Coding and Decoding for the Dynamic Decode and Forward Relay Protocol
We study the Dynamic Decode and Forward (DDF) protocol for a single half-duplex relay, single-antenna channel with quasi-static fading. The DDF protocol is well-known and has been analyzed in terms of the Diversity-Multiplexing Tradeoff (DMT) in the …
Authors: K. Raj Kumar, Giuseppe Caire
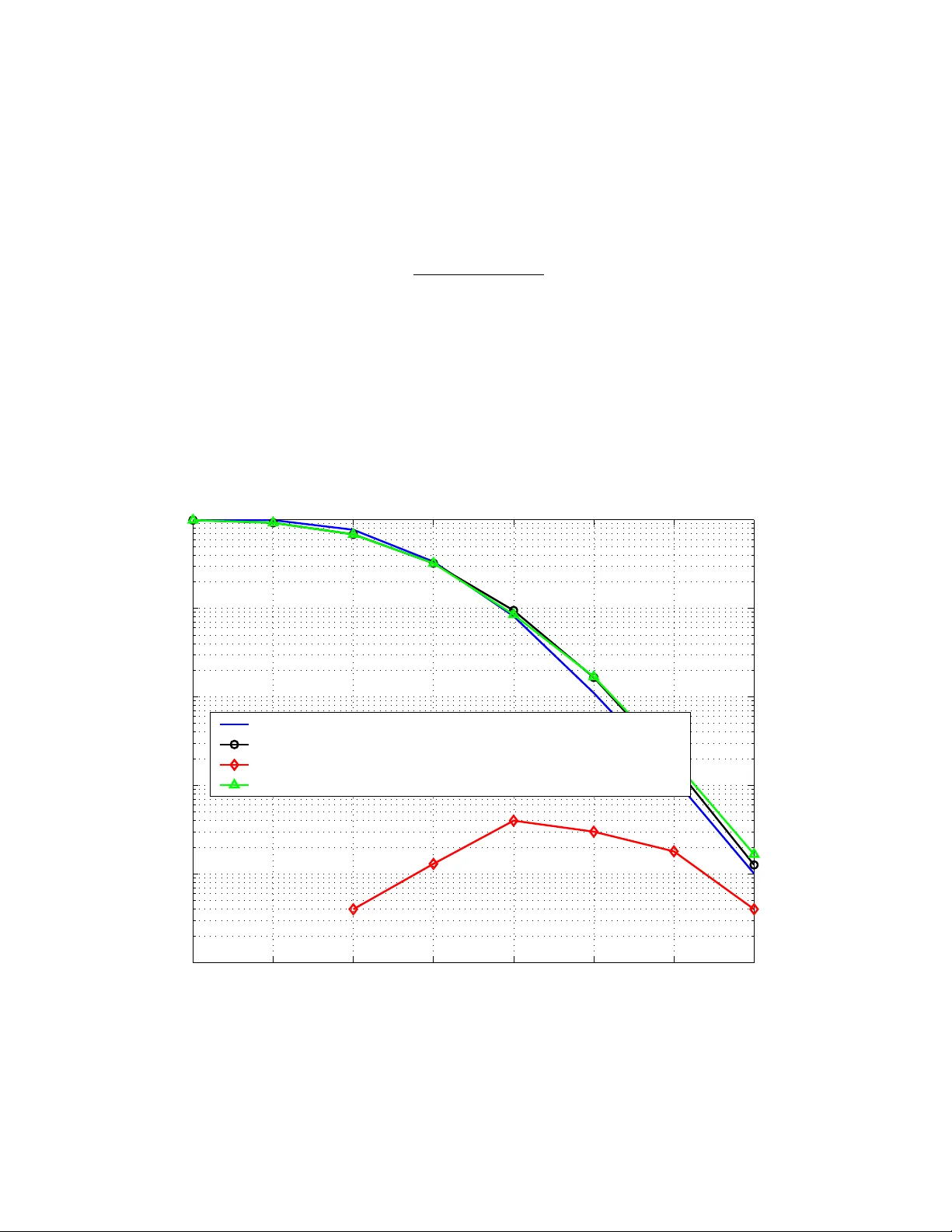
SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 1 Coding and Decoding for the Dynamic Decode and F orward Relay Protocol K. Raj Kumar and Giuseppe Caire Abstract W e study the Dynamic Decode and Forward (DDF) protocol for a single half-duplex relay , single- antenna channel with quasi-static fading. The DDF protocol is well-known and has been analyzed in terms of the Diversity-Multiple xing T radeoff (DMT) in the infinite block length limit. W e characterize the finite block length DMT and give new explicit code constructions. The finite block length analysis illuminates a few key aspects that have been ne glected in the previous literature: 1) we show that one dominating cause of degradation with respect to the infinite block length regime is the ev ent of decoding error at the relay; 2) we explicitly take into account the fact that the destination does not generally know a priori the relay decision time at which the relay switches from listening to transmit mode. Both the above problems can be tackled by a careful design of the decoding algorithm. In particular, we introduce a decision rejection criterion at the relay based on F orney’ s decision rule (a v ariant of the Neyman-Pearson rule), such that the relay triggers transmission only when its decision is reliable. Also, we show that a receiv er based on the Generalized Likelihood Ratio T est rule that jointly decodes the relay decision time and the information message achieves the optimal DMT . Our results show that no cyclic redundanc y check (CRC) for error detection or additional protocol overhead to communicate the decision time are needed for DDF . Finally , we in vestigate the use of minimum mean squared error generalized decision feedback equalizer (MMSE-GDFE) lattice decoding at both the relay and the destination, and show that it provides near optimal performance at moderate complexity . The authors are with the Department of Electrical Engineering - Systems, University of Southern California, Los Angeles, CA 90089, USA ( { rkkrishn,caire } @usc.edu ). The material in this paper was presented in part at the forty-fifth annual Allerton conference on Communication, Control, and Computing, Illinois, Sept. 26 - 28, 2007. This work was partially supported by NSF Grant No. CCF-0635326 and by the Oakley fellowship from the Graduate School at the Uni versity of Southern California. September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 2 I . I N T RO D U C T I O N Employing multiple antennas at the transmitter and the receiv er of wireless communications is known to provide significant benefits in terms of both throughput (multiplexing gain) and reliability (div ersity gain) (see [13] and references therein). When physical constraints limit the number of antennas that can be installed on a single wireless device (e.g., small sensors in sensor networks), the usage of cooperativ e wireless relay protocols is a promising alternati ve strategy . In these protocols, two or more terminals cooperate in order to mimic a super -user with multiple antennas. The relay channel was introduced by van der Meulen [2] and was studied in detail by Cov er and El Gamal [3], who characterized the capacity for the discrete memoryless as well as for the Gaussian de graded cases. The relay channel with fading was e xamined by Sendonaris et al., [4], where an achie vable rate re gion was pro vided. In the case of slo w fading, the outage behavior of half-duple x wireless relay channels was studied by Laneman et al., [5], and simple cooperative diversity protocols for signalling across these channels (such as amplify and forwar d and decode and forwar d ) were introduced. In [15], Azarian et al. used the diversity-multiplexing tradeoff (DMT) formulation of [13] to study the outage behavior of slowly-f ading relay channels in the high-SNR regime, and also introduced new classes of protocols such as the non-orthogonal amplify and forwar d (NAF) and the dynamic decode and forwar d (DDF). An impro ved DDF protocol based on code superposition was later proposed in [30]. The DDF protocol for the single relay case was subsequently studied in [16], where simplified variants of the protocol were introduced and some code design issues were addressed. Code design for the DDF protocol is also addressed in the recent contrib ution [29]. The present paper also focuses on the DDF protocol for the half-duplex, single relay single-antenna case. W ith respect to [16] and [29], we analyze explicitly the achiev able DMT of practical codes with finite block length and propose a simple DMT optimal code construction that makes use of approximately uni versal codes for the parallel channel and of the Alamouti code. Approximately univ ersal codes for the parallel channel may be obtained either from using a QAM base alphabet and a suitable unitary precoding matrix (lattice codes) or from permutation codes deriv ed from univ ersally decodable matrices (UDM) [21], [22]. W e treat both cases and giv e construction examples and comparisons. Remarkably , our codes perform very close to the outage probability and hav e generally lower decoding complexity than those pre viously proposed. Furthermore, we discuss two often ne glected issues: 1) the effect of decoding errors at the relay , and ho w to mitigate it; 2) the fact that the destination does not generally know a priori the relay decision September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 3 time. In order to tackle 1), we introduce a decision rejection criterion at the relay , such that the relay triggers transmission only when its decision is reliable. W e show that the Forney’ s decision rule (a v ariant of Neyman-Pearson rule) yields almost optimal performance with practical finite length codes, while previously proposed options suffer from significant degradation. In order to tackle 2), we treat the channel “seen at destination” as a compound channel, where each compound member corresponds to a different relay decision time. W e prov e that a receiver based on the Generalized Likelihood Ratio T est (GLR T) rule, that jointly decodes the relay decision time and the information message, achiev es the optimal DMT . W e also show that a simpler scheme that performs separate detection of the relay decision time, by ignoring the structure of the coded signal and treating it as random, is generally suboptimal and it becomes optimal only in the limit of infinite block length. As an aside, our results sho w that no side information channel or additional protocol ov erhead is needed in order to inform the destination about the relay decision time. This may yield to much simplified actual protocol design for the DDF scheme, at the cost of an augmented decoder at the destination. W ith the lattice codes advocated in this paper , the decoder at the relay has to solve a closest lattice point problem with a rank deficient lattice matrix. It is well-known that standard sphere decoding [6], [7] yields exponential comple xity in this case. In order to address this problem (again, often neglected in the current literature) we adv ocate the use of the minimum mean squared error generalized decision feedback equalizer (MMSE-GDFE) lattice decoder of [32], [34]. V ia simulation of the performance of our explicitly constructed codes, we demonstrate that this lattice decoder is able to provide near optimal performance at moderate complexity . In Section II, we introduce the system model we work with and revie w relev ant previous results. Section III presents the main result of the present paper , a characterization of the DMT of the DDF protocol for finite block length. Explicit code constructions that achie ve this DMT are provided in Section IV, and methods to enable error detection at the relay and lo w complexity decoding of these codes are also dealt with. I I . P RO B L E M D E FI N I T I O N A N D B AC K G RO U N D A. System model W e consider the single relay channel shown in Fig. 1, where S, R and D denote the source, relay and destination, and h, g 1 and g 2 denote the fading coefficients between the source-relay , source-destination and relay-destination terminals, respectiv ely . September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 4 C o d e D e s i g n f o r t h e D y n a m i c D e c o d e a n d F o r w a r d R e l a y P r o t o c o l K . R a j K u m a r D e p a r t m e n t o f E l e c t r i c a l E n g i n e e r i n g - S y s t e m s U n i v e r s i t y o f S o u t h e r n C a l i f o r n i a L o s A n g e l e s , C A 9 0 0 8 9 , U S A E m a i l : r k k r i s h n @ u s c . e d u G i u s e p p e C a i r e D e p a r t m e n t o f E l e c t r i c a l E n g i n e e r i n g - S y s t e m s U n i v e r s i t y o f S o u t h e r n C a l i f o r n i a L o s A n g e l e s , C A 9 0 0 8 9 , U S A E m a i l : c a i r e @ u s c . e d u A b s t r a c t — I . I N T R O D U C T I O N E m p l o y i n g m u l t i p l e a n t e n n a s a t t h e t r a n s m i t t e r a n d t h e r e - c e i v e r o f w i r e l e s s c o m m u n i c a t i o n s y s t e m s i s k n o w n t o p r o v i d e s i g n i fi c a n t b e n e fi t s i n t e r m s o f b o t h t h r o u g h p u t ( m u l t i p l e x i n g g a i n ) a n d r e l i a b i l i t y ( d i v e r s i t y g a i n ) [ 1 ] , [ 2 ] , [ 3 ] , [ 1 2 ] . H o w - e v e r , p h y s i c a l c o n s t r a i n t s l i m i t t h e n u m b e r o f a n t e n n a s t h a t c a n b e d e p l o y e d o n w i r e l e s s d e v i c e s s u c h a s m o b i l e p h o n e s . I n r e c e n t y e a r s , t h e u s a g e o f w i r e l e s s r e l a y c h a n n e l s w h e r e m o b i l e u s e r s c o o p e r a t e w i t h e a c h o t h e r h a s b e e n p r o p o s e d t o p r o v i d e a d d i t i o n a l d i v e r s i t y , k n o w n a s c o o p e r a t i v e d i v e r s i t y i n t h e l i t e r a t u r e . T h e r e l a y c h a n n e l w a s i n t r o d u c e d b y v a n d e r M e u l e n [ 4 ] , [ 5 ] , w h o p r o v i d e d i n n e r a n d o u t e r b o u n d s f o r t h e c a p a c i t y o f t h e r e l a y c h a n n e l . T h e r e l a y c h a n n e l w a s s t u d i e d i n d e t a i l b y C o v e r a n d E l G a m a l [ 6 ] , w h o c h a r a c t e r i z e d t h e c a p a c i t y o f t h e d i s c r e t e m e m o r y l e s s d e g r a d e d r e l a y c h a n n e l a n d t h a t o f t h e G a u s s i a n d e g r a d e d r e l a y c h a n n e l . T h e r e l a y c h a n n e l w i t h f a d i n g w a s e x a m i n e d b y S e n d o n a r i s e t a l . [ 7 ] , w h e r e a n a c h i e v a b l e r a t e r e g i o n w a s p r o v i d e d . T h e o u t a g e b e h a v i o r o f h a l f - d u p l e x w i r e l e s s r e l a y c h a n n e l s w a s s t u d i e d b y L a n e m a n e t a l . [ 8 ] , a n d s i m p l e c o o p e r a t i v e d i v e r s i t y p r o t o c o l s f o r s i g n a l l i n g a c r o s s t h e s e c h a n n e l s ( s u c h a s a m p l i f y a n d f o r w a r d a n d d e c o d e a n d f o r w a r d ) w e r e i n t r o d u c e d . I n [ 1 4 ] , A z a r i a n e t a l . e m p l o y t h e f o r m u l a t i o n o f t h e d i v e r s i t y - m u l t i p l e x i n g t r a d e o f f ( D M T ) [ 1 2 ] t o s t u d y t h e o u t a g e b e h a v i o r o f f a d i n g r e l a y c h a n n e l s , a n d a l s o i n t r o d u c e t h e c l a s s o f n o n - o r t h o g o n a l a m p l i f y a n d f o r w a r d ( N A F ) a n d d y n a m i c d e c o d e a n d f o r w a r d ( D D F ) p r o t o c o l s . T h e D D F p r o t o c o l f o r t h e s i n g l e r e l a y c a s e w a s s u b s e q u e n t l y s t u d i e d i n [ 1 5 ] , w h e r e s i m p l i fi e d v a r i a n t s o f t h e p r o t o c o l w e r e i n t r o d u c e d a n d s o m e c o d e d e s i g n i s s u e s w e r e a d d r e s s e d . T h e w o r k i n t h e p r e s e n t p a p e r a l s o f o c u s e s o n v a r i a n t s o f t h e D D F p r o t o c o l f o r t h e s i n g l e r e l a y c h a n n e l , w e w i l l i n t r o d u c e t h e f r a m e w o r k a n d t h e n o t a t i o n b e f o r e g o i n g t h r o u g h t h e d e t a i l s . A . S y s t e m m o d e l W e w o r k w i t h t h e s i n g l e r e l a y c h a n n e l s h o w n i n F i g . 1 , w h e r e S , R a n d D d e n o t e s t h e s o u r c e , r e l a y a n d d e s t i n a t i o n . F u r t h e r , l e t h , g 1 a n d g 2 d e n o t e t h e f a d i n g c o e f fi c i e n t s b e t w e e n F i g . 1 . T h e s i n g l e r e l a y f a d i n g c h a n n e l t h e s o u r c e - r e l a y , s o u r c e - d e s t i n a t i o n a n d r e l a y - d e s t i n a t i o n t e r - m i n a l s . W e a s s u m e t h a t t h e f a d i n g c o e f fi c i e n t s a r e d r a w n f r o m a n e n s e m b l e o f i . i . d . C N ( 0 , 1 ) r a n d o m v a r i a b l e s , c o r r e s p o n d i n g t o i . i . d . R a y l e i g h f a d i n g . W e a l s o a s s u m e t h a t t h e c h a n n e l s a r e q u a s i - s t a t i c , i . e . , t h e f a d i n g c o e f fi c i e n t s r e m a i n c o n s t a n t f o r a d u r a t i o n o f M T c h a n n e l u s e s a f t e r w h i c h t h e y c h a n g e a t r a n d o m i n a c c o r d a n c e w i t h t h e s p e c i fi e d d i s t r i b u t i o n . T h e s i g n a l r e c e i v e d a t t h e d e s t i n a t i o n a t t h e k t h s y m b o l i n s t a n t c a n b e m o d e l e d a s y k = g 1 x s , k + g 2 x r , k + w k , k = 1 , 2 , . . . , M T , w h e r e x s = [ x s , 1 · · · x s , M T ] T i s t h e c o d e w o r d t r a n s m i t t e d b y t h e s o u r c e ( t h a t w e a s s u m e t o b e d r a w n f r o m a c o d e X s ) , x r = [ x r , 1 · · · x r , M T ] T a r e t h e c o d e s y m b o l s t r a n s m i t t e d b y t h e r e l a y ( w h e r e t h e c o d e w o r d s x r a r e d r a w n f r o m a c o d e X r 1 ) , a n d w k i s t h e a d d i t i v e n o i s e a t t h e d e s t i n a t i o n . W e w i l l a s s u m e t h a t w = [ w 1 · · · w M T ] T i s d i s t r i b u t e d a s i . i . d . C N ( 0 , σ 2 w I ) . T h e r e c e i v e d s i g n a l a t t h e r e l a y y r = [ y r , 1 · · · y r , M T ] c a n b e w r i t t e n a s y r , k = h x s , k + v k , k = 1 , . . . , M T , w h e r e t h e a d d i t i v e n o i s e a t t h e r e l a y i s a s s u m e d t o b e i . i . d . C N ( 0 , σ 2 v ) . W e i m p o s e a p e r - s y m b o l p o w e r c o n s t r a i n t o n t h e 1 N o t e t h a t t h e l e n g t h o f t h e c o d e X r d e p e n d s o n w h e n t h e r e l a y c h o o s e s t o s t a r t t r a n s m i t t i n g , w h i c h d e p e n d s o n t h e p a r t i c u l a r p r o t o c o l c h o s e n . A l t e r - n a t i v e l y , o n e c o u l d c o n s i d e r X r t o b e o f t h e s a m e l e n g t h o f X s ; i n t h i s c a s e , t h e r e l a y m a y c h o o s e t o i g n o r e t h e fi r s t f e w c o m p o n e n t s o f t h e c o d e w o r d s o f X r a n d t r a n s m i t o n l y t h e r e s t , d e p e n d i n g o n w h e n i t c h o o s e s t o t r a n s m i t . W h i c h n o t a t i o n o n e c h o o s e s t o a d o p t i s a m a t t e r o f c o n v e n i e n c e , t h e a n a l y s i s i s t h e s a m e e i t h e r w a y . Fig. 1. The single-antenna single relay fading channel. The channel f ading coef ficients are i.i.d. CN (0 , 1) random v ariables, corresponding to i.i.d. Rayleigh fading. Follo wing the standard outage setting [5], [15], [13], we assume that the channel coherence time is considerably larger than the allowed decoding delay . In voking a time-scale decomposition argument (see for example [18]) this setting is modeled by the so-called quasi-static fading channel, where the channel coef ficients are random but remain constant over the whole duration of a codew ord, although the latter can be very large. W e consider slotted transmission where a source codeword spans M slots of length T symbols each, resulting in a total block length of M T . The relay operates in half-duplex mode. In decode and forward protocols, the block of length M T symbols is split into two phases. In the first phase the relay is in listening mode and receives the signal from the source. At a certain instant, referred to as the decision time in the following, the relay tries to decode the source information message. In the second phase, from the decision time to the end of the block, the relay switches to transmit mode and sends symbols to help the destination decode the source message. The DDF protocol is characterized by the fact that the decision time is not fixed a priori. On the contrary , the relay decides when to decode and switch to transmit mode depending on the channel coef ficient h and the received signal. Therefore, the decision time is a random variable M . W ithout loss of generality , we restrict the decision time to coincide with the end of a slot 1 , i.e., M takes on values in the set { 1 , 2 , . . . , M } , where M = M corresponds to the case where the relay does not help the destination. During phase 1 (listening phase) the signal recei ved by the relay is y r,k = hx s,k + v k , k = 1 , 2 , . . . , M T , (1) 1 Notice that T is a design parameter . Letting T = 1 provides an unrestricted decision time. In this way , there is no loss of generality in this assumption. September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 5 and the signal receiv ed by the destination is y k = g 1 x s,k + w k , k = 1 , 2 , . . . , M T . (2) During phase 2 (relay transmit phase), the signal recei ved by the destination is y k = g 1 x s,k + g 2 x r,k + w k , k = M T + 1 , M T + 2 , . . . , M T . (3) Here, x s = [ x s, 1 · · · x s,M T ] T denotes the source codeword, drawn from a code X s ⊂ C M T of rate R bits per symbol. W ithout loss of generality , we may assume that the symbols x r,k transmitted by the relay are from an auxiliary code X r ⊂ C M T with rate R and block length M T , but only the last ( M − M ) T symbols of a code word are ef fectively transmitted in phase 2, while in phase 1 the relay transmitter is idle because of the half-duple x constraint. The noise at the relay and destination, denoted by v k ∼ CN (0 , σ 2 v ) and w k ∼ CN (0 , σ 2 w ) , form two white mutually independent sequences. W e impose the same per-symbol av erage power constraint for both the source and the relay , gi ven by E | x s,k | 2 , E | x r,k | 2 ≤ E , where E denotes the symbol energy , and define the SNRs of the S-D and the S-R links to be ρ = E /σ 2 w and ρ 0 = E /σ 2 v , respectiv ely . For later use, we introduce the follo wing notation: let y j i , y j r,i , x j s,i and x j r,i , each ∈ C ( j − i ) T , denote respecti vely the received signals at the destination and at the relay from symbol time iT + 1 to j T , the source transmit signal from time iT + 1 to j T and the relay transmit signal from time iT + 1 to j T , where the latter is assumed to be zero for all times k ≤ M T . The quantities w j i and v j i are defined similarly . B. Diversity-Multiplexing T radeof f A compact and con venient characterization of the tradeof f between rate and reliability of quasi-static fading channels in the high-SNR regime is provided by the DMT introduced in [13]. In this framew ork, rate and reliability are quantified in terms of the diversity gain d and spatial multiplexing gain r . A family of coding systems, each of which operates at SNR ρ with rate R ( ρ ) and error probability P e ( ρ ) , achie ves a point ( r , d ) on the DMT plane if lim ρ →∞ R ( ρ ) log ρ = r , lim ρ →∞ log P e ( ρ ) log ρ = − d. This latter relation is written as P e ( ρ ) . = ρ − d in the e xponential equality notation of [13]. September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 6 W e will use the DMT as our performance metric when we analyze cooperati ve div ersity protocols. It is clear that the DMT of the MIMO channel with one receiv e and two transmit antennas provides an upper bound to the performance of an y relay protocol for the channel of Fig. 1. This bound, kno wn as the transmit di versity bound [5], is gi ven by d tx.div .bd. ( r ) = 2(1 − r ) . The DMT of the DDF protocol, proposed and analyzed in [15], is given by d ∗ ( r ) = 2(1 − r ) , 0 ≤ r ≤ 1 2 (1 − r ) /r, 1 2 ≤ r ≤ 1 . (4) This result is obtained by analyzing the information outage probability with Gaussian inputs, and it is achie vable (e.g., by using a Gaussian random coding argument) in the limit of both M → ∞ and T → ∞ . The relay decision time is given by M = min M , M R log(1 + | h | 2 ρ 0 ) , (5) i.e., M is set to the minimum m = 1 , 2 , . . . , M − 1 such that the mutual information between x m s, 0 and y m r, 0 for fixed and known h , giv en by mT log (1 + | h | 2 ρ 0 ) , exceeds the number of information bits per message M T R . If such an m exists, the relay triggers the decoding of the whole information message and switches to the transmission mode. If no such m exists, then M = M and the relay remains silent. Both the limit of large M and T are necessary to achiev e the DDF DMT in (4). In fact, the normalized decision time M / M must con ver ge to a continuous random variable distrib uted in [0 , 1] and, for e very decision time M = m , the number of symbols mT received by the relay must be arbitrarily large, such that the decoding error ev ent coincides with the information outage error ev ent. In this way , the corresponding probability of decoding error is arbitrarily close to the information outage probability P log(1 + | h | 2 ρ 0 ) ≤ M R m , and the probability of undetected error (i.e., the relay accepts a wrong decision) is arbitrarily small. In brief, T → ∞ is necessary in order to fix the optimal decision time based only on the channel strength | h | 2 and be sure (with arbitrarily high probability) that the decoded message is the correct one. W e should also notice that, in the limit of T → ∞ , the outage probability does not depend on the kno wledge of h at the relay decoder and of ( g 1 , g 2 ) at the destination decoder (see for example [8]). On the other hand, a common assumption made in previous works is that the destination knows exactly the relay decision time M . In practice, this assumption requires some form of protocol to provide side September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 7 information to the destination. In the DMT analysis, one should pay great care to ensure that the error probability of such side information protocol does not dominate the decoding error probability , i.e., in designing any side information protocol we must ensure that its probability of error decreases not slower than ρ − d ∗ ( r ) . Practical code design for the DDF protocol considers finite, possibly very short, M and T . In the follo wing, we will make an explicit assumption of perfect receiv er channel state information (CSIR), that is relatively easy to acquire using pilot symbols and is a common assumption in the DMT analysis of ev en finite-length codes (see [13] and [18]). On the contrary , we explicitly address the fact that the destination does not know a priori the relay decision time M and tackle this problem by analyzing an augmented decoder based on the GLR T rule. C. Existing DDF code designs In [16], a variant of the DDF protocol is proposed where the relay code X r is such that the signal recei ved at the destination reduces to an Alamouti constellation [10]. W e will refer to this scheme as the “ Alamouti-DDF” scheme, and re view it briefly in the sequel since we make use of the same approach. W ith the Alamouti-DDF , assuming that the relay decodes correctly at the decision time M = m , the signal transmitted by the relay at time k is gi ven by [16] x r,k = x ∗ s,k +1 , k = mT + 1 , mT + 3 , . . . − x ∗ s,k − 1 , k = mT + 2 , mT + 4 , . . . , (6) which reduces the signal seen by the destination for mT + 1 ≤ k ≤ M T to an Alamouti constellation. Through linear processing of the received signal y M 0 , the destination obtains the sufficient statistics for decoding, giv en by ˜ y k = g 1 x s,k + w k , k = 1 , . . . , mT p | g 1 | 2 + | g 2 | 2 x s,k + ˜ w k , k = mT + 1 , . . . , M T , (7) where the statistics of ˜ w k are identical to those of w k . In this case, it is easy to see that the mutual information per symbol at the destination, for M = m and i.i.d. Gaussian inputs, is giv en by m M log 1 + | g 1 | 2 ρ + M − m M log 1 + ( | g 1 | 2 + | g 2 | 2 ) ρ (8) and coincides with that of the original DDF scheme defined by (2) and (3), when the codebooks X s and X r are also drawn independently from an i.i.d. Gaussian ensemble. Hence, the Alamouti-DDF modification entails no loss in DMT compared to the original DDF protocol [16]. September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 8 I I I . D M T O F T H E D D F P R OT O C O L W I T H FI N I T E L E N G T H In this section, we characterize the achie v able DMT of the DDF protocol with finite M and T . First, we find an upper bound on the DMT by letting T → ∞ , assuming that the destination has perfect knowledge of the relay decision time M , and using outage probability . Then, we shall analyze the performance of Gaussian random codes with finite length, with the assumption that the destination has no knowledge of M , and find a lo wer bound that matches the upper bound. Since for i.i.d. Gaussian inputs the Alamouti-DDF yields the same mutual information as DDF , as far as outage probability is concerned we can refer to the channel defined in (7). This is a set of parallel channels for m = 1 , . . . , M , with dependent channel gains. In particular , there are two types of sub- channels: one representing the S-D link, and another set representing the composite (S,R)-D link (except for the case when m = M , which corresponds to when the relay remains inactiv e for the whole block; in this case, only the S-D link appears). The switching point between the two channels is controlled by the random variable M . W e will refer to this channel as a random switch channel (RSC). Giv en a particular switching instant M = m , we will call the ensuing channel as a m -switch channel ( m -SC). The RSC belongs to the class of “mixed channels” (see [9]), that is, a compound channel with an a priori probability distribution on the compound members. In this case, the probability distribution on the channel members (the m -SCs in (7)) is induced by the triple ( M , g 1 , g 2 ) . A. Outage pr obability analysis W e compute the DMT of the RSC defined above for arbitrarily large T under the assumption that the destination receiv er has perfect knowledge of M , and hence find an upper bound on the DMT exponent d ∗ M ( r ) for the finite-length DDF protocol. This is established by the follo wing theorem. Theor em 1: The DMT of the single relay DDF scheme with decision times m = 1 , 2 , . . . , M and finite slot length T ≥ 1 is upper bounded by d ∗ M ( r ) ≤ d out ( r ) = min 1 ≤ m ≤ M d m ( r ) + d m ( r ) , where d m ( r ) = 1 − M r m − 1 , 0 ≤ r ≤ m − 1 M 0 , m − 1 M < r ≤ m M ∞ , m M < r ≤ 1 , (9) d m ( r ) = 2 − 2 r, m < M 2 M (1 − r ) m , m ≥ M 2 (10) September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 9 for r ≥ 1 2 , and d m ( r ) = 2 − 2 r, m < M 2 2 − rM M − m , M 2 ≤ m < M (1 − r ) M (1 − r ) m , m ≥ M (1 − r ) (11) for r < 1 2 . Pr oof: Let M denote the random decision time as defined in (5) and P out ( r ) denote the outage probability of the corrsponding RSC. Also, let P m − SC out ( r ) denote the outage probability of the m -SC for gi ven m . Then, the law of total probability yields P out ( r ) = M X m =1 P ( M = m ) P m − SC out ( r ) . (12) Since in the regime of very high SNR that characterizes the DMT , scaling SNR by a constant does not change the DMT , we allow both ρ, ρ 0 → ∞ and the DMT shall not depend on the (constant) ratio ρ 0 /ρ = σ 2 w /σ 2 v . Define P out ( r ) . = ρ − d out ( r ) , P m − SC out ( r ) . = ρ − d m ( r ) , 1 ≤ m ≤ M , P ( M = m ) . = ρ − d m ( r ) , 1 ≤ m ≤ M . Then, it is clear from (12) that d out ( r ) = min 1 ≤ m ≤ M d m ( r ) + d m ( r ) . Furthermore, from standard arguments based on Fano inequality [13] and because here we are assuming that the destination recei ver is enhanced by the side information on M , it is also immediate to conclude that d ∗ M ( r ) ≤ d out ( r ) . It remains to prove (9) and (10), (11). Notice that d m ( r ) is solely a function of the S-R link and d m ( r ) is a function of the R-D and S-D links. W e analyze these quantities separately as follo ws. 1) Analysis of ρ − d m ( r ) : Let’ s consider first the case m < M . Set R = r log ρ . The probability that the relay decodes after m sub-blocks P ( M = m ) , 1 ≤ m ≤ M − 1 , corresponds to the ev ent mT log (1 + | h | 2 ρ 0 ) > M R T > ( m − 1) T log (1 + | h | 2 ρ 0 ) ⇔ n M r m log ρ < log (1 + | h | 2 ρ 0 ) < M r m − 1 log ρ o ⇔ ρ M r m − 1 ρ 0 < | h | 2 < ρ M r m − 1 − 1 ρ 0 . (13) September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 10 Since | h | 2 is exponentially distributed and ρ 0 . = ρ , we compute P ( M = m ) . = Z ρ M r m − 1 − 1 ρ M r m − 1 e − z dz = e − ρ M r m − 1 − e − ρ M r m − 1 − 1 . According to the value of the multiplexing gain, we analyze the above quantity for each 1 ≤ m < M as follo ws. • r > m M : This corresponds to M r m − 1 , M r m − 1 − 1 > 0 . In this case 2 P ( M = m ) . = ρ −∞ . • m − 1 M < r ≤ m M : This corresponds to M r m − 1 ≤ 0 , M r m − 1 − 1 > 0 . In this case, P ( M = m ) . = ρ 0 . • r ≤ m − 1 M : This corresponds to M r m − 1 ≤ 0 , M r m − 1 − 1 ≤ 0 . In this case, using a power series expansion, P ( M = m ) = " 1 − ρ M r m − 1 + ρ 2 ( M r m − 1 ) 2! + · · · # − " 1 − ρ M r m − 1 − 1 + ρ 2 ( M r m − 1 − 1 ) 2! + · · · # . = ρ M r m − 1 − 1 . A similar analysis for P ( M = M ) results in P { M = M } . = ρ M r M − 1 − 1 , 0 ≤ r ≤ M − 1 M ρ 0 , M − 1 M < r ≤ 1 . Therefore, the result for all 1 ≤ m ≤ M can be compactly e xpressed by (9), shown in Fig. 2. 2) Analysis of d m ( r ) : From (8), the outage probability of the m -SC is giv en by P m − SC out ( r ) = P I m − SC ≤ M T R , 2 The notation P . = ρ −∞ indicates that P decreases faster than any polynomial function of ρ . September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 11 A. DMT Analysis Our aim is to compute the DMT of the RSC 2 , under the assumption of lar ge T . The follo wing theorem establishes this DMT . Theor em 1: The DMT of the single relay Alamouti-DDF scheme with M − 1 decoding instants equally spaced in time (i.e., the RSC in (3)) is gi v en by d ∗ M ( r ) = inf 1 ≤ m ≤ M ! d m ( r ) + d m ( r ) " , where d m ( r ) = 1 − M r m − 1 , 0 ≤ r ≤ m − 1 M 0 , m − 1 M < r ≤ m M ∞ , m M < r ≤ 1 and d m ( r ) = & M (1 − r ) m , m ≥ M 2 2 − 2 r , m < M 2 . Pr oof: Let P m − RSC out ( r ) denote the outage probability of the m -RSC. The outage probability of the RSC in (3) is gi v en by P out ( r ) = P r { M = 1 } P 1 − RSC out ( r )+ P r { M = 2 } P 2 − RSC out ( r ) + · · · + P r { M = M − 1 } P ( M − 1) − RSC out ( r ) + P r { M > M − 1 } P M − RSC out ( r ) . (4) According to the DMT formulation, we ha v e to w ork in the re gime of v ery high SNR. Since the ratio ρ $ / ρ = σ 2 w / σ 2 v is a constant, we allo w both ρ , ρ $ → ∞ in the analysis of the DMT . Define P out ( r ) . = ρ − d ∗ ( r ) , P m − RSC out ( r ) . = ρ − d m ( r ) , 1 ≤ m ≤ M , P r { M = m } . = ρ − d m ( r ) , 1 ≤ m ≤ M − 1 , P r { M > M − 1 } . = ρ − d M ( r ) . Notice that d m ( r ) is solely a function of the S-R link and d m ( r ) is a function of the R-D and S-D links. W e analyze these quantities separately as follo ws. 1) Analysis of ρ − d m ( r ) : Set R = r log ρ . The probability that the relay decodes after m sub-blocks P r { M = m } , 1 ≤ m < M , corresponds to the e v ent ! mT log (1 + | h | 2 ρ $ ) > M R T > ( m − 1) T log (1 + | h | 2 ρ $ ) " ⇔ & M r m log ρ < log (1 + | h | 2 ρ $ ) < M r m − 1 log ρ ' ⇔ ( ρ M r m − 1 ρ $ < | h | 2 < ρ M r m − 1 − 1 ρ $ ) 2 Notice that the authors in [15] also treat a similar problem. W e will compare and contrast the results of the present paper and those in [15] in Sec. II-C Since | h | 2 is e xponentially distrib uted and ρ $ . = ρ , we compute P r { M = m } . = * ρ M r m − 1 − 1 ρ M r m − 1 e − z d z = e − ρ M r m − 1 − e − ρ M r m − 1 − 1 . According to the v alue of the multiple xing g ain, we analyze the abo v e quantity for each 1 ≤ m < M as follo ws. • r > m M : This corresponds to M r m − 1 , M r m − 1 − 1 > 0 . In this case P r { M = m } . = ρ −∞ . • m − 1 M < r ≤ m M : This corresponds to M r m − 1 ≤ 0 , M r m − 1 − 1 > 0 . In this case, P r { M = m } . = ρ 0 . • r ≤ m − 1 M : This corresponds to M r m − 1 ≤ 0 , M r m − 1 − 1 ≤ 0 . In this case, using a po wer series e xpansion, P r { M = m } = + 1 − ρ M r m − 1 + ρ 2 ( M r m − 1 ) 2! + · · · , − + 1 − ρ M r m − 1 − 1 + ρ 2 ( M r m − 1 − 1 ) 2! + · · · , . = ρ M r m − 1 − 1 . A similar analysis for P r ( M > M − 1) results in P r ( M > M − 1) . = & ρ M r M − 1 − 1 , 0 ≤ r ≤ M − 1 M ρ 0 , M − 1 M < r ≤ 1 . Therefore, we obtain for 1 ≤ m ≤ M that d m ( r ) = 1 − M r m − 1 , 0 ≤ r ≤ m − 1 M 0 , m − 1 M < r ≤ m M ∞ , m M < r ≤ 1 . (5) This is depicted in Fig. 2. ∞ 1 m M d m ( r ) m − 1 M r 1 Fig. 2. Ne g ati v e ρ -e xponent of the probability of the relay decoding after e xactly m -subblocks Fig. 2. Negati ve ρ -exponent of the probability of the relay decoding after exactly m -subblocks. where I m − SC = mT log (1 + | g 1 | 2 ρ ) + ( M − m ) T log[1 + ( | g 1 | 2 + | g 2 | 2 ) ρ ] . Defining | g 1 | 2 = ρ − α 1 and | g 2 | 2 = ρ − α 2 and applying standard approximations in the re gime of lar ge ρ , we ev entually obtain P m − SC out ( r ) . = P (( M − m ) max { [1 − α 1 ] + , [1 − α 2 ] + } + m [1 − α 1 ] + ≤ r M ) , where [ x ] + , max { 0 , x } . Since | g 1 | 2 and | g 2 | 2 are independent exponential random v ariables, the joint pdf of ( α 1 , α 2 ) is gi ven by f ( α 1 , α 2 ) . = e − ρ − α 1 − ρ − α 2 ρ − α 1 − α 2 . Therefore, P m − SC out ( r ) . = Z B ρ − α 1 − α 2 dα 1 dα 2 , where B is the two-dimensional region defined by the inequalities ( M − m ) max { [1 − α 1 ] + , [1 − α 2 ] + } + m [1 − α 1 ] + ≤ r M and α i ≥ 0 ∀ i . Using V aradhan’ s lemma [17], we obtain d m ( r ) = inf B { α 1 + α 2 } . (14) Define β = m M . The re gion B is equi v alently defined by (1 − β ) max { [1 − α 1 ] + , [1 − α 2 ] + } + β [1 − α 1 ] + ≤ r, α i ≥ 0 ∀ i. It is ob vious that we may restrict attention to α i ≤ 1 ∀ i insof ar as computing the infimum in (14) is September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 12 2 ) A n a l y s i s o f d m ( r ) : F r o m ( 3 ) , t h e o u t a g e p r o b a b i l i t y o f t h e m - R S C i s g i v e n b y P m − R S C o u t ( r ) = P r { I m − R S C ≤ M T R } , w h e r e I m − R S C = m T l o g ( 1 + | g 1 | 2 ρ ) + ( M − m ) T l o g [ 1 + ( | g 1 | 2 + | g 2 | 2 ) ρ ] . C o n t i n u i n g , P m − R S C o u t ( r ) = P r ! l o g " ( 1 + | g 1 | 2 ρ ) m · ( 1 + | g 1 | 2 ρ + | g 2 | 2 ρ ) M − m # ≤ l o g ρ r M $ . D e fi n e | g 1 | 2 . = ρ − α 1 a n d | g 2 | 2 . = ρ − α 2 . P m − R S C o u t ( r ) = P r % ρ ( M − m ) m a x { ( 1 − α 1 ) + , ( 1 − α 2 ) + } · ρ m ( 1 − α 1 ) + ≤ ρ r M & , w h e r e ( x ) + ! m a x { 0 , x } . T h u s P m − R S C o u t ( r ) = P r ! ( M − m ) m a x { ( 1 − α 1 ) + , ( 1 − α 2 ) + } + m ( 1 − α 1 ) + ≤ r M $ . S i n c e | g 1 | 2 a n d | g 2 | 2 a r e i n d e p e n d e n t e x p o n e n t i a l r a n d o m v a r i a b l e s , t h e j o i n t p d f o f ( α 1 , α 2 ) i s g i v e n b y f ( α 1 , α 2 ) . = e − ρ − α 1 − ρ − α 2 ρ − α 1 − α 2 . T h e r e f o r e , P m − R S C o u t ( r ) . = ' B ρ − α 1 − α 2 d α 1 d α 2 , w h e r e B i s t h e t w o - d i m e n s i o n a l r e g i o n d e fi n e d b y t h e i n e q u a l - i t i e s ( M − m ) m a x { ( 1 − α 1 ) + , ( 1 − α 2 ) + } + m ( 1 − α 1 ) + ≤ r M a n d α i ≥ 0 ∀ i . U s i n g V a r a d h a n ’ s l e m m a [ 1 6 ] , w e o b t a i n d m ( r ) = i n f B { α 1 + α 2 } . ( 6 ) D e fi n e β = m M . T h e r e g i o n B i s e q u i v a l e n t l y d e fi n e d b y ( 1 − β ) m a x { ( 1 − α 1 ) + , ( 1 − α 2 ) + } + β ( 1 − α 1 ) + ≤ r α i ≥ 0 ∀ i . I t i s o b v i o u s t h a t w e m a y r e s t r i c t a t t e n t i o n t o α i ≤ 1 ∀ i i n s o f a r a s c o m p u t i n g t h e i n fi m u m i n ( 6 ) i s c o n c e r n e d . W e a n a l y z e B a c c o r d i n g t o t h e f o l l o w i n g c a s e s : • α 1 ≥ α 2 : W e h a v e β ( 1 − α 1 ) + ( 1 − β ) ( 1 − α 2 ) ≤ r ⇔ β α 1 + ( 1 − β ) α 2 ≥ 1 − r . T h i s l i n e h a s i n t e r c e p t s 1 − r β a n d 1 − r 1 − β o n t h e α 1 a n d α 2 a x e s r e s p e c t i v e l y . • α 1 < α 2 : W e h a v e β ( 1 − α 1 ) + ( 1 − β ) ( 1 − α 1 ) ≤ r ⇔ α 1 ≥ 1 − r . T h e r e g i o n B i s d e p i c t e d i n F i g . 3 . T h e s o l u t i o n t o t h e p r o b l e m i n ( 3 ) c o r r e s p o n d s t o c h o o s i n g t h e l e a s t n o n - n e g a t i v e k s u c h α 2 1 1 − r β 1 1 − r 1 − β 1 − r 0 2 − 2 r α 1 2 − 2 r F i g . 3 . T h e r e g i o n B t h a t t h e l i n e α 1 + α 2 = k t o u c h e s B . I t i s i m m e d i a t e f r o m F i g . 3 t h a t t h e s o l u t i o n t o ( 6 ) i s a t ( α ∗ 1 , α ∗ 2 ) = ( 1 − r β , 0 ) f o r β ≥ 0 . 5 , a n d ( α ∗ 1 , α ∗ 2 ) = ( 1 − r , 1 − r ) f o r β < 0 . 5 . T h e r e f o r e , d m ( r ) = ( M ( 1 − r ) m , m ≥ M 2 2 − 2 r , m < M 2 . ( 7 ) T h e t h e o r e m f o l l o w s f r o m ( 4 ) , ( 5 ) a n d ( 7 ) . B . C o m p u t i n g t h e D M T O b t a i n i n g a c l o s e d f o r m s o l u t i o n t o t h e D M T e x p r e s s i o n i n T h e o r e m 1 a p p e a r s t o b e i n t r a c t a b l e . W e p l o t i n F i g . 4 v a l u e s o f d ∗ M ( r ) f o r M = 2 , 5 , 1 0 a n d 2 0 i n c o m p a r i s o n w i t h t h e o p t i m a l D M T o f t h e D D F p r o t o c o l ( c o r r e s p o n d i n g t o M = ∞ ) . W i t h i n c r e a s i n g M , d ∗ M ( r ) i s s e e n t o a p p r o a c h 0 0.2 0.4 0.6 0.8 1 0 0.2 0.4 0.6 0.8 1 1.2 1.4 1.6 1.8 2 r d * M (r) M = 2 M = 5 M = 10 M = 20 Optimal DDF (M = ! ) F i g . 4 . T h e D M T o f t h e D D F c h a n n e l w i t h fi n i t e l y m a n y r e l a y d e c o d i n g i n s t a n t s t h e o p t i m a l t r a d e o f f v e r y r a p i d l y . F o r p r a c t i c a l c o d e d e s i g n , Fig. 3. The region B . concerned. W e analyze B according to the following cases: • α 1 ≥ α 2 : W e ha ve β (1 − α 1 ) + (1 − β )(1 − α 2 ) ≤ r ⇔ β α 1 + (1 − β ) α 2 ≥ 1 − r . This line has intercepts 1 − r β and 1 − r 1 − β on the α 1 and α 2 axes respectively . • α 1 < α 2 : W e ha ve β (1 − α 1 ) + (1 − β )(1 − α 1 ) ≤ r ⇔ α 1 ≥ 1 − r . The region B is depicted in Fig. 3. The solution to the problem in (3) corresponds to choosing the least non-negati ve k such that the line α 1 + α 2 = k touches B . The analysis should be done according to whether 1 − r β ≷ 2 − 2 r ⇔ β ≶ 1 2 and whether 2 − 2 r ≷ 1 ⇔ r ≶ 1 2 . It is immediate from Fig. 3 that the solution to (14) when r ≥ 1 2 is at ( α ∗ 1 , α ∗ 2 ) = 1 − r β , 0 for β ≥ 0 . 5 , and ( α ∗ 1 , α ∗ 2 ) = (1 − r, 1 − r ) for β < 0 . 5 . F or the case when r < 1 2 , the solution to (14) is at ( α ∗ 1 , α ∗ 2 ) = (1 − r , 1 − r ) for β < 0 . 5 , September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 13 at ( α ∗ 1 , α ∗ 2 ) = 1 , 1 − r 1 − β for β ≥ 0 . 5 and 1 − r β > 1 , and at ( α ∗ 1 , α ∗ 2 ) = 1 − r β , 0 for β ≥ 0 . 5 and 1 − r β ≤ 1 . The final solution is compactly e xpressed by (10), (11). This concludes the proof of Theorem 1. B. Achievability W e consider finite length T and no a priori knowledge of M at the destination decoder . W e have the follo wing result: Theor em 2: The upper bound of Theorem 1 is achie vable. Therefore, d ∗ M ( r ) = d out ( r ) . Pr oof: W e consider the original DDF protocol (not the Alamouti v ariant) defined by (1), (2) and (3). For this channel we construct a particular coding scheme and analyze its performance. Codebook generation: For giv en M , T and R , we generate X s ⊂ C M T and X r ⊂ C M T of cardinality ρ rM T independently , with i.i.d. components ∼ CN (0 , E ) . W e let x s ( ω ) and x r ( ω ) denote the codewords in X s and in X r , respectiv ely , corresponding to the information message ω ∈ { 1 , . . . , ρ rM T } . Relay decoding: W e define the relay outage e vent at slot m as O m = ( h ∈ C : | h | 2 ≤ ρ rM m − 1 ρ 0 ) (15) Dif ferently from the case of arbitrarily large T , the relay may decode in error at time m e ven though h / ∈ O m . In the presence of such undetected err or the relay would switch to transmit mode and send a code word corresponding to an incorrect information message, thus jamming the destination receiv er . In order to avoid this event we consider a bounded distance relay decoding decision function ψ δ defined as follo ws (see [12]): for m = 1 , . . . , M − 1 , define the regions S m ( ω ) of all points y ∈ C mT for which ω is the unique message that is contained in a sphere of squared radius mT (1 + δ ) σ 2 v centered at y , i.e., | y − h x m s, 0 ( ω ) | 2 ≤ mT (1 + δ ) σ 2 v . Then, let ψ δ ( y m r, 0 , h ) = b ω ∈ { 1 , . . . , ρ rM T } if both the follo wing conditions are satisfied: 1) h / ∈ O m ; 2) y m r, 0 ∈ S m ( b ω ) ; (the relay has perfect kno wledge of its own channel coefficient h , by the perfect CSIR assumption). If these conditions are satisfied, then M = m and the relay switches to transmit mode, sending the signal x M r,m ( b ω ) for the remaining part of the block. Otherwise, it refrains from making a decision and waits for the next slot. September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 14 It should be noticed that the condition 2) above is a test on the typicality of the estimated channel noise. In f act, if ω is the transmitted message, we ha ve that | y m r, 0 − h x m s, 0 ( ω ) | 2 = | v m 0 | 2 is a central chi-squared random v ariable with 2 mT degrees of freedom and mean mT σ 2 v , that provides an empirical estimate of the noise v ariance. Destination decoding: The destination is not aw are of the relay decision time M . Hence, it makes use of an augmented decoder that simultaneously detects the decision time and the information message according to the GLR T rule: { b ω , b m } = arg max ω ,m p y M 0 | ω , m, g 1 , g 2 . (16) where p ( y M 0 | ω , m, g 1 , g 2 ) is the decoder likelihood function , i.e., the pdf of the signal received by the destination ov er the whole block length, under the hypothesis that the source transmitted the information message ω , that the relay decision time is m , and giv en the channel coef ficients g 1 , g 2 (recall that we assume perfect CSIR). Err or pr obability analysis: Let E denote the decoding error ev ent at the destination and E r denote the decoding error e vent at the relay . 3 W e can write P ( E ) = M X m =1 P ( M = m ) P ( E | M = m ) = M X m =1 P ( M = m ) P ( E , E r | M = m ) + P ( E , E r | M = m ) ≤ M X m =1 P ( M = m ) P ( E r | M = m ) + P ( E | E r , M = m ) P ( E r | M = m ) ≤ M X m =1 P ( M = m ) P ( E r | M = m ) + P ( E | E r , M = m ) . (17) First, we bound the effect of the undetected decision error at the relay . Our analysis follows closely the analysis of the MIMO-ARQ scheme in [12]. In fact, the relay applies a scheme very similar to ARQ: when it is sure about its decision it stops recei ving and starts transmitting, while if it is not sure about 3 The complement of an event A is denoted by A . September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 15 its decision it waits for the next slot. W e hav e P ( E r | M = m ) = ρ − rM T ρ rM T X ω =1 P [ b ω 6 = ω y m r, 0 ∈ S m ( b ω ) ω ≤ P | v m 0 | 2 > mT (1 + δ ) σ 2 v ≤ (1 + δ ) mT e − mT δ , (18) where the last line follows from the Chernoff bound on the tail of the chi-squared distribution. Letting δ = µ log ρ , we find P ( E r | M = m ) ˙ ≤ ρ − mT µ . Notice that P ( E | E r , M = m ) ˙ ≥ ρ − d m ( r ) where d m ( r ) is the exponent of the information outage probability of the m -SC channel giv en in (10), (11) and is not larger than 2. Hence, it is sufficient to choose µT > 2 in order to mak e the terms P ( E r | M = m ) e xponentially irrelev ant in (17). Next, let us e xamine the probabilities P ( M = m ) . Let U m = S ρ rM T ω =1 S m ( ω ) denote the subset of the relay channel output space C mT such that if y m r, 0 ∈ U m then there exists a unique codew ord within the bounded distance decoder’ s decoding sphere centered at y m r, 0 . For m = 1 , we have P ( M = 1) = P { h / ∈ O 1 } , { y 1 r, 0 ∈ U 1 } ≤ P ( h / ∈ O 1 ) . = ρ − d 1 ( r ) . (19) For brevity we let D m = { h / ∈ O m } ∩ { y m r, 0 ∈ U m } . Then, for 1 < m < M , we ha ve P ( M = m ) = P D 1 , . . . , D m − 1 , D m ≤ P D m − 1 , D m . (20) For 1 < m < M , from (20) we can write P ( M = m ) ≤ P n { h ∈ O m − 1 } ∪ { y m − 1 r, 0 / ∈ U m − 1 } o , { h / ∈ O m − 1 } , y m r, 0 / ∈ U m ≤ P ( { h ∈ O m − 1 } , { h / ∈ O m } ) + P { h / ∈ O m − 1 } , { y m − 1 r, 0 / ∈ U m − 1 } , (21) where the second inequality follows from the fact that for e vents A, B , C and D , we hav e using the distributi ve law and the union bound that P ( { A ∪ B } ∩ { C ∩ D } ) = P { A ∪ ( B ∩ A ) } ∩ { C ∩ D } ≤ P ( A ∩ C ) + P ( B ∩ A ) . September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 16 Finally , for m = M , we ha ve P ( M = M ) = P D 1 , . . . , D M − 1 ≤ P D M − 1 = P { h / ∈ O M − 1 } , { y M − 1 r, 0 / ∈ U M − 1 } + P ( h ∈ O M − 1 ) . (22) W e notice that the ev ent { h ∈ O m − 1 } ∩ { h / ∈ O m } coincides with (13) and therefore the first term in (21) decreases as ρ − d m ( r ) . It is also immediate to see that P ( h ∈ O M − 1 ) . = ρ − d M ( r ) . Hence, we are left with the analysis of the probability P { h / ∈ O m } , { y m r, 0 / ∈ U m } (23) for all m = 1 , . . . , M − 1 . A v eraging with respect to the random coding ensemble, we may choose without loss of generality ω = 1 as the reference transmitted message. W e hav e U m ⊆ | v m 0 | 2 > mT (1 + δ ) σ 2 v ∪ R m (1) , where R m (1) are the points y m r, 0 such that | y m r, 0 − h x m s, 0 (1) | 2 ≤ mT (1 + δ ) σ 2 v , and there exists some ω 6 = 1 for which also | y m r, 0 − h x m s, 0 ( ω ) | 2 ≤ mT (1 + δ ) σ 2 v . Letting for brevity ∆ x ( ω ) = x m s, 0 ( ω ) − x m s, 0 (1) , we can write R m (1) = [ ω 6 =1 n | v m 0 − h ∆ x ( ω ) | 2 ≤ mT (1 + δ ) σ 2 v , | v m 0 | 2 ≤ mT (1 + δ ) σ 2 v o . Using the union bound and the Chernof f bound we have P { h / ∈ O m } , { y m r, 0 / ∈ U m } ≤ P | v m 0 | 2 ≥ mT (1 + δ ) σ 2 v + P ( { h / ∈ O m } , R m (1)) ≤ (1 + δ ) mT e − mT δ + X ω 6 =1 P { h / ∈ O m } , n | v m 0 | 2 ≤ mT (1 + δ ) σ 2 v o , n | v m 0 − h ∆ x ( ω ) | 2 ≤ mT (1 + δ ) σ 2 v o (24) Let us consider one term in the sum in the last line of (24) for a given message ω and giv en channel h , av eraged over the random coding ensemble. Noticing that for vectors a and b and Γ > 0 we ha ve {| a + b | 2 ≤ Γ , | b | 2 ≤ Γ } ⊆ {| a | 2 ≤ 4Γ } , September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 17 we can bound this probability as P n | v m 0 − h ∆ x ( ω ) | 2 ≤ mT (1 + δ ) σ 2 v o , n | v m 0 | 2 ≤ mT (1 + δ ) σ 2 v o h (25) ≤ P | h ∆ x ( ω ) | 2 ≤ 4 mT (1 + δ ) σ 2 v h ( a ) = P ρ 0 | h | 2 χ ≤ 2 mT (1 + δ ) h ˙ ≤ ρ − mT [1 − ν ] + , (26) where (a) follows from the fact that for the randomly generated codew ords, χ = | ∆ x ( ω ) | 2 /E is a central chi-squared random v ariable with mean 2 mT and 2 mT degrees of freedom, and the last line follows by letting | h | 2 = ρ − ν and from the fact that the chi-squared cdf satisfies P ( χ ≤ u ) = O ( u mT ) for small u and P ( χ ≤ u ) = O (1) for large u . Summing over the ρ rM T − 1 messages ω 6 = 1 and inte grating with respect to the pdf of | h | 2 ov er the set O m , we obtain P { h / ∈ O m } , { y m r, 0 / ∈ U m } ˙ ≤ Z { ν ≥ 0 , [1 − ν ] + ≥ M r m } ρ − ν ρ − mT [1 − ν ] + + rM T dν . = ρ − e d m ( r ) , (27) where, from a standard application of V aradhan’ s lemma, we have e d m ( r ) = inf ν ≥ 0 , [1 − ν ] + ≥ M r m { ν + mT [1 − ν ] + − r M T } . (28) The domain of ν over which the infimum is calculated is non-empty only for r ≤ m M . This means that the set of channels for which the probability in (23) has a polynomial decrease is empty for r > m M and therefore e d m ( r ) = ∞ for r > m M . For r ≤ m M it is not hard to see that for all T ≥ 1 we have e d m ( r ) = 1 − M r m . Comparing e d m ( r ) with d m ( r ) we see that the former dominates the latter for all r ∈ [0 , 1] . It follows that for our relay bounded distance decoder and the Gaussian random coding ensemble P ( M = m ) ˙ ≤ ρ − d m ( r ) . So far we have shown that in the upper bound (17) the terms P ( E r | M = m ) are asymptotically negligible and the terms P ( M = m ) are upper bounded by the same e xponent of the outage probability based, infinite T , case. It remains to show that the terms P ( E | E r , M = m ) ha ve exponent d m ( r ) gi ven in (10), (11), and the proof will be complete. W e consider the GLR T decoder at the destination. This decoder ignores the knowledge of the a priori distribution of M and treats it as a deterministic unknown parameter . Hence, we are in the presence of a compound channel formed by the family of m -SC component channels, without any a priori knowledge of M . September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 18 Again, without loss of generality we assume message 1 is transmitted. While for the sake of notational simplicity , we omit the explicit conditioning with respect to E r , it is understood that the relay has perfect kno wledge of the transmitted information message. W e omit also the explicit conditioning with respect to CSIR and denote y M s, 0 simply by y since no ambiguity is possible at this point. Hence, the likelihood function p y M 0 | ω , m, g 1 , g 2 shall be denoted simply by p ( y | ω , m ) . The pairwise error probability for some ω 6 = 1 can be upper bounded as follows: P (1 → ω | M = m ) = P max m 0 p ( y | 1 , m 0 ) ≤ max m 0 p ( y | ω , m 0 ) M = m ≤ P p ( y | 1 , m ) ≤ max m 0 p ( y | ω , m 0 ) M = m = P M [ m 0 =1 p ( y | 1 , m ) ≤ p ( y | ω , m 0 ) M = m ! ≤ M X m 0 =1 P p ( y | 1 , m ) ≤ p ( y | ω , m 0 ) M = m . (29) W e shall analyze separately the terms inside the above sum, av eraged over the random coding ensemble. Define the e vent E 1 = p ( y | ω , m 0 ) p ( y | 1 , m ) ≥ 1 . W e first analyze the probability of the ev ent E 1 , which we then use to compute P ( E ) . Assuming M = m , the actual recei ved signal is y m 0 = g 1 x m s, 0 (1) + w m 0 y M m = g 1 x M s,m (1) + g 2 x M r,m (1) + w M m . (30) W e consider the case m 0 ≥ m and leave the case m 0 ≤ m to the reader , since it follows in an almost identical manner . Define the partial codeword differences ∆ x m s, 0 = x m s, 0 (1) − x m s, 0 ( ω ) , ∆ x m 0 s,m = x m 0 s,m (1) − x m 0 s,m ( ω ) , ∆ x M s,m 0 = x M s,m 0 (1) − x M s,m 0 ( ω ) , and ∆ x M r,m 0 = x M r,m 0 (1) − x M r,m 0 ( ω ) . The error e vent E 1 can be written as E 1 = | g 1 | 2 ∆ x m s, 0 2 + 2Re n g 1 ( w m 0 ) H ∆ x m s, 0 o + g 1 ∆ x m 0 s,m + g 2 x m 0 r,m (1) 2 + +2Re n ( w m 0 m ) H h g 1 ∆ x m 0 s,m + g 2 x m 0 r,m (1) io + g 1 ∆ x M s,m 0 + g 2 ∆ x M r,m 0 2 + +2Re n ( w M m 0 ) H g 1 ∆ x M s,m 0 + g 2 ∆ x M r,m 0 o ≤ 0 o . (31) After a little algebra, we obtain the compact e xpression E 1 = n 2Re { z H w } ≤ −| z | 2 o , September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 19 where z is defined as z , g 1 ∆ x m s, 0 g 1 ∆ x m 0 s,m + g 2 x m 0 r,m g 1 ∆ M s,m 0 + g 2 ∆ x M r,m 0 For given codebooks X s , X r , the v ariance of 2Re { z H w } is equal to 2 | z | 2 σ 2 v , which leads to P ( E 1 | X s , X r , M = m, g 1 , g 2 ) ≤ Q | z | p 2 σ 2 v ! ≤ e −| z | 2 / (4 σ 2 v ) . Define the follo wing notation, ξ i = [ x s,i (1) x s,i ( ω ) x r,i (1) x r,i ( ω )] T , 1 ≤ i ≤ M T , and ξ , [ ξ T 1 ξ T 2 · · · ξ T M T ] T ∈ C 4 M T × 1 . It can be verified that | z | 2 = ξ H M ξ , for a block diagonal M of the form M = M 1 . . . M M T , where for 1 ≤ k ≤ mT , M k = | g 1 | 2 1 − 1 0 0 − 1 1 0 0 0 0 0 0 0 0 0 0 , for mT + 1 ≤ k ≤ m 0 T , M k = | g 1 | 2 −| g 1 | 2 g 2 g ∗ 1 0 −| g 1 | 2 | g 1 | 2 − g 2 g ∗ 1 0 g 1 g ∗ 2 − g 1 g ∗ 2 | g 2 | 2 0 0 0 0 0 , and for m 0 T + 1 ≤ k ≤ M T , M k = | g 1 | 2 −| g 1 | 2 g 2 g ∗ 1 − g 2 g ∗ 1 −| g 1 | 2 | g 1 | 2 − g 2 g ∗ 1 g 2 g ∗ 1 g 1 g ∗ 2 − g 1 g ∗ 2 | g 2 | 2 −| g 2 | 2 − g 1 g ∗ 2 g 1 g ∗ 2 −| g 2 | 2 | g 2 | 2 . September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 20 It turns out that the matrices M k hav e rank 1 , for all 1 ≤ k ≤ M T . It follo ws that the eigen values of each M k are tr ( M k ) , 0 , 0 , 0 . W e now av erage P ( E 1 | X s , X r , m, g 1 , g 2 ) over the ensemble of random Gaussian codebooks. In order to do so, we use the following well-known result on the characteristic function of Hermitian quadratic form of comple x Gaussian random variables (briefly , HQF-GR V). Lemma 3: [19, Appendix 4] The characteristic function of the HQF-GR V ∆ = z H Fz , where z ∼ CN ( z , R ) is gi ven by Φ ∆ ( s ) = E [exp( − s ∆)] = exp( − s z H F ( I + s RF ) − 1 z ) det ( I + s RF ) . Therefore, P ( E 1 | m, g 1 , g 2 ) ≤ E X s , X r h e −| z | 2 / (4 σ 2 v ) i = Φ | z | 2 1 4 σ 2 v = 1 det ( I + ρ 4 M ) . Explicitly , we have 1 det ( I + ρ 4 M ) = 1 1 + ρ 2 | g 1 | 2 mT · 1 1 + ρ 4 (2 | g 1 | 2 + | g 2 | 2 ) ( m 0 − m ) T · 1 1 + ρ 2 ( | g 1 | 2 + | g 2 | 2 ) ( M − m 0 ) T . = 1 [1 + ρ | g 1 | 2 ] mT · 1 [1 + ρ ( | g 1 | 2 + | g 2 | 2 )] ( M − m ) T . (32) W e notice that (32) does not depend on m 0 , at least in the exponential equality sense. Summing over all m 0 = 1 , . . . , M and ov er all messages ω 6 = 1 , we eventually can bound the a verage probability of error of the GLR T decoder conditioned on M = m and on g 1 , g 2 as P ( E | E r , M = m, g 1 , g 2 ) ≤ X ω 6 =1 P (1 → ω | M = m, g 1 , g 2 ) ≤ X ω 6 =1 M X m 0 =1 P ( E 1 | m, g 1 , g 2 ) ˙ ≤ M ρ rM T [1 + ρ | g 1 | 2 ] mT · 1 [1 + ρ ( | g 1 | 2 + | g 2 | 2 )] ( M − m ) T . (33) Next, we shall ev aluate the diversity exponent of P ( E | E r , M = m ) = E g 1 ,g 2 [ P ( E | E r , M = m, g 1 , g 2 )] . In order to do so, we separate the outage ev ent from the no-outage event. Define the outage e vent of the m -SC as A m = ( M − m ) max { [1 − α 1 ] + , [1 − α 2 ] + } + m [1 − α 1 ] + − r M ≤ 0 . (34) September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 21 Then, P ( E | E r , M = m ) = P ( E , A m | E r , M = m ) + P ( E , A m | E r , M = m ) ≤ P ( A m ) + P ( E , A m | E r , M = m ) . (35) Recall that P ( A m ) = P m − SC out ( r ) . = ρ − d m ( r ) , where d m ( r ) is ev aluated in (10), (11). In order to ev aluate P ( E , A m | E r , M = m ) , we use (33) and write the exponential inequality P ( E | E r , M = m, g 1 , g 2 ) ˙ ≤ ρ − T g m ( α 1 ,α 2 ,r ) , where g m ( α 1 , α 2 , r ) = ( M − m ) max { [1 − α 1 ] + , [1 − α 2 ] + } + m [1 − α 1 ] + − r M . (36) Therefore, using ag ain V aradhan’ s lemma, we obtain P ( E , A m | E r , M = m ) . = ρ − d G,m ( r ) , where d G,m ( r ) = inf g m ( α 1 , α 2 , r ) > 0 α 1 , α 2 ≥ 0 { α 1 + α 2 + T g m ( α 1 , α 2 , r ) } . (37) The above infimum is achieved when g m ( α 1 , α 2 , r ) ↓ 0 , yielding d G,m ( r ) = d m ( r ) . This concludes the proof of Theorem 2. Remark. The proof of Theorem 2 is not only conceptually appealing, but also re veals a fe w very important and often neglected features that should be taken into account in the design of a DDF scheme. First, the proof sheds light on the fact that the relay must make its decision based not only on the outage condition, b ut also on the reliability of the decoding decision. Then, it sho ws also that despite the fact that the destination does not know the relay decision time, there is no need for an explicit protocol that provides this side information. In Appendix I, we analyze a simpler decoder , nicknamed r elay activity detector , based on separated detection of the relay decision time by treating the codewords as random Gaussian signals (i.e., ignoring the structure of the code). W e show that such a simple “energy detector” September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 22 is optimal if we let T → ∞ first, and then consider the high SNR performance, but it is dramatically suboptimal if we do the limits in the re verse order . In fact, for an y finite T , the relay acti vity detector yields a constant error probability , that does not vanish with SNR. C. Computing the DMT and comparisons Obtaining a closed-form solution to the DMT e xpression in Theorem 1 appears to be intractable. W e plot in Fig. 4 values of d ∗ M ( r ) for M = 2 , 5 , 10 and 20 in comparison with the optimal DMT of the DDF protocol (corresponding to M = ∞ ). 0 0.2 0.4 0.6 0.8 1 0 0.2 0.4 0.6 0.8 1 1.2 1.4 1.6 1.8 2 r d * M (r) M = 2 M = 5 M = 10 M = 20 Optimal DDF (M = ∞ ) Fig. 4. The DMT of the DDF channel with finitely many decoding decision times. W ith increasing M , d ∗ M ( r ) is seen to approach the optimal tradeoff v ery rapidly . For practical code design, ev en a relativ ely small value of M is therefore expected to have close to optimal performance in terms of di versity . September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 23 Remark. The authors in [16] consider a related problem, where T → ∞ and the relay is restricted to a finite number of decision times (say N ). These time instants coincide with the end of blocks { M j } N j =1 , with 1 ≤ M 1 < · · · < M N < M ∀ j (notice: with this notation, in our case we would have N = M and M j = j ). Further , define M 0 , 0 , M N +1 , M , and a set of “waiting fractions” { f j } N +1 j =0 by f j , M j M . Thus f 0 = 0 < f 1 < · · · < f N < f N +1 = 1 . In [16], it is proved that for any fixed N no set of waiting fractions yields a DMT curve that dominates all others. Then, a particular set of waiting fractions are chosen that yield for any fixed N a DMT curve that is not uniformly dominated 4 by any other protocol with the same number of decision times N . The resulting DMT is deriv ed and it is summarized by the follo wing lemma from [16]. Lemma 4: [16] For the DDF protocol with a gi ven number N of decision times, let f p 1 = 1 2 and f p j = 1 − f p j − 1 2 − 1 + 1 f p N f p j − 1 , for 1 < j ≤ N , then no set of fractions uniformly dominates { f p j } N j =1 . Further , the DMT corresponding to the set of fractions { f p j } N j =1 is giv en by d p ( r ) = 1 − r + 1 − r f p N + . (38) A few interesting observations can be made about this result. As it is remarked in [16], the DMT obtained through { f p j } is not asymptotically optimal, i.e., it does not conv erge to the optimal DMT of the DDF protocol as N → ∞ . Indeed, it is evident from (38) that d p ( r ) consists of two straight line segments, say L 1 for 0 ≤ r ≤ f p N and L 2 for f p N ≤ r ≤ 1 . As N → ∞ , L 1 and L 2 can at best be tangential to the curv ed part of the DMT of the DDF protocol (i.e., the 0 . 5 ≤ r ≤ 1 region) in (4). In particular , the optimal v alue of the DMT of the DDF protocol d ∗ (0 . 5) = 1 is nev er approached ev en in the limit by d p ( r ) . In contrast, the DMT d ∗ M ( r ) deriv ed in this paper is asymptotically optimal. As the number of decoding points increases, d ∗ M ( r ) dominates over d p ( r ) for almost all v alues of r , and is strictly less for only an exceedingly small range of values of r . Asymptotically , it is clear that the only set of points where d p ( r ) dominates d ∗ M ( r ) is a v ery small set of points around the point where d p ( r ) is tangent to the curved part of the DMT of the DDF protocol. 4 According to the definition in [16], protocol A uniformly dominates protocol B if, for any multiplexing gain r , d A ( r ) ≥ d B ( r ) . A protocol that is not uniformly dominated by any other protocol is said to be Pareto-optimal. September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 24 I V . D M T O P T I M A L C O D E S F O R T H E S I N G L E R E L A Y D D F C H A N N E L The authors in [15] used the ensemble of random Gaussian codes of asymptotically large block-lengths to sho w the achie v ability of the DMT of the DDF protocol. Subsequently , a construction of codes deriv ed from c yclic di vision algebras (CD A) was sho wn to achiev e the DMT of the DDF channel for arbitrary number of relays [28]; i.e., the y achiev e the corresponding tradeof f for a particular number of decoding instants. As we increase the block-length and the number of decoding instants, the DMT of these codes tends towards the optimal DMT of the DDF protocol given in (4). In a recent submission, [29], the authors present a division-algebraic construction based on the Alamouti code that is similar in flav or to the construction to be presented in this paper . Howe ver , for the codes in [29], the parameter T is fixed to 2 ; on the contrary , we will see that our code construction is valid for arbitrary values of T including the special case of T = 1 , and is hence a minimum delay construction. Decoding these codes in volves sphere or sequential decoding [31], [32] over a large dimensional lattice. It is hence of interest to construct codes that achie ve the DMT of the DDF protocol and permit low complexity decoding. Since our construction is of minimum delay , the dimensionality of the lattice to be sphere decoded is half that of the corresponding case in [29]. In order to completely specify a signalling scheme ( X s , φ, X r ) for the DDF channel, we need to define the following: 1) A code X s that is used by the source. 2) A causal decoding decision function φ ( · , · ) : ( C , C M T ) → { 1 , 2 , . . . , M } , that dictates when the relay attempts to decode the source’ s transmission based on the S-R channel gain h and the signal y r recei ved at the relay . In particular, if φ ( h, y r ) = M , the relay will not attempt to decode the transmission of the source. If φ ( h, y r ) = m, 1 ≤ m < M , then the relay attempts to decode the transmission of the source upon completion of the m th block. Because of the causality constraint, we assume that the output of φ at time m depends only on h (CSIR of the relay) and on y m r, 0 . 3) A code X r used by the relay . In the following, we will only consider the case that the relay implements the Alamouti-DDF scheme [16] gi ven in (6); hence X r is the same as X s upto coordinate permutations, sign change and conjugation. A. Design tr adeoffs Despite the importance of the decoder at the destination, as evidenced in the proof of Theorem 2, in this section we take a shortcut and we do not treat the the GLR T decoder explicitly . For the sake of simplicity , our simulations assume a genie-aided destination, ideally informed of the relay decision time. September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 25 The main focus of this section is on the design of the codebook X s and on the efficient implementation of the relay decoding decision function, in order to trigger the relay transmission only when decisions are reliable. Choosing a good relay decoding decision decision function φ is critical to ensure good performance: a conserv ativ e φ that makes the relay wait for too long before decoding results in lo w relay error probability P ( E r ) , b ut increases the destination error probability P ( E , E r ) since the relay has less time to help the destination. V ice-versa, a φ that is too aggressi ve and makes the relay decode too early yields low P ( E , E r ) but results in a large P ( E r ) , since the blocklength of the signal observed at the relay is too short to cope with atypical noise. W e shall also see through simulations that undetected decoding errors at the relay ha ve a huge impact on performance, since the relay ends up jamming the destination with high probability . W e will present our choices of X s and φ in the follo wing tw o subsections. B. Appr oximately universal X s The equiv alent channel resulting from the use of the Alamouti scheme for the relay code is a parallel channel (7) with statistically dependent fading coefficients. W e will choose X s to be a code of length M T that is appr oximately universal ov er the parallel f ading channel. A code that is approximately uni versal ov er the parallel channel (a notion introduced in [21]) meets the DMT o ver any parallel channel. Such a code has an error probability that decays exponentially with ρ for all parallel channel gains such that the corresponding mutual information is larger than the coding rate, i.e., for all channel gains in the no-outage region. Therefore, such an approximately univ ersal code X s meets the DMT of the relay DDF channel for any M . This means that, for any fixed rate R and sufficiently large SNR, the decay of error probability with SNR of our code (with finite T ) exhibits the same slope of outage probability . Howe ver , the “gap from outage” (i.e., the horizontal distance in dB between the outage probability and the actual probability of error) is not captured by the DMT optimality and in practice it may be very large, thus making a DMT -optimal scheme totally useless for practical purposes. W e shall discuss ways to close this gap in the ne xt section, by an appropriate choice of the relay decision function φ . W e may obtain approximately uni versal X s from either suitable algebraic lattices [23], [24] or from permutation codes through UDMs [21], [22]. In the follo wing we briefly re vie w these constructions. 1) Rotated QAM codes fr om algebraic lattices: Let L be an M T -dimensional extension of Q ( ı ) and let the Galois group Gal ( L | Q ( ı )) = { σ 1 , . . . , σ M T } . Denote the ring of integers of L as O L and let I be an ideal of O L . Let N L | Q ( ı ) ( · ) denote the algebraic norm from L to Q ( ı ) . W e define the code X s as September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 26 follo ws: X s = σ 1 ( ` ) σ 2 ( ` ) . . . σ M T ( ` ) ` ∈ S , where S is some finite subset of I . X s has the desirable property of a “non-vanishing” product distance, since we ha ve for each x ∈ X s that M T Y j =1 | x j | = M T Y j =1 σ j ( ` ) = N L | Q ( ı ) ( ` ) ≥ 1 , since the norm N L | Q ( ı ) ( · ) of an algebraic integer in L is an element of Z [ ı ] . This non-vanishing product distance property ensures that X s is approximately uni versal over the parallel channel [21], [29]. It can be verified that X s can equiv alently be re written as a lattice code, i.e., X s = { Gb | b ∈ B } , (39) for suitable G ∈ C M T × M T and B ⊂ Z [ ı ] M T . A particular choice of G and B that is good in terms of shaping consists of constructing G to be unitary and B to be a set of points in Z [ ı ] M T contained in a h ypercube that is centered around the origin 5 . F or the algebraic details regarding the construction of such unitary G , see [23], [24]. Notice also that choosing the information set B to be a bounded subset of Z [ ı ] M T corresponds, in practice, to choosing information symbols from a QAM alphabet, which is appealing for practical implementation. The rate of X s in this case is R = log | B | M T bpcu . P arameters for simulations: In the simulations to follo w in Sec. IV -C, we construct the matrix G using the cyclotomic construction giv en in [23]. For M = 4 and T = 1 , G is a complex 4 × 4 matrix, or equi valently a real 8 × 8 matrix. W e choose B to be a cartesian product of Q 2 -QAM alphabets, B = { a + ıb | − Q + 1 ≤ a, b ≤ Q − 1 , a, b odd } M T , for some e ven integer Q . Thus | B | = Q 2 M T . For example, by choosing Q = 4 with M = 4 and T = 1 we obtain a rate of R = 4 bpcu. 5 Notice howe ver that choosing G unitary is optimal only when we are constrained to use a linear map to encode the information vector onto the code symbols. An alternate approach is to use a constellation carved out of a dense lattice in R n and employ a non-linear sphere encoder and a mod- Λ MMSE-GDFE lattice decoder; this has been shown to yield significant performance improvements over unitary shaping [26], [27]. For simplicity of exposition, we will restrict our attention to the case of linear encoding in this paper . September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 27 2) P ermutation codes fr om UDM: Approximately univ ersal code construction from UDM were intro- duced in [21] and a general algebraic construction valid for an y number of sub-channels w as provided in [22]. Definition 1: [22] Let n and L be some positiv e integers and let q be a prime power . The L matrices A 0 , . . . , A L − 1 ov er F q of size n × n are ( L, n, q ) -UDMs if for ev ery ( k 0 , . . . , k L − 1 ) such that 0 ≤ k ` ≤ n ∀ ` , P L − 1 ` =0 k ` ≥ n , the ( P L − 1 ` =0 k ` ) × n matrix composed of the first k 0 ro ws of A 0 , the first k 1 ro ws of A 1 , . . . , the first k L − 1 ro ws of A L − 1 has full rank. ♦ The authors in [22] provide an algebraic construction of such ( L, n, q ) -UDMs for any L ≤ q + 1 . It is shown in [21] that an approximately uni versal permutation code for the parallel channel with L - branches can be obtained from ( L, n, q ) -UDMs, in the follo wing manner . Assume that we ha ve to transmit 2 n information symbols from F q . W e encode independently n -symbols each onto the I and Q sub- channels. Let u ∈ F n q denote the first n input information symbols. Map the sequence of F n q symbols { A 1 u , A 2 u , . . . , A L u } componentwise onto a L -length vector of q n -P AM symbols, and transmit the components on the I sub-channel. The next n information symbols are similarly encoded and transmitted on the Q sub-channel. The rate of such a permutation code is R = 2 n log q L bpcu . In our case, we set L = M T to obtain codes for the DDF channel. P arameters for simulations: The simulations in volving permutation codes in Sec. IV -C for M = 4 , T = 1 are deri ved from (4 , 4 , 4) -UDMs, leading to R = 4 bpcu. In order to completely specify the code, we need to provide the mapping to P AM symbols that was used. W e construct the Galois field F 4 using the primitiv e polynomial X 2 + X + 1 . Thus any element in F 4 may be associated with a polynomial b 1 X + b 0 , where the b i are either 0 or 1 , and X is a primitiv e element. Hence we may also associate each element in F 4 with the binary string b 1 b 0 . In order to map an F 4 4 vector v (which is one of the A j u considered previously) to the P AM alphabet, first concatenate the binary strings corresponding to v i ∈ F 4 , i = 1 , 2 , 3 , 4 to obtain an 8 -length binary vector b . This binary vector is mapped to the centered 256-P AM alphabet by computing 2 P 7 i =0 b i 2 i − 255 . September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 28 C. Decoding decision function φ and F orne y’ s decision rule A first choice for φ , which we shall denote φ 1 , would be to allow the relay to decode as soon as the mutual information between the source and the relay e xceeds M T R , i.e., φ 1 ( h ) = min M , M R log(1 + | h | 2 ρ 0 ) , where ρ 0 is the SNR of the source-relay link. This rule is asymptotically optimal for lar ge T , in fact it coincides with the rule in the original formulation of the DDF protocol (5). For finite T , φ 1 is suboptimal since it ignores the actual signal recei ved by the relay , i.e., the atypical beha vior of the noise may dominate the error probability for short block lengths. As an illustration of the inefficac y of this decision function at finite block-length, consider the simulation results in Fig. 5. In the simulations to follo w , we choose X s to be a rotated QAM code. W e will subsequently compare these results with those obtained by choosing X s to be a permutation code, and observe very similar trends. W e consider ML decoding at both the relay and destination for all the simulations in this sub-section. Further , we assume that the source-relay link SNR ρ 0 is 3 dB above the SNR ρ of all other links in all our simulations (the X-axis on all our plots is the SNR ρ in dBs). The simulations in Fig. 5 are for the case when X s is a rotated QAM code, T = 1 , M = 4 and R = 4 bits per channel use (bpcu). The seemingly strange non-monotonic behavior of the error probability can be understood by the following intuitive explanation. At low SNRs, the relay hardly ev er triggers before m = 4 , resulting in P ( E ) being dominated by the error probability at the destination P ( E , E r ) , and hence P ( E ) is lar ge and decreasing. Then, there is an intermediate region of SNR where the relay attempts to decode, but it decodes incorrectly with high probability and causes significant interference at the destination. Thus P ( E ) is dominated by the relay error probability P ( E r ) , and increases in this region. For suf ficiently large SNR, the relay decodes correctly with high probability and therefore helps the destination, thus providing the required cooperativ e di versity (slope of the overall error curve at high SNR). Howe ver , this happens at very large gap from the outage probability , that can be regarded as a de- facto optimal performance also for finite-length codes and not asymptotically high SNR. This simulation re veals a phenomenon that has been scantily treated in pre vious works: the ef fect of decoding errors at the relay clearly dominates the ov erall performance. This fact has often been neglected since it is neither captured by the T → ∞ case, where the atypicality of the noise has no ef fect and triggering the relay based on the outage ev ent is exact, nor by the DMT formulation, that does not capture the gap from outage, but just the asymptotic error probability curve slope. One immediate remedy consists of adopting a conservati ve relay decoding decision function, which September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 29 0 10 20 30 40 50 60 70 80 90 10 ! 4 10 ! 3 10 ! 2 10 ! 1 10 0 SNR (dB) Outage Pr(Destination decodes in error,Relay decodes correct) Pr(Relay decodes in error,Relay attempts to decode) Total error probability F i g . 5 . T = 1 , M = 4 , R = 4 b p c u , R e l a y i m p l e m e n t s φ 1 ( · ) , i . e . , i t a t t e m p t s t o d e c o d e a s s o o n a s t h e m u t u a l i n f o r m a t i o n e x c e e d s e x c e e d s M T R S i m u l a t i o n r e s u l t s u s i n g t h i s s t r a t e g y a r e s h o w n i n F i g . 6 , o n c e a g a i n f o r t h e c a s e o f T = 1 , M = 4 a n d R = 4 b p c u . I n 0 5 10 15 20 25 30 35 40 45 10 ! 5 10 ! 4 10 ! 3 10 ! 2 10 ! 1 10 0 SNR (dB) Outage Pr(Destination decodes in error,Relay decodes correct) Pr(Relay decodes in error,Relay attempts to decode) Total error probability F i g . 6 . T = 1 , M = 4 , R = 4 b p c u , R e l a y i m p l e m e n t s φ 2 ( · ) , i . e . , i t a t t e m p t s t o d e c o d e o n e r o u n d a f t e r t h e m u t u a l i n f o r m a t i o n e x c e e d s e x c e e d s M T R t h i s c a s e , t h e r e l a y e r r o r p r o b a b i l i t y i s s o l o w t h a t n o e r r o r s w e r e r e c o r d e d i n o u r M o n t e C a r l o s i m u l a t i o n ( n o r e d c u r v e i n F i g . 6 ) . T h e d o w n s i d e o f t h i s s t r a t e g y h o w e v e r i s t h a t s i n c e t h e r e l a y i s o v e r - c o n s e r v a t i v e , i t h e l p s t h e t r a n s m i t t e r l a t e , h e n c e t h e d e s t i n a t i o n e r r o r p r o b a b i l i t y P ( E , E r ) i s h i g h . I n [ 1 5 ] , t h e a u t h o r s p r o v e t h a t t h e r e i s n o l o s s i n D M T f o r t h e D D F p r o t o c o l u s i n g t h e A l a m o u t i t y p e r e l a y b y u s i n g t h e f o l l o w i n g r e l a y d e c o d e r f u n c t i o n φ 3 : φ 3 = m i n ! m a x ! M 2 , " M R l o g ( 1 + | h | 2 ρ ! ) # $ , M $ , i . e . , t h e r e l a y i s a l l o w e d t o d e c o d e a n d t r a n s m i t o n l y a f t e r t h e c o d e w o r d f r o m t h e s o u r c e i s a t l e a s t h a l f - w a y t h r o u g h . S i m u l a t i o n r e s u l t s o f t h i s p r o t o c o l s h o w n i n F i g . 7 r e v e a l t h a t t h i s s c h e m e a l s o s u f f e r s f r o m a s i g n i fi c a n t p e n a l t y a t h i g h S N R s d u e t o t h e P ( E r ) t e r m d o m i n a t i n g . I n [ 1 5 ] , t h e a u t h o r s 0 10 20 30 40 50 60 10 ! 4 10 ! 3 10 ! 2 10 ! 1 10 0 SNR (dB) Outage Pr(Destination decodes in error,Relay decodes correct) Pr(Relay decodes in error,Relay attempts to decode) Total error probability F i g . 7 . T = 1 , M = 4 , R = 4 b p c u , R e l a y i m p l e m e n t s φ 3 ( · ) , i . e . , i t i s a l l o w e d t o d e c o d e a n d t r a n s m i t o n l y a f t e r t h e c o d e w o r d f r o m t h e s o u r c e i s a t l e a s t h a l f - w a y t h r o u g h u s e a n e x t r a l a y e r o f c y c l i c - r e d u n d a n c y c h e c k ( C R C ) c o d i n g t o e n a b l e t h e r e l a y t o p e r f o r m e r r o r d e t e c t i o n ( a n d w a i t f o r a n o t h e r r o u n d i f i n c o r r e c t d e c o d i n g i s d e t e c t e d ) - w h i l e t h i s s t r a t e g y i s e f f e c t i v e i n r e d u c i n g P ( E r ) , t h e r e i s a n i n h e r e n t l o s s o f r a t e . I n f a c t , i t i s s h o w n i n [ 1 1 ] f o r t h e M I M O - A R Q c h a n n e l t h a t C R C i s s u b o p t i m a l i n t e r m s o f D M T s i n c e t h e u n d e t e c t e d e r r o r p r o b a b i l i t y m u s t d e c r e a s e a t l e a s t w i t h t h e s a m e e x p o n e n t o f S N R , a n d t h e r e f o r e t h i s e n t a i l s a n e t l o s s o f m u l t i p l e x i n g g a i n s i n c e w e n e e d C R C b i t s t h a t g r o w l i n e a r l y w i t h l o g S N R . T h e s a m e c o n s i d e r a t i o n a p p l i e s h e r e . W e p r e s e n t a n o v e l s t r a t e g y t o e n a b l e e r r o r d e t e c t i o n a t t h e r e l a y w i t h o u t f u r t h e r l a y e r s o f c o d i n g a t t h e t r a n s m i t t e r . W e m a k e u s e o f a c r i t e r i o n i n t r o d u c e d b y F o r n e y i n [ 1 3 ] t o d e c i d e w h e t h e r t h e r e l a y h a s d e c o d e d i n e r r o r ; f o l l o w i n g t h e l i t e r a t u r e , w e w i l l r e f e r t o t h i s c r i t e r i o n a s F o r n e y ’ s d e c i s i o n r u l e . W e p r e s e n t a b r i e f r e v i e w o f F o r n e y ’ s d e c i s i o n r u l e i n t h e a p p e n d i x . W e d e fi n e t h e d e c o d i n g d e c i s i o n f u n c t i o n φ F ( h , y r ) u s i n g F o r n e y ’ s d e c i s i o n r u l e a s f o l l o w s . 1 ) I f φ 1 ( h ) = M , d o n ’ t d e c o d e a n d s e t φ F ( h , y r ) = M ( w o r t h l e s s t r y i n g t o d e c o d e i f w e a r e i n o u t a g e ) 2 ) i f φ 1 ( h ) = # < M , d e c o d e a f t e r t h e # t h b l o c k a n d a p p l y t h e f o l l o w i n g t h r e s h o l d t e s t . L e t ˆ x s d e n o t e t h e o u t c o m e o f t h e r e l a y d e c o d e r , a n d l e t t h e n o t a t i o n z j d e n o t e s t h e v e c t o r c o n s i s t i n g o f t h e fi r s t j c o m p o n e n t s o f z . C h e c k i f P r ( y ! r , ˆ x ! s ) % x s ∈ X s , x s # = ˆ x s P r ( y ! r , x ! s ) ≥ τ , w h e r e τ i s s o m e p a r a m e t e r t h a t i s s e t e m p i r i c a l l y f o r e a c h S N R . I f t h e t h r e s h o l d i s e x c e e d e d , a c c e p t t h e d e c i s i o n , s e t φ F ( h , y r ) = # a n d t r i g g e r t r a n s m i s s i o n b y t h e r e l a y ; o t h e r w i s e , r e p l a c e # b y # + 1 , w a i t f o r t h e n e x t Fig. 5. X s is a rotated QAM code, T = 1 , M = 4 , R = 4 bpcu, relay implements φ 1 ( · ) . we will denote as φ 2 , defined as φ 2 = min M , M R log(1 + | h | 2 ρ 0 ) + 1 . Simulation results using this strategy are sho wn in Fig. 6, once again for the case of X s being a rotated QAM code, T = 1 , M = 4 and R = 4 bpcu. In this case, the relay error probability is so low that no errors were recorded in our Monte Carlo simulation (no such curv e is sho wn in Fig. 6). The do wnside of this strategy ho wever is that since the relay is over -conserv ativ e, it helps the transmitter too late, and the ov erall error probability P ( E , E r ) suf fers from significant degradation with respect to outage probability . In [16], the authors prov e that there is no loss in DMT for the DDF protocol using the Alamouti type relay by using the follo wing relay decoder function φ 3 : φ 3 = min M , max M 2 , M R log(1 + | h | 2 ρ 0 ) , September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 30 0 10 20 30 40 50 60 70 80 90 10 ! 4 10 ! 3 10 ! 2 10 ! 1 10 0 SNR (dB) Outage Pr(Destination decodes in error,Relay decodes correct) Pr(Relay decodes in error,Relay attempts to decode) Total error probability F i g . 5 . T = 1 , M = 4 , R = 4 b p c u , R e l a y i m p l e m e n t s φ 1 ( · ) , i . e . , i t a t t e m p t s t o d e c o d e a s s o o n a s t h e m u t u a l i n f o r m a t i o n e x c e e d s e x c e e d s M T R S i m u l a t i o n r e s u l t s u s i n g t h i s s t r a t e g y a r e s h o w n i n F i g . 6 , o n c e a g a i n f o r t h e c a s e o f T = 1 , M = 4 a n d R = 4 b p c u . I n 0 5 10 15 20 25 30 35 40 45 10 ! 5 10 ! 4 10 ! 3 10 ! 2 10 ! 1 10 0 SNR (dB) Outage Pr(Destination decodes in error,Relay decodes correct) Pr(Relay decodes in error,Relay attempts to decode) Total error probability F i g . 6 . T = 1 , M = 4 , R = 4 b p c u , R e l a y i m p l e m e n t s φ 2 ( · ) , i . e . , i t a t t e m p t s t o d e c o d e o n e r o u n d a f t e r t h e m u t u a l i n f o r m a t i o n e x c e e d s e x c e e d s M T R t h i s c a s e , t h e r e l a y e r r o r p r o b a b i l i t y i s s o l o w t h a t n o e r r o r s w e r e r e c o r d e d i n o u r M o n t e C a r l o s i m u l a t i o n ( n o r e d c u r v e i n F i g . 6 ) . T h e d o w n s i d e o f t h i s s t r a t e g y h o w e v e r i s t h a t s i n c e t h e r e l a y i s o v e r - c o n s e r v a t i v e , i t h e l p s t h e t r a n s m i t t e r l a t e , h e n c e t h e d e s t i n a t i o n e r r o r p r o b a b i l i t y P ( E , E r ) i s h i g h . I n [ 1 5 ] , t h e a u t h o r s p r o v e t h a t t h e r e i s n o l o s s i n D M T f o r t h e D D F p r o t o c o l u s i n g t h e A l a m o u t i t y p e r e l a y b y u s i n g t h e f o l l o w i n g r e l a y d e c o d e r f u n c t i o n φ 3 : φ 3 = m i n ! m a x ! M 2 , " M R l o g ( 1 + | h | 2 ρ ! ) # $ , M $ , i . e . , t h e r e l a y i s a l l o w e d t o d e c o d e a n d t r a n s m i t o n l y a f t e r t h e c o d e w o r d f r o m t h e s o u r c e i s a t l e a s t h a l f - w a y t h r o u g h . S i m u l a t i o n r e s u l t s o f t h i s p r o t o c o l s h o w n i n F i g . 7 r e v e a l t h a t t h i s s c h e m e a l s o s u f f e r s f r o m a s i g n i fi c a n t p e n a l t y a t h i g h S N R s d u e t o t h e P ( E r ) t e r m d o m i n a t i n g . I n [ 1 5 ] , t h e a u t h o r s 0 10 20 30 40 50 60 10 ! 4 10 ! 3 10 ! 2 10 ! 1 10 0 SNR (dB) Outage Pr(Destination decodes in error,Relay decodes correct) Pr(Relay decodes in error,Relay attempts to decode) Total error probability F i g . 7 . T = 1 , M = 4 , R = 4 b p c u , R e l a y i m p l e m e n t s φ 3 ( · ) , i . e . , i t i s a l l o w e d t o d e c o d e a n d t r a n s m i t o n l y a f t e r t h e c o d e w o r d f r o m t h e s o u r c e i s a t l e a s t h a l f - w a y t h r o u g h u s e a n e x t r a l a y e r o f c y c l i c - r e d u n d a n c y c h e c k ( C R C ) c o d i n g t o e n a b l e t h e r e l a y t o p e r f o r m e r r o r d e t e c t i o n ( a n d w a i t f o r a n o t h e r r o u n d i f i n c o r r e c t d e c o d i n g i s d e t e c t e d ) - w h i l e t h i s s t r a t e g y i s e f f e c t i v e i n r e d u c i n g P ( E r ) , t h e r e i s a n i n h e r e n t l o s s o f r a t e . I n f a c t , i t i s s h o w n i n [ 1 1 ] f o r t h e M I M O - A R Q c h a n n e l t h a t C R C i s s u b o p t i m a l i n t e r m s o f D M T s i n c e t h e u n d e t e c t e d e r r o r p r o b a b i l i t y m u s t d e c r e a s e a t l e a s t w i t h t h e s a m e e x p o n e n t o f S N R , a n d t h e r e f o r e t h i s e n t a i l s a n e t l o s s o f m u l t i p l e x i n g g a i n s i n c e w e n e e d C R C b i t s t h a t g r o w l i n e a r l y w i t h l o g S N R . T h e s a m e c o n s i d e r a t i o n a p p l i e s h e r e . W e p r e s e n t a n o v e l s t r a t e g y t o e n a b l e e r r o r d e t e c t i o n a t t h e r e l a y w i t h o u t f u r t h e r l a y e r s o f c o d i n g a t t h e t r a n s m i t t e r . W e m a k e u s e o f a c r i t e r i o n i n t r o d u c e d b y F o r n e y i n [ 1 3 ] t o d e c i d e w h e t h e r t h e r e l a y h a s d e c o d e d i n e r r o r ; f o l l o w i n g t h e l i t e r a t u r e , w e w i l l r e f e r t o t h i s c r i t e r i o n a s F o r n e y ’ s d e c i s i o n r u l e . W e p r e s e n t a b r i e f r e v i e w o f F o r n e y ’ s d e c i s i o n r u l e i n t h e a p p e n d i x . W e d e fi n e t h e d e c o d i n g d e c i s i o n f u n c t i o n φ F ( h , y r ) u s i n g F o r n e y ’ s d e c i s i o n r u l e a s f o l l o w s . 1 ) I f φ 1 ( h ) = M , d o n ’ t d e c o d e a n d s e t φ F ( h , y r ) = M ( w o r t h l e s s t r y i n g t o d e c o d e i f w e a r e i n o u t a g e ) 2 ) i f φ 1 ( h ) = # < M , d e c o d e a f t e r t h e # t h b l o c k a n d a p p l y t h e f o l l o w i n g t h r e s h o l d t e s t . L e t ˆ x s d e n o t e t h e o u t c o m e o f t h e r e l a y d e c o d e r , a n d l e t t h e n o t a t i o n z j d e n o t e s t h e v e c t o r c o n s i s t i n g o f t h e fi r s t j c o m p o n e n t s o f z . C h e c k i f P r ( y ! r , ˆ x ! s ) % x s ∈ X s , x s # = ˆ x s P r ( y ! r , x ! s ) ≥ τ , w h e r e τ i s s o m e p a r a m e t e r t h a t i s s e t e m p i r i c a l l y f o r e a c h S N R . I f t h e t h r e s h o l d i s e x c e e d e d , a c c e p t t h e d e c i s i o n , s e t φ F ( h , y r ) = # a n d t r i g g e r t r a n s m i s s i o n b y t h e r e l a y ; o t h e r w i s e , r e p l a c e # b y # + 1 , w a i t f o r t h e n e x t Fig. 6. X s is a rotated QAM code, T = 1 , M = 4 , R = 4 bpcu, relay implements φ 2 ( · ) . i.e., the relay is allowed to decode and transmit only after the codew ord from the source is at least half-way through. Simulation results of this protocol shown in Fig. 7 rev eal that this scheme also suffers from a significant penalty at high SNRs due to the P ( E r ) term dominating the overall error probability . In [16], the authors use an extra layer of cyclic-redundancy check (CRC) coding to enable the relay to perform error detection (and wait for another round if incorrect decoding is detected) - while this strategy is ef fectiv e in reducing P ( E r ) , there is an inherent loss of rate. In fact, it is sho wn in [12] for the MIMO-ARQ channel that CRC is suboptimal in terms of DMT since the undetected error probability must decrease with SNR at least with the same exponent of error probability itself, and this requires a number of CRC bits that gro w linearly with log SNR. The same consideration applies here. Hence, we wish to a void the use of CRC in order to detect if the relay decodes in error . W e present a no vel strate gy to enable error detection at the relay without further layers of coding at September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 31 0 10 20 30 40 50 60 70 80 90 10 ! 4 10 ! 3 10 ! 2 10 ! 1 10 0 SNR (dB) Outage Pr(Destination decodes in error,Relay decodes correct) Pr(Relay decodes in error,Relay attempts to decode) Total error probability F i g . 5 . T = 1 , M = 4 , R = 4 b p c u , R e l a y i m p l e m e n t s φ 1 ( · ) , i . e . , i t a t t e m p t s t o d e c o d e a s s o o n a s t h e m u t u a l i n f o r m a t i o n e x c e e d s e x c e e d s M T R S i m u l a t i o n r e s u l t s u s i n g t h i s s t r a t e g y a r e s h o w n i n F i g . 6 , o n c e a g a i n f o r t h e c a s e o f T = 1 , M = 4 a n d R = 4 b p c u . I n 0 5 10 15 20 25 30 35 40 45 10 ! 5 10 ! 4 10 ! 3 10 ! 2 10 ! 1 10 0 SNR (dB) Outage Pr(Destination decodes in error,Relay decodes correct) Pr(Relay decodes in error,Relay attempts to decode) Total error probability F i g . 6 . T = 1 , M = 4 , R = 4 b p c u , R e l a y i m p l e m e n t s φ 2 ( · ) , i . e . , i t a t t e m p t s t o d e c o d e o n e r o u n d a f t e r t h e m u t u a l i n f o r m a t i o n e x c e e d s e x c e e d s M T R t h i s c a s e , t h e r e l a y e r r o r p r o b a b i l i t y i s s o l o w t h a t n o e r r o r s w e r e r e c o r d e d i n o u r M o n t e C a r l o s i m u l a t i o n ( n o r e d c u r v e i n F i g . 6 ) . T h e d o w n s i d e o f t h i s s t r a t e g y h o w e v e r i s t h a t s i n c e t h e r e l a y i s o v e r - c o n s e r v a t i v e , i t h e l p s t h e t r a n s m i t t e r l a t e , h e n c e t h e d e s t i n a t i o n e r r o r p r o b a b i l i t y P ( E , E r ) i s h i g h . I n [ 1 5 ] , t h e a u t h o r s p r o v e t h a t t h e r e i s n o l o s s i n D M T f o r t h e D D F p r o t o c o l u s i n g t h e A l a m o u t i t y p e r e l a y b y u s i n g t h e f o l l o w i n g r e l a y d e c o d e r f u n c t i o n φ 3 : φ 3 = m i n ! m a x ! M 2 , " M R l o g ( 1 + | h | 2 ρ ! ) # $ , M $ , i . e . , t h e r e l a y i s a l l o w e d t o d e c o d e a n d t r a n s m i t o n l y a f t e r t h e c o d e w o r d f r o m t h e s o u r c e i s a t l e a s t h a l f - w a y t h r o u g h . S i m u l a t i o n r e s u l t s o f t h i s p r o t o c o l s h o w n i n F i g . 7 r e v e a l t h a t t h i s s c h e m e a l s o s u f f e r s f r o m a s i g n i fi c a n t p e n a l t y a t h i g h S N R s d u e t o t h e P ( E r ) t e r m d o m i n a t i n g . I n [ 1 5 ] , t h e a u t h o r s 0 10 20 30 40 50 60 10 ! 4 10 ! 3 10 ! 2 10 ! 1 10 0 SNR (dB) Outage Pr(Destination decodes in error,Relay decodes correct) Pr(Relay decodes in error,Relay attempts to decode) Total error probability F i g . 7 . T = 1 , M = 4 , R = 4 b p c u , R e l a y i m p l e m e n t s φ 3 ( · ) , i . e . , i t i s a l l o w e d t o d e c o d e a n d t r a n s m i t o n l y a f t e r t h e c o d e w o r d f r o m t h e s o u r c e i s a t l e a s t h a l f - w a y t h r o u g h u s e a n e x t r a l a y e r o f c y c l i c - r e d u n d a n c y c h e c k ( C R C ) c o d i n g t o e n a b l e t h e r e l a y t o p e r f o r m e r r o r d e t e c t i o n ( a n d w a i t f o r a n o t h e r r o u n d i f i n c o r r e c t d e c o d i n g i s d e t e c t e d ) - w h i l e t h i s s t r a t e g y i s e f f e c t i v e i n r e d u c i n g P ( E r ) , t h e r e i s a n i n h e r e n t l o s s o f r a t e . I n f a c t , i t i s s h o w n i n [ 1 1 ] f o r t h e M I M O - A R Q c h a n n e l t h a t C R C i s s u b o p t i m a l i n t e r m s o f D M T s i n c e t h e u n d e t e c t e d e r r o r p r o b a b i l i t y m u s t d e c r e a s e a t l e a s t w i t h t h e s a m e e x p o n e n t o f S N R , a n d t h e r e f o r e t h i s e n t a i l s a n e t l o s s o f m u l t i p l e x i n g g a i n s i n c e w e n e e d C R C b i t s t h a t g r o w l i n e a r l y w i t h l o g S N R . T h e s a m e c o n s i d e r a t i o n a p p l i e s h e r e . W e p r e s e n t a n o v e l s t r a t e g y t o e n a b l e e r r o r d e t e c t i o n a t t h e r e l a y w i t h o u t f u r t h e r l a y e r s o f c o d i n g a t t h e t r a n s m i t t e r . W e m a k e u s e o f a c r i t e r i o n i n t r o d u c e d b y F o r n e y i n [ 1 3 ] t o d e c i d e w h e t h e r t h e r e l a y h a s d e c o d e d i n e r r o r ; f o l l o w i n g t h e l i t e r a t u r e , w e w i l l r e f e r t o t h i s c r i t e r i o n a s F o r n e y ’ s d e c i s i o n r u l e . W e p r e s e n t a b r i e f r e v i e w o f F o r n e y ’ s d e c i s i o n r u l e i n t h e a p p e n d i x . W e d e fi n e t h e d e c o d i n g d e c i s i o n f u n c t i o n φ F ( h , y r ) u s i n g F o r n e y ’ s d e c i s i o n r u l e a s f o l l o w s . 1 ) I f φ 1 ( h ) = M , d o n ’ t d e c o d e a n d s e t φ F ( h , y r ) = M ( w o r t h l e s s t r y i n g t o d e c o d e i f w e a r e i n o u t a g e ) 2 ) i f φ 1 ( h ) = # < M , d e c o d e a f t e r t h e # t h b l o c k a n d a p p l y t h e f o l l o w i n g t h r e s h o l d t e s t . L e t ˆ x s d e n o t e t h e o u t c o m e o f t h e r e l a y d e c o d e r , a n d l e t t h e n o t a t i o n z j d e n o t e s t h e v e c t o r c o n s i s t i n g o f t h e fi r s t j c o m p o n e n t s o f z . C h e c k i f P r ( y ! r , ˆ x ! s ) % x s ∈ X s , x s # = ˆ x s P r ( y ! r , x ! s ) ≥ τ , w h e r e τ i s s o m e p a r a m e t e r t h a t i s s e t e m p i r i c a l l y f o r e a c h S N R . I f t h e t h r e s h o l d i s e x c e e d e d , a c c e p t t h e d e c i s i o n , s e t φ F ( h , y r ) = # a n d t r i g g e r t r a n s m i s s i o n b y t h e r e l a y ; o t h e r w i s e , r e p l a c e # b y # + 1 , w a i t f o r t h e n e x t Fig. 7. X s is a rotated QAM code, T = 1 , M = 4 , R = 4 bpcu, relay implements φ 3 ( · ) . the transmitter . W e make use of a criterion introduced by Forne y in [14] in the context of retransmission (ARQ) protocols to decide whether the decoder is in error or accept the decoding outcome. Here, we apply this criterion to the relay decoder , that we refer to as F orney’ s decision rule . Interestingly , Forne y’ s decision rule is similar in essence to the bounded distance decoder that we hav e considered in the proof of Theorem 2. Howe ver , while the bounded distance decoder is easy to analyze but only asymptotically optimal, F orney’ s decision rule has the remarkable property of striking an optimal balance between the probability of undetected error at the relay and the probability of rejecting the decision and w aiting for the next slot (probability of decision “erasure”, in the language of [14]). T o the best of our kno wledge, this decoding decision rule was not proposed before in the context of relay cooperative communication. W e define the decoding decision function φ F ( h, y r ) using F orney’ s decision rule as follo ws: September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 32 1) If φ 1 ( h ) = M , don’t decode and set φ F ( h, y r ) = M (worthless trying to decode if we are in outage). 2) If φ 1 ( h ) = m < M , decode after the m th block and apply the following threshold test. Let b ω denote the outcome of the relay decoder . Accept the decision and trigger the transmission mode if p ( y m r, 0 | b ω , h ) P ω 6 = b ω p ( y m r, 0 | ω , h ) ≥ τ , (40) where τ a suitable threshold set empirically for each SNR. If the threshold is not exceeded, wait for the ne xt block and repeat this step until either the threshold is exceeded or m = M . φ F is found to be extremely effecti ve in suppressing the error probability at the relay without being too conserv ativ e and refraining from helping the destination when possible. Simulation results for the case when X s is a rotated QAM code, T = 1 , M = 4 and R = 4 bpcu are sho wn in Fig. 7. b l o c k , a n d r e p e a t t h i s s t e p u n t i l e i t h e r t h e t h r e s h o l d i s e x c e e d e d o r ! = M . I f ! = M , t h e n s e t φ F ( h , y r ) = M , t h e r e l a y r e m a i n s s i l e n t . φ F i s f o u n d t o b e e x t r e m e l y e f f e c t i v e i n s u p p r e s s i n g t h e e r r o r p r o b a b i l i t y a t t h e r e l a y w i t h o u t b e i n g t o o c o n s e r v a t i v e a n d r e f r a i n i n g f r o m h e l p i n g t h e d e s t i n a t i o n w h e n p o s s i b l e . S i m u l a t i o n r e s u l t s f o r t h e c a s e w h e n T = 1 , M = 4 a n d R = 4 b p c u a r e s h o w n i n F i g . 7 . T h e e r r o r p r o b a b i l i t y i s 0 5 10 15 20 25 30 35 10 ! 5 10 ! 4 10 ! 3 10 ! 2 10 ! 1 10 0 SNR (dB) Outage P(Destination decodes in error,Relay decodes correct) P(Relay decodes in error,Relay attempts to decode) Total error probability F i g . 8 . T = 1 , M = 4 , R = 4 b p c u , R e l a y i m p l e m e n t s φ F ( · ) , i . e . , i t p e r f o r m s e r r o r d e t e c t i o n u s i n g F o r n e y ’ s r u l e w i t h i n 1 d B f r o m t h e c o r r e s p o n d i n g o u t a g e p r o b a b i l i t y . A P P E N D I X - F O R N E Y ’ S D E C I S I O N R U L E F o r n e y ’ s d e c i s i o n r u l e w a s i n t r o d u c e d i n [ 1 3 ] t o a d d r e s s t h e f o l l o w i n g t y p e s o f c o m m u n i c a t i o n s c e n a r i o s : • T h e d e c o d e r h a s t h e o p t i o n o f c h o o s i n g n o t t o d e c o d e i n t h e e v e n t o f t h e o b s e r v a t i o n s n o t b e i n g r e l i a b l e o r c o n c l u s i v e . T h i s c o r r e s p o n d s t o a n e r a s u r e . O n l y i f t h e d e c o d e r c h o o s e s t o d e c o d e , a n d d e c i d e s i n f a v o r o f a w r o n g c o d e w o r d d o e s a n u n d e t e c t e d e r r o r o c c u r . • T h e d e c o d e r h a s t h e o p t i o n o f p r o d u c i n g m o r e t h a n o n e e s t i m a t e , r e s u l t i n g i n a l i s t o f c o d e w o r d s . O n l y i f t h e c o r r e c t c o d e w o r d i s n o t i n t h e l i s t d o w e h a v e a l i s t e r r o r . W e w i l l b e p r i m a r i l y c o n c e r n e d w i t h o n l y t h e f o r m e r s c e n a r i o i n t h e p r e s e n t p a p e r , a n d w i l l h e n c e f o c u s o n l y o n t h a t c a s e i n t h e s e q u e l . T h e e r a s u r e o p t i o n c a n b e u s e d i n d e c i s i o n f e e d b a c k / A R Q s y s t e m s , a n d i n r e l a y i n g s y s t e m s a s p r o p o s e d i n t h e p r e s e n t p a p e r . I t i s c l e a r , t h a t b y a l l o w i n g t h e e r a s u r e p r o b a b i l i t y t o i n c r e a s e , t h e u n d e t e c t e d e r r o r p r o b a b i l i t y c a n b e r e d u c e d . C o n s i d e r a d i s c r e t e m e m o r y l e s s c h a n n e l ( D M C ) w i t h K i n p u t s x k , 1 ≤ k ≤ K , a n d J o u t p u t s y j , 1 ≤ j ≤ J , c h a r - a c t e r i z e d b y a t r a n s i t i o n p r o b a b i l i t y m a t r i x p j k = P r ( y j | x k ) w h i c h g i v e s t h e p r o b a b i l i t y t h a t y j w i l l b e t h e o u t p u t w h e n x k i s t h e i n p u t 5 . C o n s i d e r a b l o c k c o d e o f r a t e R ( n a t s ) a n d l e n g t h 5 A l t h o u g h F o r n e y ’ s d e c i s i o n r u l e i n [ 1 3 ] i s d e fi n e d f o r a D M C , w e w i l l u s e i t f o r t h e m o r e g e n e r a l c a s e o f a d i s c r e t e - i n p u t c o n t i n u o u s - o u t p u t c h a n n e l . N c o m p r i s i n g o f e N R c o d e w o r d s x m = ( x m 1 · · · x m N ) , m = 1 , . . . , e N R . T h e p r o b a b i l i t y o f r e c e i v i n g y g i v e n t h a t x m w a s t r a n s m i t t e d i s g i v e n b y P r ( y | x m ) = N ! i = 1 P r ( y i | x m i ) . W e d e fi n e d e c i s i o n r e g i o n s R m t o b e t h e s e t o f a l l p o i n t s y d e fi n e d o v e r t h e s p a c e o f r e c e i v e d w o r d s t h a t r e s u l t i n t h e d e c o d e r c h o o s i n g x m a s i t ’ s e s t i m a t e . I f a p a r t i c u l a r y b e l o n g s t o n o n e o f t h e R m , t h e n t h e d e c o d e r d e c l a r e s a n e r a s u r e . W e c o n s i d e r t h e c a s e t h a t a l l d e c i s i o n r e g i o n s a r e d i s j o i n t . T h e e v e n t o f a n u n d e t e c t e d e r r o r E c o r r e s p o n d s t o x m b e i n g s e n t a n d t h e r e c e i v e d v e c t o r y l y i n g i n s o m e d e c i s i o n r e g i o n R m ! , w h e r e m ! " = m , t h e p r o b a b i l i t y o f w h i c h i s g i v e n b y P r ( E ) = " m " m ! " = m " y ∈ R m ! P r ( y , x m ) . D e fi n e t h e e v e n t E 1 a s t h e c o m p o s i t e e v e n t o f e i t h e r a n e r a s u r e o r a n u n d e t e c t e d e r r o r o c c u r r i n g , t h e p r o b a b i l i t y o f w h i c h i s g i v e n b y P r ( E 1 ) = " m " y "∈ R m P r ( y , x m ) . T h e p r o b a b i l i t y o f a n e r a s u r e X i s t h e r e f o r e P r ( X ) = P r ( E 1 ) − P r ( E ) . L e t t h e d e c i s i o n r e g i o n s R m b e d e fi n e d b y y ∈ R m i f f P r ( y , x m ) # m ! " = m P r ( y , x m ! ) ≥ e N T , ( 9 ) w h e r e N i s t h e c o d e l e n g t h a n d T i s a n a r b i t r a r y p a r a m e t e r . T h e n i t i s p r o v e n i n [ 1 3 ] u s i n g a g e n e r a l i z a t i o n o f t h e N e y m a n - P e a r s o n t h e o r e m t h a t t h e r e i s n o o t h e r s e t o f d e c i s i o n r e g i o n s w h i c h g i v e s b o t h a l o w e r P r ( E 1 ) a n d a l o w e r P r ( E ) t h a n t h i s s e t d o e s . F u r t h e r , t h e c r i t e r i o n i n ( 9 ) , r e f e r r e d t o a s F o r n e y ’ s d e c i s i o n r u l e g i v e s t h e o p t i m u m t r a d e o f f b e t w e e n P r ( E ) a n d P r ( X ) , s i n c e w i t h P r ( E ) fi x e d , m i n i m i z i n g P r ( E 1 ) m i n i m i z e s P r ( X ) . T h e a r b i t r a r y p a r a m e t e r T g o v e r n s t h e r e l a t i v e m a g n i t u d e s o f P r ( E ) a n d P r ( E 1 ) ; c l e a r l y a s T i n c r e a s e s , P r ( E 1 ) i n c r e a s e s w h i l e P r ( E ) d e c r e a s e s , s i n c e t h e d e c i s i o n r e g i o n s R m s h r i n k . A C K N O W L E D G E M E N T S T h e w o r k o f K . R a j K u m a r w a s s u p p o r t e d i n p a r t b y a n O a k l e y f e l l o w s h i p f r o m t h e G r a d u a t e S c h o o l a t t h e U n i v e r s i t y o f S o u t h e r n C a l i f o r n i a . R E F E R E N C E S [ 1 ] V . T a r o k h , N . S e s h a d r i , a n d A . R . C a l d e r b a n k , “ S p a c e - t i m e c o d e s f o r h i g h d a t a r a t e w i r e l e s s c o m m u n i c a t i o n : p e r f o r m a n c e c r i t e r i o n a n d c o d e c o n s t r u c t i o n , ” I E E E T r a n s . I n f o r m . T h e o r y , v o l . 4 4 , p p . 7 4 4 - 7 6 5 , M a r . 1 9 9 8 . [ 2 ] J . - C . G u e y , M . P . F i t z , M . R . B e l l , a n d W . - Y . K u o , “ S i g n a l d e s i g n f o r t r a n s m i t t e r d i v e r s i t y w i r e l e s s c o m m u n i c a t i o n s y s t e m s o v e r r a y l e i g h f a d i n g c h a n n e l s , ” P r o c . I E E E V T C ’ 9 6 , p p . 1 3 6 - 1 4 0 . [ 3 ] I . E . T e l a t a r , “ C a p a c i t y o f m u l t i - a n t e n n a g a u s s i a n c h a n n e l s , ” E u r o p . T r a n s . T e l e c o m m . , v o l . 1 0 , n o . 6 , p p . 5 8 5 – 5 9 5 , N o v . - D e c . 1 9 9 9 . [ 4 ] E . C . v a n d e r M e u l e n , “ T h r e e - t e r m i n a l c o m m u n i c a t i o n c h a n n e l s , ” A d v . A p p l . P r o b . , v o l . 3 , p p . 1 2 0 - 1 5 4 , 1 9 7 1 . Fig. 8. X s is a rotated QAM code, T = 1 , M = 4 , R = 4 bpcu, relay implements φ F ( · ) . September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 33 The error probability is within 1 dB from the corresponding outage probability . Fig. 9 shows the results when we choose X s to be a permutation code, with T = 1 , M = 4 and R = 4 bpcu. In this figure we considered two cases: the case of a genie aided relay , where a genie provides 0 5 10 15 20 25 30 35 10 ! 4 10 ! 3 10 ! 2 10 ! 1 10 0 SNR (dB) Outage Total error probability, Genie aided relay Total error probability, relay implements Forneys test Fig. 9. X s is a permutation code, T = 1 , M = 4 , R = 4 bpcu, relay implements φ F ( · ) . the relay with the source message as soon as the mutual information exceeds M T R , and the case where the relay performs minimum distance decoding in conjunction with Forney’ s rule. The results are similar in flav our to the case where X s is a rotated QAM code, with the permutation code losing 1 dB with respect to the rotated QAM code. Notice that despite the DMT optimality , these codes may perform dif ferently depending on their shaping and coding gain. In this case, it is apparent that the rotated QAM code outperforms the permutation code, although the y achiev e the same di versity . September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 34 D. Low comple xity MMSE-GDFE Lattice Decoding As we saw in (39), the choice of rotated QAM codes mak es X s a lattice code. Let Λ be the 2 M T - dimensional lattice corresponding to the generator matrix G in (39). MMSE-GDFE lattice decoding has been sho wn to be DMT optimal for the class of lattice space-time (LaST) codes ov er MIMO channels [11], and has also been shown to perform well for deterministic structured LaST (S-LaST) codes [26], [27]. Let V (Λ) denote the fundamental V oronoi cell of an n -dimensional lattice Λ (See [20] for definitions relating to lattice theory). The lattice quantization function is defined by Q Λ ( y ) , arg min λ ∈ Λ | y − λ | and the modulo-lattice function is given by y mo d Λ , y − Q Λ ( y ) . In the sequel, we will work with the real channel model which is equiv alent to (1), (2) and (3), obtained by writing signals explicitly in terms of their real and imaginary parts (see for example [1] for details regarding the equiv alence between real and complex channel models). By slight abuse of notation, we will refer to the real equiv alent of the complex vectors and matrices x s , y , y r , Λ , G using the same notation. In order to use reduced comple xity MMSE-GDFE lattice decoding [11], information needs to be encoded onto cosets of a sublattice Λ s of Λ , as follows. Choose Λ s = Q Λ , where Q ∈ Z + . Thus | Λ / Λ s | = Q 2 M T . Let C denote the set of points { Gz | z ∈ Z 2 M T Q } , where Z Q , { 0 , 1 , . . . , Q − 1 } . The transmitter selects a code word c ∈ C , generates a pseudo-random dither signal u with uniform distribution over V (Λ s ) , and obtains the transmitted codeword x s = [ c − u ] mo d Λ s . Thus information is encoded onto the cosets of the partition Λ / Λ s : x s is a coset representative of the coset onto which the information is encoded, and belongs to the fundamental V oronoi region of Λ s . Let C ω denote the coset of Λ s in Λ onto which the information corresponding to message ω is encoded. From (1), (2) and (3) the (real equiv alent) receiv ed signals y r = y m r, 0 for M = m at the relay and y s = y M s, 0 at the destination may be written as y r = H r x s + v (41) and y s = Hx s + w , (42) September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 35 where H r ∈ C 2 mT × 2 M T and H ∈ C 2 M T × 2 M T denote the (real) equiv alent channels at the relay and destination, and v and w denote the (real equiv alent) noise at the relay and destination respectiv ely . Notice from (41) that decoding at the relay corresponds to solving an under-determined system of linear equations. W e follo w the approach of [34] in this case, where it was sho wn ho w MMSE-GDFE lattice decoding may be used to efficiently solve under-determined systems of linear equations. W e focus on decoding at the relay in the sequel, the decoder at the destination is identical upon replacing the relev ant signals and parameters at the relay with those at the destination. Let F and B denote the forward and backward filters of the MMSE-GDFE (see for example [11] for the definition of these matrices in terms of H r and the relay SNR). The relay produces the modified observation y 0 r , Fy r + Bu , and computes b z = arg min z ∈ Z 2 M T | y 0 r − BGz | 2 . The relay then decides in fav or of the coset C b ω that contains the point [ G b z ] mo d Λ s . In order to w ork with the lattice coding and decoding scheme, Forne y’ s decision rule (40) needs to be modified to take into account the fact that information is encoded onto cosets as against points in the lattice. Encoding information into cosets is equi v alent to consider a modulo- Λ s channel with output y 0 r modulo B Λ s . Hence, the relev ant likelihood function is giv en by e p ( y 0 r | ω , h ) = X λ s ∈ Λ s p e w ( y 0 r − B ( c ω + λ s ) | h ) with domain y 0 r ∈ V ( B Λ s ) , where c ω is a coset representativ e of C ω and where p e w ( w | h ) denotes the pdf of the noise induced by the modulo- Λ s channel with the dithering, that is, e w = y 0 r − Bx s where x s is the transmitted signal. Unfortunately , p e w is difficult if not impossible to determine in closed form. Ho wev er , a good practical choice that works well for good shaping lattices is to let p e w be a Gaussian pdf with i.i.d. components ∼ N (0 , σ 2 v / 2) (see [11] for a theoretical asymptotic justification of Gaussianity in this context). Then, the proposed modification of Forne y’ s decision rule (40) for the lattice MMSE-GDFE decoder is gi ven by: accept b ω at time m if P λ s ∈ Λ s p e w ( y 0 r − B ( c b ω + λ s ) | h ) P ω 6 = b ω P λ s ∈ Λ s p e w ( y 0 r − B ( c ω + λ s ) | h ) ≥ τ , (43) where, again τ is a suitable threshold set empirically for each SNR. The infinite sums at numeration and denominator can be safely truncated by restricting to a number of most lik ely lattice points, which may September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 36 be done as follows. Generate a list of N = { B λ i : λ i ∈ Λ } N i =1 of lattice points of the lattice generated by BG that are closest to y 0 r . Such a list may be generated, for example, by using a standard lattice decoder with a sufficiently large search radius. F or any giv en message ω , check whether λ i belongs to the coset c e ω + Λ s . If yes, then this point makes a contribution to wards the numerator of (43), else towards the denominator . If there exists b ω for which the corresponding ratio crosses the threshold τ then accept the decision, otherwise reject and w ait for the next slot. The modified Forne y’ s rule in (43) is seen to be quite ef fectiv e for the case when MMSE-GDFE lattice decoding is performed at both the relay and the destination. The simulations in Fig. 10 compares the performance of rotated QAM codes with T = 1 , M = 4 , R = 4 bpcu that use Forne y’ s rule (40) with ML decoding and modified Forney’ s rule (43) with MMSE-GDFE lattice decoding. The low complexity lattice decoder tracks the ML performance within 1 dB. 0 5 10 15 20 25 30 35 10 −4 10 −3 10 −2 10 −1 10 0 SNR (dB) Outage ML relay and destination MMSE−GDFE lattice decoder relay and destination Fig. 10. X s is a rotated QAM code, T = 1 , M = 4 , R = 4 bpcu, relay implements Forney’ s or modified Forne y’ s rule. September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 37 V . C O N C L U S I O N W e presented a characterization of the achie vable DMT of the single-relay DDF protocol for finite block length. Our achiev ability proof yields insight on the design of actual coding schemes. In particular , we stressed the importance of a relay decoding function that check the reliability of its decision, in order not to jam the destination. Also, we showed that the destination need not be aware of the relay decision time, since a GLR T -based decoder achiev es optimal DMT performance. This may hav e some impact on the design of practical DDF protocols, since it essentially shows that no complicated side-information channel needs to be implemented in order to explicitly notify the destination about when the relay starts transmitting. In our proofs, we considered a bounded distance decoder at the relay and an ensemble of random Gaussian codes. Then, we constructed practical and very simple codes based on lattices (rotated QAM constellations) and permutation codes. W e demonstrated via simulation that the impact of undetected decoding errors at the relay may be huge. In order to tackle this problem, we have proposed the use of Forne y’ s decision rejection rule, that pro ves to be very effecti ve. Finally , we hav e inv estigated the use of a reduced complexity MMSE-GDFE lattice decoder and modulo- Λ lattice codes, that yields the well-known low-comple xity decoding ev en at the relay . It should be remarked that the relay in v ariably has to decode an undetermined linear system, therefore standard sphere decoding algorithms fail. A few comments relating to future work are in order here. W e hav e not exploited the lo w-complexity quantization-based decoding approach for permutation codes [21], o wing to the fact that it is not com- pletely clear as to ho w we can apply a good decision rejection rule at the relay in this case. Another interesting problem relates to code design for finite but large T ; in this case, neither the constructions presented in this paper , nor those in [28], [29] are fully controllable in terms of coding gain and both entail very high decoding complexity . Concatenation of short codes based on rotated QAM constellations or permutation codes with some form of outer coding (along the lines of [25]) may prove to be appropriate for this scenario. A P P E N D I X I S E P A R A T E D R E L A Y A C T I V I T Y D E T E C T I O N In this Appendix we treat a side problem. An intuitiv e low-complexity scheme for detecting the relay decision time consists of treating M as a random parameter , and use ML detection by disregarding the structure of the channel codes. Intuiti vely , the destination should be able to detect a transition in the September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 38 recei ved power , between the listening phase and the transmission phase of the relay . This approach is referred to as separated Relay Activity Detection (RAD), since the decision time and the source codeword are separately decoded, in contrast with the GLR T decoder analyzed in the proof of Theorem 2. W e shall sho w that separated RAD yields no performance loss when we consider the limit of T → ∞ . On the contrary , it is suboptimal and actually may perform very poorly when limits are taken in the reverse order , that is, for each finite T we consider the performance as SNR gets large. W e assume that the source uses an i.i.d. random Gaussian code and the relay implements the Alamouti- DDF scheme. As before, let M denote the decision time. An ML decision time detector that is ignorant of the codebooks treats the channel input as a random Gaussian signal. The detection rule is gi ven by b M = arg max m p ( y | M = m, g 1 , g 2 ) . where p ( y | M = m, g 1 , g 2 ) shall be denoted in the follo wing simply by p ( y | m ) for simplicity , and it is gi ven by p ( y | m ) = 1 [ π ( | g 1 | 2 ρ + 1)] mT exp − | y m 0 | 2 | g 1 | 2 ρ + 1 (44) · 1 { π [( | g 1 | 2 + | g 2 | 2 ) ρ + 1] } ( M − m ) T exp −| y M m | 2 ( | g 1 | 2 + | g 2 | 2 ) ρ + 1 . (45) Suppose M = m , we define the pairwise error e vent { m → m 0 } , p ( y | m 0 ) p ( y | m ) ≥ 1 . The detector error probability is lower bounded by P ( M 6 = b M ) ≥ max m 6 = m 0 P ( m → m 0 ) , and is upper bounded by the union bound P ( M 6 = b M ) ≤ ( M − 1) max m 6 = m 0 P ( m → m 0 ) . Hence, we shall study the di versity exponent of P ( m → m 0 ) for general m 6 = m 0 . If this does not depend on m, m 0 we hav e determined the di versity exponent of the separated RAD. A. Infinite bloc k-length If M = m and T → ∞ , the law of large numbers yields the almost sure con vergence of the limits: 1 T | y n n − 1 | 2 → | g 1 | 2 ρ + 1 , 1 ≤ n ≤ m September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 39 and 1 T | y n n − 1 | 2 → ( | g 1 | 2 + | g 2 | 2 ) ρ + 1 , m + 1 ≤ n ≤ M . Thus, for lar ge T we ha ve p ( y | m ) ≈ exp − M T − mT log π ( | g 1 | 2 ρ + 1) − ( M − m ) T log π (( | g 1 | 2 + | g 2 | 2 ) ρ + 1) . Consider the case m 0 > m (the other case follows in the same way and it is omitted for brevity). W e hav e p ( y | m 0 ) ≈ exp − mT − ( M − m 0 ) T − ( m 0 − m ) T ( | g 1 | 2 + | g 2 | 2 ) ρ + 1 | g 1 | 2 ρ + 1 − − m 0 T log π ( | g 1 | 2 ρ + 1) − ( M − m 0 ) T log π ( | g 1 | 2 + | g 2 | 2 ) ρ + 1 . After some simplifications, the pairwise error probability for T → ∞ is gi ven by P ( m → m 0 | g 1 , g 2 ) = P (1 − X 1 + log X 1 ≥ 0) , (46) where we let X 1 = ( | g 1 | 2 + | g 2 | 2 ) ρ + 1 | g 1 | 2 ρ + 1 . Since log x ≤ x − 1 ∀ x ≥ 0 , we see that { m → m 0 } can occur only if | g 2 | 2 = 0 , which is an event of measure 0 . Therefore, we conclude that P ( m → m 0 ) ↓ 0 for any fixed ρ , as T → ∞ . This shows that for the infinite T case, e ven a very simple separated RAD scheme at the destination yields perfect kno wledge of the relay decision time without any need of a side information channel that in volv es some protocol overhead. B. F inite block-length W e no w fix T to be an arbitrary finite value and study the div ersity exponent of P ( m → m 0 ) as ρ → ∞ . Again, we consider only the case m 0 > m . The likelihood function for the hypothesis m 0 when M = m is gi ven by p ( y | m 0 ) = exp − m 0 T log π ( | g 1 | 2 ρ + 1) − ( M − m 0 ) T log π ( | g 1 | 2 + | g 2 | 2 ) ρ + 1 − | y m 0 | 2 + | y m 0 m | 2 | g 1 | 2 ρ + 1 − | y M m 0 | 2 ( | g 1 | 2 + | g 2 | 2 ) ρ + 1 . After some algebra, we find that P ( m → m 0 | g 1 , g 2 ) = P χ ≤ ( m 0 − m ) T X 2 log(1 + X 2 ) , (47) September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 40 where χ = y m 0 m 2 1 + ( | g 1 | 2 + | g 2 | 2 ) ρ is a central chi-squared random variable with 2 T ( m 0 − m ) degrees of freedom and mean T ( m 0 − m ) , and we define X 2 = | g 2 | 2 ρ | g 1 | 2 ρ + 1 . As an aside, notice that 1 x log(1 + x ) is a decreasing function of x that is less than 1 for all x > 0 , and approaches 1 for x ↓ 0 . Therefore, the term ( m 0 − m ) T X 2 log(1 + X 2 ) in (47) is always strictly less than E [ χ ] = ( m 0 − m ) T for all | g 2 | > 0 . Therefore, as an application of the the large deviation theorem [17], we find that P ( m → m 0 ) ↓ 0 exponentially with T for all finite ρ and | g 2 | > 0 . Thus, we reco ver in a more rigorous way the result obtained before by letting T → ∞ directly in the detector decision metric. Returning to the case of finite T , we hav e using well-known properties of the chi-squared distribution that P ( X ≤ u ) = 1 (( m 0 − m ) T )! u ( m 0 − m ) T + O ( u ( m 0 − m ) T +1 ) for small u , and ob viously P ( X ≤ u ) = O (1) when u = β ( m 0 − m ) T for some constant β > 0 . Fix an arbitrary 0 < β < 1 . From what was said before, there e xists an x 2 > 0 such that 1 x 2 log(1 + x 2 ) = β . Hence, consider the e vent E ( ρ, β ) = { X 2 ≤ x 2 } = | g 2 | 2 ρ ≤ x 2 (1 + | g 1 | 2 ρ ) . (48) It is clear that for all ( g 1 , g 2 ) ∈ E ( ρ, β ) , the pairwise error probability P ( m → m 0 | g 1 , g 2 ) in (47) is exponentially equiv alent to a constant as ρ → ∞ , i.e., P ( m → m 0 | g 1 , g 2 ) . = ρ 0 , ( g 1 , g 2 ) ∈ E ( ρ, β ) . A veraging with respect to g 1 , g 2 , and using the standard variable substitution | g 1 | 2 = ρ − α 1 , | g 2 | 2 = ρ − α 2 , we find P ( m → m 0 ) ˙ ≥ Z E ρ 0 e − ρ − α 1 − ρ − α 2 ρ − α 1 − α 2 dα 1 dα 2 . = Z E 0 ρ − α 1 − α 2 dα 1 dα 2 , where, from (48), E 0 = ( α 1 , α 2 ) ∈ R 2 + : 1 − α 2 ≤ [1 − α 1 ] + . September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 41 Using V aradhan’ s lemma, we find that the div ersity exponent of the pairwise error probability is gi ven by ∆ = inf ( α 1 ,α 2 ) ∈ E 0 { α 1 + α 2 } = 0 , since the point α 1 = 0 , α 2 = 0 belongs to the boundary of the region E 0 . This sho ws that for any finite T , a separated RAD scheme based on optimal (Maximum Likelihood) detection of the relay decision time M that ignores the codebook structure and treats the transmitted signals as random processes is very suboptimal. In fact, the probability of error of such a scheme is constant with SNR and e ventually will dominate the performance of the whole destination decoder . In some way , this result shows that the joint detection of the relay decision time and of the information message is necessary in order to achie ve the optimal (infinite T ) DDF DMT . R E F E R E N C E S [1] I. E. T elatar, “Capacity of multi-antenna gaussian channels, ” Eur op. T rans. T elecomm. , vol. 10, no. 6, pp. 585–595, Nov .-Dec. 1999. [2] E. C. van der Meulen, “Three-terminal communication channels, ” Adv . Appl. Pr ob . , v ol. 3, pp. 120-154, 1971. [3] T . M. Cov er and A. A. El Gamal, “Capacity Theorems for the Relay Channel, ” IEEE T rans. Inform. Theory , vol. 25, no. 5, pp. 572–584, Sep. 1979. [4] A. Sendonaris, E. Erkip and B. Aazhang, “User cooperation diversity-part I: system description, ” IEEE T rans. Inform. Theory , V ol. 51, No. 11, pp. 1927–1938, Nov 2003. [5] J. N. Laneman, D. Tse and G. W . W ornell, “Cooperativ e di versity in wireless netw orks: ef ficient protocols and outage behavior , ” IEEE T rans. Info. Theory , V ol. 50, No. 12, pp. 3062–3080, Dec 2004. [6] E. V iterbo and J. Boutros, “ A Universal Lattice Code Decoder for Fading Channels”, IEEE T ransactions on Information Theory , vol. 45, no. 5, pp. 1639-1642, July 1999. [7] B. Hassibi and H. V ikalo, “On the Sphere-Decoding Algorithm I. Expected Complexity”, IEEE T ransactions on Signal Pr oc. , v ol. 53, no. 8, pp. 2806-2818, Aug. 2005. [8] E. Biglieri, J. Proakis and S. Shamai, “Fading channels: information-theoretic and communications aspects”, IEEE T ransactions on Inform. Theory , v ol. 44, no. 6, pp. 2619-2692, Oct. 1998. [9] T . S. Han, Information-Spectrum Methods in Information Theory , Springer , 2003. [10] S. Alamouti,“ A transmitter div ersity scheme for wireless communications, ” IEEE J . Select. Areas Commun. , V ol. 16, No. 8, pp. 1451-1458, Oct 1998. [11] H. El Gamal, G. Caire and M.O. Damen,“Lattice Coding and Decoding Achiev e the Optimal Diversity-Multilpe xing T radeoff of MIMO Channels, ” IEEE T rans. Inform. Theory , vol. 50, No. 6, pp. 968-985, June 2004. [12] H. El Gamal, G. Caire and M. O. Damen,“The MIMO ARQ Channel: diversi ty-multiplexing-delay tradeoff, ” IEEE T rans. Inform. Theory , v ol. 50, No. 8, pp. 968-985, June 2004. [13] L. Zheng and D. Tse, “Div ersity and Multiplexing: A Fundamental T radeoff in Multiple-Antenna Channels, ” IEEE T rans. Info. Theory , v ol. 49, no. 5, pp. 1073-1096, May 2003. September 10, 2018 DRAFT SUBMITTED TO IEEE TRANS. INFORM. THEOR Y , J AN. 2008 42 [14] G. D. Forney , Jr ., “Exponential Error Bounds for Erasure, List, and Decision Feedback Schemes, ” IEEE T rans. Info. Theory , vol. 14, no. 2, pp. 206-220, Mar . 1968. [15] K. Azarian, H. El Gamal and P . Schniter “On the achie vable diversity-multiple xing tradeoff in half-duplex cooperative channels, ” IEEE T rans. Inform. Theory , vol. 51, no. 12, pp. 4152-4172, Dec. 2005. [16] A. Murugan, K. Azarian and H. El Gamal, “Cooperati ve lattice coding and decoding in half-duplex channels, ” IEEE Jnl. Selected Ar eas in Communications , V ol. 25, No. 2, pp. 268-279, Feb . 2007. [17] A. Dembo and O. Zeitouni, Large Deviations T echniques and Applications , Second edition, Springer-V erlag, New Y ork, 1998. [18] D. Tse and P . V iswanath, Fundamentals of W ireless Communication , Cambridge Univ ersity Press, 2005. [19] M. Schwartz, W . R. Bennett, S. Stein, Communications Systems and T echniques , McGraw Hill Book Company , 1966. [20] J. H. Conway and N. J. A. Sloane, Sphere P ackings, Lattices and Groups , Second Edition, Springer-V erlag, 1993. [21] S. T avildar and P . V iswanath, “ Approximately univ ersal codes ov er slow fading channels, ” IEEE T rans. Info. Theory , V ol. 52, No. 7, pp. 3233-3258, Jul. 2006. [22] A. Ganesan and P . O. V ontobel, “On the Existence of Uni versally Decodable Matrices, ” IEEE T rans. Inform. Theory , V ol. 53, No. 7, pp. 2572-2575, Jul. 2007. [23] E. Bayer-Fluckiger , F . Oggier and E. V iterbo, “New Algebraic Constructions of Rotated Z n -Lattice Constellations for the Rayleigh Fading Channel, ” IEEE T rans. Inform. Theory , V ol. 50, No. 4, pp. 702-714, Apr . 2004. [24] E. V iterbo and F . Oggier, Algebraic Number Theory And Code Design F or Rayleigh F ading Channels , Foundations and T rends in Communications and Information Theory , V ol. 1, No. 3, Now Publishers, 2004. [25] A. Guill ´ en i F ` abregas and G. Caire, “Coded Modulation in the Block-Fading Channel: Coding Theorems and Code Construction, ” IEEE T rans. Inform. Theory , V ol. 52, No. 1, pp. 91-114, Jan. 2006. [26] K. Raj Kumar and G. Caire, “Construction of Structured LaST Codes, ” Pr oc. IEEE Intl. Symp. Inform. Theory , pp. 2834- 2838, Seattle, Jul. 2006. [27] K. Raj Kumar and G. Caire, “Structured Lattice Space-T ime Trellis Coded Modulation, ” Pr oc. IEEE Intl. Symp. Inform. Theory , pp. 1931-1935, Nice, France, Jun. 2007. [28] P . Elia and P . V ijay Kumar , “Explicit, Unified, D-MG Optimal Construction for the Dynamic Decode-and-Forward Cooperativ e W ireless Network, ” Proc. F orty-F ourth Annual Allerton Conference , pp. 118-125, Illinois, Sep. 2006. [29] P . Elia and P . V ijay Kumar , “ Approximately-Universal Space-T ime Codes for the Parallel, Multi-Block and Cooperativ e- Dynamic-Decode-and-Forward Channels, ” arXiv:0706.3502v2 [cs.IT] , Jul. 2007. [30] N. Prasad and M. K. V aranasi, “High performance static and dynamic cooperativ e communication protocols for the half duplex fading relay channel, ” in Proc. of IEEE GLOBECOM , San Francisco, CA, USA, Dec. 2006. [31] M. O. Damen, H. El Gamal and G. Caire, “On maximum likelihood detection and the search for the closest lattice point, ” IEEE T rans. on Inform. Theory , V ol. 49, No. 10, pp. 2389-2402, Oct. 2003. [32] A. D. Murugan, H. El Gamal, M. O. Damen, and G. Caire, “ A Unified Framework for Tree Search Decoding: Rediscovering the Sequential Decoder , ” IEEE T rans. on Inform. Theory , V ol. 52, No. 3, pp. 933–953, Mar 2006. [33] M. O. Damen, H. El Gamal and G. Caire, “MMSE-GDFE Lattice Decoding for Solving Under -determined Linear Systems W ith Integer Unknowns, ” Pr oc. IEEE Intl. Symp. Inform. Theory (ISIT 2004), pp. 538, Chicago, Jun. 2004. [34] M. O. Damen, H. El Gamal and G. Caire, “MMSE-GDFE Lattice Decoding for Under-determined Linear Channels, ” Pr oc. 38th annual Confer ence on Information Sciences and Systems (CISS 2004), pp. 627 - 631, Princeton, USA, Mar . 2004. September 10, 2018 DRAFT
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment