A Network Protection Framework through Artificial Immunity
Current network protection systems use a collection of intelligent components - e.g. classifiers or rule-based firewall systems to detect intrusions and anomalies and to secure a network against viruses, worms, or trojans. However, these network syst…
Authors: Michael Hilker, Christoph Schommer
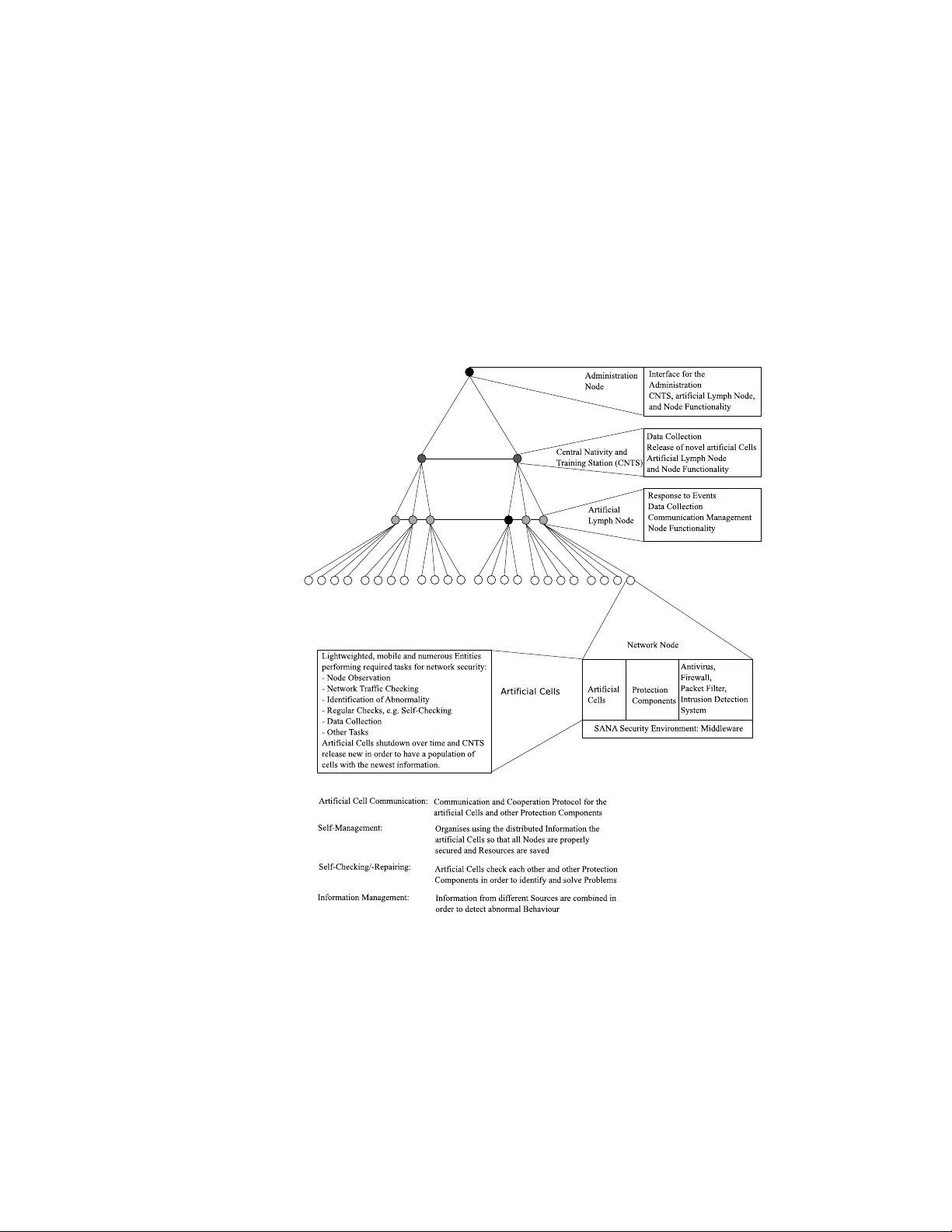
A Net w ork Protection F ramew ork through Artificial Imm unit y Mic hael Hilk er & Christoph Sc hommer Univ ersity of Luxem bourg F acult y of Science, T ec hnology , and Communications 6, Rue Ric hard Coudenho ve-Kalergi, L-1359 Luxem bourg { michael.hilker, christoph.schommer } @uni.lu Abstract. Curren t net work protection systems use a collection of in- telligen t comp onen ts - e.g. classifiers or rule-based firewall systems to detect intrusions and anomalies and to secure a netw ork against viruses, w orms, or tro jans. How ever, these netw ork systems rely on individu- alit y and supp ort an architecture with less collab orative work of the protection comp onen ts. They giv e less administration supp ort for main- tenance, but offer a large num ber of individual single points of failures - an ideal situation for netw ork attacks to succeed. In this work, we discuss the required features, the p erformance, and the problems of a distributed protection system called SANA . It consists of a co operative arc hitecture, it is motiv ated by the human immune system, where the comp onen ts corresp ond to artificial immune cells that are connected for their collab orativ e work. SANA promises a b etter protection against in- truders than common known protection systems through an adaptive self-managemen t while keeping the resources efficien tly b y an intelligen t reduction of redundancies. W e in tro duce a library of several nov el and common used protection comp onen ts and ev aluate the p erformance of SANA by a pro of-of-concept implementation. Keyw ords: Netw ork Protection, Artificial Immune Systems, Bio-Inspired Com- puting, Distributed Architectures, Information Management, Netw ork Sim ulation. 1 In tro duction The attac ks tow ards computer netw orks is increasing and the costs as well. In crime tow ards the computer net works do es 88% b elong to the infections by viruses and w orms but the attacks by humans is increasing. In addition, more and more attacks aim to receive information, whic h are afterw ards sold to earn money; this thread generates a cost of ab out 70 , 000 , 000$ [1]. The costs of intru- sions tow ards computer netw orks is measured to 150 , 000 , 000$ [2]. An emerging problem are the attac ks performed b y in ternal users, e.g. b y unsatisfied emplo yes of a compan y trying to get access to confident information. A netw ork protection system is a system that tries to protect the netw ork and its nodes against in trusions and attac ks [3]. It consists of sev eral components of different granularit y [4], ranging from parameter changes in sub-components, no des, or pack et filters to p o w erful antivirus s oft w are, firewalls, and intrusion detection systems in imp ortant netw ork no des [5]. Each protection comp onen t con tains the workflo w and the knowledge in order to p erform the tasks so that the protection system conv erges to its goals. The protection system holds the co operation betw een the different protection comp onen ts and the maintenance- and up date w orkflows. The performance of the protection system is an indication ho w secure the netw ork is against in trusions; the p erformance originates out of the p erformance of all protection comp onen ts. There exist differen t c haracteristics in order to ev aluate and compare different protection systems [6]: – The system has to b e complete; i.e. the system protects all no des against in trusions. – The provided resources has to be used efficiently . – The protection system has to secure the netw ork and all no des. It should also not influence the user and the normal workflo ws in the netw ork. – The installation, maintenance, and up date workflo ws hav e to b e easy and fast to p erform. The system has to ensure that the different protection com- p onen ts work prop erly and are up-to-date. – The system has to adapt to the current situation in the netw ork and it has to b e adaptive in order to iden tify mo dified, m utated, and/or nov el attacks. An imp ortan t characteristics of computer netw ork protection systems is that they should be extendable and cop e with up coming - more and more complex as well as in telligent - intrusions. F or example, the ZMIST virus remains hid- den in host programs [7]; common-used detection tec hniques p erforming pattern matc hing ha v e serious problems to identify it. The EVOL virus hides itself through sw apping instructions in existing programs [8]. Thus, we demand for a protection system to use an adaptive information managemen t having protection comp o- nen ts collab orated; w e demand for protection systems to b e easily extendable to wards and p ermanent protection up date. A recent approach is to mo del the biological systems for computer science where the artificial immune systems is one example. In this article, we intro- duce first a nov el framework for protection systems as artificial imm une system [9,10,11,12], which is motiv ated by the human immune system [13]. W e then suggest a computer net work protection system called SANA, present its archi- tecture, p erformance and some implementation aspects. An imp ortant asp ect is that SANA is a complex - but easy to understandable - system that does not use a centralised system [14]. It provides the features and c haracteristics explained ab o v e and provides a dynamic, efficien t, and adaptive securit y environmen t in whic h common used and nov el approac hes for netw ork security are combined [15]. These approac hes are b oth motiv ated by the Biology as w ell as Computer Science approaches. 2 Curren t Situation Curren t promising protection solutions and systems contain an architecture of differen t comp onen ts. In each no de, an tivirus softw are [16] and firewall [17] are installed; they observ e file access, activ e pro cesses, and the net work pac ket head- ers for p ossible attacks. Additionally , some no des facilitate other protection com- p onen ts lik e e.g. spam filters for identifying unsolicited and undesired messages. On the netw ork side, on hubs, switches, and routers header chec king pack et filters run in order to define a netw ork p olicy describing which routings, proto- cols, and p orts are allow ed [18]. Imp ortan t no des like e.g. internet gatew ays and email servers are secured using intrusion detection systems [5], whic h chec k each pac ket completely and observe the whole no de in order to identify in trusions. A no vel approac h are intrusion prev ention systems [19], whic h extend the antivirus soft ware and firewall to a system observing the file access and system calls as w ell as chec king the whole pack ets for intrusions. Ho wev er, these systems mostly com bine only an tivirus and firewalls extended b y some statistical approaches in order to detect unknown intrusions; ho wev er they are significantly differen t to in trusion detection systems. Curren tly , these components must b e installed and configured in each node man ually where the configuration is more and more done through a cen tralised managemen t server. The up dates of each protection comp onen t - antivirus or in trusion detection system - works as follows: eac h comp onent asks regularly a cen tral management if there exists an up date; if y es, then it do wnloads it. The an tivirus softw are and the firewall ask then the user when a suspicious even t o ccurs; the user tak es ov er the decision and pro ceeds. This is often a risk since the user is mostly not an exp ert. Additionally , the an tivirus softw are, firew alls, pac ket filters, and in trusion detection systems use a log system in order to inform the administrators about differen t ev ent. The administrator analyses suc h, but due to the enormous num ber of messages is it not p ossible for him to analyse eac h message prop erly; the intrusion s ma y sta y undetected. The different protection comp onen ts are not connected. Th us, eac h comp o- nen t works on its own and collab orative work do es not exist. This leads pri- marily to redundant chec ks: for example, the firewall and intrusion detection system in a no de chec k the pack et for similar characteristics; resources are con- sequen tly wasted. How ever, more imp ortan t is that the differen t information gathered through the different protection comp onen ts are not combined in or- der to identify intrusions or ev en to identify abnormal or suspicious b eha viour. Lastly , the protection system do es not chec k itself whether each comp onen t is up-to-date and works properly , whic h leads to the situation that different protec- tion components work with limited performance. An example for this problem is that the up date system of an antivirus soft ware do es not work prop erly and e.g. the an tivirus softw are is no longer updated and do es not iden tify the new est in trusions; this is a problem b ecause this no de is a risk for the whole net work. F or facilitating the required resources, distributed installations provide sev- eral adv antages compared to the classical client server arc hitecture. In the client serv er architecture, the client softw are - protection comp onents - p erform the tasks and demand different updates and services from the central managemen t serv er. Some approac hes for a distributed protection system exist [20], e.g. an ar- tificial immune system for net work security [9,10,11,12]. How ever, these systems mostly do not use a fully distributed approach, i.e. there are some centralised comp onen ts that are critical for the ov erall performance of the system, the sys- tem is mostly not adaptive, and the system do es not use small entities as artificial cells and more the m ulti-agent system approac h [21] using heavy agen ts with few mobilit y , lots of internal information, and lots of kno wledge ab out the current situation. A system is adaptiv e when it reconfigures itself so that it cop es with the current and future situation; also learning, self-c hecking, and -repairing is a part of adaptive workflo ws. F urthermore, common used systems do not use an approac h where many artificial cells ha ve to comm unicate and collab orate. F ur- thermore, these systems are far a w ay from production; this framew ork in tends to narro w the gap b et ween the distributed protection systems of academic researc h and pro duction. In the next section, a nov el framework for a distributed, in tegrated, and dynamic protection system is introduced in which common used and nov el ap- proac hes for net work security are com bined and whic h tries to solve the limita- tions of existing protection systems. 3 SANA: A Net w ork Protection F ramew ork through Artificial Imm unity The protection system SANA [15] is a library of different netw ork protection comp onen ts using a subsym b olic organisation and information management. SANA cop es with up coming attac ks that increase con tinuously adaption and in- telligence. The administration and main tenance is simplified, it works mainly au- tonomously . The system does not use centralised protection comp onents, which are single p oin ts of failure. Differen t comp onents and workflo ws of SANA are motiv ated by w orkflows and arc hitectures from the Biology . An ov erview is visu- alised in figure 1; the system is explained in the next sections according to this figure. 3.1 Securit y Environmen t Distributed systems with moving en tities require an en vironment in which the en tities work. Therefore, the security en vironment is installed in eac h no de and pro vides an en vironment that is used by all protection comp onen ts. The envi- ronmen t ensures the access to resources as storage, memory , CPU, and net work as w ell as ensures that each protection comp onen t is recognised when a certain ev ent o ccurs. Therefore, each protection comp onen t is installed in the security en vironment and registered for certain ev ents, e.g. arriving of a pac ket or access to a file. Thus, the protection comp onen ts are indep enden t from the underlying hardw are platform as well as netw ork proto cols and configurations, which leads to a faster deploymen t of protection comp onents. The securit y environmen ts is a middleware betw een the resources of the node and the protection components. The security environmen t also provides chec ks testing the protection comp o- nen ts if they are allow ed to access the resources and if they in tend to p erform prop erly . This ensures that not prop erly working comp onents are remov ed from the netw ork; they cannot access resources anymore. Additionally , the adminis- trators can connect to the securit y en vironment in order to administrate these as well as to access the protection comp onen ts working in this no de. The ad- ministrators can quickly add no vel components facilitating nov el approac hes of net work security . 3.2 Protection Comp onen ts The protection system consists of several protection comp onents, which p er- form the tasks required for sec uring the net work. These protection components are b oth common used protection comp onents like antivirus soft ware, firewall, pac ket filter, and intrusion detection systems in order to b enefit from their p er- formance as w ell as no vel approaches of protection components, e.g. the artificial cells. The common used protection comp onents are installed in the security en- vironmen t and p erform their tasks. SANA is an artificial immune system that facilitates common protection comp onen ts; SANA is an ev olution of common used protection systems. The common used protection comp onen ts are designed and implemented for a sp e- cific op erating system. Thus, the platform indep enden t system SANA pro vides an environmen t in order to install the protection comp onent in the securit y en- vironmen t. The security en vironment pro vides everything for chec king, e.g. the net work pack ets, the system calls, and the file accesses - middleware b et ween the protection comp onen ts and the resources. The protection components chec k these and the resp onse is transfered to the real resources through the securit y en vironment. F or other protection components, an operating systems using hard- w are virtualisation is provided wherein the protection components runs (see 3.7) [22]. With this implementation, common used protection components as e.g. an- tivirus softw are, firewall, pack et filter, and intrusion detection system are imple- men ted and reused without internal changes in the comp onen ts so that SANA is a framework for a distributed distribution system. Also, non standard ap- proac hes as e.g. virus throttle [23,24] for slowing down the propagation of intru- sions and Malfor [25] for automatically generating signatures of intrusions are implemen ted. The artificial cells are dynamic, highly specialised, ligh tw eighted, and mobile so that the system is dynamic and hard to attack. The cells are highly specialised and light w eighted b ecause they hav e only limited kno wledge ab out the situation in the net work and the v arious tasks required for netw ork securit y are distributed o ver several nodes. The cells are dynamic and mobile through moving around Fig. 1. Ov erview ab out SANA and changing of the b eha viour. The num b er of differen t t yp es of artificial cells is enormous - at least several thousands of cells - b ecause the tasks required for net work securit y are split in small pieces so that a breakdown of one artificial cell do es not break do wn the whole system. F urthermore, each t yp e of artificial cell is sev eral times present in the net work so that redundancies occur. Examples for artificial cells are in tro duced in [26,27]. Different types of artificial cells: File Access Accessing a file can install in trusions like viruses. Thus, these cells c heck each file that is accessed on the no de. No de Observ ation Artificial cells observ e the whole node including the anal- yse of the system calls and the control flow graphs of executed programs in order to iden tify and preven t installation of in trusions. Net work T raffic Analysis This type of artificial cells ev aluates each net work pac ket whether it con tains an intrusion or not. If it contains an intrusion, the artificial cells also kno w how to proceed with the pac ket, e.g. pac ket drop or disinfection. An example is the approach ANIMA for Intrusion Detection wherein the signatures of intrusions are stored in a net work like arc hitecture [28]. Iden tification of Abnormalit y In the netw ork, different examples of abnor- malit y exist. E.g. the infected no des or not proper w orking protection com- p onen ts must b e identified and remo ved. AGNOSCO is an artificial cell using the information from the distributed netw ork traffic analysis in order to iden- tify infected no des using the artificial ant colonies approac h [15]. Another approac h is ANIMA for Anomaly Detection, which stores a current view of normal netw ork traffic in order to identify and rep ort abnormal net work traffic [29]. Regular Chec ks Abnormality can also b e recognised using regular chec ks. E.g. viruses and w orms ha ve a significant signature - e.g. files, running pro cesses, and registry entries -, backdoors hav e an significan t op en p ort with service connected to this p ort, and not prop er working or outdated protection com- p onen ts can b e identified using some chec ks. Th us, these cells mov e through the netw ork, p erform the c heck, and identify the problems. When a problem is recognised, they inform other cells in order to solve the problem. Data Collection These cells collect information from the netw ork, which are used in order to monitor the netw ork and afterw ards for self-improv emen t and -learning. Other T yp es It is possible to implemen t nearly all t yp es of artificial cells where the limitations are that the cells should b e small and light weigh ted as w ell as the cells can only use the resources provided b y the security environmen t. Using the artificial cells, it is p ossible to quickly introduce nov el approac hes; tasks as describ ed b efore can b e defined and p erformed using some artificial cells. F or this, the artificial cells sh utdown ov er time where the time is defined b y the administration; v alues for this parameter are b et ween s ome min utes and up to s ome hours. The systems in the netw ork generate con tinuously new cells in order to keep the p opulation up-to-date; these systems are explained in the next section. With this w orkflow, no vel approac hes and tec hniques for net work securit y are quickly introduced and the new est information is included. 3.3 Imp ortan t No des SANA con tains the normal netw ork no des with the security environmen t and the protection comp onen ts installed in this environmen t. F or helping the admin- istrators to maintain SANA, tw o sp ecialised no des are required.These are tw o t yp es of nodes with more functionalit y , whic h are motiv ated by the human b ody . These sp ecialised nodes are required in order to collect more information and to organise the system. Artificial Lymph No des The artificial lymph no des are a meeting p oint and resp onse cen ter for artificial cells. The artificial lymph no des are an extension to the normal netw ork no des. A set of artificial lymph no des manage a small net work part - sub-sub-netw ork called. They hav e additionally the following features: – Collect status information ab out the supplied netw ork part. – Manage the communication in the sub-sub-netw ork; see also the section 3.4. – Resp ond to the messages from the artificial cells. Examples of the response are to release nov el artificial cells solving a problem (disinfection a node or up dating a protection comp onen t) and to inform the administrators. – Supply the artificial cells with additional information, e.g. whether a netw ork pac ket contains an intrusion or not. The artificial lymph no des are redundant installed where several artificial lymph no des manage a sub-sub-netw ork so that a breakdown of a few interferes less the p erformance of the ov erall system. CNTS - Central Nativit y and T raining Stations The artificial cells shut- do wn ov er time and m ust b e replaced by new ones, which include the newest information as w ell as nov el approaches of net work securit y . The CNTS produce no vel artificial cells and release these con tinuously in order to k eep the num ber of artificial cells approximately constan t. Thus, the CNTS are an extension of the artificial lymph nodes and hav e the same features as artificial lymph no des as well as the generation of artificial cells. A set of CNTS manages a part of the netw ork with sev eral sub-sub-net works included - sub-net work called. The CNTS mo del the b one marrow and thym us of the human immune system. 3.4 Artificial Cell Comm unication The artificial cells are sp ecialised and p erform only a small task. Thus, several cells ha ve to collab orate in order to iden tify and preven t attacks. Therefore, the artificial cell comm unication is introduced, whic h is a distributed fault-tolerant comm unication proto col for p oint to multi-point communication. The artificial cell communication mo dels the cell comm unication of the human b ody pro vid- ing a communication and collab oration protocol for the artificial cells and other protection comp onen ts. Therefore, we in tro duce the term artificial substanc e , whic h is used for message exc hanges. It mo dels the b ehaviour of differen t sub- stances of the human b o dy , e.g. the cytokines and hormones [13]. Each artificial substance contains the message and a header with the parameters hops-to-go and time-to-live describing the distribution area of the artificial substance. Eac h no de manages the routing of the substances where each no de has a set of no des; each substance is sen t to these no des when the distribution area is not reac hed; this set is adapted to the curren t situation in the netw ork. The artificial cell communication works as follows: one comp onen t sends a message, packs this message in an artificial substance, defines the distribution area, and gives it to the netw ork. In eac h no de, the substance is presented to all protection comp onen ts and the right components receiv e the message. The iden- tification of the right receivers is done using artificial receptors. These receptors are a public/priv ate key pair describing the t yp e and status of the artificial cells, protection comp onen ts, and artificial substances. All artificial cells, protection comp onen ts, and artificial substances con tain several artificial receptors describ- ing their type and status. Only when an artificial cell or protection comp onen t can authorise itself using the righ t k eys of the artificial receptors, it will receiv e the message stored in the artificial substance. The protection components receiv- ing the message respond to it, and the no de sends the substance to all next no des and the pro cess rep eats until the distribution area of the substance is reached. The next no des are defined by administrator and adapted by the system so that the comm unication is configured to the current situation in the netw ork. The artificial receptors are additionally used in order to secure the access to resources using authentication pro cesses. The adv an tages of the artificial cell communication are a distributed, efficien t, and fail-safe protocol without a single p oin t of failure. F urthermore, the proto col w orks fine for point to multi-point communication as used in net work security where a comp onen t sends a message to all nearby comp onen ts of a certain t yp e. 3.5 Self Managemen t The n umerous artificial cells require where their tasks are most needed. There- fore, the artificial immune cells organise as follo ws: eac h protection comp onen t kno ws how m uch security it provides (security v alue). Each no de calculates - basing on the securit y v alues of eac h component in the node - the security lev el of the no de; when this level falls b elow a certain threshold - the threshold is defined by the administrator and defines ho w m uch securit y this no de requires -, it starts a notification pro cess. This notification pro cess attracts other nearby artificial cells in order to mo ve to this node so that the securit y v alue is increased and the artificial cells in this no de are more affine to sta y than to mov e. Ho w ever, the artificial cells still w ork autonomously . F or the artificial cells, p erforming regular tasks on the no des, exist another w orkflow; we decided to use the artificial an t colonies approac h during the de- signing of this w orkflow. Briefly , the artificial an ts la y pheromone on the ground when carrying an artificial prey; these pheromones are afterw ards used in order to find other nearby preys. Here, the preys are unchec ked no des and the artifi- cial an ts are the artificial cells. Th us, in each no de n i exist a storage for v alues for these cells where each v alue v n i ,n i +1 ,t j is for a connection n i , n i +1 and for a sp ecific type t j of artificial cell, whic h is iden tified b y the artificial receptors. When a cell performs the c heck in node n i and mov es afterw ards to no de n i +1 , it increases the v alue for the connection ( n i , n i +1 ) and for the sp ecific cell t yp e t j in the no de n i . F urthermore, the no de decreases these v alues ov er time. When a cell wan ts to mo ve from node n i to another no de, it can use these v alues in order to identify the no de, which w aits the longest time for a chec k. The v alue describ es the num b er of pheromones released b y the artificial ants - artificial cells - where the pheromones disapp ear ov er time. The self management increases the p erformance enormously b ecause the ar- tificial cells are prop erly distributed o ver all nodes and enough artificial cells can still keep moving in order to provide a dynamic protection system. In addition, the artificial cells p erforming regular tasks are lead to the no des where this task is required; this reduces the required resources b ecause redundant tasks are re- duced and all no des are chec k ed regularly , whic h increases the securit y in the net work. 3.6 Information Managemen t Compared to common used protection systems, the information management of SANA is enhanced: the artificial cells analyse not only the information from one single no de, they use the information from sev eral no des for a combined anal- ysis. This is e.g. used for finding abnormal b eha viour or m ulti-step/multi-stage attac ks. F urthermore, the differen t artificial cells exchange information so that results from different analysing systems are combined ev aluated and used for finding more intelligen t and adaptiv e intrusions. F urthermore, the self-chec king p erformed b y the chec king artificial cells is done distributed so that lots of infor- mation are gathered. The w arnings and alerts are semi-automatically analysed and pro cessed - common warnings and alerts are automatically pro cessed and only nov el are directly sen t to the administration; They are also sent to the ad- ministrators as summary status information when required or demanded. The administrators can alwa ys demand a status rep ort or snapshot from the system in order to receive an o verview ab out the current situation. 3.7 Implemen tation A platform-indep endent pro of-of-concept implementation is done so that SANA can b e compared with other protection systems. The simulation runs on a net- w ork simulator implemen ting a pack et oriented netw ork - e.g. TCP/IP - where Fig. 2. Implemen tation la yers in a netw ork no de an adversarial stresses the netw ork and the protection system using many pack- ets with and without intrusions. F urthermore, the implementation can b e easily extended and also common used protection comp onents as antivirus softw are, in trusion detection systems, and firew alls are implemented in order to ev aluate and compare the p erformance of SANA. Implemen tation of Securit y En vironment The implementation of the se- curit y en vironment is crucial. It should provide the features required to run the protection comp onen ts efficiently but it should b e imp ossible that the attack ers use the security environmen t for the intrusion pro cess. F or this, the computer is divided in four lay ers: 1. The first la yer is the hardw are la yer con taining all hardw are lik e CPU, mem- ory , and storage. 2. The op erating system la yer 1 contains only the core parts of the op erating system in order to access the resources. Mostly , these are the kernel and some drivers. 3. The op erating system lay er 2 con tains the rest of the op erating system as w ell as separated the SANA securit y en vironment. 4. The softw are lay er contains in the op erating system the application soft- w are installed by the users and in the security environmen t the protection comp onen ts. The differen t lay ers are visualised in figure 2. As it can be seen in the figure, the operating system and the SANA security environmen t are separated. This is achiev ed through hardware virtualisation. In the op erating system lay er 1 is a softw are installed, which enables the features to run sev eral different op er- ating systems - guest op erating systems called - at the same time. Then, one guest op erating system has the op erating system running and one the SANA securit y en vironment. F urthermore, the op erating system cannot see the secu- rit y environmen t but vice v ersa, which is ensured through the implementation. F urthermore, op erating system la yer 1 is so installed that it only c hanges when the hardware changes. The adv antages of this installation: When an intruder installs an intrusion into the op erating system or the softw are space, it cannot access the security en vironment through the hardware virtuali- sation. If an in truder installs an intrusion in to the op erating system la yer 1, the run time environmen t recognises the c hange immediately , quaran tines the no de through a message to the neigh bours, and remo ves itself from the node; then, the attac ker do es not receive internal information from the protection system but the administrators ha ve to add the no de to the netw ork again. When the intruder tries to install itself in the security en vironment, a c hange is prohibited because this part do es not change. Lastly , if the in truder installs an intrusiv e protection comp onen t - either artificial cells or lo cal protection comp onen t - it requires the righ t keys from the artificial re ceptors in order to access the resources; without the keys, the intrusiv e comp onen t cannot p erform intrusiv e tasks in order to in terfere the net work. Thus, the intrusion can itself only install in the softw are part as b efore and has no access to the protection system SANA. An imp ortant adv antage is that the w orking op erating system and the protec- tion system runs in distinguished virtual machines. Thus, the protection system c hecks the op erating systems and softw are from outside and the intrusion has more problems to hide itself from the chec king b ecause co de armoring and stealth tec hniques often fail when the scan comes from outside. F urthermore, the vir- tual machines can b e mov ed to other machines so that a user works alwa ys with its system on all machines. In addition, the protection system is implemented in a service oriented architecture (SOA) [30] so that more complex tasks can b e demanded from the artificial lymph no des and CNTS using different virtual mac hines. E.g. a not prop er w orking security environmen t with protection com- p onen ts or a virtual mac hine with infected op erating system can b e mo ved to the administration computers and c heck ed for repairing and afterwards mov ed bac k. Another example is that complex tasks are done using an additional virtual computer running the protection comp onen ts p erforming the tasks. The disadv an tages of the approac h are an increased o verhead. How ever, when e.g. Op enVZ is used, the ov erhead is ab out 1% − 2% [22]. Additionally , nov el CPUs already contain visualization tec hniques implemented in hardware so that the ov erhead is even more reduced. 3.8 Main tenance The maintenance is imp ortan t for the administrators. The administrators de- mand for an easy-to-use and mostly autonomous administration and up date in terface where also the enhancements should b e done quickly and smo othly . Therefore, SANA pro vides differen t w orkflows: Administration The administrators can connect to eac h security environmen t in order to c heck the curren t status and administrate the distributed system. The artificial lymph no des and CNTS pro vide summary status information about the system and artificial cells can b e released in order to collect sp ecific information, whic h can b e afterwards used for further analysis. Up dates The updates are done differen tly compared to common used systems where a management serv er provides the up dates and the client soft wares do wn- load it. The disadv an tage is that the client softw are hav e to ask regularly for new up dates and outdated soft ware is not identified. Th us, SANA provides tw o differen t w ays of up dates: 1. The artificial cells are either up dated through new information from the arti- ficial lymph no des, whic h are visited regularly . Otherwise, the most common up date workflo w for artificial cells is the shutdo wn of the cells and release of new cells with the new est up dates and information. 2. The protection components are updated using up dating artificial cells. These cells are released when a new up date is av ailable. They visit all protection comp onen ts of this type and up date these. The update is rep orted in order to identify unsuccessful up dates or outdated comp onents. This workflo w is mostly used for not mo ving comp onen ts. In addition, the administrators can alwa ys connect to all security en viron- men ts in order to access the protection comp onen ts and up date these. Enhancemen ts Enhancemen ts can b e either released through a new p opula- tion of artificial cells or an installation in the security environmen ts. F or the new p opulation, the information ab out the enhancement must be added to the CNTS, which generates and releases the new artificial cells. An installation in the security environmen ts can b e either done man ually through connecting to eac h security en vironment or through an automated pro cess up dating a set of securit y environmen ts. With this, the enhancemen ts are quic kly deploy ed to the system. 3.9 Configuration of SANA After the in tro duction of the differen t parts and w orkflo ws of SANA, this section pro vides a short ov erview ab out a poss ible configuration of SANA on a real net work. Each netw ork no de, which are the computers in the net work as well as the netw ork equipment, contain a security environmen t in order to install the protection comp onen ts. Each no de con tains an an tivirus softw are and a firewall as in a common used protection system. The net work equipment hav e pac ket filters in order to define the netw ork p olicy and to close un used p orts. The artificial cells mo ve through the netw ork and pro vide a distributed protection subsystem on all no des. Imp ortan t nodes, e.g. the In ternet gatewa y and the email serv er but also imp ortan t pro ductiv e servers, run additionally to the artificial cells intrusion detection systems. The artificial lymph nodes are installed in the net work equipment so that the num b er of hops from the no des to the next artificial lymph no des is small. There are tw o to three CNTS in the net work releasing con tinuously nov el artificial cells. The self managemen t organises the artificial cells and guarantees a certain amount of security in each no de. The artificial cell communication enables the co operation b et w een the different cells. All other parts are implemen ted as describ ed ab ov e. 4 P erformance and Results The p erformance of SANA is more than acceptable. It p erforms mostly b et- ter than common used protection systems, whic h are a collection of protection comp onen ts, b ecause SANA also uses the same protection comp onents. Addi- tionally , it contains the artificial cells providing a dynamic and adaptive part. F urthermore, SANA pro vides using the security en vironment an easy to admin- istrate protection system that has man y autonomous w orkflows. The warnings and alerts of eac h protection comp onen t are analysed and pro cessed automati- cally b y other protection comp onen ts in order to adapt the behaviour - a more sophisticated information management. Therefore, different w orkflows are used: first, the information from the protection comp onents are com bined in order to iden tify infected no des and abnormal b ehaviour; second, the infected no des are disinfected and abnormal b ehaviour is observ ed; third, the w arnings and alerts are sent to the nearb y artificial cells which adapt their in ternal thresholds accord- ingly - implementation of the danger mo del; the danger mo del is an biological motiv ated approach where the cells exc hange con tinuously summary status in- formation in order to adapt their internal thresholds [31,32]. F urthermore, the protection system is highly dynamic: the artificial cells mov e contin uously and pro vide a hard to predict and to attac k protection system. F urthermore, the system can b e quickly extended with no vel approac hes for netw ork security . In the sim ulations, real netw ork attacks are mo delled where e.g. different w orms use the netw ork to propagate and the aim of the worm is to infect as man y no des as p ossible. Two simulations are performed: the first with a common used protection system consisting of an tivirus soft w are, firew all, pack et filter, and in trusion detection system, and a second with SANA. In all of our simulations SANA is more secure than the common used protection system. F urthermore, SANA adapts to the current situation b ecause iden tification of infected no des, not prop er w orking comp onen ts, and suspicious b ehaviour is detected and the problems are fixed automatically . Esp ecially , when an in trusion uses the netw ork for propagation and an intru- sion detection system chec ks the traffic b et ween the netw ork and the internet, the worm can easily infect the whole netw ork b ecause there is not an internal protection system that stops it. In this case, SANA’s artificial cells protect the no des through distributed intrusion detection and disinfection of infected no des. In the introduction, different criteria are introduced and SANA meets these: – Due to the installation in all no des SANA secures the whole netw ork. The configuration and the self management ensures that each no de is prop erly secured. All in trusions are not identified, whic h is the ideal performance of a protection system. How ever, SANA identifies almost all intrusions. – The system uses the resources efficien tly from all no des. Thus, the required resources on a single no de is reduced when SANA is used. – F or the third criteria, the system should secure all no des as w ell as it should not influence the normal pro duction. These tw o criteria are met because SANA is installed on eac h node and uses only limited resources so that the normal pro duction is not influenced. F urthermore due to its autonomous w orkflows SANA asks only rarely the user for critical security issues. – The CNTS release regularly artificial cells, which chec k, repair, and update the differen t protection comp onents for prop er w orking - self-chec king and -repairing. F urthermore, the installation is simplified because in each no de m ust only the security en vironment installed and the protection components find a common infrastructure. Due to the enormous n umber of artificial cells is a breakdo wn of one cell less imp ortan t for the ov erall performance. – SANA adapts to the current situation in the netw ork. Therefore, a sophisti- cated information management is used and the protection comp onen ts, i.e. artificial cells, identify abnormal b eha viour, infected no des, and adapt their b eha viour to the current situation in the net work. After the practical implemen tation and analysis of the system, distributed pro- tection systems are analysed more theoretically . Therefore, differen t attac k sce- narios are discussed where sev eral attacks are nearly alwa ys successful when curren t protection systems are used. Examples are that a user w ants to attack a no de, shuts it therefore down, and b o ots from an external storage device, e.g. Lin ux on an USB-stic k. The protection comp onen ts in this system are inac- tiv e and the user can install all intrusions and other protection comp onen ts of curren t protection system do es not identify it. SANA identifies infected no des quic kly , quarantines the no de, and informs the administrator. Other attacks are that no vel intrusions can infect a whole netw ork because only centralised systems iden tify it. In the next section, SANA is compared with common used protection systems. 4.1 Comparing SANA with common used Protection Systems As describ ed in the section 2 is a common used protection system a collection of differen t protection comp onen ts where each comp onent is directly installed on the no de. Mostly , all no des contain an antivirus softw are and a firewall, all net- w ork equipmen ts contain pack et filters, as w ell as imp ortan t no des are secured using in trusion detection systems. In contrast, SANA facilitates the same con- figuration of protection comp onents enhanced with the artificial cells, artificial lymph no des, and CNTS. These enable collab orativ e, dynamic, and adaptive w orkflows so that SANA iden tifies infected no des, weak p oints, and suspicious b eha viour. Due to the installation of the securit y environmen t are the protection comp onen ts distinguished from the op erating system. Hence, the comp onen ts c heck the system and consequen tly also the in trusions from outside so that it is harder for the intrusion to stealth or armour itself from the analysis. Addi- tionally , SANA can produce a static cop y of an virtual mac hine containing the user’s op erating system so that the comp onents chec k this halted system. This static copy is also used to sav e evidences of an intrusions in order to find the adv ersaries, whic h is an imp ortan t legal asp ect. Other important netw ork protection systems and comp onents are distributed and host-based intrusion detection systems. Distributed intrusion detection sys- tems install in eac h node an intrusion detection system or install capturing parts in each no de and some cen tralised analysing and resp onse centers. The second approac h has the disadv an tage that a lot of traffic is required in order to send all traffic to the analysing centers. The first approach installing in each no de an intrusion detection system has the disadv an tages that a lot of resources are required. In addition, eac h in trusion detection system requires lots of administra- tion and pro duces several w arnings and alerts, whic h must be analysed. Th us, the administrators cannot analyse these and, consequently , intrusions found but only rep orted to the log file are often not identifies. F urthermore, these approaches do not iden tify infected no des, weak p oints in the netw ork, and suspicious b e- ha viour. Widely used in big pro ductive and academic netw orks are honeyp ots and honeynets. A honeypot b ehav es like a normal computer, which pretends to con- tain imp ortan t information and pro cesses. F urthermore, the honeyp ot is nor- mally weak secured and, th us, an aim for attacks. How ever, the honeypot tries to attract the intrusion in order to trap or to delay intrusions. In addition, hon- eyp ots are used in order to identify nov el intrusions and generate a signature for these. Honeynets are a netw ork of honeyp ots in order to simulate a whole net work and to analyse the b ehaviour of in trusions in a netw ork. Honeyp ots and honeynets are not implemented b y SANA. How ev er, it is p ossible to implemen t these protection systems in a netw ork secured by SANA. When a small net work is used in a company and there is only few inter- net work comm unication, the protection system is so installed that all netw ork traffic is routed ov er a centralised no de, whic h analyses all netw ork traffic - some- times this is implemented using a broadcast net work or using adapted routing tables. Then, all other no des m ust not chec k the net work traffic and the installa- tion of protection comp onen ts is simplified. Unfortunately , this approach has the disadv antage that a lot of bandwidth is required for routing all traffic ov er this cen ter as well as the center needs lots of computational pow er in order to chec k the traffic. F urthermore, when an adversarial has control ov er some no des, the routing tables can b e easily c hanged as well as the encrypted traffic can b e only c heck ed at the destination no de. In addition, this configuration is static and does hardly iden tify suspicious b eha viour and not prop er working comp onen ts where infected no des can b e iden tified through analysing the information gathered at the centralised chec king no de. The differences to curren t protection system are the workflo ws implemented through the artificial cells. With these workflo ws, a distributed, dynamic, and adaptiv e protection system is implemented, which facilitates quic k and easy- to-use main tenance workflo ws. In addition, the information management is in- creased so that information from different no des are combined analysed in order to iden tify and solv e problems in the system. The distributed in trusion detection system deplo yed b y the artificial cells differs SANA from common used protec- tion systems; this distributed in trusion detection is analysed in section 4.5. 4.2 Sim ulation Results Before different attack scenarios are discussed in detail, some simulation results comparing SANA with common used protection system are introduced. The sim ulations of this section fo cus on netw ork based attacks where net work pack ets con taining intrusions try to infect a no de. Infected no des send pack ets with in trusions in order to propagate the attac k. Adversaries start the attack from outside the netw ork but infected no des are inside. The net work is alwa ys a big net work with at least 1000 no des. First Sim ulation: A random netw ork with 1110 no des. Three different pro- tection systems where SANA is the implementation of SANA using only artifi- cial cells, NIDS is the implementation of an IDS in the in ternet gatewa y , and NIDS&SANA is com bination of b oth. Performance: P ercent identified in trusive pack ets NIDS SANA NIDS&SANA First Simulation 48 . 67% 79 . 35% 85 . 13% After analysing the sim ulation, the results emerges out of the design. NIDS lack from the infected no des sending lots of intrusiv e pac kets. SANA lack from the bad securing of the Internet gatewa y . NIDS&SANA has the problem of infected no des, whic h are not remov ed from the netw ork. Second Simulation: The net work is a mo del of a switched compan y netw ork with 1110 no des. The configuration is similar to the first sim ulation. Two simu- lations are run: the first with 75% of the traffic is external to the Internet and the second with 25% external. P ercent identified in trusive pack ets NIDS SANA NIDS&SANA T raffic 25% internal 90 . 64% 71 . 23% 94 . 12% T raffic 75% internal 37 . 78% 74 . 71% 81 . 74% After analysing the sim ulation, the results emerges again out of the design. NIDS lac k from the infected no des sending lots of in trusive pac kets, which is mostly a problem in the simulation with lots of internal traffic due to no chec king of this traffic. SANA lac k from the bad securing of the Internet gatewa y where the most attac ks come through. NIDS&SANA has the problem of infected no des, whic h are not identified. Ho wev er, it can b e seen that the combination of SANA with an IDS in the Internet gatewa y secures the netw ork prop erly . Third Simulation: This sim ulation uses the same configuration as the second sim ulation but SANA uses the w orkflows to iden tify and disinfect infected no des. Th us, the p erformance of the NIDS is the same. P ercent identified in trusive pack ets NIDS SANA NIDS&SANA T raffic 25% internal 90 . 64% 94 . 19% 99 . 20% T raffic 75% internal 37 . 78% 90 . 68% 95 . 81% It can b e seen that the infected nodes release lots of intrusiv e pack ets and, thus, the identification of infected nodes increases the performance of the protection systems enormously . 4.3 P erformance in A ttack Scenarios The performance of SANA is analysed through several differen t attac k scenarios. These scenarios are very common in real life. F urthermore, most attacks can be reduced to these classes. W orm Attac k A w orm is a small softw are, which tries to infect a no de. There- fore, it uses the net work as propagation medium and exploits some securit y holes on the op erating system and its application softw ares. These security holes are mostly a badly implementation that can e.g. lead to a buffer ov erflow where the in trusions receive ro ot- or sup eruser-righ ts on the no de. The worm has after the infection con trol ov er the no de and can collect information, erase data, and in- terfere the usage of the no de. In addition, most w orms try to propagate through sending lots of net work pack ets con taining itself or a m utated version of itself. A famous example is the “ILOVEYOU” worm. In order to identify worm attac ks, SANA facilitates different workflo ws. The net work pack ets are c heck ed through the distributed in trusion detection sys- tem with lots of artificial cells as w ell as through centralised in trusion detection systems in imp ortant no des. When the worm is known by the protection sys- tem, it will remov e the pack ets. The chec k is p erformed from outside so that armoring and stealth tec hniques of in trusions hav e more problems to hide it- self. F urthermore, the information gathered through the distributed analysis is analysed in order to identify infected no des using e.g. the artificial cells of the t yp e A GNOSCO. Iden tified infected no des are rep orted and c heck ed b y chec king cells or by the administrators. When an infection is prov ed, the no de is isolated and disinfected. The infection is analysed for generating signatures, which are included in the next up dates. Commonly worms install e.g. bac kdo ors, files, pro- cesses, whic h are characteristic for the worm. The no des are regularly chec ked for differen t characteristics of intrusions and, when a c haracteristic is identified, it is rep orted to the administrators. The simulations show that SANA k eeps a netw ork clean from worm infec- tions. Especially the identification of infected no des and abnormal characteristics increase the p erformance compared to common used protection systems. The A GNOSCO approach identifies quickly infected no des and other cells located in the nearby artificial lymph no des start immediately a disinfection workflo w. Virus and T ro jan Horse Attac k A virus and a tro jan horse attack is similar to a worm attac k. The difference is that the virus requires a host program wherein it is included. When the host program is copied the virus is copied as well as when the host program is executed is the virus executed. A tro jan horse is a soft ware that primarily lo oks and b eha ves like a normal program but when it is executed it installs an intrusions. The tro jan normally do es not exploit a security hole, it facilitates the approach of so cial engineering where the user is manipulated in order to p erform actions. The goal of a tro jan is to install a bac kdo or, which is used by the adversarial in order to access and con trol the node. In con trast to w orms and viruses do es a tro jan not alw ays propagate. The difference b et w een the worm and the virus and tro jan horse attack are the propagation and infection workflo ws. The viruses and tro jan horses do not alw ays arrive using the netw ork where mainly all data exchanges are facilitated. The no des are observed for intrusiv e pro cesses, file acces s, and netw ork pac k- ets through the different protection comp onen ts as e.g. artificial cells, antivirus soft ware, and intrusion detection systems. When an infected file is identified, not the user is contacted as in common used protection systems, the systems analyses the w arning autonomously and pro cesses this. Only when the system do es not kno w how to pro ceed, it contacts the administrators for further steps. The workflo ws to identify and disinfect infected nodes are the same as used in the worm attack scenario. The sim ulations substantiate the performance b ecause SANA identifies and prev ents known attac ks as well as SANA identifies infected no des through the tasks p erformed by differen t artificial cells. E.g. backdoors or running processes are rep orted and remov ed by the system. Multi-Stage Attac k Multi-stage attac ks try to infect nodes or try to gather information while attacking using v arious steps. Eac h step is a sub-attack and can facilitates differen t attack techniques. These attacks are used in order to adapt an attac k tow ards the protection system in the netw ork as w ell as to collect information ab out the deploy ed protection system. The problem of these attac ks is that eac h stage is only a small tasks, whic h is normally not identified as intrusiv e or the task is normal b eha viour of programs - mimicry of normal b eha viour. In the pro cess of m ultiple stages, the attack can b oth collect information as well as find a weak p oint in the net work in order to attack and infect the no de. In order to identify the attack, the differen t stages must b e detected and this information m ust b e merged. Therefore, the artificial cells and other protection components observe the node and identify the differen t stages. This is logged and the other cells and components can read the cen tralised log in a no de. F urthermore using the artificial cell comm unication, the cells exchange contin uously summary status information where the appearance of these stages are included. Th us, the nearby cells - within some hops distance - receive the information ab out the stages and can include this into further w orkflows. Identification and disinfection of successful attacks is similar to the t wo previous attack scenarios. The simulations sho w that SANA identifies and preven ts known m ulti-stage attac ks. Unknown/no vel multi-stage attacks are identified when the stages are similar to known attacks or the infection is found using the c hecking w orkflows. Hac ker A ttack When a human attacks a netw ork is this hack er attack called. Also the emerging class of attacks performed by humans with in ternal informa- tion b elongs to this class. A ttacks p erformed by h umans are harder to identify b ecause the humans b eha v e in eac h situation different as well as unpredictable and adapt the at- tac k to the current situation in the netw ork. Ho wev er, different tasks are alw ays presen t when an intrusion is installed and SANA tries to find these characteris- tics. Therefore SANA observes the node as well as the net work traffic in order to iden tify intrusiv e b ehaviour. Additionally to common used protection systems, SANA combines using the artificial cell communication and the mov ement of cells information from different no des. The simulations sho w that esp ecially bac kdo ors e.g. installed b y hac kers are quic kly found by c hecking cells as w ell as intrusiv e b ehaviour is identified on sev eral no des and rep orted to the administration. A ttacks using encrypted VPN T raffic Curren t net works facilitate virtual priv ate netw orks (VPNs) in order to include external nodes into the system or to safely connect external services in to the net w ork. Normally , the VPNs build up a tunnel b et ween tw o no des where the traffic o ver the tunnel is mostly encrypted e.g. with IPsec. The problem for the protection system is that the traffic is encrypted and can b e only chec k ed on the tw o no des of the tunnel where one no de is mostly external. Thus, centralised protection comp onen ts present in the net work - e.g. the in trusion detection system at the internet gatew ay - cannot c heck the netw ork traffic due to its encryption. SANA protects the netw ork against the attac ks using the encrypted VPN tunnel b ecause it chec ks the netw ork traffic with the distributed intrusion de- tection system from the artificial cells at least at the in ternal no de of the VPN tunnel. When b oth no des use SANA as protection system, b oth no des chec k the traffic using the artificial cells. In addition, the node is observ ed so that the installation of an in trusion is detected as well as preven te d. Additionally , regular c hecks are p erformed so that the no des are c heck ed for infections. Our simulations sho w that SANA iden tifies the attacks, which use the VPN for attacks. In addition, the self management mak es it feasible to increase the concen tration of cells in these no des b ecause a VPN tunnel is also a risk for the net work. 4.4 Dynamic and Adaptiv e Beha viour The dynamic behaviour featured b y the artificial cells is crucial for the perfor- mance of SANA. The artificial cells mo ve and the self management ensures that eac h no de is prop erly secured. Thus, an attack er do es not alwa ys find the same configuration of the protection system and cannot b e sure to use a backdoor for further attacks. The system additionally adapts to the curren t situation. Hotsp ots of attacks are iden tified and the concentration of artificial cells in this area is increased in order to pro vide more security . The collab oration betw een the artificial cells enables the combination of information gathered in different protection pro cesses. SANA also adapts through analysing infections and au- tonomous generation of signatures in order to iden tify the intrusion afterw ards. These p oints increase the p erformance and are not av ailable in most common used protection comp onen ts. 4.5 Distributed In trusion Detection System The artificial cells for chec king netw ork pack ets implement a distributed intru- sion detection system. These cells run on all no des and ev aluate the pac kets whether they contain an in trusion or not. The generated warnings and alerts are b oth sent to the administrations and pro cessed automatically . With the righ t configuration, which is guaran teed through the self management, eac h pack et is c heck ed against all known in trusions. E.g. in all netw orks each pack et trav els at least three hops: sender, netw ork equipment, and receiver. Thus, each hop must only c heck the pac ket against 33% of all kno wn intrusions. When the net work traffic is analysed, it can b e seen that in most netw orks the pack ets trav erse mostly ab out ten hops and the configuration can be adapted to this. Also, the self managemen t can configure the system according to the normal routing paths as well as to the routing in the netw ork. The distributed intrusion detection system installed through the artificial cells works in the sim ulations well and identifies reliably the in trusions. F urther- more, the problem of pack et loss [33] of current cen tralised approaches is solv ed b ecause the dataset of known intrusions in a no de is significantly reduced. 4.6 Securit y in SANA The distributed protection system SANA can b e a risk for the netw ork. When SANA is not prop erly secured, adv ersaries can use the system in order to run attac ks, e.g. through propagating intrusions as artificial cells. Also, the artificial cells can access critical resources, which are also of sp ecial interest for an attack er. This m ust b e preven ted through a prop er securing of the protection system and its comp onen ts. Section 3.4 in tro duces the artificial receptors as a public priv ate key pair describing the type and status of all comp onen ts in SANA, esp ecially from the artificial cells. These keys are extended to a distributed public key infrastructure: eac h resource is secured using some keys and the artificial cells hav e to authorise with the righ t keys in order to receive access. Th us, unauthorised cells cannot access the important resources. Artificial cells in tro duced b y attac kers - so called bad artificial cells - receive no access to the resources b ecause they lack from ha ving the right receptors. This approach leads to the next problem that the attack ers cannot receive access to the keys of the artificial receptors. Therefore, the implementation of the securit y environmen t is imp ortan t, which is introduced in section 3.7 and visualised in figure 2. The system is organised in three parts: the hardware and the core parts of the op erating system (op erating system lay er 1), the SANA securit y environmen t with the protection comp onents, and the operating system with the applications softw are. The question is, whic h information can b e read b y the adversarial when occupying the node: – When an in trusion installs something in the operating system lay er 1, SANA uninstalls itself immediately from this no de and quaran tines the no de through informing the neigh b ours. Thus, the intrusion has no change to receive in- formation ab out the keys. Afterw ards, the administrators hav e to chec k the no de and bring it back to production through inserting it in the netw ork. – Most in trusion attac k the Windows op erating system, whic h is only a v ailable in the operating system part of the security en vironment. Using the hardw are virtualisation, it is imp ossible to access the securit y en vironment and to access the keys. When the intrusion tries to break out, it has to change the op erating system lay er 1, which is discussed in the last p oint. – The most critical problem is an installation of an in trusion in the security en vironment. An arriving intrusiv e protection component is identified and re- mo ved. When an intrusion installs itself in the environmen t, integrit y chec ks recognise this and the intrusion is identified and prev ented. Due to the small size and limited features can the en vironment safely installed so that in tru- sions cannot attack it. Different techniques are e.g. formal verification and in tegrity chec ks. T o sum up, it is hard for an adversarial to use SANA for running attac ks. In addition, self chec king by other protection comp onents and esp ecially artificial cells identify not prop er working comp onen ts quic kly and remov e them from pro duction. 5 Next Steps There are lots of op en problems and next steps in the SANA pro ject. One im- p ortan t next step is to intensiv e the research in the co operation b et ween the differen t artificial cells. Therefore, the goal is to use the danger theory for the collab oration b et ween differen t protection comp onen ts in SANA. In the implementation, the idea of using hardw are virtualisation for imple- men ting is not enough researched. Here, the next step is to analyse the required o verhead as w ell as to introduce the service orien ted architecture in detail in order to analyse the no vel features emerging out of this arc hitecture. F urthermore, to extend the library of implemented protection comp onents e.g. with honeyp orts is a next step in order to include more approaches of netw ork securit y . With the extensions, SANA is tested against more intrusions and a testb ed is built up where SANA protects a real netw ork against real attacks. 6 Conclusion As it was describ ed, the protection system SANA outperforms curren t protection systems. An intelligen t administration and a distributed arc hitecture with a standardised protection environmen t increases its p erformance. The distributed and dynamic framework makes it hard to attack and to break it completely do wn. The system is easily update and extendable where also the administration is simplified so that the system is quickly adapted to the current situation in the net work. Ac kno wledgments SANA is currently implemented at the Universit y of Luxem b ourg in the F aculty of Science, T echnology , and Communication. W e thank Ulrich Sorger, Zdzislaw Suc hanecki, and F oued Melakessou from the Univ ersity of Luxembourg for help- ful discussions and the Ministre Luxembourgeois de l’education et de la rec herche for additional financial supp ort. References 1. CSI, FBI: 2004 computer crime and security survey (2004) 2. Scalet, S.D.: Pullig threads on e-crime. cso-magazine, july 2005. h ttp://www.cso online.com/info/ecrimesurvey05.pdf (05.06.2007) 3. Sean Conv ery , C.S.: Net work Security Architectures. (Netw orking T echnology). Second edn. Macmillan T echnical Publishing (2004) 4. Dhanjani, N., Clark e, J.: Netw ork Securit y T o ols. First edn. O’Reilly Media (2005) 5. Ro esc h, M.: Snort - ligh tw eight intrusion detection for netw orks. LISA 13 (1999) 229–238 6. Debar, H., Dacier, M., W espi, A.: T o wards a taxonomy of intrusion-detection systems. Comput. Netw orks 31 (9) (1999) 805–822 7. F errie, P ., Szor, P .: Zmist opportunities, virus bulletin, h ttp://pferrie.trip o d.com/papers/zmist.p df (March 2001) 8. Szor, P ., F errie, P .: Hunting for metamorphic, symantec securit y response white pa- p er, http://www.syman tec.com/a vcen ter/reference/hun ting.for.metamorphic.p df (July 2000) 9. Aic kelin, U., Greensmith, J., Twycross, J.: Imm une system approac hes to intrusion detection - a review. Pro ceedings of the 3rd International Conference on Artificial Imm une Systems (ICARIS 2004) (2004) 10. DeCastro, L.N., Timmis, J.: Artificial Imm une Systems: A New Computational In telligence Approach. First edn. Springer (2002) 11. Hofmeyr, S.A., F orrest, S.: Imm unity by design: An artificial immune system. Pro ceedings of the Genetic and Evolutionary Computation Conference 2 (1999) 1289–1296 12. Hofmeyr, S.A., F orrest, S.: Architecture for an artificial immune system. Ev olu- tionary Computation 8 (4) (2000) 443–473 13. Janew ay , C.A., T rav ers, P ., W alp ort, M., Shlomchik, M.: Imm unobiology: the Imm une System in Health and Disease. Sixth edn. Garland Publishing (2004) 14. V argas, P .A., de Castro, L., von Zub en, F.: Artificial immune systems as complex adaptiv e systems. In: Pro ceedings of the 1st International Conference on Artificial Imm une Systems (ICARIS). V olume 1. (2002) 115–123 15. Hilk er, M., Sc hommer, C.: Sana - securit y analysis in in ternet traffic through artificial immune systems. Proceedings of the T rustw orthy Softw are W orkshop, Saarbruec ken, Germany (2006) 16. Mikusi, J.: Op en source an ti-virus for the whole netw ork: Clamav. h ttp://www.samag.com/do cuments/s=9464/sam0501a/0501a.h tm (2005) 17. Ran um, M.J.: A net work firew all. In: Pro ceedings of the First W orld Conference on System Administration and Security , 5401 W estbard Av e. Suite 1501, Bethesda, MD 20816, SANS Institute (1992) 18. McCanne, S., Jacobson, V.: The BSD pac ket filter: A new arc hitecture for user- lev el pack et capture. In: USENIX Winter. (1993) 259–270 19. Xinidis, K., Anagnostakis, K.G., Mark atos, E.P .: Design and implementation of a high-p erformance netw ork intrusion preven tion system. In: SEC, Springer (2005) 20. Duane DeCapite, C.S.: Self-Defending Netw orks. The Next Generation of Netw ork Securit y . First edn. Macmillan T echnical Publishing (2006) 21. Bellifemine, F., Poggi, A., Rimassa, G.: JADE - a FIP A-compliant agen t frame- w ork. In: Pro ceedings of the Practical Applications of Intelligen t Agen ts. (1999) 22. SWsoft: Op en vz user’s guide, v ersion, 2.7.0-8, link: h ttp://download.openvz.org/doc/op envz-users-guide.pdf. (23.05.2007) 23. Williamson, M.M.: Throttling viruses: Restricting propagation to defeat malicious mobile co de. In: ACSA C ’02: Pro ceedings of the 18th Annual Computer Security Applications Conference, W ashington, DC, USA, IEEE Computer So ciet y (2002) 24. Williamson, M.M.: Design, implemen tation and test of an email virus throttle. In: ACSA C ’03: Pro ceedings of the 19th Annual Computer Security Applications Conference, W ashington, DC, USA, IEEE Computer So ciety (2003) 76 25. Neuhaus, S., Zeller, A.: Isolating in trusions b y automatic exp erimen ts. In: Pro- ceedings of the 13th Annual Net work and Distributed System Securit y Symposium, Reston, V A, USA, Internet So ciet y (2006) 71–80 26. Greensmith, J., Aick elin, U., Cayzer, S.: In tro ducing dendritic cells as a nov el imm une-inspired algorithm for anomaly detection. Proceedings of the 4th Inter- national Conference on Artificial Immune Systems (ICARIS 2005) (2005) 27. Hilk er, M., Schommer, C.: Agnosco - identification of infected no des with artificial an t colonies. Pro ceedings of RASC (2006) 28. Hilk er, M., Schommer, C.: Description of bad-signatures for netw ork intrusion detection. AISW-NetSec 2006 during ACSW 2006, CRPIT 54 (2006) 29. Sc hro eder, B., Hilk er, M., W eires, R.: Dynamic association net works in information managemen t. In: Pro ceedings of the 4th International Conference on Machine Learning and Data Analysis (MLDA 2007). (2007) 30. Aalst, W.M.P .v.d., Beisiegel, M., Hee, K.M.v., K¨ onig, D., Stahl, C.: A SO A- Based Architecture F ramework. In Leymann, F., Reisig, W., Thatte, S.R., Aalst, W.M.P .v.d., eds.: The Role of Business Pro cesses in Service Oriented Arc hitectures. Num b er 06291 in Dagstuhl Seminar Proceedings (2006) 31. Aic kelin, U., Bentley , P ., Cayzer, S., Kim, J., McLeo d, J.: Danger theory: The link b et ween ais and ids? In: Proceedings of the Second International Conference on Artificial Imm une Systems (ICARIS 2003). LNCS 2787, pp. 147-155, Edinburgh, UK (2003) 32. Matzinger, P .: The danger model a renew ed sense of self. Science 296 (5566) (2002) 301–305 33. Sc haelick e, L., F reeland, J.C.: Characterizing sources and remedies for pack et loss in netw ork intrusion detection systems. In: Pro ceedings of the 2005 IEEE In ternational Symposium on W orkload Characterization, IEEE CS Press (2005) 188–196
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment