Pseudo-Random Bit Generation based on 2D chaotic maps of logistic type and its Applications in Chaotic Cryptography
Pseudo-Random Bit Generation (PRBG) is required in many aspects of cryptography as well as in other applications of modern security engineering. In this work, PRBG based on 2D symmetrical chaotic mappings of logistic type is considered. The sequences…
Authors: C. Pellicer-Lostao, R. Lopez-Ruiz
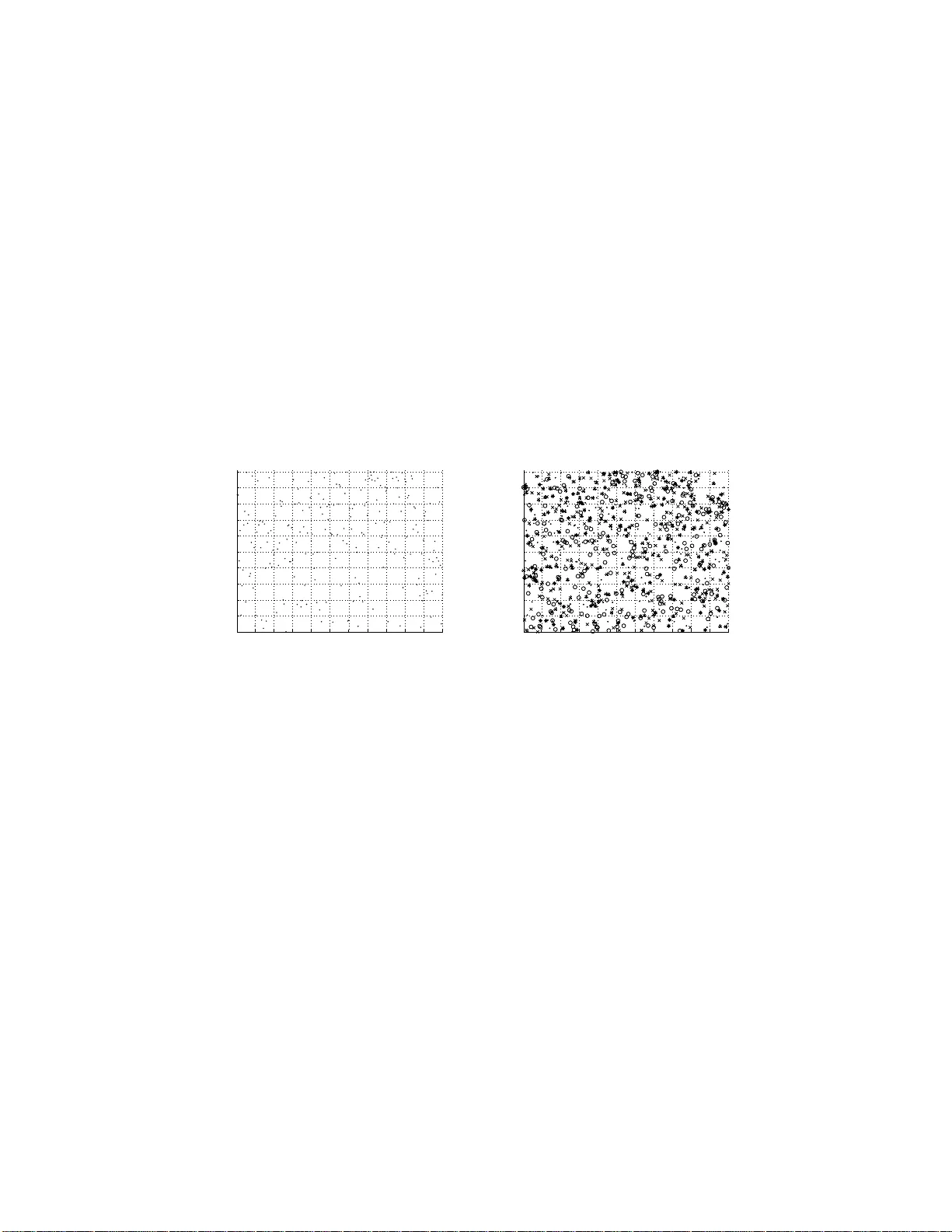
Pseudo-Random Bit Generation based on 2D c haotic maps of logistic t yp e and its Applications in Chaotic Cryptograph y C. Pellicer-Lostao and R. L´ op ez-Ruiz Department of Computer Science and BIFI, Universidad de Zarago za, 50009 - Zaragoza, Spain, carmen.pel licer@unizar.es, rilopez@uniza r.es Abstract. Pseudo-Random Bit Generatio n (PRBG) is required i n many aspects of cryptography as w ell as in other applications of mo dern secu- rit y engineering. In this work, PRBG based on 2D sy mmetrical chaotic mappings of logistic typ e is considered. The sequences generated with a chao tic PRBG of this typ e, are statistically tested and the compu t ational effectiveness of the generators is estimated. Considering this PRBG v alid for cryptography , th e size of the av ailable key space is also calculated. Different cryptographic applications can b e suitable to this PRBG, b eing a stream cipher probably the most immediate of them. Key W ords: Pseudorandom Bit Generation, Chaotic Cryp tograph y , Se- curity Engineering 1 In tro duction Many asp ects of cryptogr a ph y and moder n security engineer ing dep e nd upon the generatio n of ps e udo-random num b ers. Examples are the use of nonces in authentication pr otoco ls, salts in certain signatur e schemes, g eneration of keys or the keystreams o f s tream cyphers [1], [2]. The require ments of ra ndomness in these genera to rs v ary ac c o rding to their application. F or example, the gener ation of master keys normally requires high quality or entrop y [10]. But in the case of nonces, uniqueness can b e the main requirement for some proto cols [1]. Pseudo-Rando m Bit Genera tors (PRBG) are implemen ted by deterministic nu mer ic algor ithms and they should pass several statistical tests [2], [3], to prove themselves use ful. These tests ca n be s et up to differe nt levels of req uiremen ts of ra ndo mness depending on the future a pplication of the PRBG. T he security of the entire cryptogr aphic proto col or system, relies o n the randomness quality of the generator [10]. Over the last tw o deca des, several works hav e implemen ted PRBG based on chaotic systems (a complete survey can b e found in [4]). Chaotic systems hav e the pr o perty of b eeing deterministic in the microsco pic s pace and b ehav e ran- domly , when observed in a coa rse-gra ine d state-spa ce. The sensitivity o f chaotic maps to initial conditions make them optimum candidates to relate minimal critical information ab o ut the input, in the o utput sequence. Their iter ativ e na- ture ma k es them fast co mputable a nd able to pro duce binar y sequences with extremely long cycle le ng ths. In 2006 Madhek ar Suneel prop oses in [5], a metho d for pseudo-random binary sequence genera tio n based on the t wo-dimensional H ´ enon map. The author a lso indicates that the c hoice of the H´ enon map is ra ther arbitrary and that similar results should a lso b e attainable with other 2D maps. This pap er explore precisely this p ossibilit y , and pr esen ts a finite automata scheme as the key to a c hieve that. This compr e hensiv e scheme is then applied to tw o particular 2D dy namical systems presented in [6], which are formed b y t wo symmetrically co upled log istic ma ps. The pseudo-ra ndom prop erties of the generator s o bta ined that wa y , are in vestigated. The chaotic PRBG a lgorithm descr ibed in this pap er can b e used in different wa ys. One of its applicatio ns , and maybe the most immediate, could be the construction o f practical strea m ciphers. In this wa y , the chaotic PRBG can expand a shor t key into a long keystream, which dir ectly exclusive-or’ed with the clea r text or message, giv es the cipher text. The ev a luation o f the potential size o f the key space and the computational cost of the algo rithm makes it worth to b e considered. The pap er is str uctured as follows: Section 2 introduces c hao tic PRBG. Sec- tion 3 describ es s tatistical testing o f random seq ue nc e s . Section 4 obtains a PRBG ba sed on a 2 D symmetric a l chaotic map of lo g istic type. In Sec tio n 5 several binary sequences a re o btained and tested. The computational cos t o f the PRBG algo rithm and t he size of the key space for cryptographic applications are ev a luated in Sectio n 6. Section 7 remar ks the final conclusio ns and discusses further work to b e done. 2 Chaotic Random Bit Generation The inherent prop erties of chaos, such a s ergo dicity and sensitivity to initial con- ditions and co n trol para meters, connect it directly with cryptogra ph y character- istics of co nfusion and diffusion [7]. Additionally c hao tic dynamical systems have the adv an tag e of providing simple computable deterministic pseudo-ra ndomness. As a conse q uence of these observ ations, several works were presented s ince 1990s implementing PRBG base d on different chaotic systems [5], [9], [10], [11], [12]. In some way , it could b e said that chaos has br o ugh t into b eing a nov el br anc h for P RNG in crypto g raphy , called ch a otic PRNG. An N-dimensional deterministic dis crete-time dynamical system is an itera- tive map f : ℜ N → ℜ N of the form: X k +1 = f ( X k ) (1) where k = 0 , 1 . . . n . is the dis crete time and X 0 , X 1 . . . X n , are the states of the system a t different ins tan ts of time. In these systems, the evolution is p erfectly determined by the mapping f : ℜ N → ℜ N and the initial condition X 0 . Starting from X 0 , the initial state , the rep eated iter ation o f (1 ) g iv es rise to a fully deter minis tic ser ies o f states known as an orbit . T o build a chaotic PRBG is necessary to construct a n umerical a lgorithm that transforms the states un der chaotic be ha viour of the system in to binary nu mbers . The ex isting designs of chaotic PRNGs us e different techniques to pass from the co n tinuum to the binary world [4]. The mo st imp ortant are: 1. E xtracting one or more bits from ea c h chaotic state alo ng chaotic orbits [9]. 2. Dividing the phas e space in to m sub-spaces (defined through N = l og 2 ( m ) threshold v alues), and output a binar y num b er i = 0 , 1 , , m − 1 if the chaotic orbit visits the i th subspace [5], [10]. 3. Co m bining the o utputs o f t wo o r mo re chaotic sys tems to generate the pseudo-rando m num b ers [11], [12]. Discrete or digital chaos implemen ted on computers with finite precision is normally ca lle d “pseudo chaos”. In pseudo c haos dy namical degra dation of the chaotic prop erties of the s y stem may app ear, as throughout itera tions pseudo orbits may depa rt from the real ones in many differen t and uncontrolled ma nners [8]. Even so, the a b ov e expos ed techniques are ca pable of generating seq ue nc e s of bits o r binar y num b ers, which appea r random-like from many asp ects. One may also consider that using high dimensional chaotic systems could offer additional adv antages. While les s known, these sys tems whir l many v ariables at any ca lculation and the p erio dic patterns pr oduced by the finite pre c ision of the computer are more difficult to appear than in the low dimensional cases. In this pap er the technique of dividing the phase space is follow ed and applied on tw o symmetrica l tw o-dimensional (2D) c hao tic maps of logistic type . 3 Statistical T ests Suites In g eneral, randomness cannot b e mathema tica lly prov ed. Alternatively , differ- ent statistical batteries of tests ar e used. E ach of these tests ev a luates a relev ant random prop erty exp ected in a true random gener a tor. T o test a certain random- ness prop erty , sev er al output sequences of the gener ator under test are taken. As one knows a pr iori the statistical distribution of p ossible v a lues t hat true random sequences would b e likely to exhibit, a co nclusion c a n b e obtained up on the probability of the tes ted seq ue nce s to be r andom. Mathematically this is do ne as fo llo ws [3 ]. F or e a c h test, a st atistic variable X is sp ecified along with its co rresp ondent the or etic al r andom distribution function f ( x ). F or non-rando m sequences , the statis tic can b e exp ected to ta ke on larg er v a lues, typically far-out in the ta ils of f ( x ). A critic al value x α is defined for the theoretical distribution so that P ( X > x α ) = α , that is called the signific anc e level of the tes t. In the same wa y , theor etically other dis tribution functions and a β v alue could b e defined to assess non-random prop erties. But in practice, it is imp ossible to calculate a ll the distributions that describ e no n-randomness, for there a re an infinite num b er o f wa ys that a da ta strea m can be no n-random. When a test is a pplied, the tes t statistic v alue X s is computed on the sequence being tested. This test statistic v alue X s is compar ed to the critical v alue x α . If the test statistic v alue exceeds the cr itical v alue, the hypo thes is for ra ndomness is rejected. The rejection is done with a (100 ∗ α )% probability of having F A LSE POSITIVE error (this is ca lled a TYPE I err or , where the sequence w as ra ndom and is rejected). Other wise is not rejected (i.e., the hypothesis is accepted) with a probability o f (100 ∗ β )% o f erro r (this is called TYPE II err or or F ALSE NEG- A TIVE, the s e quence was non- r andom and is accepted). In conseq uence passing the test mer ely pr o vides a pro babilistic evidence that the generator pr oduces sequences which hav e cer tain characteristics of ra ndom sequences. F o r a given application, the v alue of α m ust b e selec ted appropriately . This is because if α is to o high TYPE I er rors may freq uen tly occur (resp ectively if α is to o lo w the same will happ en for TYPE I I error s ). F or cryptog raphic applications typical v a lues o f α ar e selected b et ween the interv al αǫ [0 . 001 , 0 . 01], which is a lso referred as a co nfidence level in the interv al [99 . 9% , 99%] for the test. Unlik e α, β is not fixed, for it dep ends on the no n-randomness defects of the generator . Nevertheless α, β and the size of the tested sequence (n) a re r elated . Then for a given statistic, a cr itical v alue and a minim um n should b e se lected to minimize the probability of a TYPE I I erro r ( β ). There exist differen t well-kno wn sources o f test suites av a ilable in the In- ternet. In the present work, Marsa glia’s Dieha rd test suite (in [13]) and NIST Statistical T e st Suite (in [3]) w er e sele c ted, for they are very a ccessible and widely used. T able 1 lists the tests co mprised in these suites. In b oth suites, the Number Diehard test suite NIST test suite 1 Birthday spacings F requency (monobit) 2 Overlapping 5-p erm ut ation F requency test within a blo c k 3 Binary rank test Cumula tive sums 4 Bitstream Runs 5 OPSO Longest run of ones in a blo c k 6 OQSO Binary matrix rank 7 DNS Discrete fourier transform 8 C ount-the-1’s test Non-ov erlapping template matching 9 A parking lot Overlapping template matching 10 Minim um distance Maurer’s universal statistical 11 3D-spheres Approximate entrop y 12 Squeeze Random excursions 13 Overlapping sums Random excursions v ariant 14 R uns Serial 15 Craps Linear complexity T able 1. List of tests comprised in th e D iehard and NIST test suites. test statistic v alue X s obtained in each test is us e d to calcula te a p-v alue that summaries the stre ng th of evidence ag a inst the randomnes s of the tested PRBG. 4 Pseudo-Random Bit Generation based on t wo-d imensional c haotic maps of logistic t yp e In [6], L´ opez-Ruiz and P´ ere z -Garc ´ ıa analyze a family of three chaotic sy stems obtained b y coupling tw o logistic maps . The fo cus here will be made on mo dels (a) and (b), whic h will be ca lled systems A and B: S Y S T E M A : T A : [0 , 1] × [0 , 1] − → [0 , 1] × [0 , 1] x n +1 = λ (3 y n + 1) x n (1 − x n ) y n +1 = λ (3 x n + 1) y n (1 − y n ) S Y S T E M B : T B : [0 , 1] × [0 , 1] − → [0 , 1] × [0 , 1] x n +1 = λ (3 x n + 1) y n (1 − y n ) y n +1 = λ (3 y n + 1) x n (1 − x n ) (2) Amazingly , these s y stems show the fo llo wing symmetry T A ( x, y ) = T B ( y , x ), which implies that T 2 A ( x, y ) = T 2 B ( x, y ). F ro m a geo metrical p oin t of view, b oth present the same chaotic attractor in the interv al λ ∈ [1 . 0 3 2 , 1 . 0843]. The dy- namics in this regime is pa rticularly interlaced around the saddle po in t P 4, that plays an impor tan t role for our prop oses: P 4 = [ P 4 x , P 4 y ] , whe re P 4 x = P 4 y = 1 3 1 + r 4 − 3 λ ! . (3) T o obtain the Symmetric Coupled Logistic Map PRBG, the alg orithm pr e- sented in [5] is applied on Sys tem A. Its functional blo ck structure is represented in Fig.1 and it is expla ined in the following para graphs. λ 1 Logistic Bimap (System A) x y i-1 i-1 y i x i -1 -1 b x b y b x i i P*i b y P*i Binary Mixing O (j) delay delay Sub-space decision 1 -1 3 3 1 -1 λ 1 > τ x > τ y Fig. 1. F unct ional blo c k structure of the prop osed algorithm in [5] for Sy stem A. In this case, the tec hnique of dividing the phase space in four sub-spaces is used. This is done in the blo ck na med as Sub-sp ac e de cision in which the threshold v alues, τ x and τ y , are employed t o conv ert the s uite into a binary sequence, b y means of the following equations : b x = 0 if x ≤ τ x 1 if x > τ x ; b y = 0 if y ≤ τ y 1 if y > τ y . (4) A purely statistica l pr ocedur e is prop osed in [5] to obtain τ x (or τ y ) as the median of a lar ge T set of x (or y ) v alues. τ x and τ y are chosen a fter the first T = 1000 iterations of the system. After obtaining S x = { b i x } ∞ i =1 and S y = { b i y } ∞ i =1 , they ar e sampled with a frequency o f 1 / P (each P iterations) a nd B x = { b P ∗ i x } ∞ i =1 and B y = { b P ∗ i y } ∞ i =1 are obtained. The effect of sk ipping P consec utiv e v a lues of the or bit is nec essary to ge t a random macros c o pic behaviour. With this op eratio n, the cor relation exis ting betw een consecutive v alues gener ated by the chaotic system is eliminated, in a way s uc h that over a P min , seque nce s generated with P > P min will app ear macro scopically random. Althoug h P is normally in tro duced as an additional key parameter in pseudo -random seq uences generation [14], it strongly determines the sp eed of the generatio n a lgorithm, so it is reco mmended to b e k ept as small as p ossible. The output binary pseudor andom sequence O ( j ) is obtained by a mixing op eration o f the actual and previous v alues of the sequence B ( j ) = [ B x ( j ) , B y ( j )] given by the truth table sketc hed in T able 2. B y ( j − 1) B y ( j − 2) 0 1 0 B x ( j ) N ot( B x ( j )) 1 B y ( j ) Not( B y ( j )) T able 2. T ruth table generating the binary sequence. Unfortunately t he sequences so formed do no t pass the minimum requir e- men ts o f ra ndomness assess e d by Diehard test suite. At this p oint, it is noticed that, to obtain g oo d results, the geometrical characteris tics of the sy stem must be tak en into acco un t. More precisely , it is found out that the division of the phase space in four sub-spaces must b e defined, in a wa y that the s ystem visits each sub- s pace according to a particular finite sta te automata. This a utomata is inferred from the H´ enon ma p b ehaviour in [5] and it has a particula r pattern of visits of the four sub-spaces. F or Systems A and B, this finite automata is depicted in Fig. 2 (a ) and 2(c). Let us name the s ub-spaces cor r espo nding to [ b i x , b i y ] with v alues [0 , 0], [1 , 0], [0 , 1] a nd [1 , 1] a s 1 ,2,3 a nd 4. Althoug h the four sub- spaces a r e no t visited equally , there ex is ts a sy mmetry of mov ements b etw een sub- spaces 1-3 and 2 -4, which ha s a characteristic mix ing of 50 % a nd 50%, a s long as a pr edominant 4 [1,1] 1 [0,0] 3 [0,1] 2 [1,0] (10%) (10%) (40%) (40%) 20% 80% 50% 50% 0 0.2 0.4 0.6 0.8 1 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 2 [1 0] 4 [1 1] 3 [0 1] 1 [0 0] (a) (b) 4 [1,1] 1 [0,0] 3 [0,1] 2 [1,0] (10%) (10%) (40%) (40%) 20% 80% 50% 50% 0 0.2 0.4 0.6 0.8 1 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 2 [1 0] 3 [0 1] 1 [0 0] 4 [1 1] (c) (d) Fig. 2. (a) Fin ite automata an d (b) final sub- sp ace d ivision for System A. (c) Finite automata and (d) final sub -space division for System B. (In b oth cases, λ = 1 . 07). (80%) and co nstan t transition b etw een 3 and 2. This leads to a highly v ariation of binary v alues in s e quences S x , S y . In the end, these conditions give the final result of an output sequence O ( j ) with a pr oper balance of ze r os and ones, or put it in a nother wa y , with pse udo-random pro perties. T o get this automata for the symmetric coupled logistic maps Systems A and B, one should c hose the diagonal a xis, whic h divides phase space in t w o parts, ea ch of which is equally visited (5 0%). And additional statistical calculus is requir e d to divide these tw o sub-spaces, in a nother two with a vis iting rate of 40%-10 % e ac h one. When this is done, o ne can observe that this is g ot by merely selecting P4 a nd the line p erp endicular to the axis in P4 as the other division line. The final sub-space division for each sy stem is pres e nted in Fig. 2 (b) and 2(d), along with the indications of the evolution of the visits to each sub-space. Finally the initial a lgorithm in Fig. 1 applied to System A, is mo dified with the appro pr iate sub-space decision blo ck. The final P RBG functiona l scheme is represented in Fig. 3. As a direct application to cryptography , the PRBG could be used fo r the construction of a stream cipher . Differe nt initial conditions, x 0 and y 0 and pa- rameters λ and P , can be applied to the input of the system and b e used as a key to generate the keystream, or o utput sequence O ( j ). The k eystrea m O ( j ) can b e XORed dire c tly with a clear text obtaining that w ay the ciphertext. λ 1 Logistic Bimap (System A) x y i-1 i-1 y >x y i x i -1 -1 b x b y b x i i P*i b y P*i Binary Mixing O (j) delay delay Sub-space decision 1 -1 3 3 i i y >-x+ 2P4 i i x 1 -1 λ 1 Fig. 3. F unctional block structure of the PRBG applied to the sy mm et ric coupled logistic map PRBG with System A. Different se q uences are obtained with the system o f Fig. 3 in next section. Their randomnes s is asses sed and demonstrates them statistica lly v alid for cr yp- tographic applications. This may indicate that the a utomata scheme presented in Fig. 2(a ) and 2(c) repres en ts a sufficient condition to obtain pseudo-r andomness. Consequently , it can r epresent a systematic sc heme to extend the algorithm in [5] to get PRBG on other chaotic maps. 5 Pseudo-Random Sequences Statistical testing T o a ssess the r andomness of the PRBG obtained in the previo us sectio n with systems A and B, s ev era l sequences ar e obtained and submitted to the Diehard [13] and NIST [3] test suites describ ed in section 3. Similar results were found for b oth systems and for simplicity , o nly those obtained with system A will be presented here after. T en sequences were generated with six different sets o f initial conditions. Their c har acteristics ar e describ ed in T able 3. Sequence S1 S2 S3 S4 S5 S6 x 0 0 . 98912 5 0 . 491335 0 . 672757 0 . 726874 0 . 39565 0 . 999851 y 0 0 . 68912 5 0 . 691335 0 . 497757 0 . 901874 0 . 49565 0 . 649851 λ 1 . 04869 1 . 05392 1 . 06961 1 . 08007 1 . 06438 1 . 07489 P D min 55 45 35 47 n.a. n.a. P N min 83 105 83 83 100 85 T able 3. Parameters P D min and P N min for different sequences S i , i = 1 , .., 6, with different initial conditions ( x 0 , y 0 ) and map parameter λ . Six of them (S1,S2,S3,S4,S5 a nd S6 ) w er e tested with Nist tests suite with 200 Mill. of bits a nd four of them (S1,S2,S3 and S4) w ere tested with Diehard tests suite with 8 0 Mill. of bits. Here, the par ameters P Dmin and P N min are the minim um sampling rate or shift factor , P min , ov er whic h, all sequence s ge ner ated with the same initial co nditions and P > P min pass Dieha rd or Nist tests suites, resp ectively . It is obser v ed here, that the Nist tests suite r equires a higher v alue of P min and that S5 and S6 were not tested with Diehard battery of tests. In the Dieha rd tests suite, e ac h of them returns one or several p-v alues which should be uniform in the interv al [0,1) when the input sequence c o n tains truly independent random bits. The significance level of the tes ts was set prop erly for cryptogr a phic applications ( α = 0 . 01 ). The so ft ware av ailable in [13] provide a total o f 218 p-v alues for 15 tests, a nd the uniformity requir emen t can b e as sessed graphically plotting them in the in terv al [0,1). 20 40 60 80 100 120 140 160 180 200 220 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 Number of p−Value p−Value 20 40 60 80 100 120 140 160 180 200 220 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 Number of p−Value p−Value (a) (b) Fig. 4. (a) Diehard test suite p-va lues obtained with all tests for initial conditions S1 with P = P D min = 55. (b) p-va lues obtained for initial conditions S 1( • ),S2( ◦ ),S3( ∗ ) and S4( × ) with P = P D min v alue in T able 3. Fig. 4(a) shows the unifor mit y distribution of the p-v alues over the in terv al [0,1) obtained for a sequenc e with initial conditions S1 a nd P Dmin = 55. Se- quences with initial v alues S1 to S4 wher e prov ed to pa ss the Diehard battery of tes ts. Fig. 4(b) presents a g raphical represe ntation of the p-v alues o bta ined for each sequence with sa mpling factor P = P Dmin v a lue in T able 3. It can be observed that some p- v alues are o ccasio nally nea r 0 or 1. Although it can no t be well appreciated in the figure, it has to be said that thos e never really r e ac h these v alues. In the Nist tests suite [3], o ne o r more p-v alues are als o re turned for each sequence under test. The s ig nificance le vel of the tests was s e t to α = 0 . 01, as in the Diehard case. Thes e tests require a sufficiently hig h length of sequences and to prove ra ndomness in one test, tw o conditions should be verified. First, a minim um pe r cen tag e of s e q uences should pass the test a nd second, the p-v alues of all sequences should a lso b e uniformly distributed in the in terv al (0 , 1). F o r this case, each of the six seq uences with initial conditions S1 to S6 ar e arrang ed in 200 sub-sequenc e s of 1Mill. bits each and submitted to the Nist battery of tests. Seq uences S prov ed to pass all tests ov er a minimum v alue of P N min , shown in T able 3. 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 0.96 0.965 0.97 0.975 0.98 0.985 0.99 0.995 1 Test number Proportion of sub−secuences that pass 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 C1 C2 C3 C4 C5 C6 C7 C8 C9 C10 0 10 20 30 40 Test number Uniformity of p−values for S4 P−values interval (a) (b) Fig. 5. In ( a), the prop ortion of sub-sequen ces S1 th at passes each test is display ed. In (b) The distribution of p -v alues of S 4 is ex amined for each test to ensure un ifor mity . The interv al b etw een 0 and 1 is divided in ten sub- interv als ( C 1 , C 2 , ..., C 10), and t he p-v alues that lie within each su bin terv al are counted and plotted. In Fig. 5(a) and 5 (b), the r esults obtained f or S 1 a nd S 4 res p ectively are graphically pres en ted, as an ex ample of what was obtained for e a c h S . The tests in the suite ar e num b ered according to T able 1. Fig. 5(a) represen ts the per cen tag e of the 200 sub-sequences of S1, tha t pass each of the 15 tests of the suite. These p ercentages are ov er the minim um pass rate required of 96 . 8893% for a s ample size = 200 binary s ub-sequences. Fig . 5(b) describ es the unifo r mit y of the distr ibution of p-v a lues obtained for the 15 tests of the suite. Here, uniformity is as sessed. The interv al (0,1) is divided in ten subinterv als ( C 1 , C 2 , ..., C 1 0) and the num b er of p-v alues that lay in each sub-interv al, among a total of 200 , are counted and prov ed to b e uniform. 6 Key space size and computational cost T o establish the complexity , and consequently the sp eed of the PRBG describ ed in Fig. 3, the principle of inv ariance is observed. This says that the efficiency of one algor ithm in different execution environmen ts differs only in a multiplicativ e constant, when the v a lues of the parameters of cost are sufficiently high. In this sens e, the a s ymptotic b ehaviour of the computational cost of the PRBG is gov erned by the c a lculus p erformed in the c hao tic blo c k. This blo ck per forms P itera tions to obtain an output bit, O ( j ). The capital theta notation ( Θ ) can be us ed to descr ibe an asymptotic tight bo und for the mag nitude of cos t of the P RBG. And consequently , the 2D sym- metric coupled logistic ma ps hav e a computational cost or complex it y of o rder Θ ( P ∗ n ). When consider ed for cryptog raphic applica tions, the key space is determined by the interv al of the parameter λ and the initial conditions that keep the dynam- ical system in the chaotic regime. These are λ ∈ [1 . 032 , 1 . 084 3] , x 0 ∈ (0 , 1) and y 0 ∈ (0 , 1). The sampling par ameter can a ls o b e consider e d as another par ameter of the key space. One must obse rv e that P should b e k ept in a suitable r ange, so that the PRBG is fast eno ug h for its desir ed application. These in terv als can be denoted with brack ets and calcula ted a s [ λ ] = 0 . 0523, [ x 0 ] = 1 , [ y 0 ] = 1 and [ P ] = 48 9 0, when ta k ing [ P ] ∈ [110 , 600 0] as the range of the sampling fa c tor. Let us consider ǫ 32 ≈ 1 . 1 921 × 10 − 7 as the smallest av aila ble precision for fixed-p oin t representation with 32 bits a nd its corresp ondent mag nitude ǫ 64 ≈ 2 . 2204 × 1 0 − 16 for floa ting -point num b ers with 64 bits. These q ua n tities give us the max im um num b er o f po ssible v alues of every parameter in any of the tw o representations. This is easily computed dividing the interv a ls by ǫ , as K λ = [ λ ] /ǫ , K x 0 = [ x 0 ] /ǫ , K y 0 = [ y 0 ] /ǫ and K P = [ P ] /ǫ . The total size of repr esen table parameter v a lues is given by K , calculated as K = K λ × K x 0 × K y 0 × K P . K is the size o f the av a ilable key-space and its loga rithm in base 2 gives us the av aila ble length of bina ry keys to pro duce pseudo-rando m s e quences in the gener ator. The v alues obtained for each num b er pre cision, are K 32 = 1 . 53 × 10 30 with a key length o f 100 bits for single precision and K 64 = 1 . 2 7 × 10 65 , with a k ey length of 216 bits for double pr ecision. These r esults a re encoura ging for reco mmending the use of the P RBG in Fig. 3 for cry ptographic a pplications, where a length of keys g reater than 10 0 is consider ed strong enough aga inst brute forc e a ttac ks, [7]. 7 Conclusions In the present work, a refinement of the algo rithm expo s ed in [5 ] by M. Suneel is presented. It consists of the introduction of a finite automata that makes po ssible its a pplication to other chaotic maps. In some way , this finite automata could be said to extend the ra nge of application of this algor ithm for other 2D chaotic systems. This is r eferred in [4] a s making the P RBG chaotic-sys tem- fr ee. The fact is that, while sys tematic, the sch eme presented in this pap er is not straight-forward. This is be c ause building the finite automata r equires neces sar- ily a detailed study o f the g eometrical pr oper ties of the dynamical evolution of the ch a o tic system. The authors apply this technique to build tw o new PRBG using tw o particu- lar 2D dynamica l systems for med by tw o sy mmetr ically coupled lo gistic maps. A set of different pseudo-ra ndom sequences are generated with one o f the P RBG. Statistical testing of these s equences s ho ws fine r esults of random pro perties for the PRBG. The estimation of the PRBG computational cost has an asy mptotic tight bo und of Θ ( P ∗ n ). The av ailable size of the key spac e is also calc ulated and a minim um le ng th o f binary keys of 10 0 a nd 2 16 bits is obtained for simple and double pr e c ision resp ectively . These preliminary results indicate a promising quality of the PRBG for cr yptographic a pplications. Consequently , the chaotic PRBG algor ithm could b e of use for differen t ap- plications in secur it y engineering. A dire c t application in cryptogra ph y could b e the co nstruction of a stream cipher . This can be easily obta ine d when the out- put sequences O ( j ) in Fig. 3 are used as a keystream. Then, this can b e directly X ORed with a clear text obtaining that wa y the ciphertext. F o r future work, the author s plan to co ns ider the geo metrical proper ties of the logistic bi-mappings to enha nce the p erformance of the presented PRBG. References 1. Anderson, R .: Securit y Engi neering, A Guide t o Build Depen dable Distributed Systems, http://www .cl.cam.ac.uk/ rja14/bo ok.h tml John Wiley and Sons I nc., New Y ork (2001) 2. Menezes, A ., va n Oorschot, P ., V anstone, S.: H andbo ok of Ap p lied Cryptography . CRC Press, Florida (1997) 3. NIST Sp ecial P ub licatio n 800-22: A Statistical T est Suite for the V alidation of Random Number Generators and Pseudo Ran d om Number Generators for Cryp- tographic Applications, (2001) 4. Li, S .: Analyses and New Designs of Digital Chaotic Ciphers. PhD thesis, School of Electronic and Information Engineering, X i’an Jiaotong U niv ersity (2003) 5. Madhek ar, S.: Cryptographic Pseudo- R andom Sequences from the Chaotic H´ enon Map. http://a rx iv .org/ abs/cs/0604018, (2006) 6. Lopez- Ruiz, R., P´ erez-Garcia, C.: Dynamics Maps with a Global Multiplicative Coupling. Chaos, Solitons and F ractals, V ol.1, pp 511-528, (1991) ; Lop ez-Ruiz, R., F ournier-Prunaret, D.: Complex P atterns on the Plane: Different T yp es of Basin F ractalization in a Two-Dimensional Mapping, I n ternational Journal of Bifurcation and Chaos, V ol. 13, 287-310 (2003) 7. Alv arez G., Li, S.: Some Basic Cryptographic Requirements for Chaos-Based Cryp- tosystems. International Journal of Bifurcation and Chaos, V ol.16, pp 2129-2151 (2006) 8. Li, S., Chen,G., Mou, X .: On the dyn amical degradation of d igital p iecewi se linear chao tic maps. International Journal of Bifurcation and Chaos, V ol.15, pp 3119-3151 (2005) 9. Protopop escu, V.A., Santoro, R.T., T ollo ver,J.S.: F ast secure encry p tion- decryption metho d b ased on c haotic dy namics. US Paten t No. 5479513 (1995) 10. Sto jano v ski, T., Ko carev, L.: Chaos based Rand om Number Generatiors. P art I: Analysis. IEEE T ransactions on Circuits and S ystems I: F undamental Theory and Applications, V ol.43, pp 281-288 (2001) 11. P o-Han, L., So o-Chang, P ., Yih- Y uh, C.: Generating chaotic stream ciphers using chao tic systems. Chinese Journal of Physics, V ol.41, pp 559-581 (2003) 12. Li, S ., Mou, X., Cai, Y.: Pseudo-random bit generator based on coup le chaotic systems and its application in stream-ciphers cryptography . INDOCR YPT 2001, LNCS, V ol. 2247, pp 316-329, Springer, H eidelberg ( 2001 ). 13. Marsag lia, G.: The diehard test suite, 1995. http://stat.fsu. edu/ geo/diehard.h tml 14. Kocarev, L.: Chaos-based Cryp tograph y: a brief o verview. IEEE Circuits and Sys- tems Magazine, V ol.1, pp 6-21 (2001)
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment