Distributed Self Management for Distributed Security Systems
Distributed system as e.g. artificial immune systems, complex adaptive systems, or multi-agent systems are widely used in Computer Science, e.g. for network security, optimisations, or simulations. In these systems, small entities move through the ne…
Authors: Michael Hilker
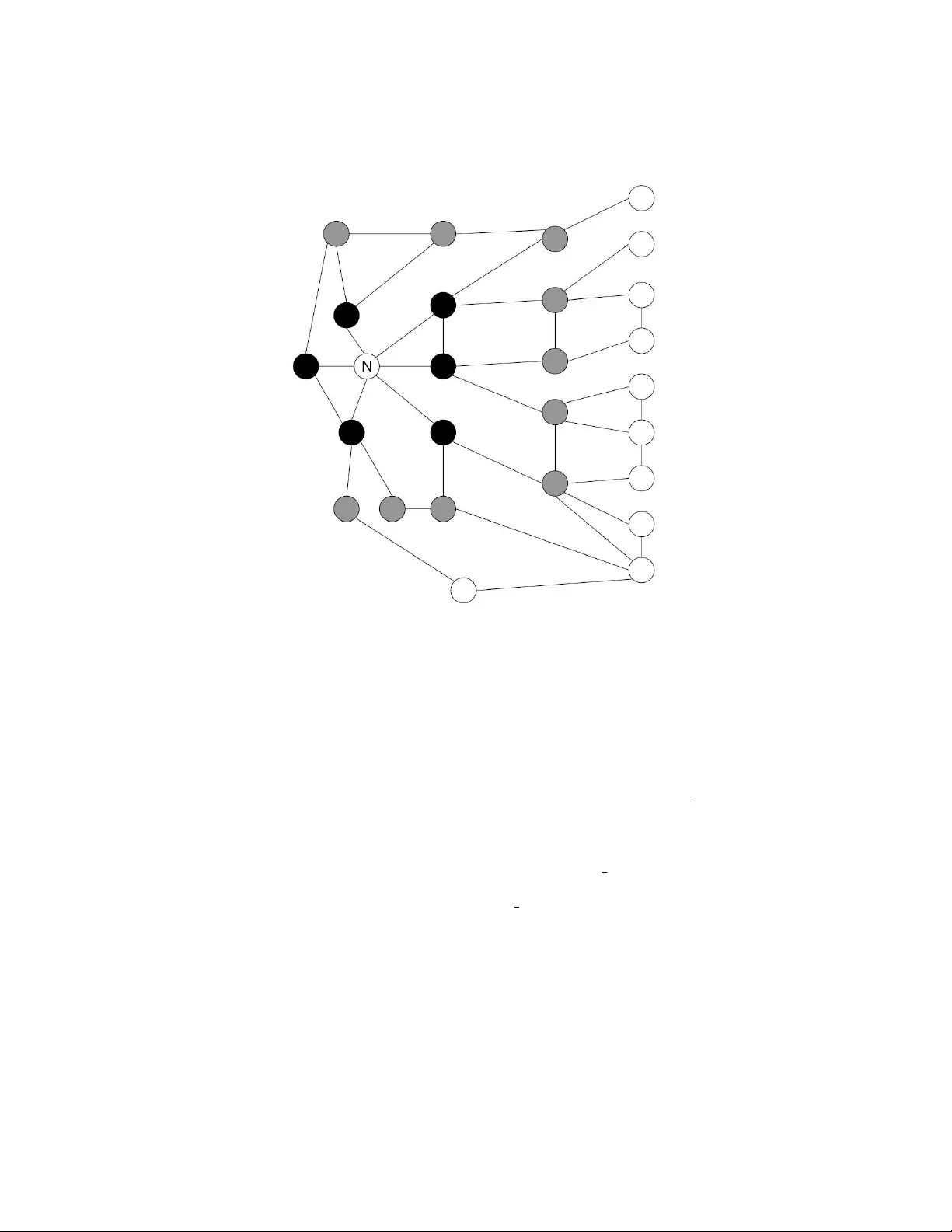
Distributed Self Managemen t for Distributed Securit y Systems Mic hael Hilk er Univ ersity of Luxembourg F acult y of Science, T ec hnology , and Comm unications 6, Rue Richard Coudenho ve-Kalergi, L-1359 Luxembourg michael.hilker@uni.lu Abstract. Distributed system as e.g. artificial immune systems, com- plex adaptiv e systems, or m ulti-agent systems are widely used in Com- puter Science, e.g. for net work security , optimisations, or sim ulations. In these systems, small entities mo ve through the net work and p erform cer- tain tasks. A t some time, the entities mov e to another place and require therefore information where to mov e is most profitable. Common used systems do not pro vide an y information or use a centralised approach where a cen ter delegates the entities. This article discusses whether small information ab out the neigh b ours enhances the p erformance of the o ver- all system or not. Therefore, t wo information-proto cols are introduced and analysed. In addition, the protocols are implemen ted and tested us- ing the artificial immune system SANA that protects a net work against in trusions. 1 In tro duction Distributed systems are widely used in computer science in order to solv e prob- lems distributed on several no des. E xamples are simulation or optimisation prob- lems, whic h run on several no des in parallel or the netw ork security where a net work is secured against in trusion like e.g. viruses, worms, and tro jans. These distributed systems are e.g. multi-agen t systems [1], complex adaptive systems [2], and artificial imm une systems [3,4,5]. These systems use small en tities - e.g. agen ts or artificial cells - that mo ve through the netw ork, perform certain tasks for netw ork securit y , and work mostly autonomously . These entities receiv e lo cal information ab out the situation in the netw ork and contain a limited knowledge ab out the ov erall goal - here secure a netw ork against intrusions. An example is that an entit y knows how to iden tify one certain intrusion and receiv es the status of the no de where the en tity resides [6]. The p erformance of the ov erall systems originates from the p erformance of all the small entities, which leads to w aste of computational pow er and decreased p erformance of the o verall system when the entities are not properly distributed o v er all nodes. A k ey problem in the distributed systems is that the entities work au- tonomously and ha ve to decide in some timestep whether they mo ve to another no de and if yes to which no de - this problem is part of the self-management of a distributed system. This problem is significan t because the distributed security system should secure the whole net work and all nodes should hav e at least a cer- tain n um b er of entities. This article discusses whether exc hanging a small piece of information ab out the nearby situation increases the p erformance of the secu- rit y system or not - lo cal information ab out a no de with some additional global information ab out the nearby region of the net w ork. Therefore, tw o information proto cols describing how and which information is exc hanged are introduced. Thereafter, the t wo approaches are implemen ted in an artificial imm une system that uses autonomous artificial cells in order to secure a netw ork against in tru- sions. Lastly , some discussions ab out the test results and the analysis conclude the paper. The domain of the application is net work security . It describ es the research in order to secure a net work against in trusions. In trusions are e.g. viruses, worms, and tro jans. There are several approac hes in order to secure a netw ork against in trusions, e.g. antivirus soft ware, pac k et filters, and intrusion detection systems [7]. Most of these common used security systems lack from the lo cal installation b ecause then they only secure one net work no de and require lots of compu- tational p ow er to c heck the whole net work traffic. F urthermore, the securit y solutions for a netw ork consist of sev eral systems, e.g. an tivirus soft w are in each no de, pack et filters in eac h router, and in trusion detection systems at the internet gatew ay and email server. Ho wev er, these systems are not connected and do not w ork together. In order to protect a netw ork against the up coming intrusions, a more sophisticated approac h is required where an example are the distributed systems. Thus, a distributed approac h is c hosen in the artificial imm une system SANA [4] where artificial cells p erform the required tasks and build up a dis- tributed in trusion detection system. These cells - the entities - mo ve through the net work and require the information where to roam next. The next section in tro- duces the existing approaches for sharing mov ement information in distributed systems. 2 Curren t situation Curren tly , there are t w o differen t approac hes in order to manage the mo vemen t of the entities in a distributed system: 1. The en tities do not work fully autonomously . A centralised system, whic h kno ws the situation of the whole netw ork, delegates the en tities - mostly agen ts - to their destinations. Thus, the system is again dep enden t on a cen tralised system, which is also a single point of failure and is a con tradiction to the idea of a distributed system. 2. When the entities work fully autonomously , in most systems they receive no information when and where to mov e. The mo vemen t is normally modelled using some probabilistic ev ents with a distribution ov er all neighbour no des. Both systems hav e significant disadv an tages. The centralised approach re- quires lots of bandwidth b ecause the center needs information from all ov er the 2 net work and the center is a single point of failure. The distributed approach reduces the bandwidth significantly but it is p ossible that the entities mo ve to inappropriate no des where e.g., some no des hav e to o many entities and other no des suffer from the low num ber of entities. Consequently , this article discusses ho w small pieces of information can help the en tities to do the right decision. 3 Information Managemen t and Proto cols F or inv estigating research in the information management, the follo wing situa- tion in the net work is assumed: An artificial immune system [4] with lots of artificial cells - the entities - pro- tects a netw ork against intrusions [6]. Therefore, a t yp e of artificial cell kno ws ho w to detect and remo ve exactly one intrusion where there are several instances of this t yp e of artificial cells, cp. the immune cells in the human immune sys- tem [8]. The whole system do es not con tain any centralised system and the artificial cells decide autonomously when and where to mov e. The artificial im- m une system presents each pack et to all artificial cells in this no de and the cells decide whether the pack et contains an intrusion or not. These cells should be distributed ov er all no des so that each no de contains approximately the same n umber of cells. In addition, the artificial immune system contains artificial cells that mov e through the netw ork and c heck the no des whether they are infected b y an in trusion or not; e.g. in lo oking for bac kdo ors or significant files and pro- cesses on the no de. These artificial cells require the information where to go b ecause the c hecks should be done uniformly in time distributed ov er all nodes; this means that each no de is chec ked regularly but not to o often. This prob- lem is the same as the general problem of the en tities mo ving to another no de. The artificial cells are the entities and the infrastructure provides the required resources for enabling the information management. F or the first problem - the mov emen t of artificial cells that chec k pack ets - the notification of insufficient security is in tro duced and for the second problem - the mov ement of artificial cells that chec k no des - the trails of entities is intro- duced. In both approaches, the required resources m ust b e limited. In the first approac h, only one net work pac ket is at most required for eac h connection in the net work. The second approach requires only some storage in the net work no des that dep ends on the n umber of differen t types of artificial cells. F urthermore, the artificial cells receive some small pieces of information and, henceforth, do not increase that m uch in size and complexity . 3.1 Notification of insufficien t Security In this approach, the problem of entities that c heck pac kets is discussed [9]. In general, this approac h can be used for all en tities, whic h p erform regularly cer- tain tasks and which are required in lots of nodes of the net work. The approach is motiv ated by the cytokines and hormones of the h umen immune system reg- ulating the immune resp onse and its immune cells motiv ate this approach [8]. 3 Fig. 1. Distribution of Notification: The no de mark ed with N has an insufficient securit y level and notifies this to its neighbours. The receiving time of this in- formation is indicated using the colour of the nodes where the more black the earlier the information arrives. The no des without a colour do not receive the information because they are to o far aw ay . F or detecting that a node n has an insufficien t n umber of en tities, it has a pa- rameter that represen ts the minimum num ber of required securit y min sec node . Eac h entit y returns on demand how man y security it provides: sec entity . The no de n asks every time step all en tities residing in this node ho w man y security eac h en tity pro vides and sums this up: sec time = P e ∈ entity node sec e ; a weigh ted sum for a more sophisticated calculation can be also used. If the securit y in this time step is b elow the required securit y min sec n > sec time , the node n starts a notification pro cess in order to allure nearb y en tities. This notification works as follo ws: 1. Using local comm unication, the node informs th e en tities that are w orking in this no de ab out the insufficient security lev el. These entities are then more affine to sta y than to mov e. Ho wev er, the entities are not forced to sta y , they still decide on their o wn. 4 2. The node furthermore sends a netw ork pac ket to all neighbours that indicate the lo w securit y lev el and the pac ket also describ es the missing lev el. 3. The nodes receiving this pack et forw ards it to all entities working in these no des. These entities then get more affine to mov e to this node than to stay or to mo ve to another no de. The change of the affinity is dep endent on the lev el of lac king securit y that is stored in the pac ket. 4. With this w orkflow, eac h no de maybe receives eac h time step sev eral pac kets describing insufficien t security lev els of several no des. Therefore, the no de will forw ard only the pac ket with the highest missing securit y lev el. 5. In order to receive a global notification, each no de forwards these notifica- tion pack ets to their neighbours. The v alue describing the missing v alue is therefore decreased by a decreasing function f d and if the v alue is still ab ov e a threshold, the pack et is forw arded to all neighbours with the decreased v alue. 6. The notification ab out insufficien t securit y in a no de is not stored. The distribution of the information that a node has insufficien t securit y lev el is visualised in figure 1. The en tities - here artificial cells - react to this information as follo ws. Eac h en tity has a function f m that describes the probability that it mov es to an- other no de. Another function f w describ es where the en tity mo ves next. These functions can ha ve sev eral parameters as the time the entit y did not mov e, the net work load, and lac king securit y level. Therefore, eac h time step a probabilistic ev ent is done that succeeds with probability f m and if this even t succeeds a sec- ond probabilistic even t using f w describ es the no de where the entit y will mo v e. When the entit y receives a notification that a no de has an insufficient v alue, the function f m will b e increased in order to increase the affinity to mov e and the second function f w is so changed that the entit y will alw ays mov e tow ards the no de with insufficient security . The function f m is visualised in figure 2. This approach is implemen ted in the artificial immune system SANA that is dev elop ed at the Universit y of Luxembourg for the purp ose of net w ork securit y (section 6). Each no de with low securit y level sends the notification each time step and the en tities react to it. In the simulations, the functions are set as follo ws: – min sec node is set to 20 where there are 60 different t yp es of artificial cells in the artificial imm une system – sec entity is the num b er of known intrusions, mostly 1 – the decreasing function f d is set to old v al ue − 1 – if a no de has an insufficien t security level the artificial cells in this no de will not lea v e it – the mo v ement function f m is sho wn in figure 2 – the where to mov e function f w is only used if there is not an y notification, otherwise the entities mov e to wards this node 5 Fig. 2. Response function f m of an entit y: f m (0) describ e the normal affinity to mo ve; f m ( x ) describ es the mo ving probability when lac king security x is received; maxim um limits response to preven t o verreaction. 3.2 T rails of Entities This approach pro vides information to entities p erforming regular chec ks in no des as identifying infected no des. In general, the approach can b e used for en tities p erforming a tasks that must b e done regularly but not to o often in a no de. Therefore, an approach is used that is motiv ated b y artificial an t colonies [10]. Eac h no de n contains storage for each outgoing connection ( v , w ). In this storage, for eac h t yp e of entit y e is a v alue stored v v ,w ,e that describ es when the last chec k took place. When an entit y do es a chec k in the no de and mo ves to the next no de, it increases this v alue v v ,w ,e and every time step the no de decreases this v alue v v ,w ,e un til it reaches zero. The entities in this no de use this information in order to ev aluate where to mo ve next. Assume the following situation: an entit y is in no de n and finishes the chec k. The next step is to mov e to another no de and the entit y receives information when an en tity of the same t yp e mov es to the neigh b ours, i.e. the v alues v v ,w ,e for eac h ( v, w ) in n for type e . Then, it uses this information for a probabilistic ev ent where the P r (mo ve to neighbour n i ) depends on the v alue that describes when the node n i w as lastly chec k ed. In addition, the v alue is not a coun ting of time steps. F or the increasing of the v alue is a function f i and for the decrease a function f d used. Then it is p ossible to when the last c heck did place at the neigh b ouring no de as well as how often in the past the no de was c heck ed by this t yp e of artificial cell. An example of f i is discussed in figure 3. This approach is also implemen ted in the artificial immune system where the storage uses float-v alues. The increasing function f i is set to c 1 + c 2 · exp ( old v al ue ) with c 1 and c 2 as a constant v alue, e.g. c 1 = 10 and c 2 = 1 1000 . The decreasing 6 function f d is set to ol d v al ue − c 3 where c 3 is a constan t v alue, e.g. 2. Th us, the v alue increases exp onen tially and decreases linearly . The probabilistic even t sets the probability for each no de dep enden t on the required security in the neigh b our no des. 4 T esting Results As already explained, the tw o techniques are implemented in an artificial im- m une system. The simulations are done using a net work sim ulator implemen ting a pack et-switching netw ork. The netw ork is a compan y-like netw ork with ab out 500 no des with different server, workstations, and services. An Internet gatewa y connects the net work to the Internet and different in trusions are implemented, whic h are mostly viruses, worms, and tro jans arriving ov er the netw ork or di- rectly by internal attacks. The results are discussed in the next tw o subsections: 4.1 Notification of insufficien t Security The notification of insufficient security w orks more than acceptable. When the parameters and functions are chosen properly , the system adapts quickly so that no des with insufficient security receive artificial cells quickly . F urthermore, the system do es not ov erreact which means that the artificial cells react to o hea vily and all cells mov e immediately to a no de with insufficient security . Then, the alternating status is preven ted: this means that all cells oscillate b etw een t wo no des because one of these t wo no des has alw a ys an insufficien t securit y lev el. The required resources are limited. F or each connection is exactly one net- w ork pack et for each time step used. The required computational p o wer is also limited b ecause the pro cessing of the information is quite fast. The p erformance increase of the artificial imm une system is observ ed. The performance with no- tification of insufficient security levels is significant higher than in the v ersion without enabled notification. F or example in one scenario, ab out 80% of the in trusions are iden tifies without the usage of the notification system; this low v alue occurs because some no des ha v e too muc h and some nodes too few artificial cells. When the notification system is e nabled, the system iden tifies ab out 98% of the intrusions b ecause all nodes ha v e a guaran teed securit y v alue. Compared to the centralised approac h with an en tity managemen t server, the notification of insufficien t security requires ab out 80% less bandwidth and the performance increases b y 15% due to the quick er adaption to w eak p oin ts in the netw ork. The reason for this is that the system quickly solv es securit y problems and the attac kers cannot use no des with insufficien t securit y in order to install in trusions. Additionally , the system distributes the artificial cells in a b etter wa y . If there is a no de with to o many artificial cells that requires to o muc h computational p ow er, there are also nodes with insufficient security and the artificial cells will solv e this problem using the information. F urthermore, it is p ossible to adapt the system to the current situation using changes of the parameters. In addition, imp ortant no des are secured with more entities, whic h is configured through changes in the notification system. 7 Fig. 3. T rails: an en tity in the left no de w ants to mo ve, reads therefore the trails, and receiv es the v alues indicating the trail. Thereafter, it mak es a probabilistic ev ent where it c ho oses uniformly a num b er from [1 , 289]. If the num b er is in [1 , 100] it mov es to the node with trail v alue 1. Else, if the n umber is in [101 , 197], it mov es to the no de with trail v alue 5. Else, if the num b er is in [198 , 288], it mo ves to the no de with trail v alue 10. Else, if the num b er is 289, it mov es to the no de with trail v alue 100. This probabilistic even t reflects the trail v alues of the neigh b ouring no des. 4.2 T rails of Entities The trails of entities work well. The system pro vides information to the entities where their tasks are required and the entities mo ve there. The entities also sa ve computational p ow er because b et ween tw o chec ks is a certain time p erio d. In our simulations, without the trails only ab out 70% of the no des are chec k ed and some no des are very often c heck ed ab out every second time-step. With the trails systems, all no des are regularly chec k ed and to o often chec ks are successfully prev ented where the required computational p o wer is reduced b y 60%. Unfortunately , when the netw ork is fragmented in sev eral parts and these parts are connected b y a few connections, the trails of en tities do not work prop erly . The reason for this is that many en tities must use these connections, they receiv e a high v alue, and the probabilit y to mov e ov er these connections is reduced. F ortunately , this problem can b e solved in using other functions in these no des: one solution is to use a decreasing function with a significant higher gradien t or to not use the trails in this node, which results to a probabilit y of 1 # neig hbour s for all neighbours. 5 Analysis In the analysis of the tw o techniques, the fo cus lays on the question how the selected information helps the entities and what other information might be 8 in teresting. In addition, the required resources are analysed and a balancing b e- t ween these tw o parameters are done. Definition: Lo cal information comes from the netw ork no de and is not sent ov er the netw ork. Global information describ es the situation in another no de and is sen t o ver the netw ork. Question: Are the information locally or globally? In the notification of insufficien t security , the information is local and global b ecause the en tities receive the information from the neigh bouring nodes directly and using forwarding from no des that are nearby . Ho wev er, using feasible pa- rameters, the entities do not receive information ab out insufficient security in no des that are far aw a y . The reason for this is that if they receive information ab out all no des with insufficien t security , the required resources are equal to the cen tralised approaches. Using the parameters, it is p ossible to trade off the prop ortion b etw een the required bandwidth and the distance where information are forw arded. In the trails of entities, the information is lo cally . There is no exchange b e- t ween the no des ab out this information and the entities receiv e only the infor- mation of a no de. Question: Does information that is more global increase the p erformance? In the notification of insufficien t securit y , using the parameters it is p ossible to choose b etw een required bandwidth and global information. How ever, when the system is so configured that the cells receive information ab out all no des with insufficien t security , the en tities receive to o man y information and will tra vel to o often through the netw ork. F urthermore, it is uninteresting that an en tit y mov es through the whole net work only to fix a problem at a far-aw a y no de. Then it is more interesting to solve the problem in the area around the no de where only lo calised information is required. The tests sho wed that a lo cal setting with a distribution of some hops results in the b est p erformance and limits the bandwidth greatly . In addition, the distribution area of the notification dep ends on the missing security v alue: the bigger the missing security lev el, the greater is the distribution area, whic h is a more adaptiv e approac h. In the trails of entities, some global information would increase the p erfor- mance. Esp ecially in the situation explained in the last section that connections with high load will not b e trav ersed by en tities, a view to other no des would mak e the decision of an en tity where to mov e more sophisticated. Then, the en- tities w ould receiv e a more global view ab out the nearby netw ork. Ho wev er, then the system m ust in vest more bandwidth and the selection whic h information to store in which no de is quite difficult. Question: Whic h other information are in teresting to use for these tw o problems? F or the proto col of notification of insufficien t security , it would be interesting to kno w how man y artificial cells are on the wa y tow ards this no de. F urthermore 9 it would b e in teresting to receiv e information ab out more than one no de so that the system do es not only adapt to the no de which has the highest v alue of lac king securit y v alue. Ho wev er, both w ould implicate lots of bandwidth and high storage space for sa ving the information. F urthermore, the w orkflow in the en tities w ould b e more complex. F or the proto col of trails of entities, it would be interesting to receive infor- mation ab out a part of a net work and not only from the neigh b ours of this no de. Ho wev er, this would again increase the required bandwidth and storage space. Question: Whic h other problems o ccur in the self-management of a distributed securit y system? In the notification of insufficient security , the follo wing questions are also of in terest: – Whic h no de has to o man y en tities. T o o man y en tities is defined so that the resources - mainly computational p ow er - is not sufficien t with the required resources from all entities. It is highly interesting that these entities mo ve to the nodes with insufficien t security lev el in order to balance the system. – Is it p ossible to design moving chains where several entities mov e from no de to no de and after one time step all no des hav e a sufficient security level? If y es, which information is required so that all entities can initiate this mo ving? F or the trails of entities, the follo wing questions are also in teresting: – Ho w to use these trails so that not too man y chec ks are p erformed on a no de? If to o many c hecks are p erformed simultaneous, the no de has to in vest to o m uch computational p ow er. – Is it maybe p ossible to use these trails in order to find no des that are con- trolled by an intrusion in absorbing cells? The problem in distributed security systems is that an attack er o ccupies a no de and has access to the security systems. Then, the attack er can remov e all incoming entities and after some time the system will lac k of to o few entities. The system can analyse the trail v alues in the no des that are nearby the infected no de and ma yb e there are association betw een an o ccupied no de and trail v alues. These questions will b e the challenges for the future researc h in distributed self managemen t of distributed securit y systems. 6 Applications Curren tly , the information management is used in the artificial immune system SANA, which protects a netw ork against intrusions [9,11]. Therefore, SANA fa- cilitates lots of small artificial cells performing autonomously the tasks required for netw ork security - the organic computing approac h. Common used secu- rit y comp onen ts lik e an tivirus softw ares, firewalls, pack et filters, and intrusion detection systems complemen t the system to b enefit from their performance. 10 The artificial cell comm unication enables the collab oration b etw een the different artificial cells where the infrastructure supplies the cells with additional informa- tion. The artificial lymph no des implement a meeting and resp onse p oint for a small part of the netw ork and the central nativit y and training stations generate and release con tin uously no v el artificial cells including the newest security tech- niques. With the sp ecialised artificial cells is it p ossible to implemen t nearly all approac hes of netw ork security . The in this article introduced self management organises the cells so that the system is alw ays prop erly secured and there is no w eak p oint in the netw ork. The information managemen t is more sophisticated implemen ted where the security components and artificial cells exc hange con- tin uously status information in order to adapt the o verall system and internal thresholds as well as parameters - implementation of the danger theory [12] and the tunable activ ation threshold [13] of the immune cells. F or the resp onse when an intrusion is found, the comp onents dev elop a defense strategy and p erform this or quaran tine the no de with informing the administrator for further tasks. Main tenance - updates, extensions, and regular self-chec ks - are p erformed by the system using specialised cells where the main tenance is automated and not prop er working as w ell as outdated comp onents are rep orted to the administra- tor. How ever, the administrator is able to access and configure all no des and comp onen ts of the system through an administration GUI. Infected no des are iden tified through regular c hec ks as well as through distributed analysis of data gathered b y v arious security components, i.e. the distributed analysis of net w ork pac kets through intrusion detection systems and artificial cells [6]. Due tos the usage of common used comp onents, the p erformance is at least as go o d as of common used securit y systems. Due to the dynamic artificial cells is the system hard to predict and to attac k, contains no single p oin t of failure, and adapts to the current situation in the netw ork. In addition, a real distributed intru- sion detection system is implemented in all no des with simplified administration w orkflows [9]. F urthermore, the notification of low security can b e used in nearly all dis- tributed systems where the num b er of entities can b e measured and thereafter mo deled using the parameters and functions. The trails can be used in all scenar- ios where a type of entit y should visit all no des regularly but not to o frequen tly . These systems are most distributed systems as the m ulti-agen t systems, the mas- siv ely distributed systems, complex adaptiv e systems, and the artificial immune systems. 7 Conclusion This article discusses t wo information protocols for distributed systems and analyses the p erformance. The t wo proto cols increase the p erformance of a dis- tributed system enormously b ecause the entities receiv e information where their tasks are required. In addition, the required bandwidth is limited b ecause a cen- tralised system is not used. The next steps are to in tro duce more information proto cols and ev aluate theoretically how the p erformance w ould increas e when 11 more bandwidth is inv ested. F urthermore, the enhancing of the distributed se- curit y systems that base on the artificial imm une system as archet ype is a next step. Ac kno wledgments The PhD-Pro ject SANA - Security Analysis in iNternet trAffic - is financially supp orted by the Univ ersit y of Luxembourg. I lik e to thank Christoph Sc hommer for helpful discussions and the Ministre Luxem b ourgeois de l’education et de la rec herche for additional financial supp ort. References 1. Bellifemine, F., Poggi, A., Rimassa, G.: JADE - a FIP A-compliant agen t frame- w ork. In: Proceedings of the Practical Applications of In telligent Agen ts. (1999) 2. V argas, P .A., de Castro, L., v on Zuben, F.: Artificial imm une systems as complex adaptiv e systems. In: Pro ceedings of the 1st In ternational Conference on Artificial Imm une Systems (ICARIS). V olume 1. (2002) 115–123 3. Aic kelin, U., Greensmith, J., Twycross, J.: Immune system approaches to in trusion detection - a review. Pro ceedings of the 3rd In ternational Conference on Artificial Imm une Systems (ICARIS 2004) (2004) 4. Hilk er, M., Sc hommer, C.: Sana - security analysis in internet traffic through artificial immune systems. Pro ceedings of the T rustw orth y Softw are W orkshop, Saarbruec ken, German y (2006) 5. Hofmeyr, S.A., F orrest, S.: Imm unity by design: An artificial imm une system. Pro ceedings of the Genetic and Evolutionary Computation Conference 2 (1999) 1289–1296 6. Hilk er, M., Schommer, C.: Agnosco - identification of infected nodes with artificial an t colonies. Pro ceedings of RASC (2006) 7. Ro esc h, M.: Snort - ligh tw eight in trusion detection for net works. LISA 13 (1999) 229–238 8. Janew ay , C.A., T rav ers, P ., W alp ort, M., Shlomchik, M.: Imm unobiology: the Imm une System in Health and Disease. Sixth edn. Garland Publishing (2004) 9. Hilk er, M., Schommer, C.: Description of bad-signatures for netw ork intrusion detection. AISW-NetSec 2006 during ACSW 2006, CRPIT 54 (2006) 10. Dorigo, M., Maniezzo, V., Colorni, A.: The Ant System: Optimization b y a colon y of co op erating agents. IEEE T ransactions on Systems, Man, and Cybernetics Part B: Cyb ernetics 26 (1) (1996) 29–41 11. Hilk er, M., Sc hommer, C.: Sana - netw ork protection through artificial immunit y . In: Proceedings of the 2nd International W orkshop on Theory of Computer Viruses (TCV 2007). (2007) 12. Aic kelin, U., Bentley , P ., Ca yzer, S., Kim, J., McLeo d, J.: Danger theory: The link b et ween ais and ids? In: Proceedings of the Second In ternational Conference on Artificial Imm une Systems (ICARIS 2003). LNCS 2787, pp. 147-155, Edinburgh, UK (2003) 13. Grossman, Z., Singer, A.: T uning of activ ation thresholds explains flexibility in the selection and developmen t of t cells in the thym us. Pro ceedings of the National Academ y of Sciences 93 (1996) 14747–14752 12
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment