Eliminating Trapping Sets in Low-Density Parity Check Codes by using Tanner Graph Covers
We discuss error floor asympotics and present a method for improving the performance of low-density parity check (LDPC) codes in the high SNR (error floor) region. The method is based on Tanner graph covers that do not have trapping sets from the o…
Authors: Milos Ivkovic Shashi Kiran Chilappagari Bane Vasic
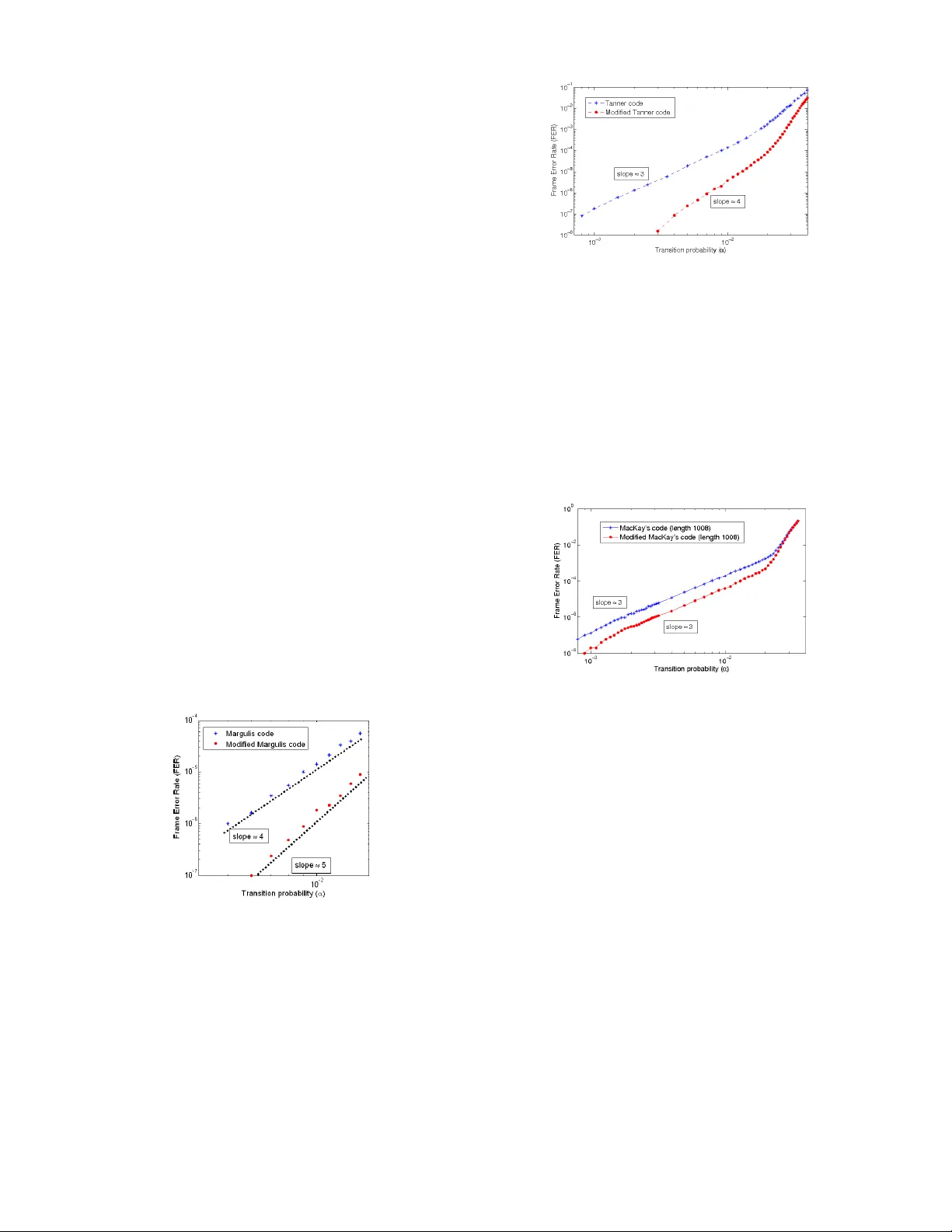
1 Eliminating T rapping Sets in Low-Density Parity Chec k Codes by using T anner Graph Covers Miloˇ s Ivko vi ´ c , Sha shi Kir an Chilappagari and Bane V asi ´ c, F ellow , IEEE Abstract — W e discuss e rror floor asympotics and present a method for impr oving the perfor mance of low-density parity check (LDPC ) codes in the high SNR (err or floor) region. The method is based on T anner graph cover s that do not hav e trapping sets from the original code. The advantage s of the method are that it is univ ersal, as it can be applied to any LDPC code/c hannel/decodi ng algorit hm and it impro ves perfor mance at the expense of incr easing the code length, without losing the code reg ularity , without changing the decoding algorithm, and, under certai n conditions, without lower ing the code rate. The propose d method can be modified to construct con volutional LDPC codes also. The method is illustrat ed by modifyi ng T anner , MacKay and Margulis codes to impr ove perf ormance on the binary symmetri c channel (BSC) under the G allager B decoding algori thm. Decoding results on A WGN channel ar e also prese nted to illustrate that optimizing codes f or one channel/decoding algorit hm can lead to perfo rmance impro veme nt on other channels. Index T erms — con volutional LDPC codes, err or floor , Gallager B, LDPC codes, min-sum decoding algorithm, T anner code, trapping s ets. I . I N T R O D U C T I O N The error-floor problem is arguably t he most important problem in the theory of low-density parity check ( LDPC) codes and iterative decoding algorithms. Roughly , error floor is an abrupt change in the frame error rate (FER) performance of an iterative decoder in the high signal-to-noise ratio (S NR) region (see [9 ] for more details and [1], [2], [3] for general theory of LDP C codes). The error floor problem for i terativ e decod ing on the binary erasure channel (BEC) is no w well understoo d, see [7], [8 ] and the r eferences therein. In the case of the additive white Gaussian noise (A WGN) channel, MacKay and Postol in [4] pointed out a weakness in the construction of the Margulis code [22] which led to high error floors. Richardson [9] presented a method to esti mate error floors of LDPC codes and presented results o n the A W GN channel. He pointed out that the decoder performance is gove rned by a small number of likely error e vents relat ed to certain topological structures in the T anner graph of the code, called trapping sets (or st opping sets on BEC [7]). 1 The ap proach from [9] w as further refined by Stepanov et al. in [10]. Zhang et al. [11] presented similar results based on hardw are decoder implementation. V onto bel and K oetter [12] established a theoretical framew ork for finite length analysis of message passing iterativ e decoding based on graph covers. This approach was used by Smarandache et al. in [13] to ana lyze the performance of LDPC codes from pro jectiv e geometries [13] and for LDPC co n volutiona l codes [14]. An early account on the most likely error even ts on the binary symmetric channel (BSC) for codes which T anner graphs have cycles M. Ivkovi´ c is with the Departmen t of Mathemati cs, Uni versit y of Arizona T ucson, AZ 85721, USA, e-mail: m ilos@math.ari zona.edu. S. K. Chila ppagari and B. V asi ´ c are with Dept. of Electrical and Computer Eng. Univ . of Arizona. An ea rlier version of this work was presented at the 2007 IEEE Intern. Symposium on Information Theory (ISIT’07). This work was supported by grants from INSIC-EHDR and NSF-CCR (Grant no. 0634969). 1 The necessary definitions will be giv en in the next section. is give n by Forney et al. i n [16]. Some results on LDP C codes ov er the B SC appear in [13], as well. A significant part of the research on error floor analysis has also focused on methods for lo wering the error floor . The two distinct approaches taken to tackle this problem are (1) modifying the decoding algorithm and (2) constructing cod es avoiding certain topological structures. Numerous modifications of t he sum-product decoding algorithm were pro posed, see, for e xample, [18] a nd [19], among others. Among the methods fr om the second group, there have been nov el constructions of codes w ith high T anner graph girth [2 1], [6], as it was observed that codes with low girth tend to have high error floors. While it is true that known trapping sets hav e short cycles [10], [17], the example of projectiv e geometry codes, that hav e short cycles, but perform well under (hard decision) iterati ve decoding, suggests that maximizing the girth is not the optimal procedure. A s the understanding of the error floor phenomena and its connection with trapping sets grows, avoiding the trapping sets directly (rather than short cycles) seems to be a more efficient way (i n terms of code rate and decoding complexity), t o suppress error floors. Code modification for improving the performance on the binary erasure channel (BE C) was studied by W ang in [20]. T o the best of our knowledge , it is the fi rst paper o n cod e modification with maximizing the size of st opping (or trapping) sets as the objecti ve. Edge swapping within the code was suggested as a way t o break the stopping sets. The method that we propose i s similar . Roughly speaking, it consists of taking two (or more) copies of the same code and swapping edges between the code copies in such a way that the most dominant trapping sets are broken. It is also simi lar to t he code constructions that appear in Smarandache et al. [14], T horpe [24], Divs alar and Jones [25] and Kelley , Sridhara and Rosenthal [26]. The advan tages of the method are: (a) it i s uni versal as it can be applied to any code/chann el model/de coding algorithm and (b) it improves performance at the expen se of increasing the code length only , without losing the code regularity , without changing the decoding algorithm, and, under certain conditions, w ithout lowering the code rate. If the length of the code is fixed t o n , the method can be applied by taking t copies of a (good) code C of l ength n/t and eliminating the most dominant trapping sets of C . The method can be slightly modified to construct con vo lutional LDPC codes as well . The details are giv en in Section III. W e apply our method and construct codes based on Margulis [22], T anner [ 21] and MacKay [23] codes and present results on the BSC when decoded using the Gallager B algorithm [1]. It is worth noting that t he error floor on the A WGN channel depends not only on the structure of the code b ut also on implementation nu ances of the decoding algorithm, suc h as numerical precision of messag es [9]. Since the Gallager B algorithm operates by passing binary messages along the edges of a graph, any concern about the numerical precision of messages does not arise. The rest of the paper is organized as follows. In Section II we introduce the notion of trapping sets an d their relation to the performance of t he code. W e explain the proposed method in Section III. W e present numerical results in Section IV and conclude in Section V. I I . B A S I C C O N C E P T S The T anner graph of an LDP C code, G , is a bipartite graph with two sets of nodes: v ariable (bit) nodes and check (constraint) nodes. The nodes connected to a certain node are r eferred to as its neighbors. The degree of a node is the number of its neighbors. The girt h g is the 2 length of the shortest cycle in G . In this paper , • represents a variable node, r epresents an ev en degree check node and represents an odd degree check node. The notion of trapping sets was first introduced in [4], but here we follo w the formalism from [19]. Definition 1: F or a given m × n matrix U = ( U i,j ) with 1 6 i 6 m, 1 6 j 6 n, the pr ojection of a set of h columns index ed by j 1 , j 2 , . . . , j h is an m × h matrix consisting of the elements u i,j , 1 6 i 6 m, j = j 1 , j 2 , . . . , j h . Definition 2: Let H be a parity check matrix of an LDPC code. An ( a, b ) trapping set T is a set of a columns of H wit h a projection that contains b > 0 odd weight rows. The definition of the trapping set abov e is purely topological, that is, a trapping set can be seen as a subgraph of the T anner graph. In other words, an ( a, b ) trapping set T is a subgraph with a va riable nodes and b odd degree checks. The most probable noise realizations that lead to decoding failure are related to trapping sets ([9], [10]). A measure of noise realization probability is referred to as pseudo-weight. Following the terminology in [10], an i nstanton can be defined as the most likely noise realization that leads to decoding failure. The instan tons on the BSC consist of the recei ved b it configurations with minimal number of erroneous bits that lead to decoding failure. Follo wing [17], the n otion specific to BSC, an alogous to pseu do- weight, can be defined as: Definition 3: The minimal number of variable nodes that have to be initially in error for the decoder to end up in the trapping set T will be referred to as the criti cal number k for that trapping set. Remark: T o “end up” in a t rapping set T means that, after a fi nite number of iterati ons, the decoder wil l be in error, on at least one v ariable node from T , at every iteration. Note that the v ariable nodes that are initially in error do not have to be wit hin t he trapping set. W e illustrate the abov e concepts with an examp le. (a) (5,3) trappin g s et (b) (4,4) trapping set Fig. 1. Tra pping s ets Example 1: The (5 , 3) trapping set in Fig. 1(a). appears (among other codes) in the T anner (155, 64) code [17] (see also the exa mples of irred ucible closed walks in the chapter 6.1 of [5]) . This t rapping set has critical number k = 3 under the Gallager B decoding algorithm (for the definition of the algorithm see [2]), meaning that, if three variable nodes, on t he diagonal from bottom left to top right, are i nitially in error , the decoder will fail to correct the errors. Fig. 1(b) illustrates a (4 , 4) trapping set. This trapping set, although smaller , has crit ical number k = 4 , ( all the variable nodes have to be in error initially for the decoder to fail). So, if a code has both (5 , 3) and (4 , 4) trapping sets, the F ER performance is dominated by the (5 , 3) trapping set. At the end of this example, we note t hat the (5 , 3) trapping set abov e is an example o f an o scillatory trapp ing set, i.e, if three v ariable nodes on the diagonal are initially in error, after the first iteration those three nodes will be decoded correctly , but the remaining two will be in error . In the decoding attempt after the second iteration those two will be correct, but the initial three will be in error again, and so on. Remark: Note that on the BEC the crit ical number is just the size of the st opping set, see [20]. W e no w clarify what “the most dominant trapping sets” means and ho w these effect code performance. Let α be the transition probability of the BSC and c k be the numb er of configurations of receiv ed bits for which k channel errors lead to a code word (frame) error . T he frame error rate (FE R) is giv en by: F E R ( α ) = n X k = i c k α k (1 − α ) ( n − k ) where i is the mi nimal number of channel errors that can lead to a decoding error (size of instantons) and n is the l ength of the code. On a semilog scale the FE R is given by the expression log( F E R ( α )) = log ` n X k = i c k α k (1 − α ) n − k ´ (1) = log( c i ) + i log( α ) + log ((1 − α ) n − i ) (2) + log „ 1 + c i +1 c i α (1 − α ) − 1 + . . . + c n c i α n − i (1 − α ) i − n « (3) In t he limit α → 0 we note that lim α → 0 h log((1 − α ) n − i ) i = 0 and lim α → 0 h log “ 1 + c i +1 c i α (1 − α ) − 1 . . . + c n c i α n − i (1 − α ) i − n ”i = 0 So, the behav ior of the FER curve for small α is dominated by log( F E R ( α )) ≈ log( c i ) + i log( α ) The log( F E R ) vs log ( α ) graph is close to a straight li ne with slope equal to i -the minimal crit ical number or cardinality of the instantons. Therefore, if two codes C 1 and C 2 hav e instanton si zes i 1 and i 2 , such that i 1 < i 2 , then the code C 2 will perform better than C 1 for small enough α, independen t of the number of instantons, just because log( α ) → −∞ as α → 0 . Note also that the critical number of the most dominant trapping sets cannot be greater than half the minimum distance. If it is the case, the performance of the decoder is dominated by the minimum weight codew ords. I I I . T H E M E T H O D F O R E L I M I NAT I N G T R A P P I N G S E T S In this section we present a method to construct an L DPC code C (2) of length 2 n from a giv en code C of l ength n and discuss a modification of the method that giv es a con v olutional LDPC code based on C . Let H and H (2) represent the parity check matrices of C and C (2) respecti vely . H (2) is initialized to H (2) = » H 0 0 H – . Stated simply , H (2) is formed by taking two copies of H say C 1 and C 2 . It can be seen that if H has dimensions m × n , then H (2) has dimensions 2 m × 2 n . Every edge e i n the T ann er graph G of C is associated with a nonzero entry H t,k . The operation of changing the v alue of H (2) t,k and H (2) m + t,n + k to “0”, and H (2) m + t,k and H (2) m,n + k to “1” is termed as swapping the edge e . Fig. 2 illustrates edge sw apping in tw o copies of a (5 , 3) trapping set. W e assume that the most 3 Fig. 2. Tra pping s et elimination dominant trap ping sets for C are kn own . The method can be described in the following steps. Algorithm: 1) T ake two copies C 1 and C 2 of the same code. S ince the codes are i dentical they hav e the same trapping sets. Initiali ze SwappedEdg es = φ ; Fr ozenEdges = φ ; 2) Order the trapping sets by their crit ical numbers. 3) Choose a trapping set T 1 in the T anner g raph of C 1 , wi th minimal critical number . Let E T 1 denote the set of all edges in T 1 . If ( E T 1 ∩ SwappedEdges 6 = φ ) goto 5. Else goto 4. 4) Swap an arbitrarily chosen edge e ∈ E T 1 \ F r ozenEdg es (i f it exists). Set SwappedEdg es = SwappedEdg es ∪ e . 5) “Freeze” the edges E T 1 from T 1 so that they cannot be swap ped in the following steps. Set Fr ozenEdges = F r ozenEdg es ∪ E T 1 . 6) Repeat steps 2 to 4 until i t is possible to remov e the trapping sets of t he desired size. Step 5 is needed because swapping additional edges fr om the (former) trapping sets might introduce trapping sets with a same critical number again. Fig. 3 il lustrates such a swapping which corresponds to just interchanging the check nodes. Fig. 3. Reintro ducing trappin g set by swappi ng two edges The T anner graph of the ne wly made code is a special double cover of the original code’ s T anner graph, interested readers are referred to [12]. Remark: There are se veral app roaches which may impro ve the efficien cy of the algorithm. Firstly , i nstead of swapping the edges at random at step 3, edges could be swapped based on the number of trapping sets they participate in, or by using some other schedule that would (potentially) lead to the highest number of trapping sets eliminated. The structure of the code can also be explo ited. For example, the Margulis (2640 , 1320) code [22], has 1320 (4 , 4) minimal trapping sets with the property that each trapping set has one edge that does not participate i n any other minimal trapping set. So, instead of swapping edges at random, the edges appearing i n only one trapping set can be swapped, and such a procedure is guaranteed to eliminate all the minimal trapping sets. Also, there is a possibility not to freeze all the edges f rom the (former) trapping sets, but only those that would, if swapped, introduce the trapping sets with the same critical number . Note, howe ver , that any edge swapping schedule can be seen as a particular realization of the random edge swapping. For all the codes that we considered, all t rapping sets with minimal cri tical number were eliminated by the algorithm with random edge swapping. The following theorem shows ho w this method affects the code rate. Theor em 1: If the code C , with parity check matrix H , and rate r (and length n ) is used in the algorithm abov e, the resulting code C (2) will have rate r (2) (and length 2 n ), such that r (2) 6 r. Pr oof: Each edge swapping operation in the algorithm can be seen as matrix modification. At the end of the algorithm, code C (2) is determined by H (2) = » H ′ B B H ′ – where H ′ and B are matrices such that H ′ + B = H , and H ′ t,k (or B t,k ) can be equal to “1” only if H t,k = 1 . If the second block row is added t o the first in H (2) , and then the the fi rst block column is added to the second, w e end up with » H ′ B B H ′ – → » H H B H ′ – → » H 0 B H – (4) The last matrix i n (4) has rank which is greater than or equal to twice the rank of H . Therefore, the code C (2) has rate r (2) 6 r where r is the rate of C . Note, that r (2) = r if B = C H + H D, for some matrices C and D, so t hat C H corresponds to linear combinations of rows of H and H D corresponds to l inear combinations of columns of H . W e also hav e a following corollary . Cor ollary 1: If the matrix H has full rank, then r (2) = r. Pr oof: T his follows from the fact that if H h as full rank, then the last matrix in (4) has full rank also. At the end of this section, we briefly discuss the minimal distance of t he modified code. Theor em 2: If th e code C has minimal distance d min , the modified code C (2) , will hav e t he minimal distance d (2) min , such that, 2 d min ≥ d (2) min ≥ d min . Pr oof: W e first prove that d (2) min ≥ d min . S uppose that the minimal weight code w ord of C (2) is c (2) , where c (2) is a colum n vecto r consisting of two vectors c 1 and c 2 of length n . Then H (2) c (2) = 0 is equi valen t t o » H ′ B B H ′ – » c 1 c 2 – = » H ′ c 1 + B c 2 B c 1 + H ′ c 2 – = 0 (5) Note that c 1 + c 2 = c is a column vector of length n, with Hamming weight w h ( c ) ≤ w h “ c (2) ” , where w h “ c (2) ” is the Hamming weight of the c (2) . Now: H c = ( H ′ + B )( c 1 + c 2 ) = H ′ c 1 + B c 1 + H ′ c 2 + B c 2 = 0 (6) because the last expression in Eq. (6 ) is equal to the sum of entries of t he last column vector in Eq. 5. So, c is a codew ord of C. If c 6 = 0 , f rom w h ( c ) ≤ w h “ c (2) ” it follows that d (2) min ≥ d min . If c = 0 then c 1 = c 2 , and from Eq. (5) follows that H c 1 = 0 , so c 1 is a code word of C and again d (2) min ≥ d min . The proof t hat 2 d min ≥ d (2) min is similar . I f we assume that c 1 is a minimal w eight code word of C, we hav e: » H ′ B B H ′ – » c 1 c 1 – = 0 (7) so 2 d min ≥ d (2) min . W e finish t his proof by mentioning that it is not difficult t o construct examples where 2 d min = d (2) min or d (2) min = d min , so the statement of the theorem is “sharp”. 4 W e described the algorithm in its basic form. H (2) can be initial- ized by interleaving the copies C 1 and C 2 in an arbitrary order , but we choose concatenation t o keep the notation simple. The method, as well as all the proofs, will hold for any interleaving. It is also possible to con sider more than two copies of t he code to further eliminate trapping sets with higher critical number . The splitting of parity check matrix H i nto H ′ and B can be seen as a way t o construct con vo lutional LDP C codes, that is, as a way to unwrap the original LDPC code C . For details on unwrapping see [15] and the references therein. The (infinite) parity check matrix can be can be constructed as: H conv = 2 6 6 6 4 H ′ B H ′ B H ′ B . . . . . . 3 7 7 7 5 (8) Note that by construction the resulting con volutional code has pseudo-co dew ords with higher pseudo-weights than original LDPC code. In t his light, Theorem 2 can be seen as a generalization of Lemma 2.4 from [14]. W e refer readers interested in con volutional LDPC codes to that paper . I V . N U M E R I C A L R E S U LT S In this section we ill ustrate the proposed method by modifying the Margulis [22], T anner [21] and MacKay [23] codes to eliminate trapping sets under the Gallager B decoding algorithm. W e use the trapping sets reported in [17]. Example 2: (Mar gulis (2640 , 1320 ) code) The parity check of this matrix has full rank, so the modified code is an (5280 , 2640) code, and has the same rate as the original code, i. e., r (2) = r = 0 . 5 . This code has 1320 (4 , 4) trapping sets with critical number 4 as t he most dominant ones . The modified (5280 , 2640) code has no (4 , 4) trapping sets and the performance is governed by (5 , 5) trapping sets (ten cycles), t hat have critical number k = 5 , Fig. 4. Fig. 4. Margul is code performance Example 3: (T anner ( 155, 64) code) This code has (5 , 3) trapping sets (Fi g. 1(a)) wit h critical number i = 3 as the most dominant ones. There are 155 such t rapping sets [17], [21]. In this case we used a version of the method in which it is possible t o swap edges from the (former) trapping sets, if no trapping set of the same or smaller crit ical number is introduced. The result was a ( 310, 126) code for which the minimal trapping sets are type (4,4) (eight cycles) with critical number k = 4 (see Fi g 1(b)). This was confirmed by numerical simulations in Fig. 5. The FE R curve changes the slope, for higher α, where F ER contribution from t he expression (3) is not negligible. Note that there was a small rate penalty to this procedure. The original T anner code has rate 0.4129, whereas the modified code has rate 0.4065. Fig. 5. T anner code performance for a longer range of α Example 4: ( MacKay’ s (1008, 504) codes) This is an example of ho w the method can be used to produce better codes of a fixed leng th. W e have taken a 504 length MacKay code and constructed a 1008 ( 2 ∗ 504 ) length code. The ne w code performs better than MacKay codes of l ength 1008. Both original 504 and 1008 length code s hav e two type s of trapping sets with critical number k = 3 , (5,3) and (3,3) (si x cycles). W e ran the algorithm so that all (3,3) trapping sets are eliminated from the ne wly constructed, but none of the (5,3) trapping sets. The results are sho wn in F ig. 6 . It can be seen that, although the FER performance Fig. 6. MacKay’ s codes performance is improved, the slope of the F ER curve is approximately the same. 2 Example 5: (A WGN channel) This examp le il lustrates two points. First is that optimizing code for one decoding algorithm can lead t o performance improvement for other decoding algorithms. The second point is that the use of an appropriate axis scaling can greatly help in error fl oor analysis and code performance prediction. W e present F ER results ov er A WGN channel and min-sum algo- rithm after 500 i terations for three codes, the original T anner (155, 64) code, our modified T anne r (310, 126) from the Example 3 and a random ( 310, 127) code with column weight 3 and r o w weight 5. In the lo w SNR region , where all kinds of error even ts are likely , t he l ength (and rate) of a code go vern the performance. In this region codes of length 310 hav e simi lar performance. For high SNR s, howe ver , code optimization i n t erms o f trapping sets becomes important and r andom code performance beco mes much worse than performance of the modified T anner (310, 126) code. Notice a pronounced error floor for the random code. What is ev en more il lustrativ e is Fig. 7(b) where we plot log( F E R ) versus S NR (not in dB) on the x-axis. T his is because for high SNRs on the A WGN channel, simil arly to Eq. (3), F E R ∝ exp( − ω in ∗ SNR / 2) , where d in is pseudo-weight of the most likely 2 It is possible that a more sophisticated algorithm would also eliminate the (5,3) trappi ng sets. Ho wev er , our goal with this exa mple was to show the performanc e when some, but not all, of the trapping sets with minimal critic al number are eliminate d. 5 error ev ent. So on the graph wit h SNR on the x-axis which is not in dB, log( F E R ) curve will approach (from abov e) a straight li ne with slope equal to − ω in / 2 as SNR → ∞ . See [5] and [12] for further details. Using these observ ations and numerical r esults obtained by simulations we can estimate that our modified code has the slope approximately equal to 20, better than the original T anner (155, 64) code with the slope of ≈ 14 . 3 Further more, considering that t he slope for the random code is ≈ 12 , we can claim that, for SNR values higher than those on the plots, the T anner code wil l perform better than the random code. (a) log ( F E R ) versus SNR in dB (b) l og( F E R ) versus SNR as E N (not in dB) Fig. 7. FER performance under min-sum decoding V . C O N C L U S I O N The proposed method allows the construction of codes wi th good FER performan ce, bu t low row/column weight (as op posed to projective geometry codes) and therefore relativ ely low decoding complex ity . Although numerical results for the Gallager B decoder are presented, we reiterate t hat the me thod ca n be used for code optimization based on the trapping sets of an arbitrary decoder . The algorithm can also be used to determine the pseudo-weight spectrum of a code as follows. Once the most likely trapping sets (those with the smallest pseudo-weight) are determined and elimi- nated by the method, t he numerically obtained decoding performance of a modified code, i. e., t he sl ope of the F ER curve with appropriate axis, gi ves an estimate of the pseudo-weight of the next most likely trapping sets - just as i t was done in the Example 5 with the T ann er code and the modified T anner code. A C K N O W L E D G M E N T The authors would like to acknowled ge v aluable discussions wit h Robert Indik, Misha Stepanov and C lifton W illiamson. 3 The estimate for the T ann er code is in accordan ce with the pseudo-wei ght of the single most like ly error ev ent of ≈ 12 . 45 reported in [10 ]. R E F E R E N C E S [1] R. G. G allag er , Low Density P arity Check Codes, Cambridge, MA: MIT Press, 1963. [2] T . J. Richardson and R. U rbank e, “The Capacit y of L ow-De nsity Parity- Check Codes Under Message-Passing Algorithm, ” IEEE Tr ans. Inform. Theory , vol. 47, no. 2, pp. 599-618, Feb . 2001. [3] T . Richardson, A. Shokrollah i, and R. Urbanke, ”Design of capacity approac hing irregula r low-densit y parity-check codes, ” IEEE T rans. Inform. Theory , vol. 47, pp. 619-637, 2001. [4] D. MacKay and M. Postol, “W ea knesses of Margulis and Ramanuja n- Margul is lo w-density parity check codes, ” Electronic Notes in Theoret- ical Computer Science, vol. 74, 2003. [5] N. Wibe rg, Codes and decod ing on gene ral graphs, Ph.D. thesis, Link ¨ oping Uni versity , 1996. [6] J.K. Moura. J. Lu, and H. Zhang, “Structu red LDPC codes with large girth, ” IEEE Signal Proc. Mag., vol. 21, no. 1, pp. 42-55, J an. 2004 [7] C. Di et al. , “Finite length analysis of lo w-density parity-c heck codes on the binar y erasure channe l, ” IE EE T rans. on Information Theory , vol . 48, no. 6, pp. 1570-1579, Jun 2002. [8] C. W ang, S. R. Kulkarni, H. V . Poor, “Upper Bounding the Performance of Arbitrary Finite LDPC Codes on Binary Erasure Channe ls, ” in P r oc. Intern. Symp. on Inform. Theory , Seattl e, W A, USA, July 9-14, 2006. [9] T . J. Richardso n, “Error Floors of LDPC Codes, ” in Proc. 41st Annual Allerto n Conf. on Communications, Control and Computing, 2003. [10] M. Stepano v , M. Chertko v , “Instanto n analysis of Low-Density Parity- Check codes in the error-floor regime, ” , Pr oc. IEEE Intern. Symp. on Inform. Theory (ISIT), Seattle , W A, USA, July 9-14, 2006. [11] Z. Zhang, L. Dolece k, B. N ikol i ´ c, V . Anantharam and M W ainwri ght “In ve stigatio n of E rror Floors of Structured L ow- Density Parity-Ch eck Codes by Hardware Emulation, in Proc. IEEE Globeco m, San Francisco, CA, USA, 2006. [12] P . O. V ontobel and R. Ko etter , “Graph-cov er decoding and finite-le ngth analysi s of message-passing iter ati ve decodin g of LDPC codes, ” preprint, av ail able online at http://www .arxiv .org/ . [13] R. Smarandache an d P . O. V onto bel,“Pseudo-Cod ew ord Analysis of T anner Graphs from Projecti ve and E uclidea n Planes, ” preprint, av aila ble online at http://a rxi v .org/ . [14] R. Smarandache, A. E . Pusane, P . O. V ontobel and D.J Costello, Jr .,“Pseudo-Co dew ord Performance Analysis for LDPC Con volut ional Codes, ” preprint, av ailabl e online at http://arxi v .org/ . [15] A. E. Pusane, R. Smarandache, P . O. V ontobel and D. J Costello, Jr ., “On derivi ng good LDPC con volut ional codes from OC LDPC Block Codes, ” in Proc. IEEE Intern. Symp on Inform. Theory , Nice, France, June 24-29, 2007, pp. 1221-1225. [16] G. D. Forne y , Jr., R. Koett er , F . R. Kschischang, and A. Reznik, “On the ef fecti ve weights of pseudocode wor ds for codes defined on graphs with cycle s, ” in Codes, Systems, and Graphical Models (Minneapolis, MN, 1999) (B. Marcus and J. Rosenthal, eds.), vol. 123 of IMA V ol. Math. Appl., pp. 101–112, Springer V erla g, New Y ork, Inc., 2001. [17] S. K. Chilappa gari, S. Sankaranara yanan, and B. V asic, “Error Floors of L DPC Codes on the Binary Symmetric Channel, ” P r oc. Intern. Conf . on Communication s, ICC 2006, Istanbul , T urke y , June 2006. [18] N. V arnica and M. Fossorier , “Improv ements in belief-propaga tion decodin g based on av eraging informati on from decoder and correcti on of clusters of nodes, ” in IE EE Communications Letter s, vol. 10, no 12. pp 846-848, Dec. 2006. [19] S. Laendner , T . Hehn, O. Milenk ovi ´ c and J. Huber , “When does one redundan t parity-check equation m atter? ” in Pr oc. IEEE Globecom, San Francisco , CA, USA, 2006. [20] C. W ang, “Code annealing and the suppressing ef fect of the cyc licall y lifted LDPC code ensemble, ” presented at 2006 IEEE Information Theory W orkshop , Chengdu, China, October 22-26, 2006. [21] R. M. T anner , D. S ridhara and T . Fuja, “ A class of Group-Structured LDPC codes, ” in Proc. ISCT A, 2001. [22] J. Rosentha l and P . O. V ontobel, “Construct ions of LDPC Codes Using Ramanuja n Graphs and Ideas From Margulis, ” in Proc. of the 38-th Allerton Conf. on Communication, Contr ol, and Computing , 2000. [23] D. J. C. MacKay , “Encyclo pedia of Spa rse Graph Code s, ” Online: http:/ /www .interf erence.phy .cam.ac.uk/ mackay/code s/data.html. [24] J. Thorpe, “Low Density Parity Check (L DPC) Codes Construc ted from Protograph s, ” JPL INP Progress Report 42-154, August 15, 2003. [25] D. Divsala r , C. Jones, “Protgraph LDPC Codes with Node Degrees at Least 3, ” in Proc. IEEE Globecom, San Francisco, CA, USA, 2006. [26] C. Ke lley , D. Sridhara, J. Rosenthal,“T ree-Based Construction of L DPC Codes Having Good Pseudocode wor d W eig hts, ” preprint, ava ilable on- line at http://ar xiv .org/ .
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment