The Capacity Of Two Way Relay Channel
This paper investigates the capacity of a wireless two way relay channel in which two end nodes exchange information via a relay node. The capacity is defined in the information-theoretic sense as the maximum information exchange rate between the two…
Authors: Zhang Shengli, Soung Chang Liew
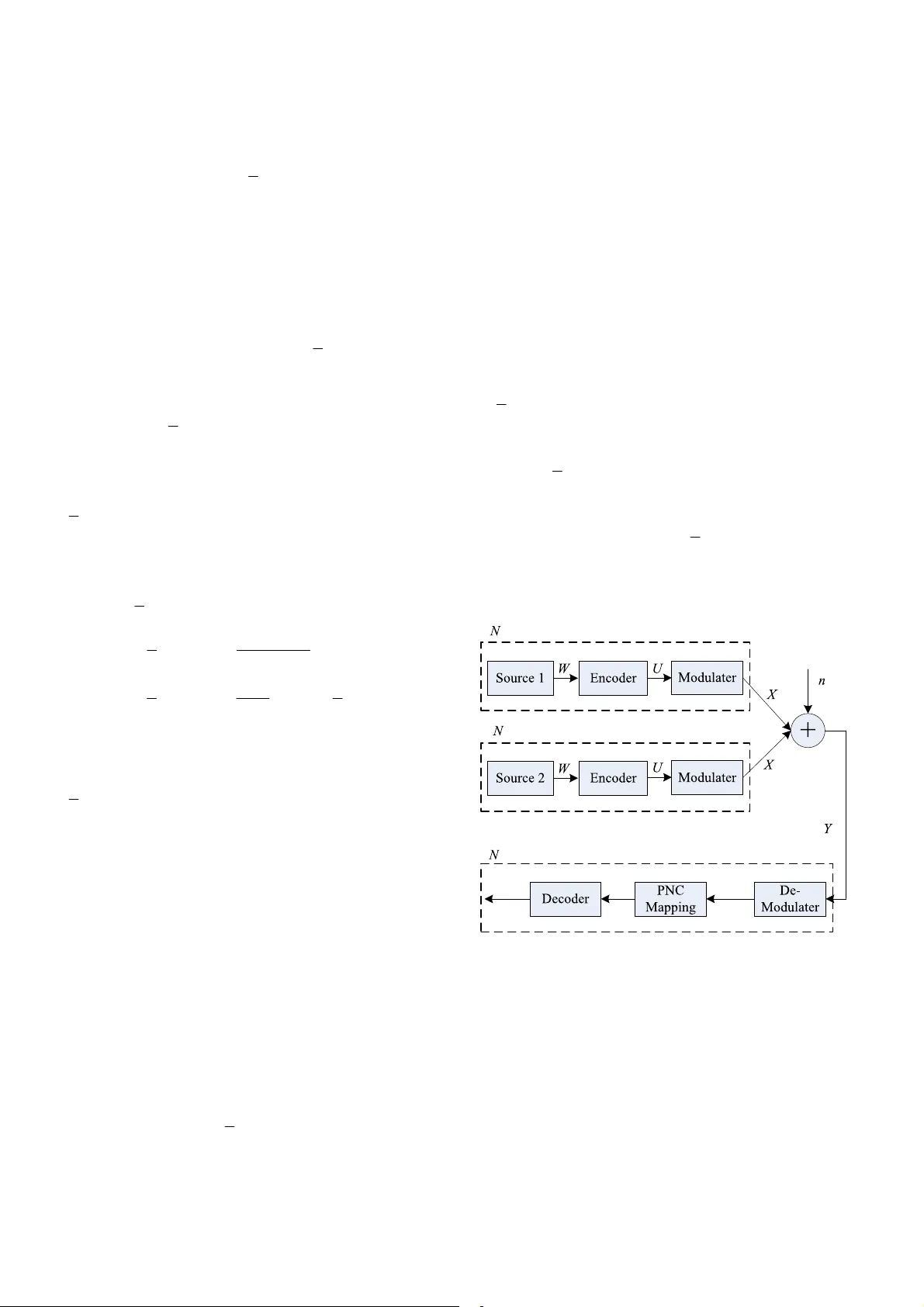
Capacity of T wo-W ay Relay Channel Shengli Zhang, Soung Chang Liew The Department of Information Engineering, The Chinese University of Hong Kong, Hong Kong, China Email: {slzhang5, soung}@ie.cuhk.edu.hk Abstract: This paper investigates the capacity of a wir eless two-way relay channel in which two end nodes exchange information via a relay node. The capacity is defined in the information-theoretic sense as the maximum information exchange rate between the two end nodes. W e give an upper bound of the capacity by applying the cut-set theorem. W e prove that this upper bound can be appr oached in low SNR region using “separated” multiple access for uplinks fr om the end nodes to the relay in which the data fr om the end nodes are individually decoded at the relay; and network-coding br oadcast for downlinks fr om the relay to the end nodes in which the r elay mixes the information from end nodes befor e forwarding. W e further pr ove that the capacity is approachable in high SNR region using physical-layer network coding (PNC) multiple access for uplinks, and network-coding broadcast for downlinks. From our proof and observations, we conjectur e that the upper bound may be achieved with PNC in all SNR regions. I. INTRODUCTION: The design and analysis of wireless two-way relay channel (TWRC) are attracting increasing attention. Among all the models for TWRC, of greatest interest is the simplest model of three-node TWRC with additive Gaussian noise. This paper focuses on a three-node TWRC system as depicted in Fig. 1. W e investigate its maximum information exchange rate, defined as the smaller of the forward-direction and reverse-direction information transfer rates. 1 N 2 N 3 N Figure 1. Three-node two way relay channel The two-way channel without a relay was first studied by Shannon in [1]. The one-way relay channel under various relay strategies has also been widely studied (see [2] and the references therein). As a combination of the two, TWRC is currently drawing much research attention. Ref. [3] gave the achievable rate regions of TWRC when relay protocols borrowed from the one-way relay channel are applied. Under the same relay protocols, [4] derived the rate regions of the TWRC when the nodes are half-duplex and a direct link between the two ends is not available. These strategies that do not exploit network coding cannot achieve the information transfer rate at capacity . Application of network coding is not very fruitful for one-way relay channel. However , applying network coding in TWRC opens up new possibilities. As shown in [5], broadcasting a network-coded version of the inputs at the relay node holds the promise of significant system-performance improvement. Based on this idea, practical joint network coding and channel coding designs were studied in [6, 7]. Ref. [8] proposed a “physical layer network coding” (PNC) scheme which further improves the transmission efficiency of TWRC. Other transmission schemes inspired by PNC were proposed and analyzed in [9, 10, 1 1] for TWRC. T o our knowledge, all the current papers on TWRC focus on the achievable rate regions or bounds under specific transmission strategies. The “ultimate” achievable maximum rate region of TWRC is still an open issue. In contrast to previous work, this paper studies the capacity of TWRC as the maximum information exchange rate under all the possible transmission strategies. In particular , we give an upper bound on symmetric information exchange rate based on the cut-set theorem. W e prove that this upper bound is approachable in low SNR region using “separated” multiple-access for uplinks and network-coding broadcast for downlinks. In separated multiple-access [13], the relay node extracts the “complete” information from each of the two nodes; the “separated” information is then combined using network coding [5] for downlink broadcast. In high SNR region, the upper bound is approachable by replacing separated multiple access with PNC multiple access. W e conjecture that the upper bound is achievable in all SNR regions with PNC. The paper is organized as follows. Section II introduces the system model studied in this paper . Section III gives upper bound of the system capacity . Section IV and V prove the tightness of the upper bound in low SNR and high SNR regions, respectively . Section VI concludes this paper . II. SYSTEM MODEL: W ith reference to Fig. 1, nodes N 1 and N 2 exchange information with the help of node N 3 . W e assume all nodes are half-duplex, i.e., each node can not receive and transmit simultaneously . This is an assumption arising from practical considerations because it is difficult for wireless nodes to remove the strong interference of its own transmitting signal from the received signal. W e also assume that there is no direct link between nodes N 1 and N 2 . A practical example is satellite communication, wherein two end nodes on the earth can only communicate with each other via a satellite relay . W e assume that the maximum transmission power of node N i is P i , and receiver noise is addictive Gaussian with unit variance at all nodes. The path loss is unit constant. By low SNR region, we mean both P 1 and P 2 approach zero, and by high SNR region we mean both P 1 and P 2 approach infinity . W e do not consider fading in this paper . Notations In this paper , n denotes the Gaussian noise. W i denote the information packet of node ,{ 1 , 2 , 3 } i Ni ∈ , and [] { 0 , 1 , 1 } , { 0 , 1 1 } i wk q k K ∈− ∈ − "" denote its k -th symbol. The q -ary information symbols are used throughout the paper . For channel coding, 1 Γ , 2 Γ and 3 Γ denote the encoding functions of N 1 , N 2 , and N 3 respectively . The coded packets of node i is () , { 1 , 2 , 3 } ii i UW i =Γ ∈ W ithin U i , [ ] {0 , 1 , 1 } , {0 , 1 1 } ii uk q k L ∈− ∈ − "" denote its k -th symbol. The coding rate of i N is therefore / i KL . W e assume all nodes use the same modulation scheme. X i denote the modulated packet of i N , and M denote the modulation mapping: () { 1 , 2 , 3 } ii XM U i =∈ W ithin X i , [ ] {0 , 1 , 1 } , {0 , 1 1 } ii xk q k L ∈− ∈ − "" denote its k -th modulated symbol. Finally , [] i yk denote the k -th received baseband signal at node N i . The capacity of the system is defined as 1, 2 2 ,1 {} max min { ( ), ( )} s all po ssible schemes CR s R s ∈ = (1) where 2, 1 () Rs is the reliable transmission rate from N 2 to N 1 under transmission scheme s , and 1, 2 () Rs is the transmission rate in the opposite direction during the same time under the same transmission scheme. III. UPPER BOUND OF THE TWRC CAP ACITY : The upper bound of the TWRC capacity defined in (1) is given in the following proposition with a cut-set proof. Proposition 1: For the TWRC model described in the previous section, the capacity defined in (1) is upper-bounded by 21 2 2 3 21 2 2 3 log ( 1 min ( , )) log ( 1 ) 1 2 log ( 1 min( , )) log ( 1 ) PP P C PP P +⋅ + ≤ ++ + ( 2 ) where 2 1 log ( 1 ) 2 i P + is the Shannon channel capacity for a Gaussian channel with SNR P i . Proof: Due to half-duplexity and the lack of a direct link between N 1 and N 2 , it is necessary to divide the transmission into two phases, one phase for N 3 ’ s reception and the other phase for N 3 ’ s transmission. The first phase is referred to as the uplink phase, which includes all the transmissions from node N 1 and/or N 2 to node N 3. Note that there are at most three possible transmission scenarios: N 1 transmits to N 3 ; N 2 transmits to N 3 ; or N 1 and N 2 transmit to N 3 simultaneously . In this phase, the maximum reliable transmission rate originating from N 1 is no more than 21 1 log ( 1 ) 2 P + . This result is obtained by applying the cut-set theorem where N 1 is regarded as the source set as in [20]. Similarly , the maximum reliable transmission rate from N 2 is no more than 22 1 log ( 1 ) 2 P + . Since we are interested in the smaller of the two rates, the transmission rate in the uplink phase is upper bounded by 21 2 1 log ( 1 min ( , )) 2 PP + . The second phase is referred as the downlink phase, which includes all the transmissions originating from N 3 . According to the Shannon channel capacity , the information transmission rate from N 3 to N 1 and/or N 2 is no more than 23 1 log ( 1 ) 2 P + . Besides the transmission rates of the two phases, the final exchange rate also depends on the time allocation. W e use t 1 to denote the total time used in the first phase, and 1- t 1 to denote the total time used in the second phase. Then the final information exchange rate is 11 21 2 2 3 1 min log ( 1 min ( , )), log ( 1 ) 22 tt PP P − ⎧⎫ ++ ⎨⎬ ⎩⎭ ( 3 ) T o maximize the value in (3), obviously we should determine the value of t 1 so that the two arguments in the min function are equal. Doing so yields the upper bound in (2). IV . APPROACHING THE UPPER BOUND IN LOW SNR REGION W ith reference to the proof of Pr oposition 1 , we must find a transmission scheme that can approach the upper bounds in both phases to prove the tightness of the upper bound in (2). Let us first consider the downlink phase. Downlink Phase Our scheme consists of two steps. The first step is to decide a function W 3 = f(W 1 , W 2 ) . After that, we could use a standard capacity approaching channel coding scheme, such as the LDPC code or the T urbo code, to encode the information W 3 = f(W 1 , W 2 ) into U 3 before modulating and broadcasting it to both N 1 and N 2 with a rate approaching 23 1 log ( 1 ) 2 P + . Fig.2 shows this transmission strategy from the viewpoint of reception at N 1 . 1 3 Figure 2. Reception of downlink transmission at node N 1 Since we use a capacity approaching channel code, N 1 and N 2 can obtain W 3 with an error probability approaching zero as long as the rate of W 3 is no more than 23 1 log ( 1 ) 2 P + . The critical issue for the downlink transmission is to find a function f such that the target information W 1 and W 2 can be decoded from W 3 at both end nodes with the same rate of W 3 . The requirement can be specified as follows: Requirement to Satisfy the Downlink Phase Upper Bound: 213 () ( ) ( ) HW HW HW == where W 1 and W 2 are decodable from W 3 at N 2 and N 1 respectively . W ith reference to the receiving part in Fig. 2, the interpretation of this requirement is as follows. In order that the transmission rate of W 2 can achieve the upper bound, there should be no information loss during the signal processing to obtain W 2 from W 3 . In other words, the entropy of W 2 obtained at N 1 should be equal to that of W 3 . T o meet this requirement, the following proposition presents the necessary and sufficient conditions that f must satisfy . Proposition 2: The function f must satisfy both of the following conditions to achieve the upper bound of the downlink phase with the given downlink transmission strategy . 21 3 12 3 (| , ) 0 ( |, ) 0 HW W W HW W W == ( 4 ) 31 3 2 (; ) 0 (; ) 0 IW W IW W == ( 5 ) Proof: W ith reference to the receiving part in Fig. 2, we have the following inequalities according to basic Information Theory rules, 22 1 3 1 3 () ( | ) ( | ) ( ) HW HW W HW W HW =≤ ≤ ( 6 ) The function f must satisfy the inequalities in (6) with equality . The satisfaction of the first inequality 21 3 1 (| ) ( | ) HW W HW W ≤ at equality is equivalent to condition (4), as shown below: 21 31 21 31 31 2 21 3 21 21 21 2 3 1 23 1 (| ) (| ) (| ) (| ) (| , ) (| ) ( ; | ) (| ) (| ) (|, ) (| , ) HW W HW W HW W HW W HW W W HW W IW W W HW W HW W HW W W HW W W − =− + =− =− + = (7) The satisfaction of the second inequality 31 3 (| ) ( ) HW W HW ≤ at equality is equivalent condition (5): 33 1 3 1 () ( | ) (;) HW HW W IW W −= ( 8 ) When N 2 is considered, we can obtain similar results. Condition (4) means that f must be reversible when W 1 or W 2 is given. Otherwise, the end nodes cannot recover their counterpart’ s information from W 3 and their self information. Condition (5) means that the output of f must be probabilistically independent of each of the two input packets alone. Otherwise, the downlink transmission in Fig. 2 is inefficient. Both conditions are needed. For example, the function 12 1 2 (, ) fWW W W =+ satisfies (4) but not (5). On the other hand, 12 0 (, ) fWW W = , where W 0 is a random packet, satisfies (5) but not (4). Neither of these functions can achieve the upper bound of the downlink phase. For an f that satisfies both (4) and (5), consider the network coding operation over a finite field, 12 1 2 (, ) fWW W W =⊕ , as in [12]. In summary , in the scheme of Fig. 2 in which the channel coding and signal processing of f are performed separately , the upper bound of the downlink transmission rate can be achieved with a valid f and a capacity-approaching channel code. W e refer to such a downlink scheme as network-coding broadcasting. In the remainder of this paper , f denotes a valid function that can achieve the upper bound in the downlink phase. Uplink Phase W e now consider the uplink phase. W e need to find a multiple-access scheme with which we can obtain 12 (, ) fW W with a rate approaching 21 2 1 log ( 1 min ( , )) 2 PP + in the uplink phase. In fact, the separated multiple-access scheme in [13] guarantees that N 3 can obtain both W 1 and W 2 with a rate at least approaching 21 2 1 log ( 1 min ( , )) 2 PP + in low SNR region, from which 31 2 (, ) Wf W W = can then be computed. Proposition 3: In low SNR region, N 3 can obtain both W 1 and W 2 at a rate approaching 21 2 1 log ( 1 min ( , )) 2 PP + with the help of the separated multiple-access scheme. Proof: Without loss of generality , we assume that 12 LL ≥ , which implies 12 PP ≤ . The two end nodes cooperate with each other to transmit at the same time to N 3 . Then N 3 decodes W 2 from the received superimposed packet Y 3 . T reating N 1 ’ s information W 1 as interference, N 3 can reliably decode W 2 with a rate approaching 22 1 1 log ( 1 /( 1 ) ) 2 PP ++ . After that, N 3 can decode W 1 after removing the information of W 2 from Y 3 . As a result, the reliable transmission rate of W 1 approaches 21 1 log ( 1 ) 2 P + . If 21 1 /( 1 ) PP P +≥ , i.e., 2 21 1 PP P ≥+ , the rate of W 1 , which is smaller than that of W 2 , approaches 21 2 1 log ( 1 min ( , )) 2 PP + . On the other hand, if 2 121 1 PP P P ≤≤ + , the rate of W 2 , which is smaller than that of W 1 , can be approximated by 1 22 1 2 21 1 21 1 2 0 1 21 21 1 1 log ( 1 /( 1 ) ) 2 1 log ( 1 ) 21 11 l o g( 1 ) l o g( 1 ) 21 2 P PP PP P P P P PP P → ++ −− =+ + + ≥+ − ⎯ ⎯ ⎯ →+ + (9) Hence, Pr oposition 3 is proved. Since we can obtain both W 1 and W 2 at a rate of 21 2 1 log ( 1 min ( , )) 2 PP + , we can obtain f(W 1 , W 2 ) (e.g., the summation of W 1 and W 2 over a finite field) at the same rate. W ith the help of separated multiple access and network-coding broadcast, we can approach the upper bound of the TWRC’ capacity in (2) in low SNR region. This result indicates that the traditional network coding, which regards network coding as an upper layer operation (i.e., W 1 and W 2 are decoded explicitly at N 3 before f(W 1 , W 2 ) is computed from W 1 and W 2 at the upper layer) is near optimal in low SNR region in TWRC. However , this is not the case in high SNR region. V . APPROACHING THE UPPER BOUND IN HIGH SNR REGION: As for low SNR region, we also need to find a multiple-access scheme that allows N 3 to obtain f(W 1 , W 2 ) with a rate approaching 21 2 1 log ( 1 min ( , )) 2 PP + in the uplink phase to prove the tightness of the upper bound in (2). W e find that tradition separated multiple access does not work any more. In this section, we show that PNC-based multiple access can approach the upper bound. For PNC multiple access, we use an f that is fixed during the whole downlink phase, as follows: 12 1 2 1 2 (, ) m o d q fW W W W W W q =+ =+ ( 1 0 ) where q + denotes the modulo- q addition (Modulo- q addition of two packets means symbol-wise modulo- q addition). It is easy to verify that the function in (10) satisfies the conditions (4) and (5). Thus, the downlink phase can approach the rate of 23 1 log ( 1 ) 2 P + . The following proposition shows that for the uplink phase, N 3 can reliably obtain 12 q WW + with a rate approaching 21 2 1 log ( 1 min ( , )) 2 PP + . Proposition 4: In high SNR region, N 3 can obtain 12 q WW + at a rate approaching 21 2 1 log ( 1 min ( , )) 2 PP + with the PNC scheme depicted in Fig. 3 if the modulo- q LDPC codes can approach the Gaussian channel capacity in high SNR region. 1 2 2 k 12 q WW + 1 1 2 1 2 j 1 U 3 k 12 XX + 3 Figure 3. T ransmission and reception diagram of PNC scheme System Description: Before the proof, let us try to understand the proposed system first. W ith reference to Fig. 3, let us assume 12 PP ≤ without loss of generality . The transmission strategy is as follows. W e first reduce the transmission power of node N 2 to P 1 so that both end nodes transmit with the same power . W e use the same block channel code, which is linear with the operation of modulo- q addition, at the two end nodes. In other words, we have 12 12 1 2 12 () ( ) ( ) qq q UU W W W W Γ= Γ = Γ += Γ + Γ = Γ + ( 1 1 ) Therefore, the length of U 1 equals the length of U 2 . The modulo- q LDPC code, first proposed by G . Gallager in [14], is an example of such a linear coding scheme. W e also assume that the q -ary P AM modulation (QAM modulation is also valid in the PNC system) is used at both end nodes, i.e., ()2 ( 1 ) ii i XM U U q == − − ( 1 2 ) The two end nodes cooperate to transmit so that the two transmitted signals reach node N 3 in synchrony . Therefore, we can denote the k -th received symbol on baseband as 31 2 [] [] [] yk x k x k n =+ + ( 1 3 ) After receiving Y 3 , N 3 can obtain an estimation of 12 XX + , with either hard detection or soft detection, denoted by k 12 XX + . Although optimal demodulation thresholds could be used to obtain k 12 XX + (see [8]), we will show that using the middle value of two adjacent constellation points as the estimation threshold is good enough to prove Pr oposition 4 . After that, N 3 will map k 12 XX + to the estimation of 12 q UU + , denoted by k 12 q UU + with a PNC mapping, as follows k k 12 1 2 () / 2 1 m o d q UU X X q += + − ( 1 4 ) Due to the linearity of Γ , 12 q UU + is the codeword of 12 q WW + as shown in (11). Therefore, we can decode k 12 q UU + with the decoding process corresponding to Γ to obtain an estimation of the target information, denoted by k 12 q WW + . Note that W 1 and W 2 are not decoded explicitly in the process to obtain 12 q WW + . A critical assumption in this proposition is that the modulo- q LDPC code can approach the Gaussian channel capacity in high SNR region. This assumption is supported by the following observations. First, [15] proved that modulo- q quantized coset (MQC) LDPC codes can achieve the Shannon capacity of any discrete memoryless channel and the simulation there showed that MQC-LDPC codes can approach the capacity of A WGN channel within a gap of 0.9 dB. Second, for modulo- q LDPC code, the shaping loss (compared to the MQC LDPC) due to the lack of quantization is at most 1.53dB as shown in [16]. Such a fixed SNR loss can be ignored in high SNR region. W e now prove Pr oposition 4 with the introduced PNC transmission scheme. Proof: First consider the point-to-point transmission in Fig. 4. Suppose the transmission power of the source is also P 1 , and other assumptions are same as in our system model. As shown in [17, Ch5.2], the symbol error rate (SER) before channel decoding is 1 Pr( ) Pr( ) Pr(| | / 2) q q Pu u x x n d q − =≠ =≠ = ≥ (15) where d is the distance between adjacent constellation points and Pr( | | / 2) nd ≥ is the probability that the Gaussian noise i X i W j 1 U Figure 4. Point-to-point transmission will cause a symbol detection error . Since we assume that the coset modulo- q LDPC code with q -ary P AM modulation can approach the Gaussian channel capacity in high SNR region, the SER after decoding, i.e., Pr( ) ww ≠ , will go to zero only if the information rate, determined by the LDPC code rate, does not exceed the Gaussian channel capacity 21 1 log ( 1 ) 2 P + in high SNR region. W e now apply the identical coset-LDPC code at N 1 and N 2 in our system of Fig. 3. Note that the coset vector in the point-to-point transmission can be achieved by the two cooperatively designed coset vectors at N 1 and N 2 . And we also set the code rate to be the same as that in the point-to-point transmission in Fig. 4. The SER of PNC scheme before decoding is k k 12 12 12 12 2 2 P r ( ( [] [] ) ( [] [] ) ) P r ( ( [] [] ) ( [] [] ) ) 1 Pr(| | / 2) qq q qq P u ku k u ku k xk x k xk x k q nd q + =+ ≠ + <+ ≠ + − =≥ (16) where the last line is derived in the paragraph after this proof. As SNR and q go to infinity , we can see that q P + in (16) will go to q P . Since the same channel encoding and decoding scheme is used, the PNC SER after channel decoding will also go to zero as in the point-to-point system. Because the code rate is same as that of the point-to-point transmission, the information rate of k 12 q WW + , which is equal to that of W 1 and W 2 , also approaches 21 1 log ( 1 ) 2 P + . SER of two superimposed P AM signal For a superposition of two synchronized q -ary P AM signals, the new constellation still looks like that of P AM, where the probability of the two end points is 2 1/ q , and the probability of all other constellation points is 2 12 / q − . Since the two P AM signals have the same transmitting power , the distance between two adjacent constellation points of the superimposed signal is the same as that of the single P AM signal case, denoted by d . The SER of the left and right end points are 1 2 Pr Pr( / 2) Pr Pr( / 2) nd nd =< − => ( 1 7 ) where n is the Gaussian noise. The SER of other points is 3 Pr Pr(| | / 2) nd => ( 1 8 ) The overall SER is 2 12 3 22 2 2 2 11 1 Pr Pr Pr 1 Pr(| | / 2) q P qq q q nd q − =+ + − =≥ ( 1 9 ) Finally , combining the PNC multiple access scheme and network-coding-like broadcasting scheme, the upper bound of the TWRC capacity is approachable in high SNR region. VI. CONCLUSION In this paper , we have investigated the capacity of three-node TWRC, in which two end nodes exchange information via a relay node. An upper bound of the capacity has been given, and the tightness of the bound has been proved in the low SNR and high SNR regions. W e conjecture that the high SNR limitation in Pr oposition 4 is not necessary for the following reasons. First, we may carefully design the constellation mappings at the two end nodes so that the superimposed signal at the relay can achieve the shaping gain. Second, with reference to the upper bound proof in the last section, we could fix SNR and increase q in (15) and (16). This has the effect of increasing the factor Pr( | | / 2) nd ≥ in (15) and (16) similarly . Meanwhile, both the factors 1 q q − and 2 2 1 q q − approach one. Third, simulation results in [18] suggest that by increasing q in PNC, the achievable rate may be able to approach channel capacity . This paper has assumed a set-up in which a direct link between the two end nodes is unavailable. W e conjecture that this assumption is not necessary for the results we have obtained as long as links are half-duplex (i.e., a node cannot receive and transmit at the same time), and the capacity of the direct link between the two end nodes is no better than half of either of the relay links between the end nodes and the relay node. The PNC uplink transmission scheme in Fig. 3 can be viewed as a specific scheme for “computation over multiple access channels” first studied in [19]. For the computation over multiple-access channels, the receiving node is interested in a function of the inputs, instead of each individual input. Theoretical results on the capacities of such multiple-access channels for certain functions of inputs have been obtained in [19]. The case of the function as modulo- q addition of the inputs, such as in our PNC scheme in Fig. 3, is first addressed in our paper here. Reference: [1] C. E. Shannon, “Two-way communication channels,” in Proc. 4th Berkeley Symp. Math. Stat. and Prob. , vol. 1, pp. 611–644, 1961. [2] G . Kramer, M. Gastpar , and P Gupta, “Cooperative Strategies and Capacity Theorems for Relay Networks” IEEE Trans. on Inform. Theory , V ol.51(9), pp.:3037 – 3063, 2005 [3] B. Rankov and A. Wittneben, “Achievable rate regions for the two-way relay channel,” in Proc. IEEE Int. Symposium on Inf. Theory , (Seattle, (WA)), 2006. [4] B. Rankov , and A. Wittneben, “spectral ef ficient protocols for half duplex fading relay channels”, IEEE JSAC , vol. 25 (2), pp. 379-389, Feb. 2007. [5] Y . W u, P .A. Chou, S.Y . Kung, “Information exchange in wireless networks with network coding and physical-layer broadcast ”, Pr oc. 39th Annual Conf. Inform. Sci. and Systems (CISS) , 2005 [6] C. Hausl, and J. Hagenauer , “Iterative Network and Channel Decoding for the T wo-W ay Relay Channel”, Pr oc. of IEEE International Confer ence on Communications , 2006. [7] S. Zhang, Y . Zhu, S. C. Liew , and K. B. Letaief ,” Joint Design of Network Coding and Channel Decoding for W ireless Networks”, Proc. WCNC2007, Hong Kong, 2007. [8] S. Zhang, S. Liew , and P . Lam, “Physical layer network coding,” ACM Mobicom2006 , 2006 [9] S. Zhang, S. Liew , and P . Lam, “Physical layer network coding,” http://arxiv .or g/ftp/arxiv/papers/0704/0704.2475.pdf [10] T . Cui, T . Ho, and J. Kliewer, “Relay strategies for memoryless two way relay channels: performance anal ysis and optimization”, submitted to ICC’08. [1 1] S. J. Dim, P . Mitran, and V . T arokh, “performance bounds for bi-directional coded cooperation protocols”, 27 th , ICDCSW , pp. 83, June 2007. [12] S.-Y .R. Li, R.W . Y eung, and N. Cai, “Linear network coding”, IEEE Trans. on Inform. Theory , vol. 49(2), pp. 371–381, 2003. [13] T . Cover, and J. Thomas, “Elements of information theory ,” 2 nd ed. New Y ork: Wiley , 2006. [14] R. G . Gallager , “Low density parity check codes”, Cambridge, MA. MIT Press, 1963 [15] A. Bennatan, D. Burshtein, “On the application of LDPC codes to arbitrary discrete memeoryless channels”, T rans. Inform. Theory , vol. 50(3), pp. 417-438, 2004. [16] G. D. Forney, Jr. and G. Ungerboeck, “Modulation and Coding for Linear Gaussian Channels”, IEEE Trans. on Inform. Theory , vol. 44, pp. 2384–2415, October 1998. [17] J. G .. Proakis, “Digital communication,” 4 th ed, McGraw-Hill Press, 2000. [18] Y . Hao, D. Goecket, Z. Ding, D. T owsley , and K. K. Leung, “Achievable rates of physical layer network coding schemes on the exchange channel,” submitted to ICC2008. [19] B. Nazer, M. Gastpar , “Computation over multiple access channels,” IEEE T rans. Inform, Theory , vol. 53, pp. 3498-3516, 2007. [20] Y . W u, “Network coding for multicast,” Ph.D thesis, Department of EECS, MIT , Cambridge, Jan. 2006.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment