Information Hiding Techniques: A Tutorial Review
The purpose of this tutorial is to present an overview of various information hiding techniques. A brief history of steganography is provided along with techniques that were used to hide information. Text, image and audio based information hiding tec…
Authors: Sabu M. Thampi
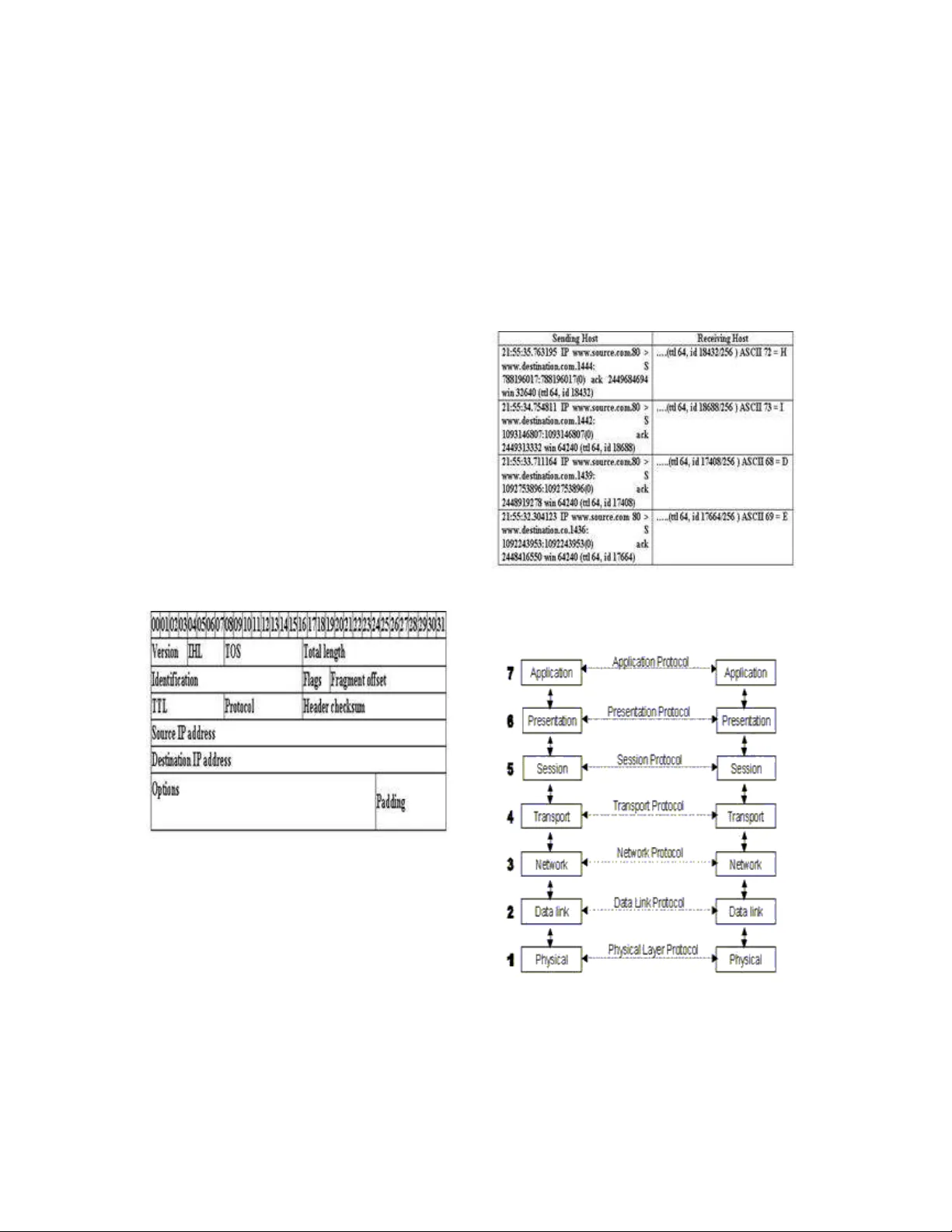
ISTE-STTP on Network Security & Cryptography , LBSCE 2004 Information Hiding Techniques: A Tuto rial Rev ie w Sabu M Thampi Assistant P rofessor Department of Computer Science & E ngineerin g LBS College of Engineeri ng, Kasara god Kerala- 6715 42, S.India smtlbs@yahoo.c o.in Abstract The purpose of this tutori al is to present an overview of vario us infor mation hiding techniques. A brief his tory of stegano graphy is pr ovided along with techni ques that were used to hi de inf ormation. Text, im age and audio based inf ormation hidin g techniques are disc ussed. This paper also provides a basic int roduction t o digital water marking. 1. History of Inf orma tion Hidin g The idea of communicating secretl y is as old as commu nication itself. In this section, we briefl y discuss the historic al developme nt of inf ormation hiding techniques such as steganograph y/ watermar king. Earl y ste ganogra phy w as me ssy. Before phones, before mail, bef ore horses, mess ages were sent on foot. If you wanted t o hide a message, you had tw o choices: ha ve the messen ger mem orize it, or hide it on the mes senger. While informa tion hiding t echniques have rece ived a tremendous attenti on recentl y , its ap plication goes back t o Greek ti mes. Accordi ng to Gree k historia n Herodotus, the fa mous Greek t yrant Histiae us, while in prison, used unusual method t o send mes sage to his son-in-law. He shave d the hea d of a sla ve to tattoo a messa ge on his sca lp. Histiae us the n waited until the hair gre w bac k on slave’s head prior to sendin g him off to his son-i n- law. The secon d st ory als o ca me f rom Herodotus, w hich claims t hat a s oldier named Demera tus neede d t o send a mes sage to Sparta t hat Xerxes inte nded t o invade Greece. Back t hen, the writi ng medium was written on wax-covered tablet . Demeratus remo ved the wax from t he tablet, wrot e the sec ret messa ge on the unde rl y ing wood, r ecover ed the tablet with wax to make it a ppear a s a blank ta blet and f inall y sent the d ocument without being detected. Invisible in ks have a lwa y s been a popular met hod of ste ganograp hy. Anci ent R omans used to writ e betwee n li nes usin g i nvisible inks based on rea dil y available s ubstances such as fruit juice s, urine and milk. When heated, the invisible inks would darken, and become legible. Ovid i n h is “ Art o f Love” su ggests usin g milk to write i nvisibl y . Later chemicall y aff ected sympathe tic inks w ere de veloped. Invisible inks were used as rec ently as Worl d War II. Modern invis ible in ks f luoresce under ultra violet light and a re used a s anti-c ounterfeit devices. For e xample, "VOID" is printed on checks a nd other official documents i n a n ink that a ppears u nder the str ong ultraviolet l ight used f or photocopies. The monk Johan nes Trit hemius, c onsidered one of the founders of m odern cr yptogr aphy, had ingenuit y in spades. His three volume work Ste g anographia, written ar ound 1500, descri bes an exten sive s y ste m for concealing secret messa ges within i nnocuous texts. O n its surface, the book seems t o be a ma gical te xt, and the init ial reaction in the 16th cent ury was so str ong that Steganogra phia was onl y circulated priva tely until publicati on in 1606. But less than f ive y ears ago, Ji m Reeds of AT&T Labs deciphere d mysteri ous codes i n the third volume, s howing tha t Trithemius' work i s more a tre atise on cr y pt ology t han demonolog y . Reeds' fascinating acc ount of the code breaki ng pr ocess is quite reada ble. One of Trit hemius' sche mes was t o c onceal messa ges in l ong in vocations of t he nam es of an g e ls, with the secret message a ppearing as a patter n of lett ers within the words. For exa mple, as ever y other letter i n e very other word: p adiel a p o r s y mesarpon o m e u a s pelud yn m a l p r e a x o which re veals "pr y mus a pex." Another clever in vention i n Steg anographi a was t he "Ave Maria" c ipher. The book c ontains a series of tables, each of which has a list of w ords, one per lette r. To c ode a m essage, t he me ssage letters are replace d by the corresp onding words. If the table s a re used in order, one table per lette r, then t he coded messa ge will appear to be a n innocent prayer. The earliest actual book on s teganograph y was a four hundred pa ge work writte n by Gaspari S chott in 1665 and ca lled Ste ganographic a . Alth ough most of t he ideas came f rom Trithe mius, it was a start. Further de velopment i n the field occurred in 1883, with the p ublication of Auguste Kerc hoffs’ Cryptographi e militai re . Although this work was mostly about cr yptography, it describes some principles that a re worth keeping i n mind when designing a new steganogra phic system. ISTE-STTP on Network Security & Cryptography , LBSCE 2004 But i t was duri ng t he twe ntieth ce ntur y that steganogra phy t ruly flowered . An exa mple of this comes fr om earl y i n the centur y, during t he Boer War. The Britis h emplo y ed Lord R obert Bade n- Powell f ounder of Bo y Sc out moveme nt a s a scout. His job was t o mark the positi ons of Boer artiller y bases. To ensure he was not suspec ted b y t he Boers, if he was caught, he would mark his maps into drawings of b utterflies . Ap pearing i nnocent to a casual o bserver, certain ma rkings on the win gs were a ctuall y the positions of t he enem y militar y installati ons. During World Wa r II, null ciphers (unencr ypted messa g e) were used to hide secret messa ges. The null cipher, which often app eared t o be i nnocent messa g e about ordinary oc currences, would not alert su spicion, a nd woul d thus not be i ntercepted. For exam ple, the followi ng message was sent b y German spy during W WII. Apparently neutr al’s prote st is t horoughly discounte d and ignore d. I sman har d hit. Block ade issue affect s pretext for em bargo on by-pro ducts, ejectin g suets and vege table oils . Decoding this messa ge by takin g the sec ond letter in each w ord reveals t he followin g secret message. Pershing sail s from NY June 1. W ith the adven t of photogr aphy, m icrofilm w as created as a wa y to store a large amount of informat ion in a ver y small space. I n both wor ld wars, the Germa ns used "microd ots" to hide inform ation, a technique whi ch J. Edgar Hoover ca lled "the enemy's m asterpiece of espionag e." A secre t message was photograp hed, reduced t o th e size of a print ed period, and then pasted into an innocuou s cover message, maga zine, o r new spaper. The American s caug ht on onl y when t ipped by a double agent: "Wa tch out for the dots -- lots and lots of little dot s." A whole other branch of ste gan ography, Linguistic steganogra phy, cons ists of l inguistic of langua ge form of hidde n writing. These are the “sema grams” and the “open c ode”. A se magram is a sec ret messa g e that is not i n a written f orm. For example, a s ystem can use long blades of grass in a picture as dashes in Morse code, with s hort blades f or dots. Open codes ar e il lusions or code words. In World War 1, for exa mple, German s pies used f ake orders for ciga rs to repr esent various t y p es of Brit ish warships – crui sers and de stroyers. Thus 500 ci gars needed i n Portsmout h meant t hat five crui sers were in P ortsmouth. Fingerprint s a re cha racteristi cs of an object t hat ten d to distinguish it fr om other similar objects. The y enable the owner t o trace aut horized users di stributing them illegall y. Digital fin gerprintin g produces a metafile that descri be the c ontents of the s ource file. In the case of encr ypted satellite tele v isi on br oadcasting, for instance, users coul d be i ssued a s et of keys to decr y pt t he video strea ms and the television station could insert fingerpri nt bits int o e ach pac ket of the traffic t o detect unauth orized uses. If a group of u sers give t heir subset of k eys to unauthorized people (so that the y can als o decr ypt the traf fic) at least one of the key donors can be traced when the unau thorized decoder is ca ptured. Figure 1 - Inf ormation Hi ding Tec hniques A covert ch annel could be defined a s a communicati ons channel t hat transfers some ki n d of information using a method or iginally not i ntended to transfer this kind of inf ormati on. Observers are unaware t hat a covert me ssage is bein g c ommunicate d. Only the sende r and reci pient of the message notice it. With the c omputer age, inf ormation hidi ng has been given a marvel ous b oost. We are sure t o see a great expansion of stega nographic al techniques in the coming years. 2. What is Steganography and why is it important? Steganogra phy or Stego as it oft en ref erred to in the IT communit y, literall y means, “Covered writing” which is deri ved fr om the Gree k langua ge. Steganogra phy is defined as f ollows, “Stegan ography is t he art and scie nce of communicati ng in a wa y whic h hi des the e xistence of the c ommunicati on. T he goal of Stegano graphy i s to ISTE-STTP on Network Security & Cryptography , LBSCE 2004 hide messages inside other har mless me ssages in a way tha t does n ot al low a ny enem y t o e ven de tect that there is a second m essage pre sent”. In a digital world, Steganogra phy a nd cr y pt ograph y are both inte nded t o protect inf o r mation fr om unwanted parties. Bot h Steganogra phy and Cr y ptogr aphy ar e e xcellent means by whic h t o acc omplish this but neither technolog y al one is perfect and b oth can be br oken. It i s for this reaso n that m ost e xperts would s uggest using both t o add multiple la yers of sec urity. Steganogr aphy Vs Cr yptography The t erm Steganogra phy me ans, “c over writing” whereas cr yptograph y means “se cret writi ng”. Cr y ptogr aphy is t he study of methods of sending messa g e s in distinct form so tha t onl y the i ntended recipients ca n remove the di sguise a nd re ad the messa g e. T he message we want to s end is called plain tex t and disguise d mes sage is called cipher text. The pr ocess o f converting a plai n text to a cipher text is called e ncipherin g or e ncr y pt ion, and the r everse proces s is called decipheri ng o r decr yption. Encr yption pr otects c ontents during the transmissi on of the da ta fr om se nder t o recei ver. However , after rec eipt a nd subseque nt decr yption, the data is no longer pr otected and is the clear. Steganogra phy hi des message s i n plai n sight rather than enc rypting t he messa ge; it is embe dded in the data (that has to be protecte d) and doesn’t require secret transmis sion. The messa ge is carrie d i nside data. Steganogra phy can be u sed i n a lar ge amount o f data f ormats i n the digital world of t oday. The most popular data f ormats a re .bmp, . doc, .gif, .jpe g, .mp3, . txt a nd . wav. Steganogra phic tech nologies are a very im portant pa rt of t he future o f Interne t securit y and pri vacy on op en s y ste ms suc h as Internet. Figure 2a : Cryptography Steganogra phic researc h is pr imarily dri ven by the lac k of strength in the cr y pt ographic systems on their own and t he desire t o have complete secrec y in an open-s y st ems envir onment. Man y Govern ments ha ve cre ated la ws t hat ei ther limit the strength of cr yptosystems or prohibit them complete ly. T his unfortunatel y lea ves t he majorit y of the I nternet communit y either with rel ativel y weak a nd a lot o f the ti mes bre akable e ncr y pt ion algorithms or n one at all. This is where Ste ganograph y comes in. Stegan ography can be used t o hide important data inside another file so that onl y the parti es intende d to get the messa ge e ven know s a secre t mes sage exi sts. It is a good practice to use Cr yptograph y and Steganogra phy together. Neither S teganogra phy n or Cr yptograph y is considered “turnke y s olutions” to ope n syste ms pri vacy, b ut using both technol ogies together can provide a very acceptable a mount of privac y for a nyone connec ting to and communica ting over these s ystems. Figure 2b: Steganogra phy Figure 3 3. A Detailed Look at Steganography In this sect ion we wi ll discu ss Steganogra phy at lengt h. We will start by l ooking at t he diffe rent t ypes of Steganogra phy general ly use d in practic e toda y along with s ome of t he other principles that are used in Steganogra phy. To sta rt, let ’s l ook at what a the o r eticall y perfect secret communicati on ( Stega nograph y ) would consi st of. To illustrate this conce pt, we will use three fictit ious characters named Am y, Bret and Crystal. Am y w ants to s end a sec ret messa ge ( M) t o Bret using a ra ndom (R) ha rmless message to c reate a cover ( C), which can be sent to Bret with out rais ing suspic ion. Amy the n changes the c over message (C ) to a st ego-ob ject ( S) by embeddin g the secret mess age (M) i nto the cover ISTE-STTP on Network Security & Cryptography , LBSCE 2004 messa g e (C) by using a stego-ke y (K). Am y s hould then be a ble to sen d the stego- object (S) to Bret without being de tected by Cr ystal. Bret will then be able t o read the secre t messa ge (M) because he knows t he s tego-key (K) used t o embed i t int o the cover mes sage (C). In order to e mbed secret data into a co ver message, the cover must c ontain a suffi cient am ount of redundant data or n o i se. Th is is becau se in the embed ding pr ocess S teganograph y a ctuall y replaces redunda nt d at a with t he s ecre t m ess age. This limit s t he t y pe s of data that we ca n u se with Steganogra phy. There are basicall y three t ypes of stega nographic protocols used. The y are Pure Ste ganograph y, Secret K e y Ste ganograp hy, a nd Public Ke y Steganogra phy. Pure Stegan ography is defined as a ste ganographic system t hat does not requir e the e xchange of a cipher such as a stego-ke y . T his me thod of Steganogra phy is the least secure mea ns b y wh ich to com municate secretl y because the se nder an d recei ver can rely onl y up on the presumpti on that no other parties a re a ware of this secr et message. Secret K e y Steganogra phy is defi ned as a Steganogra phic s ystem that r equires the excha nge of a secre t key ( stego-ke y) pri o r t o communi cation. Secret Key Ste ganograph y takes a c over messa ge and e mbeds t he sec ret message inside of it using a secret ke y (ste go-ke y ). Only the parties who know the secre t ke y can r everse the pr ocess and read the secret messa ge. Unlike Pure Steganogra phy wh ere a perc eived i nvisible c ommunicati on chan nel is present, Secre t Ke y Stegano graph y e xchanges a stego- k e y, w hich make s it more su sceptible t o intercepti on. The benefi t to Sec ret Key Steganogra phy is even if it is intercept ed; onl y parties who know the secret key ca n extract the secret messa ge. Figure 4: Ste ganographic Protocols Public Ke y Ste ganograph y takes the co ncepts from Public Key Cr yptograph y as explaine d below. Public Ke y Ste ganograph y i s defi ned a s a steganogra phic system that uses a public key and a private key to sec ure the co mmunication between the parties wanti ng to commu nicate secret ly. T he sender will u se the public k ey dur ing th e encodi ng pr ocess and onl y the pri vate ke y, which has a direst mathematical re lationshi p w ith the pu blic ke y , ca n decipher the secret messa ge. Public Key Steganogra phy pr ovides a more r obust way of implementing a ste ganograp hic s yst e m because it can utilise a muc h more r obust and resea rched technology in Public Ke y Cr y pt ography. Throughout the hi story dif fere nt media t y pes have been used t o hide informati on. With ad vancement s in computer industr y this num ber is onl y incr easing. Some of the media types ar e computer file s ystem, transmission protocol s, a udio files, te xt fi les a nd images. A brief intr oduction f or encodin g messa ges in various me dia types is gi ven below. Kerchoff ’s Principle The security of the system has to be based o n the assumption t ha t the enemy has full kn owledge of the design and implementation de tails of the steganographic system. The on ly missing information for the ene my is a short, easi ly exch angeable ra ndom number sequence, the secret key. W ithout t his secret key, the ene m y should no t have the chance to even su s pect that on an o bserve d communication chann el, h idden communication is tak ing place. 3.2 Co mputer File Syste m Where it s tores nor mal data, a c omputer file sy ste m can a lso be used to hide inform ation betwee n in nocent files. For exa mple a hard dri ve while showing the visible partition to a computer user ma y contai n hidden partitions that can c arr y hi dden files inside them. For example sfspatch is a kernel p atch, w hich intr oduces module supp o rt for the stega nographic file on a Linux machine. Sfs patch e mploys encr yption alon g with steganogra phic techni ques to hide informati on on the disk so it is not visible t o a casual u ser. FAT 16 s ystem on Mic rosoft Wind ows hosts al locate 32 kilobytes of dis k space to each file. If the file size i s only a f ew kilobytes , the rest of the space ca n be used to hide inf ormation. 3.3 Transmission Pr otocol Covert channels can be establishe d u sing the control data, timin g properties of transmissi on or of t he user data. In this approach it is very difficult or almost impossible t o pr ove the exis tence of covert c hannels, because the informati on is stripped off at the recei ver. But if the informati on is hidde n using user data, it remains on the ha rd dis k until it is spec ificall y deleted. Thus network s ystems ca n be utilized in cr yptograph y to establish hidden channe ls of c ommunications. Transmissi on Control Protoc ol ( TCP) and Internet Protocol ( IP) are some of the few protocol s t hat can be used t o hide information inside certain he ader fi elds. ISTE-STTP on Network Security & Cryptography , LBSCE 2004 Some T CP/IP fields are either c hanged or strip ped off by packet filterin g mec hanisms or through fragme nt r e-assem bly. However, there are f ields that are less l ikel y t o change or altered. The se fields include: Iden tification field, Sequence Number field and Acknowled ge Sequence Number field. • Hidin g information w ithin an IP header The Ide ntificati on field within an IP header provides netw ork devices wi th a unique numb er to identif y packets that ma y require reassembl y . As presented b y Nei l F. J ohnson in I NFS 7 62 c lass a t Geor g e Mason Universit y (GMU), replacin g the identificati on fiel d with t he numerical ASCII representa tion of t he c haracter t o be encode d provides a n ea s y wa y to hide inf ormation wit hin this f ield. In his exa mple, J ohnson select s a n unsigned inte ger to b e trans mitted as the identificati on field. The ASCII val ue of this i nteger can be achi eved b y dividing th e integer b y 256. At t he transmittin g en d clie nt host c onstruct a packet to i nclude the desi red i dentification number along wit h sour ce and destin ation addres s. In this example I ha ve chose n 18432, 1 8688, 17408 a nd 17664 as the four ide ntificatio n field values for the four IP packets. This process i s depicted in Ta ble 1. Once t he ASCII value of the i dentification f ield is calculated at the destination, the dec oded messa ge is found t o be the w ord “HIDE .” Table 1: The I P Header Similar techniques can als o be used to enc ode information i n the Seq uence Number field of a TCP pac ket. • Se ssion Layer An Open Systems Interc onnection Refere nce model ( OSI) uses packet structures to sen d information acr oss the net work fr om one la yer t o another as well as from one n et work terminal to another. A net work packet consists of packe t headers, user da ta a nd packet trailers. All the packets sent acr o ss the network have t he same packet str ucture. The sessi on la yer allows t wo machines to es tablish sessions over t he network. These sessions all ow ordinar y data tr ansfer plus en hanced services f or som e applications . This function is a chieve d via software that can "mount" remote dis cs on a local machine. Richard Popa, wh o has c onducted re search in this are a at t he Universit y of Timisoa ra, ha s described the following sche me t hat ca n be use d t o establ ish covert communicati on channel: "Suppose we have two files on the disk of Alice, Bob can re ad o ne of them. If he r eads the fi rst file then Alice records a ze ro and if he reads the second file s he records a one. " Table 2: H iding data in the ide ntification fi eld The fac t that Oscar can see this traffic should not arouse his su spicion, since it is i rrelevant to him that Bob reads one file rather than an o t her. Figure 5: Open Systems In terconnect ion Ref erence model (OSI) 3.4 Encodin g Secret M essages in Te xt Encodin g sec ret m essages in text can be a ver y challengin g task. Th is i s because text files ha ve a ver y small am ount of redundant data to replace with a secret message. Another drawback i s the e ase of which te xt ISTE-STTP on Network Security & Cryptography , LBSCE 2004 based Ste ganograph y can be a ltered b y an unwanted parties by just cha nging the text itse lf or reformatti ng the t ext t o some other form (fr om .txt to .doc , etc.). There ar e numerous meth ods b y which to a ccomplish text based Ste ganograph y. These methods are: Ope n spa ce method, Syntactic methods a nd Semantic methods ( Figure 4). 3.4.1 O pen Space Me thods There are couple wa ys to empl oy the open s pace in text f iles to e ncode t he i nformation. Th i s met hod works bec ause to a c asual rea der one extr a space at the end of li ne or a n extra spa ce bet ween two words d oes not prompt abnormality. However, open space methods are only useful with ASCII format. • Inter-se ntence space me thod enc odes a “0” b y adding a si ngle space a fter a period in E nglish prose. Adding tw o spaces would enc ode a “ 1”. This meth od wor ks, but r equires a la rge amount of data to hide only l ittle i nformation. Also many word pr ocessing tools automaticall y c orrect the spaces between sentences. Line-shif t encoding i nvolves actuall y s hifting each line of text verticall y up or down by as little 3 centimeters. Dependi ng on w hether the line was up or down fr om t he stationar y line would e quate to a value t hat w ould or coul d be enc oded i nto a secret messa g e. Figure 6: Ste ganography in Text • End-of-li ne space meth od ex ploits white space at the end of eac h line. Data encoded u sing a predetermi ned numbe r of space s at the e nd of each li ne. For exa mple t wo spac es will encod e one bit, four spaces will enc ode tw o bits and eight spaces will e ncode three b its and so on. This te chnique works better than the inter- space me thod, because increa sing the n umber of spaces can hide more data. • Right-j ustification of text can als o be used to encode data within text fil es. Calc ulating and controlling the s paces between words enc ode data in i nnocent text files. One sp ace between word s represents a “ 0” and tw o s paces repre sent a “1”. However, this ap proach ma kes it difficu lt t o decode t he data as i t bec omes i mpossible to distinguish a single inn o ce nt s pace form an encode d one. For this purpos e another technique based on Manc hester c odin g i s use d. Hence “0 1” is int erpreted a s “ 1” and “ 10” is interpreted as “0”. Whereas “00” a nd “11” ar e consi dered the null b it strings. • Feature s pecific enc oding invol ves enc oding secret messages into formatted text by c hanging ce rtain text attri butes s uch as ver tical/horizonta l length of letters such as b, d, T, etc. This is b y far the hardest text enc oding method to interce pt as e ach t y pe of formatted te xt has a large amount of features that can be used for encodi ng t he secret message. All of the above t ext ba sed encoding methods require either the ori ginal fi le or the knowledge of the original files formatti ng t o be able to decode the secr et message. 3.4.2 Syntacti c Methods Syntactic met hods exploit the use of punc tuation and structure of text to hide data without sc ientificall y altering the meaning of the messa ge. For e xample t he two phr ases “ bread, b utter, a nd milk” and “ bread, butter and milk” are grammaticall y co r rect but differ in the use of com ma. One can e mpl oy t his struc ture alternativel y i n a text message t o represent e ither a “1” of one m ethod is used a nd to r epresent a “ 0” if t he other met hod is employed. 3.4.3 Semanti c Methods Semantic met hods assi gn two s ynonyms a pri mar y or secondar y value. These values are then tra nslated into binary “ 1” or “0”. F or exa mple the word “big” is assigned a primar y an d the word “lar ge “ is assigned secondar y . Therefore, dec oding a me ssage woul d translate t he use of primar y to be “1” an d secondar y to a “0”. The pr oblem in this app roach is that replace ment of synon yms ma y change t he meaning or structure of the sentence. For example cal ling someone “cool” has a differe nt meaning tha n calling him or her “chill y”. Our t ool anal ysis f or text file Steganograph y will cover a pr oduct namel y “S NOW”, that ma kes use of en d of lines of text f or encodi ng messa ges. 3.4.4 Conce aling Mess ages in Text Files: SNOW Snow is a f ree f or non- commercial use progra m available at http://w ww.darkside.c om.au/snow and is authored b y Matthew K wan. ISTE-STTP on Network Security & Cryptography , LBSCE 2004 The encodin g sche me used by snow relies on the fact th at spaces and tabs ( known as whitespace ), when appearing at the end o f lines, are invisible when d ispla y e d in prett y well a ll text viewin g programs. This allows messa ges to be h i dden in ASCII t ext wi thout aff ecting the text's visual representa tion. And since trai ling spac es an d ta bs occasionall y occur naturall y, the ir e xistence should not be s ufficient to i mmediatel y ale rt an obser ver who st umbles across the m. The snow pr ogram ru ns in two modes - messa ge concealme nt, and mess age extra ction. During concea lment, t he followin g steps are ta ken. Message -> optional c ompression -> optional encr yption -> concealme nt in text Extracti on reverses t he process. Extract data from te xt -> optional decr y pt ion -> optional unc ompressi on -> messa ge The progra m has the ha ndy a bility to tell you how much data it c an fit i n the desired c over file: Issuing t he comma nd “snow –S cover .txt” produc es the f ollowing output: File has stora ge capac ity of betwee n 1763 and 2012 bits. Our e mbedded data, m y sec ret.txt is only 10 7 bytes, so we know it will easil y f it wit hin this cover fil e. If spac e is of concer n, the program al so offers a fla g t o compress the data, howe ver the aut hor n otes that “if t he data is not text, or of there is lot o f data, the u se of the built-in compres sion is not recommen ded”, and suggests that the user pre-c ompress t he da ta wit h more r obust compressi on tools such as winzip. Snow al so provide s t he abilit y t o encr ypt t he data to be hidde n with a pass word-protecte d key. It uses the au thor’s own I CE encr yption protocol, allowin g for pass words or pass p hrases o f up to 117 0 character s. ICE stands f or Information Conceal ment Engine . It is a 64-bit pri vate ke y block ci pher, in t he traditi on of DES. However, unlike DES, it was designe d t o b e secure a gainst differe ntial and linear cr yptanal y sis, and has no ke y compleme ntation wea knesses or weak keys. In addition, its key size ca n be an y multi ple of 64 bits, whereas the DES ke y i s li mited to 5 6 bits. The ICE algorithm is publ ic d omain, and source c ode ca n be downloa ded. To em bed our secret data in our file we issu e the comman d: snow –C –f mysecret.t xt –p mypa ssword cove r.txt stego.t xt This comma nd c ompresses t he message c ontained in m ysecret.txt, e ncrypts it with the password- protected k e y using “m ypassword” and embeds it in cover.txt, creating the stego file called stego.t xt. The output fr om the com mand inf o r ms t he user that it compressed the origi nal me ssage by 41.87% and that the message used a pproximatel y 25. 14% of the available spa ce in the c over file. The extraction process is just a s strai ghtfor ward, issuing the c ommand: snow –C –p mypassword st ego.txt will output the c ontents of o ur sec ret message file to open. The ste go.txt, when opened with a c ommon text editor, like M icr osoft Word, lo oks identical to the origina l, despite ha ving gai ned 655 b yt es in size with t he addition of the secret message. Also, b y telling Microsoft W ord t o sh ow spec ial format ting marks, one can e asil y see the i nserted tabs and spaces in the ste go document. Due t o t he pre sence of strong encrypti on scheme an d wit hout knowing t he pass word the attacker can not extra ct the hidden messa g e. 3.5 Data Hiding in the Graphic File s Coding secret messa ges i n digital images is b y far the most widely use d of all methods in the digital world of today. This is because it ca n take advantage of the limited power of the h uman visual s ystem ( HVS). Almost a n y plai n te xt, ci pher text, image and an y other media t hat can be encoded into a bi t stream can be hidden i n a di gital ima ge. With the contin ued growt h of strong graphics power i n computers and the researc h being put into image ba sed Ste ganograph y , this field will conti nue to grow at a ver y rapid pace. To a c omputer, an i mage is an arra y of n umbers t hat represent li ght intensitie s at vari ous points, or pixels. These pixels make up the ima ges ras ter da ta. W hen dealing with di gital images f or use with Steganogra phy, 8-bit and 24- bit per pixel i mage f iles are t ypic al. Both ha ve adva ntages an d disadva ntages, as we will explain below . 8-bit i mages are a great format to use becau se of t heir rel atively small size. The drawback is that only 25 6 possible c o l ors ca n be used which can be a potential pr oblem d uring encodin g. Usuall y a gra y scale c o l or palette i s used when dea ling with 8- bit images such as ( .GIF) because its gradual change in c olor will be ha rder to detect after t he image has been enc oded with t he secret messa ge. 24-bit images offer muc h m o re fl exibility wh en u sed for Steganogra phy. The large numbers of col ors ( over 16 million) that can be u sed go well b e yond t he HVS, which makes i t very har d to dete ct once a secret message, has bee e ncoded. The othe r benefit is t hat a much larger a mount of hidden d ata can be e ncoded into 24-bit digital image a s opposed to a n 8-b it di gital image. The one major drawbac k t o 24-bit digital images is their l arge size (us uall y i n MB) makes them ISTE-STTP on Network Security & Cryptography , LBSCE 2004 more suspect than the much s maller 8-bi t d igital images (usually in K B) when se nt over a n op en system suc h a s Internet. Digital i mage compres sion (lossy compressi on – jpeg) i s a good solution t o large di gital images such as 24 -bit i mages mentioned earlier. Informati on can be hid den man y di fferent ways i n images. Strai ght mes sage insertion can be done, which wil l simpl y e ncode eve ry b it of informati on in the ima ge. M ore c omplex encoding can be d one to embe d the messa ge onl y in ``noisy'' are as of the image that will attract less at tention. The message may a lso be scatter ed ran doml y thr oughout the cover i mage. The most c omm on a pproaches to information hiding in i mages a re: • Least significa nt bit (L SB) inserti on • Masking a nd filtering tec hniques • Transform ations Each of th ese can be applied to various images, with var ying de grees of s uccess. Eac h of the m suffers to varying degrees from operations perf ormed on ima ges, suc h as crop ping, o r resoluti on decrementing, or decreases in t he colour depth. • Least Sig nificant Bit Insertion The l east signifi cant bit i nsertion method is probabl y the mos t well-known image steganogra phy techniq ue. It is a comm on, simple approach t o e mbeddi ng i nformation i n a graphical image file. Unfortu nately, it is extremel y vulnera ble t o attac ks, suc h as image manipulati on. A simpl e conversi on from a G IF or B MP f ormat to a l ossy com pression f ormat such a s JP EG can destro y t he hidde n information in t he image. When appl y in g LSB techniq ues t o each byte of a 24-bit ima ge, t hree bits can be e ncoded i nto eac h pixel. ( As each pixel i s repres ented b y t hree b ytes.) Any change s in the pixe l bits will be i ndiscernible to t he human e ye . For e xample, the letter A ca n be hidden in t hree pixels. As sume the ori ginal three pixels ar e represented b y t he three 24- bit words below: ( 00100111 11101 001 11001000 ) ( 00100111 11001000 11101001 ) ( 11001000 00 100111 11101001 ) The b i nar y value f or t he letter A i s (10 000011). Insertin g the binar y value of A into the thre e pixel s, starting fr om the top left byte, wou ld result in: (00100111 1110100 0 11001000) (00100110 11001000 1110100 0 ) (11001000 00100111 11101001) The emp hasised bits are the onl y bits that act uall y change d. The main adva ntage of LSB insertion is that da ta ca n be hi dden i n th e l east a nd sec ond to l east bits and still the human e ye would be unable t o notice it. When usin g LSB tec hniques on 8-bit i mages, more care needs t o be ta ken, as 8-bit formats are not a s forgiving t o data c hanges as 24-b it f ormats are. Care needs t o be t aken i n the selecti on of t he c over i mage, so that cha nges to the data wil l not be visible in t he stego-ima ge. Commonl y known i mages, (suc h as famous pai ntings, like t he Mona Li sa ) shou ld be avoided. In fact, a simple picture of your do g woul d be quite suff icient. When modif ying t he LSB bits in 8-bit ima ges, the pointers to e ntries in the pal ette are c hanged. It is important to remember that a change of e ven one bit could mean t he differenc e between a s hade of red an d a shade of blue. Such a chan ge would be i mmediatel y noticeable on the displa yed i mage, and is t hus unaccepta ble. For this rea son, data- hiding e xperts recommend usin g grey-scale palettes, where the differences between shade s is not a s pronounced. • Masking and Filtering Masking and f ilterin g techni ques hi de inf ormation by marking an ima ge i n a manner similar to pap er watermar ks. Because water marking tec hniques a re more i ntegrated into t he i mage, the y ma y be applied without fe ar of image destruc tion from loss y compression. B y coveri ng, or masking a f aint but perceptible signal wit h another to make t he first n on- perceptible, we e xploit the fact that the hu man visual system c annot detect slight chan ges i n cert ain te mporal domains of t he image. Masking tec hniques are more suitabl e f or use in l ossy JPEG images t han LSB ins ertion because of t heir relative i mmunit y to image o perati ons suc h a s compression a nd croppi ng. • Transfor mations Transform Domain tools util ize an algo r ithm suc h as the Discrete Cosine Transfor mation (DCT) or wavel et transformation to hi de inf ormation in significa nt are as of the image. The J PE G image f ormat uses a d iscrete cosine transf ormation (DCT) to transf o rm successi ve 8x8 pi xel bl ocks of the image into 64 DCT c oefficients each. The least -significant bits of the quantized DC T coefficients are used a s redu ndant bits i nto whic h t he hidden message is embed ded. The m odification of a single DCT coefficient affe cts all 64-image pixels. For that rea son, there are no kn own visual attac ks a gainst the JPEG image format. Stego-tool s which utiliz e one o f the ma ny transf orm domain techniques are m ore robust, ha ve a higher resilience to attacks agains t the ste go-image s uch a s compression, cropping a nd image processin g. As of this writing al l of the stego-tools which can ma nipulate JPEG ima g e s are tra nsform domain tool s s uch as; ISTE-STTP on Network Security & Cryptography , LBSCE 2004 Jpeg-Jste g, JPHide, Outgues s, PictureMarc an d S y sCop. Figure 7: Block Diagra m of JPEG image compression 3.5.1 Pixel Calculator There are a number of e asy t o use t ools a vailable on the Internet t o hi de information in ima ge files. To b et ter u nderstan d a nd ap preciate some o f the processes used b y these tools some understa nding of digital i mage pr ocessing becomes ess ential. Written by Steve Tenim oto and his te am at Universit y of Was hington, Pixel Calc ulator is a ver y int eresting tool t o understand di gital images. Pixel Calculator a lso pr ovides a neat fe ature of achieving som e ver y basic Ste ganograph y. Pixel calculat or is e quipped with two basic t ools. A zoomin g tool is provided t o l earn the exa ct pixe l value by z ooming into an ima ge u ntil the pixel values are visible. A calc ulator tool i s the n used to change or modify pixel values. Learning the pixel values a nd chan g i ng them us ing the calc ulator is the key in hiding the inf ormati on i nside a n image. Figure:6 depic ts t he image file I us ed a s cover t o hide the inf ormation. I used the z ooming to ol to f ind a n are a of interest where nei ghboring pixel val ues are close to each other. These values are visible in Figure 8. Usin g the calculat or tool, I started to replace the pixel values in the image with a magic numbe r, sa y 90. I repeated thi s process until I wa s done t y pin g t he hidden messa ge. Figure 9 shows the image with a h idden message on the left hand side and the dec oded me ssage at the right hand s ide. The red circle on top o f the mountai n pea k represent s t he are a where the messa g e is hidden. To decode t he messa ge, calculator tool is used a gain to c onvert bits lowe r than the “magic number” to “0” whereas, t he higher ones are c onverted to “255.” This process converts rest of the image bla ck an d white, w hile revealing t he hidden message in gra y color. Figure 8: Cover Image and Unif orm Pixel Area 3.5.2 Conce aling M essages i n JPEG Image File s: Jsteg Jsteg hi des the da ta i nside ima ges stored in t he JFIF format of the J PEG standard. It was believed that t his t y pe of stegano graph y was impossible, or at least infeasible, since the JPEG standard uses lossy encodin g to c ompress its data. An y hidden data would be overwhelme d b y the noise . The t rick u sed by t his steganogra phic implementati on i s t o r ecognize t hat JPEG enc oding i s split int o l ossy and non-l ossy sta g e s. The l ossy sta ges use a discret e c osine transf orm and a quantizati on ste p t o com press the image data; the n on- lossy stage the n uses Huffman codi ng t o further compress the i mage data. As suc h, we c an insert t he steganogra phic data into the i mage data bet ween those two steps and not risk c orruption. Figure 9: Encoded Picture and Decoded Messa ge To comp ile the package, simpl y f ollows t he step s given: To inject a data file into a J PEG/JFIF ima ge, simpl y add the option "-steg f ilename" t o the " cjpeg" command line. If the da ta file is too l arge for the image, " cjpeg" will inform you. At this point, you c an compress the data file, incr ease t he qualit y of the image ( thereb y increasin g ima ge size), or t ry a different i mage. ISTE-STTP on Network Security & Cryptography , LBSCE 2004 Extracti on of a data file works similarl y. The "- steg filena me" opti on to "djpeg" writes t he steganogra phic data t o the file, wiping out its previous c ontents. Usuall y, the decoded i mage sent to stan dard output is red irecte d to "/dev/null".’ 3.6 Data Hiding i n Audio File s Encodi ng secret messa ges in au dio is the mos t challengi ng technique to u se when dealing with Steganogra phy. This is be cause the huma n audit or y system (HAS) has such a d ynamic range that it c an listen over. T he HAS perc eives over a ra nge of power greater than one bi llion to one and a range of frequencies greater tha n one thousa nd to one. Sensitivit y to a dditive rando m noise is a lso ac ute. Pert urbations in a sound file c an be detected as low as one part i n t en million. However the re a re some “holes” av a ilable i n this p er spective r ange where data ma y be hid den. While the HAS has a large dynamic range, it often ha s a fairl y small differe ntial r ange. A s a result, loud sounds te nd t o mask out quiet soun ds. Ther e are s ome environme ntal di stortions so c ommon a s t o be ignored b y the listener in most c ases. There are two conce pts to consider bef ore ch oosing an enc oding techniq ue for audi o. The y ar e the digital f ormat of the a udio a nd the tra nsmission medium of t he audio. There are three main digital a udio for mats typicall y in use. The y are Sample Quantization, Temporal Sampling Rate and P erceptual Sampling. • Sample Q uantization which i s a 16-bit linear sampling archi tecture used by popu lar audio formats such as . WAV and . AIFF. • Temporal Samplin g uses se lectable frequencies (8 kHz, 9.6 kHz, 10 kHz, 1 2 kHz, 16 kHz, 22.05 kHz and 44.1 kHz.) t o sample the a udio. Sam pling ra te puts an up per boun d on the usable porti on of the frequenc y ra nge. Generall y, the higher the sam pling ra te is, the higher the usa ble data space gets. • Pe rceptual Sam pling f ormat c hanges the statistics of the a udio drastic ally b y enc oding only the part s the l istener perceives, thus maintaining the sound but changing the s ignal. This format is used b y t he most p opular digital audio on the Inter net toda y in ISO MPE G (MP3). Transmiss ion medium (pat h the a udio takes fr om sender t o re ceiver) mus t also be considered when encodi ng secret messa ges in au dio. The f our transmissi on medium s are discussed below. • Digital e nd-to-end en vironme nt: If a sound fi le is c opied directly from machine t o m ac hine, but ne ver modifie d, then it will go thr ough this environme nt. As a res ult, the samplin g will be exactl y the same between the e nc oder and decoder. Ver y l ittle c onstrai nts are p ut on data hiding in thi s environ ment. • Increased/de creased re sampling e nvironment: In this envir onment, a si gnal is r esampled t o a hi gher or lower sam pling rate, but re mains di gital throughout. Althou gh t he abs olute magn itude a nd phase of mos t of the signal a re pre served, t he temporal c haracteristic s of the signal are cha nged. • Analog t ransmission and resampl ing: This occurs when a signal is c onverted to a n anal og state, played on a relati vely c lean anal og line, and resampled. Absolute si gnal magnitude, sample quantisation an d temporal sampling rate are not preserved. In general, p hase will be preserve d. • ''Over the air'' en v ir onment: T his occ urs w hen t he signal i s ` `played into the a ir'' a nd ``resa mpled with a micr ophone''. The signal will be s ubjected to possible unknown nonlinear modifications causing pha se change s, ampl itude chan ges, drifting of different frequenc y components, echoes, etc. The signal representatio n a nd transmissi on environment both need to b e considered when choosing a data- hiding method. 3.6.1 Met hods of Audio Data Hidin g We now nee d t o consi der so me methods of audio da ta hiding. In l ow-bit encoding data is embedded by replacing the Leas t Sign ificant Bit (LSB) of eac h sampling point by a coded binar y string. This results in a lar ge am ount of data that ca n be encode d in a si ngle audi o file . For examp le if t he ideal n oiseless channel capaci ty is I K bps then t he bit rate will be 8 Kbps give n an 8 kHz sampled sequence. W hile t he si mplest way to hide data in the audio f iles, low- bit encodin g scheme ca n be destroyed by the chan nel noise a nd re-sampling. Phase coding when i t can be used has proven t o be m ost effec tive cod ing tec hniques i n ter ms of signal to noise rati o. In this method the phase of the original audi o signal is repla ced with the refere nce phase of the data t o be hidden. It is discovere d that a channel capacit y of approxima tely 8 b ps can be achie v e d by al locating 128 f requency slots per bit with a little background noise. The procedur e f or p hase coding is a s follows: • The original s ound se quence is broke n into a series of N sh ort segments. • A discrete Fourier transf orm (D FT) i s applied to ea ch segment, to brea k crea te a matrix of the phase and magnitude. • The p hase d iff erence bet ween eac h a djacent segment is calc ulated. • For segment S0, the first segment, an artificial absolute phase p0 is created. ISTE-STTP on Network Security & Cryptography , LBSCE 2004 • For all other se gments, ne w pha se frames are cre ated. • The new pha se a nd original m agnitude are combined t o get a new se gment, Sn. • Finall y , the new seg ments ar e concatenated t o create the enc oded outp ut. For the decoding process, the sy nchr onisation of the se quence i s d one bef ore the decodi ng. The length of the segm ent, the D FT points, and the data inter v a l must be known at th e receiver. T he value of the underl ying phase of the first se gment is detecte d as 0 or 1, which represent s t he c oded binary stri ng Figure 10: A sinusoidal Funct ion * , characterized by a peri od (L), an a mplitude (A) and a pha se( φ φ φ φ ) Note: The length of the cycle, L is known as the period of the f unction. The am plitude is the size of the v ariation – the height of a peak or depth of a trough. The phase is the position of t he start of cycle, relative to som e reference p oint (e. g., the origin) A sine fu nction has φ =0, where as a c osine function has φ = π /2 Modern steganogra phic s ystems u se sprea d- spectrum commun ications to t ransmit a narrowband signal over a much larger bandwidth so t hat the s pectral density of the signal in the channe l l ooks like noi se. The two different sprea d-spectrum techniques t hese tools e mploy a re cal led direct -sequence and frequency ho pping . The former hides information by phase-modul ating the data signal (carrier) with a pseudorand om nu mber sequence t hat b oth the sender and the recei ver know. The la tter divi des the availa ble bandwidth i nto multiple channel s and hops between these channels (also triggered b y a pseudorandom number se quence). Echo hi ding, a f orm of data hidin g, is a method for e mbedding informati on int o an audio si gnal. It seeks to d o so in a robust fashion, while not perceivabl y degrading the host signal ( cover a udio). Ec ho hiding introduces c hanges to the c over a udio tha t ar e characteristic of en vironmental conditions rather tha n random noise, thus it is r obust i n light of man y loss y data compre ssion algorithms. Like all good Stegano graphic methods, echo hiding seeks its data into data stream with minimal degradation of the original data strea m. B y minimal degradati on, we mean t hat the c hange i n the cover a udio is either i mperce ivable or simpl y dismisse d by the listener a s a c ommon n on- objectiona ble environme ntal dist ortion. The partic ular distorti on we ar e introducing is similar t o t he res onances found i n a room due to walls, furniture, etc. T he difference be tween t he stego audio a nd the cover audi o is similar to the difference between lis tening to a compact disc on headphones and listening to it form s peakers. With the hea dphones, we hear the sound as i t wa s recorded. With the speakers, we hear the sound plus echoes caused b y r oom acoustic s. By correctl y ch oosing t he distorti on we are introduci ng for e ch o hiding, we can make such distortions i ndistinguishable f rom t hose a r oom might intr oduce in the a bove spea k er c ase. 3.7 Con cealing M essages in I mage an d Audio Files Using S-Tool s S-Tools (Ste ganograph y Tool s) brings y ou the capabilit y of concealing file s within vari ous f orms of data. Users of S- Tools can opt t o encr y pt their information using the strongest sta te-of-the-art encr y pti on al gorithms currentl y known within t he academic world, so t hat eve n an enem y e quipped with a c opy of S-Tools cann o t be completel y sure data is hidden unless he has your secret pas sphrase. You could use S-T ools to conceal pri v ate or confidential informat ion t hat you don't want to f all into the wrong ha nds. You c ould use it to send inf o r mation to a nother indi vidual via a br oadcast networ k such as Usenet. B y a greeing on a passphrase you can keep the information out of unauth orised hands. Alternativel y you c ould use S-Tools to verify your cop y ri ght over an image b y storin g an e ncrypted cop y righ t stateme nt in the graphic a nd extractin g it in the e vent of a dispute. How S-Tools hides yo ur data S-Tools can hide multi ple files in one object. If you have selected c ompression then the files are individuall y c ompressed and st ored together with their names. If y ou are n ot using c ompressi on t hen just the raw fil e data is stored al ong with the names. Then S- Tools pre pends some rand om garbage on t o t he front of the data in order to prevent two ident ical set s of file s encr y pti ng the same. The w hole lot is then e ncr y pted using t he pas sphrase that you ch ose t o generate the key (actuall y , MD 5 is used to hash the passphrase d own to 128 eve nly distributed key bits). The e ncr y pti on algorithms a ll operate in Cipher Feedback Mode (CFB). ISTE-STTP on Network Security & Cryptography , LBSCE 2004 It would be to o eas y to hi de the da ta b y just spreading i t acr oss the a vailable bits in a linear fashion, so S-Tools seeds a cr yptographicall y strong pse udo-random num ber generat or f rom your passphrase and u ses its outp ut in order to c hoose the positi on of the next bit from t he cover data t o use. For instanc e, if your soun d file had 1 00 bits available for hidin g , and you wante d to hi de 10 bits in it, t hen S-T ools w ould not choose bits 0 thr ough 9 as t hat would be tr iviall y detectable b y a potentia l enem y . Instead it might c hoose bits 63, 32, 89, 2, 53, 21, 3 5, 44, 99, 80. Or it might c hoose a ny te n others, it all depends o n the pa ssphrase t hat y ou enter. As you can s ee, the job o f a potential enem y has just become ver y difficult indeed. How data is hidden in sound s Sound samples are, b y their ver y n ature, inaccurate estimates of t he correct value of t he soun d wave at a particular moment in time. The s ound s amples in Windows WAV files are stored as either 8 or 16 bit values that event uall y get pas sed to the DA converter in your so undb oard. For 8 bit s ampl es this mea ns that the va lues can range between 0 and 255. 16 bit samples range betwee n 0 and 65535. All S-Tools does is t o distri bute the bit- pattern that correspond s to t he file t hat you want to hi de a cross the least significan t bits of the s ound sam ple. For example, supp ose that a sound sa mple had the following e ight b y tes o f inf ormation in it somew here: 132 134 137 141 121 101 74 38 In binar y, this is: 1000010 0 1000011 0 10001 00 1 100 0110 1 0111100 1 0110010 1 01001 01 0 001 0011 0 (LSB of each b y te shown in ita lics) Suppose t hat we want t o hi de the bin ary byte 11010101 (213) inside this sequence. W e simply replace the LSB ( Least Significa nt bit) of each sample byte w it h the correspondi ng b it from the byte we are tr ying t o hi de. So t he a bove s equence will chan ge to: 133 135 136 141 120 101 74 39 In binar y, this is: 10000101 10000111 10001 000 100 01101 01111000 01100101 01001 010 001 00111 As you c an clearly see, the v alues of the sound samples ha ve chan ged by, at m ost, one val ue either way. This will be ina udible to the human ear, yet we have c onceal ed 8 bits of informati on within t he sample. This is t he theor y b ehind how S- Tools does its job. How data is hidden i n pictur es All c omputer-base d picture s ar e c omposed of a n arr ay of d ots, called pixels, t hat ma ke up a very fi ne grid. Each one o f these pi xels has its own c olour, represented internall y as separat e quantitie s of re d, green and blue. W ithin Wind ows, ea ch of the se c olour levels may range betw een 0 (none of the colour) and 255 (a f ull amount of the colour). A pixel with an RGB value of 0 0 0 is blac k, a nd one with a value of 255 255 2 55 is white. S-Tools works by 'sprea ding' the b it-pattern of t he file that y ou w a nt to hide acr oss the least-signif icant bits (LSB's) of the colour level s in the image. For a 24 bit image this is simple becau se 24 bit images are stored inter nally as RGB triples, a nd all we nee d to do is spread our bits a nd sa ve out the new file. T he drawback to thi s is t hat 24 bit i mages are uncomm on at the m oment, a nd woul d t herefore att ract t he atten tion of thos e w hose atte ntion you are tr ying to avoid attracting! They are also ver y lar ge as t hey c ontain 3 bytes f o r e very pixel (f or a 640x4 80 i mage this is 640x480x 3=921600 bytes). It i s considerabl y m ore difficult to hide an y t hing within a 256-colour image. This is be cause t he ima ge may alread y h a ve o ver 200 col ours whic h our meddling wil l carr y to way over t he absol ute maximum of 256. Looking at a little t heor y it is ea sy t o see that an ima g e with 32 or less c olours will never e xceed 2 56 col ours, no ma tter how m uch we me ddle with it. To see this, visualise the 3 LSB's of an RG B tr iple as a 3-bit number. A s we pass thr ough it in our hidin g pr ocess we ca n c hange it to an y one of 8 p ossible values, the binary digits from 000 to 111, one of which is the original patter n. If one colour can 'expand' to up t o 8 colour s, how many distinct c olours can w e have before we are in danger of excee ding t he li mit o f 256? Simple, 256/8=32 colours. There is no guaran tee that 32 colours i s our upper limit f or ever y fi le that you want to hide though. If you're l ucky t he file will not change a c olour t o all of it s 8 p ossible combination s and the n we are able to keep one more of t he ori ginal col ours. In practice, however, you wil l often find pictures being reduced to t he mini mum of 3 2 colours. S-T ools tries t o reduce the number of ima ge colours i n a manner t hat preserves as much of t he image detail a s possible. I use d a progra m call ed FileRa y , to compare the binar y values of t wo ima ge files that were operated on using ISTE-STTP on Network Security & Cryptography , LBSCE 2004 S-Tools. c ov.gif was used as the co ver mediu m t o hide ste go.gif. T he resulta nt file was named hidden. gif. C omparison of the origina l image to the ste go data reveals cha nges in the LSB. Figure 11 s hows the comparis on betwee n the two image files. T he ori ginal ima ge is sh own in t he bott om pane and the s teg o i mage i s r eflected in the top pane. 4. Stegan alysis As the techniq ues to hide information get more complica ted a nd com putati onally i nvolved, the detecti on of s uch cover medium has become considera bly more c hallenging as w ell. Howe ver, given ti me, dedicati on an d te chnolog y it is possible to de tect t he pre sence of hidden informati on in some stego mediu ms. A fe w to ols have known signature s t hat ma y predict the presence of hi dden information. Techniq ues like encr yption an d compressi on ar e used to make it difficult t o decipher the hidden i nformation. However, knowing the f act that there is hidden inf ormation present in the cover destro ys the purpose of steganogra phy. Figure 1 1: Comparis on of co ver image wit h stego in binar y Steganal ysis is “the practice of attac king Steganogra phic methods by d etection, destr uction, extracti on or mod ification of em bedded dat a”. This is the Ste ganogra phic a nalogue to c ryptanal ysis, which refer s t o atte mpts to brea k cr y ptogra phic protocols. With Cr yptographic protocols, cr y ptana lysis is generall y c onsidered t o be succefu l if t he adversar y can re trieve the encr ypted message. Steganogra phy adds the addit ional require ment that the stegano graphicall y hidden message is not even detecta ble b y t he adve rsary; t hat is, not onl y shoul d the attacker not be a ble t o find t he messa ge, but he should n ot e ven know i t e xists. The defin ition of success in ste ganalysis depe nds upon your intent. For the securit y professi onal c harged with pr otecting hi s emplo y er ’s data, a successful result would be proving the existe nce of hidden data being sent, and not necessaril y the abilit y to e xtract it. F or the data thief, wishing t o perhaps use a digital image that c ontains a protective watermar k, succe ss would be not onl y detectin g the e xistence of the watermar k , but would also re quire destr oying it without damaging t he integrit y of the desired c over file. Research shows that some well-known tools like S- Tools ha v e known signatures and c an be re cognized if proper technique s a re used. S-Tool s w orks by re ducing the number o f colors of the cover image to 3 2, but expands t hem over several col or palet te entries, if t he palette is then sort ed by l uminance, bl ocks of col ors appear to be the sa me, but actual ly ha ve a one-bit variance. This t y pe of variance pattern is extremel y rare in a natural image. There ar e six formal categorie s of detecti on techniq ues available for steganal ysis. The f ollowin g table summarizes what the atta cker has availabl e to him in each case: Stego Object Original Cover Object Hidden Message Stego Algorith m or Tool Stego only X Known cover X X Known message X X Chosen stego X X Chosen message X Known stego X X X A stego only attack , while c onsidered the most diff icult attack i n tha t one has the lea st inf ormation to go on, i s far from im possible, especi all y if ones goal is to merel y dete ct t hat there is a hidden message a nd n ot necessaril y ha ve t he ne ed to extract it. For text f iles using e mpty s pace methods, like the one u sed with the Snow tool, m erely opening the documen t with an editor t hat shows f ormatting code s woul d i ndicate t hat there were oddities in the f ormatting. The m essage could be easil y de stroyed throu gh simply removi ng the extra spaces and ta bs. S imilarly, for other text meth ods such a s line and wor d shift meth ods, vis ual inspec tion of t he te xt itself c ould indicate an omalies. For i mage and audi o files with me ssages embed ded with LSB methodol ogy, detection with onl y the stego file available i s a little more difficult. Detection in this case ISTE-STTP on Network Security & Cryptography , LBSCE 2004 would rely on the appeara nce of visua l or a udible distortions or patterns. With t he “Known-c over” met hod, one has both the original innocent cover file a s well as the resulting stego file. A nomalous patter ns and exce ss n oise in the ste go file are much more easil y detectab le whe n compari ng it to the original, particular ly if the fi le format makes use of compre ssi o n (as in JPEG files) that would s how u p as excess noise even in as innoce nt fi le. Destruct ion or dist ortion of L SB encode d messages in ima ges in i mage files can be simpl y a matter of zeroing out t he LSB fields of the file in question , image c onversion, croppi ng or th e applicati on of other ima ge formattin g change s. For audio files, m ethods to da mage the hidden messa ge include then intr oduction of a random relative amplitude si gnal a nd rec onstructi ng the fil e b y ignoring bad signals. A “known- message” attac k gives the attac ker the knowled ge of the secret messa g e tha t i s hidden in the file. A “c hosen-stego” attac k provi des the a ttacker with the extracti on tool to reac h the data, and the “chosen message” tech nique a ssumes t he attac ker has the s tego tool itself, and can embed and detec t messa g e a t will. There are other ways to brea k up attac k-types, and these are al so useful in describing t he vulnera bilities of various me thods. Wa yner di vides common attac k methods b y functiona l properties rather tha n adversarial as sumptions; a ttacks are divided into visual or a ural at tacks, struct ural attacks, and statistical attac ks. Vi sual and aural attacks de scribe the huma n fact or in attac ks; humans can often percei ve t he modificati ons in the cover obj ect because it d oesn’t l ook or soun d right. In te xt ste ganograph y this ca n be e xtended to format- based, le xical, g ram matical, semantic, and rhetorical attac ks. Among others. Struct ural attac ks refer to detectin g the patte rns in m odifications made in the data f ormat (for example, using e xtra space in files or enc oding schemes to store information is often detectable through structural attacks). Statistical attac ks dete ct anomalies in the statistical profile of t he stego -object (f or e xample, images whose color palette has bee n changed to hide information often contain n on-standard c olors or range s of c olors which would not normally be generated b y image s oftware). 5. Digital Watermark i ng -- Steering the Future of Security Watermar ks were first used i n Eur ope t o ide ntif y the guild t hat man ufactured paper. The y were like trademarks or signature s. Var y ing t he paper’s density c reates watermar ks in paper. Normall y invisible, a water mark ima ge become s visible as darke r and l ighter areas w hen the paper is held up to the light. Wire or re lief scu lptures are placed i n the paper mold and when t he paper slurr y is drained of its water a nd dried t he thin ner are as cr eated by the wire or sculpture show clearl y when held up to the li ght. Wate rmarks are still used in qualit y stationa ry and have e v e n been added to c urrencies of various c ountries. A watermar k is a form, image or text that is impres sed onto pa per, which pr ovides evi dence of i ts authenticit y. Digital wate rmarking is a n extension of thi s c oncept in the digital world. In rece nt ye ars t he phenome nal growth of the Internet ha s hi ghlighted the need f or mechanis ms to pr otect own ership of di gital me dia. Exactl y identical copies of digital information, be it images, text or audio, can be produced a nd distri buted easil y . In such a sce nario, w ho is the artist and who the plagiarist? It’s impossible t o tel l--or w as, until now. Digital water marking is a techni que that pr ovides a solution t o t he longsta nding pr oblems fa ced with copyrightin g digital data. Digital watermar ks are pieces of inf ormation added to digital data ( audi o, video, or still images) that c an be detected or extra cted later t o make an assertion about the data. T his i nformation can be textual data a bout t he author, its c opyright, etc; or it can b e a n i mage itself. The digital watermarks re main intact under transmission / tra nsformati on, allowing us to p rotect our ownershi p rights in digital form. Figure 12: Watermar k in currency Watermar k on new $100 bill shows Benjamin Franklin when you hold the bill up to the light. A given water mark ma y be unique to eac h cop y (e. g. to identif y the intende d r ecipient), or be com mon to multiple c opies (e. g. to i dentif y the docume nt s ource). ISTE-STTP on Network Security & Cryptography , LBSCE 2004 In eit her case, the watermarki ng of the doc ument involves t he t ransformati on of t he original into another f orm. Th i s distinguis hes di gital watermar king from digital f ingerprintin g, w here the o r iginal file remains in tact and a new create d file 'descri bes' the original file 's content. 5.1 General Framewor k for Wat ermarking A digital watermark i s, in essence, a hidde n messa g e, withi n a digitized i mage, video or a udio recordi ng. The watermar k is i ntegrated into the content i tself. So it require s no additi onal stora ge space. In general, a ny watermarki ng scheme (a lgorithm) consists of three parts. • The watermar k • The encoder (insertion al gorithm) • The decoder an d comparator (verificat ion or extraction or detecti on algorithm) Figure 13: Digital Cop y of fif teenth century drawing wi th digital wate rmark super imposed. Each owner has a unique watermar k or an owner can als o p ut diff erent water marks in di fferent objects. The mar king a lgorithm i ncorpora tes t he watermar k i nto the object. The verification algorithm a uthenticates the ob ject determ ining both the owner a nd the inte grity of the ob ject. 5.1.1 Encoding Process Let us de note an image by I, a signa ture b y S= s1,s2,… and t he watermarked image b y I. E is a n encoder f unction, it ta kes an image I a nd a signature S, and i t generat es a new i mage w hich is called watermarked i mage I, mathemat ically, E(I,S) = I ′ ………………….. (1) Figure 14: E ncoder 5.1.2 Decoding Pr ocess A decode r function D ta kes an ima ge J (J can be a watermar ked or un- watermarked image, and possibl y corrupted) wh ose ownership is to be deter mined and recovers a signature S’ f rom the image. In this process an additional image I can als o be include d which is often the original and un- watermar ked version of J. This i s d ue to t he fact that some e nc oding s cheme s may make use of the original images in the watermar king process t o provide e xtra robustne ss against intentiona l and uni ntentional corr uption of pixels. Mat hematicall y, D(J,I) = S ’ ………… . (2) The extracted si gnature S’ wi ll t hen be c ompared with the owner signat ure seq uence b y a c omparator f unction C δ δ δ δ and a binar y output d ecis ion generate d. It is 1 if there is match a nd 0 otherwise, which c an be represented as f ollows. Where C is the c orrelator, x= C δ δ δ δ ( S’, S). c is the correlati on o f t wo signatures and δ δ δ δ i s c ertain threshol d. Without loss of generalit y, w atermar king sc heme can be tre ated a s a t hree-tupple (E, D, C δ δ δ δ ). Following figures de monstrate the d ecoder and the compar ator. Figure 15: Decoder Figure 16: Comparator A water mark must be detectable or extra ctable t o be useful. De pending on the wa y the watermark is inserted a nd depe nding o n the nature o f the watermar king al gorithm, the method can i nvolve ver y ISTE-STTP on Network Security & Cryptography , LBSCE 2004 distinct app roaches. In some wa termarking schemes, a water mark ca n be extra cted in its exact form, a pr ocedure we call watermar k ext raction. In other cases, we can detect onl y whether a specific given water marking signal is prese nt in a n i mage, a procedure we call water mark detecti on. It should be noted that water mark extrac tion can prove ownershi p whereas wa termar k de tection ca n onl y verif y ownership. 5.2 Watermarking Algorithms Watermar ks an d water marking tec hniques can be divided int o vari ous ca tegories i n various ways. The water marks ca n be ap plied in spatial d omain. An alt ernative t o spatial domain watermarking is frequenc y domain watermarking. It has b ee n pointed out t hat the freque ncy domain me thods are more r obust than the spat ial domain tec hnique s. • A si mple Spati al water marking alg orithm -- The LSB techn ique The L SB techn ique is t he s implest tech nique of watermar k i nsertion. If we specif ically consider still images, each pi xel of t he color image has three compone nts -- red, gree n a nd blue. Let us a ssume we allocate 3 b y te s for each pi xel. Then, ea ch colour has 1 b y te, or 8 bits, i n which the in tensit y of that colour ca n be specifie d on a scale of 0 t o 255. So a pixel that is bright purple in colour would have full inte nsities of red a nd blue, b ut no green. Thus that pixel can be sh own as X0 = {R= 255, G=0, B= 255} Now let’s have a l ook at another p ixel: X1 = {R= 255, G=0, B= 254} We’ve changed all the value of B here. But how much o f a difference d oes it make to the hum an e y e? For the e ye, detecti ng a differe nce of 1 on a color scale of 2 56 i s almost imp ossible. Now since each c olor is stored i n a separate byte, t he last bit in each b yte store s this differenc e of one. That is, the differe nce betwee n v al ues 255 an d 254, or 127 and 126 is stored in the last bit, called t he Least Significa nt Bit (LSB). Since this differe nce d oes not m atter much, when we replace t he color intensity information in the LSB wit h watermar king inf ormation, t he image will still look t he sa me to the naked e ye. Thus, f or ever y p ixel of 3 b y te s (24 bits), we can hide 3 bits of waterma rking inf ormation, in the L SBs. Thus a simple algori thm for this techni que would be: Let W be watermarking inf ormation For every pixe l in the ima ge, Xi Do Loop: Store the next bit fr om W in the LSB positi on of Xi [ red] b yt e Store the next bit fr om W in the LSB positi on of Xi [ green] b yte Store the next bit fr om W in the LSB positi on of Xi [ blue] b y te End Loop To ex tract w ater mark i nformati on, we would simpl y need t o ta k e all t he data i n the LSBs of t he c olor b ytes and c ombine them. Image manipulat ions, suc h as resamplin g, rotation, f ormat con versions and cr opping, will i n m ost cases result in the water mark informa tion being lost. • Frequency based Wate rmarkin g Watermar king i n t he f requenc y d omain invol ves selecting the pixel s t o be modified base d on t he frequenc y of occurr ence of t hat parti cular pixel. This i s to overcome the great est disadvantage of tec hniques operating in t he spatial domain i.e. susceptibili t y to cropping. The m osaic atta ck (In a m osaic attack, the attacker breaks up t he e ntire watermarke d image int o many small parts. For exampl e, a watermar ked i mage on a w e b pa ge can b e cut up and reassembled as a whole using t ables i n HTML. The only de fence against this a ttack is t o t ile a very small waterma rk all over t he image, an d all ow retrie val of the water mark f rom a ny of t he s mall subsection s of the fragment ed i mage. However, the attacker can alwa ys create sma ller blocks, a nd the water marked im age als o has to be lar g e enough t o be distinguisha ble), defeats most implementat ions o f digital w atermar k i ng operati ng in the spatial dom ai n but the fr equency domain watermar king is less suscept ible. The LSB technique can a lso be applied in the frequenc y dom ain select ing the pixels accordin g t o frequenc y , though not r obust. Common transf orms, such as Fast Fourier Transform s, alte r the value of pixels within the original image ba sed on their frequencies. The watermar k is more c ommonl y applied to the lower frequencies within a n image as higher frequencies are usuall y lost w hen a n ima ge is compressed or to f requencie s c onsidered to c ontain perceptuall y si gnificant infor mation. Freq uency b ased techniques result in a water mark t hat is di spersed throughout t he ima ge, therefore, le ss s usceptible to attack b y cr opping. However these tec hniques are susceptible t o stan dard fre quency fi lters an d l ossy compression algorit hms, which te nd t o filter out less significant f requencies. 5.3 Types of Dig ital Watermarks Watermarks a nd waterm arking techni ques can be divided into various categories in various ways. The watermarks can be appl ied in spatial d omain. An alternative t o spat ial domain water marking i s frequenc y domain water marking. ISTE-STTP on Network Security & Cryptography , LBSCE 2004 Visible wat ermark is a sec ondary tra nslucent overlaid i nto the primar y ima ge. The water mark appears visible to a casual viewer on a careful inspection. A fra gile waterm ark is a mar k, whic h is sensitive to a modifica tion of the ste go-mediu m. A fra g ile watermar king scheme shou ld be able t o detec t an y change in the si gnal a nd identi fy where it has taken place a nd p ossibly w hat th e si gnal was bef ore modificat ion. It serves at proving the aut henticit y of a docum ent. On the opposite, a robust water mark should be stuck to the doc ument it has be en e mbedded i n, in such a wa y that an y s ignal transf orm of re asonable strength ca nnot re move the water mark. Hence a pirate willing to remove the watermar k will not succee d unless the y d ebase the document t oo much to be of c ommercial inte rest. Dual watermar k is a combina tion of a vi sible and an invisible water mark. In t his type of watermar k an i nvisible water mark is use d as a bac k up f or the visible watermar k as clear from the followin g diagram. Private watermar king a nd n on-blin d-watermarkin g mean the sa me: the origina l cover si gnal is required during the detection p r ocess. By as ymmetric watermar king or p ublic-ke y watermarki ng, people refer t o watermar king schemes with propertie s remindin g a symmetric cr yptos y ste m ( or public ke y cr y ptos ystem). No suc h syste m reall y exist s yet although som e possible su ggestions ha ve been made. In this c ase, t he dete ction pr ocess (and i n particular the detection ke y) is full y kn own to an y on e as opp osed t o blind watermar king where a secret key is requir ed. So here , only a 'p ublic key' is needed f or verificati on and a 'private key' (secret) is used f or the e mbedding th ough. Knowle dge of t he public key d oes not help to c ompute the pri vate ke y , it does not either allow rem oval of the mar k nor it allows a n attacker to forge a mar k. Source-base d watermar k are desirable f or ownershi p i dentifica tion or a uthenticati on where a unique watermark identif ying the own er is introduced to all copies of a particular image being distributed. A s ource-ba sed water mark c ould be used for authenticat ion and t o deter mine whethe r a recei ved image or other electronic data has been tempered wit h. The waterm ark c ould al so be estimati on-based where eac h distributed cop y ge ts a unique watermar k identifying the partic ular buyer. The destination-ba sed watermar k could be used to trace t he buyer in the case of illegal reselling. 5.4 Applic ations of Dig it al Wate rmarks Visible Water mark Visible watermarks ca n be used in the f ollowing case s: • Visible watermar king f or e nhanced cop y right protection. In such situations, wher e images are made a vailable t hrough Inter net t he c ontent owne r is concer ned that the i mages will be used commerciall y (e. g. Imprinting coffee mugs) without pa y me nt of r oy a lties. Here the c ontent owner desire s an owners hip mar k, that i s visuall y apparent, but w hich does n ot pre vent image being used for other purposes (e.g. scholarl y research). • Visible watermarkin g used to indicate owners hip origins. In this c ase i mages ar e made available through the Internet and t he content owne r desire s to indicate the ownership of t he underl y in g materials ( librar y manus cript), so an observer might be encoura ged t o patronize the institu tions that own t he material. Invisible Robust Water mark: Invisible r obust water marks find ap plication in following case s. • Invisible waterma rking t o de tect misappropria ted images. In thi s scena rio, the seller of di gital images is concer ned, t hat his, fee ge nerating images ma y be purchased b y an i ndividual who will ma ke them available for free, this w ould deprive the owner of lice nsing re venue. • Invisible watermarki ng as e vidence of ownership. In this scenario, the se ller that of the digital images suspects one of his ima ges has bee n edited and pu blished without pa y ment of r oyalties Here, the detection of the seller’s water mark in the image is intended to serve as evide nce that t he published i mage is pr operty of seller. Invisible Fr agile Water marks Following are t he applicati ons of invisible fr agile watermar ks. • Invisi ble wa termarking for a trustworth y camera. In this sce nario, i mages are captured with a digital camera f or later inclusi on in news articles. Here, it i s t he desire of a news a genc y to verif y that a n im age is true to the original capture and ha s n ot been edite d to falsif y a scene. In this case, an invisi ble watermark is embedded at capt ure time; its prese nce at the time of publicat ion i s intend ed to indicate t hat the image has not been atte nded s ince it w as captured. • Invisi ble watermarkin g to de tect alternation of images st ored in a digi tal libra ry. In this c ase, images (e. g. hu man f ingerprints) have been scanned a nd st o r ed in a digital libr ary; t he content owner desires the abilit y t o detect any ISTE-STTP on Network Security & Cryptography , LBSCE 2004 alternation of the ima ges, wi thout the nee d to compare the im ages to the scan ned materials. 6. Audio Watermarking Digital audio wa termark ing i nvolves the concealment of data within a discr ete audio f ile. Applications f or thi s tec hnolog y are numer ous. Intellectual propert y pr otection is curr ently the mai n driving f o rce be hind research in t his area. To combat online music pirac y, a digital watermar k could be adde d to all rec ording prior to r elease, signif y in g not only the au thor of t he wor k, b ut the user who has purchased a le gitimate cop y . Ne wer operating s ystems equipped w ith digital ri ghts manageme nt soft ware ( DRM) will extract the watermar k fr om a udi o file s pr ior to pla ying them on the s ystem. The DRM softwa re wil l en sure t hat the user has pai d for the song by comp aring the watermar k t o the e xisting purchase d licenses on the system. • DC W atermarkin g Scheme This secti on details the im plementati on of a digital audio waterm arking sche me, whic h can be used t o hide auxiliar y information within a s ound file. Figure 17: T ypes of Water marking Techniques The DC water marking sc heme hides waterm ark data i n l ower f requency components of t he au dio signal, which are bel ow t he pe rceptual t hreshold of the human a uditor y system. Watermark Insert ion The process of insert ing a digita l watermar k int o an audio f ile can be divided int o f our main processes (see Figure 8). A original aud io file i n wave f o r mat is fe d i nto t he s y ste m, where it is su bsequentl y framed, anal y z ed, and processed, to attach the inaudible watermar k t o the output signal. Framing The audio file is portione d into fr ames which ar e 90 millisec onds in duration. With a 90 ms frame size, our bit rate for watermarked data i s equal t o 1 / 0.09 = 1 1.1 bits per sec ond. Spectral Analysis Next, spectr al anal y s is is perf ormed on the si gnal, consisting of a fast Fourier transform ( FFT), which allows us t o c alculate the l ow fre quency comp onents of each f rame, as well as the overall fra me power. From the FFT, we a re now able to determ ine t he low frequenc y ( DC) c omponent of the frame as well as t he frame spectral power. Figure 18. Watermark I nsertion Process. DC Removal From t he a bove s pectral analysis of eac h fra me, w e have calc ulated t he low fr equenc y (DC) compone nt F(1), which can now be r emoved b y s ubtraction from each fra me . Watermark S ignal Additi on From the s pectr al anal ysis com pleted pre viously, w e calculated the spectr al p ower for eac h fr ame, which i s now utilised f or embe dding t he watermar k s ignal da ta. The power in each frame determines the am plitude of the water mark whic h c an be added t o the l ow frequenc y s pectrum. Wate rmark Extr action The process of e xtractin g the digita l watermark fr om the au dio file is si milar t o t he technique for i nserting the watermark. The com puter processing require ments for e xtraction are slightl y lower . A mar ked a udio file in wave format i s fed into the s y ste m, where it is subsequentl y fra med, anal ysed, a nd pr o ce ssed, to remove t he e mbedde d data which exists as a d igital watermar k. Framing As with the i nsertion pr ocess, the audi o file is partitioned int o frames which are 90 milli seconds in duration. Figure 19: Watermar k Extracti on Process Spectral Analysis Subsequent to the fr aming of t he water marked audio signal, we perf orm spec tral anal ysis on the si gnal, consisting of a fast Fourier transform ( FFT), which ISTE-STTP on Network Security & Cryptography , LBSCE 2004 again allows us to calculat e the l ow fr equenc y compone nts of ea ch frame, as well as the overall frame pow er. Watermar k Signal Extraction From the spectral anal y si s completed previousl y, we calcul ated the spectral power f or each fr ame, which all ows us to e xamine the low fre quenc y power in e ach fr ame and subsequentl y extra ct the watermar k. In order to attain higher hidden data den sity i n the watermar ked signal, m ore advanced t echnique s must be use d such as spread spectr um, phase encodi ng, or echo hidi ng. 7. Conclusions In t his t utorial, we take a n intr oductory l ook a t information hi ding t echnique s. Historical detail is discussed. Se veral meth ods for hi ding data in t ext, image, and a udio are described, with appr opriate introducti ons to the envir onment of each mediu m, as well as the strengths and w ea knesses o f each meth od. Most data hi ding systems take advantage of huma n p ercept ual we aknesses, but have weaknesse s of their own. In areas where cr y pto graph y a nd strong e ncr yption a re being outlawed, c itizens are lookin g a t ste ganograp hy t o circumvent suc h policies and pa ss messa ges covertl y. Commercial applications of steganogra phy in the form of digital wa termarks are currentl y being used t o tr ack the c opy r ight a nd ownershi p of electronic m e dia. We conclude that for now, it seems tha t no s ystem of data hiding is totally immune a ttac k . However, ste ganograph y has i ts plac e in securit y. It in no wa y c an replace cr y pto graph y , but is inten ded to supple ment it. Its applicati on i n water marking f or use in detecti on of unauthori sed, illegall y copied materi al i s continuall y being realise d and de veloped. References [1] Petitcolas, F.A.P., Anderson, R., Kuhn, M. G., "Infor mat ion Hiding - A Survey" , July1999, URL: http://www.cl.cam.ac.uk/~f app2/publications/ieee99- infohiding.pdf (11/26/0117:0 0) [2] An archive of steganography an d steganalysis tools: URL: http://members.tripod.com/stega nography/stego/software.h tml (11/26/01 17:00) [3] Katzenbeis s er, S., Petitcolas, F.A.P., Information Hiding Techniques for Steganography and Digital Watermarkin g, Norwood: Artech House, 2000, pg 56 - 92 [4] Johnson, N.F., Jajodia, S., " Steganalysis of images created using c urrent steganogra phic tool s ", A pril 19 98, U RL: http://www.ise.gmu.edu/~njoh nson/ihws98/jjgmu.html (11/26/01 17:00) [5] Pro vos, N ., Honeyman, P., " Detecting Ste ganographic Content on the Internet" , August 2001, http://www.citi.umich.edu/tec hreports/reports/citi_tr_01- 11.pdf (11/26/01 17:00) [6] McCullagh, D., " Secret Messages Come in .Wavs" , Feb 20, 2001, Wired News, URL: http://www.wired.com/news/politic s/0,1283,41861,00.html (11/26/01 17:00) [7] Artz , D., " Digital Steganography: Hiding Data within Data " , IEEE Internet Computin g, May- June 2001, pg 75-80 [8] B eyda, W.J., Da ta Communications From Ba sics to Broadband 3 rd editio n, Upper Sa ddle [9] R iver: Prentice Hall, 2000, pg 38 - 40 [10] Kelley, J ., "Terrorist instructions hidden online", USA TODA Y, 06/19/2001,URL: http://www.usatoday.com/life/cy ber/tech/2001-02-05-binladen- side.htm (11/26/01 17:00) [11] J ohnson, N.F., Jajodia, S., " Exploring Steganography: Seei ng the Unseen " , February 1998, URL: http://www.jjtc.com/pub/r2026.pdf ( 11/26/01 17:00) [12] J ohnson, N.F., Jajodia, S., " Stegan aly s is: The Investigation of Hidden Information", IEEE Information Technology Conferenc e, September 1998, [13] URL: http://www.jjtc.com/pub/it98a.htm (11/26/01 17:0 0) [14] Kelley, J., "T error groups hide b ehind Web encryption", USA TODA Y, 06/19/2001, [15] URL: http://www.usatoday.com/life/cyber/tech/2001-02-05- binladen.htm (11/26/01 17:00) [16] McCullagh, D., " Bin Laden: Steganography Master?", Wire d New s, 07 Feb 2001, [17] URL: http://www.wired.com/news/politic s/0,1283,41658,00.html (11/26/01 17:00) [18] Schneier, B., Cry pto-Gram Newslette r, October 15 1998, [19] URL: h ttp://www.counterpane.com/cry p to- gram-9810.html (11/26/01 17:00) [20] B .Tao and B .Dic kinso n, “Adap tive Wa te rm a rking in DCT Domain”, Proc. IEEE International Conference on Acoustics, Speech and Signal Processing, ICASSP- 97, 1997, Vol.4, pp.1985-2988. [21] R . G . V an Sc hyndel, “A Digita l Wat ermark”, Proc. IEEE International Conference on Image Processing, ICIP-94, 1994, Vol.2, pp.86-90. [22] Saraju P. Mohanty, “Watermarking of Digital Images”, A Master Degree’s Project Report, Dept. of EE, Indi an Institute of Science, Bangalore - 560 012, I ndia, Jan. 1999. Courtes y: WWW
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment