Minimum-energy broadcast in random-grid ad-hoc networks: approximation and distributed algorithms
The Min Energy broadcast problem consists in assigning transmission ranges to the nodes of an ad-hoc network in order to guarantee a directed spanning tree from a given source node and, at the same time, to minimize the energy consumption (i.e. the e…
Authors: Tiziana Calamoneri, Andrea E.F. Clementi, Angelo Monti
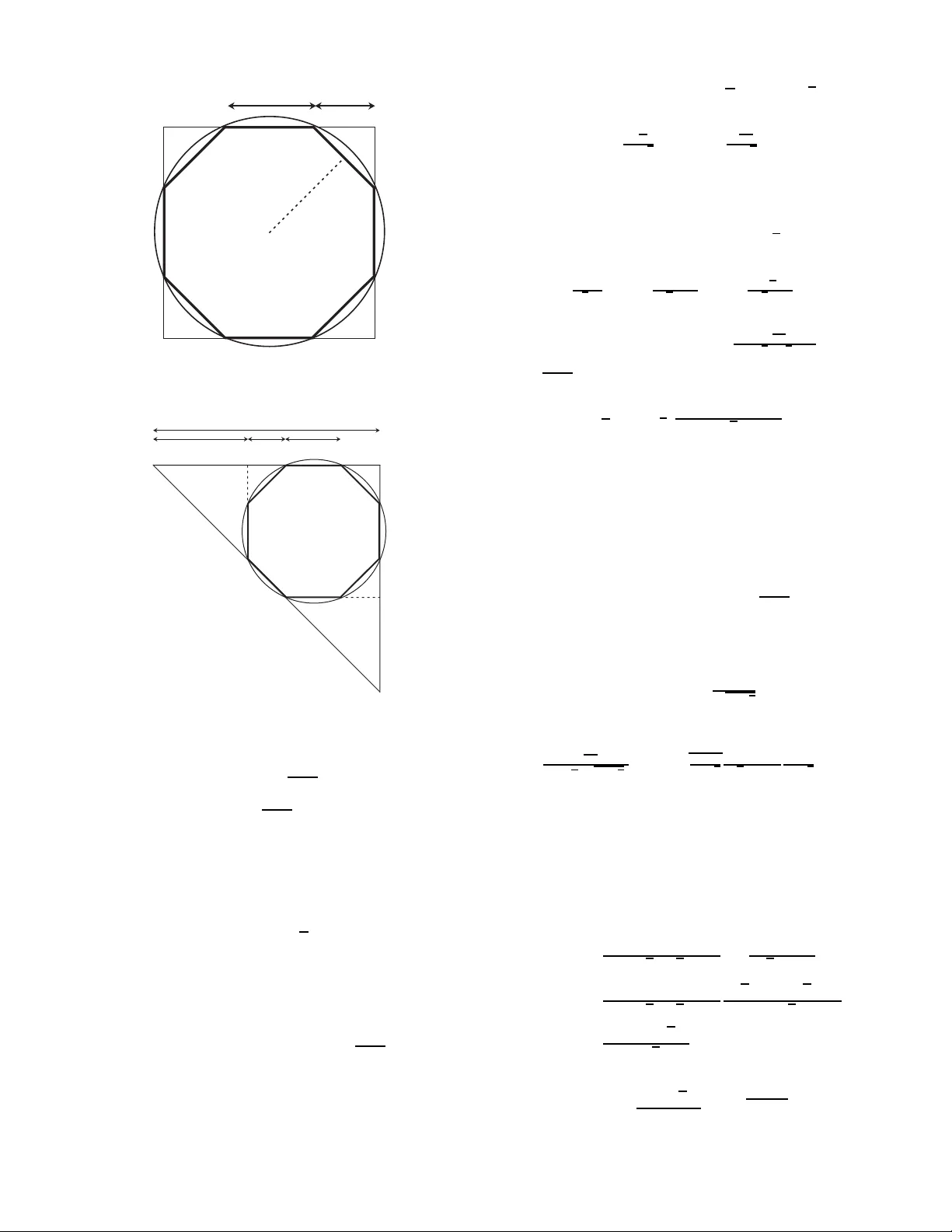
Minim um-ener gy br oadcast in random-grid ad-hoc netw orks: appr o ximation and distribu ted algorithms ∗ Tiziana Calamoneri Dipar timento di Informatica Sapienza Univ ersità di Roma calamo@di.un iroma1.it Andrea E.F . Clementi Dipar timento di Matematica Unive rsità di Roma II, “T or V ergata” clementi@mat.uniro ma2.it Angelo Monti Dipar timento di Inf or matica Sapienza Univ ersità di Roma monti@di.uniro ma1.it Gianluca Rossi Dipar timento di Matematica Unive rsità di Roma II, “T or V ergata” gianluca.ro ssi@uniroma2.it Riccardo Silv estri Dipar timento di Informatica Sapienza Univ ersità di Roma silve r@di.uniroma1 .it ABSTRA CT The Min Ene r gy Bro adcast p roblem consis ts in assign- ing transmissi on ranges to the nodes of an ad-ho c netw ork in order to guarantee a directed spanning tree from a given sour c e nod e and, at the same time, to minimize th e energy consumption (i.e. the ener gy c ost ) yielded b y the range as- signmen t. Min Ener gy Br oadcast is kn o wn to be NP- hard. W e consider r andom-grid networks where no des are chosen indep endently at random from th e n p oints of a √ n × √ n square grid in th e plane. The probabilit y of the existence of a node at a given p oint of the grid do es d epen d on that p oin t, that is, the probability distribution can be non-uniform . By using in formation-theoretic arguments, we prov e a low er b ound (1 − ǫ ) n π on the en ergy cost of any feasible solution for this problem. Then, we provide an efficient solution of energy cost not larger than 1 . 1204 n π . Finally , w e present a fully-distributed protocol that con- structs a broadcast range a ssignment of energy cost not larger t han 8 n , thus still y ielding constant approximation. The ener gy lo ad is well balanced and, at the same time, the work c omplexity (i.e. the energy d ue to all message trans- missions of the proto col) is asymptotically optimal. The completion time of the protocol is only an O (log n ) factor slo w er than the optim um. The approximati on q ualit y of our distributed solution is also experimentally eval uated. All b ound s hold with probabilit y at least 1 − 1 /n Θ(1) . 1. INTR ODUCTION ∗ Researc h partially su pp orted by t h e European Union under the Pro ject AEOLUS Range assignments in ad -hoc n etworks. In ad-ho c net- w orks, no des are able to v ary their transmission ranges in order to provide go od netw ork connectiv it y and lo w energy consumption at the same time. More precisely , th e trans- mission ranges determine a (directed) c ommunic ation gr aph G ( S, E ) o ver the set S of no des: a no de v , with transmis- sion range r , can transmit to another no de w ( so, e dge ( u, w ) ∈ E ) if and only if w b elongs to the disk centered in v and of radius r . The transmission range of a no de de- p ends, in turn, on th e energy p ow er supplied to the node. In particular, the p o w er P v required by a no de v to cor- rectly transmit data to another station w must satisfy t h e inequality P v ≥ dist ( v , w ) 2 , where dist ( v , w ) is the Eu- clidean distance b et wee n v an d w . In severa l w orks [1 , 12, 17, 24], it is assumed that no des can arbitrarily v ary t heir transmission range o ver the ” larg e” set { dis t ( s, t ) | s, t ∈ S } . How ever, in some imp ortan t netw ork scenarios (like sensor netw orks), this assumption is not realistic: the adopted tech- nology allo ws no des to ha ve only few p ossible transmission range v alues. F or th is reason, we adopt the mod el consid- ered in [9, 10, 16, 38] where n o des are ab le to choose their transmission range from a r estricte d set Γ. A fun damenta l class of algorithmic p roblems arising from ad-ho c wireless n et w orks consists in the r ange assignment pr oblems : find a transmission range assignmen t r : S → Γ such that (1) the resulting communication graph satisfies a given connectivity prop erty Π, and (2) the ener gy c ost cost ( r ) = P r ( s ) 2 of the assignment is minimized (see [17, 24]). Several research works [1, 12, 8, 17] ha ve b een devoted to the Mi n Energy B r o adcast problem where Π is defined as follo ws: Given a sour c e no de s , the c ommunic ation gr aph has to c ontain a dir e cte d sp anning tr e e r o ote d at s (a br anch- ing fr om s ) . Previous theoretical results on Mi n Energy Bro adcast concern worst-c ase analysis only . This p roblem is k n o wn to b e NP- h ard [12] even when Γ = { 0 , l 1 , l 2 } for l 1 < l 2 and l 1 is set to any fixed p ositiv e constan t. The most famous approximation algorithm is the MST -based heuristic [17]. This h euristics works in Θ ( n 2 ) time and its p erformance analysis has been the sub ject of sev eral w orks o ver the last years [12, 18, 36]. In [1], it is fin ally prov ed the tight b ound 6 on its approximation ratio. More re- cently , a n ew p olynomial-time algorithm is provided in [8 ] that achiev es approximation ratio close to 4. This algorithm applies a rather complex edge-con traction technique on the MST-based solution. I ts p resen t best versio n w orks in Θ( n 5 ) time and the design of an y efficien t distributed version seems to b e a very h ard task. It is imp ortant to observe that the MST-based heuristic is ” far” from ac hieving optimal solutions even on a complete square grid of n p oints [5, 19]: its worst-case ap p ro xima- tion ratio on su c h grids is not smaller th an 3. In [19], it is also ex perimentally observed that this heuristic has a bad b eha vior when applied to random r e gular instances suc h as faulty square grids. F urthermore, the MST-based heuristic requires a large range set Γ. The ab ov e discussion leads us to study Min Ener gy Bro ad- cast ov er r andom grid net wo rks. Given a √ n × √ n grid of p oin ts of the Euclidean plane (without loss of generalit y , ad- jacen t p oints are placed at unit distance), eac h point 1 i is selected as a no de of the random grid net w ork indep endently with probabilit y p i . This no de pr ob ability can b e any v alue in the interv al [ p min , p max ] where p min and p max are tw o ar- bitrary positive constan ts in the in terv al (0 , 1). W e remark that our random grids are in general non un iform: Random grids p ro vide a go od mo del for several ad-ho c and sensor netw orks. On one hand, by va rying t he p i ’s va lues, it is p os- sible to mo del non h omogenous input configurations with regions of d ifferen t no de d en sities. On the other h and, the grid structure guarantees a minimal distance among n odes: this is often a desired property in order to optimize area co verage and a voi d messag e collisi ons. Nevertheless, as dis- cussed later, all our results also hold for th e standard uni- form r andom distribution (i.e. th e random inpu t formed by choosing n p oints in d ep en dently and u n iformly at random from a 2-dimensional square) [25, 33]. Our r esults. 1) W e p ro vide a low er b ound on the energy cost of feasible solutions for any range assig nment problem on random grids where the required p rop erty Π i mplies th e existence of a disk cov er. W e say that a range assignment is a (disk) c overing assignmen t if it guarantees th at every nod e of the n et wo rk is within t h e p ositive range of some nod e. Min Ener gy B r oadcast is just one of those imp or- tant cases requiring cov ering range assignments. Let l 1 b e the minim um p ositiv e range in Γ. F or any 0 < ǫ < 1, if l 1 = Ω( 1 ǫ ) then w e p ro ve that the energy cost of any cov ering range assignmen t is with high p rob ab ility 2 (in short, w.h.p.) at least (1 − ǫ ) n π . Observe that the lo wer b ound tends to n/π for any l 1 such th at l 1 = ω (1), so for minimal ranges m uch smaller than the c onne ctivity thr eshold Θ( √ log n ) [15, 22 , 33, 34 ]. The pro of ’s tec hnique of the low er b ound d eparts signifi- cantl y from all those adopted in this t opic and uses information- theoretic arguments. By using this result, we will pro ve that 1 F or th e sak e of simplicit y , w e here assume that p oints are labelled with index i = 1 , . . . , n . 2 Here and in the sequel the t erm with high pr ob ability means that the ev ent holds with probability at least 1 − 1 n a for some constant a > 0. the next t w o algorithms are almost optimal. 2) W e provide a simple an d efficient algorithm for random grids that uses minimal range l 1 = Θ( √ log n ) and returns a solution of energy cost not larger than 1 . 1204 n π w.h.p.: In virtue of ou r low er b ound, t h is is very close to the optimum. Observe that our low er bou n d h olds for any cov ering range assignmen t while th e upp er b ound holds for feasible range assignmen ts of Min Energy Bro a dcast : th is implies that, for l 1 = ω (1), the extra-cost, due to the required tree con- nectivity prop erty , is ” almost” neglig ible in ran d om grids (it is still an op en p roblem whether t his is in fact negligible). Our algorithmic solution w orks in O ( n log n ) time and needs a set Γ of lo garithmic size (in n ). The range assignment is inspired to the one p ro vided in [5 ] for complete squ are grids (i.e. every p oin t of the grid is a no d e of the n et wo rk). How- ever, the p robabilistic cost analysis of our construction for r andom grids is definitely not related to th at in [5]. 3) It is common opinion that th e developmen t of efficient, prov ably-goo d di stribute d algorithms is presently t he ma- jor challenge ab out range assignmen t p roblems [4, 36, 17]. W e provide an efficient distributed algorithm for Mi n En- ergy B r oadcast on rand om grids. W e inv estigate the p er- formance of the protocol in tw o different scenarios: single br o adc ast a nd many-br o adc ast , i.e., a sequence of consecu- tive broadcast op erations. In b oth cases, b esides the energy cost of the returned range assignmen t, w e consider furth er imp ortant complexity aspects that determine the qu alit y of a distribut ed solution. - Work Complexity. In th e ad-h oc netw ork mo del, the work c omplexity of a distributed algorithm (i.e. protocol) for Min Energy Br oadcast is defined as the sum of th e energy cost of al l transmissions made by the proto col to p erform the broadcast operation [23, 27, 35]. This complexity mea- sure thus considers b oth the cost to c onstruct the range as- signmen t and t he cost to use it to broadcast th e message (the latter b eing exactly the cost of th e range assignment defined for centralized algorithms). Since b oth th e ab o ve energy costs are paid by t he n odes, a protocol can be really considered energy efficien t only if it has a small work com- plexity . - Ener gy-L o ad Balancing. In some real ad-h oc netw orks (such as sensor netw orks), it is also imp ortan t to equally distribute the energy load to all no des. F or in stance, solu- tions, assigning large ranges to few no des, are not feasible in scenarios where no des have limited battery charges . In such a case, we aim to design solutions t hat are well energy- load balanced. Notice th at, in t he many-broadcast scenario, th is corresponds to m ax imize network l ifetime according to the mod el in [6, 7]. - (Amortize d) Completion Time. Another relev ant asp ect of a broadcast p rotocol is the c ompletion ti m e , i.e., the number of time steps required to complete one broadcast op eration. In the many-broadcast scenario, the amortize d c ompletion time is the aver age completion time for one b roadcast op er- ation. Our aim is to derive a protocol having pr ovably-go o d p erfor- mance with resp ect to al l the ab o ve complexity asp ects. T o the b est of our knowl edge, no av ailable proto col has b een sho wn to have this o vera ll p erformance. W e first define a very simple range assignment where only one p ositive range in Γ is used, provided that it is not smaller than c √ log n where c is a suitable p ositive constan t (ob- serve again that this v alue is asymp totically eq uiv alent to the connectivity threshold). This solution is th en shown to b e w.h.p. feasible and to hav e an energy cost not larger than 8 n . Thanks to our lo w er b ound, the ac hieved en ergy cost yields a constant appro ximation ratio. Moreov er, this sim- ple range assig nment can be constructed and managed by an efficient proto col. W e assume ev ery no de initially kno ws n and its relative p osition with resp ect to th e grid only . Po- sitioning information can b e obtained by using GPS systems or Ad-H oc Positio ning System (APS) [31]. This assumption is reasonable in static ad-ho c netw orks since every no de can store onc e and for al l its position in the set- up phase. The protocol exp loits a fully-distribut ed pivot-electi on strategy b orro w ed from [6]. W e prov e that the w ork complexity of t h e proto col is equ iv- alen t to the energy cost of the centralized versio n and hence, thanks again to our low er b oun d (clearl y , a lo w er bound for the energy cost is also a low er bound fo r the work complex- it y), it achiev es a constant approxima tion ratio as well . It is imp ortant to emphasize t hat th e b est distributed algorithm to compute an MST in the ad-ho c mod el has an exp ected w ork complexity Ω( n log n ) [21, 23 , 28, 29]. By comparing this b ound with the Θ( n ) w ork complexity achiev ed b y our protocol, w e can state that an y MST-based solution [17, 8 ] cannot yield go o d w ork complexity in this scenario. Ot h er distributed solutions ha ve b een considered in the literature [4, 27, 35, 37], how ever their p erformance analysis is based on exp erimental tests only . W e also compared the work complexity of our protocol to the energy cost of the cen- tralized MST-based solution ov er thousands of random in- stances with differen t sizes and d ensities. The a verage p er- formance ratio b etw een the tw o solutions is alwa y s b et wee n 2 and 3 (see Section 4.1) th us confirming our analytical re- sults. Our protocol yields a goo d energy-load b alanced solution: there are Θ( n/ log n ) pi vots , i.e., the no des having range Θ( √ log n ) (the remaining no des have range 0). F urth er- more, thanks to the pivot-election strategy [6], a goo d energy- load balance is also obtained with resp ect to an arbitrary se- quence of broadcast op erations, i.e., for the many-broadcast scenario. At every n ew op eration, the pivot task is indeed assigned to no des according to a R ou n d R ob in rule. W e sho w this yields an almost optimal li f e-time of the netw ork according to the energy consumption model in [6 , 7]. As for the single broadcast scenario, the comp letion time of our proto col is slow er than the optimum by a Θ(log n ) factor. A s for the many-broadcast scenario, when the num- b er of b roadcast op erations is Ω(log n ), then the amortized completion time is optimal. Finally , w e notice that, by using t he technique in [30 ], our protocol can be emulated on the standard uniform random distribution [25, 33]. The same holds for the centralized algorithm achieving cost 1 . 1204 n π and for t he lo w er bou n d as well. The relative pro ofs for t he u niform d istribution are easier and, so, they are omitted in t his extend ed abstract. P ap er’ s Or ganization. In Section 2, we p ro vide the proof of the lo w er b ound. In Section 3, w e describe the centralized algorithm yielding almost optimal cost. Finally , Section 4 is devoted to the description of our distributed protocol and its analysis. 1.1 Pr eliminaries The squ are grid R of √ n × √ n p oints will be indexed from 1 to n . Without loss of generality , the distance b etw een adjacen t p oints is set to 1. T o eac h p oint i of R , a probabilit y v alue p i is assigned such th at p min ≤ p i ≤ p max where p min and p max are arbitrary constants in ( 0 , 1). W e consider the random input mo del R ( R, p 1 , . . . , p n ) where an instance S ⊆ R has probability P R ( S ) = Y i ∈ S p i · Y i ∈ R − S (1 − p i ) Observe that th is probability distribution is equival ent t o select each p oint i ∈ R ind epen dently with probability p i . A selected point will b e called no de . In the sequ el, a subset S ⊆ R selected according to the ab ov e random distribution will b e simply called r andom set . A set of d isks C = { D 1 , . . . , D m } is said to be an l -cov er for S ⊆ R if the follo wing prop erties hold: i ) All disks of C h a ve radius at least l , where l is some positive v alue. ii) Every disk of C has its center on a no de of S . iii) Every no de of S is cov ered by some disk of C . Observe th at a range assignment r : S → Γ = { 0 , l 1 , l 2 . . . , l k } can be represented by the famil y of disks C = { C 1 , . . . , C ℓ } yielded by the p ositiv e v alues of r , and its energy cost is defined as cost ( C ) = ℓ X i =1 r 2 i where r i is the radius of C i (1) F urthermore, a feasible range assignment for the Min En- ergy Bro ad cast problem, with inp u t S and Γ, un iquely determines an l 1 -cov er for S having the same cost. Notice that the con vers e is not true in general. 2. THE LO WER BOUND In th is section, we provide a lo w er b ound on th e cost of any c overing range assignment for a random set S ⊆ R . Definition 1 L et Pr [ R, ǫ, l ] b e the pr ob ability that a r andom set S ⊆ R has an l -c over of c ost not lar ger than (1 − ǫ ) n π . Theorem 2 L et δ, p min and p max b e thr e e c onstants such that 0 < δ < 1 and 0 < p min ≤ p max < 1 . L et S ⊆ R b e any r andom set. Then, for any ǫ with 0 < ǫ < 1 , for sufficiently lar ge n , and for l ≥ 5(1 − ǫ ) 1 6 ǫ (1 − δ ) p min it holds that Pr [ R, ǫ, l ] ≤ 2 − 1 100 (1 − δ ) ǫp min n +log(4 n )+ t + e − δ 2 2 p min ⌊ n t ⌋ + t wher e t = 2 6 6 6 100 3 log “ 1 − p min p min p max 1 − p max ” + 1 ǫ (1 − δ ) p min 3 7 7 7 The above theorem clearly implies our low er b oun d stated in the In tro duction and it requires n o restricti on ab out the transmission-range set Γ bu t a low er b ound on l 1 = l that does not d epend on n . In particular, if ǫ is any p ositiv e constant then, for sufficiently large grids and a sufficiently large c onstant l (so l do es not dep end on n ), Pr [ R , ǫ, l ] is not larger than the invers e of an expon ential function in n . The theorem’s pro of makes use of the follo wing com binato- rial result. Lemma 3 L et R 1 , . . . , R t b e a p artition of the n p oints in R and let ( k 1 , . . . , k t ) b e any t -tuple of inte gers such that 0 ≤ k j ≤ | R j | = n j . Then, the numb er of subsets S of R such that | S ∩ R j | = k j ( 1 ≤ j ≤ t ) admitting an l -c over C with l ≥ √ e and cost ( C ) ≤ (1 − ǫ ) n π is at most 2 λ ( n,q,ǫ,l, t ) · t Y j =1 „ n j k j « wher e q = min n k j n j | 1 ≤ j ≤ t o and λ ( n, q , ǫ, l, t ) = − q l og e 1 − (1 − ǫ ) „ 1 + 1 2 l 2 + 1 √ 2 l « 2 ! + 1 − ǫ π l 2 log 64 eπ l 6 1 − ǫ ! n + log (4 n ) + t W e now provide a brief description of the information-the or etic approac h adopted to prov e the abov e lemma. Let S b e a subset of p oints of R satisfying th e hyp othesis of the lemma. By ex ploiting the l -cov er C , we will pro ve that S can b e enco ded into a b inary string cod ( S ) of length at most log 2 λ ( n,q,ǫ,l, t ) · t Y j =1 „ n j k j « ! The lemma thus follo ws since the num b er of these sets S can- not exceed the num b er of binary strings of the above length. Pr oof of Lemma 3. Let S b e a subset of p oints of R satis- fying the hyp oth esis of t h e lemma. Consider the l -co ver C ′ of S ha ving the same centers of C an d where eac h radius r in C is replaced with a radius r ′ = p ⌈ r 2 ⌉ . Clearly , t his change is negligible in terms of cost. W e now show that, thanks t o C ′ , S can b e enco ded into a binary string of length at most log 2 λ ( n,q,ǫ,l, t ) · t Y j =1 „ n j k j « ! Thus th e thesis follo ws by noting that the n umber of these sets S cannot exceed th e n umber of binary strings of the above length . The binary string cod ( S ) enco ding S is the concatenation of four substrings N U M , C E N , RAD and C OV . a) N U M rep orts the number m of centers of C . b) C E N rep orts information to recov er the ind ices of the m nod es of S th at are centers in C (we assume that the n points in t h e grid are num b ered from 1 to n ). c) R AD reports information t o reco ver the radii of th e m nod es in C ′ . d) C O V rep orts information to reco ver the indices of the nod es in S . W e no w explain how t hese data are enco ded and then b ound the length of each of the four substrings. a) The n umber m of cen ters in C is at most | S | ≤ n . Thus w e enco de it by a binary string of fixed length (i.e. ⌈ log( n + 1) ⌉ ). Hence | N U M | = ⌈ log( n + 1) ⌉ ≤ log n + 1 (2) b) The centers of C are a subset of the n p oints in R and so we enco de th em b y a string of fixed length, i.e. ‰ log „„ n m « + 1 «ı Since in the cov er, eac h of the m centers has radius at least l , it must hold ml 2 ≤ cost ( C ). F rom the hypoth - esis cost ( C ) ≤ (1 − ǫ ) π n , we get m ≤ (1 − ǫ ) n π l 2 (3) As for substring C E N , we obtain | C E N | = & log n m ! + 1 ’ ≤ log n m ! + 1 ≤ m log ǫn m + 1 ≤ (1 − ǫ ) n π l 2 log eπ l 2 1 − ǫ + 1 Observe th at in the ab ov e inequ alities w e used “ en m ” m ≤ „ eπ l 2 1 − ǫ « (1 − ǫ ) n πl 2 since th e funct ion ` ǫn x ´ x is increasing in the range [1 , n ]; then, from (3), m is in t he range [1 , (1 − ǫ ) n πl 2 ]. c) Let no w r ′ 1 , r ′ 2 , . . . r ′ m b e th e radii in C ′ arranged by in - creasing order of the indices of the m centers. In order to giv e the information on th e radii of C ′ , we enco de string ⌈ r 1 ⌉ 2 # ⌈ r 2 ⌉ 2 # . . . ⌈ r m ⌉ 2 # in binary where bit 0 is encoded as 00, bit 1 as 11 and the symb ol # as 01. W e thus get | RAD | = 2 m + 2 m X i =1 ⌈ log( ⌈ r i 2 ⌉ + 1) ⌉ ≤ 2 m + 2 m X i =1 ⌈ log( r i 2 + 2) ⌉ ≤ 2 m + 2 m X i =1 (log r i 2 + 2) = 2 log m Y i =1 r i 2 + 6 m ≤ 2 log „ cost ( C ) m « m + 6 m ≤ 2 log l 2 cost ( C ) l 2 + 6 m ≤ 4 (1 − ǫ ) n π l 2 log l + 6 (1 − ǫ ) n π l 2 = 4 (1 − ǫ ) n π l 2 log ( √ 8 l ) (4) In the abov e inequalities, we fi rst used Q m i =1 r i 2 ≤ “ cost ( C ) m ” m since the pro duct is max imized when all factors hav e the same v alue. Next, w e used “ cost ( C ) m ” m ≤ l 2 cost ( C ) l 2 since the fun ction “ cost ( C ) x ” x is increasing in the range [1 , cost ( C ) e ]; the v alue of m is in the range [1 , cost ( C ) /l 2 ]; ml 2 ≤ cost ( C ) and cost ( C ) /l 2 ≤ cost ( C ) /e for l ≥ √ e . Finally , we b ounded m using (3). d) I n order to enco de the no des in S , we use t strings. The j -th string en codes the k j p oin ts of S in R j . The k j p oin ts of S in R j co vered by C ′ are a subset of t h e n ′ j p oin ts in R j co vered by C ′ . Hence, we enco de these k j p oin ts with a binary string of length & log t Y j =1 „ n ′ j k j « + 1 ’ Since for integers a, b and c where a ≤ b ≤ c it holds that „ b a « ≤ ` b c ´ a „ c a « , we get | C OV | = t X j =1 ‰ log „ “ n ′ i k i ” + 1 «ı ≤ t X j =1 „ log “ n ′ i k i ” + 1 « ≤ log t Y j =1 “ n ′ i k i ” + t ≤ log 0 @ t Y j =1 n ′ j n j ! k j “ n j k j ” 1 A + t ≤ log t Y j =1 n ′ j n j ! k j + log t Y j =1 “ n j k j ” + t = log t Y j =1 1 − n j − n ′ j n j ! k j + log t Y j =1 “ n j k j ” + t ≤ log t Y j =1 e − k j n j ( n j − n ′ j ) + log t Y j =1 “ n j k j ” + t ≤ log e − P t j =1 q ( n j − n ′ j ) + log t Y j =1 “ n j k j ” + t = − q ( n − n ′ ) l og e + log t Y j =1 “ n j k j ” + t (5) where n ′ is the num b er of p oin ts of R cov ered by C ′ . W e now give an u pp er b ound for n ′ . Let x b e the number of p oin ts of R co vered by a disk D of radius r and, for each of these points, consider the square of area 1 centered in the p oint. These t squares are disjoint and are cov ered by the disk obtained by extending the radius r of d isk D t o r + 1 / √ 2 . So, th e num ber of p oin ts of R co vered by a disk of radius r is b ounded by π ( r + 1 / √ 2) 2 . Moreo ver, it holds that r ′ i = p ⌈ r i 2 ⌉ ≤ p r i 2 + 1 < r i + 1 2 l where the last inequality follo ws since r i ≥ l . W e thus obtain n ′ ≤ m X i =1 π „ r ′ i + 1 √ 2 « 2 ≤ m X i =1 π „ r i + 1 2 l + 1 √ 2 « 2 = π m X i =1 r i 2 + „ 1 2 l + 1 √ 2 « 2 m + 2 „ 1 2 l + 1 √ 2 « m X i =1 r i ! W e can n o w use H ¨ o lder’s inequality and obtain m X i =1 r i = m X i =1 ` r i 2 ´ 1 2 ≤ m „ P m i =1 r i 2 m « 1 2 = p m · cost ( C ) Since m ≤ cost ( C ) /l 2 , we get n ′ ≤ π cost ( C ) 1 + „ 1 2 l + 1 √ 2 « 2 1 l 2 + 2 „ 1 2 l + 1 √ 2 « 1 l ! ≤ (1 − ǫ ) „ 1 + 1 2 l 2 + 1 √ 2 l « 2 n F rom (5), w e get | C OV | ≤ − q log e 1 − (1 − ǫ ) „ 1 + 1 2 l 2 + 1 √ 2 l « 2 ! n + log t Y j =1 „ n ′ j k j « + t (6) W e now combine th e b ound s in (2), (4), (4) and (6) (resp ec- tively on t he length s of NUM, CEN, RA D and COV) and obtain | cod ( S ) | ≤ log n + 1 + (1 − ǫ ) n π l 2 log eπ l 2 1 − ǫ + 1 + 4 (1 − ǫ ) n π l 2 log( √ 8 l ) + log t Y j =1 „ n ′ j k j « + t − q log e 1 − (1 − ǫ ) „ 1 + 1 2 l 2 + 1 √ 2 l « 2 ! n = log(4 n ) + l og t Y i =1 “ n i k i ” + t + „ 1 − ǫ π l 2 log 64 eπ l 6 1 − ǫ − q l og e 1 − (1 − ǫ ) „ 1 + 1 2 l 2 + 1 √ 2 l « 2 !! n ✷ Pr oof of Theor em 2. W e assume n ≥ 1000 9 0 @ log “ 1 − p min p min p max 1 − p max ” + 1 δ (1 − δ ) p min ǫ 1 A 2 F or an y S , with S ⊆ R , define the binary function χ as follo ws χ ǫ,l ( S ) = 1 if S has an l -cover of cost at most (1 − ǫ ) n/π 0 otherwis e Clearly , it h olds t hat Pr [ R, ǫ, l ] = X S ⊆ R P R ( S ) χ ǫ,l ( S ) (7) Let us partition R into t regions R 1 , R 2 , . . . , R t where | R j | = n j such that for 1 ≤ j ≤ t j n t k ≤ n j ≤ l n t m and R j = ( j − 1 X i =1 n i + k | 1 ≤ k ≤ n j ) . Define µ j as the exp ected num ber of p oints in j , i.e., µ j = P i ∈ R j p i . Let F b e the family of subsets of R having, in eac h region, a num b er of p oin ts not too small w.r.t. the exp ected number, i.e, F = { S ∈ 2 R | | S ∩ R j | ≥ (1 − δ ) µ j , 1 ≤ j ≤ t } F rom (7) we get Pr [ R, ǫ, l ] = X S ⊆F P R ( S ) χ ǫ,l ( S ) + X S ⊆ 2 R −F P R ( S ) χ ǫ,l ( S ) (8) W e start giving an upp er b ound on the first addend of the righ t-hand of the ab ov e equation. Let A = { ~ k = ( k 1 , . . . , k t ) | ~ k ∈ Z t and (1 − δ ) µ j ≤ k j ≤ n j , 1 ≤ j ≤ t } and, for eac h ~ k ∈ A , defi ne F ~ k = { S ∈ F | | S ∩ R j | = k j , 1 ≤ j ≤ t } Consider any set S ~ k ∈ F ~ k such that P R ( S ~ k ) ≥ P R ( S ) for every S ∈ F ~ k . Then, X S ⊆F P R ( S ) χ ǫ,l ( S ) = X ~ k ∈ A X S ∈F ~ k P R ( S ) χ ǫ,l ( S ) ≤ X ~ k ∈ A X S ∈F ~ k P R ( S ~ k ) χ ǫ,l ( S ) = X ~ k ∈ A P R ( S ~ k ) X S ∈F ~ k χ ǫ,l ( S ) ≤ X ~ k ∈ A P R ( S ~ k )2 λ „ n, min k j n j | 1 ≤ j ≤ t ff ,ǫ,l,t « t Y i =1 „ n i k i « (9) where t h e last step follow s from Lemma 3. F un ction λ is decreasing in q and min 1 ≤ j ≤ t k j n j ff ≥ min 1 ≤ j ≤ t (1 − δ ) µ j n j ff ≥ min 1 ≤ j ≤ t (1 − δ ) p min n j n j ff = (1 − δ ) p min W e thus get X S ⊆F P R ( S ) χ ǫ,l ( S ) ≤ X ~ k ∈ A P R ( S ~ k )2 λ ( n, (1 − δ ) p min ,ǫ,l,t ) t Y i =1 “ n i k i ” = = 2 λ ( n, (1 − δ ) p min ,ǫ,l,t ) X ~ k ∈ A P R ( S ~ k ) t Y i =1 “ n i k i ” = = 2 λ ( n, (1 − δ ) p min ,ǫ,l,t ) X ~ k ∈ A X S ∈F ~ k P R ( S ~ k ) (10) Assume without loss of generalit y that the p oin ts in R are num bered in increasing order w.r.t. their probability i.e. 0 < p min = p 1 ≤ p 2 ≤ . . . p n = p max < 1. Let q 0 = p min ≤ q 1 ≤ q 2 . . . ≤ q t = p max where q j = max { p i | i ∈ R j } , for 1 ≤ j ≤ t . Consider an y set S ∈ F ~ k , then P R ( S ~ k ) = t Y j =1 P R j ( S ~ k ∩ R j ) = t Y j =1 0 @ Y i ∈ S ~ k ∩ R j p i Y i ∈ R j − S ~ k (1 − p i ) 1 A = t Y j =1 0 @ Y i ∈ S ∩ R j p i Y i ∈ R j − S (1 − p i ) Y i ∈ ( S − S ~ k ) ∩ R j 1 − p i p i Y i ∈ ( S ~ k − S ) ∩ R j p i 1 − p i 1 C A ≤ t Y j =1 0 B @ P R j ( S ∩ R j ) Y i ∈ ( S − S ~ k ) ∩ R j 1 − q j − 1 q j − 1 Y i ∈ ( S ~ k − S ) ∩ R j q j 1 − q j 1 C A = t Y j =1 P R j ( S ∩ R j ) „ 1 − q j − 1 q j − 1 « | ( S − S ~ k ) ∩ R j | „ q j 1 − q j « | ( S ~ k − S ) ∩ R j | ! ≤ t Y j =1 „ P R j ( S ∩ R j ) „ 1 − q j − 1 q j − 1 q j 1 − q j « n j « ≤ t Y j =1 P R j ( S ∩ R j ) t Y j =1 „ 1 − q j − 1 q j − 1 q i 1 − q j « ⌈ n t ⌉ = P R ( S ) „ 1 − p min p min p max 1 − p max « ⌈ n t ⌉ (10) implies that X S ⊆F P R ( S ) χ ǫ,l ( S ) ≤ 2 λ ( n, (1 − δ ) p min ,ǫ,l,t ) X ~ k ∈ A X S ∈F ~ k P R ( S ) „ 1 − p min p min p max 1 − p max « ⌈ n t ⌉ = 2 λ ( n, (1 − δ ) p min ,ǫ,l,t ) „ 1 − p min p min p max 1 − p max « ⌈ n t ⌉ · X S ∈F P R ( S ) ≤ 2 λ ( n, (1 − δ ) p min ,ǫ,l,t ) „ 1 − p min p min p max 1 − p max « ⌈ n t ⌉ (11) Now we p ro vide an upp er b oun d on λ ( n, (1 − δ ) p min , ǫ, l , t ) = ( f ( l ) − g ( l )) n + log(4 n ) + t where f ( x ) = 1 − ǫ π x 2 log 64 eπ x 6 1 − ǫ and g ( x ) = − (1 − δ ) p min log e 1 − (1 − ǫ ) „ 1 + 1 2 x 2 + 1 √ 2 x « 2 ! F unction f ( x ) is decreasing for x ≥ 5(1 − ǫ ) 1 6 (1 − δ ) p min ǫ , so it holds that f ( l ) ≤ (1 − ǫ ) 2 3 π „ (1 − δ ) p min ǫ 5 « 2 log 64 eπ „ 5 (1 − δ ) p min ǫ « 6 ! Moreo ver , for every a, c > 0, it holds that a log c a ≤ c e log e . Thus, by setting a = δp min ǫ 5 and c = (64 eπ ) 1 6 , we get f ( l ) ≤ 12 5( eπ ) 5 6 (1 − δ ) p min ǫ log e (12) F unction g ( x ) is increasing for x > 1 and, by a simple cal- culus, we obtain g ( l ) ≥ 5 − √ 2 − 1 5 (1 − δ ) p min ǫ log e (13) F rom (12) and (13), we obtain λ ( n, (1 − δ ) p min , ǫ, l , t ) ≤ − 7 100 (1 − δ ) p min ǫn log e +log(4 n )+ t Moreo ver since l n t m log „ 1 − p min p min p max 1 − p max « < 6 100 (1 − δ ) p min nǫ (11) implies X S ⊆F P R ( S ) χ ǫ,l ( S ) ≤ 2 − 1 100 (1 − δ ) p min ǫn log e +log(4 n )+ t (14) W e no w giv e an u pp er b ound on the second addend in (8). Let µ = m in { µ 1 , µ 2 , . . . , µ t } ≥ p min ⌊ n t ⌋ , then X S ⊆ 2 R −F P R ( S ) χ ǫ,l ( S ) ≤ X S ⊆ 2 R −F P R ( S ) = 1 − X S ⊆F P R ( S ) = 1 − t Y j =1 P R ( | S ∩ R j | ≥ (1 − δ ) µ j ) = 1 − t Y j =1 (1 − P R ( | S ∩ R j | < (1 − δ ) µ j )) ≤ 1 − t Y j =1 „ 1 − e − δ 2 2 µ j « ≤ 1 − t Y j =1 „ 1 − e − δ 2 2 µ « = 1 − „ 1 − e − δ 2 2 µ « t ≤ te − δ 2 2 µ e te − δ 2 2 µ = e ln t − δ 2 2 µ + te − δ 2 2 µ ≤ e t − δ 2 2 µ ≤ e − δ 2 2 p min ⌊ n t ⌋ + t (15) Finally , by com bining (8), (14) and (15), the theorem fol- lo ws. ✷ 3. AN ALMOST OPTIMAL SOLUTION W e now provide an efficient construction of a coveri ng range assignmen t for a random set S ⊆ R of energy cost very close t o the low er b ound (1 − ǫ ) n/π . Then w e will trans- form it, with additional cost o ( n ) only , into a feasible broad- cast range assignment th at u ses Θ(log( n/ log n )) ranges and such th at the (p ositiv e) smallest among them, i.e. l 1 , is Θ( √ log n ). The disk c overing construc tion. The construction of the co vering is recursive and exploits a tiling of th e square with octagons and triangles. The sq uare R of side √ n is partitioned in to four triangles and an o ctagon (see Figure 1); up to when th ere exists a tri- angle with side c √ log n , it is further on partitioned into fi ve triangles (three small an d tw o b ig triangles) and an o ctagon (see Figure 2). Starting from this partition, it is p ossible to pro duce a disk co vering O C T as follo ws (in the sequel, a range assignmen t is seen as a di sk assignmen t with centers on nodes in S ): • for each triangle of the partition, if it contains at least one no de, then one of them is selected as center of a disk ha ving radius c √ 2 log n . Observe that this disk co vers any other point inside th e same triangle. • for each o ctagon, if it con tains at least one p oin t t hat is not cov ered yet, then Lemma 5 implies that there l l' Figure 1: The starting configuration of the partition of the square into triangles and an o ctagon. x a x x b x c Figure 2: The general step of the partition pro ce- dure of the square into triangles and o ctagons. is a nod e at d istance O ( √ log n ) to the center of th e octagon, w.h.p. Let this no de b e th e center of a disk having radius r + O ( √ log n ), where r is the radius of the disk that circumscrib es t he considered o ctagon; th e introduced d isk co ver s all p oints in th e octagon. Theorem 4 Given a r andom set S , then, w.h.p., disk c ov- ering OC T has c ost cost ( OC T ) ≤ 1 , 12 n π + o ( n ) Pr oof. Let S b e th e set of all th e o ctagons in the parti- tion, and for each s ∈ S call r s the radius of the disk th at circumscribes o ctagon s . Denoting by t b e th e num b er of triangles in the partition, by construction it holds t hat: cost ( C ) ≤ 2 tc 2 log n + X s ∈ S ( r s + c p log n ) 2 (16) Let l b e the side of th e triangles created d uring the fi rst step and let l ′ b e th e side of the first o ctagon (see Figure 1). The follo wing equations hold: 2 l + l ′ = √ n and l ′ = √ 2 l . F rom these, we derive: l = √ n 2+ √ 2 l ′ = √ 2 n 2+ √ 2 (17) The recursive step depicted in Figure 2 pro duces triangles of t wo different sides and an o ctagon. Let x a , x b and x c b e the lengths of the sides of the bigger triangles, t h e smaller triangles an d the o ctagon, resp ectively . These lengths are tied from the follo wing relationships: x c = √ 2 x b , x a = x b + x c and x a + 2 x b + x c = l , implying: x a = l √ 2+1 x b = l ( √ 2+1) 2 x c = √ 2 l ( √ 2+1) 2 (18) F rom (17) and (18), th e triangles of the partition, generated during step i , ha ve side length x i = √ 2 n (2+ √ 2)( √ 2+1) i , where 0 ≤ i < k and k is the smallest integer val ue such that x i < c √ log n , i.e. , k = ‰ 1 2 log (1+ √ 2) n c 2 (2 + √ 2) 2 log n ı (19) Observe that all o ctagons (but the first one) of the partition are prod uced by partitioning some triangle of side length x i , 0 ≤ i < k . Denote by r the radius of the disk that circumscribes the first o ctagon, b y r i the radius of the disk that circumscrib es th e o ctagon pro duced by partitioning a triangle of side length x i , and by t i the number of such triangles. Then , w e can rewrite (16) as follo ws: cost ( C ) = t · o (log n ) + q − 1 X j =0 k − 1 X i =0 t i ( r 2 i + 2 c p log nr i + c 2 log n ) + ( r + c log n ) 2 (20) W e remind th at the radius of th e disk that circumscribes a regular o ctagon h a ving side l is l √ 2 − √ 2 . So, we can use (17) and (18) to compute t h e follow ing v alues of r and r i , respectively , where 0 ≤ i < k : r = √ 2 n (2+ √ 2) √ 2 − √ 2) r i = q 2 n 2 − √ 2 1 ( √ 2+1) i +2 1 2+ √ 2 (21) In order to comput e the v alue of t i , observe that trivially t 0 = 4 ( see Figure 1) and t 1 = 8 ( see Figure 2). At step i , t i = 2 t i − 1 + 3 t i − 2 . Unrolling th e recursion we get: t i = 3 i +1 + ( − 1) i ≤ 3 i +1 + 1 (22) In order to ev aluate cost ( C ), we bound all terms app earing in (20) b y exploiting (21) and (22): k − 1 X i =0 t i r 2 i < n (2 + √ 2)( √ 2 + 1) 4 + ∞ X i =0 3 i +1 + 1 ( √ 2 + 1) 2 i = n (2 + √ 2)( √ 2 + 1) 4 ( √ 2 + 1)(4 √ 2 + 3) 2 √ 2 < (64 − 45 √ 2) n 4 √ 2 (23) ( r + c log n ) 2 = (2 − √ 2) n 2 + o ( p n log n ) (24) By combining Equations (22) and (19) w e obtain: t = 3 k +1 + 1 ≤ 9 „ 1 c (2 + √ 2) « 1 log 3 ( √ 2+1) „ n log n « 1 2 log 3 ( √ 2+1) = o „ n log n « (25) where the last step is true b ecause 1 2 log 3 ( √ 2+1) < 1. F ur- thermore, 2 c p log n k − 1 X i =0 t i r i = o ( n ) (26) Equation (22) implies th at P k − 1 i =0 t i < t k ; Then, from (25) w e get: c 2 log n k − 1 X i =0 t i = o ( n ) (27) By combining formulas (20), (23), ( 24), (26) and (27) we conclude t hat cost ( C ) = (64 − 45 √ 2) n 4 √ 2 + (2 − √ 2) n 2 + o ( n ) < 1 . 1204 n π + o ( n ) ✷ F r om Cover ing to Br oadca sting. In order to guaran tee that the pro duced co vering b ecomes a b roadcast, w e need to connect the source to the disk centers in OC T . W e start from the source, lo cated in any place of the square, and build a chain of d isks tow ards th e center of the grid. Thanks to Lemma 5, th e maximum radius of suc h d isks can be bou n ded by O ( √ log n ), w.h.p. (see Fig. 3 ). W e now show that the additional cost due to this construction turns out to b e sub- linear. s Figure 3: Constr uction of the chain of disks con- necting the source to the center of the first disk . The cost of th e connection b etw een t h e source and th e cen- ter of th e squ are is O ( √ n √ log n ) w.h.p. Then we hav e t o connect all t he other centers to p oints already reached by the information sent from the source. The t otal cost due to this step is b ound ed by P k j =1 t j x j O ( √ log n ). By replacing the formulas for t j and x j w e get: k X j =1 t j x j O ( p log n ) = O ( p log n ) k X j =1 (3 j +1 + 1)( √ 2 − 1) j l 0 = O ( p log n ) √ n 2 + √ 2 ( k X j =1 3 j +1 ( √ 2 + 1) j + k X j =1 ( √ 2 − 1) j ) = O ( p log n ) √ n 2 + √ 2 Θ((3( √ 2 − 1)) k +1 ) = O ( p log n ) √ n 2 + √ 2 ( 1 c (2 + √ 2) r n log n ) 1 log 3( √ 2 − 1) ( √ 2+1) This cost is sub-linear since it is O ( n 0 . 63 ). It is not hard to verif y th at th e ab ov e ov erall construction can b e p erformed in O ( n log n ) time. 4. AN EFFICIENT DISTRIBUTED PR O TO- COL Let us consider the fol low ing simple algorithm to construct a broadcast range assignment. Let l be any range in Γ such that l ≥ 2 √ 2 c √ log n where c is the constant determined by Lemma 5 below. Algorithm cell-alg . a. Grid R is partitioned into squar e c el ls of side length λ = l/ (2 √ 2). b. In every non-empt y cell, choose one of its no des and assign range l to it. This no de is called the pivot o f the cell. c. The cell cont aining the source wil l ha ve the source as pivot . d. Al l other nodes hav e range 0. The pro of of the follo wing lemma is a simple application of Chernoff ’s Bound. Lemma 5 L et p min , p max , and c b e thr e e c onstants such that 0 < p min ≤ p max < 1 and c ≥ 16 /p min . L et S ⊆ R b e a r andom grid. Consider the p artition of R into squar e cells of side length λ wher e c √ log n ≤ λ ≤ √ n . Then, a c onstant γ > 0 exists such that every c el l c ontains w.h.p. at l e ast γ λ 2 no des. Constant γ c an b e set as (1 / 2) p min . It is then easy to prove the follow ing Theorem 6 Algorithm cell-alg y ields a br o adc ast r ange assignment r that i s w.h.p. fe asible and its c ost satisfies cost ( r ) = n λ 2 · (2 √ 2 λ ) 2 = 8 n Thanks to our low er b oun d in Theorem 2, cell-alg yields c onstant app ro ximation. Making it in distributed wa y. Algorithm cell-alg can b e con verted, without p aying any extr a ener gy c ost , into an efficien t, ener gy-lo ad b alanc e d proto col that p erforms a se- quenc e of br o adc ast op er ations . W e describ e the proto col for the man y-broadcast scenario and, thus, besides minimizing the en ergy spent by a single broadcast operation, w e aim to evenly distribute t he transmission task among all no des (but t h e source). According to th e standard radio communication mo del [2, 11, 26], we assume that no des act in discrete un iform time steps and are n on sp ontaneo us. Ho w ever, we assume a w eaker, lo c al synchronous model: if, at a given time step t , t h e range of a message transmission cov ers a cell, then, at time step t + 1, (only) the no des of that cell are activ ated and, so, they will agree on the same t ime step. W e assume that every no de v kn o ws the num ber n of p oints and its relativ e coordin ates in the square grid R . F rom its relativ e coordinates eve ry no de computes a un ique lo c al label with respect to its cell. These local labels va ry from 1 to λ 2 . The k - th message sent by the source is denoted as m k . Phase k consists of the sequence of time steps where m k is broad- casted. W e assume that m k conta ins the v alue k . The proto col performs, in parallel, t w o tasks: i) it constru ct s a broadcast communication graph starting from the source and ii ) transmits the source message along th is graph to all nod es. The procedure is executed for ev ery broadcast operation from source s . Every nod e keeps a local counter counter initially set to − 1. Procedure Bro adcast ( m k ) Source s transmits, with range l , h m k , i i where i is the index of its cell. All nodes (but s ): • If ( k ≤ γ λ 2 ) then ( γ is the constan t of Lemma 5) – When a node v r eceiv es, for the first time w. r.t. phase k , h m k , i i from the pivo t of a neigh bor cell i , it becomes activ e. – An activ e node, at every time step, incremen ts its local coun ter coun ter by one and chec ks whether i ts local label is equal to the v alue of i ts counter . If this is the case, it becomes the pivot of its cell and transmi ts, with range l , h m k , j i where j is the index of its cell. – When an activ e node in cell i r eceiv es h m k , i i , it (so the piv ot as well) records i n a lo c al arr ay P [ k ] the current v alue of i ts counter , i.e. the lo cal lab el of the pivo t, and b ecomes i nactive. • else (i. e. ( k > γ λ 2 )) – When a node v r eceiv es, for the first time w. r.t. phase k , h m k , i i fr om the pivot of a neigh b or cell i , it c hec ks if its lo cal lab el is equal to P [ k mo d γ λ 2 ]. If this i s the case, it becomes the pivot of its cell and transmits, with range l , h m k , j i where j is the index of its cell. F act 7 Even though no des initial ly do not know anything ab out e ach other, al l no des i n the same c el l ar e activate d (and disactivate d) at the same time step; so, their lo c al c oun- ters shar e the same value at every time step. F urthermor e, after the first γ λ 2 br o adc ast op er ations (i.e. phases), al l no des i n the same c el l know the set P of pivots of that c el l. More precisely , if j 0 < j 1 < j 2 < . . . j k . . . are the lo- cal lab els of the no des in a cell, then, during t h e fi rst γ λ 2 broadcast op erations (i.e. phases), the pivot of th e cell at phase k will be the no de having local lab el j k . Procedure Bro ad cast has the follo wing prop erties. Energy Cost. As for each single broadcast op eration, Bro adcast yields a b roadcast range assignmen t equiv alen t to th at of cell-alg . So, Theorem 6 holds as w ell. W ork Comple xity . Definition 8 L et { g 1 , g 2 , . . . , g h } b e the set of al l messages sent by the no des ac c or ding to a pr oto c ol P . Then, the work complexity of P is h X i =1 l 2 i , wher e l i is the r ange use d to send g i The ov erall number of no de transmissions (i.e. the mes- sage complexit y) of every execution of Bro adcast is 8 n/l 2 . Eac h transmission h as range l , so th e w ork complexity is not larger th an 8 n . As for the man y-broadcast scenario, our lo wer b oun d in The- orem 2 easily implies that a wo rk k (1 − ǫ )( n/π ) is w.h.p. required to p erform a sequence of k broadcasts (since th e lo w er b ound holds for t he energy cost). I t follo ws that our protocol ac hieves an almost optimal work complexity for the many-broadcast op eration as w ell. Load Bal ancing and Netw ork Lifetime. The exp en- sive pivot’s task is evenly assigned, w.h.p., to γ λ 2 nod es (see L emma 5) in the same cell by using a round robin sc hedule. This is crucial when the num b er of broadcasts increases and no des hav e limited b attery charge. As for th e many-broadcast op eration, it is p ossible to show that our protocol achiev es an almost maximal lifetime according to the consump tion mod el in [7, 6]. In this model, the goal is to maximize the lif etime of the netw ork while guarantee - ing, at an y ph ase k , a broadcast op eration from the source. F ormally , each n ode v is in itially equ ipp ed with a battery charg e 3 B > 0. Whenever a no de transmits with range l , its battery charg e is reduced by amount β · l 2 where l denotes the range assigned to no de v and β > 0 is a fix ed constan t dep ending on the adopted technology . W e assume β = 1, how ever, all our results holds for any β > 0. Then, the Max LifeTi me problem is to maximize the num- b er of indep endent broadcast operations till some no d e will die (i.e. its battery charge b ecomes 0). In [7], Max Life- Time is sho wn to b e NP-hard. Theorem 9 B r o adcast p erforms a se quenc e of indep en- dent br o adc ast op er ations whose length i s only a c onstant factor smal ler than the optimum, w.h.p. Sketch of pr o of . W e h a ve already observed that th e work complexity of B r oadcast for any single broadcast op era- tion is not larger than α opt , where α is a positive constant 3 Here w e assume t hat, at the very beginning, all nod es are in th e same energy situation. and opt is the optimal work complexity . So, th e maximal num ber of in d epen dent broadcast operations is not larger than nB / opt . Thanks to the lo cal round robin strategy in every cell, the energy load of the many-broadcast op eration is well balanced ov er at least a (large) constant fraction η of all no des. So the number of broadcast op erations p erform by B r oadcast is at least ηnB α opt = ( η /α ) nB opt , w.h.p. ✷ (Amortized) Com pletion Time . Theorem 10 The amortize d c ompletion time (i.e. the av- er age numb er of time steps to p erform one br o adc ast op er a- tion) over a se quenc e of T br o adc ast op er ations is w.h.p. O ( l √ n/T + √ n/l ) Sketch of pr o of . F or a singl e broadcast op eration p erformed by Bro adcast , we define the delay of a cell as t he num b er of time steps from its activ ation time till the selection of its pivot. Ob serv e that the sum of delays in trod uced b y a cell during th e first γ λ 2 broadcasts is at most λ 2 = Θ( l 2 ). Then, the delay of an y cell b ecomes 0 for all broadcasts after the first γ λ 2 ones. Moreo ver, a broadcast can pass o ver at most O ( √ n/l ) cells. By assuming that a maximal length path (this length b eing Θ( √ n/l )) together with maximal cell de- la y can b e found in each of the fi rst min { γ λ 2 , T } broadcasts, w e can b ound the maximal ov erall dela y with O ( l √ n ) (28) Finally , the number of time steps required by ev ery broad- cast without dela ys is O ( √ n/l ) (29) since the length of an y path on the broadcast tree is O ( √ n/l ). By combining (28) and ( 29), we get the theorem boun d. ✷ F or brevity’s sake, the amortized completion time has been analyzed without considering the i nterfer enc es due to c ol l i- sions among p iv ot transmissions [2]. H o w ever, in order to a void such collisions, we can further organize Bro adcast into iterative stages : in every stage, only cells with not col- liding p iv ot transmissions are active. Since th e num b er of cells that can interfere with a given cell is constant, this further scheduling will increase the ov erall time by a con- stant factor only . This iterativ e pro cess can b e efficiently p erformed in a d istributed wa y since every node know s n and its position, so it kno ws its cell. Corollary 11 The c ompletion time of one single br o adc ast op er ation is O ( l √ n ) . The wo rst scenario for our proto col o ccurs when T is small, sa y T = O (1). Indeed, assume that a transmission range l = Θ( √ log n ) is av ailable in Γ, t h en w e get an amortized completion time O ( √ n log n ) that is a factor log n larger then the optimum. Notice that in this case, the net wo rk diameter is Θ( p n/ log n ) w.h.p. Whenever T = Ω(log n ), w e instead get O ( p n/ log n ) amor- tized completion time which is optimal. 4.1 Experimen tal results In t h is subsection, w e p resen t the exp erimental results w e hav e obtained b y runn ing Algorithm cell-alg . W e hav e generated 1000 instances for every side length √ n ∈ { 13 , 20 , 25 , 30 , 50 , 100 } and for no de-pr ob abili ty p ∈ { 0 . 2 , 0 . 5 } . As usual, our im- plementatio n b enefits of some parameter tun ing and opti- mization: the pivot no d e (b ut the source no de) inside every cell is the one closer to the center of the cell and useless, re- dundant ranges are remov ed. These tasks can b e p erformed also by th e d istributed protocol, after the first phase (i.e. for t ≥ γ λ 2 ), without p a ying an y extra energy cost since, after that time, every node of a cell k no ws all its cell neighbors. Moreo ver , the transmission range l is set 4 to √ 2 log n , while the cell-size parameter λ is set to log n . Notice that, accord- ing to such c hoices, the feasibilit y (i.e., th e existence of a path from th e source no de to all other no des in th e indu ced comm unication graph) is tested too. In T able 1 (columns ” # of feasible sol.” ), th e num b er of feasible solutions for th e different combinations of n and p are rep orted. The solution costs of cell-alg are compared to the cost of the solution retu rned by t he centralized MST-based algo- rithm. W e remind that while t he en ergy cost of cell-alg is an upp er b ound on the work complexit y of our distributed proced ure Bro ad cast the energy cost of the MST-b ased solution do es not provide any information ab out the work complexity of its distributed implemen tations ( this can b e muc h larger). T able 1 sho ws, for all chosen va lues of p and √ n , the min i- mum, av erage and maxim um ratio b et we en th e costs of th e solutions returned by th e tw o algorithms. As for ce ll-alg , only the costs of f e asible solutions are considered. 5. REFERE NCES [1] C. Ambuehl. An optimal b ound for the MST algorithm to comput e energy efficient broadcast trees in wireless netw orks. In Pro c. of 32th ICALP , 1139–1150, 2005. [2] R . Bar-Y ehuda, O. Goldreich, and A . Itai. On the time-complexity of broadcast in multi-hop radio netw orks: An exp onential gap b et we en determinism and randomization, JCSS , 45, 104-126, 1992. [3] R . Bar-Y ehuda, A. I sraeli, and A. It ai. Multiple comm unication in multi-hop radio net wo rks, SI COMP , 22 (4), 875-88 7, 1993. [4] M. Cagali, J. Hubaux, and C. Enz. Minimum-energy broadcast in all -wireless net wo rks: np-completeness and distribution issues. In Pro c. of ACM MO BI COM , 172–182 , 2002. [5] T. Calamoneri, A. Clemen ti, M. D i Ianni, M. Lauria, A. Monti, and R. S ilv estri. Minimum Energy Broadcast and Disk Co ver in Grid Wireless N et wo rks. In Proc. of SIROCCO’06 , L N CS, 2006. [6] T. Calamoneri, A. Clemen ti, E. F usco and R. Silvestri. Maximizing th e num b er of broadcast op erations in static random geometric ad-hoc net w orks. In Proc. of OPODIS , LNCS, 200 7. 4 Notice that, for th e tested sizes n , this range is smaller than the threshold 2 √ 2 c √ log n defined in Section 4: this is the reason wh y the feasibil ity rate is n ot 100% fo r larg e n . cost ( cell-alg ) vs cost ( M S T ) p = 0 . 2 p = 0 . 5 √ n # of f easible sol. min a v erage max # of feasible sol. min a verage max 13 744/1000 2.044 2.072 2.118 100 0/1000 2.544 2.808 3.086 20 892/1000 1.896 2.092 2.145 999/1000 2.506 2.666 2.994 25 762/1000 2.040 2.127 2.164 998/1000 2.341 2.617 2.808 30 740/1000 2.163 2.217 2.242 997/1000 2.512 2.610 2.666 50 858/1000 2.313 2.398 2.450 999/1000 2.673 2.824 2.949 100 967/1000 2.300 2.347 2.352 10 00/1000 2.604 2.659 2.702 T abl e 1: Exp erimental results. [7] G. Calinescu, S. Kap oor, A. Olshevsk y , A. Z eliko vsky . Netw ork lif etime and p ow er assig nment in ad ho w wireless n et wo rks. In Proc. of ESA , LN CS, 2003. [8] I. Caragiannis, M. Flammini, and L. Moscardelli. A n exp onential improv emen t on the MST heuristic for the minim um en ergy broadcast p roblem. In Proc. of ICALP , LNCS, 2007. [9] M. Cardei and D-Z D u. Improving wireless sensor netw ork lif etime through p ow er organizatio n. Wir eless Networks , 11, 333– 340, 2005. [10] M. Cardei, J. W u, and M. Lu . Improving n et wo rk lifetime using sensors with ad justable sensing ranges. Int. J. Sensor Networks , 1 (1/2), 41–4 9, 2006. [11] M. Chrobak, L. Gasieniec, an d W. Ry tter. F ast broadcasting and goss iping in radio net wo rks, J. Algor ithms , 43(2), 177–189, 2002. [12] A. Clementi, P . Crescenzi, P . P enna, G. Rossi and P . V occa. On the Complexity of Computing Minimum Energy Consump t ion Broadcast S ubgraphs. I n Pro c. of 18th ST A CS , LNCS 2010, 121–131 , 2001. F ull ve rsion in http://www .dia.unisa.i t/ ∼ penna/no-bl ood-for-oil.html . [13] A. Clementi, P . Penna, and R. Silves tri. On the P ow er Assignment Problem in R adio Netw orks. ACM Mobil e Networks and Applic ations (MONET) , 9, 125–140 , 2004. [14] P . Crescenzi and V. Kann, A Compen d ium of N P Optimization Problems. http://www .nada.kth.se / ∼ viggo/wwwcom pendium/ . [15] A. Dessmark and A. Pelc. Broadcasting in geometric radio netw orks. Journal of Discr ete Algorithms , 2006. [16] O. Egecioglu and T. Gonzalez. Minim um-energy broadcast in simple graphs with limited no de p ow er. In Proc. of IASTED PDCS , 2001. [17] A. Ephremides, G.D. Nguyen, and J.E. Wieselthier. On the Construction of Energy- Efficien t Broadcast and Multicast T rees in Wireless Netw orks. In Proc. of 19th IEEE INFOCOM , 585–594, 2000. [18] M.Flammini, R.Klasing, A.Nav arra, S .P erennes. Improv ed A pproximatio n Results for the Minimum Energy Broadcasting Problem, Algorithmic a , 49(4), 318–336 , 2007. [19] M. Flammini, A. Nav arra, and S. Perennes. The Real Approximation F actor of t h e MST H euristic for th e Minim um Energy Broadcast. In Proc. of WEA , 22–31, 2005. [20] A. D. Flaxman, A. M. F rieze, and J. C. V era. On the a verage case p erformance of some greedy approximation algorithms for the uncapacitated faci lity location problem. In Proc. of 37-th ACM STO C , 441–449 , 2005. [21] R. Gallager, P . Humblet, and P . Spira. A distributed algorithm for minim um spanning tree. ACM T r ans. on Pr o gr. L anguages and Systems , 5 (1), 66–77, 1983. [22] P . Gu pta and P .R. K umar. Critical pow er for asymptotic conn ectivit y in wireless netw orks. In Sto chastic Analysis, C ontr ol, Optimization and Applic ations . Birkhauser, 547–566, 1999. [23] M. Khan , G. Pa ndurangan, and V.S.A. Kumar. Distributed A lgorithms for Constructing A pproximate Minim um Spanning T rees in Wireless S ensor Netw orks. IEEE T r ansactions on Par al lel and Distribute d Systems , 2008, to appear. [24] L. M. Kirousis, E. Kranakis, and D. Krizanc, and A. Pelc. Po wer Consumption in P ack et Radio Netw orks. The or etic al C om puter Sci enc e , 243 , 289–30 5, 2000. [25] G. Kozma, Z. Lotker, M. Sharir, and G. Stupp. Geometrically aw are communication in random wireless netw orks. In Pro c. of 23r d ACM PODC , 2004 . [26] E. Kranakis, D. Krizanc, and A. Pelc. F ault-toleran t broadcasting in radio netw orks. Journal of Algorith ms , 39, 47–67, 2001 . [27] X. Li, G. Calinescu and P . W an. Distributed construction of planar spanner and routing for ad ho c wireless netw orks. Pro c. of INFOCOM , 2002. [28] X. Li. Localized construction of low wei ghted structures and its applications in in wirele ss ad-ho c netw orks. A CM Wir eless Networks , 200 3. [29] X. Li, Y. W ang, W. S ong, and O. F rieder. Localized lo w-w eight graph and its applications in wireless ad-h o c netw orks. In Pro c. of IEEE INF OCOM , 2004. [30] Z. Lotker and A . Nav arra. Managing R an d om Sensor Netw orks b y means of Grid Emulation. In Proc. of NETWORKING , LN CS 3976, 2006. [31] D. Niculescu and B. N ath. Ad-H oc Posi tioning System (APS). In Proc. of IEEE GLOBECOM , 2001. [32] K. Pahla va n and A. Levesque. Wir eless Information Networks . Wiley- I nters cience, 1995. [33] M. Penrose. R andom Ge ometric Gr aphs . Oxford Universit y Press , 2003. [34] P . S an ti and D. M. Blough. The Critical T ransmitting Range for Connectivit y in Sparse Wireless A d Ho c Netw orks IEEE T r ans. on Mobile Computing , 2: 25-39, 2003. [35] R. Ramanathan and R. Rosales-Hain. T op ology contro l of m ultihop wireless netw orks u sing transmit p o w er ad justment. In Proc. of IEEE-INFOCOM , 2000. [36] G. Calinescu, X.Y. Li, O. F rieder, and P .J. W an . Minim um-Energy Broa dcast Routing in S t atic A d Ho c Wireless Netw orks. In Pro c. of 20th IEEE INFOCOM , 1162–11 71, April 2001. [37] Y. W ang, X . Li, and O. F rieder. Distributed Spanner with b ound ed d egree for wireless ad ho c n et w orks. I EEE T r ans. on Computers , 53(1 2): 1629–1 635, 2004. [38] J. W u and S. Y ang. Cov erage and conn ectivit y in sensor netw orks with adjustable ranges. Pro c. of Intern. Workshop on Mobile and Wir eless Networking (MWN) , 2004.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment