Crossing Borders: Security and Privacy Issues of the European e-Passport
The first generation of European e-passports will be issued in 2006. We discuss how borders are crossed regarding the security and privacy erosion of the proposed schemes, and show which borders need to be crossed to improve the security and the priv…
Authors: Jaap-Henk Hoepman, Engelbert Hubbers, Bart Jacobs
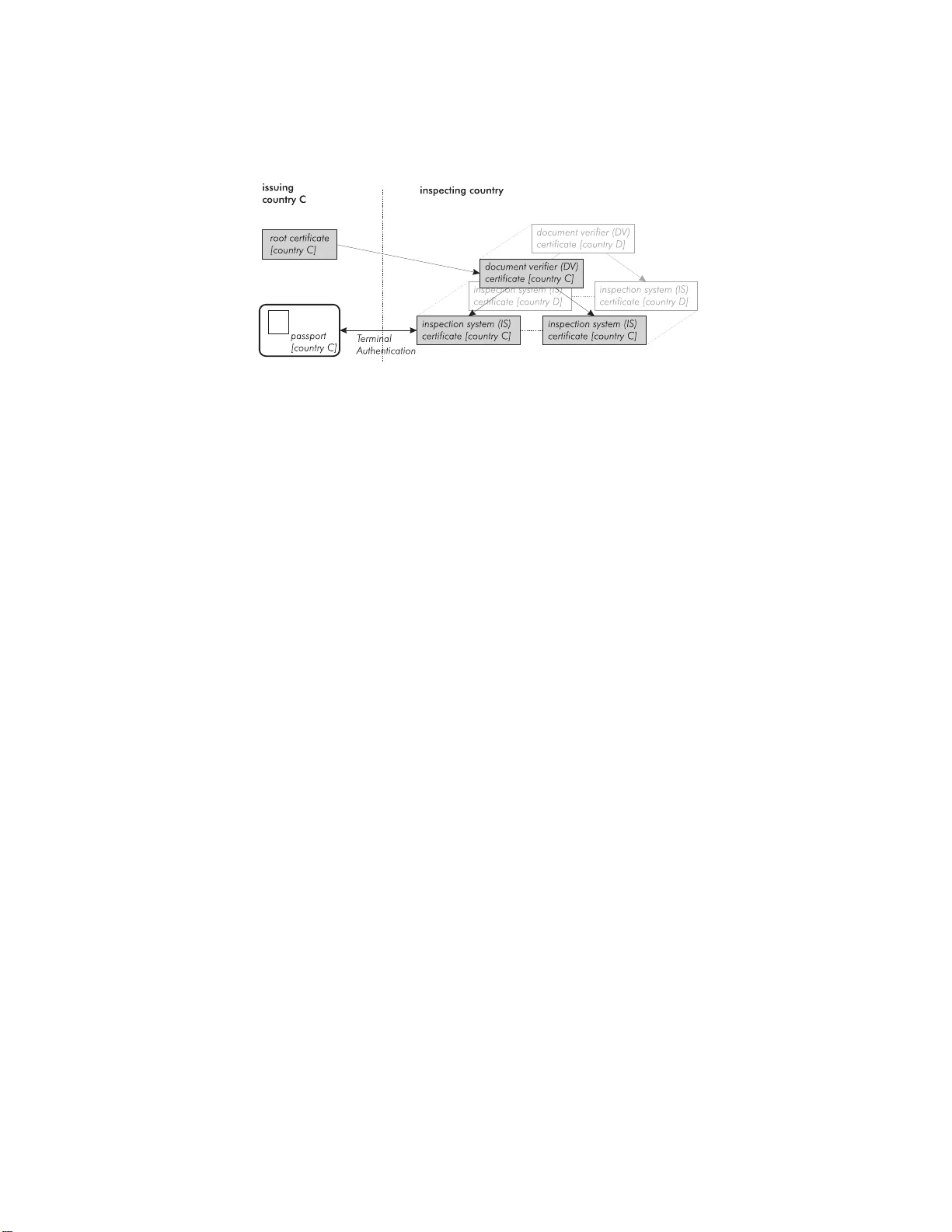
Crossing Borders: Securit y and Priv acy Issues of the Europ ean e-P assp ort ⋆ Jaap-Henk Ho epman, Engelb ert Hubber s, Bart Jaco bs, Martijn Oostdijk, Ronny Wic hers Schreur Institute for Computing and I nformation Sciences Radb oud Universit y N ijmegen P .O. Box 9010, 6500 GL Nijmegen, the Netherlands { jhh,hubb ers,bart,m artijno,ronny } @cs.ru.nl Abstract. The first generation of Europ ean e-passp orts will b e issued in 2006. W e discuss how b orders are crossed regarding the security and priv acy erosion of the prop osed schemes, and show which b orders need to b e crossed to impro ve th e security and t h e priva cy protection of th e next genera tion of e-passp orts. In particular we discuss attacks on Basic Access Control due to the lo w entrop y of the data from which the access keys are derived, we sketc h th e Europ ean prop osals for Exten ded A ccess Con trol and the weaknesses in that sc h eme, and show ho w fundamentally different design decisions can make e-p assports more secure. 1 In tr o duction After several years of preparation, ma n y co un tries start issuing e-passp orts with an embedded chip holding biometric da ta o f the passp ort holder in 2006. This is a ma jor IC T- op eration, inv o lving many coun tries, most of them providing their own implementation, using biometrics at an unprece de nted scale. Passpo rt s ecu- rity m ust conform to in ternational (public) standards, issue d by the Int ernational Civil Aviatio n Or ganization (ICA O) [ 11 , 10 ]. The standa rds cover confidential- it y , integrity and authenticit y of the pa ssp ort data, including the facial image. Additionally , the Europ ean Union (EU) has develop ed its own s ta ndards (called “Extended Access Control”). The present pap er r eviews these developmen ts (like in [ 14 , 15 ]) esp ecially from a E ur op ean p ersp ective, with c o rresp onding emphasis o n fingerpr int pro- tection. Also it tries to put these developmen ts within a wider p ersp ective o f ident it y mana g ement (IM) by governmen ts, fo llowing [ 8 ]. This leads to a “r evi- sion” plan for e-passp or ts. F rom an academic background we, the author s, clo sely fo llow the introduc- tion of the e-pa ssp ort in the Netherla nds. W e have advised the gov er nmen t on several matters, and are inv olved in public de ba tes on related issues. W e have received a n ear ly tes t version of the e-pas sp ort, and developed our own reader- side s o ft ware, bas e d on the ICAO proto cols. W e have had acces s to confidential ⋆ Id: passport.tex,v 1.44 2006/06/30 07:25:14 ronny Ex p 2 Ho ep man et al. material regarding the EU-proto co ls. How ever, the pres ent pap er is base d solely on publicly av aila ble ma terial, and is or ganised a s follows. W e first discuss the main secur it y requir e men ts the new e-passp or t s hould satisfy . After a brief discussion of bio metry in Sect. 3 , we desc rib e the standar d security measur es of the ICA O standard and the weaknesses asso ciated with them in Sect. 4 . F uture Europ ean e-pa s sp orts will b e equipp ed w ith Ex tended Access Control, which we outline in Sect. 5 , and whose s hortcomings we also study . e-Passp orts enable new applica tions. Sect. 6 discusses the danger o f such function creep but also in vestigates the new p ossibilities crea ted b y such ap- plications. W e study identit y management issues of the e-pa ssp ort in Sect. 7 , and ev a luate the rea lisation of the original go als in Sect. 8 . W e finish the pa- per with so me prop osa ls for more fundamental changes to the architecture of a second gene r ation of e-pas sp orts that will incre ase b oth their security and their flexibility of use in new applications. 2 Aims and Securit y Goals It is a fact that mo der n pass po rts are har d to forge. Thus, many criminal or gan- isations do not even tr y such fraud, but instead collect lar ge num b ers of gen uine passp orts, and pick one that shows a r easona ble resemblance to a member that needs a new identit y . Similar ly , passp or ts are sometimes b o rrow ed for illeg al bo rder cross ing, and later returned to the r ightful owner. The or iginal aim of the use o f biometrics in travel do cuments is thu s to com- bat “ lo ok-alike” fr aud. Hence the emphasis is on bio metric verific ation (instead of identific ation ), inv o lv ing a 1:1 chec k to make sure that a pa rticular passp or t really b elongs to a particular p erson. The biometr ics of the passp o rt holder will b e included in a chip that is embedded in the pas sp ort. Co mm unication with the chip will b e wir eless, a nd not via contact p oints, b ecause wire le ss co mmun ication allows higher data ra tes, do es not inv o lve wear, and do es not require a change of the standar d for mat of the passp ort to for instance credit-car d siz e 1 . The wireles s character do es intro duce new security risks (with re s pe ct to traditional pa s sp orts), for the holder , the issuing state, and for the acc e pting state. A t a high level of abstraction, the following three sec ur ity g o als s eem reasona ble. The fir s t tw o fo cus on co nfiden tiality for the pa s sp ort holder. The last one mainly concerns the accepting (and also is s uing) sta te. 1. A pas sp ort r eader s hould identify itself first, so that only “ trusted” parties get to read the information stor ed in the chip. 2. No identifying information should b e r e le ased without consent of the pass- po rt holder. 3. The r e ceiver of the information should b e able to establish the integrit y and authenticit y of the data. 1 A change of format for other official do cuments, like a drivers licence, is seen as less problematic, b ecause such a d ocu ment is not stamp ed. Crossing Borders 3 The fir st goa l re la tes to the situation where for instance a p olice officer wis hes to check your identit y . In most countries you have the rig ht to ask the p olice officer in question to identif y himself firs t, so that you c a n b e s ur e tha t you are dealing with a genuine representative of the s tate. The sec ond goal is r elev ant to prevent “RFID-b ombs” [ 14 ] for instance, that are a ctiv ated by the immedi- ate pres e nc e o f (the passp ort of ) a particular p er son, or citizen of a particula r country . Such information is a lso useful for a terroris t who is trying to decide whether to blow himself up in a particular bus. W e shall ev aluate the rea lisation of these goals later on, in Sect. 8 3 Biometry This pap er do es not fo cus on the biometry inv o lved, but a few words are in order. ICAO has o pted for the use of facial images and fingerprints as primary biometrics b ecause they are rea sonably familiar , easy to use , and non-intrusive. A controv ersia l issue—from a priv acy per s pe ctive—is that the passp ort chip will not co ntain templates but pictures (actual JPEGs ). The re a son is tha t there is no well-established digital s tandard for such templates, a nd early co mmitmen t to a closed propr ietary fo rmat is no t desira ble. This mea ns that if a pa ssp ort chip (or data base, o r r eader) is compromised, original bio metric da ta leaks out, which may lead to reconstructio n and additiona l (identit y) fra ud. The effectiveness of biometry is highly ov er rated, esp ecially by p oliticians and p olicy makers. Despite rapid g rowth in a pplications, the large - scale use of biometry is untested. The difficulty is that it is not only unpr ov en in a huge single application (such as e-passp o r ts), but also not with many differen t applications in parallel (including “biometry for fun”). The interference caus e d by the diversity of applicatio ns—each with its own security policy , if any—ma y lead to unfo r eseen forms of fraud. A ba sic is sue that is o ften ov er lo ok ed is fallback. What if my biometric iden- tit y ha s b een c o mpromised, a nd I am held r esp onsible for something I r eally did not do, how can I still prove “it wasn’t me”? The Netherla nds ha s recently conducted a field test for the enro lment pro c e- dures of the bio metr ic passp o rt, see [ 19 ], inv olv ing almos t 15.0 0 0 participants. The precise interpretation o f the outcome is unclear , but failure-to-a cquire turns out to b e a significant problem, esp ecia lly for young and elderly pe o ple. Substa n- tial num b ers o f p eople will th us not have appropriate biometric travel do cuments, so that fully automatic b order cro ssing is not a n o ptio n. 4 Standard Security Measures (ICAO) The v ario us ICAO standards for machine re adable travel do cuments, notably [ 11 ] and [ 10 ], sp ecify pr ecise requirements for a ccessing and interpreting the conten ts of the embedded chip. Different security c o ntrols ar e describ ed to ensur e that different s ecurity goa ls a re met. W e discuss these in the order in whic h the mechanisms are used in a t ypical sess ion be tw een reader (o r: insp ection s ystem, 4 Ho ep man et al. Fig. 1. E xample of a Dutch pa ssp ort. The tw o b ottom lines of text a re the MRZ. the computer that is attempting to r ead information fr om the do cument) and the Europ ean passp ort chip. BAC : Basic A c c ess Contr ol. Before any information ca n b e rea d from a pa ssp ort, the rea der needs to go throug h b asic ac c ess c ontr ol (BAC). This is a challenge- resp onse proto co l in which the r eader pr ov es to the passp or t that it ha s knowl- edge of the conten ts of the machine r eadable z one (MRZ). The MRZ consists of tw o lines of optically reada ble text containing among other s the name of the holder, and the passp o rt num b er. It is print ed on the first pa ge of the physical do cument (See Fig. 1 ). The pr o cedure is as follows. The rea der o ptically rea ds the co nt ent s o f the MRZ, and derives the ac c ess key see d k IFD / ICC from the data it r eads. After that, the reader prov es to the chip that it has optically r ead the MRZ by sig ning a r andom challenge from the chip using a key derived from the access key seed. Subsequently , passp ort and insp ection system exchange s ome extra random data, which is then used to gener ate se s sion keys and an initial counter for s e cure messaging. The sessio n keys are fresh for each sess ion. BAC pr even ts so -called skimming of passp or ts, i.e., reading the conten ts without the cardholder ’s knowledge. Note that BAC do es no t authent icate the reader: any one who knows the MRZ ca n s uccessfully complete BAC and co n tin ue reading o ther information on the chip. SM: Se cur e Messaging. Confidentialit y and integrit y of all communication b e- t ween r eader a nd pas s po rt is provided by so-called s e cur e messaging . Commands sent to the passp or t as well a s r esp onses sent back to the reader a re encry pted and augmented with a message a uthentication co de (MAC), using the keys estab- lished during BAC. A sequence counter is included to preven t replay of mes sages. P A: Passive Authentic ation. The data store d on the passp or t is o r ganised in a logical data structure (LDS), which cons ists of a num b er of files (called data groups). Typical examples of data gro ups are: a file co ntaining the information in the MRZ, a file containing a JPEG imag e o f the cardho lder’s face, and files containing other biometric features such as the car dholder’s fing erprints. Crossing Borders 5 Each data group in the LDS is hashed. All these hashe s together for m the (do cument ) se curity obje ct SO LD S . The security ob ject is signed by the issuing country and the result, SO D , is stored on the passp o rt as well. This means that the insp ection system can check tha t the conten ts of the LDS hav e not bee n alter e d during comm unication, thus ensuring the int egrity of the LDS. The standards r efer to this in teg r ity pr otection mechanism as p assive authentic ation . AA: A ctive Authentic ation. T o pr even t cloning of the chip, an int egrity mecha- nism called active aut hentic ation is used, in which the passp or t proves p os session of a priv ate key k AA using a challenge-resp o ns e pro to col. The cor resp onding pub- lic key , needed by the insp ectio n system to chec k the resp onse of the passp ort, is part o f the LDS and can b e read b y the insp ection system. A hash of this public key is s igned through the SO D , to ensure authenticit y . 4.1 Guessing the Access Key T o access the pa ssp ort without having its MRZ, one needs to guess the acces s key seed k IFD / ICC , which is 12 8 bits lo ng. The Nationa l Institute of Standar ds and T ec hno logy (NIST) [ 18 ] and the ECR YPT EU Netw o r k of Ex c e llence on cryptolog y [ 3 ] recommend 80 bits for a minimal level o f genera l purpo se protec - tion in 20 05, and 112 bits ten years fro m now. In other words, the a ccess key seed is long enough to provide adequate security . But the fact that the access key seed is derived fro m information in the MRZ can b e used to the a ttack ers’ adv antage. The ‘MRZ-informa tion’ consists of the concatenation of the passp or t num ber , date of bir th and da te of expiry , including their r esp ective chec k digits, as describ ed in [ 9 ]. Given a g uess for the MRZ- information, the co rresp onding access key seed k IFD / ICC is easily calculated, and from that all other s e ssion k eys can be derived a s well. These keys can then be tried against a tr anscript of an eavesdroppe d communication session betw ee n this passp ort and the reade r , to see if they deliver meaningful da ta. T o estimate the a mount of work the a ttack er needs to p er form for such an o ff- line attack, we estimate the a mount of Shannon entrop y of each of these fields. W e should stres s this is a very crude approach (unless we assume the underly ing probability distributions ar e uniform). F or low er b ounds, we should in fact use the Guessing entrop y [ 17 ] ( P i ip i ) or even the min-entrop y (min i − log p i ). The Shannon entrop y only gives us an upp er b ound, but if that b ound is small the security of the system is most cer tainly weak. The entrop y of the date of birth field is log (100 × 3 65 . 25) = 15 . 1 6 bits, as it can co ntain only the last tw o digits of the y ear of bir th. I f one can see the holder of the passp or t and g uess his age correct within a mar gin of 5 years, the en tropy of this field decreases to 10 . 8 3. The date of expiry is determined by the da te o f iss uing and the v alidit y p er io d of a passp ort. In the Netherlands, passp o r ts a re v a lid for 5 y ears, and are issued only on working days (barring exceptional circumstances ). F or a valid passp or t, the entrop y of this field b ecomes log(5 × 365 . 25 × 5 / 7) = 1 0 . 34. 6 Ho ep man et al. Fig. 2. K nown dates of issuing reduce the sear ch spa ce. The MRZ field for the p assp ort numb er can contain 9 characters . If the pa ss- po rt num b er is longer , the excess characters are s to red in the MRZ optiona l data field (which is not used to der ive the a ccess key seed). The e ntropy of the passp or t num b er field, a ssuming digits and upp er-ca se letters only , b ecomes log((26 + 10) 9 ) = 4 6 . 53. Many countries hav e further restrictions on the format of their passp ort num b er s. Passp or t n umber s may co ntain check digits, o r start with a c ommon prefix to distinguish pass po rt types (e.g ., militar y passp or ts). A t b est, the total entrop y o f date o f birth, date of ex piry and passp ort num b er bec omes 15 . 16 + 10 . 34 + 46 . 53 = 7 2 . 03, which is le ss than 8 0 bits recommended b y bo th NIST and ECR YPT [ 3 , 1 8 ] to protect against eav esdr o pping a nd other off- line atta cks. It is sufficient to protect aga inst skimming a ttacks (where po ssible keys are tried on- line) be cause the passp ort is slow to r esp ond to each individual key tried. In certain co unt ries the situatio n is ev en w o rse. Often, pa ssp ort n um ber s a re issued sequentially . This implies there is a co r relation betw een the da te of is sue (and therefore date of expiry ) and the passp or t num b er. Moreov er, all curre ntly v alid passp o r ts num b er s (ignoring sto le n o r otherwise inv alidated ones) form a consecutive rang e, which is no long er than the total num b er of p eople of that nationality . F or the Dutch pas sp ort for instance, bo unding the p o pula tion fro m ab ov e by 2 0 million, the pa ssp ort num b er entropy drops to lo g(20 × 10 6 ) = 24 . 2 5. With sequentially issued pa ssp orts, the entrop y drops even further with ev- ery known combination of a pass po rt num b er and the expiry da te. Supp ose we know k such co mb inations. This gives rise to k + 1 int erv als of p o ssible passp or t nu m ber s for a given date ra nge L et us ta ke the ra ther p essimistic a pproach tha t we do not assume anything ab out the distr ibution of pa ssp orts ov e r dates within those interv als (although it is very likely that passp or ts are is sued at a r easona bly constant rate). O n the o ptimistic s ide, let us a ssume the k known pas sp orts a re issued evenly distributed ov er the v alidit y per io d length. This reduces the sear ch space by a fa c tor k + 1 as illustrated in Fig. 2 . Hence the e ntropy of expiry date plus pa ssp ort num ber drops with log( k + 1). F or the Dutch passp or t, using k = 15 Crossing Borders 7 and the fig ures ab ove, the entrop y of the passp or t num b er b ecomes a s small a s 20 . 25, and the to tal entrop y could b e as s mall as 1 0 . 83 + 10 . 34 + 20 . 25 = 41 . 42 (when we assume we can guess the age of the passp ort holder). One obvious idea is to include the MRZ optional data field in the list of MRZ items that is used to derive the MRZ access key seed. This would incr ease the entrop y of the MRZ a ccess key seed, esp ecially if this optional data field is filled with ra ndom data. Unfortunately so me countries alr eady use this field for other purpo ses. In the Netherlands, for instance, this field stores the so cial- fiscal num b er, which is uniquely linked to an individual and not very secr et information. In fact, this idea was recently rejected for inclusion in the ICAO standards. 4.2 T raceabilit y T o avoid collisio ns, co nt actless smar t cards and RFID s y stems use unique low- level tag ident ifiers in the ra dio communication pro to col. This is also true for the e-passp or ts. If this identifier is fixed (which is usually the case in RFID ta gs and contactless s ma rt cards), passp orts ar e clearly ea sily traceable. Note that b ecause this identifier is us ed in the very first stages of setting up a co nnection b etw e e n the pass p o rt and the reader, no for m of a ccess control or reader authentication can b e per formed. Luckily , this anti-collision identifier do es no t hav e to b e fixe d. The num b er can also b e randomly gener ated each time the passp ort comes within r ange of a reader. I f the random generator is o f s ufficient quality (and this is certa inly an issue in low-end RFID sy s tems), the pa ssp ort can no longer b e traced throug h the anti-collision identifier. How ever, the anti-collision identifier cr eates a p os sible subliminal channel. F or instance, ins tea d of s imply gener ating a rando m num b er r , the pa ssp ort could b e instructed to gener a te an anti collis io n identifier like id = E k NSA ( r , p assp ortnumb er ) . The r e sulting string looks ra ndom, b ecause of the ra ndomness of r and the prop erties o f the encryption function. But clear ly it ca n b e decrypted by the owner o f k NSA to r eveal the pa ssp ort num b er. Unless the pass p o rt chip is reverse engineered, the existence of such a subliminal channel ca nnot b e detected. Another subliminal channel exis ts when Active Authen tication is used [ 5 ]. Recall that active authentication r equires the passp or t to sign a challenge fro m a r eader using its unique priv ate key . Be c ause the challenge is tota lly deter mined by the r e ader, the reader ca n embed informa tion into this string, which is un- knowingly signed by the passp ort. F o r instance, the challenge could contain the bo rder cr ossing lo cation, a nd the cur r ent date and time. A sig nature adds an extra layer of no n-repudiability to the b o rder cro ssing logs, and can be used to prov e this fact to other s. The challenge could also contain the passp ort num ber of the p erson verified ahea d of you a t b order insp ection, po ssibly linking you to the pe rson you were trav elling with. 8 Ho ep man et al. Even if all the ab ov e issues are addressed, discriminating features of pass- po rts remain. Different countries may use differen t chip supplier s. Later batches of pa s sp orts will us e more a dv anced technology , or may contain differen t o r ad- ditional informatio n 2 . In the future, newer versions of chip op erating systems may b e used. All these differ ences may b e noticeable by lo oking carefully at the b ehaviour of the chip on the radio channel, a t the chip’s Answer T o Reset (A TR), which is sent in r eaction to a res et co mmand by the reader, or at the resp onses the chip g ives (or do esn’t give) to sp ecific ca rd c o mmands s ent to it. W e expec t to see lar ge differences in b ehaviour esp ecially o n unintended, unex- pec ted or even unsp ecified input sent to the card. All these things are p o ssible befo re BAC has b een p erformed. Other applications may b e put on the passp orts (see Sect. 6 ) as well. These applications may even be accessible b e fore BAC has b een pe r formed. The set o f av a ilable a pplications may a ctually c onstitute a na r row pr ofile tha t ide n tifies a sp ecific s et of po ssible passp ort ho lders, and may r e veal the pla ce of work, or the banks the passp or t holder has ac counts with. W e conclude that even without acc e ss to the MRZ, i.e., in the classic skim- ming scenario o n streets, public transp ort, etc., passp orts still leak informa tio n that can be traced back to individuals, or groups of individuals. 5 Extended Access Con trol Standardisation of the security fea tures and biometr ics to b e used in Europ ea n passp orts has b een taken up indep endently (but o f co ur se in accor dance with the ICAO s tandards) by the Europ ea n Union [ 7 ]. In re c ognition of the fact that biometric informa tio n is quite sensitive, the E urop ean Union ha s ma ndated that such data s hould b e protected by a so-ca lle d “E xtended Access Co nt rol” mech- anism. T he technical sp ecifica tions of the Euro p ea n e-pass p o rt are drafted by a sp ecial EU Committee, founded as a result of Article 6 of Re g ulation 1 683/9 5 laying down a uniform format for visas [ 6 ]. Public information ab o ut the details of E xtended Access Control ha s recently bec ome av a ilable [ 5 , 16 ]. This a llows us to discuss cer tain shortcomings in the schemes under co nsideration, althoug h we wish to stress that these schemes are a huge improv ement over the extremely minimal security fea tures imp osed b y the ICAO standards. Extended Acces s Co n trol consis ts of tw o phases, Chip Authen tica tio n fol- low ed by T erminal Authen ticatio n. Chip Authen tica tion per forms the s ame func- tion as Active Authentication in the ICAO standards , i.e., proving the ch ip is genuine and thus pr otecting the pass po rt a gainst cloning. It av oids the pro blems asso ciated with active authentication, like the challenge se ma nt ics discus sed in the previous sectio n. Chip authentication achiev es its task by first ex changing a session key using a Diffie-Hellman key exc hange. The chip uses a static key pair for this, the public part of which is par t of the log ical data structure (LDS) on 2 Indeed, the first passp orts will b e issued without fingerprints. Crossing Borders 9 Fig. 3. Extended Access Control cer tificates the chip and thus signe d thro ugh the security ob jects SO D . The terminal uses a fresh key pair for each sessio n. Authen ticity of the chip is established once the chip prov es that it knows the s e s sion key , which happ ens implicitly when the session key is used success fully to communicate with the chip. T erminal Authentication aims to prov e to the chip that the terminal is al- low ed to access the da ta on the chip. This access is gr anted through a chain of certificates, the ro ot o f which is the issuer of the passp or t at hand (see Fig. 3 ). In other words, the issuer of the pa ssp ort controls who can access the data on the pas sp ort. This ro ot issues Do cument V e r ifier (DV) Cer tificates, one for each country that is g r anted a ccess to the data on the pa ssp ort. These DV cer - tificates ar e used to generate Insp ection System (IS) certificates, which can b e distributed to insp ection systems (e.g., rea de r s/terminals ) a t b or de r cro ssings. Each pas sp ort issued by a par ticula r country can verify the authenticit y of these D V c ertificates, and hence of the IS cer tifica tes is sued through these DV cer - tificates. A v alid IS certifica te gra nt s ac c ess to certain data on the chip. All certificates hav e a limited v alidity p erio d. T erminal a uthen tication, as pr op osed, do e s hav e a few weaknesses. First o f all, the chip cannot keep time itself, and do es not have access to a r e liable s ource of time either. This makes it ha rd to chec k whether a certificate ha s expired or no t. This, in tur n, mak es it practically impo ssible to revoke a certificate. The pro blem is the following. A terminal w ith a v alid IS certificate and a v alid D V c ertificate can access the sensitive data on many passp o rts. When such a terminal is stolen, thes e access rights re ma in, e ven when the v alidity p erio d of thes e cer tificates has expired: the chip do es not know the co rrect time, and the termina l do es not hav e to tell it the corre c t time. This is the cas e even if certificates have extremely shor t v alidity per io ds, like a single day . W e s ee that one stolen ter minal br e aks the intended sec ur ity goa l of ter minal a uthen tication. Of course, stolen ter mina ls do no t make skimming attacks p os s ible: a terminal still needs access to the MRZ in order to p erform bas ic acces s control. T o mitigate the problem somewhat, the standar ds pro po se that the chip keeps the most recent da te seen on a v alid certifica te. In other words, the chip adv ances its 10 Ho ep man et al. idea of the current time each time it pass es a b or der insp ection system. This only saves the frequent trav ellers; p eople that ba rely use their pass po rts stay vulnerable for a long time. Secondly , the certificate hie r arch y itself p ose s a pro blem. The hier arch y is quite shallow. It do es no t make it easy to allow acce ss to the biometric data for o ther applicatio ns b eyond b o rder insp ectio n, even though such applica tions are already b eing discussed to day (see also Sect. 6 b elow). T o acquire a ccess, one has to apply for IS certificates a t the country DV, o r for a DV cer tificate at ea ch iss uing country . The latter would create a h uge ma na gement ov erhead, as it would require ea ch co unt ry to reliably verify the identit y and trus tw or- thiness of the r equesting applicant and issue certifica tes in resp onse. The first makes it impo s sible for countries to differentiate access rights a mong different applications, and would make the country D V resp onsible for the issuing of IS certificates for each and every termina l inv o lved in the new applica tion. This is clear ly impractica l, if we consider the use of passp or ts for home banking or single sign-on systems that req uire terminals at e ach a nd every PC. Making the certificate hierarch y large r and more flexible ma y not be an option. It means the chip has to verify even more certificates b efor e it ca n grant access. This do es put quite a burden o n the pro ce s sing capa bilities of the chip, which sho uld gua r antee rea sonably shor t transa ction times. No o ne is willing to stand in the queue at b order insp ection for an even longer amount of time, simply b eca use the new passp orts contain new, but slow, technology . A different, more flexible, appro ach is discus s ed in Sect. 9 . 6 New Applications The new e-pas sp ort requires a n international infras tructure for biometric verifi- cation. This is a huge pro ject, o f whic h the effectiveness and risks are uncertain. The main driving forc e is p olitical pressure: the lo gic of p olitics simply req uires high profile a ction in the face o f international terroris m. Once implemented, it inevitably leads to function creep: new p ossible a pplications emer ge, either sp on- taneously or v ia new p olicy initiatives. W e shall discuss tw o s uch applica tions, and s p ecula te ab out the future. Once we obtain a new pass po rt with a high-end chip embedded with which we can communicate o urselves (via op en sta ndards), we c a n a sk ours e lves whether we can also use it for our own purp oses. W e briefly disc uss tw o options: logon, and dig ital signature s. The e-passp o rt can b e used to log on to your computer ac c o unt. F o r instance, if you give your MRZ (o r the asso ciated keys) to your computer or lo ca l netw ork , the log on pro cedure can set up a challenge-r esp onse session with your passp or t: activ ation of the chip happ ens via the MRZ, and checking of a sig nature written by the pa ssp ort-chip on a challenge gener ated by your computer c an pro ceed via the public key o f the do cument sig ner. It allows your co mputer to chec k the integrit y of the pas sp orts security o b ject, which contains the public k ey corres p o nding to the priv ate signature- key o f your passp ort. Crossing Borders 11 This authentication pr o cedure only involv es “s omething you hav e”: any one holding your passp or t can log in to your machine. Y ou can strengthen the pro- cedure by requir ing a usual pas s word, or even a biometric ch eck based on a compariso n of facial images (a freshly taken one, and the one o n the chip). Y ou may also wish to use your e-pass p o rt to sig n do cuments and emails using the embedded priv a te key for Active Authentication. This is not s uch a go o d idea, for tw o rea sons. First of all, the signature is obtained by exploiting the challenge- resp onse mechanism for another purp ose. Such interference should be av o ided, bec ause a challenge-resp ons e at a bo rder ins p ectio n co uld then b e misused to trick you into signing a certain do cument. Secondly , proving your identit y after signing r equires publication of your MRZ, together with the s e curity o b ject of your pas sp ort-chip (which is integrit y- protected b y a signature of the do cument signer): this o b ject couples the public key (for your signature) to identif ying information such as your name. But relea sing the MRZ a llows everyone to acces s your passp ort, through Basic Access Control. The underlying pro blem is that the e -passp ort was not designed with a n embedded useful certificate (such as X.50 9) for the holder. Once there is a n infrastruc tur e for biometric verification, it b ecomes na tural to ask : wh y not use it for iden tification as well? People may lo ose (willing ly or un willingly) their passp o r t, or may apply fo r multiple copies , p oss ibly un- der different names. Indeed, the governmen t o f the Nether lands is prepar ing legislation [ 1 , 2 ] to set up a central database with bio metric information, in o r- der to “ increase the effectiveness of national iden tification laws”. Such a central database g o es b eyond what is required by Euro pe a n dir ectives. The p ossibility o f biometric identification of the entire (passp or t-holding) po pulation involv es a change of p ower bala nce b etw een states and their citizens. Consent or co o pe ration is then no lo nger needed fo r identification. T r acing and tracking of individuals b eco mes p ossible o n a sca le that we hav e no t seen b efore. Assuming the biometric passp ort leads to a reliable infr a structure for verifica- tion and identification of individuals , the so cietal press ure w ill certainly increa se to use it in v arious other sector s tha n just b order insp ection. Such applicatio ns are not foreseen—or cov er ed by—Europ ean reg ulations. Interested pa rties are po lice and intelligence forces, banks and credit car d companies, so cial security organis ations, car rental firms, cas ino s, etc. Where do we dr aw the line, if any? W e see tha t the in tr o duction of the new e-passp o r t is not only a la rge tech- nical and o rganisa tional challenge, but also a s o cietal one. Governmen ts are im- plicitly asking for a c c eptance of this new technology . This acc eptance que s tion is not so explicit, but is cer tainly ther e. If some p olitica l action g roup makes a strong public cas e a gainst the e-pass p o rt, and mana ges to co nvince a la rge part of the p opula tion to immediately destroy the em bedded chip after issuance—for instance b y putting the passp ort in a microw ave—the whole enterprise will fail. The interesting p oint is that individua ls do hav e decisive p ow er over the use of the chip in their e-pas sp ort. Even strong er, such a p o litical action gr oup may decide to build disr uptive eq uipmen t that can destroy the RFID-chips from some distance, s o that passp orts a re destroyed without the holder knowing (immedi- 12 Ho ep man et al. ately). T o counter suc h mo vemen ts, g ov er nments may try to ma ke it sufficiently unattractive o r even imp ossible to cro ss b orders for trav elle rs without a func- tioning passp o r t. This is only p ossible, how ever, if the num b ers o f br oken chips is r e latively low. And in any case, it will not improve p opularity of the scheme to b egin with. 7 Iden tity Managemen t Issues Ident it y mana g ement (IM) is ab o ut “rules-4 -roles” : regula tion o f identification, authentication and authorisa tion in and b etw een organisa tions. The new e- passp ort is part of IM by states. It forms an iden tification and authentication mechanism that is forced up on citizens, pr imarily fo r in ternational mov ement, but also for internal purp oses . Ident ification a nd authent ication in everyday life is a nego tiation pr o cess. When a stra ng er in the street asks for your biometric data, you will refuse. But you may e ngage in a conv ersation, discover m utual interests, and exchange busi- ness ca rds or phone num b ers. Upo n a next contact more iden tifying infor mation may be released, po ssibly leading to a gra dual buildup o f trust. The e-pa ssp ort, in contrast, pr ovides a rig id format. In certain situations it forms an ov erkill, for instance when you just need to prove that you a re over eighteen. When IM g o es digital a nd b ecomes formalised o ne would like to have more flexible mechanisms, with individual co ntrol via p er sonal p o licies. In the future we may ex pe c t to b e ca r rying identit y to kens that flexibly r eact to the environmen t. Three basic rules for such systems ar e : – The environment sho uld authenticate itself first. F or instance, when the en- vironment can prove to b e my home, my p olicy allows my to ken to r elease m uch p erso nal info r mation, for instance ab out my music preference or hea lth. – Authen ticatio n should b e p oss ible in small p ortions, for instance via cer tifi- cates or credentials saying “this p ers o n is ov e r eighteen”, with a sig nature provided by a relev ant authority . – Automatic re cognition o f individuals, for instance via an implant ed RFID chip that br oadcasts your p ersona l (so cial security) num b er, is excluded. Priv acy is impo rtant for p erso nal security—and not, a s to o o ften stated, only an imp ediment to public secur it y . 8 Ev alua tion of Security Goals In Sect. 2 we hav e for mulated three se curity go a ls that w e consider r easona ble . In this section we ev aluate whether the curr ent system meets these go als. R e aders should identify themselves first In the usual sens e of “authenticated” o r “trusted” readers, this goal is not r eached. F or instance, we managed to write our own terminal a pplication that retrieves the public infor ma tion like the facial image from the chip. And our reader is not c onsidered trusted. The implemented Crossing Borders 13 BAC proto co l o nly assur es that the reader has knowledge of the MRZ on the passp ort. In the Europ ean implementation of E AC the reader must authenticate itself a nd hence this go al is mor e or less met for the information marked a s sensitive, but weaknesses exist (see Sect. 5 ). Consent by the p assp ort holders Theor etically this goal is reached. By use of BAC any terminal that tries to read informa tion fir st needs to r ead the MRZ information printed on the ins ide of the passp o rt. Hence the holder must give his consent for the transa ction by op ening his passp ort. How e ver, as we hav e seen in Sect. 4.2 some subliminal channels exist that may leak infor mation a bo ut the card even b efore BAC has b een applied or in o ther words even b efore the holder has given his c onsent. Pr o of of inte grity and authenticity The integrit y part of this goa l is rea ched by the secure messa ging system, which is applied fo r a ll communication after BAC. As we hav e seen in Sect. 4 b oth commands and resp onses are encrypted and augmented with a messag e authentication co de to provide in tegrity a nd confidentialit y . Authenticit y of the informa tio n is guar anteed through Passive Authen tica tion (see Sect. 4 ) 9 e-P assp ort v2 Un til now we hav e discussed se veral iss ues with the security and priv acy protec- tion of the curr ent prop osed standa r ds for bio metric passp or ts, from b oth ICA O and, in particula r , the E U. W e hav e a rgued that protectio n mechanisms s ho uld be improv ed. How ever, improvemen ts to such standa rds ar e at b e st incremental, and do not usually challenge the primary desig n decisio ns. In fact, such funda- men tal changes would certainly b e backw a rds inco mpatible, a nd require a totally new standa rd. I n our o pinion, more fundamen ta l changes ar e required to really provide str ong secur ity a nd pro p er priv acy protection to the new generatio n of e-passp or ts. 9.1 Av oidi ng Contac tless Cards The mos t fundamental change is to recons ider the choice for a wir eless commu- nication interface b etw ee n the chip in the pa ssp ort and the terminal at bo rder insp e ction. Using a wireless interface makes skimming attacks p ossible. It is ex- actly the fear of this po ssibility that has s parked a huge controv ersy ov er the current e-passp or t prop osa ls. Initially , the US passp o r ts would not even imple- men t Basic Access Control. Now they a re even considering to include metal shields in the co ver pages of the pass po rt to function as a F a r aday ca ge, to ph ysically disable the wireless communication link. But all Basic Access Control rea lly is , is a very elab ora te wa y to a chieve exactly the s ame as what is a chieved when inser ting a smart card with c o ntacts int o the slot of a reader: namely that the ho lder of the pass p o rt allows the 14 Ho ep man et al. owner of the terminal to read the data on the chip. Then, why no t simply use smart ca r ds with contacts for the new e-passp o r t? The main a rguments ag a inst this have b een the form-facto r of the passp or t, and the need for a s ufficient bandwidth to quickly tr ansmit the biometric data from the ca rd to the ter minal. How ever, identit y cards and drivers licenses with dimensions similar to credit cards (ID-1) are alr eady under considera tion. And bandwidth co ncerns are no longer an iss ue either. Many smart card suppliers alr eady sell smar t car ds with int egrated USB 1 .1 interfaces that allow for a muc h higher throughput, using the orig inal [ 12 ] ISO contact mo dule found on the ca rd, a nd standar dis ation for this approach is underwa y [ 1 3 ]. Such a s olution would ta ke aw ay all worries asso ciated with using a wirele ss chip, and would keep the e- passp ort clear of all discussions surr o unding the (p erceived) priv acy iss ue s with RFID. 9.2 On-line T ermi nal Authent ication Once a co nnection b etw een passp ort and terminal is established, a decision has to be made regar ding the access rights of the terminal a nd to deter mine which data on the passp o rt it is allow e d to rea d. Cur r ent EU prop o sals for extended access control a r e found wan ting: stolen terminals ca nnot be revoked, and the shallow, rigid cer tificate hierar ch y prop ose d to r egulate access do es no t allow for fle x ible and/or dynamic access con tro l p olicies (see Sect. 5 ). The EU approach was chosen to allow for off-line, mo bile ter minals, like those tha t ar e used by mobile bo rder insp ectio n units. B ut clearly such mobile terminals can b e co nnected to the netw o rk ov e r a wireless link, if only through GPRS, which is the standard on ce ll phones these days. If we assume that terminals are always connected to the netw ork, w e can use on-line terminal authentication. The gener a l idea is then the following. Each terminal owns a priv ate/public key pair . Each terminal is used fo r a particular applicatio n. This applicatio n is enco ded in a certifica te C AA that con- tains the public key K T A of the terminal, and whic h is signed by the applicatio n authority AA . Access rig hts ar e as s o ciated with a pplication. E a ch co unt ry sto r es, for ea ch applicatio n autho r ity that it wishes to r ecognise, the acces s rig hts for that applica tion. These access rig hts ar e stored in the back o ffice. The back o ffice also stores the public keys of all terminals that hav e b een r evok ed. On-line terminal authen tication then pro ceeds as follows. First, the terminal sends the certifica te C AA (containing its public key K T A ) to the chip. The chip and the terminal per form a challenge-resp ons e proto co l in which the terminal prov es to the chip that it owns the priv ate key corresp o nding to K T A . This establishes the identit y o f the terminal. Next, the chip sets up a n authenticated channel b etw een itself and the back o ffice of the issuing country . It can do so using a country cer tificate that is stor ed in the chip dur ing p er sonalisa tio n. The channel s ho uld not be vulner able to replay attacks. It sends C AA (and K T A ) to the back-office. Ther e, C AA is verified against the known a pplication authorities (this v alidates that K T A was certified b y suc h an a uthority) and K T A is chec ked against the list of a ll revoked ter minals. If these chec ks pa ss, the access rights for AA a re sent back to the chip. If no t, then the empty set (i.e., no access rig hts) is Crossing Borders 15 sent back to the chip. The chip interprets the access rig hts it r eceives a nd grants access to the terminal a ccordingly . Beca use the channel is authent ic a nd do es not allow r eplay attacks, the access rights received by the chip corres po nd to the certificate it sent to the back office. With on-line terminal authentication, terminals can b e r e vok ed in re a l-time: as so on a s they are marked as revoked in the back offices of the iss uing country , no pa s sp ort of that country will allow that terminal access to its da ta . Also, the a c cess p ermissions ca n b e changed dyna mically , and can even be based o n the exac t time the request was made, or on the sp ecific usage pattern of the passp ort. The gener al idea can b e r efined to also allow r evocation of termina ls by the countries that mana ge them, instead of requiring them to inform all other countries that a particula r terminal should b e revoked (b ecause it was stolen, for instance). Also, more levels o f c ertificates can be intro duce d, to ma ke management of access rights easier. 9.3 Other Improv emen ts In Sect. 3 we have seen that r eal pictures are stored on the chip. With an immediate c o nsequence tha t who ever is able to re trieve these images fr om the chip, has access to g o o d biometr ic data , which he can use for ident it y theft. Using templates that work like a one-way function, it will b e p ossible to chec k whether the template on the chip matches the template der ived fro m the pe r son who is claiming to b e the holder o f the passp or t. This lea king of rea l biometric da ta may not s eem such a big dea l in a time whe r e many pictures are published on the Int ernet. The p oint here is that these pictures for the passp or ts a r e taken under go o d conditions and hence provides highly a c curate biometr ic infor mation. The entrop y-related off-line attacks discussed in Sect. 4.1 a re p oss ible b ecause a g uess of MRZ-information dir ectly lea ds to all keys used in a communication session. These keys ca n b e chec ked against a transc r ipt o f that session to ver- ify the gue s s. The situation is similar to many password-based a uthent ication and ses sion-setup proto co ls . Encrypted key exchange pr oto cols, discov ered b y Bellovin and Merritt [ 4 ], do not suffer fro m this problem. T he r e a low entropy password is used to exchange a high en tropy secret that c annot efficient ly b e guessed using an off-line attack 3 . Using encrypted key exchange pr oto cols for basic access control would strengthen the secur ity of the pass po rt c o nsiderably . In Sect. 6 we have seen that it will be inevita ble tha t other applications wan t to use the infra structure av ailable on the chip for other purp oses than the original ones. In the cur rent s ystem it is alrea dy p os sible to sign things with a priv ate key , but this causes some unw a nted side effects as a lready describ ed in Sect. 6 . In order to pr even t this the standards s hould b e rewr itten in suc h a wa y that at least these additiona l functions can b e us e d and pr e fer ably in a disjoint setting from the bo rder inspec tion functions. A p oss ible implementation for this could b e to have an X.509 certificate included with a public key that has nothing to do with the MRZ or other information needed for the b or de r insp ectio n tasks. 3 Of course on-line attacks where all p ossible passw ords are tried one by one can never b e preven t ed. 16 Ho ep man et al. References [1] Kamerstuk I I 2004/2005 , 25 764, nr. 26. (Official communication of t he Dutch parliamen t) . [2] Kamerstuk I I 2004/2005, 29 754, n r. 5. (Official communication of the D utch parliamen t) . [3] Y early rep ort on algorithms and keysizes (2005). T echnical rep ort, IST-2002- 507932 ECR YPT, January 2006. D.SP A.10 Rev 2005-0.2. [4] Stev en M. Bello v in and Michael Merritt. Encrypted key exchange: Passw ord- based proto cols secure against d ictionary attacks. In IEEE Se curity & Privacy , pages 72–84, Oakland, CA, US A, Ma y 1992. IEEE. [5] BSI. Adv anced security mechanisms for machine readable tra vel do cuments – extended access control (eac). T ec hnical Rep ort TR-03110, BSI, Bonn, Germany , 2006. [6] Proposal for a council regulation amending regulation (ec) no 1683/9 5 laying do wn a uniform format for visas. OJ C , 51:219–22 0, F ebruary 26 2002. [7] Proposal for a council regulation on standards for securit y features and biometrics in eu citizens’ passp orts. OJ C , 98:39, April 23 2004. [8] Ja ap-Henk Ho epman and Bart Jacobs. E-p assp orts without the big picture. eGov Monitor , F ebru ary 20 2006. http://www .egovmoni tor.com/node/4716 . [9] ICA O. Machine Readable T ra vel Do cuments. T ec hnical rep ort, I CAO, 2003. 5th edition. [10] ICA O. Developmen t of a logical data structure - LDS for optional capacity ex- pansion technologi es, revision 1.7. T ec hnical rep ort, ICAO, May 2004. [11] ICA O. PKI for machine readable trav el do cuments offering ICC read- only access, versi on - 1.1. T ec h nical rep ort, Oct 2004. [12] ISO 7816. ISO/IEC 7816 Identification cards – Integrated circuit(s) cards with conta cts. T echnical report, IS O JTC 1/SC 17. [13] ISO 7816-12. I SO/IEC 7816 Identification cards – I ntegra ted circuit(s) cards – Part 12: Cards with contacts – U SB electrical interface and op erating pro cedures. T echnical report, I SO JTC 1/SC 17. [14] A. Juels, D. Molnar, and D. W agner. Security issues in e-passp orts. In Se- cur eComm 2005 , 2005. [15] Ga urav S. Kc and Paul A. K arger. Security and priv acy issues in machine read- able trav el do cuments (MR TDs). IBM T ec hn ical Rep ort (RC 23575), IBM T. J. W atson Research Labs, April 2005. [16] Dennis K ¨ ugler. S ecu rit y m echanisms of the biometrically enhanced (eu) pass- p ort. Presentation at the Security in Perv asiv e Computing conference, Boppard, German y , April 2005. www.spc- conf.org/ 2005/slide s/SPC_Passport.pdf . [17] J .L. Massey . Guessing and entropy . In Pr o c. 1994 IEEE I nternational Symp osium on Inf ormation T he ory , page 204, 1994. [18] National Institute of Stand ards and T echnology . R ecommendation for key man- agemen t . T ec hnical Rep ort S p ecial Publication 800-57 Draft, NIST, Au gust 2005. [19] Ev aluation rep ort biometrics trial 2B or not 2B, 2005. www.europe anbiometr ics.info/ images/resources/88_630_file.pdf .
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment