Wireless Local Area Networks with Multiple-Packet Reception Capability
Thanks to its simplicity and cost efficiency, wireless local area network (WLAN) enjoys unique advantages in providing high-speed and low-cost wireless services in hot spots and indoor environments. Traditional WLAN medium-access-control (MAC) protoc…
Authors: Ying Jun Zhang, Peng Xuan Zheng, Soung Chang Liew
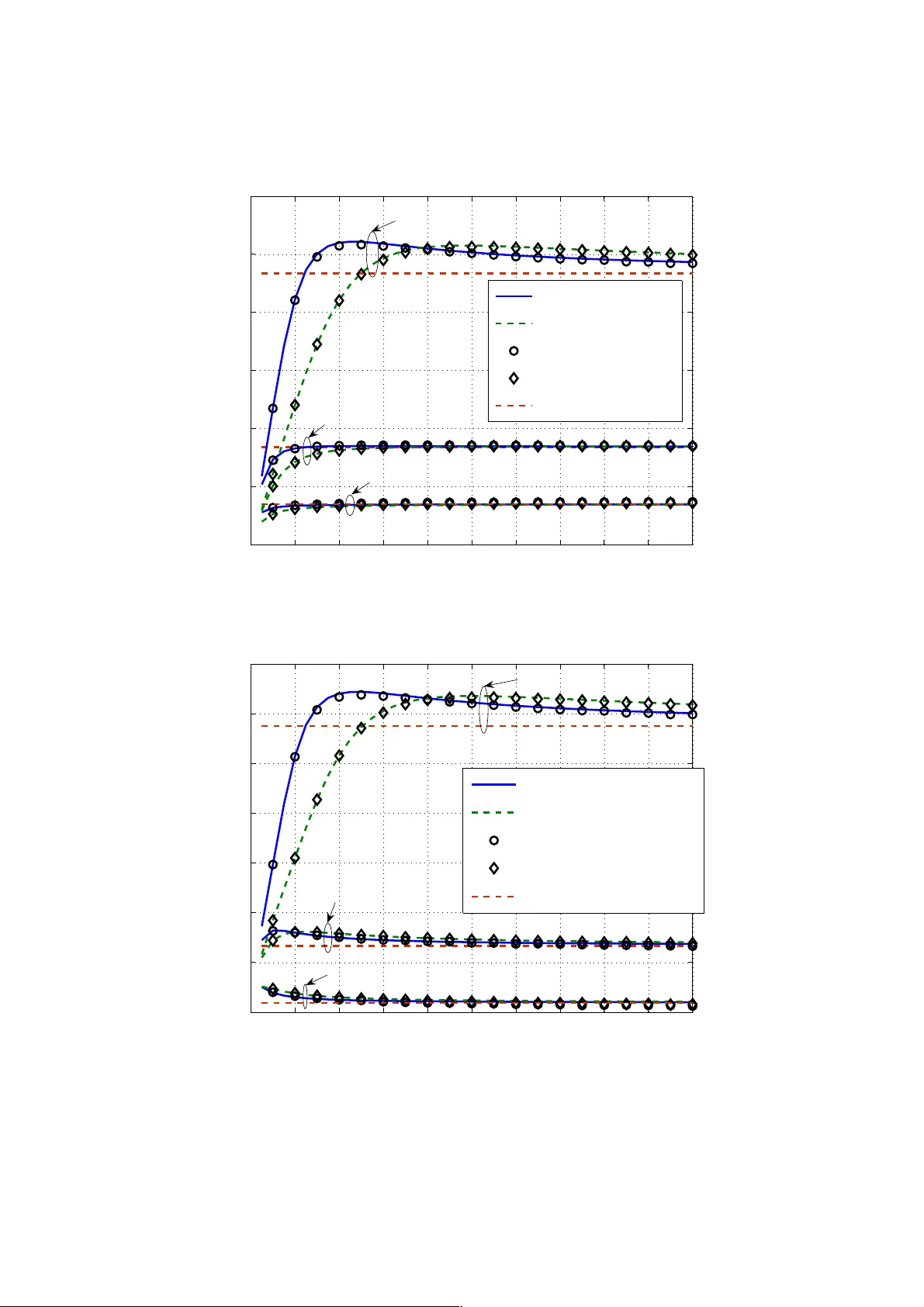
1 Wireless Local Area Networks with Multiple-Packet Re ception Capability Abstract - Th anks to i ts si mpl icity and cost effi cien cy, w irel ess local are a net work (WLAN ) en joy s unique advantages in prov iding high-speed and lo w-cost wireless services in hot spots and indoor environm ents. Traditi onal WLAN m edium-access -control (MA C) protoco ls assume that only one station can tran smit at a time: si multaneou s tran smissions of m ore than one sta tion causes the destruction of all packets involved. By exploiti ng recent advances in PHY-la yer multiuser detection (MUD) techniques, it is possibl e for a receive r to receive multiple pack ets simultaneously . This paper argues that such multipacket reception (M PR) capab ility can greatly e nhance the capacity of future WLANs. In add ition, it prov ides the M AC-laye r and PHY-la yer desig ns needed to ac hieve the improve d capacity. Fi rst, t o demonstrate MUD /MPR as a po werful ca pacity-enha nceme nt techniq ue, we prove a “ super-linear ity” res ult, which s tates tha t the system through put per unit cost increas es as the MPR capability i ncreases. Second, we show that the commonly depl oyed binary exponenti al backoff (BE B) alg orithm in toda y’s WLAN M AC may not be optima l in an MPR system , and that the optimal backoff fac tor incre ases with the MPR capability: th e number of p ackets that can be received si multaneousl y. Third, bas ed on the above ins ights, we design a joint MAC-PHY layer protoco l for an IEEE 80 2.11-like WL AN that in corporates advanced PH Y-layer blind de tection an d MUD techniques t o implem ent MPR. Key words: Multiuser Detection, Mu ltipac ket R eception, WLAN, Expon ential Backoff Correspon ding Author: Ying Jun (Angela) Z hang Emai l: yjzhang@ie.cuhk.edu.hk Tel:/Fax: (852) 2609 8465 2 I. I NTRODUCT ION A. Motivati on The last decade has witnessed a surge of interest in wireless local area ne tworks (WLAN), where mobile statio ns share a common wi reless medium through con tention-based medium access control (MAC). In WLANs, col lision of pack ets occurs when more than one stati on transmits at the same time, causing a waste of bandwidth. T he rece nt adva nces i n multiuser detection (MUD) techniques [1] open up new opportun ities for resolving collisions in the physical (PHY) layer. For example, in CDMA [2][2] or multiple- antenna [ 3] systems, m ultiple pac kets can be received sim ultane ously usi ng MUD techniques without collisi ons. WLAN capac ity can be expecte d to improve great ly with such techniques. To date, most previous work on MUD has been restricted to the PHY lay er. To fully util ize the multipack et reception (MPR) capability for capacity enhanc ement in WLAN, however, it is essential to u nderstand the fundament al impact of MPR on the MAC -layer de sign. With t his backd rop, this paper is a first study of the MAC-layer throughput performance and the collision reso lution schemes for WLANs with MP R. B. Key Contributions The key contrib utions of this paper are as follo ws: • To demonstra te MUD/MPR as a powerful capacity -enhancement te chnique at the system level, we analyze the MAC-layer throughput of WLAN s with MP R capability under both finite-node and in finite-nod e assumption s. In contrast to previous wo rk in [4 ]-[7], ou r model is su fficiently general to cov er both carrier-sensing and non-carrier-sensing networks. We prove that in random- access WLANs, network throug hput increases super-linearly with the MPR cap abilit y of th e channel. That is, throughpu t divided by M increases as M increases, where M is t he number of packets tha t can be reso lved simultaneou sly. The super-linear throughpu t scaling imp lies that the achievable throughput per unit cost increases with MPR capability of the channel. This provides a strong ince ntive t o deploy MPR i n next-genera tion wireles s networ ks. • We study the effect of MPR on the MAC-layer collision resol ution scheme. When packets col lide, an exponential b ackoff (EB) scheme is commonly used to schedule the retransm issions, in w hich the waiting time of the next re transmission will get multiplicatively long er for each collision incurred. In the co mmonly adopted binary exponential backo ff (BEB) scheme (e.g., used in Ethernet [16], WiFi [ 17], etc.), the multi plicative (a bac koff fact or) is eq ual to 2. W e show in this 3 paper that BEB does not necessarily yield the close-to-optimal networ k throughput when the wireless channe l can accomm odate more tha n one simultaneous pac ket transmission. Instead, the optimal bac koff fac tor heavil y depends on the relative durations of idl e, collisio n, and suc cess slots. BEB is far from op timum for b oth non- carrier- sensing networks and carrier-sensing networks opera ted in basic ac cess mode. The op timal backoff fa ctor increases with the MPR capability. Meanwhile , BEB is close to optimum for carrier-sensin g networks when RTS/ CTS access mode is adopted. • Built on th e theoretical underp innings established above, we propose a practical p rotocol to ful ly exploit the MPR capability in IEEE 802.11-like WL ANs. In contrast to [8]-[9 ], we con sider not only the MAC layer proto col design, but also the PHY-layer signal processing to enable MPR in distri buted rand om-access WLA Ns. As a result, the pro posed protoc ol can be implem ented in a fully d istributed m anner wit h margi nal modifi cation of curre nt IEEE 802. 11 MAC. C. Related Work on MPR and Collision Resolution Schemes The firs t atte mpt to mo del a ge nera l MPR channe l in ra ndom -access wirele ss net work s was made b y Ghez, Verdú, and Schwar tz in [4]-[5] in 1988 an 1989, respectively. The stability properti es of slotted ALOHA sy stems wi th MPR were studied und er a simp le infini te-user and single-bu ffer assu mption . In 2005, Nawa re et al studi ed the sta bility a nd delay of finite-u ser ALOHA s ystems over both symm etric and asymmetric MPR channels [6]. In [7], the a uth ors studied the stability and capacity regions of MPR networks whe n an optim al MAC protoco l is available . The pre vious analyses have ma inly focuse d on the stability of n etworks with MPR. Moreover, they are limited to eith er a specific MAC protocol, namely ALOHA [4]-[6], or an idealized optimal MAC [ 7]. Lit tle wo rk ha s been do ne to in vesti gat e the effect of MP R on the perform ance of prac tical rando m -access wireless networks with backoff sche mes. Our pap er here is an at tempt along this di rection. In addition, the super-linearity result as a motivating factor for MPR in thi s paper i s also ne w. Protocols that exploit the MPR capab ilit y of networks have been studie d by Zhao and Tong in [8]-[9]. In [8], a multi- queue service r oom (MQSR) MAC p rotoc ol was propos ed for network s with heteroge neous users. The dra wback of the MQSR prot ocol is its hi gh com putati onal cos t due to up dates of the joint d istribution of all users’ states. To reduce complexity, a suboptimal dynamic queue protocol was propos ed in [9]. In bo th protoco ls, acces s to the comm on wireless cha nnel is contr olled by a central c ontroller, whic h grants ac cess t o the chan nel to an appr opriate s ubset of users at th e beginnin g 4 of each slot. By contrast, this paper provides a di stributed IEEE 802.11-lik e MAC protocol that is more applicable to practical implementations. Exponential Backoff (EB) as a collisio n resolution techni que has been extensiv ely studied in differen t contexts [11]-[14]. Stability upper bound of Binary EB (B EB) has been given by Goodman under a finite-node model in [11] and recently improved by Al-Ammal in [12]. The throughpu t and delay character istics of a sli ghtly modif ied EB schem e have been studied i n [13] in the context of slotted ALOHA. The characteristic s of EB in steady state is furth er investigated in [14] in time sl otted wireless networks with equal sl ot length. All the existi ng work on EB has assum ed that the w ireless c hannel ca n only accommodat e one ongoing transmission at a time. This paper is a first attempt to look at EB for an MPR system. The rem ainder of t his pa per is organize d as f ollows . In Sec tion II, we describe the s ystem m odel and introduce the background knowledge on MUD and EB . In Section III, we prove that the m aximum achievable throughput of MPR WLAN scales super-linearly with the MPR capability of the channel. In Section IV, we investigate the effect of MPR on EB. We illustrate that the widel y used BEB scheme is no longer cl ose-to-optimal in MPR n etworks. In Section V, a MAC-PHY protocol is proposed to realize MPR in IEEE 802. 11 WLAN s. Section VI conclud es this pa per. II. SYSTEM MODEL A. System Description We consider a fully connected ra ndom -access netw ork with N infinitely backlogged mobile stations . We assume that t he time axis is divi ded into slot s and pac ket transmissi ons start only at the begi nning of a slot. In addition, after each transmission, the transm itting stations have a m eans to discover the result of the transmission, i.e., succes s or failure. If the transmission fails due to collision, the colliding stations will schedule retransmissions accordi ng to a collision resolution scheme (e.g., EB). We assume that the ch annel has the ca pability to acco mmodate up to M simultaneous transmissions. In other words, packets can be received correctly whe never the numbe r of simultaneou s transmissions is no larg er than M . When more than M stations contend for the ch annel at the sa m e time, collision occurs and no packet can be deco ded. We ref er to M as MP R capability he reafte r. In our model, the length of a tim e slot is not ne cessarily fi xed and ma y vary under differ ent contexts [10]. We refer to this variable-length slot as backoff slot hereaf ter. In WLANs, the length of a backoff slot depends on the c ontention outc ome (hereaf ter referred to as channel status). L et i T denote the 5 length of an id le time slot when nobody transmits; c T denote the leng th of a colli sion time sl ot when more th an M stations cont end for t he chann el; and s T denote the length of a tim e slot due to succ essful transmis sion w hen the number of trans mitti ng stati ons is a nywhere from 1 to M . The durations of i T , c T , and s T depend on t he underlying W LAN configurati on. For non-carrie r-sensing networks suc h as slotted ALOHA, the st ations are not aware of the channel stat us and the duration of all backof f slots are equal to the transmission ti me of a packet. Th at is, slot i c s TT T T L R = === , (1) where L is the packet size and R is the data transmission rate of a station. On the other hand, for carrier - sensing net works, stations can dist inguish be tween vari ous types of channe l status and the d urations of different t ypes of slots may not be th e same. For exampl e, in IEEE 802.11 DCF basic access m ode, i s c T TH L R S I F S A C K D I F S TH L R D I F S σ δ δ δ = ⎧ ⎪ =+ + + + + + ⎨ ⎪ =+ + + ⎩ (2) where σ is the time nee ded for a station to detect the packet tr ansmissi on from any o ther stat ion and is typically much smaller than c T and s T ; H is the transmission time of PHY header and MAC header; ACK is th e transmission time o f an ACK pa cket; δ is the propagation delay; and SIF S a nd DIFS are the inter-frame space durations [17]. Si milarly, in IEEE 802.11 DCF request-t o-send/c lear-to-sen d (RTS/CTS) access s chem e, the slot durations are give n by i s c T TR T S S I F S C T S S I F S HL R S I F S A C KD I F S TR T S D I F S σ δδ δ δ δ = ⎧ ⎪ =+ + + + + ⎪ ⎨ ++ + + + + + ⎪ ⎪ =+ + ⎩ (3) where RTS and CTS d enote th e transmission time of RTS and CTS pack ets, respectiv ely. By al lowing the duration s of i T , c T , and s T to va ry according to the underlyi ng system, the analysis o f this paper applies to a wide spec trum of various WLANs, including b oth non-ca rrier-se nsing a nd carrier- sensing networks. 6 B. Multiuser Detection This subsection briefly introduces t he PHY layer M UD techniques used to decode multiple p ackets at the receiver. Let () k x n denote th e data sym bol transmitte d by user k in symbol duration n . If there are K stations transmitting toge ther, then the rec e ived signal at a rece iver is given by 1 () () () () ()() () K kk k nn x n n n n n = =+ = + ∑ yh w H x w . (4) where () n w denotes the additive noise, [ ] 12 () () , () , () K nn n n = Hh h h , and [ ] 1 () () , , () T K nx n x n = x . In CDMA syst ems, vecto r k h is the spreading sequence of user k . In multip le antenna syst ems, k h is the channel v ector, with the m th element being t he channel co efficient fro m user k to the m th recei ve antenna. The receiver a ttempts to obta in an estimate of the transmitted symbols () n x from the received vector () n y . To this end, various MUD t echniques have be en propos e d in the li terature. For example, the zero-forci ng (ZF) receiver is one of the most popula r linear detectors. It m u ltiplies the received vector by the pseudo -inverse of matrix () n H , denote d by () n + H , and the decision st atistics become () () () () () () ZF nn n n n n ++ == + rH y x H w . (5) The minimum -mean-square-error ( MMSE) receiver is the optimal linear de tector in the sens e of maximi zing the signal- to-interfere nce-an d-noise ratio (SINR). The decision s t atistics is calculate d as ( ) 1 () () () () () MMSE H H nn n n n η − =+ rH H I H y (6) where I is the identity matrix, and η is the variance of the addit ive noise. Given the decision statist ics, an estim ate of () k x n can be obtaine d by feed ing the k th element of ( ) ZF n r or ( ) MMSE n r into a quantizer. Other MUD techniq ues include maximum-lik elihood (ML), parallel interference canc ellation (PIC), successive in terference cancellation (SIC) , etc. Intere sted readers are referred to [1] for more details. C. Exponential Backoff EB adaptively tunes the transmission probability of a stat ion according to the traffic intensity of the network. It work s as follows. A backlogged station sets its b ackoff timer by rando mly choosing an integer within the range [ ] 0, 1 W − , where W denote the size of the con tention window. The backoff timer is decreased by one fo llowing each backoff sl ot. The station tran smits a packet in its queue once the back off timer reach es zero. At the firs t transm ission atte mpt of a packe t, 0 WW = , referred to as the 7 minim um content ion windo w. Each tim e the transmission is unsucc essful, t he W is multip lied by a backoff factor r . That is, the contention window size 0 i i Wr W = after i successive transm ission failures. III. S UPER -L INEAR T HROUGHPUT S CALING IN WLANS WITH MPR This sectio n investi gates the impact of MPR on the throu ghput of ra ndom-access WLANs. I n particular, we prove that the maximum achiev able throughput scales super-linearly with the MPR capability M . In practica l sy stem s, M is directly related to the co st (e.g., bandwi dth in CDMA system s or antenna in multi-antenna systems ). Super-linear scaling o f throughput implies that th e achievable throughput per unit cost incre ases wi th M . Th is provi des a st rong ince ntive to consid er MPR in next- generati on wireless networks. As mentioned earlie r, the transmiss ion of stations is dic tated by the un derlying EB schem e. To capture the f undamentally achie vable spectrum efficiency of the sys tem, the f ollowing anal ysis assumes that each station transmits with probability t p in an arbitrary slot, without caring how t p is achieved. The assumption will be made more rigorous in Section IV, w hich relates t p to EB parameters s uch as r and 0 W . A. Throughput of WLANs with MPR Define throughput to be the averag e number of in formation bits tr ansmitted successfully per second. Let () , N t SM p denote the through put of a WLAN with N stations when each station transmits at probabi lity t p and the MPR capability is M . Then, ( ) , N t SM p can be calcula ted as the rati o betwee n the average p ayload information bits transmitted per backoff slot to the average leng th of a backoff sl ot as follows. () [ ] [] {} 1 pay lo ad inform ation bits tran smitte d in a ba ckof f slot , length o f a backoff s lot Pr bits/sec Nt M k idle i coll c succ s E SM p E kX k L PT P T P T = = = = ++ ∑ (7) In the above, X is a random variable denotin g the number a ttem pts in a slot. {} ( ) Pr 1 N k k tt N Xk p p k − ⎛⎞ == − ⎜⎟ ⎝⎠ . (8) 8 Let () 1 N idle t Pp =− (9) be the probability that a backoff slot is idle; {} ( ) 11 Pr 1 MM N k k succ t t kk N PX kp p k − == ⎛⎞ == = − ⎜⎟ ⎝⎠ ∑∑ (10) be the probability that a backoff slot is busy due to successful packet transmissions; and {} ( ) 11 Pr 1 NN N k k coll t t kM kM N PX k p p k − =+ =+ ⎛⎞ == = − ⎜⎟ ⎝⎠ ∑∑ (11) be the probability that a backoff slot is busy due to collision of packets. The throughput of non -carrier-sensing networks su ch as slotted ALOHA can be obtained by substituting (1) into (7), whi c h leads to following expression. () {} () 1 1 Pr , 1 bits/sec M M Nk k k Nt t t k slot kX k L N SM p R k p p k T − = = = ⎛⎞ == − ⎜⎟ ⎝⎠ ∑ ∑ . (12) Similarly, the through put of carrier-sensing networ ks, such as IEEE 802 .11 DCF basic-access mode and RTS/CTS access mode, c an be obtaine d by substit uting (2) and (3) into (7) res p ectivel y. We now derive the asymptotic throughput when the population size N approaches infinity. In thi s case, we assume that (i) the system has a non-zero asymptotic throughput; and (ii) the number of attempt s in a backoff slot is approximated by a Poisson distribution with an average attempt rate t Np λ = . Both of thes e assumpti ons are valid under an appro priate EB scheme, whic h will be elaborated in Se ction IV. Let () , SM λ ∞ be t he asympt otic thr oughput whe n MPR capabi l ity is M and av erage atte mpt rat e is λ . Then, we derive from (7) that () {} 1 ,l i m P r M N N k idle i coll c succ s L SM S k X k PT P T P T λ ∞ →∞ = == = ++ ∑ (13) {} () 1 1 0 ! ! Pr 1 bits /sec k M a k idle i coll c succ s k M k idle i coll c succ s idle i coll c succ s L ke PT P T P T k L e PT P T P T k L XM PT P T P T λ λ λ λλ λ − = − − = = ++ = ++ =≤ − ++ ∑ ∑ where Equality (a) is due to the Po isson appro ximatio n. In p articul ar, when slot i c s TT T T L R == = = , 9 () {} 1 1 0 , Pr 1 bits/se c ! k M k SM R e R X M k λ λ λλ + − − ∞ = == ≤ − ∑ (14) B. Super-Linear Th roughput Scaling Having derived th e throughput exp ressions for both fin ite-popul ation and in fi nite-popu lation models, we now address the question: how does thro ughput scale as M increa ses. In par ticul ar, we ar e inter ested in the behavior of the maximum throughput when the channe l has a MPR capability of M . This directly relates to the channel- access efficiency that is achievable in MPR networks. Given M , the maximum throughput can be achieved by optimizing the transmission probability t p (or equivalently λ in th e infinite-population mo del). The optimal transmission probability can in tu rn be obtained by adjusting the backoff factor r in practica l WLANs, as will be discussed in Section IV. Let () ** () , () NN t SM S M p M = and ( ) ** () , () SM S M M λ ∞∞ = denote the maximum achievable throughputs, where * () t p M and * () M λ denote the optimal t p and λ when th e MPR capability is M , respectively. In Theorem 1, we prove that the throughput scal es super-linearly with M in non-carrier- sensing netwo rk with infin ite population. In other word s, * () SM M ∞ is an increasing func tion of M . In Theorem 2 , we further prov e that * () SM M R ∞ appr oaches 1 when M →∞ . This implies tha t the throughput p enalty due to d istributed r andom access diminishes wh en M is very large. In Theorem 3 in Appendix A, we p rove that the same super-linearity hold s for WLANs with fini te population. Theorem 1 ( Super-l inearity ) : * () SM M ∞ is an increasing function of M . It is obvi ous that at the opt imal * () M λ ( ) ( ) ** * 1 ** 11 () () 00 () (1 ) ( ) ( ) (, ) 0 !! kk MM MM kk M kM M SM Re R e kk λλ λλ λλ λ λ + −− −− ∞ == = + ∂ =− = ∂ ∑∑ . (15) Conseque ntly, () ( ) ** ** 1 () () 0 () () !( 1 ) ! kM M M M k MM ee kM λλ λλ − −− = = − ∑ , (16) or { } { } ** () () Pr 1 Pr M M XM M X M λλ λλ == ≤− = = . (17) To prove Theorem 1, we show that ** (1 ) (1 ) ( ) SM M SM M ∞∞ ++ ≥ for all M in the following. ( ) ** (1 ) 1 , (1 ) SM S M M λ ∞∞ + =+ + (18) 10 () () {} () ** * *1 * 1 1 *( ) ( ) 0 ** () * () () 1, ( ) !! ,( ) ( ) P r 1 kM M M M k M MM SM M R e R e kM SM M R M X M M SM M λλ λλ λλ λ λλ ++ − −− ∞ = ∞ = ∞ ≥+ = + =+ = + = ∑ where the last eq uality is due to (1 4) and (17). Theref ore, we have ** (1 ) ( ) 1 SM SM M MM ∞∞ + ≥∀ + . □ It is obvious that in a WLAN with MPR capability of M , the maximum possible throughput is MR when there exists a perfect scheduling. In prac tical random-access WLANs, the actual throughpu t is always smaller than MR , due to the throughput penalty resulting fro m packet collisions and id le slots. For example, the maximum throughput is well known to be 1 R e − when 1 M = . Theorem 2 proves that the throug hput pe nalty dim inishes as M becomes large. That is, the maximum t hroughput app roaches MR even though the channel access is b ased on random conten tions. Theorem 2 ( Asymptotic c hannel-access efficien cy ): * () lim 1 M SM MR ∞ →∞ = . Before prov ing Theorem 2, we presen t the following tw o lemmas. Lemma 1 : (a) lim ( ) 1 M SM R λ ∞ →∞ = for any attempt rate M λ < ; (b) lim ( ) 0 M SM R λ ∞ →∞ = for any attemp t rate M λ > ; and (c ) lim ( ) 0 . 5 M SM R λ ∞ →∞ = for attempt rate M λ = . Due to the pa ge limit, onl y the pro of of Lemma 1(a) is presente d here, as it is more relevant to the proofs of Lemma 2 and T heorem 2. Interested rea d ers are refe rred to Appendix B for the proof of Lemma 1(b) an d 1(c). Proof of Lemma 1 ( a ): {} () () 1 0 (1 ) (, ) P r 1 1 !! 11 1 ! kk M kk M k MM z kM SM R X M R e R e kk z Rz e R z e z k λ λ λλ λλ λλ λ λ λ λλ −∞ −− ∞ == ∞ −− − − = ⎛⎞ =≤ − = = − ⎜⎟ ⎝⎠ ⎛⎞ ≥− ≥ − ∀ > ⎜⎟ ⎜⎟ ⎝⎠ ∑∑ ∑ (19) Let () (1 ) () 1 Mz fz R z e λ λ −− =− be the lower bound o f () SM ∞ . By solving () 1( 1 ) ( 1 ) () 0 Mz M z fz RM z e z e z λλ λλ −− − − − ∂ =− = ∂ , (20) 11 it can be easily found that * zM λ = maxi mi ze s () f z and * 1 () 1 M M M fz e RM λ λ λ ⎛⎞ − ⎜⎟ ⎝⎠ ⎛⎞ =− ⎜⎟ ⎝⎠ (21) Since * 1 z > , M λ < . Let cM λ = where 1 c < . Eqn. (21) can be written as () () * 1 () 1 M c fz ce R λ − =− (22) It is obviou s that ( ) 1 1 1 c ce c − < ∀≠ . (23) Therefore, () () ( ) * 1 (, ) ( ) lim lim lim 1 1 M c MM M SM f z ce R R λ λ λ − ∞ →∞ →∞ →∞ ≥= − = , (24) On the other han d, the first e quality of (19) im plies (, ) 1 SM R λ λ ∞ ≤ . (25) Com binin g (24) and (2 5), we ha ve () lim 1 M SM M R λ λ ∞ →∞ = ∀< , ( 26) and Lemma 1(a) follows. □ Lemma 2 : The optimal attempt rate * () M M λ < and * lim ( ) 1 M MM λ →∞ = . Proof of Lemma 2: The mode of Poisso n di stribution is equal to λ ⎢ ⎥ ⎣ ⎦ , where ⎢⎥ ⎣⎦ i den otes th e larg est integer that is smaller than or equal to the argument. When M λ ≥ , { } { } Pr Pr 0 1 XM X i i M => = ∀ ≤ ≤ − , (27) which conflicts with Eqn. (17). Ther efo re, the optimal at tempt rate * () M M λ < . (28) Com binin g (12), (1 7), (2 8) a nd Lemm a 1, we h ave { } * () lim P r 1 M M MX M λλ = →∞ = = . (29) Let * cM λ = where 1 c < . Eqn. (29 ) can be writ ten as () lim 1 (1 ) ! M cM M cM e M − →∞ = − , (30) 12 and () () 11 (1 ) (1 ) ! ! lim lim MM cc c MM MM ce e e MM − − →∞ →∞ − == = (31) where the last equality is due to the Stirling’s formula [15]. Solving E qn. (31), w e have * lim l im 1 MM c M λ →∞ →∞ = = . □ Proof of Theorem 2 : From Lemma 1 and Lemma 2, it is obvious that * lim ( ) ( ) 1 M SM M R λ ∞ →∞ = . The above re sults are il lustrated in Fig. 1, where * () SM M R ∞ is plotted as a fun ction of M in non - carrier-sen sing slotted ALOHA systems. The figure shows that * () SM M R ∞ increa ses with M . In Theore m 1-3, super-li nearity is proved a ssuming the network is non-carrier -sensin g . In Fig. 2 and Fig. 3, th e optimal throughput * () SM ∞ and * () SM M ∞ are plotted for carrie r-sensing netw orks, respectively, with system p aramete rs listed in Table I. The figures show that system through put is greatly e nhanced due to t he MPR enhancem ent in the PHY layer. M oreover, the sup er-linear throughput scal ability holds fo r carrier-sensing networks wh en M is relati vely large. IV. I MPACT OF MPR ON EB IN WLAN MAC In this section, we study the c haracter istic behavior of WLAN M AC and EB when the chan nel has MPR capability. We first establi sh the rela tionship be tween transmission pro bability t p (or λ ) and EB parameters incl uding backoff factor r and minimum contention window 0 W . Bas ed on the analy sis, we will then study how the optimal backoff strategy changes with the MPR capability M . A. Transmission Probability We use an inf inite- state Mark ov chain, as shown in Fig. 4, to m o del of operat ion of EB with no retry limit. The reason for the lack of a retry limit is that i t is theor etic ally mor e inter estin g to lo ok at the limiting case when the retry limit is infinitely large. Having said this, we note that th e analysi s in our paper can be easily extended to the case where th ere is a retry limit. The state in the Mark ov chain in Fig. 4 is t he back off sta ge, whic h is also equa l to the number of retra nsmissions e xperien ced by the station. As mentioned in Section II, the contention window size is 0 i i Wr W = when a st ation is in state i . In the figure, c p denotes the conditional collision probability , which is the probability of a collision 13 seen by a packet be ing transmitted on the c hannel. Note that c p depends on the transmissi on probabilities of stations other than t he transmitting one. In our model, c p is ass umed to b e independent of the bac koff stage of the transmitting st ation. I n our nume rical results, we sh ow that the a n alyt ical results obtain ed under this assumption are very accurate when N is reaso nably lar ge. With EB, transmission probability t p is equal to the probability that the backoff timer of a station reaches zer o in a slot. Note that t he Markov pr ocess of MPR ne tworks is s imilar to the o nes in [10, 14] , excep t that th e condit ional col lision p robabil ity c p is different for 1 M > . Therefore, Eqn. (32) ca n be derived in a similar way as [10, 14] : 0 2( 1 ) (1 ) 1 c t cc rp p Wp r p − = −+ − (32) where 1 c rp < i s a necessary condition for th e steady state to be reachable. The detai led derivation of (32) is omitt e d due to page limit. Interested reade rs are referr ed to [10, 14] . Likewise, the conditional collision probability c p is equal to the probability that there are M or m ore stations out of th e remaini ng 1 N − stations conte nding for the cha nnel. We thus have the fo llowing rela tionship: 1 1 0 1 1( 1 ) M kN k ct t k N pp p k − − − = − ⎛⎞ =− − ⎜⎟ ⎝⎠ ∑ . (33) It can be ea sily shown t hat t p is a decr easing function of c p for any 1 r > in (32). Meanwhile, c p is an increasing function of t p in ( 33). Theref ore, the curves dete rmined by (32) a nd (33) have a uni que intersection corresponding to the ro ot of the non linear syste m. By so lving the nonlinear system (32)- (33) numerically for different N , we plot the analytical res u lts of t Np in Fig. 5. In the figures, B EB is adopted. That is, 2 r = . The min imum co ntention window si ze 0 16 W = o r 32. To validate the analy sis, the simulation results are plotted as markers in the figures. In the simulation, the data are collected by running 5,000,000 rounds after 1,000,000 rounds of warm up. From the figure s, we can see that the analytical results ma tch the simulatio ns very well. M o reover, it shows that t Np converges to a constant quant ity when N becomes large. Th is is a basic assump tion in the previous section when we calculated the asy mptotic throughput . The constant quantity that t Np converges to c an be calc u lated as f ollows. For large N , the num ber of attempts in a slot ca n be modeled as a Poisson proc ess. That is, 14 {} Pr ! k Xk e k λ λ − == (34) where lim t N Np λ →∞ = . (35) The conditional coll ision probability in this limiting case is given by {} 1 0 lim P r 1 ! k M c N k p XM e k λ λ − − →∞ = =≥ = − ∑ . (36) When th e system is ste ady , the total attempt rate lim t N Np λ →∞ = shou ld be fi nite. T here for e, 0 2( 1 ) lim lim 0 (1 ) 1 c t NN cc rp p Wp r p →∞ →∞ − = = −+ − , (37) whic h impl ies 1 lim c N p r →∞ = . (38) Combining (3 6) and (3 8), we get t he foll owing equa tion 1 0 1 1 ! k M k e kr λ λ − − = = − ∑ . (39) λ can the n be calculate d numeric ally from (39) gi ven M and r . To validat e the Poisson assum ption, we plot λ in Fig. 5. The fi gure shows that t Np calculated from (32) and (33), does converge to λ when N is large. Note that th e relations hip between t p , λ , and EB established above do not depend on the duration of the underlying ba ckoff slots, and t herefore can be applie d in both non-carrie r-sensi ng and carrier- sensing net works. Before leav ing this s ub-sectio n, we vali d ate an other assum ption adopted in Sect ion III. That is, EB guarantees a non -zero throughput wh en N approa ches infi nity. To t his end, t he throu ghput of slotted ALOHA is plotted as a functi on of N i n F i g . 6 w h e n B E B i s a d o p t e d . I t c a n b e s e e n t h a t t h e throughput s with th e same M co nverge to the same constant as N increases, regardles s of the minimum contention window 0 W . Similar phenom enon can also be obse rved in carrier-s ensing networks, as illustrated in Fig. 7, where the throu ghput of IE EE 802.11 WLAN with basic access mode is plotted with detailed system parameters listed in Table I. The asymptotic through put when N is very large depends only on the MPR capability M and the backo ff factor r . 15 B. Optimal B ackoff Factor In Section I II, we have investi g ated th e maximum network through put that is ac hieved by optim al transmission probability * () t p M and * () M λ . The previous sub-sect ion shows that transm ission probability is a functio n of b ackoff f actor r . Mathem atically, the optima l r that maximizes through put can be obtai ned by solving the e quation () 0 SM r ∂∂ = . In this secti on, we investigate how the optim al backoff factor r changes with th e MPR cap ability M . In Fig. 8 and Fig. 9, we p lot the through put as a function of r for both non-car rier sens ing networks and carrier-se nsing networ ks in basic-access mode . From the figure, we can see t hat the optimal r that maximizes throughput incr eases with M for moderate to large M . This observa tion can be intuiti vely explaine d for non-ca rrier-sensing netw orks by (14), (39), an d Lemma 1 as f o llows. E qns. (14) a nd (39) indicate that {} (, ) 1 Pr 1 1 SM XM R r λ λ ∞ = ≤− = − . (40) As Le mma 1 in dic ates, when M is large, (, ) SM R λ λ ∞ increases wi th M and eventu ally appro aches 1. Conseque ntly, r increases with M . As the figures show, the throughpu t decreases sharply when r m oves from the optimal * r to 1. On the other hand, the curve i s flat when r is l arger than the * r . Therefore, in order to avoid dramatic throughput d egradation, it is not wise to op erate r in the regio n betwee n 1 and * r . Note that when M is large, * r is larger than 2. This implies that the widel y used BEB m ight be far f rom optim al in MPR WLANs. To furth er see how well BEB works, we plot the ratio of the throughput obtain ed by BEB to the maximum achievable throu ghput in Fig. 10. The opti mal r that achieves the maximum throughput is plotted versus M in Fig. 11. In the figures, we can see t hat BEB only achie ves a small fraction o f the maximum achievable throu ghput when M is large in non-car rier-sensi ng and IEEE 802.11 bas ic-access mode. For ex ample, when 10 M = BEB only achieves about 80 percen t of the maximum thro ughput in non-carr ier-sen sing netw orks. In RT S/CTS mode, in co ntrast, the pe rformance of BEB is c lose to optimal for a large ra nge of M . Therefore, we arg ue from an e ngineering point of view that BEB (i.e., 2 r = ) is a good choice for RTS/CT S access schem e, while on the other ha nd tuning r to the optimal is important for non- carrier-sensing and b asic-access schemes. Moreover, it is always safe to set r to b e large enoug h, based on the obs e rvations fr om Fig. 8 and Fig. 9. 16 V. MPR P ROTOCO L FOR IEEE 802 .11 W LAN Having investigated the fundamental performance of WLANs with MPR, we now propose a practical protoco l to impleme nt MPR in the widely ad opted IEEE 802. 11 WLAN. In pa rticular, th e propose d protocol consists of both the MAC protocol and P HY signal pro cessing s cheme. To limit the scope, we focus on RT S/CTS mechanism in this sect ion. A brief discussion on the deploymen t of MPR in basic- access mode can be found in App endix C. Throughout this section, we assume that the MPR capability is brough t by the multiple antennas mounted a t the ac cess poin t (AP). This ass umptio n complies with t h e hardwa re request of t he latest MIMO-based WLAN stand ards. However, the proposed MAC-PHY p rotocol can be easi ly exte nded to CDMA network s, as the received signal structure s in multi-antenna an d CDMA system s are almost the same (r efer to Se ction II-C). A. MAC Protoc ol Descri ption The MAC protoc ol closel y follows the IEEE 802.11 RTS/ CTS access m echanism, as illustra ted in Fig. 12. A station with a packet to transmit fi rst sends an RTS frame to the AP. In our MPR MAC mode l, when mul tiple s tation s transmi t RTS frames at the sam e time, the AP can su ccessfully dete ct all the RTS frames if and only if the num ber of RTSs is no lar ger tha n M . When the number o f transmitting stations exceeds M , collisi ons occur and the AP cannot decode a ny of the RTSs. The stations will retransmit their RTS frames after a backo ff time period ac cording to the origin al IEEE 802.11 pr otocol. W hen the AP detects the RTSs successf ully, it responds, after a SIFS period, with a CTS frame that g rants tra nsmission perm issions to all t he requesting stat ions. Then the tra n smittin g stations will star t transmitting DATA frames af ter a SIFS, and the AP will acknowledge the recepti on of the DATA frames by an ACK fra me. The formats o f the RTS and Data frames are th e same as those defined in 802 .11, while the CTS and ACK frame s have been m odified to ac commodat e multiple tr ansmitting statio n s for MPR. In part icular, there are M receiver addre ss fields in the CTS a nd ACK frames to id entify up to M intended r ecipients. As descri bed above, our MPR MAC is ver y simila r to the ori ginal IE EE 802.11 MAC. In fact, to maintain this sim ilarity in the MAC layer, the cha llenge is pushed down to the physical layer. For example, in the propos ed MPR MAC, the AP is res p onsi ble to dec ode all the RTSs trans mitted simultaneously. However, due to the rando m-access nature W LAN, the AP has n o priori k nowledge of who the senders are and the channe l state infor mation (CSI) on the corr esponding links. This imposes a major cha llenge on the PHY layer, as th e MUD techniques in troduced in Section II, such as ZF and 17 MMSE cannot be directly appl ied. To tack le th ese problems, we introduce the physica l layer techniques in n ext subse ction. B. PHY-Layer Signal Processing Mechanism In this subsection, we propose a PHY mechanism to impl ement MPR in IEEE 802.11. The basic idea is as fol lows. RTS p ackets are typi cally transmitted at a lower d ata rate th an the da ta packets in IEEE 802.11. T his setting is part icularly suitab le for bli nd detecti on schem es which ca n separate the RTS packets without knowing the prior knowledge of th e senders’ identities and CSI [18 , 19]. Upon successfully decoding the RTS pa ckets, the AP can then identify th e senders of the packets. Training sequences, to be transmitted in the preamble of the data packe ts, are then allocated to these users to facilitate channel estimation during the data transmi ssion phase. Since the multiple stations transmit their data packet s at the same ti me, their training sequences should b e mutually or thogonal. In our system, n o more than M simultaneous tran smissions are allo wed. Therefore, a t otal of M ortho gonal sequences are required to b e predefined and mad e known to all st ations in th e BSS. The sequence allocation decision is sent to the users via the CTS packet. During th e data transm ission phase, CSI is estim ated from the orthogonal tra ining sequences that are transmit ted in the preamb le of the data p ackets. With the estima ted CSI, various MUD techn iques can be applied to separate the multiple data packets at the AP. Using coherent detection, data packets can be tran smitted at a much higher rate than th e RTS packet s without involving excessiv e computa tional com plexity. As MUD techni ques have been intr oduced in Sec tion II, we f ocus on the blind separati on of RTS packets i n this subsecti on . Assum e that there are K statio ns transm itting RTS packet s toget her. Then, the received signal in symbol duration n is given b y (4), where the ( m , k )th element of H denotes the chan nel coeff icie nt fr om us er k to the m th antenna at the AP. Assuming that the channel is constant ov er an R TS pa cket , whi ch is comp osed of N symbol periods, we obtain the followi ng bloc k form ulation of t he data = + YH X W (41) where [ ] ( 1 ), ( 2), ( ) N = Yy y y , [ ] ( 1 ), ( 2), ( ) N = Xx x x , and [ ] ( 1 ), ( 2), ( ) N = Ww w w . The pr oblem to be address ed here is the estim ation of the n umber of sour ces K , the channel matrix H , and the symbo l mat rix X , given the arra y output Y . a) Estimation of the number of so urces K 18 For an easy star t, we ignore the wh ite noise for t he moment an d have = YH X . The rank of H is equal to K if K M ≤ . Likewise, X is full-row-r ank when N i s m u c h l a r g e r t h a n K . Consequently, we have () rank K = Y and K is equal to the number of nonzero singular values of Y . W ith whi te noise added t o the data, K can be estimated from the number of singular values o f Y that are significant ly larger th an zero. b) Estimatio n of X and H In this pa per, we adopt the Finite Al ph abet (F A) based blind de tection al gorithm to estimate X and H , assumi ng K is known. The maximum-likelihood estimator yields the following separable least- squares mini mization problem [18] 2 min F ∈Ω − H, X YH X (42) where Ω is the finite alphabet to which t he elements o f X belon g, and 2 F ⋅ is the Frobenius norm. The minimization of (4 2) can be carried out in two step s. First, we minimize (42) with respect to H and obtain ( ) 1 ˆ HH − + == HY X Y X X X , (43) where () + ⋅ is the pseudo -inverse of a matrix. Sub stituting ˆ H back into (42), we obtain a new criter ion, which is a functio n of X only: 2 min H F ⊥ ∈Ω X X YP , (44) where () 1 H HH − ⊥ =− X PI X X XX , and I is the identity matrix. The global minimum of (44) can be obtained by enumerati ng over all possible choic es of X . R educed-complexit y iterative algorithms that solve (44) iterativ ely such as ILSP and ILSE were introduced in [19]. Not being one of the foci of this paper, the d etails of ILS P and ILSE are not cove red here. I nterested re aders are r eferred to [2 0] and the refere nces ther ein. Note that th e scheme pr oposed in this secti on is only one way of im p lemen ting MPR in WL ANs. It ensures t hat the orth ogonal tra ining se quences ar e tran sm itted in the preambles of data packets. This leads to highly reliable channel estimation tha t facilitates th e user of MUD techniques . In Appendix C, we briefly disc uss anothe r scheme tha t is applicabl e to both bas ic-access an d RTS/CTS access mo d es. VI. C ONCLUSION 19 With the recent advances in PHY-layer MUD techniques, it is no long er a physical constraint for the channel to acc ommodate only one ongoing pa cket transmissi on in WLANs. To fully util ize MPR capability of the PHY channel, it is essenti al to understand the fu ndamental impact of MPR on the MAC-layer. This paper has studied the char acteristic behavior of random-access WLANs with MPR. Not only does our analy sis lay down a theoreti cal foundation for the performance evaluation of WLANs with MPR, it is also a useful aid for syst em design in terms of setting operati ng parameters. Our analyt ical framework is genera l and appl ies to va rious WLANs including non-ca rrier-sensing and carrie r-sensi ng networks. In The orem 1 and 3, we have prove d that the th roughput in creas es super- linearly with M for both finite and in finite population cases. This is the case in non-carrier-sensing networks for al l M , and in carrier-sensing networks for large M . Moreov er, Th eor em 2 sh ows t hat th e throughput pe n alty d ue to distrib uted random ac cess dim i nishes w hen M approac hes infi nity. Suc h scalabilit y provides strong ince ntives for furthe r investi gations on engi neering and implem entation details of MPR system s. Based on the analysis, we f o und that the c ommonly depl oyed BEB schem e i s far from op timum in mo st syst ems except th e carrier-sensin g systems w ith RTS/C TS four-way handshake. In p articular, the optimum r increases with M for larg e M . We further note that the throughput d egrades sharply when r is smaller than the optimum value, while the curve is much flatte r when r exceeds th e optimu m. Therefo re, for sy stem robustness, i t is preferable to set r larg e enough to avoid dramati c throughpu t degradation. Having understood the fu ndamental behavior o f MPR, we propose a practical protocol to explo it the advanta ge of MPR i n IEEE 802.11-like WLANs. By incorporating a dvance d PHY-layer bli nd detection a nd MUD techniques, the protocol ca n im plem ent MPR in a f u lly dis tributed m anner with marginal m odification of MAC layer. R EFERENCES : [1] S. Verdu, Multiuser det ection , Cambridge University Press, Ca mbridge, UK, 1998. [2] P. B. Rapajic and D. K. Borah, “Adaptive MMSE ma ximum likelihood CDMA multiuser detection,” IEEE J. Select. Areas Commun. , vol. 1 7 , no. 12, pp. 211 0-2122, Dec. 1999. [3] I. E. Telatar, “Capacity of Multi-Antenna Gaussian Channels,” Euro. Trans. Telecommun., vol. 10, no. 6 , pp. 585–95, Nov. 1999 . [4] S. Ghez, S. Verdú, and S. Schwartz, “Stability pr operties of slotted ALOHA wi th multipacket reception capability,” IEEE Trans. Autom. Contro l, vol. 33, no. 7, pp. 640-649, Jul. 1988. [5] S. Ghez, S. Verdú, and S. Schwartz, “Optimal decentralized control i n the random access multipacke channel,” IEEE Trans. Autom. Control, vol. 34, no. 11, pp. 1153-1163, Nov. 1989. 20 [6] V. Naware, G. Mergen, and L. Tong, “Stabilit y and delay of finite-user slotted ALOHA with multipacket reception,” IEEE Trans. Inform. Theory, vo l. 51, no . 7, pp. 2636-2656, July 2005. [7] G. Mergen and L. Tong, “Stability and capacity of regular wireless networks,” IEEE Trans. Inform. Theory, vol. 51, no. 6, pp. 1938-1953, June 2005. [8] Q. Zhao and L. Tong, “A multiqueue service room MA C protocol for wireless networks with m ultipacket reception,” IEEE/ACM Trans. Network., vo l. 11, no. 1, pp. 125-13 7, Feb. 2003. [9] Q. Zhao and L. Tong, “A dynamic queue protocol for multi-access wireless networks with multipacke t reception,” IEEE Tram s. Wireless Commun., vo l. 3, no. 6, pp. 2221-2231, Nov. 2004. [10] G. Bianchi, “Performance analysis of the IEEE 802.11 distribu ted coordination function,” IEEE J. Select. Areas Commun. , vol. 18, no . 3, pp. 535-547, Mar. 2000. [11] J. Goodman, A. G. Gre enberg, N. Madras, and P. March, “Stability of binary exponential backoff,” J. ACM , vol. 35, no. 3, pp. 579-602, 1988. [12] H. Al-Ammal, L. A. Goldberg, and P. MacKenzie, “A n improved stability bound for binary exponential backoff,” Theory Com put. Syst. , vol. 30, pp. 229-244, 2001. [13] D. G. Jeong and W. S. Jeon, “Performance of an e xponential backoff scheme for slotted-A LOHA protocol in local wireless env ironment,” IEEE Trans. Veh. Tech. , vol. 44, no. 3, pp. 470-479, Aug. 1995. [14] B. J. Kwak, N. O. Song, and L. E. Miller, “Performance analysis of exp onential backoff,” IEEE/ACM Trans . Net working , vo l. 13, no. 2, pp. 343-355, April 2005. [15] W. Feller, “Sti rling ’s Formula,” An introduction to prob ability theory and its applica tions, vol. 1, 3rd ed. New York: Willey, pp. 50-53, 1968 . [16] ANSI/IEEE Std 802.3-1985, IEEE standards for local area netwo rks: carrier sen se multiple access with collision detection (CSMA /CD) access method and physical layer specifications , 1985. [17] IEEE Std 802.11-1997 L ocal and metropolitan area networks- specific requiremen ts-Part 11: Wireless LAN medium access control ( MAC ) and physical layer ( PHY ) specifications , Nov. 1997. [18] S. Talwar, M. Viberg, and A. Paulraj, “Blind separat ion of synchronous co-channel digital signa ls using an antenna array, Part I: Algorithms,” IEEE Trans. Signal Processi ng , vol. 44, no. 5, pp. 1184-1197, May 1996. [19] C.B. Papadias, A.J. Paulraj, “A con stant modulus algorith m for multiuser signa l separation in presen ce of delay spre ad using ant enna arra ys,” IEEE Signal Processing Letters , vol. 4, no. 6, pp. 178-181, June 1997. [20] S. Talwar, M. Viberg, and A. Paulraj, “Blind estimation of multiple co-channel digital signals using an antenna array,” IEEE Signal Processing Lett. , vol. 2, no. 1, pp. 29-31, Feb. 1994. [21] K. P. Choi, “On the medians of Gamma distributions and an equation of Ra manujan,” Proc. American Math. Society , vol. 121, no. 1, pp. 245-251, May 1994. [22] J. Chen and H. Rubin, “Bounds for the difference between median and mean of Gamma and Poisson distri butions,” Statist. Probab. Lett. 4 , pp. 28 1-283, 1986. A PPENDIX A: S UPER -L INEAR T HROUGHPUT S CALING IN WLAN S WITH F INITE P OPULATION Theorem 3 ( Super-linearity with finite popul ation ) : ** (1 ) ( ) 1 NN SM SM MM + ≥ + for all M N < From (12), we ha ve 21 {} 1 11 00 (, ) ( 1 ) (1 ) (1 ) 11 Pr 1 ( 1 , ) bits/sec 11 M kN k Nt t t k MM kN k kN k tt tt tt kk tt tt Nt tt N SM p R k p p k NN Np p Rp p R k p p kk pp Np p RX M S M p pp − = −− − − == ⎛⎞ =− ⎜⎟ ⎝⎠ ⎛⎞ ⎛⎞ =− − − ⎜⎟ ⎜⎟ −− ⎝⎠ ⎝⎠ =≤ − − − −− ∑ ∑∑ (A1) and {} (1 , ) P r ( , ) 11 tt N tN t tt Np p SM p R X M SM p pp += ≤ − −− . (A2) Meanwhile, {} 1 1 (1 , ) ( 1 ) ( , ) (1 ) P r 1 M kN k Nt t t N t k N SM p R k p p SM p R M X M k + − = ⎛⎞ += − = + + = + ⎜⎟ ⎝⎠ ∑ (A3) Substituting (A3) to (A2), we get { } ( ) { } (,) P r 1 ( 1 ) P r 1 , N tt t t SM p R N p X M R p M X M M N p =≤ − − + = + ∀ < . (A4) At the optimal * () t p M , the derivative (,) 0 Nt t SM p p ∂∂ = . Thus, {} {} * * * () () () (,) 1 Pr ( 1 ) 1 ( 1 ) Pr 1 0 tt tt tt Nt t pp M pp M pp M t SM p p RN X M R M M X M p = = = ∂ = ∂ ⎛⎞ ≤+ + − + = + = ⎜⎟ ⎝⎠ , (A5) Combining (A4) an d (A5), () {} () {} {} * * * ** () * * () () (,) (, () ) () ( 1) ( ) ( 1) P r 1 ( 1) 1 ( ) P r 1 (1 ) P r 1 tt tt tt Nt Nt t t pp M t t pp M pp M SM p S M pM pM p RM p M M X M RM p M X M RM M X M = = = ∂ = ∂ −+ − + = + − + − = + =+ = + (A6) It is obviou s that { } * ** * () ( 1 ,( 1 ) ) ( 1 ,( ) ) ( ,( ) ) ( 1 ) P r 1 t Nt Nt N t p M SM p M SM p M SM p M R M X M ++ ≥ + = + + = + (A7) Substituting (A6) to (A7), we have * ** * (, ( ) ) 1 ( 1 ,( 1 ) ) ( ,( ) ) ( ,( ) ) Nt N t Nt Nt SM p M M SM p M SM p M SM p M M M + ++ ≥ + = . (A8) Hence, ** (1 ) ( ) 1 NN SM SM M N MM + ≥∀ < + . □ 22 A PPENDIX B Proof of Lemma 1 (b) and 1(c) {} () () 1 0 1 (1 ) 00 () P r 1 ! 1 !! k M k kk M MM M z kk SM R X M R e k zz Rz e Rz e Rz e z kk λ λλ λ λ λλ λλ λλ λ − − ∞ = −∞ −− − − − − == =≤ − = ≤≤ = ∀ < ∑ ∑∑ (B1) Let (1 ) () Mz gz R z e λ λ −− = be th e upper bound o f () SM ∞ . By solving () 1( 1 ) ( 1 ) () 0 Mz M z gz RM z e z e z λλ λλ −− − − − ∂ =− + = ∂ (B2) it can be easily found that * zM λ = mini mi ze s () g z and * 1 () M M M gz e RM λ λ λ ⎛⎞ − ⎜⎟ ⎝⎠ ⎛⎞ = ⎜⎟ ⎝⎠ . (B3) Since * 1 z < , M λ > . Let cM λ = where 1 c > . Eqn. (B3) can be written as () () () () * 11 () M M cc gz ce ce R λ −− == . (B4) Due to Eqn. (23 ) () () * 1 () () lim li m li m 0 M c MM M SM gz ce RR λλ − ∞ →∞ →∞ →∞ ≤ == (B5) On the other ha nd, it is obvi ous that () 0 SM R λ ∞ ≥ (B6) Combining (B 5) and (B6), we have () lim 0 M SM M R λ λ ∞ →∞ = ∀> , (B7) and Lemm a 1(b) follows . To prove Lem ma 1(c), we note th at the median of Poisson dis t ribution is bo unded as follows [2 1]-[22]: log 2 medi an 1 3 λ λ −≤ ≤ + . (B8) When M λ = and M →∞ , the m edian a pproac hes M . Acco rding to the first equ ality of (19 ), {} { } () lim lim Pr 1 lim Pr 0.5 MM M SM XM XM R λ ∞ →∞ →∞ →∞ =≤ − =≤ = . □ 23 A PPENDIX C MPR IN IEEE 802 .11 B ASIC A CCESS M OD E In Section VI, we have introduced a MAC-PHY pro tocol for implementing MPR in IEEE 802.11 RTS/CTS WLANs. The protocol relies on the blind sepa ration of low-r ate RTS packets to identify senders and allocate orthogon al training sequences to them. In this section, we briefly describe an alternative protocol that is applica ble to both basic-ac cess m o de. The protoc ol works as foll o ws. Upo n transmitti ng a data packet, a statio n randomly pic ks a training sequence f rom a pool of orth ogonal sequences. If m ore than one statio n picks the sa me sequenc e, then the receiver cannot resolve these t ransmissions an d a collision happen s between the packets involved. For other packets that have selected a unique orthogonal seque nce, the receiver ca n estim ate their CSI, and conseq uently appl y MUD schem es to separate the packets. Note that the number of orthogonal sequences is p roportional to th e length of the tr aining sequences. On one hand, a small number of orthogon al sequences lead to a higher probabili ty of collision . On th e other hand, having more sequ ences leads to a larg er overhead for chann el estimation . Therefore, the number of seque nces is a paramete r to be optimized in this protoc ol. The propose d protoc ols have their respect ive disadvantages and advantages. T he one propos ed in this section requires a lower computational complexity , as there is no n eed to do blind detection . However, collision may happen e ven if less than M station s attemp t to tran smit tog ether , when mor e than one station picks th e same sequence. In contrast, the on e proposed in Section VI guarantees th at packets c an be resolved as long as the number of attempts is smaller than M (assuming small noise). It also ensures that there is no collision b etween training se quen ces of data packets. Ho wever, the computational complexity could be h igh if the RTS packets are transmitted at a high rate . 24 TABLE I S YSTEM P ARAMETERS U SE D IN C ARRIER -S ENSING N ETWORKS (A DOPTED FROM IEEE 802.11 G ) Packet payload 8184 bits MAC header 272 bits PHY overhead 26 µs ACK 112 bits + PHY overhea d RTS 160 bits + PHY overhea d CTS 112 bits + PHY overhea d Basic rate 6 Mbps Data rate 54 Mbps Slot time σ 9 µs SIFS 10 µs 0 20 40 60 80 100 120 0.35 0.4 0.45 0.5 0.55 0.6 0.65 0.7 0.75 0.8 0.85 M S ∞ * (M)/MR Fig. 1: Super-linear scalability of the throughput of non-carrier sensing slotted ALOHA netwo rks 25 0 2 4 6 8 10 12 14 16 18 20 0 50 100 150 200 250 300 350 400 450 M S ∞ (M) basic access RTS/CTS Fig. 2 Optim al throughp ut of carri er-sensin g net works 0 50 100 150 200 16 18 20 22 24 26 28 M S ∞ (M)/M basic access RTS/CTS Fig. 3: Super-linear scalability of the thro ughput of carrier-sensing networks 26 Fig. 4: Markov chain model for the backoff stage. 0 20 40 60 80 100 120 140 160 180 200 0 0.5 1 1.5 2 2.5 3 3.5 4 4.5 5 N Np t analysis with W 0 =16 analysis with W 0 =32 simulation with W 0 =16 simulation with W 0 =32 λ M =5 M =1 M =2 Fig. 5: Plots of Np t versus N when r = 2; li n es are analytical results calculated from (2) and (3), markers are simulation results. 27 0 20 40 60 80 100 120 140 160 180 200 0 0.5 1 1.5 2 2.5 3 N S N ( M , p t )/ R analysis with W 0 =16 analysis with W 0 =32 simulation with W 0 =16 simulation with W 0 =32 S ∞ ( M , p t )/ R M =5 M =1 M =2 Fig. 6 : Normalized throughput of non-carrier -sensing slotte d ALOHA networks when 2 r = 0 20 40 60 80 100 120 140 160 180 200 20 30 40 50 60 70 80 90 N S N ( M , p t ) (Mbps) analysis with W 0 =16 analysis with W 0 =32 simulation with W 0 =16 simulation with W 0 =32 S ∞ ( M , λ ) M =5 M =1 M =2 Fig. 7 : Throughput of carrier-sensing basic-access netw orks when 2 r = 28 1 2 3 4 5 6 7 8 9 10 0 1 2 3 4 5 6 r S ∞ ( M , λ )/ R M=1 M=5 M=10 Fig. 8: Throughput versus r f o r non-ca rrier-sensing slotted ALOHA networks 1 2 3 4 5 6 7 8 9 10 0 20 40 60 80 100 120 140 160 180 200 r S ∞ ( M , λ ) (Mbps) M =1 M =5 M =10 Fig. 9: Throughp ut vers us r for carrier-sensing networks with basic-access mode 29 0 2 4 6 8 10 12 14 16 18 20 0.7 0.75 0.8 0.85 0.9 0.95 1 M BEB throughput / S ∞ * (M) basic access RTS/CTS access non−carrier−sensing Fig. 10 : R atio of the t h roughp ut of BEB t o maxim al throughput ve rsus M 0 2 4 6 8 10 12 14 16 18 20 1 2 3 4 5 6 7 8 M r * basic access RTS/CTS access non−carrier−sensing Fig. 11 : Optimal r versus M 30 Fig. 12: Time line example for the MPR MAC
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment