On the Capacity and Design of Limited Feedback Multiuser MIMO Uplinks
The theory of multiple-input multiple-output (MIMO) technology has been well-developed to increase fading channel capacity over single-input single-output (SISO) systems. This capacity gain can often be leveraged by utilizing channel state informatio…
Authors: Il Han Kim, David J. Love
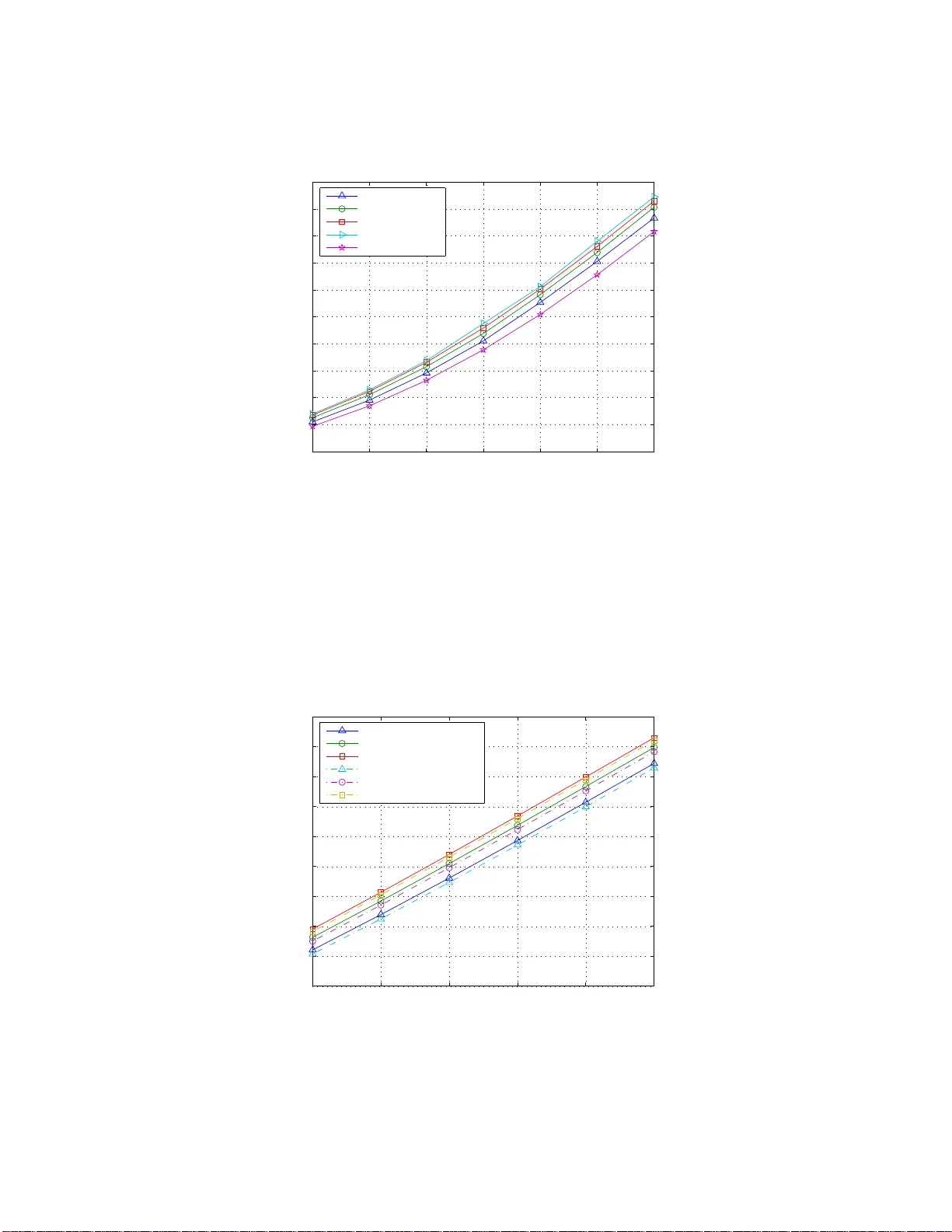
On the Capacit y and Design of Limited F eedbac k Multiuser MIMO Uplinks ∗ Il Han Kim and Da vid J. Lo v e Sc ho ol of Electrical and Computer Engineering Purdue Univ ersit y EE Building 465 North w estern Ave. W est Lafay ette, IN 47907 (Ph) 765-496 -6797 (F ax) 765- 494-0880 kim385@ecn.purdue.edu, djlov e @ecn.purdue.edu August 24, 2021 Abstract The theory of multiple-input multiple -outp ut (MIMO) tec hnology has b een w ell-deve lop ed to increase fading channel capacit y o ver single-input single-output (SISO) systems. This capacit y gain can often b e leveraged by utilizing channel state information at the transmitter and the receiver. Users make use of this channel state information for transmit signal adaptation. In this corresponden ce, we deriv e the capacity region for the MIMO multiple access channel (MIMO MAC) when partial channel state information is a v ailable at the transmitters, where we assume a synchronous MIMO multiuser up link. The p artial channel state information feedback has a cardinalit y constraint and is fed back from th e basestation to t he users using a limited rate feedbac k c hannel. Using this feedbac k informatio n, w e prop ose a fin ite cod ebo ok design metho d t o maximize sum- rate. In this corresponden ce, the cod ebo ok is a set of transmit signal cov aria nce matrices. W e als o derive the capacit y region and co deb ook design metho ds in the case th at t he cov ari ance matrix is rank- one ( i.e. , b eamforming). This is motiv ated b y the fact that beamforming is optimal in certain conditions. The simulation results show that when the number of feedback bits increases, the capacit y also increases. Even with a small num b er of feedback bits, the performance of th e prop osed system is close to an optimal solution with the full feedback. Index T erms -Limited feedback, MAC systems, MIMO systems, CSI at receiver (CSIR), CSI at transmitter (CSIT), Rayleig h channels, Grassmannian subsp ace packing ∗ This wo rk was supported in part by the NSF under grant CCF0513916, the Korea Research F oundation Grant funded by the K or ea go vernmen t (MOEHRD) (KRF-2005-215-D00207), and the SBC F oundation 1 In tro duction Multiple access systems a re being widely studied to effectively support multiple users at the basestatio n d uring uplink transmission. In m ultiple-input m ultiple-output m ultiple access channels (MIMO MACs), it is known that the channel state information at the tra nsmitters (CSIT) helps increase system p erforma nce (e.g., s um- r ate c a pacit y) regardless o f whether it is p erfect or par tial [1–5]. CSIT can b e full channel information [1–3], channel co v ariance information [4, 5], channel mean informa tion [4 , 5], etc. Esp ecially in frequency division duplexing (FDD) systems, because channel state infor ma tion (CSI) is not recipro cal b et ween uplink channel and downlink channel, this information should b e fed back fr o m the receiver to the tr a nsmitters. In real co mm unication systems, how ever, the feedback resour ces allotted for CSI feedback must b e a small p ortion o f the data b eing tr a nsmitted on the downlink b ecause feedback bits are overhead tha t ca uses p e r formance deg radation. In this cor resp ondence, w e fo cus on limited feedbac k sc hemes, where the receiver is assumed to hav e p erfect knowledge of the CSI and the receiver tr a nsmits a limited n umber of feedback bits to the transmitter accor ding to the CSI. It is o f our in terest to optimize signa l cov ariance matrices of each user using a limited num b er of feedback bits. The basestation and users are a ssumed to hav e knowledge o f a co deb oo k of cov ariance ma tr ices des ig ned offline. The limited num b er of feedback bits allows each use r to identify the cov ariance matrix chosen by the ba sestation fo r them to use during trans mis s ion. The main co n tributions of this cor resp ondence are given b elow: 1) In MIMO systems, we prov e the co ding theore m for MACs when a limited num b er of feedback bits is av ailable at the tra nsmitters. Based on the proved co ding theo rem, w e give a metho d to des ign a co debo ok (set of cov a r iance matrices) for ea c h user under a finite feedback ca rdinality co nstraint to maximize the sum-r ate ca pacit y . Assuming B bits of feedbac k, the ba sestation sele cts one co deword that maximizes the sum-rate a mo ng 2 B elements in a co ode b o ok. This co deb o ok is assumed to b e known to b oth the ba s estation a nd the users. The index cor resp onding to the chosen co deb o ok matrix is fed back to the users. 2) In single user MIMO scenarios, b eamforming is optimal under cer ta in conditio ns [6–10] when feedback is channel mean or channel cov a riance information. In multiuser scena rios, b eamforming is ge ner ally not universally optimal, i.e. , the full capacity ra te regio n c a nnot b e achiev ed. How ever, if so me criteria are satisfied, the sum-r ate is asymptotically a c hieved by be amforming. Studied in [11], the optimality of b eamforming was derived when channel feedback is perfect. In [4, 5], the optimality of b eamforming was prov ed when feedbac k is c hannel cov aria nce or channel mean information. Motiv ated by these w or ks, we co nstrain the ra nk of each user’s cov ariance matrix to one, i.e. , each user p erforms b eamforming on his/her own arr ay . W e derive the ca pacit y reg ion of the b eamforming 1 system a nd prop ose tw o metho ds to de s ign the b eamforming vectors: eigenbeamforming with a co debo ok designed using Lloyd’s a lgorithm and Gras smannian subspace packing with r andom p ow er allo cation of ea c h use r . 2 System Ov erview In this section, we introduce the system mo del under cons ideration. A t ypical MIMO MA C commun icatio n system is presented in Fig. 1. Let M t be the num ber o f transmit antennas a t each use r a nd M r be the num ber o f receive antennas. In this setup, the rec e ived signal is given by y y y n = K X k =1 H H H ( k ) n x x x ( k ) n + z z z n = h H H H (1) n H H H (2) n · · · H H H ( K ) n i x x x (1) n x x x (2) n . . . x x x ( K ) n + z z z n ≡ H H H n x x x n + z z z n , n = 1 , . . . , N , (1) where K is the nu mber of us ers and x x x ( k ) n ∈ X M t is the transmitted sig nal fro m the k -th use r with X denoting the transmit symbol alphab et. Her e, n is the time index a nd N is the blo ck leng th of each co de x x x N 1 = { x x x 1 , . . . , x x x N } . H H H ( k ) n is the M r × M t channel matr ix from the k -th us e r to the basestation. z z z n is the co mplex Gaussian noise with zero mean and cov a r iance σ 2 I I I . Here we assume that data symbols o f e a c h user are indep endent of each other, i.e. , E h x ( k ) n x ( l ) n ∗ i = O M t × M t , ∀ k 6 = l , where O M t × M t is M t × M t all zero matrix . W e a ssume a Rayleigh flat fading environmen t, where the channel indep endently changes from tra ns mission to transmis s ion. W e a lso a ssume that the channel state information U n ∈ U a nd V n ∈ V are av ailable at the tra nsmitters and the receiver, res p ectively , where U is the space of CSIT a nd V is the space o f channel state informa tion at the r e c eiv er (CSIR). CSIT U n is fed back to the transmitters based on the c ur rent CSIR V n . W e assume that the channel c o efficients a re estimated p erfectly at the receiver. Since the channel fading is assumed to b e indep e nden t for each n , the transmitted symbol is a function of the feedback CSIT U n . W e assume noiseless feedba c k, i.e. , the users know U n per fectly . Message W ( k ) for user k , k = 1 , . . . , K , is encoded to x ( k ) n for n = 1 , . . . , N depending on the feedbac k U n . These enco ded signals ar e sent through the c hannel with channel transition probability p y y y N 1 | x x x N 1 , H H H N 1 , wher e H H H N 1 = { H H H 1 , . . . , H H H N } and y y y N 1 = { y y y 1 , . . . , y y y N } . Aft er receiving y N 1 , the receiver deco des y N 1 to ( ˆ W (1) , . . . , ˆ W ( K ) ). Assuming the discr ete memoryless channel mo del, the sys tem is character iz e d by the following channel tra ns ition probability p y y y N 1 | x x x N 1 , H H H N 1 = N Y n =1 p ( y y y n | x x x n , H H H n ) . (2) This is illustr ated in Fig. 2. 2 3 Capacit y Results In this section, we give capacity results when complete CSIR and pa r tial CSIT are av ailable at the re c e iv er and the transmitters, r espectively . Partial CSIT is assumed to consist o f feedba c k information from the bas e station to the users. The system mo del o f Fig . 2 ca n be trans fo rmed into a n equiv alent system without C SIR and CSIT [12–16] by seeing U n as a channel state and V n as a channel output. Similarly , in this multiple access system, we first enco de each W ( k ) int o the matrix T ( k ) n ∈ X M t ×|U | , n = 1 , . . . , N , and select one column of T ( k ) n according to the current feedback U n ∈ U s uch that x ( k ) n = T ( k ) n ( U n ). With the proba bilit y distribution function p ( H H H n , u n , v n ), the equiv a len t channel is characterized by the channel tr ansition probability [15] p ( y y y n , v n | T T T n ) = X u n , H H H n p ( H H H n , u n , v n ) p ( y y y n | T T T n ( U n ) , H H H n ) , (3) where T T T n = T T T (1) n T · · · T T T ( K ) n T T . Fig. 3 pres en ts this eq uiv alent system mo del. W e a s sume that the CSIR includes bo th the CSIT c o mponent and the channel co efficient matrix, and the receiver feeds ba c k the U n comp onen t of the CSIR to the transmitters . This means that the receive channel state informatio n is given by V n = ( H n , U n ) [1 6]. W e a ssume the finite rate feedback satisfies |U | = 2 B with U = { u (1) , . . . , u (2 B ) } . T o derive the m ultiple acces s capacity region, let S = { k 1 , . . . , k |S | } ⊆ { 1 , . . . , K } b e a user subset. E ac h user cov ariance matrix is giv en b y Q Q Q ( k ) ( U n ) = E h x ( k ) n x ( k ) n ∗ U n i for n = 1 , . . . , N , k = 1 , . . . , K , w ith the pow er constraint T r Q Q Q ( k ) ( U ) ≤ P k for ∀ U ∈ U . This means that w e do not allow the av erag e sum transmit pow er conditioned on so me feedback information to exceed P k for any feedback pos sibilit y . In this setup, the capa cit y region is g iv en by the following theore m. Theorem 1 F or a fixe d mapping fr om U to n Q Q Q ( k ) ( U ) o K k =1 such that T r Q Q Q ( k ) ( U ) ≤ P k for k = 1 , . . . , K , t he c ap acity r e gion is the K -dimensio nal p olyhe dr on ( R R R : X k ∈S R ( k ) ≤ E V " log 2 det I I I + σ − 2 X k ∈S H ( k ) Q Q Q ( k ) ( U ) H ( k ) ∗ !# , ∀S ⊆ { 1 , . . . , K } ) , (4) wher e R R R = R (1) · · · R ( K ) T is the ra te ve ctor. Add itional ly, fo r individ ual p ower c onstr aints T r Q Q Q ( k ) ( U ) ≤ P k for k = 1 , . . . , K , the c ap acity r e gion is given by C M AC ( P 1 , . . . , P K ) = C l [ { Q Q Q ( k ) ( U ) } K k =1 , T r ( Q Q Q ( k ) ( U ) ) ≤ P k ( R R R : X k ∈S R ( k ) ≤ E V " log 2 det I I I + σ − 2 X k ∈S H ( k ) Q Q Q ( k ) ( U ) H ( k ) ∗ !# , ∀S ⊆ { 1 , . . . , K } ) ! , (5) wher e C l denotes the c onvex closur e op er ation. 3 W e pr o ve this theor e m in the App endix A. Fig. 4 shows an exa mple for the capacity regions of t wo use r systems corr espo nding to U 2 = u (1) , u (2) and U 4 = u (1) , u (2) , u (3) , u (4) for fixed p o wer allo cation P 1 and P 2 . The capa cit y regio n is a union of capacity pentagons for fixe d cov ar iance matric es that are g iv en by (4). Remark [17–19] With a sum p ow er cons tr ain t P K k =1 P k ≤ P , the ca pacit y re g ion is given by C union ( P ) = C l [ P K k =1 P k ≤ P C M AC ( P 1 , . . . , P K ) . (6) using the duality be tw een the MIMO MAC and MIMO BC (br oadcasting channel). 4 Co deb o ok Design Pro cedure Under a Sum P o w er Constrain t In this s ection, w e give a method to design a co deb o ok in a finite rate feedba c k e n vironment to maximize the s um-rate. The sum-rate ca n b e re pr esen ted as K X k =1 R ( k ) ≤ E V " log 2 det I I I + σ − 2 K X k =1 H ( k ) Q Q Q ( k ) ( U ) H ( k ) ∗ !# ≤ E V " max Q Q Q (1) ( U ) ,...,Q Q Q ( K ) ( U ) log 2 det I I I + σ − 2 K X k =1 H ( k ) Q Q Q ( k ) ( U ) H ( k ) ∗ !# = 2 B X q =1 max H q , T r ( Q Q Q q ) ≤ P E " log 2 det I I I + σ − 2 K X k =1 H ( k ) Q Q Q ( k ) q H ( k ) ∗ ! H ∈ H q # P q , (7) where H = H (1) · · · H ( K ) , P q = P ( H ∈ H q ), and H = {H 1 , . . . , H 2 B } is the pa rtition o n the c hannel matrix spa ce H . W e let Q Q Q ( k ) q = Q Q Q ( k ) ( u ( q ) ) and Q Q Q q = diag Q Q Q (1) q , . . . , Q Q Q ( K ) q to simplify the notatio n, whe r e u ( q ) is a r ealization o f U a nd diag ( · , . . . , · ) is a blo ck diago na l o pera tor. In this setup, the basestation can simply feed back the cov aria nce index q ∈ { 1 , 2 , . . . , 2 B } to notify which cov aria nce matrix Q Q Q q should b e used to maximize the achiev able sum-rate. This means that we ca n convey this CSIT using a finite rate feedback channel that sends the sa me B bits o f feedba ck to all us ers. W e a pply Lloyd’s a lgorithm [20 ] to solve the maximiza tio n pro blem. 1 Because the detailed pr o cedur e of Lloyd’s algorithm is similar to [2 0], we only emphas ize the difference. In the pr oce s s of des igning the co deb o ok using Lloyd’s algorithm, one of the steps is to so lv e the optimization problem e Q Q Q q = argmax Q Q Q q :T r ( Q Q Q q ) ≤ P E " log 2 det I I I + σ − 2 K X k =1 H ( k ) Q Q Q ( k ) q H ( k ) ∗ ! H ∈ H q # △ = argmax Q Q Q q :T r ( Q Q Q q ) ≤ P f ( Q Q Q q ) (8) 1 As described in [20], Lloyd’s algorithm conv erges to local optimum. As in [20], to obtain a p oint close to the globall y optimal p oint, we run the s ame algori thm sev eral times with differ ent initial test channels and initial co debo oks. Among the lo cal optimum poi nts, we c ho ose the b est p oin t that gives the b est capacit y v al ue. 4 for a fixed partition H = {H 1 , . . . , H 2 B } . W e illustrate the approximate pr o cedur e of so lving this optimization problem. By the heuristic appr oximation of [20 ], f ( Q Q Q q ) = E log 2 det I I I + σ − 2 H Q Q Q q H ∗ H ∈ H q P q (9) ≈ log 2 det I I I + σ − 2 E H ∗ H H ∈ H q Q Q Q q P q (10) = log 2 det I I I + σ − 2 R R R q Q Q Q q P q (11) = log 2 det I I I + σ − 2 S S S q Q Q Q q S S S ∗ q P q . (12) Here R R R q = E [ H ∗ H | H ∈ H q ] = S S S ∗ q S S S q with S S S q = h S S S (1) q · · · S S S ( K ) q i , wher e S S S ( k ) q ∈ C M t K × M t . Thus, the optimization problem b ecomes e Q Q Q q = argmax Q Q Q q :T r ( Q Q Q q ) ≤ P log 2 det I I I + σ − 2 K X k =1 S S S ( k ) q Q Q Q ( k ) q S S S ( k ) q ∗ ! P q . (13) Therefore, the sum p ow er iter ativ e waterfilling algorithm [2] can b e a pplied to this kind of optimization problem by treating the lo cally av eraged S S S (1) q , . . . , S S S ( K ) q as the channel matrices. So lving for q = 1 , . . . , 2 B , we can obtain the co debo ok Q = n e Q Q Q 1 , . . . , e Q Q Q 2 B o . Note that (13) is an a pproximation of the optimal solutio n of the original problem. Remark In a typical MAC s ystem, a sub optimal solution can b e found using individual p ow er constraints. Indee d, the sum-ra te maximizatio n proble m under indiv idual pow er constra in ts is a sp ecial case of the sum-rate maximization problem under the sum p ower constraint. W e can a lso apply Lloyd’s algor ithm to design a co debo ok under indiv idua l power co nstraints. An intermediate step in applying Lloyd’s algor ithm is to s o lv e the optimizatio n problem e Q Q Q (1) q , . . . , e Q Q Q ( K ) q = argmax n Q Q Q ( k ) q o K k =1 :T r “ Q Q Q ( k ) q ” ≤ P k E " log 2 det I I I + σ − 2 K X k =1 H ( k ) Q Q Q ( k ) q H ( k ) ∗ ! H ∈ H q # . (14) The same pr oce dure as the sum p ow er cons tr ain t c a se gives e Q Q Q (1) q , . . . , e Q Q Q ( K ) q = argmax n Q Q Q ( k ) q o K k =1 :T r “ Q Q Q ( k ) q ” ≤ P k log 2 det I I I + σ − 2 K X k =1 S S S ( k ) q Q Q Q ( k ) q S S S ( k ) q ∗ ! P q , (15) and this pro blem can b e s olved b y the individual p ower iterative waterfilling algor ithm [1] with the effective channels S S S (1) q , . . . , S S S ( K ) q . 5 Limited F eedbac k MAC Beamforming In this section, we c onsider b eamforming transmission for each user. W e obtain the ca pa cit y reg ion and deriv e co debo ok design metho ds fo r the limited feedback environment. 5 5.1 Capacit y Analysis In the b eamforming tra ns mission, the received signal is given b y y y y n = K X k =1 H H H ( k ) n w w w ( k ) n x ( k ) n + z z z n = h H H H (1) n H H H (2) n . . . H H H ( K ) n i w w w (1) n x (1) n w w w (2) n x (2) n . . . w w w ( K ) n x ( K ) n + z z z n , n = 1 , . . . , N , (16) where w w w ( k ) n ∈ C M t is the b eamforming vector of the k -th users. W e assume that E x ( k ) n 2 = 1, which means that the tr ansmission p ow er of the system is given by P K k =1 w w w ( k ) n 2 . In the limited feedback system with B bits of feedback, the co deb o ok is g iven by W = { w w w 1 , . . . , w w w 2 B } , where w w w q = w w w (1) q T . . . w w w ( K ) q T T . Based o n the curr en t feedback u ( q ) , the b eamforming vector is selected by w w w ( u ( q ) ) = w w w q for s ome 1 ≤ q ≤ 2 B . The capacity regio n in the limited feedback sys tem is given in the following corolla ry . Corollary 1 F or sum p ower c onstr aint P K k =1 P k ≤ P with w w w ( k ) ( u ( q ) ) 2 ≤ P k for k = 1 , . . . , K , the c ap acity r e gion subje ct t o a b e amforming c onstr aint is C beamf or ming union ( P ) = C l [ P K k =1 P k ≤ P C l [ { w w w ( k ) ( u ( q ) ) } K, 2 B k =1 ,q =1 , k w w w ( k ) ( u ( q ) ) k 2 ≤ P k ( R R R : X k ∈S R ( k ) ≤ E V " log 2 det I I I + σ − 2 X k ∈S H ( k ) w w w ( k ) ( U ) w w w ( k ) ( U ) ∗ H ( k ) ∗ !# , ∀S ⊆ { 1 , . . . , K } ) . (17) The pro of immediately follows from Theorem 1. 5.2 Eigenbeamforming with Lloyd ’s Algorithm In this section, we der iv e the b eamforming co deb oo k desig n metho d using eigenbea mfor ming with Lloyd’s algo rithm. As in Section 4, the sum-ra te can be r epresented a s K X k =1 R ( k ) ≤ 2 B X q =1 max H q , k w w w q k 2 ≤ P E " log 2 det I I I + σ − 2 K X k =1 H ( k ) w w w ( k ) q w w w ( k ) q ∗ H ( k ) ∗ ! H ∈ H q # P q . (18) W e a lso let w w w ( k ) q = w w w ( k ) ( u ( q ) ) fo r the nota tio nal simplicity . W e can also a pply Lloyd’s a lgorithm to so lv e this kind of problem [20]. Similar to Section 4, in the pro cess of solving for the co debo ok using Lloyd’s a lgorithm, o ne of the steps is to so lve e w w w q = argmax w w w q : k w w w q k 2 ≤ P E " log 2 det I I I + σ − 2 K X k =1 H ( k ) w w w ( k ) q w w w ( k ) q ∗ H ( k ) ∗ ! H ∈ H q # P q △ = argmax w w w q : k w w w q k 2 ≤ P f ( w w w q ) . (19) 6 This is not a convex optimization pr oblem a nd is therefo r e difficult to so lv e. Th us we approximate this pr oblem by using a low er b ound and employing the heuristic appr oximation from [20]. First, we claim that log 2 det I I I + σ − 2 K X k =1 H ( k ) w w w ( k ) q w w w ( k ) q ∗ H ( k ) ∗ ! ≥ log 2 1 + σ − 2 K K X k =1 w w w ( k ) q ∗ H ( k ) ∗ H ( k ) w w w ( k ) q ! . (20) This follows fr o m the fact that log 2 det I I I + σ − 2 K X k =1 H ( k ) w w w ( k ) q w w w ( k ) q ∗ H ( k ) ∗ ! ≥ log 2 det I I I + σ − 2 H ( l ) w w w ( l ) q w w w ( l ) q ∗ H ( l ) ∗ = log 2 1 + σ − 2 w w w ( l ) q ∗ H ( l ) ∗ H ( l ) w w w ( l ) q for 1 ≤ l ≤ K b ecause log 2 det( · ) is monotonica lly increas ing in the semi-definite c o ne. Bec ause lo g 2 is monotonically increasing function, it is satisfied that det I I I + σ − 2 K X k =1 H ( k ) w w w ( k ) q w w w ( k ) q ∗ H ( k ) ∗ ! ≥ 1 + σ − 2 w w w ( l ) q ∗ H ( l ) ∗ H ( l ) w w w ( l ) q . (21) Adding (21) to b oth sides for 1 ≤ l ≤ K and dividing by K results in det I I I + σ − 2 K X k =1 H ( k ) w w w ( k ) q w w w ( k ) q ∗ H ( k ) ∗ ! ≥ 1 + σ − 2 K K X k =1 w w w ( k ) q ∗ H ( k ) ∗ H ( k ) w w w ( k ) q . (22) Then by the heuristic appr oximation of [20], f ( w w w q ) ≥ E " log 2 1 + σ − 2 K K X k =1 w w w ( k ) q ∗ H ( k ) ∗ H ( k ) w w w ( k ) q ! H ∈ H q # P q (23) ≈ log 2 1 + σ − 2 K K X k =1 w w w ( k ) q ∗ E h H ( k ) ∗ H ( k ) H ∈ H q i w w w ( k ) q ! P q (24) = log 2 1 + σ − 2 K K X k =1 w w w ( k ) q ∗ R R R ( k ) q w w w ( k ) q ! P q (25) ≡ g ( w w w q ) , where R R R ( k ) q = E h H ( k ) ∗ H ( k ) H ∈ H q i . Instead of maximizing f ( w w w q ), we utilize the low er bo und g ( w w w q ) b ecause it is eas ier to o btain an analytical solutio n. Let w w w ( k ) q = α ( k ) q v v v ( k ) q , w w w ( k ) q ∈ C M t , where α ( k ) q = w w w ( k ) q and v v v ( k ) q = 1. Then g ( w w w q ) = log 2 1 + σ − 2 K K X k =1 w w w ( k ) q ∗ R R R ( k ) q w w w ( k ) q ! = log 2 1 + σ − 2 K K X k =1 α ( k ) q 2 v v v ( k ) q ∗ R R R ( k ) q v v v ( k ) q ! . (26) W e c a n select v v v ( k ) q as the unit-no rm eigenv ector asso ciated with the maximum eigenv alue o f R R R ( k ) q . Then, g ( w w w q ) = lo g 2 1 + σ − 2 K K X k =1 α ( k ) q 2 λ ( k ) q 2 ! , (27) 7 where λ ( k ) q 2 is the maximum e ig en v alue of R R R ( k ) q . By the Sch wartz inequa lit y , g ( w w w q ) ≤ lo g 2 1 + σ − 2 K v u u t K X k =1 α ( k ) q 2 2 v u u t K X k =1 λ ( k ) q 2 2 . (28) Equality holds if a nd only if α ( k ) q 2 = a λ ( k ) q 2 (29) for s ome p ositive constant a . Since P K k =1 α ( k ) q 2 = P , a = P P K k =1 λ ( k ) q 2 . (30) Therefore α ( k ) q = √ P λ ( k ) q r P K k =1 λ ( k ) q 2 (31) and w w w ( k ) q = √ P λ ( k ) q r P K k =1 λ ( k ) q 2 v v v ( k ) q , (32) where λ ( k ) q 2 is the maximum e ig en v alue of R R R ( k ) q and v v v ( k ) q is the cor resp onding unit-norm eigenv ector. The pro posed metho d can a dditionally b e v alida ted by the pap ers [4 , 5, 9], which state that when the cov ar iance feedback is av a ilable at the tra nsmitters the optimum b eamforming vectors can be found as the eigenv ector asso ciated with the ma x im um eigenv alue of the cov aria nce channel matrix of each user. 5.3 Grassmannian Design In this section, we develop the Gra nssmannian co debo ok by solving the Gra ssmannian subspace packing problem [21] with r andom power a lloca tion. References [22–25] dea lt with a r andom b eamforming co deb oo k by emplo ying r andom vector quantization (R V Q) in single user s y stems. This is based on the idea that the right s ingular vector of the channel whic h maximizes the capacity is random and isotropically distributed [2 4] under the assumption of an independent and iden tically distributed (i.i.d.) complex Gaussian channel matr ix. In the same se ns e, in the MAC bea mforming problem, each user ’s channel is i.i.d., a nd ther efore we can assume that the p ow er allo cation of each user is ra ndomly distributed acc o rding to s um power co nstraint. In this corre s pondence, the b eamforming direction of each user will b e genera ted in the Grass ma nnian sense [21 ]. The co debo ok design pro cedure will b e descr ibed in the fo llo wing. 8 5.3.1 Co deb o ok design Let W = { w w w 1 , . . . , w w w 2 B } b e the be amforming co debo ok, wher e w w w q = w w w (1) q T · · · w w w ( K ) q T T . Here the sum p ow er constraint is given b y k w w w q k 2 ≤ P for q = 1 , . . . , 2 B . Then the sum-r a te capacity is C beamf or ming sum = E H , W " max w w w q ∈W log 2 det I I I + σ − 2 K X k =1 H ( k ) w w w ( k ) q w w w ( k ) q ∗ H ( k ) ∗ !# = E H , W max w w w q ∈W log 2 det I I I + σ − 2 H W W W q W W W ∗ q H ∗ , (33) where W W W q = w w w (1) q 0 0 0 M t · · · 0 0 0 M t 0 0 0 M t w w w (2) q · · · 0 0 0 M t . . . . . . . . . . . . 0 0 0 M t 0 0 0 M t · · · w w w ( K ) q (34) is a bea mforming matrix obtained by augmenting with each us er’s b eamforming vector with the zero column vector of length M t , 0 0 0 M t . W e can see that (33) is the c a pacit y formula for the sing le user MIMO system with the cov ar iance matrix W W W q W W W ∗ q of the co nstraint that W W W q is blo ck diago nal when { W W W 1 , . . . , W W W 2 B } is a co deb o ok. Note that W W W q ∈ C M t K × K has or thogonal co lumns, but it is not unitar y b ecause W W W ∗ q W W W q 6 = αI I I , wher e α is some non-nega tiv e constant chosen a ccording to sum p ow er constra in t. In the unitary case of s ingle user MIMO sy stems, r eferences [22, 24] designed random c o deb o oks b y R V Q and r eference [21] designed Grass mannian co deb oo ks by Gras smannian subspac e packing with the F ubini-Study distanc e . Ho wev er, these co debo ok design metho ds ar e no t directly applicable to our problem b ecause our augmented b eamforming matrix is not unitar y . In this section, we will ass ume that w w w ( k ) q = α ( k ) q v v v ( k ) q , where α ( k ) q is the p ow er allo cation factor for the user k and v v v ( k ) q is the no rmalized unit-norm b eamforming vector for the user k . Here we assume tha t P K k =1 α ( k ) q 2 = P for sum power co nstraint P . The augmented b eamforming ma tr ix is given by W W W q = B B B q V V V q , (35) where B B B q = A A A q ⊗ I I I with A A A q = diag α (1) q , . . . , α ( K ) q and V V V q = v v v (1) q 0 0 0 M t · · · 0 0 0 M t 0 0 0 M t v v v (2) q · · · 0 0 0 M t . . . . . . . . . . . . 0 0 0 M t 0 0 0 M t · · · v v v ( K ) q . (36) 9 T o maximize the sum-rate, it suffices to max imize the average determinant C beamf or ming sum . = E H , W " max w w w q ∈W det I I I + σ − 2 K X k =1 H ( k ) w w w ( k ) q w w w ( k ) q ∗ H ( k ) ∗ !# = E H , W max w w w q ∈W det I I I + σ − 2 H B B B q V V V q V V V ∗ q B B B ∗ q H ∗ = E H , W max w w w q ∈W det I I I + σ − 2 H A V V V q V V V ∗ q H ∗ A , (37) where . = means the equiv alence o f the optimiza tion a nd H A = H B B B q . Th us, the c o deb o ok de s ign pro ble m can b e viewed as the unitary co deb o ok design of V △ = { V V V 1 , . . . , V V V 2 B } with the equiv a le nt channel H A [21]. This problem can be solved by Grass mannian subs pa ce packing using the F ubini-St udy distanc e . The F ubini-St udy distanc e is g iv en by [2 1] d F S ( V V V q , V V V r ) = arcco s | det( V V V ∗ q V V V r ) | = arccos K Y k =1 v v v ( k ) q ∗ v v v ( k ) r ! . (38) Let δ F S ( V ) = min 1 ≤ q
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment