Improved lower bound for deterministic broadcasting in radio networks
We consider the problem of deterministic broadcasting in radio networks when the nodes have limited knowledge about the topology of the network. We show that for every deterministic broadcasting protocol there exists a network, of radius 2, for which…
Authors: Carlos Brito, Shailesh Vaya
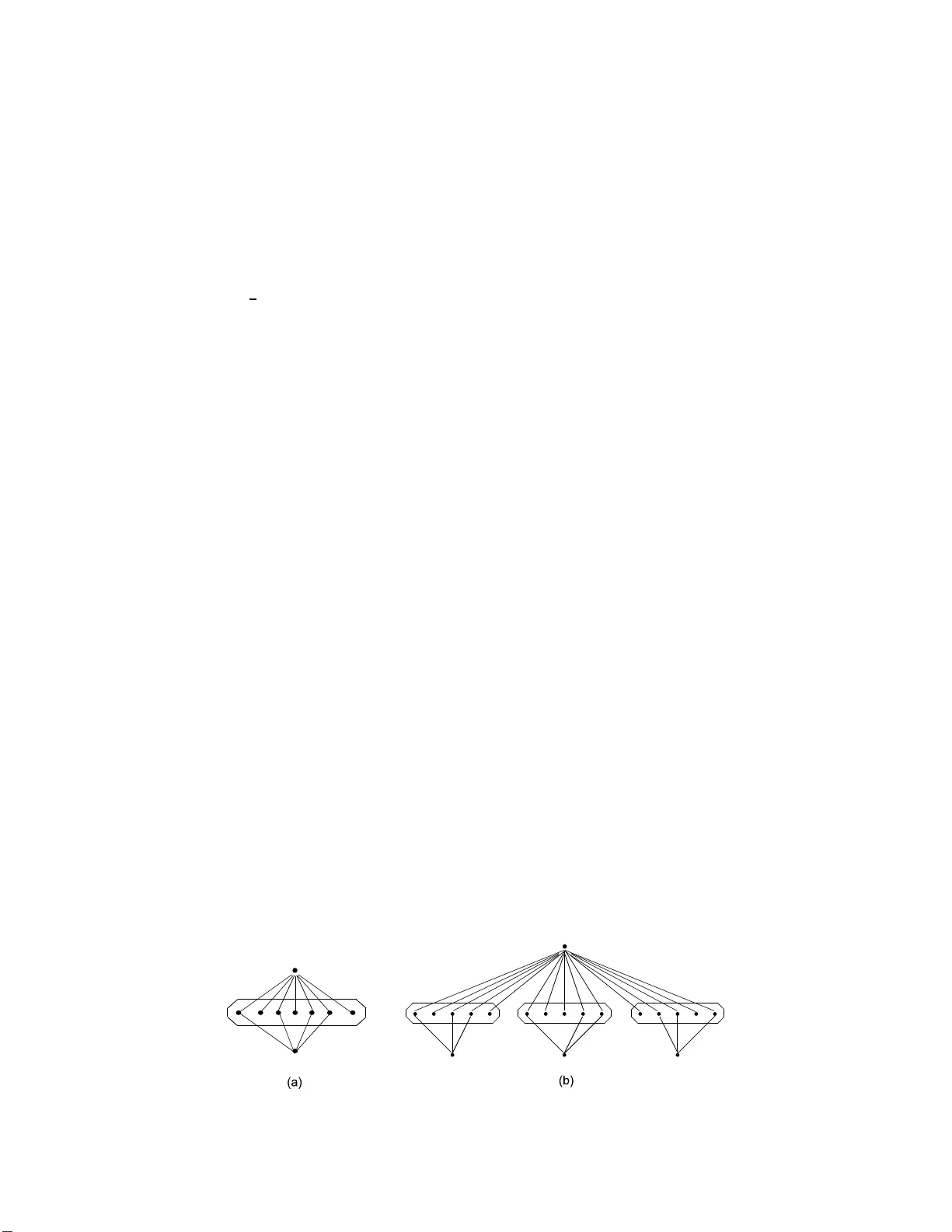
Impro v ed lo w er b ound for deterministic broadcasting in radio net w orks Carlos Fisch Brito ∗ Shailesh V a y a † No v emb er 11, 2018 Abstract W e consider the problem of deterministic broadcasting in radio net w ork s wh en the n odes ha ve limited knowledge ab out the top ology of the netw ork. W e sho w that for every determin- istic broadcasting proto col there exists a net w ork, of radius 2, for whic h the p rotocol tak es at least Ω( n 1 2 ) round s for completing the broadcast. Ou r argument can b e extend ed to pr o v e a lo wer b oun d of Ω (( nD ) 1 2 ) roun d s for broadcasting in radio net w orks o f radius D . This resolv es one of the open problems p osed in [29], where in the authors prov ed a lo wer b ound of Ω( n 1 4 ) roun ds for broadcasting in constan t diameter n et w orks . W e pr o v e the n ew lo w er b oun d f or a sp ecial family of radius 2 n et w orks . Eac h net work of this family co nsists of O ( √ n ) comp onen ts whic h are conn ect ed to eac h other via only the source no de. A t the heart of the pr o of is a nov el sim ulation argument, whic h essent ially s ays that an y arbitrarily complicated strategy of the source no de can b e sim ulated by th e n odes of the netw orks, if the sour ce no de just transmits partial topological knowledge ab out some comp onen t ins tea d of arbitrary complicated messages. T o the b est of our kno w ledge this t yp e of sim ulation argumen t is no v el and ma y b e useful in furth er impro ving the lo w er b ound or ma y find use in other applications. Keyw ords: radio n et w orks, d ete rministic broadcast, lo w er b oun d , advice string, simulatio n, selectiv e families, limited top ological knowle dge. ∗ Departamento de Computa¸ c˜ ao, Universidade F eder al do Cear´ a , F o rtaleza, Brazil. E-mail: carlos@lia.ufc.br. Research in this w ork was co nducted while the author w as a gr aduate studen t at UCLA. † Department o f Co mputer Science and Engineering, Indian Institute of T echnology Madras, Chennai, India - 60003 6. E-mail: v ay a@ c se.iitm.ernet.in. Resear c h in this work w a s conducted while the a uthor w a s a g raduate student at UCLA. 1 1 In tro ductio n One of the most fu ndamen tal and well stu died p roblems in d istributed computing is th e problem of br oadca sting. In broadcasting there is a sour c e no de whic h p ossesses a message that should b e sent to all the remaining no des of the net work. If the source no de is d ir ect ly connected to all the no des of the netw ork then the message can b e sen t to the rest of the no des in a single transmission. What mak es the p roblem of broadcasting non-trivial is that the source no de m a y not b e directly connected to the rest of the net wo rk and the top ology of the net work m a y b e arbitrary . Th e minim u m requiremen t on the top ology of a net work so that broadcasting can b e completed is that the n et w ork is connected. There are sev eral metrics to measure the complexit y of a broadcasting pr otocol, like roun d complexit y (min- im u m num b er of r ounds n eeded to complete broadcasting), message complexit y (minimum n um b er of messages n eeded to b e sen t to complete b roadcasti ng) etc ., which can b e defined in terms of the num b er of no des in the net work n , the radiu s of th e net w ork D , etc. The most imp ortan t and p rev ale n t complexit y measure under wh ic h the broadcasting problem has b een studied is the r ound c omplexity of the broadcasting p rotocol. This wo rk fo cuses on the round complexit y of d eterministic broadcasting proto cols in sp ecial kinds of netw orks called r adio networks . Ad-ho c radio ne tw orks. Broadcasting proto cols find many applications in A d-ho c wir e- less netw orks. Ad-ho c wireless n et w orks are used in s cenarios lik e battlefields, emergency dis- aster reliefs an d other situations where there is n o infrastructure for communicatio n net w orks . Sensor net works are also an examp le of w ireless radio net works. Unlike the traditional w ir e- less net works these netw orks d o not h av e a base station to wh ic h the no des can comm unicate. No des which are within the range of their radio signals comm unicate via radio transmissions, while n odes that are far off rely on other no des of the n et w ork to exc hange messages. Comm unication in these net works is stru ctur ed using sync hr onous time-slots. In ev ery round eac h no de either acts as a transmitter or as a receiv er. A radio net wo rk can b e mo deled as an undir e cte d connected graph as follo ws: Eac h no de in the graph repr esen ts a pro cessor, and t w o n odes are connected by an edge if the corresp onding pro cessors lie within the transmission r ange of eac h other. A message tr ansmitted by a no de can p oten tially reac h all its neigh b ors . Ho w ev er, if more than one neigh b oring n ode send a message in the s ame round, then a collision o ccurs. This is the mo del that w as prop osed in the seminal pap er on radio net works [3], and has b een generally considered in the literature [29 ]. In [34], the authors adopt a more p essimistic mo del for radio transmission, according to wh ic h when tw o or more neigh b orin g no des transmit a message in the same round, the receiving no de receiv es the message fr om one of th em and the messages from others are lost. The m odel considered in this w ork is th e one traditionally considered in the literature on radio broadcasting, i.e. as stated in [3 ], [29], [30]. 1.1 Related W ork The study of br oa dcasting in radio n et w ork s w as initiated by Bar-Y eh ud a, Goldreic h and Itai in [3]. In [29], Ko w alski and P elc establish a low er b ound of Ω ( n 1 / 4 ) r ounds for the deterministic broadcasting p roblem on radio net w orks of diameter 4 (and ( nD 3 ) 1 / 4 rounds for net works of d iamet er D ) in the mo del considered traditionally , i.e., whic h is the mo del stated in [3 ]. When the to p ology of the r adio n et w ork is kno wn to a ll the n od es of the net work, a deterministic broadcasting p rotocol of O ( D lg 2 2 n ) was give n in [11], for net works of r adius D . This cen tralized br oadca sting proto col h as recen tly b een imp ro v ed to O ( D lg 2 n + lg 2 2 n ) rounds b y [30]. A proto col r unning in O ( D + lg 5 2 n ) round s w as giv en in [21] and this has b een most recen tly impro ved to O ( D + lg 4 2 n ) in [20]. A low er b ound of Ω(lg 2 n ) rou n ds has b een pro v ed in [1], for the cen tralized setting. The setting wh ere the no des are giv en only their o wn lab els, but not the lab els of their neigh b orin g n od es has also b een studied quite extensiv ely . Researc h in this pr oblem has led to the introd uction of v ery in teresting com b inatorial concepts like sele ctive fam ilies . The use of selectiv e families in the d esign of d ete rministic p r otocols for u nkno wn netw orks was in tro duced b y Chlebus et. al. in [12]. Several recen t wo rks exploit this com bin ato rial tool, sp ecifically the use of p r obabilistic metho d, for obtaining goo d lo w er and u pp er b oun ds for the b roadcast ing pr oblem [16], [12], [14]. The problem of b roadcasti ng on d irecte d rad io n etw orks h as receiv ed muc h attent ion. The proto col give n by [12] requires O ( n 2 ) roun d s for completion. This upp er b ound was reduced to O ( n 3 2 ) round s by a b reakthrough result of [13]. In a further br eakt hrough, [14], the authors deplo y ed t he pr obabilistic metho d to b ring the upp er b ound fr om O ( n lg 2 2 n ) to within logarithmic factors of the b est known low er b oun d Ω( n lg 2 D ). In [29], a fu rther impro v ement has b een made for small diameter net w orks. They establish an upp er b oun d of O ( n lg 2 n lg 2 D ). In [9], the authors defin e and deploy new combinato rial stru ctures to reduce this gap b et ween lo wer and u pp er b ounds to O (lg 2 D ) f actor i.e., giv e a b roadcasti ng p r otocol runn in g in O ( n lg 2 2 D ) r ounds. Randomized proto cols f or the br oadca sting problem ha ve b een stu d ied in [3], [32], [27]. In these proto cols, the nod es do not kn o w the lab els of their n eigh b oring n odes and ma y in fact ha v e non-uniqu e lab els. In [3], a br oadcasting proto col run n ing in O ( D lg 2 n + lg 2 2 n ) rounds is give n. A low er b ou n d of Ω( D lg 2 ( N/D )) rounds w as prov ed f or this problem in [27 ]. The lo w er b ound of Ω (lg 2 2 n ) roun ds for b r oadca sting p rotocols also h olds for this prob lem. A broadcasting proto col running in O ( D lg 2 ( n/D ) + lg n 2 ), matching the lo wer b oun d, wa s prop osed in [32]. In the w ak e u p pr oblem, eac h no de in the net w ork either w ake s-up sp on taneously or is activ at ed by receiving a wa k e-up signal from another no de. Eac h activ e no de transmits the w ak e-up signal according to a giv en proto col. The r unning time of a w ak e-up proto col is the num b er of steps counted from t he fir st sp onta neous wak e-up, u n til all no des become activ at ed. T his p roblem has b een studied under differen t assumptions in [15], [8 ], [22], [25 ]. Async h ronous radio broadcasting has b een studied in [10]. In the n ext section, we shall present an outline of the pro of of the low er b ound. The rest of the p aper shall b e dev oted to form ali zing this outline. 2 Some early dev elop men ts and outline of the Pro of The s tu dy of br oa dcasting in radio net works was initiated b y Bar-Y ehuda, Goldreich an d Itai in [3], where they constructed a class of net w orks, referr ed to as simple BGI-net w orks (see Figure 1(a)), f or whic h they pr esented a low er b ou n d for deterministic broadcasting. In [29], Ko walski and Pelc observ ed that for simple BGI-net w ork s the role of the source n ode cannot b e ignored in ac hieving faster broadcast. They go on to d escrib e a deterministic proto col in whic h the source assists other no des in the n etw ork to co mplete broadcast on an y BGI-net work in O (lg 2 n ) r ounds. Figure 1: (a) BGI-net work and (b) C2 net w ork F or the result in [4], [5], w e in tro duced a more elab orate class of net w orks, (see Figure 1(b)) for which w e ask ed the questions: ”If the broadcast pr oto col run s for at most r rounds , how m u c h assistance can the source nod e pr ovide? Can this assista nce b e quan tified in terms of the n um b er of rou n ds, the topology of the net work and argued to b e insufficient to significan tly exp edite b roadcasting?” . The fir st attempt to formalize this id ea w as an in formatio n theoretic argument presented in [4 ]. Basically it is argued in [4] that even if the role of the source no de is sub stituted b y an advice string enco ding some partial knowle dge ab out the top ology of the un derlying net w ork in consideration, the assistance is found to b e insufficien t, in formation theoretically sp eaking, to complete broadcast in √ n roun ds on at least some of th e net works. Th is argumen t emplo ys a straigh tforw ard generalization of a lo wer b oun d on the size of selectiv e families, [16]. In this generalization w e found a tec hnical gap. The generaliza tion is p erhaps true for families of subsets with sp ecial p rop erties, but we b eliev e that form ulating an argument f or the lo wer b ound along the original lines wo uld mak e the pro of u n necessarily complicated. Along the same lines an oracle argumen t, [28], wa s also sk etc hed in [5]. This argumen t h as the conceptual problem to ameliorate which the original inf ormatio n theoretic argument was pr oposed in [4]. Namely , if an oracle provides the iden tities of the t w o n odes w ith least IDs which transmitted in a giv en round when a collision is d etec ted, then dep ending on the sp ecification of the proto col the information p ro vided by the oracle can also leak partial kno w ledge ab out the top olog y of the net w ork. F or example, it may b e the case that the pr otocol sp ecifies that some no des in la ye r L 1 , with IDs smaller than the ones rev ealed by the oracle also transmit in this round if connected to the appropriate n o de in la yer L 2 (see Figur e 2). Then, an interpretation of the oracle message is that these n odes are not connected to the corresp onding no des in L 2 in the give n netw ork. Th is kno wledge ab out the top ology of the net w ork ma y b e exploited in ac hieving faster br oadca st in future an d cann ot just b e ignored. In this work w e pr esen t a more d irect pro of of th e lo wer b oun d, along lines similar to the original in formatio n theoretic argument. The p roof consists of three main comp onen ts: In the first comp onen t it is shown thr ough a series of sim u latio n b ased reductions that, if an arbitrary deterministic b roadcast proto col π 0 completes br oadca st in r rounds on ev ery C 2 net work, then there must exist another deterministic b roadcast proto col in whic h the sour ce is giv en an advice string at the b eginning of the pr otocol π ′ whic h the source tr ansmits along with the broadcast message at the b eginning of the pr otocol an d remains silen t for the rest of the protocol. This advice string consists of r blo c ks of binary strings eac h of whic h enco des one of the follo w ing tw o t yp es of messages: φ (wh ic h denotes a collision or empt y m essag e), or a tuplet < i, C i > where C i denotes the configuration of the i th BGI-comp onen t in the net work. The proto col π ′ m u st complete broadcast in at most 3 ∗ r r ounds on every netw ork of the C 2 family . Th ese redu ctions are presented in Section 5. The essence of the second comp onen t is to u tiliz e meaningful connections b et w een the messages encoded in th e advice string and the to p ology of the co rresp onding underlying net work. F or this we consider the set of all th e unique advice s tr ings pro vided to the source no de for d ifferen t n et w orks from C 2 family . W e select one suc h advice string whic h m us t b e pro vided to the source no de for a large subset of C 2 net works. This subset of net wo rks has the prop ert y that all the d ifferen t p ossible configurations of at least one BGI-comp onen t are present in some n et w ork of the sub s et. These arguments are presented in Section 6. The ab o ve t w o comp onen ts are combined with a kno wn lo wer b ound on the size of selec tiv e families, or alternative ly a hitting game argument fr om [3], to complete the pro of of the lo wer b ound, Theorem 4.2. 2.1 Organization of the re st of the pap er The rest of the pap er is d ev oted to form aliz ing the ab o ve argument. S ect ion 3 describ es the mo del in detail and introdu ces notations and definitions used in th e text. Section 4 states some auxiliary results and prov es the main theorem. The statemen t of the redu ctio ns and their pro ofs are p resen ted in Section 5. Section 6 describ es the pr ocedur e PRU NE() that c ho oses an app r opriate advice string and a corresp onding subset of C 2 net works as menti oned ab o ve . 3 Descrip t ion of the mo del and general definitio ns Definition [3],[29]: A broadcast proto col π for a radio netw ork is a sync hronous multipro- cessor proto col which pro ceeds in r ounds as follo w s: 1. No des ha v e distinct lab els from the set { 0 , 1 , . . . , m } , wh er e m is a p olynomial on the n um b er of n odes in the netw ork. A distinguish ed no de with lab el 0 is called the sour c e no de. 2. All no des execute iden tical copies of the same proto col π . 3. In eac h round, every no de either acts as a trans mitter or as a receiv er (or is inactiv e). 4. A no de receiv es a message in a sp ecific r ound if and only if it acts as a r ece iv er and exactly one of its n eig h b ors transmits in that roun d. Otherwise, it receiv es φ . W e assume that the messages are authentica ted, that is, when a no de r ece iv es a message it kno w s the lab el of the transmitting no de. 5. The action of a n od e in a sp ecific roun d is d ete rmined by (a) Initial inpu t, whic h conta ins its o wn lab el an d th e lab els of its neigh b ors . (b) Messages receiv ed b y the no de in previous rounds . 6. In round 0, only the source no de transmits th e broadcast message. 7. Only no des that hav e receiv ed a message are allo w ed to transmit. That is, th e only sp ontane ous transmission is the one b y the source in round 0. 8. Broadcast is completed in r round s if all the no des receiv e the source message in one of the rounds 0 , 1 , . . . , r − 1. 3.1 C 2 net w orks Figure 2: C2 net w ork W e pro v e the low er b ound f or a family of n et w orks, called C 2 net works, with radiu s 2 and a simp le comm unication structure. Intuitiv ely , a C 2 net work is formed b y connecting a n um b er of BGI-net works via a common source n o de (see Figure 2). More p recisely , the no des of a C 2 net work are d ivided into three la ye rs: L 0 , L 1 and L 2 , where: • la yer L 0 consists only of the source no de; • la yer L 1 consists of √ n groups of √ n no des eac h, all of whic h are connected to the source no de. • la yer L 2 consists of √ n n odes, eac h one of whic h is asso ciated w ith a distinct group of no des in L 1 and connected to an arbitrary subset of no des of th e group. W e call eac h group of no des in L 1 together with the asso ciat ed no de in L 2 a BGI- comp onen t, or alternativ ely a comp onen t, of the netw ork. The lab els of th e no des in a net w ork are arbitrary b ut fixed for all the C 2 net works. Th us, w hat distin gu ish es t w o net works N and M of C 2 family is only the top ology of one or more BGI-co mp onen ts. Ob serving th at there exists 2 √ n distinct p ossible top ologi es for a BGI-comp onen t, we can giv e a complete description of a comp onent by a tuplet < i, τ > , where i is an ind ex for th e comp onent w h ic h is b eing describ ed and τ is an in teger in th e range [0 . . . 2 √ n − 1]. 3.2 Advice string υ ( π , N , t ) An advice string υ ( π , N , t ) is an arr a y of t ele men ts, eac h of whic h could p ote n tially enco de partial top ologic al information ab out the netw ork N . More p recisel y , eac h element consists of either φ or a tup let < i, τ i > whic h d escribes the top ology of a BGI-comp onen t of the net work N. The sp ecific con ten ts of the advice strin g υ ( π , N , t ) d ep end s on the first t r ounds of the execution of proto col π on netw ork N . 4 Main theor e m In this section we present the main theorem 4.2 which prov es the low er b oun d. Theorem 4.2 com bin es the three parts of the argument Lemm a 4.1 (simulati on based reductions), Lemma 4.2 (selection of an advice string and an appropriate sub set of netw orks) an d Theorem 4.1 (a w ell kn o wn lo wer b ound on the size of selectiv e families). Lemma 4.1 Assume that ther e exists a pr oto c ol π that c omp letes br o adc ast in at most r r ounds on ev ery network of the C 2 family. Then, ther e exists a deterministic br o adc ast pr oto c ol π ′ such tha t • the no des in layer L i tr ansmit only in r ounds t ≡ i (mo d 3), for i = 0 , 1 , 2 . • for e ach network N of the C 2 family ther e is an advic e string υ ( π 3 , N , r ) which is pr ovide d to the sour c e no de at the set up phase along with the br o adc ast message. • the sour c e tr ansmits the br o adc ast message and the string υ ( π 3 , N , 3 r ) in r ound 0 . • the sour c e r emains silent in ev ery r ound i > 0 . • the pr oto c ol π ′ c ompletes br o adc ast on network N i n at most 3 ∗ r r ounds Lemma 4.2 L et π ′ b e the pr oto c ol given by lemma 4.1, with r < √ n 2 . Then, ther e exists an advic e string υ and a subset of networks S ⊂ C 2 such tha t 1. Pr oto c ol π ′ c ompletes br o ad c ast in at most 3 ∗ r r ounds on every network of subset S , when the sour c e no de is pr ovide d with the advic e string υ in the set u p phase. 2. Ther e exists an index i such that, for e ach p ossible top olo g y of a BGI-c omp onent, ther e is a network N ∈ S whose i th c omp onent has e xactly this top olo gy. Definition 4.1 ([16 ]) L et [ n ] = { 1 , . . . , n } and let k ≤ n . A family F of subsets of [ n ] is a ( n, k ) -sele ctive if for every non empty subset Z of [ n ] such that | Z | ≤ k , ther e is a set F in F su ch that | Z T F | = 1 . Theorem 4.1 ([16]) L et F b e a ( n, k ) -sele ctive family, with n > 2 and 2 ≤ k ≤ n/ 64 . Then it holds that, |F | ≥ k 24 log 2 n k . Theorem 4.2 F or every deterministic pr oto c ol π that runs f or o ( √ n ) r ound s, ther e exists a C 2 network N such that π do es not c omplete br o adc ast when exe cu te d on N . Pro of: Assume, to the cont rary , that th er e exists a broadcast p rotocol π that completes broadcast in less than √ n/ 1536 rounds on ev ery C 2 net work. T hen by applying lemma 4.1 w e obtain a pr otocol π ′ . Let υ , S, i b e the advice string, subset of net w orks and index giv en b y Lemma 4.2 for proto col π ′ . The pro of is based on the f oll o win g observ ation. Supp ose that x is a no de in la yer L 1 and y is a n ode in la y er L 2 of the i th BGI-comp onen t of the net w ork. According to th e defi nition of a broadcast proto col, the b eha vior of no de x in a giv en round dep ends on its o wn lab el, wh ic h is fixed, the lab els of its neighbors and the sequ en ce of m essag es r eceiv ed in previous roun ds. The source is alwa ys a n eigh b or of x , b ut x ma y or ma y not b e connected to y . Ho w ev er, if x is n ot connected to y , then x cannot transmit the message to y an d complete broadcast on this BGI-comp onent , so we fo cus our atten tion on the situation w hen x is connected to y . No w, from lemma 4.2, w e get that the source transm its the same message in r ound 0 when p rotocol π ′ is executed on every net work of s ubset S , n amely the br oadca st message and advice string υ . A t th is p oin t, we wo uld lik e to conclude th at, wh en connected to y , the no de x has exactly the same b ehavio r in the exec utions of protocol π ′ on different netw orks of sub set S . Ho wev er, w e still hav e to consider the messages r ece iv ed by x fr om the no de y , whic h can b e transmitted in d ifferen t rounds on the differen t netw orks b elonging to subset S . But then, we recall that the only sp on taneous transmission is made by the source in round 0, and so if y makes a transmission the task of broadcast has already b een completed on this BGI-comp onen t. Thus, we ma y co nclude that, when connected to y , no de x has alw a ys the same b eha vior wh en π ′ executes on ev ery net work of S , up to the round in whic h broadcast is completed on comp onen t i . Next, w e present the pro of of the lo w er b ound formally . Consider the family F = { F 0 , F 1 , . . . , F r − 1 } of subsets of no des fr om the BGI-comp onen t i , defin ed as follo ws. A no de x b elongs to subset F j if and only if there exists a net work N ∈ S s uc h that 1. x is connected to y in the n et w ork N 2. x transmits in round 3 ∗ j + 1 wh en π ′ is executed on net w ork N 3. y do es n ot receiv e an y message up till round 3 ∗ j + 1 wh en π ′ is executed on N . No w, w e claim that F corresp ond s to a ( √ n, √ n )-selec tiv e family . T o s ee this, n ote that for an arbitrary n et w ork N , the subs et of no des in la yer L 1 of the i th BGI-comp onen t of net work N that are connected to the nod e y , corr esp ond to an arbitrary subset of [ √ n ]. Let this sub set b e called Z . Since π ′ completes broadcasting on net w ork N in at most 3 ∗ r rounds, there must exist some j < r su c h that in round 3 j + 1, for the fi rst time, exactly one no de fr om subset Z transmits. But this is equiv alen t to sa ying that there exists a su bset F j in F suc h that | F j ∩ Z | = 1. Finally , to appy the theorem 4.1, w e restrict ourselve s to ( n, k )-selectiv e families, w here k ≤ n 64 . Ho w ever, it is easy to see that if F is ( √ n, √ n )-selectiv e, then it is also ( √ n, √ n/ 64) -selectiv e. Now, r = |F | ≥ √ n 64 · 24 ∗ log n ≥ √ n 1536 . But this con tradicts our initial assumption that there exists a d ete rministic broadcast proto col π that completes b roadcast in less than √ n/ 1536 round s on every n etw ork of C 2 family . W e note here th at b etter constants could b e d eriv ed by using the hitting game argumen t from [3 ]. How ev er, we b eliev e that the current lo wer b ound is not asymp toti cally close to the optimal and h ence hav e c hosen n ot to optimize the constan ts. Belo w, w e n ote a coroll ary to the ab o v e theorem f or net w orks of arbitrary d iameter D . Corollary 4.1 Every deterministic br o adc ast pr oto c ol must take Ω( √ n ∗ D ) r ounds to c om- plete b r o adc ast on r adio networks of diam eter D . 5 Reduction s ( Pro of of the Lemma 4.1) In this section we pr esen t a series of sim ulation based reductions to p ro v e Lemma 4.1. 5.1 Reduction 1 The fir st reduction sho ws that w e ma y consider proto cols with a simp lified communicat ion structure, at the cost of a constant facto r (= 3) increase in the num b er of rounds. I n these proto cols, the no des co ordinate their transmissions so that collisions inv olving no des f r om differen t la ye rs do not o ccur. Lemma 5.1 Assume that ther e exists a pr oto c ol π 0 that c ompletes br o adc ast in at most r r ounds on every C 2 network. Then, ther e exists a pr oto c ol π 1 that c ompletes br o adc ast in at most 3 ∗ r r ounds on every network of C 2 family, su ch that the no des in layer L i tr ansmit in r ound t only if t ≡ i (mo d 3), for i = 0 , 1 , 2 . Pro of: Proto col π 1 sim u late s eac h round t of pr otocol π 0 in the s equ ence of r ounds 3 t , 3 t + 1 and 3 t + 2. The idea is that, in roun d 3 t + i , eac h no de in la y er L i tak es th e action that it w ould take in roun d t under proto col π 0 . Assuming that π 1 includes the description of pr otocol π 0 , then it is sufficien t to sho w that eac h no de w in the n et w ork can compu te the list of messages receiv ed by itself up to roun d t under proto col π 0 , durin g the execution of π 1 . The claim is certainly tr u e for t = 0. Now, sup p ose that, at the b eginning of roun d 3 t , ev ery n o de in the net work has the correct list of messages receiv ed up to round t − 1 un der proto col π 0 . Then, eac h n o de can tak e the appropriate action during rounds 3 t , 3 t + 1 and 3 t + 2, and up d ate th eir list of receiv ed message s as follo ws . If w is a no de in la ye r L i , then a) if w transmits a message in r ound 3 t + i , it app ends φ to its list of receiv ed messages, since it cannot receiv e a message in a round in whic h it acts as a trans mitter. b) otherwise, if exactly one neigh b or of w transmits durin g round s 3 t , 3 t + 1 and 3 t + 2, it app ends this message to the list; else it app end s φ . Condition (a) is obvio us. The only issue on condition (b) is th e abilit y of the n o de w to detect that a single neighbor tr an s mitte d in roun ds 3 t , 3 t + 1 and 3 t + 2. If w b elongs to la y er L 0 or L 2 , then all its neigh b ors are in la ye r L 1 and, according to the definition of a br oadca st p rotocol, it receiv es a message in round 3 t + 1 if and only if exactly one of its neigh b ors transmit. If w b elongs to la yer L 1 , then it h as the source and p ossibly a no de f rom la ye r L 2 as neighbors. Bu t since in this case no collision is p ossible, w can d etec t exactly whic h of its neigh b ors transm itte d. Hence, the conditions ab ov e guarantee that, at the b eginning of round 3( t + 1), eac h no de in the net work h as the correct list of m essag es receiv ed un der proto co l π 0 up to round t . W e denote by Π 1 the class of proto cols satisfying th e conditions of lemma 5.1. 5.2 Reduction 2 The second reduction shows that, instead of transmitting arbitrary messages, the source can just retransmit whatev er message it r ecei v ed in the previous L 1 transmission roun d. The idea is that the no des of la ye r L 1 can s imulate the b eh avior of the source, once they h a v e the sequence of messages it has receiv ed so far, and in this w a y to reco v er the message that the source sh ould hav e transmitted dur ing the execution of some other proto col. Lemma 5.2 Assume tha t ther e e xists a pr oto c ol π 1 of the class Π 1 , that c ompletes br o adc ast in at most 3 r r ounds on every C 2 network. Then, ther e exists a pr oto c ol π 2 , also of the class Π 1 , that c ompletes br o adc ast in at most 3 r r ounds on every C 2 network su ch that, in r ound 3 t , the sour c e just r etr ansmits whatever message it r e c eive d i n r ound 3 t − 2 . Pro of: In proto col π 2 the n odes of the net w ork b eha v e as follo ws. The source n ode b eha ves according to th e statement of the lemma. The no des in la yer L 2 just sim ulate pr otocol π 1 . The n od es in lay er L 1 decide wh at actio n to p erform in round 3 t + 1 in t w o steps. First, they u se the list of messages receiv ed from the source u p to round 3 t to simulate the b eha vior of the source un der proto col π 1 , and obtain the sequence of messages that th e source sh ould hav e transmitted up to roun d 3 t in the execution of proto col π 1 . This second list, together with th e list of messages receiv ed fr om a p ossible neighbor in la ye r L 2 , allo ws them to sim ulate their o wn b eha vior under proto col π 1 and compute the appropriate action to p erform in roun d 3 t + 1. W e denote by Π 2 the class of proto cols satisfying th e conditions of lemma 5.2. 5.3 Reduction 3 This redu ctio n sho ws that, instead of transmitting arbitrary m essag es, the source can just send descrip tions of BGI-comp onen ts of the net work on whic h the pr otocol is b eing executed. The idea is that, with the descrip tion of a BGI-comp onen t and the list of messages transmitted b y the sour ce, an y no de of the net work can reco ver the messages transmitted by the no des of this comp onen t to the source, and this is all that is requ ired to simulate a p rotocol of th e class Π 2 . Lemma 5.3 Assume that ther e exists a pr oto c ol π 2 of the class Π 2 that c om pletes br o adc ast in at most 3 r r ounds on ev ery C 2 network. Then, ther e exi sts a br o adc ast pr oto c ol π 3 , of the class Π 1 , that c ompletes br o adc ast in at most 3 r r ounds on every C 2 network such that • the sour c e is pr ovide d, as input, with a c omplete description of the network on which the pr oto c ol is b eing exe cute d. • in r ound 3 t the sour c e tr ansmits: a) the br o ad c ast message µ , if t = 0 . b) φ , if no message is r e c eive d in r ound 3 t − 2 . c) < i, τ > , if a message is r e c eive d in r ound 3 t − 2 ; in this c ase, the tuplet < i, τ > is a description of the BGI-c omp onent of the tr ansmitting no de in the network on which the pr oto c ol is b eing exe cute d. Pro of: In proto col π 3 the n odes of the net w ork b eha v e as follo ws. The s ou r ce no de b eh a v es according to the statement of the lemma. The no des in la ye r L 2 just sim u lat e proto col π 2 . The no des in la yer L 1 need, for the sim ulation of protocol π 2 , to compute, in eac h round 3 t , the message r ece iv ed b y the sour ce in round 3 t − 2. W e consider t wo cases: 1. If the source transm its φ in roun d 3 t , this means that it has receiv ed no message in round 3 t − 2, either b ecause n o neigh b or transm itted or b ecause a collision o ccurred. 2. If the source transmits < i, τ > in round 3 t , this means that a single neigh b or, from the BGI-comp onen t i , tr an s mitte d in round 3 t − 2. T o reco ver this message , eac h no de in L 1 can sim ulate the b ehavio r of th e no des in comp onent i up to r ound 3 t − 2, using the description τ and the list of messages transmitted by the source u p to round 3( t − 1) under proto col π 2 . W e denote by Π 3 the class of proto cols that satisfy th e conditions of lemma 5.3 5.4 Reduction 4 This reduction sh o ws that, instead of pro viding the source with a complete d escrip tion of the top olog y of the net w ork, it is suffi cie n t to provide it with just a p artia l top ologic al information in the form of an advice string. Moreo v er, the b eha vior of the sour ce is further restricted so that no w it just transmits the adv ice string together with the broadcast m essage in round 0, and remains silent thereafter. The idea is that the advice s tring gives the sequ ence of messages transmitted b y the source u nder pr otocol π 3 , and with this inform atio n the no d es in la ye r L 1 can carry out a complete sim ulation of proto col π 3 on th e netw ork. Lemma 5.4 Assume that ther e exists a pr oto c ol π 3 fr om class Π 3 , that c ompletes br o adc ast in at most 3 r r ounds on every network of family C 2 . Then, ther e exists a br o adc ast pr oto c ol π 4 , of the class Π 1 , such that • for e ach network N in C 2 ther e is an advic e string υ ( π 3 , N , 3 r ) such that pr oto c ol π 4 c ompletes br o adc ast on network N in at most 3 r r ounds when the sour c e is pr ovide d with this advic e string in the set up phase. • the sour c e tr ansmits the br o adc ast message and υ ( π 3 , N , 3 r ) in r ound 0 . • the sour c e r emains silent in ev ery r ound i > 0 . Pro of: The con tent of the advice string υ ( π 3 , N , 3 r ) is just the sequence of messages trans- mitted b y the source no de in the first 3 r r ounds of the execution of proto col π 3 on net wo rk N . In proto col π 4 the no des of the net work b eha v e a s follo ws. The source no de b eha v es according to the statemen t of the lemma. The no des in lay er L 2 just sim ulate proto col π 3 . In eac h round 3 i + 1, the n odes in la y er L 1 read the i th en tr y of the advice strin g υ ( π 3 , N , 3 r ), to obtain the message that the source would transmit in round 3 i und er p rotocol π 3 , and then sim u late their o wn b eha vior under proto col π 3 to compute the appr opriate action to p erform in this r ound. The pr otocol π 4 giv en by Lemma 5.4 is the p rotocol π ′ men tioned in the Lemma 4.1 of Section 4. 6 Pro cedu r e Prune (Pro of of th e Lemma 4 .2) In this section we describ e a pr ocedur e to obtain an advice string υ and a corresp onding subset of netw orks S ⊂ C 2 for a proto col π ′ giv en b y Lemma 4.1, su c h that the follo wing tw o conditions hold true: 1. Proto col π ′ completes broadcast in at most 3 ∗ r r ou n ds on ev ery net w ork of subset S , when the source no de is pr o vided with the advice string υ in the set up phase. 2. There exists an index i suc h that, for eac h p ossible top ology of a BGI-comp onen t, there is a net work N ∈ S w hose i th comp onen t h as exactly this top olog y . Recall that protocol π ′ is obtained through a series of reductions, and let π 3 b e the proto col from w hic h π ′ is obtained in the last r eduction. Under proto col π 3 , the source transmits only the br oa dcast m essag e µ , the message φ , an d top ological information of BGI-comp onent s < i, τ > . The sequence of messages transmitted b y the source no de under protocol π 3 (disregarding message µ ) giv es the advice string υ ( π 3 , N , 3 r ) pro vided to the source in the execution of protocol π ′ . The subset of net w orks S is constructed by the execution of pro cedure Pr une(), and considers the execution of pr otocol π 3 on ev er y net wo rk in C 2 . In the d escription of Pr une() and in the argumen ts that f ollo w, w e us e the notation ε ( π 3 , M , 3 t ) to indicate whic h ev ent o ccurs in roun d 3 t when π 3 is executed on net work N . There are three p ossibilities: • ε ( π 3 , M , 3 t ) = φ in dicate s that the source transmits φ in round 3 t b ecause none of its neigh b ors transm itte d in round 3 t − 2. • ε ( π 3 , M , 3 t ) = ρ indicates that the source transmits φ in round 3 t b ecause more than one of its n eigh b ors transmitted in round 3 t − 2. • ε ( π 3 , M , 3 t ) = < i, τ > giv es the message tr an s mitte d by the source in round 3 t when only one no de from la y er L 1 transmits in r ound 3 t − 2. Procedur e Prune( π 3 ,r) { S := set with all networks of C 2 If r = 1 Then Return S For t := 0 To r − 1 Do { If there exists N ∈ S with ε ( π 3 , N , t ) = ρ Delete from S every network M with ε ( π 3 , M , t ) 6 = ρ Else, if there exists N ∈ S with ε ( π 3 , N , t ) = < i, τ > , for some i Fix an arbitrar y such network N , and Delete from S every network M with ε ( π 3 , M , t ) 6 = ε ( π 3 , N , t ) } Return( S ) } No w, observe that all the net w orks in the set S returned by Prun e() are asso ciated with the same s equence of ev en ts ε ( π 3 , M , 3) , . . . , ε ( π 3 , M , 3( r − 1)). F rom this, it easily follo w s that the source transmits the same sequence of messages when pr otocol π 3 is executed on ev ery net work of the subset S . Let υ denote the advice string corresp onding to this sequence of messages, th en the ab o ve condition (1) h olds. T o chec k th at cond itio n (2) also holds, we fi x an arbitrary net work N from S , execute proto col π 3 , on N and mark its comp onen ts as follo w s: 1. If ε ( π 3 , M , 3 t ) = φ , then no comp onen t is marked. 2. If ε ( π 3 , M , 3 t ) = < i, τ > , then mark comp onen t i . 3. If ε ( π 3 , M , 3 t ) = ρ , then c h oose tw o of the no des that transmit in round 3 t − 2 arb itrarily , and mark the resp ectiv e comp onent s. Let B b e the set of comp onen ts marked in this pro cedure. Lemma 6.1 L et M b e a C 2 network whose c omp onents liste d in B have the same top olo gy as in network N . Then, M b elongs to the set S r eturne d b y Prune(). Pro of: W e prov e the lemma b y induction on r . The case of r = 1 is trivial. F or the ge neral case, we fi rst observ e that ev ery net work N ′ whic h satisfies ε ( π 3 , N ′ , t ) = ε ( π 3 , N , t ), f or t = 0 , 1 , . . . , r − 1, b elongs to the subset S . So, w e w ill pro v e that the net w ork M satisfies all those equations. Supp ose that the lemma h olds for r = k . Now let us consider the case of r = k + 1. By the ind uctiv e hyp othesis, w e ha ve that ε ( π 3 , M , t ) = ε ( π 3 , N , t ), for t = 0 , 1 , . . . , k − 1, so w e only n eed to show that ε ( π 3 , M , 3 k ) = ε ( π 3 , N , 3 k ). There are three cases to consider: Case 1: ε ( π 3 , N , 3 k ) = ρ In this case, more than one no de fr om L 1 transmit in roun d 3 k − 2 when π 3 is execute d on n et w ork N . Let x and y b e the no des chosen in step (3) of the marking pro cedure ab o v e, and supp ose that x and y b elong to the BGI-comp onen ts i and j , r esp ectiv ely . W e claim that x and y also transmit in round 3 k − 2 w hen π 3 is executed on netw ork M , whic h imp lies th at ε ( π 3 , M , 3 k ) = ρ . T o c hec k the claim, observe that th e BGI-comp onen t i and j h a v e the s ame top ologies in net w orks N and M . S ince the n o des in these comp onen ts receiv e the same sequence of messages from the source u p to round 3( k − 1), they ha ve iden tical b eha viors in rounds 3 k − 2 and 3 k − 1 when π 3 is executed on net w orks N and M . This follo ws from the definition of a d eterministic broadcast proto col. In particular, no des x and y transmit in roun d 3 k − 2 wh en π 3 is executed on net w ork M . Case 2: ε ( π 3 , N , 3 k ) = < i, τ > In this case, a single no de f r om L 1 transmits in round 3 k − 2 when π 3 is executed on netw ork N . Let x b e such no de, which, according to the message, b elongs to the i th BGI-comp onen t. No w, w e claim that x is also th e single no de to transmit in roun d 3 k − 2 w h en π 3 is executed on net work M . Before pro v in g the cla im, w e observ e that the BGI-comp onen t i is mark ed in the pro cedure ab o v e, and so it has exactly the same top ology on netw orks N and M . Thus, if the claim holds, we ha ve ε ( π 3 , M , 3 k ) = < i, τ > , as r equired. The fact that no de x transmits in round 3 ∗ k − 2 when proto col π 3 is executed on net work M follo ws b y the same argumen t giv en in case 1. No w, supp ose that some other no de in L 1 also transmits in the same r ound. Then, a collision would o ccur and the source w ould transmit ρ in its next transmission r ound 3 ∗ k . Ho wev er, b y the in ductiv e h yp othesis, the net work M survives up to the ( k + 1) th iteration of Prune(), an d so in this iteration th e net work N would b e purged f rom set S , whic h is a con tradiction. Hence, x is the only nod e to tr ansmit in round 3 k − 2 wh en π 3 is executed on net w ork M . Case 3: ε ( π 3 , N , 3 k ) = φ In this case, there is no trans mission in round 3 k − 2 when proto col π 3 is executed on N . A similar argument to the one giv en in case 2 allo ws to conclude that there is also no tr ansmission in round 3 k − 2 when proto col π 3 is executed on net w ork M . Hence, ε ( π 3 , M , 3 k ) = φ . Finally , condition 2 easily follo ws from lemma 6.1 by observing that, when r < √ n/ 2, the set B has less than √ n comp onen ts. Thus, if i is a BGI-comp onen t wh ic h do es not b elong to B , then every net w ork M whic h has exactly the same top ology as that of net work N excepting the i th comp onen t, b elongs to the subset S . Ac knowledgemen t(s): W e w ould lik e to thank Dariusz Ko w alski a nd And rzej P elc for useful discussions and encouraging u s to w ork on the lo wer b ound. W e thank E li Gafni for some initial co llab oratio n regardin g this wo rk, though he has dignifiedly c hosen not to b e a co-author. W e also thank Gunes Er cal and Ch en Avin for useful comments and suggestions ab out the pr esen tation of an earlier d raft of this wo rk. References [1] N. Al on, A . Bar-Noy , N. Li nial and D. Peleg. A lower b ound for r adio br o adc ast , Journal of Computer and System Sciences 43(1991), 290-298. [2] B. Awerbuc h. A new distribute d depth-first-se ar ch algorithm , Inform ation Processing Letters 20 (1985), 147-150. [3] R. Bar - Y ehuda, O.Goldreich and A. Itai. On the t ime co mplexity of b r o adc ast in r adio networks: an ex p onential gap b etwe en determinism and r andomization , Journal of Computer and System Sciences 45 (1992), 104-126. [4] C. Brito and S. V ay a. An information the or etic lower b ound for br o adc asting in r adio networks , manuscript, submitted to 44th Annual IEEE F oundations of Computer Science, FOCS’03. [5] C. Br ito and E. Gafni and S. V a ya. An information the or etic lower b ound for br o adc asting in r adio ne tworks , Symposium in Theoretical Asp ects of Computer Science, ST ACS 2004 . [6] B. Brusc hi and M. D el Pint o. Lo wer b ounds for the br o adc ast pr oblem in mobile r adio networks , Distributed Computing 10(1997), 129-135 [7] I. Chlam tac and A. F arago. M aking tr ansmission sche dule immune to top olo gy changes in multi- hop p acket r adio networks , IEEE/ACM T r ans. on Net w orking 2(1994), 23-29 [8] , B.S. Chlebus and D. Kow alski. A b e tter wake-up in r adio networks , In Proceedings of Ann ual Symp osium on Principles of Distributed Computing, POD C 200 4. [9] A. Czuma j and W. Rytter. Br o adc asti ng Algorithm s in R adio Networks with Unknown T op olo gy , T o appear in Pro cee dings of the 44th Ann ual IEEE Symposium on F oundations of Computer Scienc e, F OCS 2003 , Cambridge, MA. [10] B.S. Chlebus and M. Rokicki. Asy nchr onous br o adc asting in r adio networks , T o app ear in Internat ional Collo quium in Structural Information and Communication Complexity , (SIROCCO’2004), LNCS 3104, 57-68. [11] I. Chlamtac and O. W einstein. The wave exp ansion appr o ach to br o adc asting in multihop r adio networks , IEEE T ransactions on Communicat ions 39(1991), 426-433. [12] B.S. Chlebus, L. Gasieniec, A. Gibb ons, A. P elc and W. Rytter. Deterministic br o adc asting in unknown r adio networks , In Pro ceedings of 11th Annual A CM-SIAM Symp osium on Discrete Algorithms, SODA’99 861-870. [13] B.S. Chlebus, L. Gasieniec, A. Gibb ons, A. Ostlin and J.M . Robson. Deterministic r adio br o adc asting . In Pro- ceedings 27th Internationa l Col loquium on Automata, Languages and Programming, ICALP’ 2000,LNCS 1853, 717-728. [14] M. Chrobak, L. Gasieniec and W. Rytter. F ast br o adc asting and gossiping in ra dio ne tworks , In Proceedings 41st Ann ual IEEE Symp osium on F oundations of Computer Science, FOCS’2000, 575-581. [15] M. Chrobak, L. Gasieniec and D. Ko wa lski. Wake up pr oblem in multihop r adio networks , In Proceedings of 15t h Ann ual ACM-SIAM Symposium on Discrete Algorithms, SODA’2004, 985-993. [16] A.E.F. Clemen ti, A. Mon ti and R. Silvestri. Sele ctive families, sup erimp ose d c o des, and bro adc asting on unknown r adio networks , In Pr oceedings 12th Annual A CM-SIAM Symposium on Discrete Algorithms (SODA’2001) , 709- 718 [17] Cruz, R., and Ha jek, B. , A new upp er b ound to the thr oughput of a multi-ac c ess b r o adc ast channel. , IEEE T ransactions Information Theory IT-28, 3 (May 1982), 402-405. [18] G. De Marco and A. P elc. F aster br o adc asting i n unknown r adio networks , Information Pro cessing Letter 79(2001) ,53-56. [19] P . Er d¨ o s, P . F rankl, and Z. F uredi. F amilies of finite sets in which no set is c over e d by the union of r others , Israel Journal of M athematics 51(1985) ,79-89. [20] M. El kin and G. Kortsartz. Impr ove d br o adc ast sc he dule for r adio networks , In Sixteent h Annual ACM-SIAM Symposium on Discrete Algori thms, SODA 2005. [21] I. Gab our and Y. Mansour. Br o adc ast in r adio networks , In Pro ceedings 6th Annua l ACM-SIAM Symp osi um on Discrete Algorithms, SODA 1996,577-585. [22] L. Gasieniec, A. Pelc and D. Peleg. The wakeup pr oblem in synchr onous br o adc ast syste ms , In SIAM Journal on Discrete Mathematics 14, 2001, 207-222. [23] F.K.Hwang. The time c omplexity of deterministi c br o adc ast in r adio networks , Di screte A ppli ed Mathematics 60(1995) ,219-222. [24] P . Indyk, Explicit c onstructions of sele c t or and r elate d c ombinatorial structur es, with appl ic ations , In Pro cee dings 13th Annual A CM-SIAM Symposium on Discreet Algorithms, SODA’2002, 697-704. [25] T. Jurdzinski and G. Stach o wiak, Pr ob abilistic algorithms for the wake up pr oblem i n single-hop r adio ne t works In Pro cee dings of 13t h In ternational Symp osium on Algorithms and Computing, ISAA C 2002, LNCS 2518, 525-549. [26] W.H.Kauz and R.R. C. Singleton, Nonr andom binary sup erimp ose d c o des , In IEEE T ransactions on Information Theory 10(1964), 363-377. [27] E. Kushil evitz and Y . Mansour, An Ω( D log ( N/D )) lower bo und for br o adc ast in r adio networks , SIAM Journal on Computing 27(1998), 702-712 [28] M. MOLLE, Uni fic ations and extensions of the multiple ac c ess c ommunic ations pr oblem. Ph.D. Thesis, Universit y of California, Los Angeles, Los Angeles, Calif., July 1981. [29] Dariusz R. Ko wa lski and Andrzej Pelc, Deterministic Br o adc asting Time in R adio Networks of Unknown T op olo gy , In Pro ceed ings 43rd Symp osium on F oundations of Computer Science, FOCS’200 2. [30] Dariusz R. K o walski and Andrzej Pelc, Time of deterministic br o adc asting in r adio networks with lo c al know le dge , In SIAM Journal of Computing 33(4): 870-891, 2004. [31] Dariusz R. Kow alski and A. Pelc, F aster Deterministic Br o adc asting in A d H o c R adio Networks , In Pro ceedings 43rd Symp osium Theoretical Asp ect s of Computer Science, ST A C S 2003. [32] D. Kow alski and A. Pelc, Time c omplexity of r adio br o adc asting: adaptiveness vs obliviousness and vs r andom- ization vs determinism , Theoretical Computer Science 333 (2005),355-371 [33] D. Kow als ki and A. Pe lc, Centr alize d deterministic br o adc asting in undir e cte d multihop r adio networks , In Pro- ceedings of 7th Internationa l W orkshop on Approximation algorithms for Combinat orial Optimization Pr oblems, APPRO X 2004, LNCS 3122,171-182. [34] Err ata r e gar ding ”On the Time-Compl exity of Br o adc ast in R adio Networks: An Exp onential Gap Betwe en Deter- minism and R andomization” , Dec. 2002, av ailable from http : //w w w.w isdom.w eiz mann.ac.il/ oded/p b g i.html
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment