owe ver, the inequality constraint I ( V | Q ) ≥ I ( V ′ | Q ) on V ′ can be replaced by I ( Q 1 , V | Q 0 ) ≥ I ( Q 1 , V ′ | Q 0 ) . W ithd rawing the equality constraint gives the following uppe r bou nd, | Φ c b ( m, l ) ∩ T V ( C j lm ) | ≤ X V ′ ∈ V ( Q ): I ( Q,V ) ≥ I ( Q,V ′ ) X ( j ′ l ′ m ′ ) ∈ W (1) b | T V ( C j lm ) ∩ T V ′ ( C j ′ l ′ m ′ ) | + X V ′ ∈ V ( Q ): I ( Q 1 ,V | Q 0 ) ≥ I ( Q 1 ,V ′ | Q 0 ) X ( j ′ l ′ m ′ ) ∈ W (2) b | T V ( C j lm ) ∩ T V ′ ( C j ′ l ′ m ′ ) | T o bou nd the expectatio n on the left, it suffices to boun d the expectation of | T V ( C j lm ) ∩ T V ′ ( C j ′ l ′ m ′ ) | on the rig ht b y the Packing Lemma[ 3 ], which is stated in a convenient f orm with c onditionin g in Lemm a A.4 . If ( j ′ , l ′ , m ′ ) ∈ W (1) b ( m ) , th en C j lm is ind ependen t of C j ′ l ′ m ′ . Applyin g th e Packing Lemm a witho ut cond itioning giv es, f or all δ > 0 , n > n 0 ( δ, |U ||X | ) , E | T V ( C jlm ) ∩ T V ′ ( C j ′ l ′ m ′ ) | | T V ( C jlm ) | ≤ exp {− n [ I ( Q, V ′ ) − δ ] } If ( j ′ , l ′ , m ′ ) ∈ W (2) b ( m, l ) instead, then C j lm is co nditiona lly indepen dent of C j ′ l ′ m ′ giv en U m . The Packing Lemm a gives, E | T V ( C jlm ) ∩ T V ′ ( C j ′ l ′ m ′ ) | | T V ( C jlm ) | ≤ exp {− n [ I ( Q 1 , V ′ | Q 0 ) − δ ] } 17 The reason for this sepa ration is that the two types of error lead to two dif ferent ex ponents. 11 Combining th e last three inequalities, we have for n suffi- ciently large th at, E | Φ c b ( m, l ) ∩ T V ( C j lm ) | | T V ( C j lm ) | ≤ J LM exp {− n [ I ( Q, V ) − δ ] } + J L exp {− n [ I ( Q 1 , V | Q 0 ) − δ ] } where we have used the fact that |W (1) ( m ) | = J L ( M − 1) and |W (2) ( m, l ) | = J ( L − 1) ; replaced I ( Q, V ′ ) and I ( Q 1 , V ′ | Q 0 ) by their min ima I ( Q, V ) and resp ectiv e ly I ( Q 1 , V | Q 0 ) which correspo nd to th e mo st slowly decayin g terms; an d ap plied the T ype Counting Lemma to | V n ( Q ) | . Hence, lim inf n →∞ − 1 n log β ( V , Θ , Φ c b ) ≥ | min { I ( Q, V ) − R M , I ( Q 1 , V | Q 0 ) } − R J − R L | + = | I ( Q 1 , V | Q 0 ) − R J − R L + | I ( Q 1 V | Q 0 ) − R M | − | + because min { a, b } = b + min { 0 , a − b } . B. Expon ent for Eve The exponen t of β ( V , Θ , Φ c e ) for Eve can be calculated analogo usly . W ith MMI deco ding Φ c e ( m ) ∩ T V ( C j lm ) is the set of z ∈ T V ( C j lm ) th at has I ( U m ∧ z ) n o larger than I ( U m ′ ∧ z ) for some m isleading codeword U m ′ where m ′ ∈ M \ { m } . i.e. Φ c e ( m ) ∩ T V ( C j lm ) = { z ∈ T V ( C j lm ) ∩ T Q 1 V ′ ( U m ′ ) : el sem ′ ∈ M \ { m } , V ′ ∈ V e ( V ) } where the set o f pro blematic condition al type s for Eve is V e ( V ) := { V ′ ∈ V ( Q ) : I ( Q 0 , Q 1 V ′ ) ≥ I ( Q 0 , Q 1 V ) } . By the unio n bou nd, | Φ c e ( m ) ∩ T V ( C j lm ) | ≤ X V ′ ∈V e ( V ) X m ′ ∈ M \{ m } | T V ( C j lm ) ∩ T Q 1 V ′ ( U m ′ ) | Since C j lm is independ ent of U m ′ where m ′ 6 = m , the Packing Lemma A.4 withou t conditio ning (but w ith ˆ Q assign ed as Q 0 , and ˆ V assigned as Q 1 V ′ ) gives, for a ll n ≥ n 0 ( δ, |U | ) , E | T V ( C jlm ) ∩ T Q 1 V ′ ( U m ′ ) | | T V ( C jlm ) | ≤ exp {− n [ I ( Q 0 , Q 1 V ′ ) − δ ] } Substituting this into the pr evious inequ ality , we have for n sufficiently large tha t, E | Φ c e ( m ) ∩ T V ( C j lm ) | | T V ( C j lm ) | ≤ M exp {− n [ I ( Q 0 , Q 1 V ) − δ ] } where we have rep laced I ( Q 0 , Q 1 V ′ ) by it minimum I ( Q 0 , Q 1 V ) . The expon ent is theref ore, lim inf n →∞ − 1 n log β ( V , Θ , Φ c e ) ≥ | I ( Q 0 , Q 1 V ) − R M | + which completes the pro of the Lemma VI.1 V I I . R E S U LT S The exponen ts o f β ( V , Θ , Ψ) , β ( V , Θ , Φ c b ) and β ( V , Θ , Φ c e ) calculated in Lemma V .3 an d Lemma VI.1 using the random code in Definition IV . 3 and the coding scheme in De fini- tion IV .2 g iv e an initial set of lower b ounds to the expo nents by Lemma IV .2 . As discussed in Sectio n IV -B , the bou nds can then be extended with prefixed DMC ˜ V by rewriting ( W b , W e ) as ( ˜ V W b , ˜ V W e ) . T o obtain the final version o f the boun ds, consider th e following rate r eallocation: move the fir st R ∈ [0 , R L ] bits of the secre t to the end o f the pu blic message, an d encod e them with a wiretap channel code at rate ( R M + R, R L − R ) . Theorem VII.1 (In ner bound of achievable exponent trip les) . F or every rate triple ( R M , R L , R λ ) , we have for all R ∈ [0 , R L ] , R J ≥ 0 , finite sets U and ˜ X , distribution Q := Q 0 ◦ Q 1 ( Q 0 ∈ P ( U ) , Q 1 ∈ P ( X ) U ) , tr ansitional pr oba bility matrix ˜ V ∈ P ( X ) U × ˜ X , th e exponen t triple ( E b , E e , S e ) satisfying the following is achievable (see Definition III.3 ) fo r the wir etap chan nel { W b , W e } . E b ≥ min V ∈ P ( Y ) U ×X D ( V k ˜ V W b | Q ) + | I ( Q 1 , V | Q 0 ) − R J − R L + R + | I ( Q 0 , Q 1 V ) − R M − R | − | + E e ≥ min V ∈ P ( Z ) U ×X D ( V k ˜ V W e | Q ) + | I ( Q 0 , Q 1 V ) − R M − R | + S e ≥ min V ∈ P ( Z ) U ×X D ( V k ˜ V W e | Q ) + R L − R − R λ + | R J − I ( Q 1 , V | Q 0 ) | − + From this, we can com pute an inne r bou nd to the region of strongly achiev able rate triple for wh ich a bove in ner bou nd to the achiev able exponent triple are all strictly p ositiv e. T o simplify notation, let ( U , ˜ X , X , Y , Z ) be som e ra ndom vari- ables distributed as Q 0 ( u ) Q 1 ( ˜ x | u ) ˜ V ( x | u, ˜ x ) W b ( y | x ) W e ( z | x ) . (Note that ( U , ˜ X ) → X → YZ .) Since inform ation diver g ence D ( V k W ) is zer o at V = W an d positive otherwise, the exponents are p ositiv e iff, for R ∈ [0 , R L ] and R J ≥ 0 ( 31a ) ( 31b ) ( 31c ) ( 31d ) ( 31e ) R J + R L − R < I ( ˜ X ∧ Y | U ) R J + R L + R M < I ( U ˜ X ∧ Y ) R M + R < I ( U ∧ Z ) R L − R > R λ R L − R + R J > R λ + I ( ˜ X ∧ Z | U ) R and R J can b e eliminated witho ut loss of optimality by the Fourier-Motzkin e limination[ 10 ] (see Lemma A.5 ), which giv es the fo llowing. Theorem VII.2 (I nner boun d o f stron gly achiev ab le r ate triples) . ( R M , R L , R λ ) is str on gly a chievable for the wir e tap channel { W b : X 7→ Y , W e : X 7→ Z } if ( 32a ) ( 32b ) ( 32c ) ( 32d ) ( 32e ) 0 ≤ R λ < R L R λ < I ( ˜ X ∧ Y | U ) − I ( ˜ X ∧ Z | U ) 0 ≤ R M < I ( U ∧ Z ) R M + R λ < I ( U ∧ Y ) + I ( ˜ X ∧ Y | U ) − I ( ˜ X ∧ Z | U ) R M + R L < I ( ˜ X ∧ Y | U ) + min { I ( U ∧ Y ) , I ( U ∧ Z ) } for some ( U , ˜ X ) → X → YZ with P Y | X = W b and P Z | X = W e . 12 It is admissible to have U a s a de terministic functio n o f ˜ X a nd |U | ≤ 4 + min {|X | − 1 , |Y | + |Z | − 2 } | ˜ X | ≤ |U | (2 + min { |X | − 1 , |Y | + |Z | − 2 } ) which imp lies U → ˜ X → X → YZ a nd I ( U ˜ X ∧ Y ) = I ( ˜ X ∧ Y ) . The ad missible co nstraints are o btained fr om [ 2 ] as de - scribed in Lemma A.6 . They can be imposed without changin g the inner bound . E xample A.4 illustrates h ow to comp ute an inner boun d of the achievable rate tup les using the Multi- Parametric T oolb ox[ 7 ] in Matlab. The closu re of the rate region o f ( R M , R L , R λ ) is indeed equiv a lent to the closure of the r ate region o f ( R 0 , R 1 , R e ) in Theorem 1 of [ 2 ]. Mo re precisely , we h av e th e fo llowing. Proposition VII.3 (Equi valent rate region) . Let R be the inne r bound of str ongly a chievable rate tuples ( R M , R L , R λ ) in Theor em VII.2 , and R ′ be the set of r a te tuples that satisfies, ( 33a ) ( 33b ) ( 33c ) ( 33d ) 0 ≤ R λ < R L R λ < I ( ˜ X ∧ Y | U ) − I ( ˜ X ∧ Z | U ) 0 ≤ R M < min { I ( U ∧ Y ) , I ( U ∧ Z ) } R M + R L < I ( ˜ X ∧ Y | U ) + min { I ( U ∧ Y ) , I ( U ∧ Z ) } for some ( U , ˜ X ) → X → YZ with th e sam e a dmissible constraints as R . Then, R = R ′ . Hence, R is conv ex by L emma 5 o f [ 2 ] and the closu re of its projection on ( R M , R L ) is the ra te region fo r th e asymmetric bro adcast channel by Coro llary 5 of [ 2 ]. Su ppose W b is m or e capa ble [ 5 ] than W e , i.e. I ( X ∧ Y ) ≥ I ( X ∧ Z ) for all P X ∈ P ( X ) . Then it is a dmissible to have ˜ X = X (i.e. no pre fix DMC) by a stra ightforward exten sion o f the proof of Theorem 3 in [ 2 ]. It also fo llows that 0 ≤ R λ < max P X [ I ( X ∧ Y ) − I ( X ∧ Z )] is the pr ojection of R on R λ . Assume the strong er con dition th at W b is less noisy [ 5 ] than W e , i.e. I ( U ∧ Y ) ≥ I ( U ∧ Z ) f or any U → X → YZ . Th en, by Theorem 3 in [ 2 ], it is addmissible to have U determin istic in addition to ˜ X = X to obtain th e projectio n on ( R L , R λ ) . Pr oof o f Pr opo sition VII.3 : W ithou t loss of g enerality , consider some U → ˜ X → X → YZ with U ∩ ˜ X = ∅ . Let U α be a rando m variable such th at it is ˜ X with probab ility α and U with pr obability 1 − α , and that 1 { U α = ˜ X } is indepen dent of ( U , ˜ X , X , Y , Z ) . 18 Then, U 1 = ˜ X , U 0 = U , U α → ˜ X → X → YZ , I ( U α ∧ Y ) = (1 − α ) I ( U ∧ Y ) + αI ( ˜ X ∧ Y ) I ( ˜ X ∧ Y | U α ) = I ( ˜ X ∧ Y ) − I ( U α ∧ Y ) and similarly for Z . Thu s, w e can define R α and R ′ α as the correspo nding r ate poly topes defined by the linear co nstraints in ( 32 ) an d ( 33 ) respectively . If we impose ( 33c ) on R 0 , the resulting polytope is the same as R ′ 0 because ( 32c ) and ( 3 2d ) are r edunda nt un der ( 32b ) and ( 33c ). Thus, R 0 ⊃ R ′ 0 , which implies R ⊃ R ′ . If I ( U ∧ Z ) ≤ I ( U ∧ Y ) , then ( 33c ) is equiv alen t to ( 32c ) . By the previous argumen t, R 0 = R ′ 0 . 18 This proof technique is from the proof of T heorem 4.1 in [ 3 , p.360]. P S f r a g r e p l a c e m e n t s R M R L R λ (a) R ′ 0 P S f r a g r e p l a c e m e n t s R M R L R λ (b) R ′ α P S f r a g r e p l a c e m e n t s R M R L R λ (c) Hull( R ′ 0 , R ′ α ) Fig. 6. R 0 ⊂ H ull( R ′ 0 , R ′ α ) for the case I ( U ∧ Y ) ≤ I ( U ∧ Z ) ≤ I ( ˜ X ∧ Y ) If I ( ˜ X ∧ Y | U ) ≤ I ( ˜ X ∧ Z | U ) , then both R 0 = R ′ 0 = ∅ by identical constraints ( 32b ) and ( 33b ). Consider I ( U ∧ Y ) ≤ I ( U ∧ Z ) ≤ I ( ˜ X ∧ Z ) ≤ I ( ˜ X ∧ Y ) . Choose α such that I ( U α ∧ Y ) = I ( U ∧ Z ) . T he conv ex hu ll, Hull( R ′ 0 , R ′ α ) , contain s R 0 primarily be cause the hyper plane of ( 32c ) a nd ( 32d ) for R 0 intersects a t, R λ = I ( ˜ X ∧ Y ) − I ( ˜ X ∧ Z ) ≤ I ( ˜ X ∧ Y | U α ) − I ( ˜ X ∧ Z | U α ) which is con tained b y the half-spa ce ( 33b ) ( with non -strict inequality instead ) fo r R ′ α . Th is is illustrated in Fig. 6 . For compariso n, R 0 is p lotted with blue d otted fram e in eac h sub-figur e. It is co ntained by the co n vex hu ll in Fig. 6(c) as expected. Finally , co nsider the case I ( ˜ X ∧ Y ) < I ( ˜ X ∧ Z ) . Choose α such that I ( U α ∧ Y ) = I ( ˜ X ∧ Y ) − I ( ˜ X ∧ Z | U ) . 19 Then, Hull( R ′ 0 , R ′ α ) c ontains R 0 primarily because the hyper plane of ( 32d ) intersects with the plan e R λ = 0 at, R M = I ( ˜ X ∧ Y ) − I ( ˜ X ∧ Z | U ) which is co ntained by th e half- space (with non- strict inequal- ity) o f ( 33c ) f or R ′ α . This is illustrated in Fig. 7 . Hence, we have R 0 a subset of Hull( R ′ 0 , R ′ α ) for som e α ∈ (0 , 1) , which implies R ⊂ R ′ as desired. V I I I . C O N C L U S I O N In doub t of a unifyin g measure of security , we have con- sidered su ccess expo nent as an alter nativ e to equiv o cation rate for the wiretap cha nnel co nsidered in [ 2 ]. W e replac e the maximal co de construction an d typical set deco ding in [ 2 ] with the rando m codin g scheme and maximum em pirical 19 If I ( ˜ X ∧ Z | U ) = 0 , choose α to approach 1 from belo w to ensure that R ′ α 6 = ∅ . 13 P S f r a g r e p l a c e m e n t s R M R L R λ (a) R ′ 0 P S f r a g r e p l a c e m e n t s R M R L R λ (b) R ′ α P S f r a g r e p l a c e m e n t s R M R L R λ (c) Hull( R ′ 0 , R ′ α ) Fig. 7. R 0 ⊂ H ull( R ′ 0 , R ′ α ) for the case I ( ˜ X ∧ Y ) < I ( ˜ X ∧ Z ) mutual info rmation decoding in [ 6 ]. The lower bound s o n the error exponents follow from [ 6 ] with th e well-known Packing Lemma (see L emma A. 4 ), while th e lower bo und on the success expo nent is obtain ed with the appr oach of [ 4 ] and a technique we call the Overlap Lemma (see Lemma V .2 ) . This lem ma giv es a d oubly expo nential behavior tha t ena bles us to guaran tee g ood realization of the ran dom c ode for effecti ve stoch astic enco ding by tra nsmission of ju nk data (see Section IV -B ). Com bining with the prefix DMC techniqu e in [ 2 ] tha t adds artificial m emoryless noise to the chan nel input symbols, and a rate realloca tion step of tr ansferring some secret bits to the public message be fore encod ing (see Section VII ), we obta in the final inner boun d of th e ach iev able exponent triples in Theor em VII.1 with the co rrespond ing strongly achievable rate triples in Theo rem VII.2 . Propo si- tion VII.3 shows that th is inner bo und to the rate region is conv ex and c oincides with th e region o f achiev able r ate triples in Theor em 1 of [ 2 ]. It is a straightfo rward extension to consider the maximu m error expon ents an d av erage success exponent over the m es- sages. The same bo und f ollows by the u sual expurgation argu- ment and a m ore care ful ap plication o f the do ubly expo nential behavior of the Overlap Lemma. Whether this tradeoff is optimal, h owe ver, is unclear . It would be surprising if one can further improve the tra deoff by impr oving the co ding sch eme. A P P E N D I X Example A.1 (Max imum a pr iori and aposteriori success probab ility) . Consider the f ollowing probability matrix, P Z := 5 8 3 8 P S | Z := 4 5 1 5 2 3 1 3 from which the a priori p robability is P S = 3 4 1 4 . W itho ut knowing Z , Eve gu esses S successfu lly with pro bability at most 3 4 if one guess is allowed, an d 1 if two guesses are allowed. If she knows Z , she still ha s the same maximum probab ility of success in each case because the mo st p robab le candidate for the secret is the same r egardless of wh ether Z is observed. Hence, Eve canno t a chieve a b etter success probab ility regardless o f Z , even though Z is no t in depend ent of S . Success probability fails to express the notion of p erfect secrecy in this sense. Example A.2 (Transmission of junk d ata) . Conside r the case when there is no public message, an d the co ding is not restricted to constant com position code. Fig. 8 illustrates the approa ch of transm ission of junk d ata thro ugh a wiretap channel, which consists of a binary noiseless channel for Bob and a bin ary erasure ch annel for Eve. While the chann el X 0 1 Y 0 / / 1 _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ 1 / / 1 _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ (a) Channel W b to Bob X 0 1 Z 0 / / . 5 ε + + . 5 W W W W W W W W W W W W W W W 3 3 . 5 g g g g g g g g g g g g g g g 1 / / . 5 ` ` ` ` ` ` ` ` ` ` ` ` ` ` (b) Channel W e to Eve l j c j l := ( j, j ⊕ l ) 0 0 00 0 1 11 1 0 01 1 1 10 f ( l ) := c J l , J ∼ Bern( . 5) (c) Stochastic encoder f q Fig. 8. An exampl e of tra nsmission of jun k data input is perfectly ob served by Bob , half of it is erased on av erage bef ore it reaches Eve. Alice exploits th is b y sen ding one bit of junk J unif ormly distributed in { 0 , 1 } tog ether with on e bit o f secret l ∈ { 0 , 1 } in two channel u ses. The channel input is X = ( J , J ⊕ l ) wh ere ⊕ d enotes the XOR operation . Bob can recover the secr et per fectly by the decod er φ b ( y ) := y (1) ⊕ y (2) since his observation Y is equal to X . Eve can use the same d ecoding if the re is n o erasure. Howe ver, if the re is one or more erasures, her observation Z becomes indep endent of the secr et, in which case she should unifor mly randomly pick 0 or 1 as her guess to min imize the condition al error probab ility , provided that she can only m ake one guess. 20 Thus, the conditional error probability is 0 if there is no erasur e, wh ich hap pens with probab ility 1 / 4 , and 1 / 2 otherwise. T he overall con ditional error p robability is 3 / 8 . Note that if Alice u ses a pr efix DMC as described in Section IV -B , Bob cannot achieve zero er ror pr obability . I n 20 W e allo w stochasti c decodin g here since the focus is the probability at block length n = 2 instead of the ex ponent when n → ∞ . 14 other words, prefix DMC is strictly inf erior in this ca se. 21 Example A.3 (Prefix d iscrete mem oryless chan nel) . Consider prefixing the wiretap ch annel { W b : X 7→ Y , W e : X 7→ Z } with the discrete m emoryless ch annel { ˜ V } defin ed in Fig. 9 . Each arrow connects an inp ut alphab et to an outp ut alphabet if the corr esponding transition pr obability , labeled in th e arrow , is non-ze ro. Consider the case without prefix ing the wiretap X 00 01 10 11 ˜ X 0 1 3 b b b b b b b b b b 0 0 b b b b 2 3 Z Z Z Z Z Z Z Z Z Z , , Z Z Z Z 1 2 3 d d d d d d d d d d 1 1 d d d d 1 3 \ \ \ \ \ \ \ \ \ \ - - \ \ \ \ (a) Prefix channel ˜ V X 00 01 10 11 Y 0 . . 1 ] ] ] ] ] ] ] ] ] ] ] ] ] ] 2 2 1 e e e e e e e e e e e e e e 1 - - 1 [ [ [ [ [ [ [ [ [ [ [ [ [ [ 1 1 1 c c c c c c c c c c c c c c (b) Channel W b to Bob X 00 01 10 11 Z 0 . . 1 ] ] ] ] ] ] ] ] ] ] ] ] ] ] 6 6 . 5 m m m m m m m m m m m m m m m m 1 - - . 5 [ [ [ [ [ [ [ [ [ [ [ [ [ [ 1 1 . 5 c c c c c c c c c c c c c c 2 ( ( . 5 P P P P P P P P P P P P P P P P 0 0 1 ` ` ` ` ` ` ` ` ` ` ` ` ` ` (c) Channel W e to Eve ˜ X 0 1 Y 0 / / 1 _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ 1 / / 1 _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ (d) ˜ V W b ˜ X 0 1 Z 0 / / 1 3 _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ 8 8 1 3 r r r r r r r r r r r r r r r r r 1 * * 1 3 U U U U U U U U U U U U U U U 3 3 1 3 g g g g g g g g g g g g g g g 2 % % 1 3 K K K K K K K K K K K K K K K K K K . . 1 3 ] ] ] ] ] ] ] ] ] ] ] ] ] ] ] (e) ˜ V W e Fig. 9. An exampl e of prefix discrete memoryle s s channel channel with ˜ V . Since W b is a weakly symmetric ch annel, the capacity is 1 b it by the capacity form ula for weak ly symmetric in Th eorem 8.2.1 of [ 1 ]. Bob can achieve the capa city of 1 bit with zero erro r proba bility and a single use of the channel iff Alice encod es 1 bit of infor mation u sing any o f the following co deboo ks θ (1) := { 00 , 10 } , θ (2) := { 0 0 , 11 } , θ (3 ) := { 01 , 10 } and θ (4 ) := { 01 , 1 1 } . If Alice wants to have zero er ror prob ability for Bob in n channel uses with rate n b its, the co deboo k has to be some concatenatio n of codebo oks f rom { θ ( i ) } 4 i =1 . However , the channel inp ut X n would n ot be ind ependen t of the chan nel o utput Z n to Eve. T o argue this, con sider the i -th chan nel use only . Suppose Alice uses θ (1) to enco de a u niformly r andom bit at that time slot. Then, g i ven Z ( i ) = 0 , we have X ( i ) = 10 with pr obability 2 / 3 rath er than the p rior pr obability 1 / 2 . The o ther cases can be argued similarly . In sh ort, not randomizin g over the 21 It would be more interest ing to find an exa mple in which prefix DMC is inferior e ven if Bob’ s probabili ty of error cann ot be made to 0 by adding noise with memory like what the transmission of junk data does. code u nav oid ably leaks inform ation to Eve. Howev er , if the random ization is don e by tran smitting junk data, th e usefu l data rate would d rop below the capac ity 1 b it. Consider prefixing the wiretap channel with ˜ V . The prefixed channel ˜ V W b to Bob is a noiseless bin ary chan nel as sh own in Fig . 9(d) . Th e p refixed channel ˜ V W e to E ve, howe ver , is completely noisy as shown in Fig. 9(e) . One can ch eck that the channel outp ut Z is in depend ent of X fo r any input distribution on X . Thus, Alice can tr ansmit at the capac ity 1 bit with zero error prob ability for Bob but without leaking any inf ormation to Eve. Pr efixing discrete memo ryless chann el is strictly b etter than transmitting junk data in this ca se. Lemma A.1 (r andom codeword) . F o r δ > 0 , n ∈ Z + , Q := Q 0 ◦ Q 1 ( Q 0 ∈ P n ( U ) , Q 1 ∈ V n ( Q 0 , X )) , V ∈ V n ( Q, Z ) , u ∈ T Q 0 , n -sequenc e X u niformly rando mly chosen fr o m T Q 1 ( u ) , then Pr { z ∈ T V ( u ◦ X ) } = T X | U , Z ( u , z ) T X | U ( u ) ≤ exp {− n [ I ( Q 1 , V | Q 0 ) − δ ] } wher e the last inequ ality holds for all n ≥ n 0 ( δ, |U ||X | ) ; ( U , X , Z ) in the first equality is a random tuple with joint distribution P U , X , Z := Q 0 ◦ Q 1 ◦ V ; T P X | U , Z is denoted by T X | U , Z and similarly for others; a nd T X | U , Z ( u , z ) with ( u , z ) ∈ T U , Z is denoted by T X | U , Z . Pr oof: Consider z ∈ T QV , for which the de sired p rob- ability is non-z ero. Since u ∈ T U , X ∈ T X | U ( u ) , and z ∈ T Z , the event that { z ∈ T V ( u ◦ X ) } , o r equ iv alently , { z ∈ T Z | U , X ( u ◦ X ) } , happen s iff ( u , X , z ) ∈ T U , X , Z . Th is happen s iff X ∈ T X | U , Z ( u , z ) . Hence, for all z ∈ T Z , Pr { z ∈ T V ( u ◦ X ) } = P r X ∈ T X | U , Z ( u , z ) = T X | U , Z ( u , z ) T X | U ( u ) ≤ exp {− n [ I ( X ∧ Z | U ) + δ ] } where the last inequ ality is tru e for all n ≥ n 0 ( δ, |U ||X | ) due to L emma 1.2.5 of [ 3 ] that | T X | U , Z ( u , z ) | ≤ exp { n H ( X | U , Z ) } | T X | U ( u ) | ≥ ( n + 1) −|U | |X | exp { nH ( X | U ) } Since I ( X ∧ Z | U ) = I ( Q 1 , V | Q 0 ) , this giv e s the desired bound . Lemma A.2. F or all n, exp( nR ) , exp( nδ ) ∈ Z + exp( nR ) exp( nδ ) ≤ exp { (log e + n ( R − δ )) exp( nδ ) } Pr oof: Let a := exp( nR ) a nd b := exp( nδ ) . Th en, we have the well-known inequ ality that a b ≤ a b e b , which gives the R.H.S. of the bo und as desired . T o derive this, note that e x ≥ (1 + x ) f or all x ≥ 0 . Thu s, e ax ≥ (1 + x ) a = a X i =1 a i x i = ⇒ a b ≤ e ax − b ln x Setting x = b/a gives the desired ine quality . 15 Lemma A.3 (list size constra int) . F or an y subset S ⊂ Z n of observation s and list dec oder ψ with list size λ , the corr espo nding de cision r egion map Ψ : L 7→ 2 Z n satisfies, ( 34 ) X l ∈ L | Ψ( l ) ∩ S | = λ |S | Pr oof: The pro of is by the double countin g prin ciple, X l ∈ L | Ψ( l ) ∩ S | = X z ∈S X l ∈ L 1 { l ∈ ψ ( z ) } = X z ∈S λ = λ |S | Lemma A.4 (Packing (with c ondition ing)) . Conside r some finite sets U , X and Y , type Q 0 ∈ P n ( U ) , and canonica l condition al types Q 1 ∈ V ( Q 0 , X ) and ˆ Q 1 ∈ V ( Q 0 , ˆ X ) . Let Q := Q 0 ◦ Q 1 and ˆ Q := Q 0 ◦ ˆ Q 1 be th e corr e sponding joint types; U b e some random n -sequen ce distributed over T Q 0 ; X and ˆ X be ind ependen tly and u niformly randomly drawn fr om T Q 1 ( U ) an d T ˆ Q 1 ( U ) r espe ctively; C := U ◦ X and ˆ C := U ◦ ˆ X denote the element-wise concatena tions. Then, for all δ > 0 , n ≥ n 0 ( δ, |U ||X | ) , V ∈ V n ( Q, Y ) ∩ V n ( ˆ Q, Y ) , E | T V ( C ) ∩ T ˆ V ( ˆ C ) | | T V ( C ) | ! ≤ exp n − n [ I ( ˆ Q 1 , ˆ V | Q 0 ) − δ ] o Pr oof: Con sider some realiza tion u ∈ T Q 0 of U . By condition al indep endence between X an d ˆ X , E | T V ( C ) ∩ T ˆ V ( ˆ C ) | U = u = X y ∈ T Q 1 V ( u ) Pr { y ∈ T V ( u ◦ X ) } Pr n y ∈ T ˆ V ( u ◦ ˆ X ) o ≤ X y ∈ T Q 1 V ( u ) | T X | U , Y | | T X | U | exp {− n [ I ( ˆ Q 1 , ˆ V | Q 0 ) − δ ] } = | T Y | U || T X | U , Y | | T X | U | exp {− n [ I ( ˆ Q 1 , ˆ V | Q 0 ) − δ ] } where the first inequality follows fro m Lemma A.1 (bo th the equality and inequality cases) ∀ n ≥ n 0 ( δ, |U ||X | ) with U , X and Y an d T X | U , Y etc. defined analo gously . Di vide both sides by | T V ( u ◦ X ) | = | T Y | U , X | , and app ly that fact that | T Y | U || T X | U , Y | = | T X | U || T Y | U , X | , E | T V ( C ) ∩ T ˆ V ( ˆ C ) | | T V ( C ) | U = u ≤ exp {− n [ I ( ˆ Q 1 , ˆ V | Q 0 ) − δ ] } A veraging b oth sides over U gives the desired bo und. Lemma A.5 (Fourier-Motzkin) . The rate co nstraints in ( 31 ) with R ∈ [0 , R L ] and R J > 0 defin es the same re g ion of (no n- ne gative) r a te triples ( R M , R L , R λ ) as the rate constraints in ( 32 ) d o. Pr oof: Consid er app lying the Fourier-Motzkin elimina- tion. From ( 31 ) an d R ∈ [0 , R L ] , we have, − R < 0 − R + R J + R L < I ( ˜ X ∧ Y | U ) R − R L ≤ 0 R + R M < I ( U ∧ Z ) R − R L + R λ < 0 R − R J − R L + R λ < − I ( ˜ X ∧ Z | U ) R J + R L + R M < I ( U ˜ X ∧ Y ) Adding each of th e first two inequ alities to the next four eliminates R , which , toge ther with R J ≥ 0 , gives, − R J ≤ 0 − R J − R L + R λ < − I ( ˜ X ∧ Z | U ) R J + R L + R M < I ( U ∧ Z ) + I ( ˜ X ∧ Y | U ) R J + R λ < I ( ˜ X ∧ Y | U ) R J + R L + R M < I ( U ˜ X ∧ Y ) R M < I ( U ∧ Z ) − R L + R λ < 0 R λ < I ( ˜ X ∧ Y | U ) − I ( ˜ X ∧ Z | U ) where we h av e r emoved some in activ e constrain ts. Add ing each of th e first two inequ alities to the next three ine qualities eliminates R J , wh ich giv es ( 32 ) as desired. Example A.4 (Inn er bound of strongly ach iev able rate triples) . Consider the following wiretap chan nel and p refix DMC. % wiretap channe l p = 0 . 1 ; PY X = [ 1 − p p ; p 1 − p ; . 5 . 5 ] ; % P Y | X r = . 4 ; PZX = [ 1 0 ; 1 − r r ; r 1 − r ] ; % P Z | X % input distributions and prefix DMC P X = [ . 2 5 . 2 5 . 5 ] ; P t X = PX ; P XtX = e y e ( 3 ) ; % P X , P ˜ X and P X | ˜ X q = . 3 ; PU tX = [1 − q q ; 1 0 ; 0 1 ] ; % P U | ˜ X The prefix DMC is noiseless, i.e. X = ˜ X . The cha nnel an d U are co nstructed based o n Cou nter-example 2 in [ 5 ] with slight modification s. 22 Define the Bayes’ rule, cond itional mu tual informa tion and entropy functio ns as follows. f u n c t i o n P XY = b a y e s ( P YX , PX ) % compute P X | Y from P Y | X and P X P XY = r e p m a t ( PX , s i z e ( PY X , 2 ) , 1 ) . ∗ P YX ’ ; P XY =P X Y . / r e p m a t ( sum ( PX Y , 2 ) , 1 , s i z e ( P XY , 2 ) ) ; f u n c t i o n IQ VP = I ( Q , V , P ) % compute I ( Q, V | P ) i f n a r g i n < 3 P= o n e s ( 1 , s i z e ( Q , 1 ) ) . / s i z e ( Q , 1 ) ; e n d IQV P=H ( Q ∗ V , P) − H ( V , P ∗ Q ) ; f u n c t i o n h =H ( Q , P ) % compute H ( Q | P ) Q ( Q = = 0 ) = 1 ; h= − P ∗ sum ( l o g 2 ( Q ) . ∗ Q , 2 ) ; Then, the m utual info rmation exp ressions req uired f or the r ate region can be com puted as follows. % deri ved values P U = P t X ∗ P UtX ; P tX U = b a y e s ( PU tX , P t X ) ; % P U and P ˜ X | U PYt X = PX tX ∗ P Y X ; P YU = P tXU ∗ PYt X ; % P Y | ˜ X and P Y | U P Z t X= PXt X ∗ PZX ; PZU = Pt XU ∗ P Z t X ; % P Z | ˜ X and P Z | U IUY= I ( PU , P YU ) ; It X Y U = I ( Pt XU , PYt X , P U ) ; % I ( U ∧ Y ) and I ( ˜ X ∧ Y | U ) IU Z = I ( PU , PZU ) ; I t X Z U = I ( PtX U , PZ t X , P U ) ; % I ( U ∧ Z ) and I ( ˜ X ∧ Z | U ) 22 This is such that the resulting constraints ( 32 ) on the rate region are not redundan t for the purpose of il lustrati on. 16 Using the Mu lti-Parametric T o olbox [ 7 ] , we first d efine the poly tope satis fying the constraints from ( 3 1 ) on ( R, R J , R M , R L , R λ ) ; and then pro ject it to ( R M , R L , R λ ) , which should give the desired region in ( 32 ). % constraints from ( 31 ) on ( R, R J , R M , R L , R λ ) A =[ − e y e ( 5 ) ; − 1 1 0 1 0 ; 1 0 0 − 1 0 ; 1 0 1 0 0 ; 1 0 0 − 1 1 ; 1 − 1 0 − 1 1 ; 0 1 1 1 0 ] ; b = [ z e r o s ( 1 , 5 ) I t X Y U 0 I U Z 0 − I t X Z U IUY + I t X Y U ] ’ ; P = p o l y t o p e ( A , b ) ; R= p r o j e c t i o n ( P , [ 3 4 5 ] ) ; % Project to ( R M , R L , R λ ) to obtain ( 32 ) Finally , p lotting th e region g iv es Fig. 10 . o p t i o n s . w i r e = 1 ; p l o t ( R , o p t i o n s ) ; x l a b e l ( ’R_M’ ) ; y l a b e l ( ’R_L’ ) ; z l a b e l ( ’ R_{\lambda}’ ) ; s e t ( gc a , ’CameraPosition’ , [ 1 . 5 − 0 . 5 1 ] , . . . ’CameraUpVector’ , [ − 0 . 5 0 . 2 0 . 8 ] , ’DataAspectRatio’ , [ 1 1 1 ] ) ; P S f r a g r e p l a c e m e n t s R M R L R λ ( 32a ) ( 32b ) ( 32c ) ( 32d ) ( 32e ) 0 0.05 0.1 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0 0.05 0.1 Fig. 10. An example of an inner bound to stron gly achie vable rate tuples As expected, each facet corre sponds to a co nstraint in ( 32 ), indicated in the figu re. Lemma A.6 (admissible con straints) . Consider some random variables in the Markov chain U ′ ˜ X ′ → X ′ → YZ distributed over the finite sets U ′ , ˜ X ′ , X , Y and Z r espe ctively . Then ther e e xists U → ˜ X → X → YZ with, P Y | X ( y | x ) = P Y | X ′ ( y | x ) , ∀ ( x, y ) ∈ X × Y P Z | X ( y | x ) = P Z | X ′ ( z | x ) , ∀ ( x, z ) ∈ X × Z and ( 35a ) ( 35b ) ( 35c ) ( 35d ) I ( U ∧ Y ) = I ( U ′ ∧ Y ) I ( U ∧ Z ) = I ( U ′ ∧ Z ) I ( ˜ X ∧ Y | U ) = I ( ˜ X ′ ∧ Y | U ′ ) I ( ˜ X ∧ Y | U ) = I ( ˜ X ′ ∧ Y | U ′ ) and ( 36a ) ( 36b ) ( 36c ) |U | = 4 + min {|X | − 1 , |Y | + |Z | − 2 } | ˜ X | = |U | (2 + min {|X | − 1 , |Y | + |Z | − 2 } ) H ( U | ˜ X ) = 0 Furthermore , X = X ′ if |X | − 1 ≤ |Y | + |Z | − 2 . Pr oof: Since the f ollowing proof is a minor extension to [ 2 , ( A.22)], we will gi ve o nly th e ch anges as follows. Read ers should refer to [ 2 ] fo r details. W ith ˜ X ′′ := ( U , ˜ X ′ ) , we h av e I ( ˜ X ′′ ∧ Y | U ) = I ( ˜ X ′ ∧ Y | U ) and similar ly for I ( ˜ X ′′ ∧ Z | U ) . It suffices to show the desired existence with ˜ X ′ replaced by ˜ X ′′ on the R.H.S. of ( 35 ). Consider the case |X | − 1 ≤ |Y | + |Z | − 2 . The admissible constraint ( 36 ) is equivalent to [ 2 , (A.22 )]. (n .b . V in [ 2 ] is ˜ X here.) The p roof therein also implies X = X ′ . beca use ( X ′ , Y , Z ) need no t b e ch anged. Suppose |X | − 1 > |Y | + |Z | − 2 instead. T o achiev e H ( Y ) and H ( Z ) in [ 2 , (A.24), (A.25 )], on e ca n r eplace (A.23) by ( 37 ) Pr( Y = y ) = X u ∈U Pr { U = u } f y ( ¯ p u ) Pr( Z = z ) = X u ∈U Pr { U = u } f z ( ¯ p u ) where, u sing the notatio n in [ 2 ], f y ( ¯ p ) := ¯ p Y ( y ) and f z ( ¯ p ) := ¯ p Z ( z ) Only |Y | − 1 o f the functions f y ( ¯ p ) and |Z | − 1 of the fu nctions f z ( ¯ p ) are con sidered. Thus, as a co nsequence of the Eggleton - Carath ´ eodor y Theo rem, U takes at m ost ( |Y | + |Z | − 2) + 4 different values to preserve (A.24) to (A .27) in [ 2 ] and ( 37 ) defined above. Similarly , (A.28) can be replaced by the corresp onding expr essions o n Pr( Y = y | U = u ) and Pr( Z = z | U = u ) . For ev ery fixed u , there exists a ran dom variable V u with no more than ( |Y | + |Z | − 2) + 2 values preserving the set of desired eq ualities. W ith ˜ X her e playing the role of the new V in [ 2 ], ( 36 ) follows. R E F E R E N C E S [1] Thomas M. Cover and Joy A. Thomas. E lements of Information Theory . A W ile y-Interscience Publicat ion, 1991. ISBN:0-471-06 259-6 . [2] Imre Csisz ´ ar and J ´ anos K ¨ orner . Broadcast channels with confidentia l messages. IEE E T ransacti ons on Information Theory , IT -24(3):339–348 , May 1978. doi:10.1109 /TIT . 1978.1055892 . [3] Imre Csisz ´ ar and J ´ anos K ¨ orner . Information Theory: Coding Theorems for Discret e Memoryless Systems . Akad ´ emiai Kiad ´ o, Budapest, 1981. ISBN:0-12-198 450-8 . [4] G ¨ uther Dueck a nd J ´ anos K ¨ orner . Reliabi lity function of a discret e memo- ryless chann el at rates abo ve capaci ty . IEE E T ransacti ons on Information Theory , IT -25(1):82–85, January 1979 . doi:10.1109 /TIT . 1979.1056003 . [5] J. K ¨ orner and K. Marton. The comparison of two noisy cha nnels. In I. Csisz ´ ar and P . Elias, editors, T opics in Information Theory , pages 411– 423. Colloquia Mathematic a Societatis J ´ anos Bolyai, North Holland, Amsterdam, 1975. [6] J ´ anos K ¨ orner and Andrea Sgarro. Unive rsally attai nable error expone nts for broadcast channe ls w ith degraded message sets. IEEE T rans- actions on Information Theory , IT -26(6):670–679 , Nov ember 1980. doi:10.1109 /TIT . 1980.1056275 . [7] M. Kva snica, P . Grieder , and M. Baoti ´ c. Multi-Pa rametric T oolbox (MPT), 2004. A vaila ble from: http:/ /contro l.ee.ethz.ch/ ∼ mpt/ . [8] David Malone and W ayne Sulli v an. Guesswork is not a Substi tute for Entropy . In P r oceedings of the Information T echno logy and T elecom- municati ons Confer ence , October 2005 . [9] J. L. Massey . Guessing and entrop y . In ISIT: Proce edings IEE E Internati onal Symposium on Informati on Theory , sponsor ed by The Informatio n Theory Society of The Institu te of Electrical and Electr onic Engineer s , 1994. doi:10.1109 /ISIT .1994.394764 . [10] Jiˇ r ´ ı Matouˇ sek and Bernd G ¨ artner . Understandi ng and Using Lin- ear Pr ogr amming . Springer Berlin Heidelber g New Y ork, 2007. ISBN:3-540-30 697-8 . [11] Neri Merha v and Erdal Arikan. T he shannon cipher system with a guessing wiretapper . IEEE T ransacti ons on Information Theory , 45(6):1860 –1866, Sept ember 1999. doi:10.1109/ 18.782106 . [12] C. E. Shannon. A mathematical theory of communicat ion. The Bell System T echn ical Journal , 27:379–423, 623–656, October 1984. doi:10.1145 /584091.5840 93 .
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment