Secrecy Capacity Region of a Multi-Antenna Gaussian Broadcast Channel with Confidential Messages
In wireless data networks, communication is particularly susceptible to eavesdropping due to its broadcast nature. Security and privacy systems have become critical for wireless providers and enterprise networks. This paper considers the problem of s…
Authors: Ruoheng Liu, H. Vincent Poor
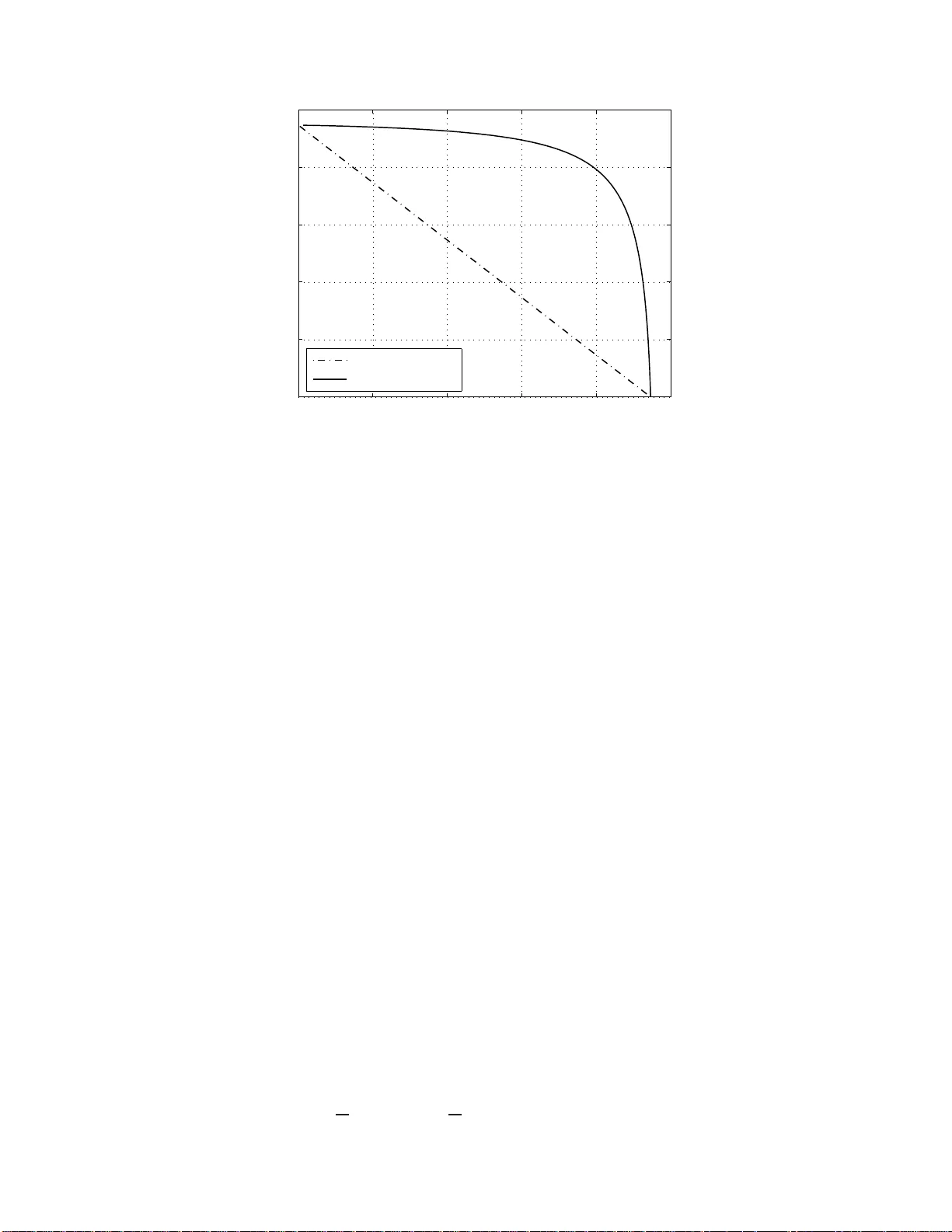
Secrecy Capacity Region of a Multi-Antenna Gaus sian Broadcast Channel with Confidential Mes sages Ruoheng Liu and H. V incent Poor Abstract In wireless data networks, commun ication is particu larly suscep tible to eavesdroppin g due to its bro adcast nature. Security and priv a cy systems have b ecome critical for wireless providers an d enter prise ne tworks. This paper considers the problem of secret commun ication over the Gau ssian b roadcast chan nel, where a multi-antenn a transmitter sends ind ependen t confidential m essages to two users with info rmation-theo r etic secrecy . That is, each user would like to o btain its o wn con fidential message in a r eliable a nd saf e manner . This com munication mode l is referr ed to as the mu lti-antenna Gaussian br oadcast channel with con fidential messages (MGBC-CM). Unde r this com munication scenario, a secret dir ty-paper coding schem e and the correspon ding achie vable s ecrecy rate region are first dev eloped based o n Gaussian c odeboo ks. Ne xt, a co mputable Sato-ty pe outer boun d on the secr ecy capacity region is provided f or the MGBC -CM. Furthermo re, the Sato-type outer b ound prove to be c onsistent with the bound ary of the secret dir ty-paper codin g achiev able rate region, and h ence, the secrecy cap acity region of th e MGBC-CM is established . Finally , two numerica l examples d emonstrate that both users can achieve positive rates simultaneou sly u nder the inform ation-theo retic secrecy requireme nt. Index T erms secret comm unication, broad cast ch annels, multiple a ntennas, infor mation-the oretic secrecy I . I N T RO D U C T I O N The need for ef ficient, reliable, and secret data com munication ov er wireless networks has been rising rapidly for decades. Due to its broadcast n ature, wireless communi cation is particularly su sceptible to ea vesdropping. The inherent problemati c nature of wireless networks exposes not only the risks and vulnerabilities that a malicious user can e xploit and se verely comprom ise the network, but also mu ltiplies information confidentiality concerns with respect to in-network terminals . Hence, security and p ri vac y systems hav e become critical for wireless providers and enterprise networks. This research was supported by the National Science Foundation under G rants ANI-03-38807 and CNS -06-2563 7. T he material i n this paper was presented in part at the First International W orkshop on Information Theory for S ensor N etworks, Santa Fe, NM, June 18 - 20, 2007 Ruoheng Liu and H. V incent Poor are with Department of Electrical Engineering, Princeton Univ ersity , Pr inceton, NJ 08544 , USA, email: { rliu,poor } @princeton .edu. 2 p( x |w 1 ,w 2 ) us er 1 us er 2 t rans mi tter (W 1, W 2 ) Y 1 Y 2 X s tochast i c encoder Z 1 Z 2 h g dec W 1 H(W 2 | Y 1 ) dec W 2 H(W 1 | Y 2 ) Fig. 1. Multiple-antenna Gaussian broadcast channel wi th confidential message In this work, we consi der multi ple antenna secret broadcast in wireless networks. This research is inspired by the semin al paper [ 1], in whi ch W yner int roduced the so-called wir etap channel and p roposed an information theoretic approach to secret c ommun ication schemes. Under the assumption that the c hannel to the eavesdropper is a degraded version of t hat to the d esired receiver , W yner characterized th e capacity- secrecy tradeoff for the discrete memoryless wi retap channel and sho wed that secret communication is possible without sharing a secret ke y . Later , t he result was e xtended by Csisz ´ ar and K ¨ orner who determined the secrecy capacity for the non -degraded br oadcast channel (BC) with a singl e confidential message intended for on e of the us ers [2]. In more general wireless network scenarios, secret com munication may in volve mul tiple users and multiple antennas. Motivated by wireless commu nication, where transmi tted signals are broadcast and can be recei ved by al l u sers within the communication range, a significant research effort has been i n vested in th e study of the information-th eoretic limits of secret commun ication in different wireless network en vironm ents including multi-user com munication with confidential messages [3]–[11], secret wireless communication on fading c hannels [12]–[15], and the Gaussian multiple-input single-output ( MISO) and multiple-in put multiple-output (MIMO) wiretap channels [16]–[21]. These issues mot iv ate us to study the mult i-antenna Gaussi an BC with confidential messages (MGBC- CM), in which independent confidential messages from a multi-antenna transmitter are to be communicated to two users. The corresponding broadcast communication model is shown in Fig. 1. Each user would like to obtain its own message reliably and confidentially . T o give insight into this problem, we first con sider a sing le-antenna Gaussian BC. Note t hat this channel is degraded [22], which means that i f a message can be successfully decoded by the inferior user , then the 3 superior user is also ens ured of decoding it. Hence, the secrecy rate of t he i nferior user is zero and this problem i s reduced to t he scalar Gaussian wiretap channel problem [23] whose s ecrec y capacity is now the maximum rate achiev able by the superior user . Thi s analy sis giv es rise to the question : can the transmitt er , in fact, commu nicate with bot h users confidentially at non zero rate under some other condition s? Rough ly speaking, the answer is in the affi rmative. In particular , the transmi tter can communicate when equipp ed with sufficiently separated multip le antennas. W e here hav e two goals motiv ated directly by questions arising in practice. The first is to determine the condition und er which both users can obtain t heir own confidential m essages in a reli able and safe m anner . This is equi valent to e va luating the secrec y capacity region for the MGBC-C M. The second is to show how the transmitt er should broadcast confidentiall y , whi ch i s e quiv alent to designing an achie vable secr et coding scheme. T o thi s end , we first describe a secret dirty-paper coding (DPC) scheme and deri ve the corresponding achie vable sec recy rate region based on Gaussian codebooks. The secret DPC is based on double-binning [24] whi ch enables bot h joi nt encoding and preserving confidentiality . Next, a computable Sato-type outer bound on the secrec y capacity region is de veloped for the MGBC-CM. Furthermore, the Sato-type out er boun d prove to be cons istent with the boundary o f the secret dirty-paper cod ing achie vable rate region, and hence, the secrecy capacity region of the MG BC-CM is establi shed. Finally , two num erical examples dem onstrate that b oth users can achie ve posi tiv e rates sim ultaneously under the information-theoretic secrecy requirement. The remainder of this paper is organized as follows. The sy stem model and definitions are int roduced in Section II. The main results on the secrecy capacity region o f the MGBC-CM is state in Section III . The achiev abili ty proof associated with the secret DPC schem e i s established in Section IV. The con verse proof is derived in Section V b ased on the Sato-type o uter bound. Finally , Section VI shows numerical examples and Section VII point s our our conclus ions. I I . S Y S T E M M O D E L A N D D E FI N I T I O N S A. Channel Model W e consider t he communication o f confidential messages to two users over a Gaus sian BC via t ≥ 2 transmit-antennas. Each u ser is equi pped wi th a si ngle receive-antenna. As shown in Fig. 1, t he t ransmitter sends independent confidential messages W 1 and W 2 in n channel uses with nR 1 and nR 2 bits, re spectively . The message W 1 is destined for us er 1 and eav esdropped by us er 2, whereas the m essage W 2 is destined 4 for us er 2 and eavesdropped by us er 1. This com munication scenario is referre d to as the multi-antenna Gaussian BC with con fidential messages . The Gaussian BC is an additive noi se channel and the received symbols at u ser 1 and u ser 2 are represented using the following expression: y 1 ,i = h H x i + z 1 ,i y 2 ,i = g H x i + z 2 ,i , i = 1 , . . . , n (1) where x i ∈ C t is a complex input vector at ti me i , { z 1 ,i } and { z 2 ,i } correspond t o two independent , zero-mean, unit-variance, compl ex Gaussian noise sequences, and h , g ∈ C t are fixed, compl ex channel attenuation vectors imposed on user 1 and user 2, respectively . The channel i nput is constrain ed by tr( K X ) ≤ P , where P is th e av erage to tal power limitati on at the transmit ter . W e also assume that both the transm itter and users are awar e of the attenuation vectors. B. Important Channel P arameters for the MGBC-CM For th e M GBC-CM, we are interested in the following important p arameters, whi ch are related to the generalized eigen va lue problem (see Appendix I for the details). Let λ 1 and e 1 denote the largest generalized eigen value and th e corresponding normalized eigen vector of the pencil ( I + P hh H , I + P gg H ) so th at e H 1 e 1 = 1 and ( I + P hh H ) e 1 = λ 1 ( I + P gg H ) e 1 . (2) Similarly , we define λ 2 and e 2 as the largest generalized eigen value and t he corresponding normalized eigen vector of the pencil ( I + P gg H , I + P hh H ) so th at e H 2 e 2 = 1 and ( I + P gg H ) e 2 = λ 2 ( I + P hh H ) e 2 . (3) An useful prop erty o f λ 1 and λ 2 is described i n the following l emma. Lemma 1: For any channel attenuati on vector pair h and g , the largest generalized eigenv alues of th e pencil ( I + P hh H , I + P gg H ) and the pencil ( I + P gg H , I + P hh H ) satisfy λ 1 ≥ 1 and λ 2 ≥ 1 . (4) Moreover , i f h and g are linearly i ndependent, then b oth λ 1 and λ 2 are strictly greater than 1 . Pr oof : W e provide t he p roof in Appendi x I. 5 C. Defini tions W e now define the secret codebook, the probabilit y of error , the secrecy lev el, and the secrecy capacity region for the MGBC-CM as follows. An (2 nR 1 , 2 nR 2 , n ) secr et codebook for the MGBC-CM consist s of the following: 1) T wo message sets W 1 = { 1 , . . . , 2 nR 1 } and W 2 = { 1 , . . . , 2 nR 2 } . 2) An stochastic encoding function is specified by a matrix of c onditio nal probability density p ( x n | w 1 , w 2 ) , where x n = [ x 1 , . . . , x n ] ∈ C t × n , w k ∈ W k , and Z x n p ( x n | w 1 , w 2 ) = 1 . 3) Decoding functions φ 1 and φ 2 . The decoding function at user k is a d eterministic mapping φ k : Y n k → W k . Remark 1: T o increase the randomness of transm itted messages, we consider a st ochastic encoder at th e transmitter . In other words, p ( x n | w 1 , w 2 ) is t he conditi onal probability density th at the messages ( w 1 , w 2 ) are joi ntly encoded as the channel input s equence x n . At the receiv er ends , the error performance and the secrecy lev el are e valuated by the following performance measures. 1) The reliability is m easured by the maxi mum error probability P ( n ) e , max P ( n ) e, 1 , P ( n ) e, 2 where P ( n ) e,k is the error probability for user k given by P ( n ) e,k = 2 − n ( R 1 + R 2 ) X w 1 ∈W 1 X w 2 ∈W 2 Pr φ k ( Y n k ) 6 = w k ( w 1 , w 2 ) sent . (5) 2) The secrecy l e vels with respect to confidential m essages W 1 and W 2 are measured, respectively , at user 2 and user 1 wi th respect to the equivocation rates 1 n H ( W 2 | Y n 1 ) and 1 n H ( W 1 | Y n 2 ) . (6) A rate pair ( R 1 , R 2 ) is said to be achiev able for the MGBC-CM if, for any ǫ > 0 , th ere exists an 6 (2 nR 1 , 2 nR 2 , n ) code that satisfies P ( n ) e ≤ ǫ , and t he informatio n-theoretic secrecy requirement 1 nR 1 − H ( W 1 | Y n 2 ) ≤ nǫ and nR 2 − H ( W 2 | Y n 1 ) ≤ nǫ. (7) The secr ecy capacity r e gion C MG s of the MGBC-CM is the closure of the set of all achiev abl e rate pairs ( R 1 , R 2 ) . I I I . M A I N R E S U LT : S E C R E C Y C A PAC I T Y R E G I O N F O R T H E M G B C - C M The two-user Gaussian BC w ith m ultiple transmi t-antennas is non-degraded. For this channel, we hav e the follo wing closed-from result on the secrecy capacity region under the inform ation-theoretic secrecy requirement. Theor em 1 : W e cons ider an MGBC-CM mo deled i n (1). Let γ 1 ( α ) = 1 + αP | h H e 1 | 2 1 + αP | g H e 1 | 2 , (8) γ 2 ( α ) be the largest generalized eigen value of the pencil I + (1 − α ) P 1 + αP | g H e 1 | 2 gg H , I + (1 − α ) P 1 + αP | h H e 1 | 2 hh H , (9) and R MG ( α ) denote t he union o f all ( R 1 , R 2 ) satisfyi ng 0 ≤ R 1 ≤ log 2 γ 1 ( α ) and 0 ≤ R 2 ≤ log 2 γ 2 ( α ) . (10) The secrecy capacity region of the MGBC-CM is C MG s = co ( [ 0 ≤ α ≤ 1 R MG ( α ) ) , (11) where co {S } denotes th e con vex hull o f the set S . Pr oof : W e provide the achiev abi lity proof in Section IV based on a s ecret dirty paper coding scheme, and show the con verse proof in Section V based on a Sato-type outer bo und. 1 This definition corresponds to t he so-called weak secr ecy-ke y rate [25]. A st ronger measurement of the secrecy level has been defined by Maurer and W olf in terms of absolute equi voca tion [25], where t he authors have sho wn that the former definition could replaced by the latter without any r ate penalty in a wiretap channel. 7 Based on Theorem 1, we can calculate the b oundary of the secrecy capacity region C MG s by choosi ng α t o trade off the rate R 1 for the rate R 2 . In particular , when α = 1 , we obtain γ 1 (1) = e H 1 ( I + P hh H ) e 1 e H 1 ( I + P gg H ) e 1 = λ 1 (12) and γ 2 (1) = 1 (13) where (12) follows from the definitions of λ 1 and e 1 in (2). Theorem 1 implies that the rate p air (log 2 λ 1 , 0) is achiev able. In fact, t his rate pair is t he corner poi nt corresponding to t he maximum achiev able rate of user 1 in t he capacity region C MG s . Cor ollar y 1: For t he M GBC-CM, the maxim um secrecy rate of user 1 is giv en by R 1 , max = max 0 ≤ α ≤ 1 log 2 γ 1 ( α ) = log 2 λ 1 (14) where λ 1 is the l ar gest generalized eigen value of the pencil ( I + P hh H , I + P gg H ) . Pr oof : See Appendix II. Example 1: (MISO W i retap Channels) A special case of the M GBC-CM model is t he Gaussian MISO wiretap channel studied i n [16], [18], [20], where t he transmitter sends confidential in formation to only one user and treats another user as an eavesdropper . Let us consider a Gaussian MISO wiretap channel modeled in (1), where user 1 is the legitimate receive r and user 2 is the eavesdropper . Corollary 1 im plies that the s ecrec y capacity of the Gaussian MISO wiretap channel corresponds to the corner point of C MG s . Hence, the s ecrec y capacity of the Gaussian M ISO wiretap channel is given by C MISO s = log 2 λ 1 , (15) which coincides with the result of [18]. For t he MGBC-CM, the actions of user 1 and user 2 are symmetric to each other , i.e., each user decodes it s own message and ea vesdrops th e confidential information belonging to ano ther user . Based on symmetry of th is two-user BC m odel, we can express the secrecy capacity region C MG s in an alternative way . Cor ollar y 2: For an MGBC-CM modeled in (1), the secrecy capacity region can b e written as C MG s = co ( [ 0 ≤ β ≤ 1 R MG − 2 ( β ) ) (16) 8 where R MG − 2 ( β ) denotes the uni on of all ( R 1 , R 2 ) satisfyi ng 0 ≤ R 1 ≤ log 2 ξ 1 ( β ) and 0 ≤ R 2 ≤ log 2 ξ 2 ( β ) , (17) ξ 1 ( β ) is t he l ar gest generalized eigen value of the pencil I + (1 − β ) P 1 + β P | h H e 2 | 2 hh H , I + (1 − β ) P 1 + β P | g H e 2 | 2 gg H (18) and ξ 2 ( β ) = 1 + β P | g H e 2 | 2 1 + β P | h H e 2 | 2 . (19) Pr oof : The deriv ation follows from the same approach of the p roof for Th eorem 1 by rev ersing t he roles of user 1 and user 2 . Remark 2: Theorem 1 and Corollary 2 imply t hat if α and β satisfy t he implicit function γ 1 ( α ) = ξ 1 ( β ) , then R MG ( α ) = R MG − 2 ( β ) . For example, it i s easy to check R MG (1) = R MG − 2 (0) . Now , by applying Corollary 2 and setting β = 1 , we can show that the rate pair (0 , log 2 λ 2 ) i s th e corner point correspond ing to the maximum achiev able rate of user 2 in the capacity region C MG s . Cor ollar y 3: For t he M GBC-CM, the maxim um secrecy rate of user 2 is giv en by R 2 , max = log 2 λ 2 (20) where λ 2 is the l ar gest generalized eigen value of the pencil ( I + P gg H , I + P hh H ) . Pr oof : The deriv ation follows from the s ame app roach of the proof for Corollary 1. Corollaries 1 and 3 imply that for the MGBC-CM, both users can achie ve positive rates with i nformation- theoretic secrecy if and on ly if λ 1 > 1 and λ 2 > 1 . Lemma 1 illusrtates that t his condition can be ensured when the attenuat ion vectors h and g are lin ear independent. I V . S E C R E T D P C C O D I N G S C H E M E A N D A C H I E V A B I L I T Y P RO O F W e first briefly re view t he prior information-theoretic result on the achiev able rate region for the BC with confident ial messages (BC-CM) o f [24]. Based on thi s result, we develop the achiev able secret coding 9 scheme for the MG BC-CM and find t he capacity achieving input cov ariance matrix. A. Double-Binning Inner bound for t he BC-CM An achiev able rate region for the BC-CM has been est ablished in [24] based on a double-bin ning scheme th at enables b oth joint encoding at the t ransmitter by using Slepian-W olf binning [26] and preserving confidential ity by u sing random binning. W e sum marize t he double-binn ing codeboo k and encoding strategy in Appendix III for completeness. Lemma 2: ( [24, Theorem 3]) Let V 1 and V 2 be auxi liary random variables, Ω denot e the class of joint probabil ity dens ities p ( v 1 , v 2 , x , y 1 , y 2 ) that factor as p ( v 1 , v 2 ) p ( x | v 1 , v 2 ) p ( y 1 , y 2 | x ) , (21) and R I ( π ) denot e the union o f all ( R 1 , R 2 ) satisfying 0 ≤ R 1 ≤ I ( V 1 ; Y 1 ) − I ( V 1 ; Y 2 | V 2 ) − I ( V 1 ; V 2 ) (22) and 0 ≤ R 2 ≤ I ( V 2 ; Y 2 ) − I ( V 2 ; Y 1 | V 1 ) − I ( V 1 ; V 2 ) (23) for a given joint prob ability density π ∈ Ω . For the BC-CM, any rate p air ( R 1 , R 2 ) ∈ co ( [ π ∈ Ω R I ( π ) ) (24) is achiev able. The proof of Lem ma 2 can be found in [24 ]. Here, we provide an alternative view on this result . Since randomization can increase s ecrec y , we employ stochastic encoding at the transmitt er so that t he size of the secret codebook is larger t han t he si ze of m essage s et. Let R ′ denote the redun dant rate used to prev ent the con fidentiality . The best known achie vable region for a general BC was found by Marton of [27 ]. Now , for a given joint densi ty p ( v 1 , v 2 , x ) , a special case of the M arton sum rate (without a common rate) is gi ven by R 1 + R 2 + R ′ ≤ I ( V 1 ; Y 1 ) + I ( V 2 ; Y 2 ) − I ( V 1 ; V 2 ) . (25) On the o ther hand, the t otal (both the i ntended and t he ea vesdropped) information rate ob tained by user 2 is li mited by I ( V 1 , V 2 ; Y 2 ) . Intui tiv ely , to keep t he message W 1 secret from user 2, t he redundant rate R ′ 10 should satis fy t hat R 2 + R ′ ≥ I ( V 1 , V 2 ; Y 2 ) . (26) This implies that to s atisfy the i nformation-theoretic secrec y requirement, the achie vable secrecy rate o f user 1 can be written as R 1 ≤ [ I ( V 1 ; Y 1 ) + I ( V 2 ; Y 2 ) − I ( V 1 ; V 2 )] − I ( V 1 , V 2 ; Y 2 ) . (27) Similarly , the achie vable secrecy rate of us er 2 can be written as R 2 ≤ [ I ( V 1 ; Y 1 ) + I ( V 2 ; Y 2 ) − I ( V 1 ; V 2 )] − I ( V 1 , V 2 ; Y 1 ) . (28) Bounds (27) and (28) lead t o the achiev able secrecy rate region in Lemm a 2 . Remark 3: For the BC with confidential messages, one can employ joint encodi ng at the transmitter . Howe ver , to preserve confidentiali ty , both achie vable rate expressions i n (22) and (23) include a penalty term I ( V 1 ; V 2 ) . Hence, compared wit h Marton’ s achiev able region [27] for a general BC, here, one need to pay “doub le” for joi ntly encodi ng at the transm itter . B. Secr et DPC Scheme for the MGBC-CM The achiev able strategy i n Lemma 2 introduces a double-binni ng coding scheme. H o wev er , when the rate region (24) is used as a constructive technique, it not clear how to choose the auxiliary random var iables V 1 and V 2 to im plement the double-binni ng codebook, and hence, one has to “guess” the density of p ( v 1 , v 2 , x ) . Here, we employ t he DPC technique with the do uble-binning code structure to dev elop the secr et DPC (S-DPC) achiev able rate region for the MG BC-CM. For the MGBC-CM, we consi der a secret dirty-paper encoder with Gaussian codebooks as follows. First, we sperate the channel i nput X into t wo random vectors U 1 and U 2 so that U 1 + U 2 = X . (29) 11 W e choose U 1 and U 2 as well as auxi liary random variables V 1 and V 2 as follows: U 1 ∼ C N (0 , K U 1 ) , U 2 ∼ C N (0 , K U 2 ) , independent of U 1 V 1 = U 1 + bh H U 2 and V 2 = U 2 (30) where K U 1 and K U 2 are cov ariance matrices of U 1 and U 2 , respectively , and b = K U 1 h 1 + h H K U 1 h . (31) Based on the conditions (30) and Lemma 2, we obtain a S-DPC rate region for the MGBC-CM as foll ows. Lemma 3: [S-DPC region] Let R S − DPC I ( K U 1 , K U 2 ) denote th e union of all ( R 1 , R 2 ) satisfyi ng 0 ≤ R 1 ≤ log 2 1 + h H K U 1 h 1 + g H K U 1 g (32) and 0 ≤ R 2 ≤ log 2 1 + g H ( K U 1 + K U 2 ) g 1 + h H ( K U 1 + K U 2 ) h + log 2 1 + h H K U 1 h 1 + g H K U 1 g . (33) Then, any rate pair ( R 1 , R 2 ) ∈ co [ tr( K U 1 + K U 2 ) ≤ P R S − DPC I ( K U 1 , K U 2 ) (34) is achiev able for the MGBC-CM. Pr oof : See the Appendi x III. Remark 4: W e choo se the random variables U 1 , U 2 , V 1 , V 2 and X as the same as the classical DPC strategy (e.g., see [28], [29]). Ho wever , the S-DPC scheme is dif ferent from the classical one. The codebook and the codin g s tructure of t he S-DPC scheme is based on the dou ble-binning (see Appendix III). C. Achievability Pr oof of Theor em 1 The S-DPC achiev able rate region (34) requires optimi zation of t he cov ariance m atrices K U 1 and K U 2 . In order t o achieva ble the boundary of C MG s , we cho ose K U 1 and K U 2 as follows: K U 1 = αP e 1 e H 1 and K U 2 = (1 − α ) P c 2 ( α ) c H 2 ( α ) , for 0 ≤ α ≤ 1 (35) 12 where e 1 is defined in (2) and c 2 ( α ) is a normali zed eigen vector of the pencil (9) corresponding to γ 2 ( α ) so that c H 2 ( α ) c 2 ( α ) = 1 and I + (1 − α ) P 1 + αP | g H e 1 | 2 gg H c 2 ( α ) = γ 2 ( α ) I + (1 − α ) P 1 + αP | h H e 1 | 2 hh H c 2 ( α ) . (36) Since U 1 and U 2 are independent, (29) implies that the i nput covar iance matrix can be written as follows: K X = K U 1 + K U 2 = αP e 1 e H 1 + (1 − α ) P c 2 ( α ) c H 2 ( α ) , for 0 ≤ α ≤ 1 . (37) Hence, we have tr( K X ) = tr( K U 1 + K U 2 ) = P , (38) i.e., the channel input power constrain t is satisfied. Next, ins erting (35) into (32) and (33 ), we obt ain 1 + h H K U 1 h 1 + g H K U 1 g = γ 1 ( α ) (39) and [1 + g H ( K U 1 + K U 2 ) g ][1 + h H K U 1 h ] [1 + h H ( K U 1 + K U 2 ) h ][1 + g H K U 1 g ] = γ 2 ( α ) . (40) where the intermediate steps for deriving (40) are given in Appendi x III. Now , by substitu ting (39) and (40) into L emma 3, we obtain the desired achie va ble result. Remark 5: The s ecrec y capacity region C MG s can be achie ved by u sing t he S-DPC scheme, in which the capacity achieving input cova riance matrix is with rank 2 . Furthermore, by reve rsing th e roles of user 1 and user 2 , we h a ve the achie vability proof for Corollary 2. V . S A T O - T Y P E O U T E R B O U N D A N D C O N V E R S E P R O O F In this section , we first d escribe a new Sato-type outer bound that can be applied to both discrete memoryless and Gaussian broadcast channels with confidential messages. Ne xt, a computable Gaus sian version of this bo und is derived for the MGBC-CM. Final ly , we prove t hat the Sato-type outer b ound coincides with th e secrecy capacity region C MG s . 13 A. Sato-T ype Outer Bound W e consider an im portant p roperty for t he BC-CM in the foll owing l emma. Lemma 4: Let P denot e the set of channels p ˜ Y 1 , ˜ Y 2 | X whose marginal distributions satis fy p ˜ Y 1 | X ( y 1 | x ) = p Y 1 | X ( y 1 | x ) and p ˜ Y 2 | X ( y 2 | x ) = p Y 1 | X ( y 2 | x ) (41) for all y 1 , y 2 and x . The secrecy capacity region C MG s is the s ame for the channels p ˜ Y 1 , ˜ Y 2 | X ∈ P . Pr oof : W e provide t he p roof in Appendi x III . W e note t hat P is the set of chann els p ˜ Y 1 , ˜ Y 2 | X that have the same marginal dis tributions as the original channel transit ion density p Y 1 ,Y 2 | X . Lemma 4 imp lies that the secrec y capacity region C MG s depends onl y on marginal distributions. Theor em 2 : Let R O P ˜ Y 1 , ˜ Y 2 | X , P X denote the un ion of all rate pairs ( R 1 , R 2 ) satisfying R 1 ≤ I ( X ; ˜ Y 1 , ˜ Y 2 ) − I ( X ; ˜ Y 2 ) (42) and R 2 ≤ I ( X ; ˜ Y 1 , ˜ Y 2 ) − I ( X ; ˜ Y 1 ) (43) for given di stributions P X and P ˜ Y 1 , ˜ Y 2 | X . The secrecy capacity region C MG s of the BC-CM satisfies C MG s ⊆ \ P ˜ Y 1 , ˜ Y 2 | X ∈P ( [ P X R O P ˜ Y 1 , ˜ Y 2 | X , P X ) . (44) Pr oof : See the Appendi x III. Remark 6: The outer bound (44) f ollows by e valuating the secrec y le vel at each user end in an individual manner , while by letting the users decode their messages in a coop erative manner . In t his sense, we refer to this bou nd as “Sato-type” ou ter bound. For example, we consi der the confidential message W 1 that is desti ned for user 1 (corresponding to ˜ Y 1 ) and eav esdropped b y user 2 (corresponding t o ˜ Y 2 ). W e assume that a genie g iv es user 1 the signal ˜ Y 2 as the side information for decodi ng W 1 . Note that the ea vesdropped s ignal ˜ Y 2 at user 2 is alw ays a degraded version of t he ent ire receiv ed signal ( ˜ Y 1 , ˜ Y 2 ) . This permits the us e of the wiretap channel resul t of [1]. Remark 7: Although Theorem 2 is based on a de graded ar gument, the out er bound (44) can be applied to general broadcast channels with confidential messages. 14 B. Sato-T ype Outer Bound fo r the MGBC-CM For the G aussian BC, th e family P is the set of channels ˜ y 1 = h H x + ˜ z 1 ˜ y 2 = g H x + ˜ z 2 (45) where ˜ z 1 and ˜ z 2 correspond to arbitrarily correlated, zero-mean, unit-variance, complex Gaussi an random var iables. Let ρ denote the cov ariance between ˜ Z 1 and ˜ Z 2 , i.e, Co v ˜ Z 1 , ˜ Z 2 = ρ and | ρ | 2 ≤ 1 . Now , t he rate re gion R O P ˜ Y 1 , ˜ Y 2 | X , P X is a function of the noise cov ariance ρ and the input cov ariance matrix K X . W e con sider a compu table Sato-type o uter bound for th e MGBC-CM in the fol lowing lemma. Lemma 5: Let R MG O ( ρ, K X ) denote th e union of all rate pairs ( R 1 , R 2 ) satisfyi ng 0 ≤ R 1 ≤ f 1 ( ρ, K X ) (46) and 0 ≤ R 2 ≤ f 2 ( ρ, K X ) (47) where f 1 ( ρ, K X ) = min ν ∈ C log 2 ( h − ν g ) H K X ( h − ν g ) + 1 + | ν | 2 − ν ∗ ρ − ρ ∗ ν (1 − | ρ | 2 ) (48) and f 2 ( ρ, K X ) = min µ ∈ C log 2 ( g − µ h ) H K X ( g − µ h ) + 1 + | µ | 2 − µ ∗ ρ − ρ ∗ µ (1 − | ρ | 2 ) . (49) For th e M GBC-CM, the secrecy capacity region C MG s satisfies C MG s ⊆ [ tr( K X ) ≤ P R O ( ρ, K X ) (50) for any 0 ≤ | ρ | ≤ 1 . Pr oof : W e provide t he p roof in Appendi x III . C. Con verse Pr oo f o f Theor em 1 In this sub section, we prove that the Sato-type outer bou nd of Lemma 5 coin cides with the secrecy capacity region C MG s by properly choo sing the parameter ρ . 15 1) Choosing the p arameter ρ : Note that Lem ma 5 is t rue for any ρ s uch that 0 ≤ | ρ | ≤ 1 . In particul ar , we consider ρ o , g H e 1 h H e 1 . (51) The definition s of λ 1 and e 1 in (2) im ply that | h H e 1 | 2 − λ 1 | g H e 1 | 2 = λ 1 − 1 P . (52) Since λ 1 ≥ 1 (see Lem ma 1), we obtain g H e 1 h H e 1 ≤ 1 . (53) Hence, we can choose ρ = ρ o in Lemma 5. 2) Determini ng the r ela tionship between K X and α : W e observe that the rate region R MG O ( ρ o , K X ) defined i n Lemma 5 is a fun ction of the input covariance m atrix K X , whil e the rate region R MG ( α ) defined in Theorem 1 is a functio n of α . In order to prove the main result, we build the relations hip between K X and α in the following l emma. Lemma 6: For any input cov ariance matrix K X with tr( K X ) ≤ P , t here exists a α ∈ [0 , 1] such that L ( K X , α ) = 0 , where L ( K X , α ) = [ h − ρ o γ 1 ( α ) g ] H ( K X − αP e 1 e H 1 )[ h − ρ o γ 1 ( α ) g ] . (54) Pr oof : W e provide t he p roof in Appendi x IV. Based on t he fun ction L ( · ) , we define the su bset of inpu t cov ariance matri ces in terms of α as follows: L ( α ) = { K X : L ( K X , α ) = 0 } . (55) Moreover , Lem ma 6 imp lies that [ 0 ≤ α ≤ 1 L ( α ) = { K X : tr( K X ) ≤ P } . (56) 3) Bound o n f 1 ( ρ o , K X ) : Now , we prove that if K X ∈ L ( α ) , t hen f 1 ( ρ o , K X ) ≤ log 2 γ 1 ( α ) . (57) 16 Let ν ( α ) = ρ o γ 1 ( α ) . For a gi ven K X ∈ L ( α ) , t he definition (48) i mplies that f 1 ( ρ o , K X ) ≤ log 2 [ h − ν ( α ) g ] H K X [ h − ν ( α ) g ] + 1 + | ν ( α ) | 2 − ν ∗ ( α ) ρ o − ρ ∗ o ν ( α ) 1 − | ρ o | 2 = log 2 αP [ h − ρ o γ 1 ( α ) g ] H e 1 2 + 1 + | ρ o | 2 γ 2 1 ( α ) − 2 | ρ o | 2 γ 1 ( α ) 1 − | ρ o | 2 . (58) Based on t he definit ion of ρ o in (51), we ha ve h − ρ o γ 1 ( α ) g = h − γ 1 ( α ) gg H e 1 h H e 1 = hh H − γ 1 ( α ) gg H h H e 1 e 1 . (59) Hence, [ h − ρ o γ 1 ( α ) g ] H e 1 2 = | h H e 1 | 2 − γ 1 ( α ) | g H e 1 | 2 2 | h H e 1 | 2 = | h H e 1 | 2 − γ 1 ( α ) | g H e 1 | 2 [1 − γ 1 ( α ) | ρ o | 2 ] = γ 1 ( α ) − 1 αP [1 − γ 1 ( α ) | ρ o | 2 ] (60) where the last st ep of (60) fol lows from th e definition of γ 1 ( α ) i n (8). Substituti ng (60) into (58), we obtain f 1 ( ρ o , K X ) ≤ log 2 [ γ 1 ( α ) − 1][1 − γ 1 ( α ) | ρ o | 2 ] + 1 + | ρ o | 2 γ 2 1 ( α ) − 2 | ρ o | 2 γ 1 ( α ) 1 − | ρ o | 2 = log 2 γ 1 ( α ) − | ρ o | 2 γ 1 ( α ) 1 − | ρ o | 2 = log 2 γ 1 ( α ) . (61) 4) Bound o n f 2 ( ρ o , K X ) : Here, we prove that if K X ∈ L ( α ) , t hen f 1 ( ρ o , K X ) ≤ log 2 γ 2 ( α ) (62) where γ 2 ( α ) is the largest generalized eigen value of the pencil (9). In fact, the smallest generalized eigen value of the pencil (9) is γ 1 ( α ) /λ 1 . This resul t is described in t he following lemm a. Lemma 7: γ 1 ( α ) /λ 1 and e 1 ( α ) are the small est generalized ei gen value and the correspond ing norm al- 17 ized eigen vector of the pencil I + (1 − α ) P 1 + αP | g H e 1 | 2 gg H , I + (1 − α ) P 1 + αP | h H e 1 | 2 hh H (63) where λ 1 and e 1 ( α ) are defined in (2), and γ 1 ( α ) is defined in (8). Pr oof : W e provide t he p roof in Appendi x IV. Based on t he pro perty of g eneralized eigen values (see Appendix I), Lem ma 7 im plies that e H 1 I + (1 − α ) P 1 + αP | g H e 1 | 2 gg H c 2 ( α ) = 0 (64) and e H 1 I + (1 − α ) P 1 + αP | h H e 1 | 2 hh H c 2 ( α ) = 0 (65) where c 2 ( α ) is t he normalized eigen vector of the pencil (9) corresponding to γ 2 ( α ) . Hence, (1 − α ) P 1 + αP | g H e 1 | 2 e H 1 gg H c 2 ( α ) = − e H 1 c 2 ( α ) (66) and (1 − α ) P 1 + αP | h H e 1 | 2 e H 1 hh H c 2 ( α ) = − e H 1 c 2 ( α ) . (67) By combini ng the definitions o f ρ o in (51) and γ 1 ( α ) in (8), we ob tain ρ o = g H e 1 h H e 1 = 1 γ 1 ( α ) h H c 2 ( α ) g H c 2 ( α ) ∗ . (68) W e now establish the relationship between γ 1 ( α ) and γ 2 ( α ) based on (68) in t he following lemm a. Lemma 8: For any α ∈ [0 , 1 ] , g − ρ ∗ o γ 2 ( α ) h | g − ρ ∗ o γ 2 ( α ) h | 2 = c 2 ( α ) (69) and [ h − ρ o γ 1 ( α ) g ] H [ g − ρ ∗ o γ 2 ( α ) h ] = 0 (70) where γ 1 ( α ) is defined in (8), and γ 2 ( α ) and c 2 ( α ) are the largest generalized eigen value and the corresponding normali zed eigen vector of the pencil (9). Pr oof : W e provide t he p roof in Appendi x IV. Let c 1 ( α ) denote the normalized vector of h − ρ o γ 1 ( α ) g , i.e., c 1 ( α ) , h − ρ o γ 1 ( α ) g | h − ρ o γ 1 ( α ) g | 2 . (71) 18 Note that Lemma 8 impl ies that c 1 ( α ) and c 2 ( α ) are orthogonal. Moreov er , since the input covariance matrix K X is Hermit ian and positive semid efinite, we ob tain c H 1 ( α ) K X c 1 ( α ) + c H 2 ( α ) K X c 2 ( α ) ≤ tr( K X ) = P . (72) Hence, for a giv en K X ∈ L ( α ) , we ha ve c H 2 ( α ) K X c 2 ( α ) ≤ P − αP | c H 1 ( α ) e 1 | 2 = (1 − α ) P + αP | c H 2 ( α ) e 1 | 2 . (73) Inserting (69) i nto (73), we obtain [ g − ρ ∗ o γ 2 ( α ) h ] H K X [ g − ρ ∗ o γ 2 ( α ) h ] ≤ (1 − α ) P ζ ( α ) + αP η ( α ) (74) where ζ ( α ) , | g − ρ ∗ o γ 2 ( α ) h ) | 2 (75) and η ( α ) , | g − ρ ∗ o γ 2 ( α ) h | 2 | e H 1 c 2 ( α ) | 2 . (76) In Appendix IV, we prove the foll owing equ ality (1 − α ) P ζ ( α ) + αP η ( α ) = [ γ 2 ( α ) − 1][1 − γ 2 ( α ) | ρ o | 2 ] . (77) Next, we consider the bound on f 2 ( ρ o , K X ) . Let µ ( α ) = ρ ∗ o γ 2 ( α ) . For a giv en K X ∈ L ( α ) , t he definition (49) implies that f 2 ( ρ o , K X ) ≤ log 2 [ g − µ ( α ) h ] H K X [ g − µ ( α ) h ] + 1 + | µ ( α ) | 2 − µ ∗ ( α ) ρ o − ρ ∗ o µ ( α ) 1 − | ρ o | 2 ≤ log 2 (1 − α ) P ζ ( α ) + αP η ( α ) + 1 + | ρ o | 2 γ 2 2 ( α ) − 2 | ρ o | 2 γ 2 ( α ) 1 − | ρ o | 2 . (78) 19 0 0.4 0.8 1.2 1.6 2 0 0.4 0.8 1.2 1.6 2 R 1 (bits) R 2 (bits) time−sharing capacity region Fig. 2. Comparison of the S ato-type outer bound and secrecy rate region s achiev ed by time-sharing and simplified DPC schemes for the examp le MGBC-CM in (81) Now , subst ituting (77) into (78), we obtain f 2 ( ρ o , K X ) ≤ log 2 [ γ 2 ( α ) − 1][1 − γ 2 ( α ) | ρ o | 2 ] + 1 + | ρ o | 2 γ 2 2 ( α ) − 2 | ρ o | 2 γ 2 ( α ) 1 − | ρ o | 2 = log 2 γ 2 ( α ) . (79) Finally , Combini ng (56), (61) and (79), we have the d esired resul t: [ tr( K X ) ≤ P R O ( ρ, K X ) ⊆ [ 0 ≤ α ≤ 1 R MG ( α ) . (80) V I . N U M E R I C A L E X A M P L E S In t his sectio n, we stud y two nu merical examples to illustrate the secrecy capacity region of t he M GBC- CM. For simplicit y , we ass ume that the Gaussi an BC has real inp ut and output alphabets and the channel attenuation vectors h and g are real too. Under this condition, all calculated rate values are divided by 2 . Example 2: In the first example, we con sider the following M GBC-CM y 1 y 2 = 1 . 5 0 1 . 801 0 . 871 x 1 x 2 + z 1 z 2 (81) where h = [1 . 5 , 0] T , g = [1 . 801 , 0 . 87 2 ] T , and the total power const raint is set t o P = 10 . Fig. 2 i llustrates the secrecy capacity region for the channel (81). W e observe that e ven though each component of the 20 0 0.4 0.8 1.2 1.6 2 0 0.4 0.8 1.2 1.6 2 R 1 (bits) R 2 (bits) time−sharing capacity region Fig. 3. Comparison of the S ato-type outer bound and secrecy rate region s achiev ed by time-sharing and simplified DPC schemes for the examp le MGBC-CM in (82) attenuation vector h (im posed on user 1) is strictly less than the corresponding component of g (i mposed on user 2), b oth users can achieve pos itiv e rates simultaneously under the in formation-theoretic secrecy requirement. Example 3: In the second example, we consider t he MGBC-CM as follows y 1 y 2 = 1 . 414 1 . 414 0 . 4 1 . 959 x 1 x 2 + z 1 z 2 (82) where h = [1 . 414 , 1 . 414] T , g = [0 . 4 , 1 . 959] T , and the total power P = 10 . The secrec y capacity region of the channel (82) is calculated and depicted in Fig. 3. Moreover , we compare t he secrecy capacity region with th e secrecy rate region achieved by the tim e- sharing schem e (indicated by the d ash-dot line). T he time-sharing refers to t he scheme in which the transmitter sends the confidential mess age W 1 with total power P 1 during a fraction τ 1 of time, and sends the confidential m essage W 2 with total power P 2 during a fraction τ 2 of tim e, where τ 1 + τ 2 = 1 and τ 1 P 1 + τ 2 P 2 = P . Note that in each time fraction, the MGBC-CM reduces to a Gaussian MISO wi retap channel. Using such time-sharing, the rate pair τ 1 2 log 2 λ 1 ( P 1 ) , τ 2 2 log 2 λ 2 ( P 2 ) is achiev able, where λ 1 ( P 1 ) and λ 2 ( P 2 ) are the largest g eneralized eigen values of the pencil ( I + P 1 hh H , I + P 1 gg H ) and the p encil ( I + 21 P 2 gg H , I + P 2 gg H ) , respectiv ely . Both Fig. 2 and Fig. 3 demonst rate that the time-sharing scheme i s strictly subop timal for p roviding the secrec y capacity region. V I I . C O N C L U S I O N In this paper , we have in vestigated the secrec y capacity region of a generally non-degraded Gaus sian BC with confidential messages for two users, where the transmit ter has t antennas and each user has a single antenna. For t his m odel, we have prop osed a secret dirty-paper codi ng scheme and introduced a computable Sato-type outer bound. Furthermore, we ha ve p rove d t hat the boundary of the secret dirty- paper coding rate region is consistent with the Sato-typ e out er boun d for t he m ultiple-antenna Gaussian BC, and hence, we have obtained the secrec y capacity region for the MGBC-CM. Unlike the single-antenna Gaussian BC-CM case, in which only t he superior user can obtain confidential information at a posi tiv e s ecrec y rate, o ur result has illustrated that b oth us ers can achieve strictly positive rates with informati on-theoretic secrecy through a multi ple-antenna Gaussian BC if att enuation vectors imposed on user 1 and user 2 are linear independent. Therefore, it becomes more practical and m ore attractiv e to achieve information -theoretic secrecy in wi reless networks b y em ploying mul tiple transm it- antennas at the physical l ayer . A P P E N D I X I T H E G E N E R A L I Z E D E I G E N V A L U E A N D R A Y L E I G H Q U OT I E N T P RO B L E M A generalized eigen value problem is to determine the nontrivial solution s of the equation A e = λB e (83) where A and B are matrices and λ is a scalar . The values of λ that satisfy (83) are the generalized eigen values and t he corresponding vectors of e are the g eneralized eigen vectors. In particular , if A is Hermitian and B is Hermiti an and posi tiv e definite, then we hav e the fol lowing properties of A e = λB e : 1) The generalized eigen values λ i are real. 2) The eigen vectors are “ B -orthogonal”, i.e., e H i B e j = 0 for i 6 = j. (84) 22 3) Simil arly , e H i A e j = λ j e H i A e j = 0 for i 6 = j. (85) Next, we describe th e well-known Rayleigh’ s quotient [30 ] as follows. Theor em 3 : (see [30]) Let r ( c ) be the Rayleigh’ s quotient defined as r ( c ) , c H A c c H B c . (86) where A is Hermitian and B is Hermit ian and positive definite. The quo tient R ( c ) is maxim ized by the eigen vector e max corresponding to th e largest generalized eigenv alue λ max of the pencil ( A, B ) : max c R ( c ) = e H max A e max e H max B e max = λ max (87) and R ( c ) is m inimized by t he eigen vector e min corresponding to the smal lest generalized eigen value λ min of the pencil ( A, B ) : min c R ( c ) = e H min A e min e H min B e min = λ min . (88) The p roof of Theorem 3 can be found in [30, Chapter 6]. Now we prove Lemma 1 based on t he Rayleigh ’ s quotient principle. Pr oof : ( Lemma 1 ) Since both ( I + P hh H ) and ( I + P gg H ) are Hermitian and positive definite matrices, the definit ion of λ 1 and Theorem 3 imply that λ 1 = max c c H ( I + P hh H ) c c H ( I + P gg H ) c . (89) W e consider a unit vector c 0 that is orthogonal wi th the vector g , i.e., c H 0 c 0 = 1 and c H 0 g = 0 . Now , we hav e λ 1 ≥ c H 0 ( I + P hh H ) c 0 c H 0 ( I + P gg H ) c 0 = 1 + P | c H 0 h | 2 . (90) This i mplies that λ 1 ≥ 1 . Furthermore, w hen h and g are l inear independent, t here exists a unit vector 23 c 0 so that c H 0 g = 0 and c H 0 h > 0 . (91) Substitutin g (refeq:lg2) in to (90), we obt ain λ 1 > 1 . By usi ng the same approach, we can show that λ 2 ≥ 1 , and, in particular , λ 2 > 1 when h and g are li near independent. A P P E N D I X I I P RO O F O F C O RO L L A RY 1 Pr oof : Theorem 1 dem onstrates t hat for a given α ∈ [0 , 1] , the maxi mum achiev able secrecy rate of user 1 is γ 1 ( α ) . This implies that R 1 , max = max 0 ≤ α ≤ 1 γ 1 ( α ) . (92) W e also no tice t hat λ 1 = γ 1 (1) . Hence, it is sufficient t o show t hat γ 1 ( α ) is a no ndecreasing fun ction on an interval [0 , 1 ] . Let κ ( α ) , dγ 1 ( α ) dα . (93) Based on t he definit ion of γ 1 ( α ) in (8), we can write κ ( α ) = P | h H e 1 | 2 (1 + αP | g H e 1 | 2 ) − (1 + αP | h H e 1 | 2 ) P | g H e 1 | 2 (1 + αP | g H e 1 | 2 ) 2 = P ( | h H e 1 | 2 − | g H e 1 | 2 ) (1 + αP | g H e 1 | 2 ) 2 (94) Now , the definitions of λ 1 and e 1 in (2) im ply that | h H e 1 | 2 − λ 1 | g H e 1 | 2 = λ 1 − 1 P . (95) Moreover , Since λ 1 ≥ 1 (see Lem ma 1), we obtain κ ( α ) ≥ 0 , (96) 24 and hence, γ 1 ( α ) is a nondecreasing functio n o n an interval [0 , 1 ] . Therefore, we ha ve R 1 , max = max 0 ≤ α ≤ 1 γ 1 ( α ) = λ 1 . A P P E N D I X I I I S E C T I O N I V D E R I V A T I O N S ( Double-Binning Scheme ) : By cont rast with the class ical DPC scheme, the secret DPC schem e is based on th e double-binni ng code structure as follows. Let R ⋆ 1 = I ( V 1 ; Y 2 | V 2 ) , R ⋆ 2 = I ( V 2 ; Y 1 | V 1 ) and R ‡ = I ( V 1 ; V 2 ) . (97) Generate 2 n ( R k + R ⋆ k + R ‡ ) code words v n k ( w k , j k , l k ) , w k = 1 , 2 , . . . , 2 R k , j k = 1 , 2 , . . . , 2 R ⋆ k , l k = 1 , 2 , . . . , 2 R ‡ , independently at random according to p ( v k ) . B ased on the labeling, we partition the c odebook { v n k ( w k , j k , l k ) } into 2 nR k bins , where bin w k represents the message index w k . W e further divide bin w k into 2 nR ⋆ k sub-bins . Each sub-bin ( w k , j k ) contains 2 nR ‡ code words. T o s end t he m essage p air ( w 1 , w 2 ) , the t ransmitter em ploys a joint stochastic encoder . W e first randomly select a sub-bi n ( w 1 , j 1 ) from t he bin w 1 and randoml y cho ose a cod e word v n 1 ( w 1 , j 1 , l 1 ) from t he sub- bin ( w 1 , j 1 ) . Next, we randomly select a sub-bin ( w 2 , j 2 ) from the bin w 2 and find a code word v n 2 ( w 2 , j 2 , l 2 ) in the s ub-bin ( w 2 , j 2 ) so th at the sequences v n 1 ( w 1 , j 1 , l 1 ) and v n 2 ( w 2 , j 2 , l 2 ) are jo intly typical with respectiv e to p ( v 1 , v 2 ) . Since each sub-bin contains 2 nI ( V 1 ; V 2 ) code words, th e encodi ng is successful with probability close to 1 as long as n is lar ge. Finally , we generate t he channel input sequence x n ( w 1 , w 2 ) according to th e mapping p ( x | v 1 , v 2 ) . Pr oof : ( Lemma 3 ) W e first check the power constraint. Since U 1 and U 2 are independ ent and X = U 1 + U 2 , the covariance m atrices K U 1 and K U 2 satisfy tr( K U 1 + K U 2 ) = tr( K X ) ≤ P . (98) Follo wing from [29, Theorem 1] and using the setting in (30), we can immediately ob tain the well- 25 known successive dirty-pap er encodi ng result: I ( V 1 ; Y 1 ) − I ( V 1 ; V 2 ) = I ( U 1 ; h H U 1 + Z 1 ) = log 2 (1 + h H K U 1 h ) . (99) Since V 2 = U 2 is independent of U 1 and V 1 = U 1 + bh H U 2 , we obtain I ( V 1 ; Y 2 | V 2 ) = I ( U 1 + bh H U 2 ; Y 2 | U 2 ) = I ( U 1 ; Y 2 | U 2 ) = log 2 (1 + g H K U 1 g ) . (100) Combining (22), (99) and (100), we ha ve R 1 ≤ I ( V 1 ; Y 1 ) − I ( V 1 ; V 2 ) − I ( V 1 ; Y 2 | V 2 ) = log 2 1 + h H K U 1 h 1 + g H K U 1 g . (101) Moreover , we can compute I ( V 2 ; Y 2 ) = h ( Y 2 ) − h ( Y 2 | V 2 ) = h ( g H ( U 1 + U 2 ) + Z 2 ) − h ( g H U 1 + Z 2 ) = log 2 1 + g H ( K U 1 + K U 2 ) g 1 + g H K U 1 g . (102) and I ( V 2 ; Y 1 | V 1 ) + I ( V 1 ; V 2 ) = I ( V 1 , V 2 ; Y 1 ) − [ I ( V 1 ; Y 1 ) − I ( V 1 ; V 2 )] = log 2 1 + h H ( K U 1 + K U 2 ) h 1 + h H K U 1 h . (103) Substitutin g (102) and (103) into (23), we obtain that R 2 ≤ I ( V 2 ; Y 2 ) − I ( V 1 ; V 2 ) − I ( V 2 ; Y 1 | V 1 ) = log 2 1 + g H ( K U 1 + K U 2 ) g 1 + g H K U 1 g − log 2 1 + h H ( K U 1 + K U 2 ) h 1 + h H K U 1 h = log 2 1 + g H ( K U 1 + K U 2 ) g 1 + h H ( K U 1 + K U 2 ) h + log 2 1 + h H K U 1 h 1 + g H K U 1 g . (104) 26 Applying Lemma 2 with bounds (101) and (104), we ha ve the desired result. Pr oof : ( Equation (40) ) For con venience,we define d ( K U 1 , K U 2 ) , [1 + g H ( K U 1 + K U 2 ) g ][1 + h H K U 1 h ] [1 + h H ( K U 1 + K U 2 ) h ][1 + g H K U 1 g ] = 1 + g H K U 2 g 1 + g H K U 1 g 1 + h H K U 2 h 1 + h H K U 1 h − 1 . (105) Since c H 2 ( α ) c 2 ( α ) = 1 , we substitute (35) i nto d ( K U 1 , K U 2 ) and obtain d ( K U 1 , K U 2 ) = 1 + (1 − α ) P g H c 2 ( α ) c H 2 ( α ) g 1 + αP | g H e 1 | 2 1 + (1 − α ) P h H c 2 ( α ) c H 2 ( α ) h 1 + αP | h H e 1 | 2 − 1 = c H 2 ( α ) c 2 ( α ) + (1 − α ) P c H 2 ( α ) gg H c 2 ( α ) 1 + αP | g H e 1 | 2 c H 2 ( α ) c 2 ( α ) + (1 − α ) P c H 2 ( α ) hh H c 2 ( α ) 1 + αP | h H e 1 | 2 = c H 2 ( α ) I + (1 − α ) P gg H 1 + αP | g H e 1 | 2 c 2 ( α ) c H 2 ( α ) I + (1 − α ) P hh H 1 + αP | h H e 1 | 2 c 2 ( α ) . (106) Note that γ 2 ( α ) and c 2 ( α ) are th e lar gest generalized eig en value and the corresponding normali zed eigen vector of the pencil (9), i.e., I + (1 − α ) P 1 + αP | g H e 1 | 2 gg H c 2 ( α ) = γ 2 ( α ) I + (1 − α ) P 1 + αP | h H e 1 | 2 hh H c 2 ( α ) . Hence, we have d 2 ( K U 1 , K U 2 ) = γ 2 ( α ) . (107) A P P E N D I X I V S E C T I O N V D E R I V A T I O N S Pr oof : ( Lemma 4 ) It is suf ficient to show that the error probabil ity P ( n ) e and the equivoca tions H ( W 2 | Y n 1 ) and H ( W 2 | Y n 1 ) are the same for the channels p ˜ Y 1 , ˜ Y 2 | X ∈ P when we use the sam e codebook and encoding s chemes. W e note t hat P ( n ) e = max P ( n ) e, 1 , P ( n ) e, 2 ≤ P ( n ) e, 1 + P ( n ) e, 2 . (108) 27 Hence, P ( n ) e is small if and only if both P ( n ) e, 1 and P ( n ) e, 2 are small. Howe ver , for given cod ebook and encoding scheme p ( x n | w 1 , w 2 ) , the decoding error probability P ( n ) e,k and the equiv ocation rate at user k depend onl y on the m ar ginal channel probability density p ˜ Y k | X . Therefore, th e same code and encoding scheme for any p ˜ Y 1 , ˜ Y 2 | X ∈ P gives t he s ame P ( n ) e and equiv ocation rates. This concludes the proof. Pr oof : ( Theorem 2 ) Here we prove Theorem 2 and deriv e the outer bound for R 1 . The outer bound for R 2 follows by symmet ry . The secrecy requirement (7) imp lies that nR 1 = H ( W 1 ) ≤ H ( W 1 | Y n 2 ) + nǫ. (109) On the oth er hand, Fano’ s inequality and P e ≤ ǫ imply that H ( W 1 | Y n 1 ) ≤ ǫ log ( M 1 − 1) + h ( ǫ ) , nδ 1 . (110) where h ( x ) is the bin ary entropy function . Based on (109) and (110), we have nR 1 ≤ H ( W 1 | Y n 2 ) + nǫ ≤ H ( W 1 | Y n 2 ) − H ( W 1 | Y n 1 ) + n ( δ 1 + ǫ ) ≤ H ( W 1 | Y n 2 ) − H ( W 1 | Y n 1 , Y n 2 ) + n ( δ 1 + ǫ ) (111) = I ( W 1 ; Y n 1 | Y n 2 ) + n ( δ 1 + ǫ ) (112) where (111) follows from conditio ning reducing ent ropy . Since W 1 → X n → ( Y n 1 , Y n 2 ) forms a Markov chain, we can further bound (11 2) as follows nR 1 ≤ I ( X n ; Y n 1 | Y n 2 ) + n ( δ 1 + ǫ ) ≤ n X i =1 I ( X i ; Y 1 ,i | Y 2 ,i ) + n ( δ 1 + ǫ ) . (113) Finally , b y applying Lemma 4, we can replace Y 1 and Y 2 by ˜ Y 1 and ˜ Y 2 , respecti vely . Hence, we have the Sato-type out er bound on R 1 . Pr oof : ( Lemma 5 ) Here, we proof Lemma 5 based on the Sato-type outer bound in Theorem 2. 28 For th e Gauss ian BC defined i n (45), the upp er bound (42) on R 1 can be rewritten as follows: I ( X ; ˜ Y 1 , ˜ Y 2 ) − I ( X ; ˜ Y 2 ) = h ( ˜ Y 1 , ˜ Y 2 ) − h ( ˜ Y 1 , ˜ Y 2 | X ) − h ( ˜ Y 2 ) + h ( ˜ Y 2 | X ) = h ( ˜ Y 1 | ˜ Y 2 ) − [ h ( ˜ Z 1 , ˜ Z 2 ) − h ( ˜ Z 2 )] = h ( ˜ Y 1 | ˜ Y 2 ) − log 2 (2 π e )(1 − | ρ | 2 ) . (114) The first term of (114) can b e further boun ded as follows h ( ˜ Y 1 | ˜ Y 2 ) = h ( ˜ Y 1 − ν ˜ Y 2 | ˜ Y 2 ) ≤ h ( ˜ Y 1 − ν ˜ Y 2 ) for any ν ∈ C (115) where the inequali ty follows from removing conditioni ng. Moreover , the maxi mum-entropy theorem [22] implies that h ( ˜ Y 1 − ν ˜ Y 2 ) ≤ log 2 (2 π e ) V ar ˜ Y 1 − ν ˜ Y 2 = log 2 (2 π e ) V ar ( h − ν g ) H X + V ar ˜ Z 1 − ν ˜ Z 2 = log 2 (2 π e ) ( h − ν g ) H K X ( h − ν g ) + 1 + | ν | 2 − ν ∗ ρ − ρ ∗ ν . (116) Combining (114), (11 5) and (116), we obtain the foll o wing upper bou nd: I ( X ; ˜ Y 1 , ˜ Y 2 ) − I ( X ; ˜ Y 2 ) ≤ min ν ∈ C log 2 ( h − ν g ) H K X ( h − ν g ) + 1 + | ν | 2 − ν ∗ ρ − ρ ∗ ν (1 − | ρ | 2 ) (117) = f 1 ( ρ, K X ) . (118) Next we prove th at for given ρ and K X , the expression I ( X ; ˜ Y 1 , ˜ Y 2 ) − I ( X ; ˜ Y 2 ) is m aximized by Gaussian input dis tributions. Wh en X is a Gaussian random vector with zero-mean and covariance matrix K X , the channel (45) implies th at ˜ Y 1 and ˜ Y 2 are zero-mean Gaus sian random variables. Choosi ng ν = ν o = Co v ˜ Y 1 , ˜ Y 2 V ar ˜ Y 2 . (119) Note that E ( ˜ Y 1 − ν o ˜ Y 2 ) ˜ Y ∗ 2 = Co v ˜ Y 1 , ˜ Y 2 − ν o V ar ˜ Y 2 = 0 , (120) the Gaussian random variables ˜ Y 1 − ν o ˜ Y 2 and ˜ Y 2 are uncorrelated, and hence they are statistically inde- 29 pendent. This im plies t hat h ( ˜ Y 1 | ˜ Y 2 ) = h ( ˜ Y 1 − ν o ˜ Y 2 ) = log 2 (2 π e ) ( h − ν o g ) H K X ( h − ν o g ) + 1 + | ν o | 2 − ν ∗ o ρ − ρ ∗ ν o . (121) Inserting (121) into (114) we have I ( X ; ˜ Y 1 , ˜ Y 2 ) − I ( X ; ˜ Y 2 ) = log 2 ( h − ν o g ) H K X ( h − ν o g ) + 1 + | ν o | 2 − ν ∗ o ρ − ρ ∗ ν o (1 − | ρ | 2 ) ≥ f 1 ( ρ, K X ) . (122) Bounds (118) and (12 2) imply that Gaussian input distributions are optimal for the e xpression I ( X ; ˜ Y 1 , ˜ Y 2 ) − I ( X ; ˜ Y 2 ) . Follo wing the s ame approach, we can prove that for g iv en ρ and K X , Gaussian input dis tributions maximize the expression I ( X ; ˜ Y 1 , ˜ Y 2 ) − I ( X ; ˜ Y 1 ) , the upp er bound (43) on R 2 . This l ets us restrict attenti on to zero-mean Gaussian X with covariance matrix K X . Now , bounds (42) and (43) become R 1 ≤ f 1 ( ρ, K X ) (123) and R 2 ≤ f 2 ( ρ, K X ) (124) This yields t he rate region R MG O ( ρ, K X ) . Hence we ha ve th e desired result. Pr oof : ( Lemma 6 ) For a given K X , we first ev aluate L ( K X , 0) and L ( K X , 1) . Since γ 1 (0) = 1 and the inpu t covar iance matri x K X is positive semidefinite, we obtain L ( K X , 0) = ( h − ρ o g ) H K X ( h − ρ o g ) ≥ 0 . (125) On the oth er hand, since γ 1 (1) = λ 1 and K X is Hermitian and po sitive semidefinit e, we ha ve L ( K X , 1) = ( h − ρ o λ 1 g ) H ( K X − P e 1 e H 1 )( h − ρ o λ 1 g ) ≤ tr( K X ) | h − ρ o λ 1 g | 2 − P | ( h − ρ o λ 1 g ) H e 1 | 2 ≤ P | h − ρ o λ 1 g | 2 − P | ( h − ρ o λ 1 g ) H e 1 | 2 . (126) 30 Based on t he definit ion of ρ o in (51), we can compute h − ρ o λ 1 g = h − λ 1 gg H e 1 h H e 1 = ( hh H − λ 1 gg H ) e 1 h H e 1 = ( λ 1 − 1) e 1 P h H e 1 (127) where the last step follows from the definitio ns λ 1 and e 1 in (2). M oreov er , si nce e H 1 e 1 = 1 , (127) can be rewritten as L ( K X , 1) ≤ P ( λ 1 − 1) e 1 P h H e 1 2 − P λ 1 − 1 P h H e 1 e H 1 e 1 2 = 0 (128) W e note that L ( K X , α ) is a continuous function on the interval α ∈ [0 , 1] for a giv e K X . Since L ( K X , 0) ≥ 0 and L ( K X , 1) ≤ 0 , there exists α ∈ [0 , 1] su ch t hat L ( K X , α ) = 0 . Pr oof : ( Lemma 7 ) W e note that λ 1 and e 1 are t he largest generalized eigen value and the corre- sponding no rmalized eigen vector of the p encil [ I + P hh H , I + P gg H ] . Based on the Rayleigh’ s q uotient principle in Theorem 3, we obtain max c c H ( I + P hh H ) c c H ( I + P gg H ) c = e H 1 ( I + P hh H ) e 1 e H 1 ( I + P gg H ) e 1 = λ 1 . (129) Hence, we have min c (1 + αP | g H e 1 | 2 ) + c H [(1 − α ) P gg H ] c (1 + αP | h H e 1 | 2 ) + c H [(1 − α ) P hh H ] c = e H 1 ( I + P gg H ) e 1 e H 1 ( I + P hh H ) e 1 = 1 λ 1 . (130) By using t he definit ion of γ 1 ( α ) in (8), we have min c c H I + (1 − α ) P 1 + αP | g H e 1 | 2 gg H c c H I + (1 − α ) P 1 + αP | h H e 1 | 2 hh H c = e H 1 I + (1 − α ) P 1 + αP | g H e 1 | 2 gg H e 1 e H 1 I + (1 − α ) P 1 + αP | h H e 1 | 2 hh H e 1 = γ 1 ( α ) λ 1 . (131) Now , t he Rayleigh’ s quotient principle implies that γ 1 ( α ) /λ 1 and e 1 ( α ) are t he smallest generalized eigen value and the corresponding normali zed eigen vector of the pencil (9). 31 Pr oof : ( Lemma 8 ) W e first show t hat [ g − ρ ∗ o γ 2 ( α ) h ] ∝ c 2 ( α ) . Since γ 1 ( α ) is real and ρ o = 1 γ 1 ( α ) h H c 2 ( α ) g H c 2 ( α ) ∗ , (132) we have g − ρ ∗ o γ 2 ( α ) h = g − γ 2 ( α ) γ 1 ( α ) hh H c 2 ( α ) g H c 2 ( α ) = [ γ 1 ( α ) gg H − γ 2 ( α ) hh H ] c 2 ( α ) γ 1 ( α ) g H c 2 ( α ) . (133) Note that (36 ) impli es that (1 − α ) P 1 + αP | g H e 1 | 2 gg H − γ 2 ( α ) (1 − α ) P 1 + α P | h H e 1 | 2 hh H c 2 ( α ) = [ γ 2 ( α ) − 1] c 2 ( α ) . (134) Based on t he definit ion of γ 1 ( α ) in (8), we ob tain [ γ 1 ( α ) gg H − γ 2 ( α ) hh H ] c 2 ( α ) = 1 + αP | h H e 1 | 2 (1 − α ) P [ γ 2 ( α ) − 1] c 2 ( α ) . (135) Now , we can rewritten (133) as g − ρ ∗ o γ 2 ( α ) h = (1 + αP | h H e 1 | 2 )[ γ 2 ( α ) − 1] γ 1 ( α ) g H c 2 ( α )(1 − α ) P c 2 ( α ) . (136) Hence, we obt ain g − ρ ∗ o γ 2 ( α ) h | g − ρ ∗ o γ 2 ( α ) h | 2 = c 2 ( α ) . (137) Next we prov e that [ h − ρ o γ 1 ( α ) g ] H c 2 ( α ) = 0 . The definitions of λ 1 and e 1 in (2) im plies th at hh H e 1 = λ 1 − 1 P I + λ 1 gg H e 1 . (138) Substitutin g (138) into (59), we obtai n h − ρ o γ 1 ( α ) g = 1 h H e 1 λ 1 − 1 P I + λ 1 gg H − γ 1 ( α ) gg H e 1 = λ 1 − 1 P h H e 1 I + λ 1 − γ 1 ( α ) λ 1 − 1 P gg H e 1 . (139) 32 Based on t he definit ion of γ 1 ( α ) in (8), we ob tain λ 1 − γ 1 ( α ) = λ 1 − 1 + α P | h H e 1 | 2 1 + αP | g H e 1 | 2 = ( λ 1 − 1 ) + α P ( λ 1 | g H e 1 | 2 − | h H e 1 | 2 ) 1 + αP | g H e 1 | 2 = ( λ 1 − 1 ) 1 − α 1 + αP | g H e 1 | 2 (140) where the l ast step follows from (52). Substitut ing (139) i nto (140), we ha ve h − ρ o γ 1 ( α ) g = λ 1 − 1 P h H e 1 I + (1 − α ) P 1 + αP | g H e 1 | 2 gg H e 1 . (141) Now (64) and (141) imply that [ h − ρ o γ 1 ( α ) g ] H c 2 ( α ) = 0 . (142) Combining with (137), we have t he desired result. Pr oof : ( Equation (77) ) First, we consider ζ ( α ) defined in (75). Based on (133) and (136), ζ ( α ) can be rewritten as ζ ( α ) = [ g − ρ ∗ o γ 2 ( α ) h ] H [ g − ρ ∗ o γ 2 ( α ) h ] = (1 + αP | h H e 1 | 2 )[ γ 2 ( α ) − 1] (1 − α ) P c H 2 ( α )[ γ 1 ( α ) gg H − γ 2 ( α ) hh H ] c 2 ( α ) | γ 1 ( α ) g H c 2 ( α ) | 2 = 1 + αP | h H e 1 | 2 (1 − α ) P [ γ 2 ( α ) − 1] 1 γ 1 ( α ) − γ 2 ( α ) | ρ o | 2 . (143) Now , we consider (1 − α ) P ζ ( α ) = [ γ 2 ( α ) − 1][1 + αP | g H e 1 | 2 − γ 2 ( α ) | ρ o | 2 − α P | h H e 1 | 2 γ 2 ( α ) | ρ o | 2 ] = [ γ 2 ( α ) − 1] { 1 − γ 2 ( α ) | ρ o | 2 + αP | g H e 1 | 2 [1 − γ 2 ( α )] } (144) where the l ast step of (144 ) follows from ρ o = ( g H e 1 ) / ( h H e 1 ) . Next, we consider η ( α ) defined in (76). No te that (66) implies that | e H 1 c 2 ( α ) | 2 = (1 − α ) P 1 + α P | g H e 1 | 2 2 | g H e 1 | 2 | g H c 2 ( α ) | 2 . (145) 33 Combining (132), (14 3) and (145), we obtain η ( α ) = ζ ( α ) | e H 1 c 2 ( α ) | 2 = (1 + αP | h H e 1 | 2 )( γ 2 ( α ) − 1) (1 − α ) P " 1 γ 1 ( α ) − γ 2 ( α ) γ 2 1 ( α ) h H c 2 g H c 2 2 # | e H 1 c 2 ( α ) | 2 = [ γ 2 ( α ) − 1] | g H e 1 | 2 (1 − α ) P | g H c 2 ( α ) | 2 1 + αP | g H e 1 | 2 − γ 2 ( α ) (1 − α ) P | h H c 2 ( α ) | 2 1 + αP | h H e 1 | 2 = [ γ 2 ( α ) − 1] 2 | g H e 1 | 2 (146) where the last s tep of (146) follows from the definiti on of γ 2 ( α ) in (36). Combining (14 4) and (146), we obtain the desired resul t. R E F E R E N C E S [1] A. D. W yner , “The wire-tap channel, ” Bell Syst. T ech. J. , vol. 54, no. 8, pp. 1355–138, Oct. 1975. [2] I . Csisz ´ ar and J. K ¨ orner , “Broadcast channels with confidential messages, ” IE EE T rans. Inf. Theory , vol. 24, no. 3, pp. 339–3 48, May 1978. [3] Y . Oohama, “Coding for relay channels wit h confidential messages, ” in Pr oc. IEEE Information Theory W orkshop , Cairns, Australia, Sep. 2001, pp. 87–89. [4] I . Csisz ´ ar and P . Narayan, “Secrecy capacities for multiple t erminal, ” IEEE Tr ans. Inf. Theory , vol. 50, no. 12, pp. 3047–3 061, Dec 2004. [5] E . T ekin and A. Y ener, “The Gaussian multiple access wire-tap channel wit h collecti ve secrec y constraints, ” in Pr oc. IEEE Int. Symp. Information Theory (ISIT) , Seattl e, USA, Jul. 2006. [6] — —, “The multiple access wi re-tap channel: W ireless secrecy and cooperativ e jamming, ” in Proc. I nformation T heory and Application W orkshop, ITA , S an Diego, CA, Jan. 2007. [7] Y . Liang and H. V incent Poor, “Generalized multiple access channels w ith confidential messages, ” IEEE T rans. Inf. Theory , submitted (under revision), April 2006. [Online]. A v ailable: http://arxiv .org/PS$ $cache/cs/pdf/06 05/060501 4.pdf [8] R . Liu, I. Maric, R. D. Y ates, and P . S pasoje vic, “The discrete memoryless multiple access channel with confidential messages, ” in Pr oc. IEEE Int. Symp. I nformation Theory (ISIT ) , Jul. 2006, pp. 957 – 961. [9] R . L iu, I. Maric, P . Spasoje vic, and R. Y ates, “Discrete memoryless interference and broadcast channels with confidential messages, ” in P r oc. All erton Confer ence on Communication, Contr ol, and Computing , Sep. 2006. [10] L. Lai and H. El Gamal, “The relay-eavesd ropper channel: Cooperation for secrecy , ” I EEE T rans. Inf. Theory , submitted, Dec. 2006. [11] M. Y uksel and E. Erkip., “The relay channel with a wiretapper , ” in Pr oc. F orty-Fir st Annual Confer ence on Information Sciences and Systems (CISS) , Baltimore, MD, USA, Mar . 2007. [12] J. Barros and M. Rodrigues, “Secrecy capacity of wireless channels, ” in Pro c. IE EE Int. Symp. Information Theory (ISIT) , Seattl e, USA, Jul. 2006. [13] Z. Li, R. Y ates, and W . Trapp e, “Secrecy capacity of indeped ent parallel channels, ” in Pr oc. Al lerton Confer ence on Commun., Contr ., Computing , Monticello, IL, USA, Sep. 2006. 34 [14] Y . Liang, H. V incent Poor, and S. Shamai (Shitz), “Secure communication ov er fading channels, ” IEEE T rans. Inf. Theory , submitted, Nov . 2006. [Online]. A vailable: http://arxiv .org/PS$ $cache/cs/pdf/070 1/0701024 .pdf [15] P . Gopala, L . Lai, and H. El G amal, “On the secrecy capacity of fading channels, ” i n P r oc. IEEE Int. Symp. Information Theory (ISIT) , Nice, France, June 24-29, 2007. [16] Z. Li, W . Trappe, and R. Y ates, “S ecret communication via multi-antenna transmission, ” in Pr oc. F orty-Fir st A nnual Confer ence on Information Sciences and Systems (CISS) , Baltimore, MD, USA, Mar . 2007. [17] R. Liu and H. V incent Poor, “Multiple antenna secure broadcast over wireless networks, ” in Proc. Fir st International W orkshop on Information Theory for Sensor Net works , Santa Fe, NM, June 18-20, 2007, pp. 125–139 . [18] A. Khisti, G. W ornell, A. Wiese l, and Y . Eldar, “On the Gaussian MIMO wiretap channel, ” in Pr oc. IEE E Int. Symp. Information Theory (ISIT) , N ice, France, June 24-29, 2007. [19] A. Khisti and G. W ornell, “S ecure transmission wit h multiple antennas: The MISOME wiretap channel, ” IE EE Tr ans. Inf. Theory , submitted, August 2007. [20] S. Shafiee and S. Ulukus, “ Achiev able rates in gaussian MISO channels with secrecy constraints, ” i n Proc. I EEE I nt. Symp. Information Theory (ISIT) , N ice, France, June 24-29, 2007. [21] S. Shafiee, N. Liu, and S. Ulukus, “T oward s the secrecy capacity of the Gaussian MIMO wire-tap channe l: The 2-2-1 channel, ” IEEE T rans. Inf. Theory , submitted, September 2007. [22] T . Cov er and J. Thomas, E lements of Information Theory . Ne w Y ork: John Wile y Sons, Inc., 1991. [23] S. K. Leung-Y an-Cheon g and M. E . Hellman, “T he Gaussian wire-tap channel, ” IEEE Tr ans. Inf. Theory , vol. 24, no. 4, pp. 51–456 , Jul. 1978. [24] R. Liu, I. Maric, P . Spasojevic, and R. Y ates, “Discrete memoryless i nterference and broadcast channels with confidential messages: Secrecy rate re gions, ” IEE E T rans. Inf. Theory , submitted, Feb 2007. [Online]. A va ilable: http://arxiv .org/PS$ $cache/cs/pdf/07 02/070209 9.pdf [25] U. Maurer and S . W olf, “Information-theoretic ke y agreement: F rom w eak to strong secrecy for free, ” in Pr oc. E UR OCRYPT , Lectur e Notes in Computer Science , vo l. 1807, 2000, pp. 351–368 . [26] D. Slepian and J. K. W olf, “Noiseless coding of correlated information sources, ” IEEE Tr ans. Inf. Theory , vol. 19, no. 4, pp. 471–480, Jul. 1973. [27] K. Marton, “ A coding theorem for t he discrete memoryless broadcast channel, ” IEEE T rans. Inf. Theory , vol. 25, pp. 306–311, May 1979. [28] G. Caire and S. Shamai (Shitz), “On t he achiev able throughput of a multiantenna Gaussian broadcast channel, ” IEEE Tr ans. Inf. Theory , vol. 49, no. 7, pp. 1691–1706, Jul. 2003. [29] W . Y u and J. M. Cioffi, “S um capacity of Gaussian vector broadcast channe ls, ” IEEE T rans. Inf. T heory , vol. 50, pp. 1875–189 2, Sep. 2004. [30] G. Strang, Li near Algebr a and Its Applications . W ellesley , MA: W ellesley-Cambridge Press, 1998.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment