Graph-Based Decoding in the Presence of ISI
We propose an approximation of maximum-likelihood detection in ISI channels based on linear programming or message passing. We convert the detection problem into a binary decoding problem, which can be easily combined with LDPC decoding. We show that…
Authors: Mohammad H. Taghavi, Paul H. Siegel
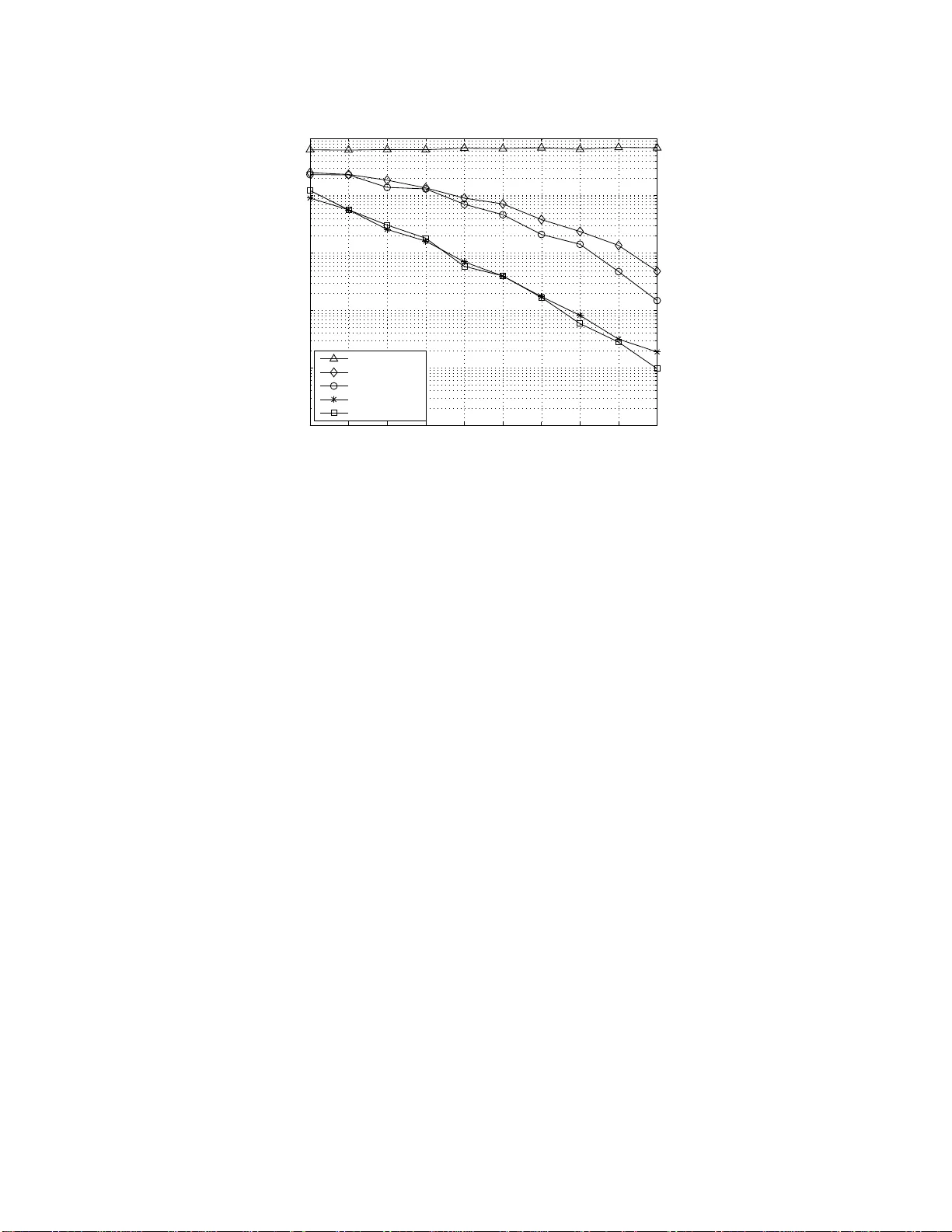
1 Graph-Based Decoding in the Presence of ISI Mohammad H. T agha vi and Paul H. Siegel Center for Magneti c Recording Research Univ ersity of California, San Diego La Jolla, CA 92093-040 1, USA Email: (mtaghavi, psiegel)@ucsd.edu Abstract W e propo se an approx imation o f maximum-likeliho od detection in ISI channels b ased o n linear progr amming or message passing. W e conv ert the detection prob lem into a binary decoding problem , which can be easily combined with LDPC deco ding. W e show that, for a certain class of channels and in the absen ce of coding , the proposed techniqu e provides the exact ML solution witho ut an exponen tial complexity in th e size of channel memory , wh ile for some other channels, this method has a non- diminishing prob ability o f failure as SNR inc reases. Some an alysis is provide d for th e error events of the proposed technique under linear progra mming. I . I N T RO D U C T I O N Intersymbol interferenc e (ISI) is a characteristic of many data c ommunications and storage cha nnels. Systems operating on these channels employ error - correcting codes i n conjunction wi th some ISI reduction technique, which, in magn etic recording systems, is often a c on ventional V iterbi detector . It is known that s ome gain will be obtained if the eq ualization and d ecoding b locks are combined at the rec eiv er by exchanging soft information b etween them. A p ossible approac h to achieving this g ain is to use soft- output equalization methods such as the BCJR algorithm [1] or the so ft-output V iterbi algorithm (SO V A) [2] along wit h iterati ve de coders. Howev er , both BCJR a nd SO V A suf fer from expo nential comp lexity in the length of the channe l memory . Kurkoski et al. [3] propose d two graph represe ntations of the ISI cha nnel tha t can be comb ined with the T anne r graph of the LDPC code for messa ge-pass ing decod ing. Th eir bit-based rep resentation of the channel co ntains many 4-cycles, wh ich resu lts in a significant p erformance degrada tion compared to maximum-likelihood (ML) d etection. On the other ha nd, me ssage passing (MP) on their state-base d representation, where me ssage s c ontain state rather than bit information, has a performance and overall October 26, 2018 DRAFT 2 complexity s imilar to B CJR, while benefiting from a parallel structure and reduc ed d elay . Among other works, S ingla et al. [4] applied messa ge pas sing on a bit-base d g raph representation of a two-dimensional ISI channel c ombined wit h an LDPC T an ner graph. Howe ver , s imilar to the case of o ne-dimensiona l ISI, the abundance of sho rt cycles prevents the algorithm from performing close to optimal. Linear programming (LP) ha s be en recen tly applied by Feldman et al. [5] to the problem of ML decoding of LDPC code s, as an a lternati ve to MP techn iques. In this me thod, the binary parity-chec k constraints of the c ode are relaxed to a set of linea r constraints in the real do main, thus turning the integer problem into an LP problem. While LP decoding performs closely to MP algo rithms such as the sum-product algorithm (SP A) and the min-sum algorithm (MSA), it is much easier to ana lyze for finite code lengths. Moti v ated by the suc cess of LP decoding , in this work we stud y the problem of ML detec tion in the presenc e of ISI, which c an be written as an integer q uadratic program (IQP). W e con vert this problem into a b inary decoding problem, which can be use d for MP dec oding, or , after relaxing the binary con straints, LP decod ing. Furthermore, deco ding an und erlying LDPC co de ca n b e inc orporated into this problem simply by including the parity checks of the cod e. By a ge ometric analys is we sh ow tha t, in the absenc e of coding, if the impulse response of the ISI channe l satisfies certain con ditions, the proposed LP relaxation is gua ranteed to produce the ML solution at all SNR values. This means tha t there a re ISI ch annels, which we call LP-proper chan nels, for which uncode d ML de tection c an be ac hiev ed with a complexity p olynomial in the channe l memory size. On the other end of the spe ctrum, so me channe ls are LP-impr oper , i.e. the LP method results in a no nintegral solution with a proba bility bounded aw ay from zero at all SNR, even in the a bsence of noise. Furthermore, we observe s ome intermediate asymptotically LP-pr oper cha nnels wh ere the performance asymptotically con verges to that of ML detection at high SNR. When mes sage pass ing is used ins tead of L P , we observe a similar behavior . Moreover , wh en LD PC decod ing is incorporated in the detec tor , LP-proper channels achieve very go od performanc e, while some other channe ls cannot go be lo w a certain word error rate (WER). The res t of this pape r is or ganized as follo ws . In Section II, we describe the c hannel, an d introduce the LP relaxation of ML de tection. The performance an alysis and simulation re sults of uncoded graph-based detection are presented in Section III. In Se ction IV , we s tudy the combination o f graph-bas ed detection and LDPC decoding , and Sec tion V co ncludes the paper . October 26, 2018 DRAFT 3 Fig. 1. Binary-input ISI channel. I I . R E L A X A T I O N O F T H E E Q UA L I Z A T I O N P RO B L E M A. Channel Model W e co nsider a partial-response (PR) channe l with bipo lar (BPSK) inp uts, a s desc ribed in Fig. 1, and use the follo wing notation for the transmitted symbols. Notation 1: The bipolar version of a binary sy mbol, b ∈ { 0 , 1 } , is denoted by ˜ b ∈ {− 1 , 1 } , a nd is giv en by ˜ b = 1 − 2 b. (1) The partial-response channe l transfer polyn omial is h ( D ) = P µ i =0 h i D i , where µ is the channe l memory s ize. Thus , the o utput se quenc e of the PR cha nnel in Fig. 1 before adding the white Ga ussian noise can be written as y t = µ X i =0 h i ˜ x t − i . (2) B. Maximum-likelihood (ML) Detection Having the vector of received samples r = [ r 1 r 2 · · · r n ] T , the ML de tector solves the optimization problem Minimize r − y 2 Subject to x ∈ C , (3) where C ⊂ { 0 , 1 } n is the code book a nd k · k 2 denotes the L 2 -norm. By expan ding the s quare of the objectiv e function, the prob lem b ecomes equiv alent to minimizing X t ( r t − y t ) 2 = X t r 2 t − 2 r t X i h i ˜ x t − i + X i h i ˜ x t − i ! 2 = X t r 2 t − 2 r t X i h i ˜ x t − i + X i h 2 i ˜ x 2 t − i + X X i 6 = j h i h j ˜ x t − i ˜ x t − j , (4) October 26, 2018 DRAFT 4 where, for simplicity , we have dropp ed the limits of the summations. Equiv alently , we can write the problem in a general matrix form Minimize − q T ˜ x + 1 2 ˜ x T P ˜ x , Subject to x ∈ C , (5) where in this problem q t = P i h i r t + i , and P = H T H , with H de fined as the n × n T oep litz matrix H = h 0 0 · · · . . . . . . h µ · · · h 0 0 0 h µ h 0 0 . . . . . . . . . 0 · · · 0 h µ · · · h 0 . (6) Here we have assumed that µ zeros a re padded at the b eginning and the e nd of the transmitted se quence , so that the tr ellis diagram corresp onding to the ISI channel starts and ends at the zero state. If the signals are unc oded, i.e. C = { 0 , 1 } n , and q and P are cho sen arbitrarily , (5) will represe nt the ge neral form of an integer quadratic programming (IQP) problem, which is, in general, NP-hard. In the specific case of a PR cha nnel, wh ere we hav e the T oeplitz structure of (6), the problem can be solved by the V iterbi algorithm with a co mplexity linear in n , b ut exponential in µ . Howe ver , this mode l c an also be use d to describe other prob lems s uch a s detec tion in MIMO or two-dimensional ISI cha nnels. Also, when the source s ymbols hav e a non-binary alphabe t with a regular lattice structure su ch a s the QAM and P AM alphabets, the problem can b e reduced to the binary problem of (5) by introducing some new variables. C. Pr ob lem R elaxation A co mmon approac h for solving the IQP problem is to first con vert it to an integer LP problem by introducing a new variable for ea ch quad ratic term, and the n relax the integrality cond ition; e.g. see [6]. While this relaxed p roblem does n ot n ecess arily have a n integer solution, it can be us ed along with branch-and -cut techn iques to solve integer problems of reas onable siz e. A more recent metho d is based on dualizing the IQP problem twice to obtain a con vex rela xation in the form of a semi-definite program (SDP) [7][8]. In this work, we use the linea r relaxation d ue to the lower complexity of solving LP s c ompared to SDPs. Unlike in [6], whe re the a uxiliary variables are ea ch defin ed as the product of two 0-1 variables, we October 26, 2018 DRAFT 5 define the m as the produ ct of ± 1 variables, which, a s we will see, translates into the modulo-2 addition of two bits when we move to the 0-1 d omain. This relaxation is more su itable for our pu rpose, since modulo-2 additiv e constraints are similar to parity-check constraints; thus, message -passing decoders designed for linear co des can be applied without a ny mo dification. Howe ver , it ca n be shown that this relaxation gi ves the exac t same solution as in [6]. T o linearize (4), we defi ne ˜ z t,j = ˜ x t · ˜ x t − j , j = 1 , . . . , µ, t = j + 1 , . . . , n . (7) In the binary domain, this will be equivalent to z t,j = x t ⊕ x t − j , (8) where ⊕ stand s for modulo-2 addition. Hence , the right-hand side of (4) is a linear combination of { x t } and { z t,j } , plus a c onstant, giv en that ˜ x i 2 = 1 is a constant. W ith some simplifications, the IQP in (5) can be rewri tten as Minimize X t q t x t + X t X j λ t,j z t,j , Subject to x ∈ C , z t,j = x t ⊕ x t − j , j = 1 , . . . , µ, t = j + 1 , . . . , n , (9) where, in the equalization problem, λ t,j = − P t,t − j = − min( µ − j,n − t ) X i =0 h i h i + j . (10) In this optimization prob lem, we call { x i } the information bits, and { z t,j } the state b its. It ca n be seen from (10) that λ t,j is indepe ndent of t , except for indices n ear the two ends of the b lock; i.e. 1 ≤ t ≤ µ and n − µ + 1 ≤ t ≤ n . In practice, this “ed ge effect” can b e n eglected due to the z ero p adding at the transmitter . For clarity , we sometimes drop the first subs cript in λ t,j , when the analysis is sp ecific to the PR detection problem. The comb ined equalization and dec oding problem (9) has the form of a single de coding problem, which can be rep resented by a lo w-density T ann er graph. Fig. 2 sh ows a n example of the c ombination of a PR channe l of memory s ize 2 with an LDP C cod e. W e call the up per and lower layers of this T an ner graph the code layer and the P R layer (or the PR g raph), res pectively . The PR layer of the g raph c onsists of October 26, 2018 DRAFT 6 Fig. 2. PR channel and LDPC code r epresented by a T anner graph. µn c heck nodes c t,j of degree 3, e ach con nected to two information bit nodes x t , x t − j , and one distinct state bit n ode, z t,j . Also, the PR layer can contain cycles of len gth 6 an d higher . If a c oefficient, λ t,j , is zero, its co rresponding state bit n ode, z t,j , and the check node it is connected to can b e eliminated from the graph, as they have no e f fect o n the decoding process . It follows from (10) that the coefficients of the state bits in the objectiv e fun ction, { λ t,j } , a re only a function of the P R chan nel impulse response, while the coe f ficients o f the information b its are the res ults of matched filtering the noisy received signal by the cha nnel impulse response, and therefore depende nt on the noise rea lization. Once the variable coefficients in the objective function are determined, LP decoding can be applied to s olve a linear relaxation o f decoding on this T a nner graph. W e call this method LP detection . In the relaxation o f [5], the binary pa rity-check con straint corresp onding to each c heck node c is relaxed as follo ws. Let N c be the index set of neighb ors of check node c , i.e. the variable nodes it is directly conne cted to in the T a nner g raph. Then, we include the follo wing constraints X i ∈ V x i − X i ∈ N c \ V x i ≤ | V | − 1 , ∀ V ⊂ N c s.t. | V | is odd . (11) In addition, the integrality c onstraints x i ∈ { 0 , 1 } are relaxed to bo x co nstraints 0 ≤ x i ≤ 1 . This relaxation has the “ ML c ertificate property , ” i.e . if the solution of the relaxed LP is integral, it will also be the solution of (9). The coefficients in the linear objective function, after some n ormalization, can also be treated as log- likelihood ratios (LLR) of the c orresponding bits, which can be used for iterati ve MP d ecoding . In this work, we have mostly use d the Min-Sum Algorithm (MSA), since, similar to LP deco ding, it is not aff ected by the uniform normalization of the variable coefficients in (9). October 26, 2018 DRAFT 7 I I I . P E R F O R M A N C E A N A L Y S I S O F U N C O D E D D E T E C T I O N In this section, we study the performance of L P detection in the a bsenc e of coding, i.e. solving (5) with C = { 0 , 1 } n . It is known that if the of f-diagonal elements of P are all nonpos iti ve; i.e. λ t,j ≥ 0 , ∀ j 6 = 0 , t , the 0-1 problem is solvable in polynomial time by reduc ing it to the MIN-CUT problem; e .g. see [9]. As an example, Sankaran and Ephremides [10] ar gued using this fact that when the spreading sequence s in a synchronou s CDMA system have nonpositiv e cross correlations, optimal mu ltiuser de tection can b e done in polyno mial time. In this s ection, we deriv e a slightly weaker co ndition than the non negativit y of λ t,j , as the ne cessa ry and sufficient co ndition for the succe ss of the LP relaxation to result in a n integer s olution for any value of q in (9). This analysis also sheds some li ght on the question of ho w the algorithm behaves in the general case, where this condition is not satisfie d. For a che ck node in the T an ner graph con necting information bit node s x t and x t − j and state bit no de z t,j , the constraints (11) can be summarized as z t,j ≥ max [ x t − x t − j , x t − j − x t ] z t,j ≤ min [ x t + x t − j , 2 − x t − x t − j ] , (12) which can be further simplified as | x t − x t − j | ≤ z t,j ≤ 1 − | x t + x t − j − 1 | . (13) Since the re is exactly one su ch pair o f up per and lo wer bound s for e ach state b it, in the s olution vector , z t,j will be equal to either the lower or u pper bound, depen ding on the sign of its coef ficient in the linear objectiv e function, λ t,j . Hence, having the coefficients, the c ost of z t,j in the objec ti ve function can be written as λ t,j z t,j = λ t,j | x t − x t − j | if λ t,j ≥ 0 , λ t,j − λ t,j | x t + x t − j − 1 | if λ t,j < 0 , (14) where the first term in the se cond line is cons tant and doe s not aff ect the solution. Con seque ntly , by substituting (14) in the objec ti ve function, the LP problem wil l be projected into t he original n -dimens ional space , giving the equ i valent minimization problem Minimize f ( x ) = X t q t x t + X X t,j : λ t,j > 0 | λ t,j || x t − x t − j | + X X t,j : λ t,j < 0 | λ t,j || x t + x t − j − 1 | , Subject to 0 ≤ x t ≤ 1 , ∀ t = 1 , . . . , n, (15) October 26, 2018 DRAFT 8 which ha s a c on vex and p iecewise-linear objecti ve function. Each ab solute value term in this expression correspond s to a che ck n ode in the PR layer of the T ann er graph represe ntation of the channel. A. LP-Pr op er Ch annels: Guaranteed ML P e rformanc e For a clas s o f channels , which we ca ll L P-pr op er chann els , the proposed LP relax ation of uncod ed ML detec tion always giv es the ML solution. Th e follo wing theorem provides a c riterion for recognizing LP-proper channe ls. Theorem 1: The LP relaxation o f the integer optimization problem (9), in the abse nce of coding, is exact for every transmitted seq uence a nd ev ery no ise configuration if and o nly if the follo wing co ndition is satisfied for { λ t,j } : W eak N onnegativity Condition (WNC) : Every check node c t,j , co nnected to variable nodes x t and x t − j , which lies on a cycle in the P R T anne r graph correspond s to a no nnegativ e coefficient; i.e. λ t,j ≥ 0 . Pr oo f: W e first prove that WNC is suf ficient for guaranteed con ver ge nce of LP to the ML seque nce, and the n show that if this condition is no t satisfied, there are c ases wh ere the LP a lgorithm fail s. In the proof, we make use of the follo wing definition. Definition 1: Consider a piecewise-linear function f : R n 7→ R . W e c all a a b r eakpoint of f if the deriv ative of f ( a + sv ) with res pect to s chan ges at s = 0 , for any nonze ro vector v ∈ R n . 1) Sufficiency: It is sufficient to show that under WNC, the solution of (15) is a lw ays at one of the vertices of the unit cube, [0 , 1] n . First cons ider (15) wit hout the box c onstraints. The optimum point, x ∗ , of the objective function has to oc cur either at infinity or at a breakpoint of this piece wise-linear func tion. Since the nonlinea rity in the func tion comes from the terms in volving the absolute value function, e ach breakpoint, a , is de termined by making n o f these absolute value terms active , i.e . setting their arguments equal to zero. These n terms should have the prope rty that the linear s ystem of equations obtained by setting their arguments to z ero has a unique solution. When the fe asible region is restricted to the unit cube [0 , 1] n , the optimum can also oc cur a t the bounda ries of this region. W ithout loss of ge nerality , we ca n ass ume that the optimum p oint lies on a number , k , of hype rplanes co rresponding to the box constraints in (15), whe re k = 0 , . . . , n . This will make exactly k v ariables, x i , i ∈ I , equa l to e ither 0 o r 1, where | I | = k . In ad dition, at leas t n − k other equations a re needed to de termine the remaining n − k fractional variables. The se equations will be the res ults of ma king a nu mber of abs olute value te rms acti ve, each of the m having one of the two forms x t = x t − j or x t + x t + j = 1 , de pending on whether λ t,j > 0 or λ t,j < 0 , resp ectiv ely . Whe n an October 26, 2018 DRAFT 9 absolute v a lue te rm in (15) is ac ti ve, either both, or none of its variables can be integer . Since the former case do es no t provide an equation in te rms of the fractional variables, we can as sume that all these a ctiv e absolute value terms only in volve fractiona l vari ables. Now the q uestion become s under wha t condition su ch equ ations ca n hav e a unique and non integral solution. W e c an illustrate this s ystem o f equations by a depen dence graph , whe re the vertices correspond to the unknowns, i.e., the n − k fractional variable n odes, and between vertices x s and x s − i there is a positive edg e if λ s,i > 0 and a ne gative edge if λ s,i < 0 . An example of a depende nce graph sa tisfying WNC is shown in Fig. 3. In the so lution of the system of equations , if two vertices are connected in the de penden ce graph by a positive edg e, they will have the same value. Hen ce, we c an merge these two vertices into a single vertex, and the value that this vertex takes will be shared by the two original vertices. If we do this for e very pos iti ve ed ge, we will be left with a reduce d depe ndence graph that has only negative edges . W e claim that, if WNC is satisfied, the reduced grap h will be tree. T o see this, consider a negati ve edge e t,j connec ting vertex x t on its “left side” to vertex x t − j on its “right side” in the o riginal d epende nce graph. By a ssumption, e t,j is not o n a cycle, which means if we remove it, its left side and right side will become d isconnec ted. Clearly , d uring the above-mentioned mer ging of vertices, no new conne ction will be created b etween the left and right sides of e t,j . Hence , ev ery negati ve edge will still not be on any cycle at the end of the mer ging procedure, and, in other words, the reduced depend ence graph will be a tree. S ince trees hav e fe w er edge s than vertices, the s ystem of eq uations for determining the unknown variables will be und er- determined, and no ne of the nodes in the depend ence graph will have a unique solution. Conse quently , the only case where we have a unique solution for all the variables will be k = n , which me ans that all of the variables { x i } are integral. This proves the sufficiency of WNC. 2) Neces sity: W e prove the necess ity of the condition by a counter example. Consider a cas e where the realization of the n oise sequen ce is such that the received seq uence is zero. This will make { q t } , the coefficients o f the linea r term in (15 ), e qual to zero. Hence we are left with the positiv e-weighted sum of a n umber of absolute value terms, each of them being greater than or e qual to zero. The objectiv e function will bec ome zero if a nd o nly if all the se terms are zero, wh ich is sa tisfied if x = [ 1 2 , . . . , 1 2 ] T . W e need to show that if WNC is not s atisfied, eq uating a ll the absolute value terms to zero will de termine a unique a nd fractional value for at lea st one of the eleme nts of x . Co nsider the depende nce graph of this sys tem of equations. W e know that there is at least one cycle containing a nega ti ve edge. Consider the equa tions corres ponding to one suc h cycle. W ithout loss of gen erality , we can as sume that all these equations hav e the form x t + x t + j = 1 , since if any of the m ha s the form x t = x t + j , we ca n combine October 26, 2018 DRAFT 10 Fig. 3. The dependence graph of the system of linear equations with one cluster of cycles. Solid lines represent positive edges and dashed li nes represent negati ve edges. these two variables into on e. Conse quently , the system of eq uations correspon ding to this cycle , after some column permutations will have the matrix form 1 1 0 · · · 0 1 1 0 . . . . . . 1 · · · 0 1 x i 1 x i 2 . . . x i l = 1 1 . . . 1 . (16) Since the co efficient matrix is full rank, the u nique solution o f this sy stem is x i k = 1 2 , k = 1 , . . . , l . Th is means that no integral vector x can make the objective function in (15 ) zero, a nd therefore the algorithm fails to find an integral s olution. This proves the ne cess ity of WNC for gu aranteed succes s of the LP relaxation. Cor o llary 1: T he solutions of the LP relaxation of unco ded ML equa lization are i n the space { 0 , 1 2 , 1 } n . Pr oo f: The values of fractional eleme nts of x are the u nique solutions of a system of linear equations of the forms x t = x t + i and x t + x t + i = 1 . The vector [ 1 2 , . . . , 1 2 ] satisfies all these equations , a nd, hence, has to be the unique solution. B. Implications of the WNC In the PR chan nel eq ualization problem, due to the pe riodic s tructure of the T ann er graph and the coefficients of the state variables, the WNC implies that at lea st one of the following statements should be valid: 1) The PR T ann er g raph is acyclic. Ex amples include any PR channel with memory size µ = 1 , and the memory-2 chann el h ( D ) = 1 + D − D 2 . October 26, 2018 DRAFT 11 2) Nonnegativity Condition (NC): All state v ariables ha ve nonnega ti ve coefficients; i .e. λ t,j ≥ 0 ∀ t, j . Lemma 1: Condition 1 implies that, among { λ t,j : j = 1 , 2 , . . . } , o n a verage at most one can be nonzero for each t . Pr oo f: Let κ be the average numb er of nonzero elements of { λ t,j : j = 1 , 2 , . . . } for each t . Then, it is eas y to see that the PR T anner grap h will have 3 κn edge s and n (1 + 2 κ ) vertices (i.e. variable o r check nodes ). But the graph ca n be acyc lic on ly if 3 κn ≤ n (1 + 2 κ ) − 1 , which mea ns tha t κ < 1 . In a on e-dimensiona l ISI c hanne l, where the state co efficients are given by (10), NC implies that the autocorrelation function of the discrete-time impulse respons e of the c hannel s hould be nonpo siti ve at any point other that the ze ro time s hift. As the me mory size of the channel inc reases, this condition be comes more restrictiv e, so that a long and rando mly-chosen impulse respo nse is not very likely to satisfy NC. Howe ver , it is v ery common, particularly in magnetic recording ap plications, to use the P RML techniqu e, where the overall impulse response of the ch annel is first equ alized to a target impulse respo nse, in order to s implify the subs equent detection stages. Th e tar get c hannel resp onse is usu ally optimized to provide the best d etection performance. A possible approach for employing the linea r relaxation of ML detection in this a pplication can be to optimize the target channel subject to NC , which e nables us to a chieve the performance of V iterbi detection, a lthough without an exponential complexity in the memory size. An interes ting a pplication of this result is in 2-D channe ls, for wh ich there is n o fea sible extension of the V iterbi algorithm. In a 2 -D ch annel, the rece i ved s ignal r t,s at coordinate ( t, s ) in terms of the transmitted symbol seque nce { ˜ x t,s } has the form r t,s = µ X i =0 ν X j =0 h i,j ˜ x t − i,s − j + n t,s . (17) Hence, follo wing the sa me proce dure that results in (10), the co efficients of the state vari ables in the 2-D channe l can also be obtained. In particular , the state variable defi ned as z ( t,s ) , ( k, l ) = x t,s ⊕ x t − k, s − l will have the coefficient γ k ,l = − µ X i =0 ν X j =0 h i,j h i + l,j + l . (18) In this express ion, for simplicity , we h ave droppe d the ( t, s ) index due to the independ ence of the γ from t and s , except ne ar the boundaries, which, in turn, can b e res olved by proper truncation of the transmitted array . Theorem 1 guarantees that ML de tection can be achieved by linear relaxation if N C is satisfied , i.e. γ k ,l ≥ 0 for any k , l > 0 . An exa mple of a 2 -D chann el satisfying NC is given by the matrix [ h i,j ] = 1 1 1 − 1 . (19) October 26, 2018 DRAFT 12 C. Err o r Ev ent Characterization: asy mptotically L P-Pr op er a nd LP-Improper Channe ls W e showed that if WNC is n ot satisfied, there a re no ise c onfigurations tha t results in the f ailure of LP detection to fin d the ML seq uence. Ho wev er , for some channels, such n oise configurations might be highly unlikely at high SNR values. W e h av e observed that for some ISI c hannels violating WNC, the probability of obtaining a fractional solution becomes domina ted by the proba bility that the ML sequen ce is different from the transmitted word. W e call these channe ls asymptotically LP-pr oper , since for these c hannels the WER of L P detec tion is asymptotically equ al to that of ML de tection as the SNR increases . On the other hand, for some other c hannels, which we call LP -impr ope r channe ls, there is a non-diminishing p robability that the solution of LP detection is nonintegral, as the SNR increa ses. In this subsec tion, we study the pe rformance of the un coded LP detec tion for gen eral ISI ch annels and deriv e conditions for failure of the detec tor to find the ML solution. The se conditions will he lp us to classify dif ferent chan nels based on their pe rformance. W ith some modifications , these co nditions can also be applied to 2-D ISI channe ls. Since here we focus on s tationary 1-D PR ch annels, as explained in Section II, we can assu me that λ t,j = λ j is indepen dent of t . Definition 2: Giv en the solution of LP detection, the fractional set , F = { i 1 , . . . , i n − k } ⊂ { 1 , . . . , n } , is the se t o f indice s of information bit n odes in the T a nner graph of the PR chan nel that have fractional values in the solution, ˆ x . W e know from C orollary 1 that the fractional e lements in the solution, ˆ x , are a ll equal to 1 2 . A reasona ble assumption su pported by our simulations at high SNR is tha t if the ML solution, x , is correct, the integer e lements o f ˆ x are correct, as well. In other words, we have ˆ x i = 1 2 if i ∈ F, x i if i / ∈ F . (20) For the ob jecti ve function f ( · ) of (15) we can write g ( x , ˆ x ) , f ( x ) − f ( ˆ x ) ≥ 0 . (21) By expan ding f using (15), this inequality can be written in terms of { λ t,j } , x , a nd q . Before doing so , we present the followi ng lemma to simplify the abso lute value terms in (15). Lemma 2: Let x t and x s be binary variables and ˜ x t and ˜ x s be their bipolar versions, res pectively . In addition, let’ s d efine h ( x, y , λ ) , | λ || x − y | if λ ≥ 0 , | λ || x + y − 1 | if λ < 0 . (22) October 26, 2018 DRAFT 13 Then, the follo wing equations hold: 1) h ( x t , x s , λ | t − s | ) = 1 2 | λ | t − s | | − 1 2 λ | t − s | ˜ x t ˜ x s , 2) h ( x t , 1 2 , λ | t − s | ) = 1 2 | λ | t − s | | , 3) h ( 1 2 , 1 2 , λ | t − s | ) = 0 . Pr oo f: T he equa tions can be verified by using (1), and c hecking the possible values for x t and x s . By using Le mma 2, a nd cance lling the terms that are common betwee n f ( x ) an d f ( ˆ x ) , g ( x, ˆ x ) can be written as g ( x , ˆ x ) = X t ∈ F q t x t − 1 2 + X s ∈ F , s µ . Since we assu med that x is equal to the transmitted seque nce, we can expan d q t as q t = µ X i =0 h i r t + i = µ X i =0 µ X i =0 h i h j ˜ x t + i − j + µ X i =0 h i n t + i = − t + µ X s = t − µ λ | t − s | ˜ x s + η t , (24) where η t , P i h i n t + i . By substituting (24) into (23 ), a nd using the fact that x t − 1 2 = − 1 2 ˜ x t , w e obtain g ( x , ˆ x ) = X t ∈ F 1 2 λ 0 + X s ∈ F , s 0 . (27) October 26, 2018 DRAFT 14 If the transmitted sequ ence, x , is given, we can estimate the probab ility that the su f ficient failure condition gi ven by Theorem 2 is satisfie d, and determine the domina nt error event causing this failure. In order to do that, for any giv en F , we ca n calcula te a “distance” for the error event c orresponding to F defined as d F = − c F − 1 2 ˜ x T F ¯ P F ˜ x F , (28) and the vari ance of the noise correspo nding to this error event, giv en by σ 2 F , var h η T F ˜ x F i = var X s n s s X t = s − µ, t ∈ F ˜ x t h s − t = σ 2 X s h s X t = s − µ, t ∈ F ˜ x t h s − t i 2 , (29) where σ 2 is t he vari ance of each noise sample, n t . Hence, the probability that the error e vent corresponding to F occurs will b e equa l to p ( F , ˜ x F ) = Q ( d F σ F ) , (30) where Q ( x ) is the Gauss ian Q func tion. In order to find the dominant error event ov er all transmitted se quence s, for every choice of the index set, F , we s hould find the vector ˜ x F ∈ {− 1 , 1 } | F | that maximizes the probability in (30). Howe ver , this will req uire an exha ustiv e sea rch over all ˜ x F . As an alternative, we can upper bound this probability by finding the smallest distance d min F , min ˜ x F d F and the largest v ariance σ 2 F max , max ˜ x F σ 2 F , and computing Q ( d min F /σ max F ) . Fort unately , each of these two optimization problems can be solved by dynamic programming (V iterbi algorithm) over a trelli s of at mos t 2 µ states. Specifica lly , if the minimum d istance is negati ve, there is a prob ability ind epende nt of the SNR that the seque nce ˜ x F correspond ing to that distan ce exists in the transmitted block, and gi ven tha t ev ent, the probability of failure, ( 30 ) , will be greater tha n 1 2 for any SNR value. The refore, there will be a non-diminishing probability of failure as SNR goes to infinity . This motiv a tes the follo wing results: Cor o llary 2 (LP-Improper Channe ls): If for a n ISI chan nel, there is a index set F ⊂ { 1 , . . . , n } and a vec tor ˜ x F ∈ {− 1 , 1 } | F | for which d F defined in (28) is negativ e, LP detec tion on this c hannel w ill have a non-diminishing WER as SNR grows; i.e., the chan nel is improper . On the other hand, if for an ISI c hanne l the probability of failure co mputed by the proposed technique decreas es more stee ply than the WER of ML detection as SNR increases , the WER of LP dete ction October 26, 2018 DRAFT 15 will be asymptotically equa l to that of ML d etection. In this cas e, the ch annel will be asymptotically LP-pr o per . Remark 1: The error events cons idered in this analysis are not the only p ossible types of detector failure. This analysis is intende d to approximate the gap betwee n the performance of LP a nd ML detection methods by e stimating the probability that L P detec tion fails to find the integer op timum (i.e., ML) solution, given the ML detector is su ccess ful. As mentione d be fore, we only studied the e vents where a vector having the form of (20) ha s a lower cost than the transmitted word. Therefore, even if (27) does not hold for any F , it is theoretically possible, although no t very likely , as we observed in prac tice, that LP detection has a fractional solution. Of particular interest among the po ssible error events is the o ne whe re the all- 1 2 vector has a lower cost than the correct solution; i.e., F = { 1 , . . . , n } in (27). For a given transmitted seq uence x , this ev ent is not neces sarily the most likely one. Howev er , stud ying this event provides us with a s implified sufficient condition for the failure of LP detection, which further clarifies the distinction between the dif ferent classes of ISI channe ls. The distan ce, δ , corresponding to this event is obtained by putting F = { 1 , . . . , n } in (28). If the block length, n is muc h lar ger than the channel me mory length, µ , we c an n eglect the “edge effects” caus ed by the indices that are within a distanc e µ of o ne of the two en ds of the sequenc e; thus, we will have δ = − nλ 0 − n µ X j =1 | λ j | − µ X j =1 λ j X t ˜ x t ˜ x t + j = − nλ 0 − n µ X j =1 | λ j | − µ X j =1 λ j ρ j , (31) where ρ j is the autocorrelation of ˜ x with a shift equal to j . On the othe r ha nd, for the noise variance, ς 2 , c orrespond ing to this event we have from (29) ς 2 = σ 2 X t µ X j =0 h j ˜ x t − j 2 = σ 2 ˜ x T P ˜ x = − σ 2 nλ 0 − 2 σ 2 µ X j =1 λ j ρ j . (32) Note that δ and ς 2 have a s imilar depend ence on the transmitted se quence . A p ossible approach for finding the likelihood of occurrence of an all- 1 2 error ev ent is to maximize δ ς over a ll poss ible transmitted sequen ces. However , with a random transmitted s equenc e, the probability that this quantity become s clos e to its worst case may b ecome very low for long block lengths. As an October 26, 2018 DRAFT 16 alternati ve, h ere we show that as n grows while µ rema ins fixed, the dep endenc e of both δ an d ς 2 on the transmitted sequen ce beco me negligible compared to the con stant term. Lemma 3: Let ˜ x 1 , . . . , ˜ x n be a seq uence of i.i.d. ± 1 rando m variables, each equally likely to be + 1 or − 1 , and let ρ j = P n − j t ˜ x t ˜ x t + j . T hen, for fixed µ , a s n → ∞ 1 n µ X j =1 λ j ρ j → 0 almost surely . (33) Pr oo f: For ea ch j = 1 , . . . , µ , ρ j is the sum of n − j terms o f the form ˜ x t ˜ x t + j . Clearly , e ach of these terms is equally likely to be e qual to +1 or − 1 . Furthermore, it can be shown that these terms are mutually indepen dent 1 . Hence, using the strong law o f lar ge numbers, we have ρ j n = n − j n 1 n − j n − j X t =1 ˜ x t ˜ x t + j → 0 almost surely , (34) where we used the fact tha t n − j /n → 1 , since 1 ≤ j ≤ µ . Co nsequ ently , 1 n µ X j =1 λ j ρ j = µ X j =1 λ j ρ j n → 0 almost surely , (35) since it is a linear combina tion of a fin ite number of variables, each going to zero almost surely . Using Lemma 3 in (31) and (32) for large n , we can write δ = n h | λ 0 | − µ X j =1 | λ j | + o (1) i , (36) and ς 2 = σ 2 n | λ 0 | + o (1) , (37) where we used the fact that λ 0 = − P h 2 i ≤ 0 . Since the probability of the all- 1 2 error event is equal to Q ( δ /ς ) , the a bove results motiv ate us to define the following parameter to c haracterize this proba bility in the limit of n → ∞ . Definition 3: The LP distanc e , δ ∞ , of a partial-response chan nel is g i ven by δ ∞ = 1 | λ 0 | | λ 0 | − µ X j =1 | λ j | . (38) The LP dis tance is dimen tion-less parameter that c an take values be tween −∞ and 1 . The followi ng theorem gi ves a new sufficient condition in terms of the LP-distance for a chan nel to be LP-imprope r . Theorem 3: The WER of u ncoded LP detection over an ISI channe l with the transmitted seq uence generated as a ran dom sequen ce o f i.i.d. Bernouli (1 / 2) bina ry s ymbols goes to 1 as the block len gth n 1 For a proof of this st atement refer to P roposition 1.1 of [11]. October 26, 2018 DRAFT 17 goes to infinity for a ny SNR, i.e., the ch annel is LP-improper , if the LP distance, δ ∞ , of the cha nnel is nonpos iti ve Pr oo f: As me ntioned earlier , the probability o f the all- 1 2 ev ent is e qual to Q ( δ /ς ) . From (36) and (37), for lar ge n we have δ ς = √ n δ ∞ p | λ 0 | σ + o (1) . (39) If δ ∞ < 0 , the right-hand side will approach −∞ as n increas es, h ence, Q ( δ /ς ) will go to 1. Having δ ∞ as a measu re of LP-properne ss for LP de tection, it is interesting to study how it beh av es for LP-proper chan nels; i.e ., those sa tisfying WNC in Theo rem 1. The follo wing lemma provides an answer to this question. Lemma 4: For L P-proper chan nels that satisfy NC (define d in in III-B) δ ∞ > 1 2 | λ 0 | . Pr oo f: F or any ISI channe l, we ca n write h µ X i =0 h i i 2 = X i h 2 i + X X i,j ; i 6 = j h i h j = | λ 0 | − 2 µ X j =1 λ j ≥ 0 . (40) Hence, µ X j =1 λ j ≤ 1 2 | λ 0 | . (41) Since NC is satisfied , λ j ≥ 0 , ∀ j ≥ 1 . Therefore, we have δ ∞ = | λ 0 | − µ X j =1 λ j ≥ 1 2 | λ 0 | . (42) D. Simulation Results W e have simulated cha nnel d etection on the PR T ann er graph us ing LP decoding and MSA for three PR chann els of memory size 3: 1) CH1: h ( D ) = 1 − D − 0 . 5 D 2 − 0 . 5 D 3 (with δ ∞ = 1 2 , satisfies WNC; LP-proper), 2) CH2: h ( D ) = 1 + D − D 2 + D 3 (with δ ∞ = 1 2 ), 3) CH3: h ( D ) = 1 + D − D 2 − D 3 (with δ ∞ = 0 ; LP-improper). October 26, 2018 DRAFT 18 −2 0 2 4 6 8 10 −5 10 −4 10 −3 10 −2 10 −1 10 0 Normalized SNR, dB BER CH1, LP CH1, MSA CH2, LP CH2, MSA CH2, ML CH3, LP CH3, MSA Fig. 4. BER for CH1-CH3. SNR is define d as the transmitted signal power to t he receiv ed noise v ariance. Uncoded bit e rror rates (BER) of detec tion on these c hanne ls us ing LP a nd MSA are s hown Fig. 4. Since CH1 satisfies WNC, LP will be equiv alent to ML on this cha nnel. For CH2, we have also provided the BER of ML. Exce pt at very low SNR where we se e a sma ll difference, the performance of L P and ML are nea rly e qual, which mean s that CH2 is an a symptotically LP-proper c hannel. For bo th CH1 a nd CH2, MSA, con ver g es in a t most 3 iterations and has a BER very close to that of LP . On the othe r hand, for CH3, which is an LP-improper ch annel, we ob serve tha t the BERs of LP and MSA are a lmost con stant. In Fig. 5, we stud ied the effect of δ ∞ of ISI ch annels on the performance of LP de tection. In this scena rio, we rando mly generate 2 00 ISI channe ls w ith memo ry 4, such tha t the taps o f the impulse response are i.i .d. wit h a zero-mean Gauss ian distribution. In addition, we no rmalize eac h channe l so that the total e nergy of the impulse response is one; i.e. | λ 0 | = 1 . W e simulated the uncode d LP detection with random transmitted seq uence s of len gth 100 at the SNR of 11 dB. In the upper and middle plots of Fig. 5, res pectively , the WER of LP detection a nd the ratio o f the WER of LP detection to that of ML detection are shown versus δ ∞ for the se chann els. In this work, ML detection was performed by using the cutting-plane method proposed in [12 ]. This method is based on using redundant p arity checks (RPC) gen erated b y modulo-2 co mbination of a s ubset of parity-check c onstraints. Once the LP decoding results in a nonintegral s olution, we look for RPCs that, after linear relaxa tion, introduce a cut, i.e., make the current solution infeasible , and re-solve the LP after adding these cons traints. This is continued until we ob tain a n integral so lution, wh ich is the ML seq uence . For 192 of the 200 chan nels that we stud ied, October 26, 2018 DRAFT 19 −0.8 −0.6 −0.4 −0.2 0 0.2 0.4 0.6 0.8 10 −2 10 0 d ∞ WER LP −0.8 −0.6 −0.4 −0.2 0 0.2 0.4 0.6 0.8 10 0 10 2 d ∞ WER LP / WER ML −0.8 −0.6 −0.4 −0.2 0 0.2 0.4 0.6 0.8 0 10 20 30 d ∞ Fig. 5. Upper and middle plots: Performance of LP detection versus δ ∞ for random ISI channels of memory 4 at the SNR of 11 dB. Lower plot: The histog ram of δ ∞ . this algorithm always su ccess fully provided the ML so lution with a fe w iterations. The res ults in Fig. 5 de monstrate a strong c orrelation be tween the performance o f the algorithm a nd the value of δ ∞ . In particular , almos t every channel with δ ∞ < 0 . 1 has a WER close to 1, while for almost ev ery cha nnel with δ ∞ > 0 . 4 , the WER of LP is very close to that of ML detection. W e have obs erved that d etection by MSA h ad a similar behavior , except for some c hannels with 0 . 05 < δ ∞ < 0 . 3 , for which MSA is significantly su perior to LP . In o ther words, the transition from LP-improper to LP-proper behavior starts from sma ller v alues of δ ∞ for MSA. As a n estimate of the proba bility density func tion of δ ∞ for this random co nstruction of the channe l response , its histogram has be en inc luded in the lower plot of Fig. 5. October 26, 2018 DRAFT 20 I V . C O M B I N E D E Q UA L I Z A T I O N A N D L D P C D E C O D I N G One of the main advantages of the graph -based detection propose d in Sec tion II is that it lends itself to the combining of the e qualization with the dec oding of a n underlying error-correcting c ode. In this section, we study this joint detec tion scheme using both the linear programming and the MP algorithms. A. Coded Linear Pr ogramming De tection Joint LP e qualization and dec oding, i.e ., the linear relaxation of (9), is a linear optimization problem in the form of the uncod ed LP detection, with the addition o f the linea r inequalities c orrespond ing to the relaxation of the parity-chec k c onstraints of the code . Thes e n ew constraints cut off from the fea sible polytope so me of the fractional vertices that can trap the unco ded detection problem, but they also a dd new fractional vertices to the polytope. It is not ea sy to deriv e g eneral conditions for the succ ess or failure of this p roblem. Howe ver , we can make the follo wing generalization of Theorem 3: Cor o llary 3: Co nsider a linear code with no “tri v ial” (i.e., degree -1) parity ch eck, used on a chan nel satisfying δ ∞ < 0 , where δ ∞ is defined in ( ?? ). The n, cod ed LP d etection on this s ystem has a non- diminishing WER for large b lock len gths. Pr oo f: W e have shown in Section III-C that if this condition is satisfied, the all- 1 2 vector will have a lo wer c ost than the transmitted vector with high p robability . 2 It is now enough to show that the a ll- 1 2 vector will no t b e cu t off by a ny error co rrecting cod e. T o see this, cons ider a relaxed parity-check inequality of the form X i ∈ V x i − X i ∈ N c \ V x i ≤ | V | − 1 , ∀ V ⊂ N c s.t. | V | is odd , (43) where N c ≥ 2 . T o prove that this constraint is s atisfied by the a ll- 1 2 vector , we conside r two cases: | V | = 1 , and | V | ≥ 2 . If | V | = 1 , the first su m in (43) will be equal to 1 / 2 , and the s econd sum will be greater than or equal to 1 / 2 , since N c \ V h as at least one member . Hence, the left-hand side of (43) will be les s tha n or equal to | V | − 1 = 0 . Also, if | V | ≥ 2 , the first sum will be equa l to | V | / 2 ≤ | V | − 1 , while the se cond sum is non-negativ e. The refore, the left-hand side of the ineq uality will be less than or equal to its right-hand side. Conseq uently , in both cases (43) will be satisfied . 2 The deriv ation of the limit of δ was based on the assumption that the transmitted sequence is an i .i.d. sequence, so that (3) holds. While the tr ansmitted sequen ce is no longer i. i.d. i n the presence of coding, we implicitly assume that (3) still holds. This is a suf ficiently accurate assumption for all codes of practical interest. In particular, (3) can be pro ved for a random ensemble of LDPC codes. October 26, 2018 DRAFT 21 B. Coded Message-P ass ing Detection Similar to LP de tection, MP de tection can be extended to code d systems by ad ding the p arity-check constraints of the code to the PR T anner graph , as shown in Fig. 2, an d treating it as a single T anner grap h defining a linear code. Desp ite many similarities, LP and MP deco ding sche mes have a diff erent nature, which makes them b ehave d if ferently when used for joint equa lization an d detection. For example, we cannot de ri ve a conclus ion similar to C orollary 3 for MP detection. On the contrary , we have obs erved in the simulation results that there are LP-improper chan nels for which code d MP de tection does not inherit the undes irable performance of unco ded MP detection. In this work, we use both the min-sum algorithm and the sum-product algorithm (SP A) for the implementation of co ded MP d etection. Similar to the uncod ed case, a s the o bjectiv e coefficients of MSA, we use the same c oefficients a s those of LP d etection, i.e., { q t } and { λ t,j } , sinc e MSA is in variant under the scaling o f the c oefficients. For SP A, we obs erve that each q t contains a Gaussian noise term with vari ance propo rtional to σ 2 . Hence, one can ar gue tha t a suitable normalization of the objec ti ve coefficients to es timate the “ equiv alent LLRs ” is to multiply all the objec ti ve coefficients by 2 /σ 2 . An advantage of this normalization is that, in the absenc e o f ISI, the normalized coefficients be come the true LLR of the receiv ed s amples. In this work, we have used the equiv a lent LLRs obtaine d by this normalization for SP A detection. MSA an d SP A decod ing are, respe cti vely , approximations of ML and a posteriori probab ility (APP) detection on the T ann er graph d efining the code . The se approximations becomes exact if the me ssage s incoming to a ny n ode a re statistically indep endent. This hap pens if the T anne r g raph is cyc le-free a nd the channel observations (i.e., the a priori LLRs) a re indepen dent. In the propose d graph -based detection neither of thes e two con ditions is satisfie d. In particular , the PR laye r of the graph con tains many 6-cycles, and the channel observations, { q t } , are the results of matched filtering of the received s ignal, a nd thus contain colored noise. In order to miti gate the positive feed back due to the cycles of the PR layer , we propose selective message passing for coded de tection, which has a modified c ombining rule for mes sages at the information bit nodes. This modified co mbining scheme is illustrated in Fig. 6. In this method, the me ssage o utgoing from an information bit no de through a n edge e in the code laye r is comp uted as a combination of the channe l obs ervation and the messag es inco ming to the bit node throug h all edges, except edge e . On the othe r h and, the messa ge outgoing through an edge in the PR laye r is a c ombination of the channe l observation a nd messages incoming through o nly the edges in the code laye r . Since there are no 4-cycles October 26, 2018 DRAFT 22 Fig. 6. Selectiv e message passing at the information bit nodes: (a) Calculating a message outgoing to the code layer (b) Calculating a message outgoing to t he PR layer . in the PR laye r of the gra ph, this modification blocks any closed-loop circulation of messages inside the PR layer . In other words, messag e passing inside the PR layer will bec ome loop-free. However , the re still remain cycles in the code layer , as well as cycles that are generated by combining the code an d PR layers. In our simulations, s electiv e MP performed as an eff ecti ve tool for improving code d MP detection of some chann els with und esirable properties, such a s the EPR4 chann el. C. Simulation Results In this subs ection, w e prese nt simulation results of coded de tection in the presenc e of ISI us ing the scheme s prop osed in this section. In a ll cas es, we have us ed a regular LDPC code of length 200, rate 1 / 4 , and variable degree 3. The follo wing PR chann els have been used in these simulations: 1) No-ISI Channel: h ( D ) = 1 , 2) EPR4 Channel: h ( D ) = 1 + D − D 2 − D 3 ( δ ∞ = 0 , LP-improper), 3) Modified EPR4: h ( D ) = 1 + D − D 2 + D 3 ( δ ∞ = 1 2 , asymptotically LP-proper), 4) PR4 Channel: h ( D ) = 1 − D 2 ( δ ∞ = 1 2 , LP-proper). In F ig. 7, the B ER of cod ed LP and MSA detection h as bee n plotted versus E b / N o for the above channe ls. For a ll cha nnels, exce pt in the ISI-free cas e, code d MSA detec tion outpe rforms c oded LP detection. In particular , for the EPR4, coded LP detection has a BER of abo ut 1 / 2 for all S NR values, as predicted by Corollary 3, while coded MSA detection has a monotonic ally-decreasing BE R. T o study the behavior of the dif feren t de tection metho ds for the EP R4 channel in more d etail, in Fig. 8, the BER has been plotted versu s E b / N o for LP , MSA, selec ti ve MSA, SP A, and se lecti ve SP A. One can obs erve in this fig ure that se lecti ve message passing is mo stly effecti ve for MSA, for which there is October 26, 2018 DRAFT 23 2 3 4 5 6 7 10 −5 10 −4 10 −3 10 −2 10 −1 10 0 E b /N o BER No ISI, LP No ISI, MSA EPR4, LP EPR4, MSA Modified EPR4, LP Modified EPR4, MSA PR4, LP PR4, MSA Fig. 7. BER vs. E b / N o for coded LP detection and coded MSA detection in four chan nels. a 0. 5 dB SNR g ain. In addition, by using SP A instead of MSA, we obtain a 2 dB SNR gain. W e have observed that, for the othe r three channel, the gap between MSA and SP A was betwee n 0.3 to 0.7 dB. V . C O N C L U S I O N In this paper , we introduced a ne w graph representation of ML detection in ISI channe ls, which can be used for combined equa lization and decoding using LP relaxation o r iterati ve messa ge-passing methods. By a g eometric study o f the problem, we deri ved a necessa ry and s ufficient cond ition for the equalization problem to gi ve the ML solution for all transmitted s equen ces and all noise configurations under L P relaxation. Moreover , for certain other ch annels v iolating this condition, the performance of LP is very close to that of ML at high SNRs. For a third class of channels, L P detection h as a probability of f ailure bounde d away from zero at a ll SNR, ev en in the a bsenc e of noise . In a s tep toward the ana lysis of the performance in the g eneral ca se, we deriv ed a d istance, δ ∞ , for ISI channels, which can be use d as a tool to estimate the asy mptotic behavior of the prop osed detection method. S imulation results show that messag e-passing techniques have a similar p erformance to that of LP for most chan nels. In add ition, we studied graph-bas ed joint detection and decod ing of chann els with LDPC-code d inpu ts. Simulation results indicate that, in contrast to the uncoded case , mess age-pas sing d etection s ignificantly outperforms LP detection for some channe ls. October 26, 2018 DRAFT 24 2.5 3 3.5 4 4.5 5 5.5 6 6.5 7 10 −5 10 −4 10 −3 10 −2 10 −1 10 0 E b /N o BER LP MSA Selective MSA SPA Selective SPA Fig. 8. BER vs. E b / N o for variou s cod ed detection schemes in t he EPR4 channel. R E F E R E N C E S [1] L. R. Bahl, J. Cock e, F . Jelinek, and J. Ra vi v , “Optimal decoding of li near codes for minimizing symbol error rate, ” IEEE T rans. Inform. Theory , v ol. IT -20, pp. 284-287, Mar . 19 74. [2] J. Hagenauer and P . Hoecher , “ A V iterbi algorithm with soft- decision outputs and its applications, ” in Proc. IEEE GLOBECOM , Dallas, TX, No v . 19 89, vol. 3, pp. 168 0-1686. [3] B. M. K urko ski, P . H. Sie gel, an d J. K. W olf, “Joint me ssage-passing decoding of LDPC co des and partial-respon se channels, ” IEEE T ra ns. Inform. Theory , v ol. 48, no. 6, pp. 14 10-1422 , Jun. 2002. [4] N. Singla, J. A. O’S ulliv an, R. Indeck, and Y . W u, “Iterative decoding and equalization for 2-D recording channels, ” IEEE T rans. Magnetics, vol. 38, no. 5, pp. 2328-233 0, Sep. 2002. [5] J. F eldman, M. J. W ainwright, and D. Karger , “Using linear programming to decode binary li near codes, ” I EEE T ran s. Inform. Theory , vol. 51, no. 3, pp. 954-972, Mar . 2005 . [6] L. J. W atters, “Reduction of integer polynomial programming problems to zero-one linear programming problems, ” Operation s Researc h , vo l. 15, no. 6, pp. 1171 -1174, Nov . -Dec. 1967. [7] C. L emar ´ echal and F . Oustry , “Semidefinite relaxations and Lagrangian duality with application to combinatorial optimiza- tion, ” Rapport de Rec her che no. 3710, INRIA, Jun. 199 9. [8] M.X. Goemans and D .P . W il liamson, “Improved approximation algorithms for maximum cut and satisfiability problems using semidefinite programming, ” J. ACM , vol. 42, no. 6, pp . 1115-1145, Nov . 1995 [9] J. M. W . Rhys, “ A selection problem of shared fixed costs and network flows, ” Mana geme nt Sci , vo l. 17, no. 3, pp.200-2 07, Nov . 1970. [10] C. S ankaran and A. Ephremides, “Solving a class of optimum multiuser detection problems with polynomial complex ity , ” IEEE T ra ns. Inform. Theory , v ol. 44, no. 5, pp. 1958-1961, Sep. 1998. October 26, 2018 DRAFT 25 [11] I. D. Mercer, “ Autocorrelations of rando m binary sequences, ” Combinatorics, Pr obability and Computing , v ol. 15, no. 5, pp. 663-671, Sep. 2006. [12] M. H. T agha vi and P . H . Siegel, “ Adaptiv e methods for linear programming decoding, ” Submitted to IEEE T rans. Inform. Theory , Mar . 200 7. October 26, 2018 DRAFT
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment